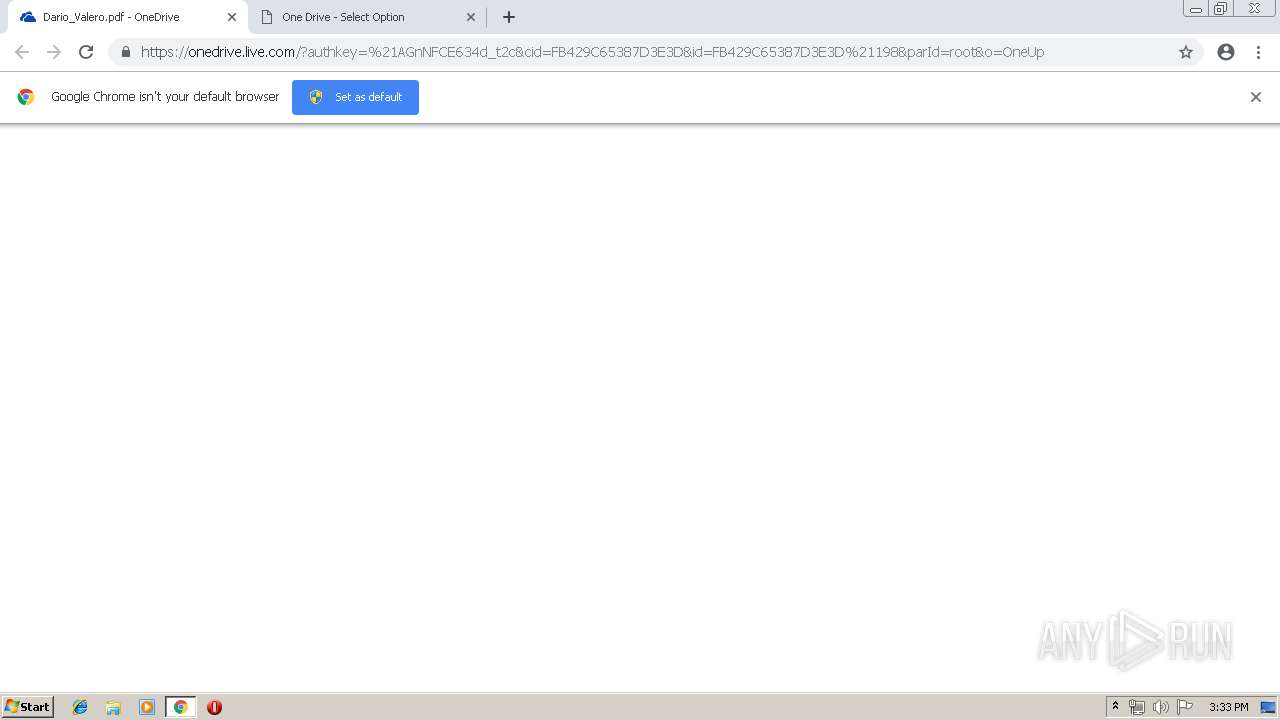
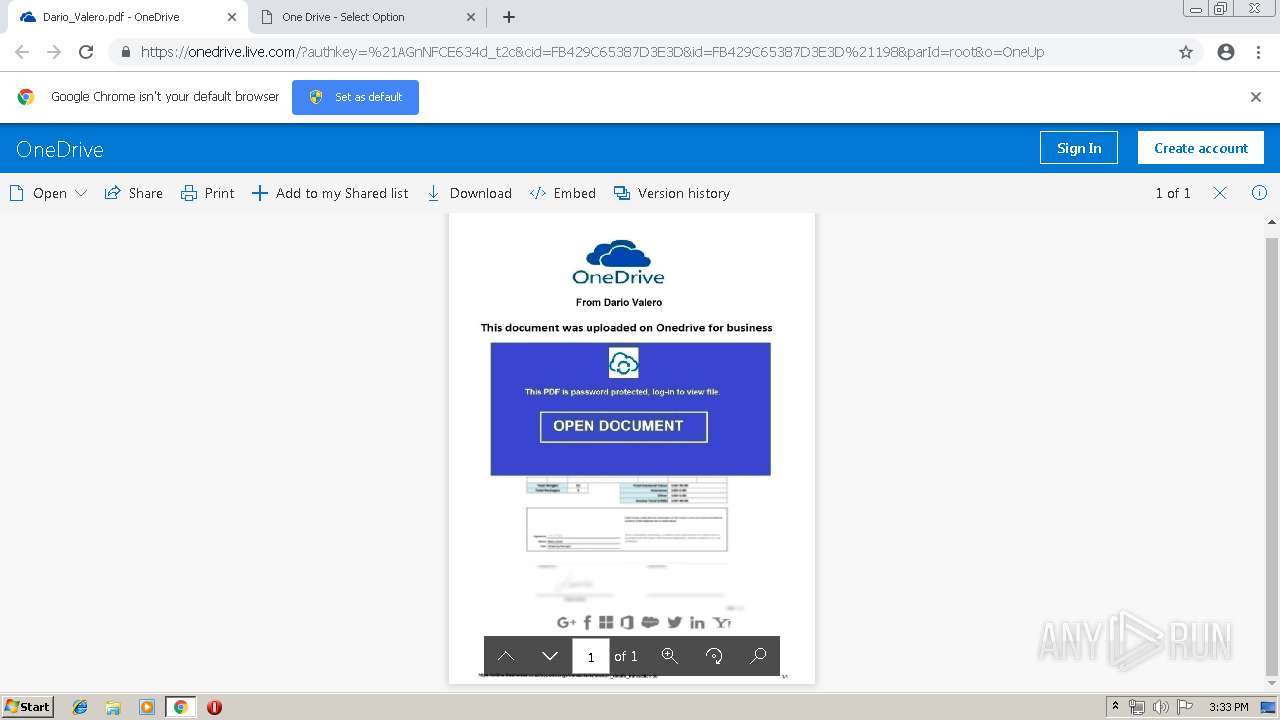
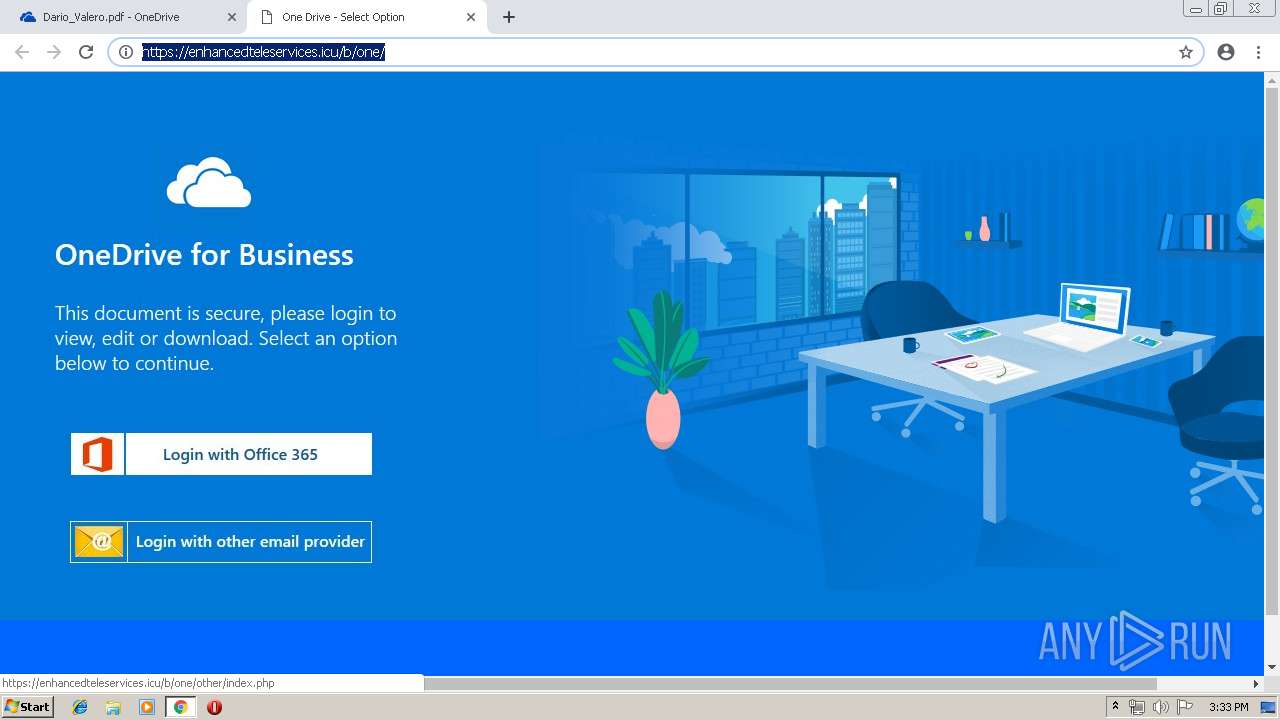
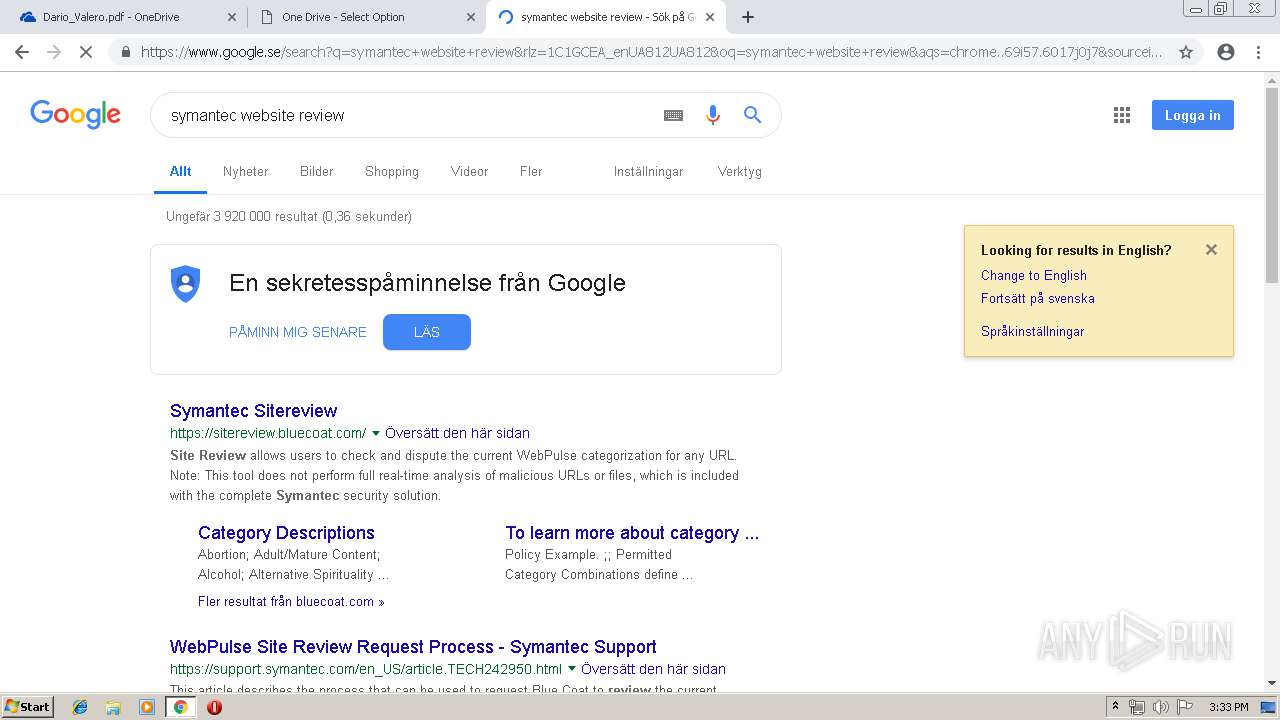
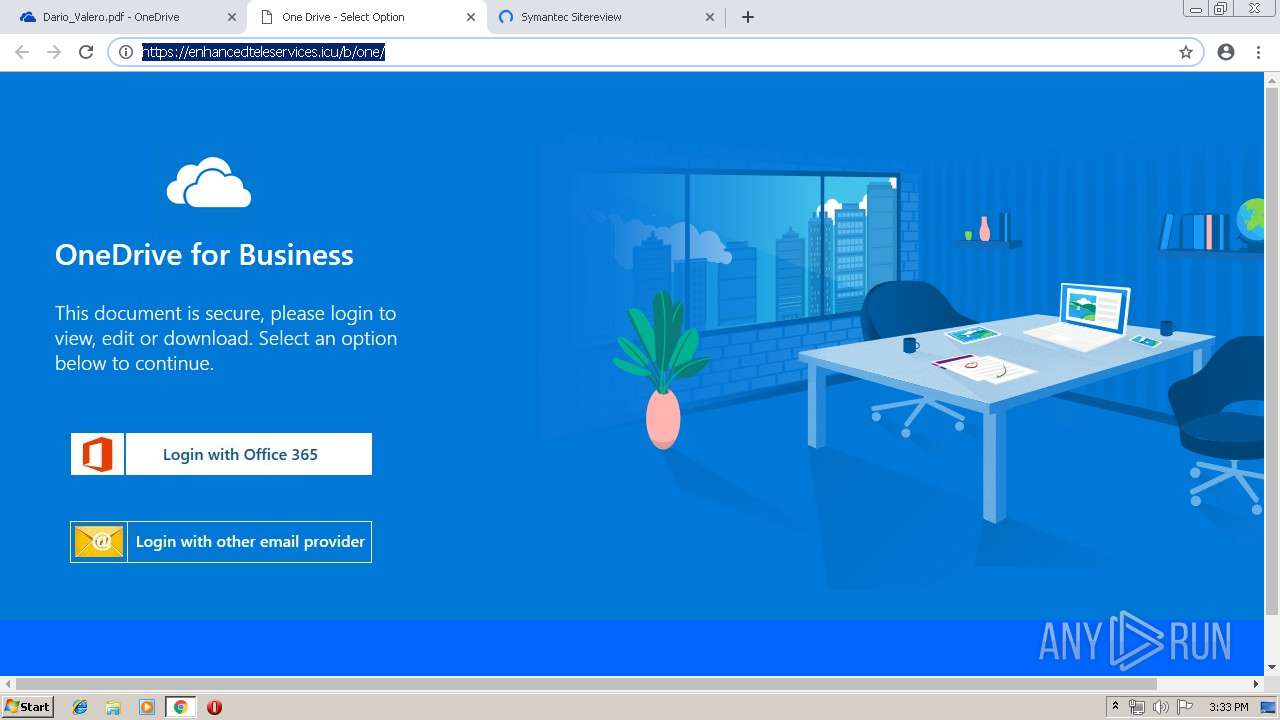
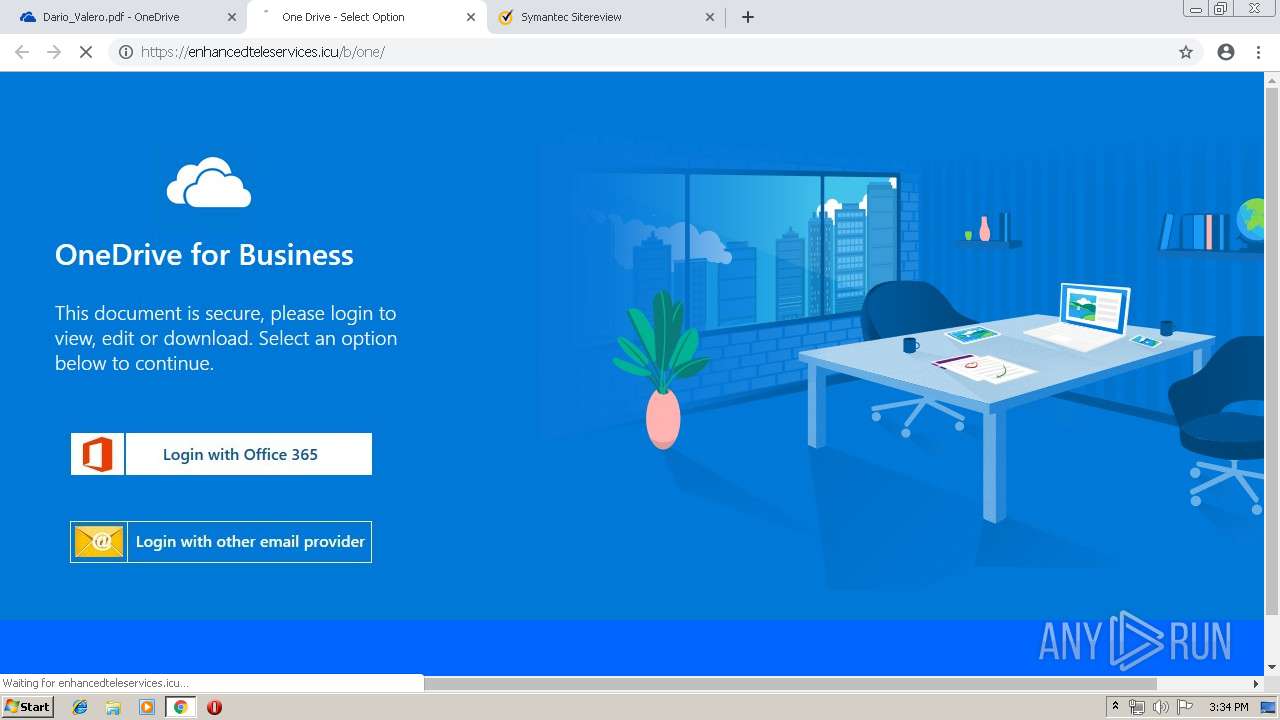
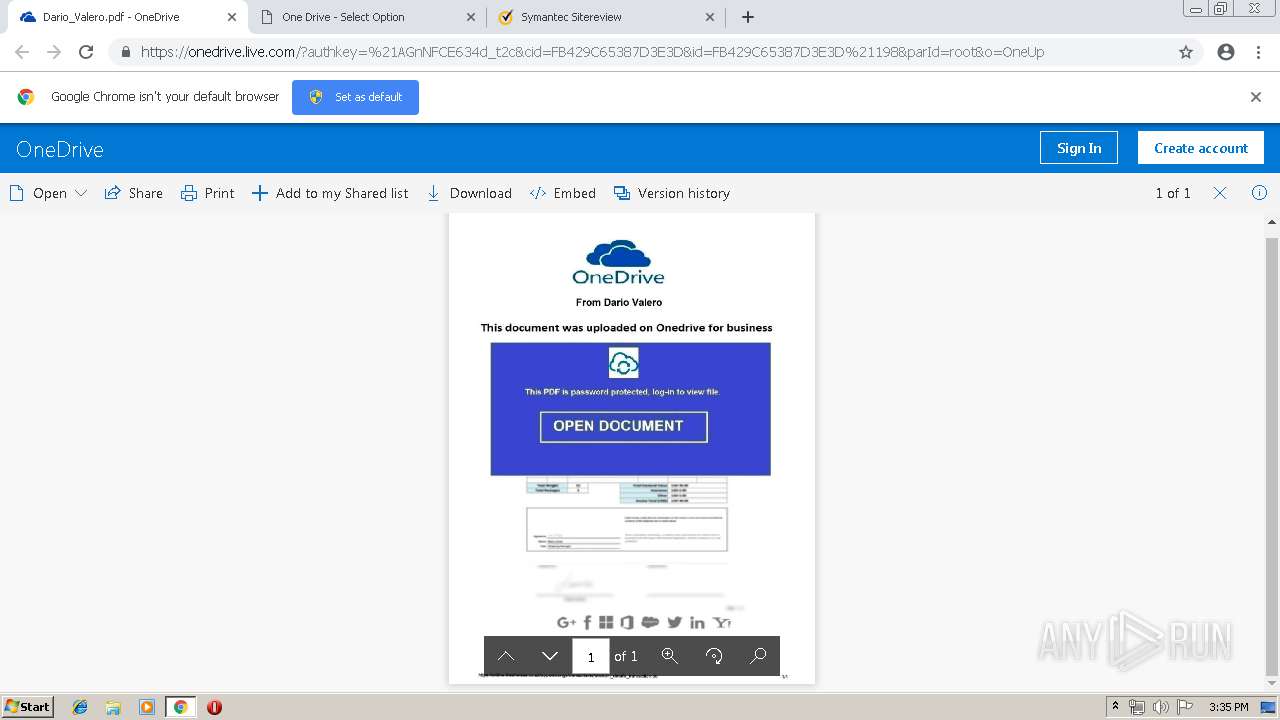
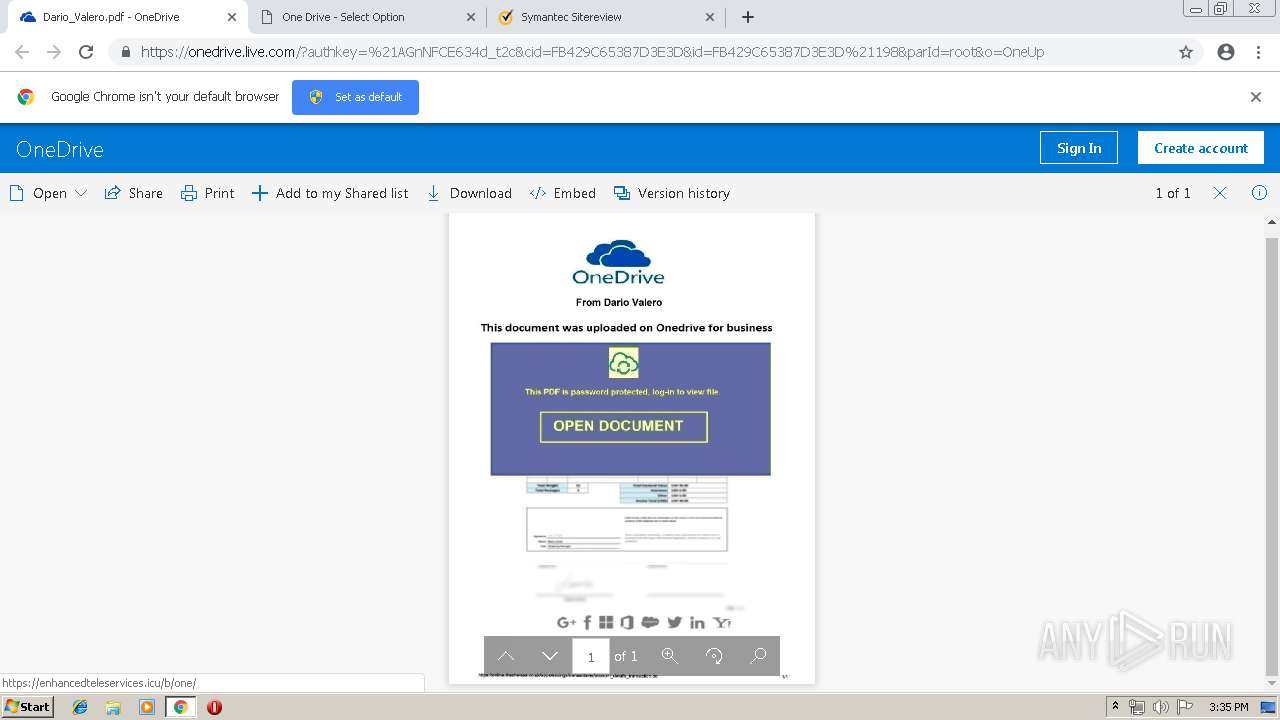
| URL: | https://onedrive.live.com/?authkey=%21AGnNFCE634d%5Ft2c&cid=FB429C65387D3E3D&id=FB429C65387D3E3D%21198&parId=root&o=OneUp |
| Full analysis: | https://app.any.run/tasks/6d0a2b58-22ed-49b5-8b3f-81de2ef5974c |
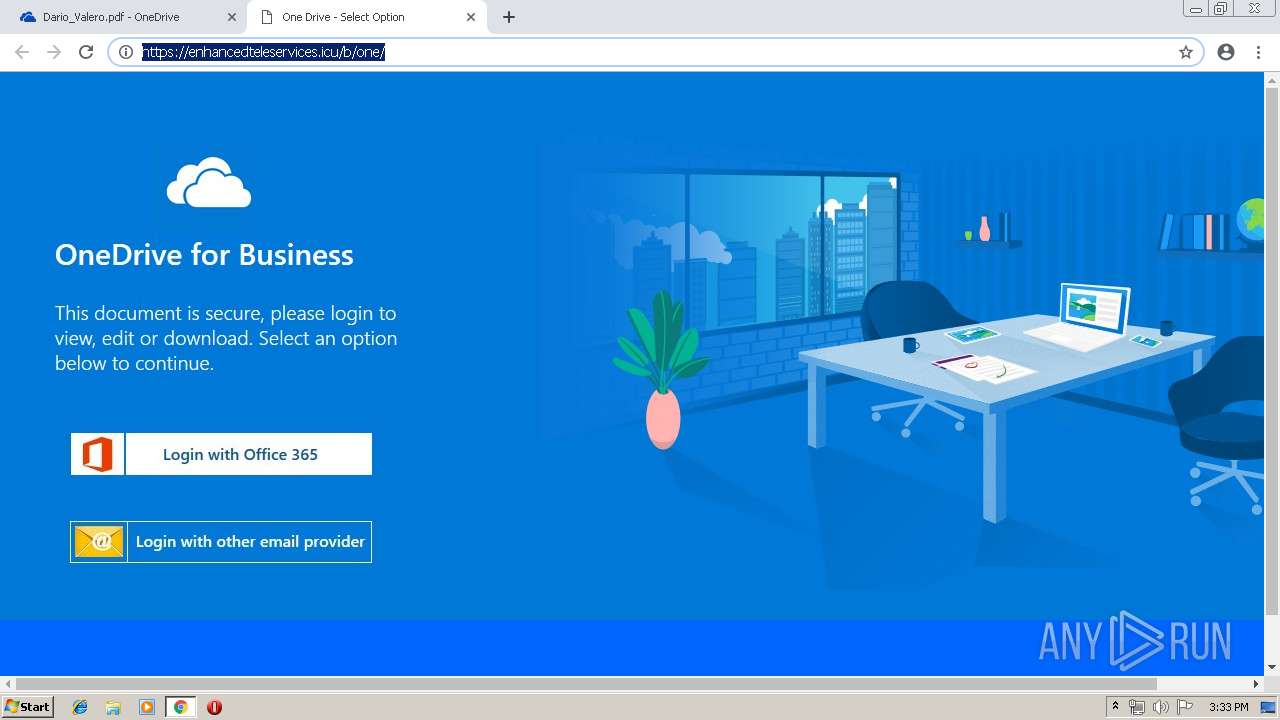
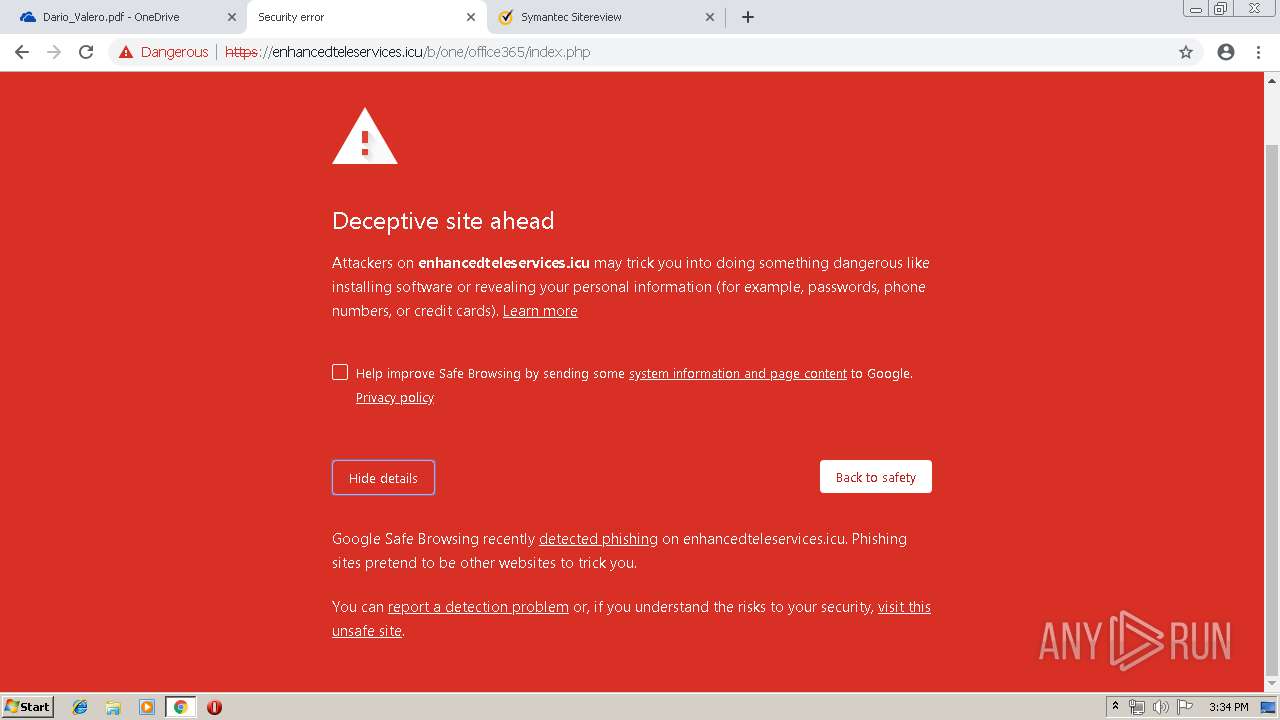
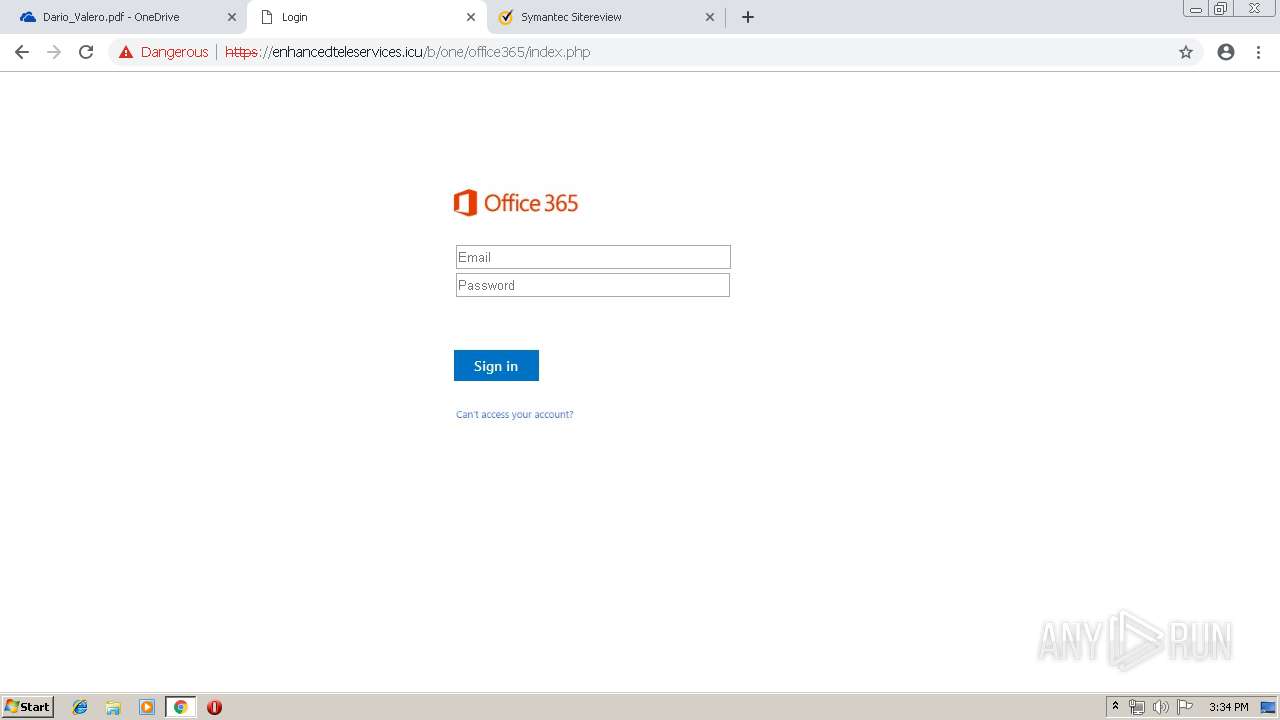
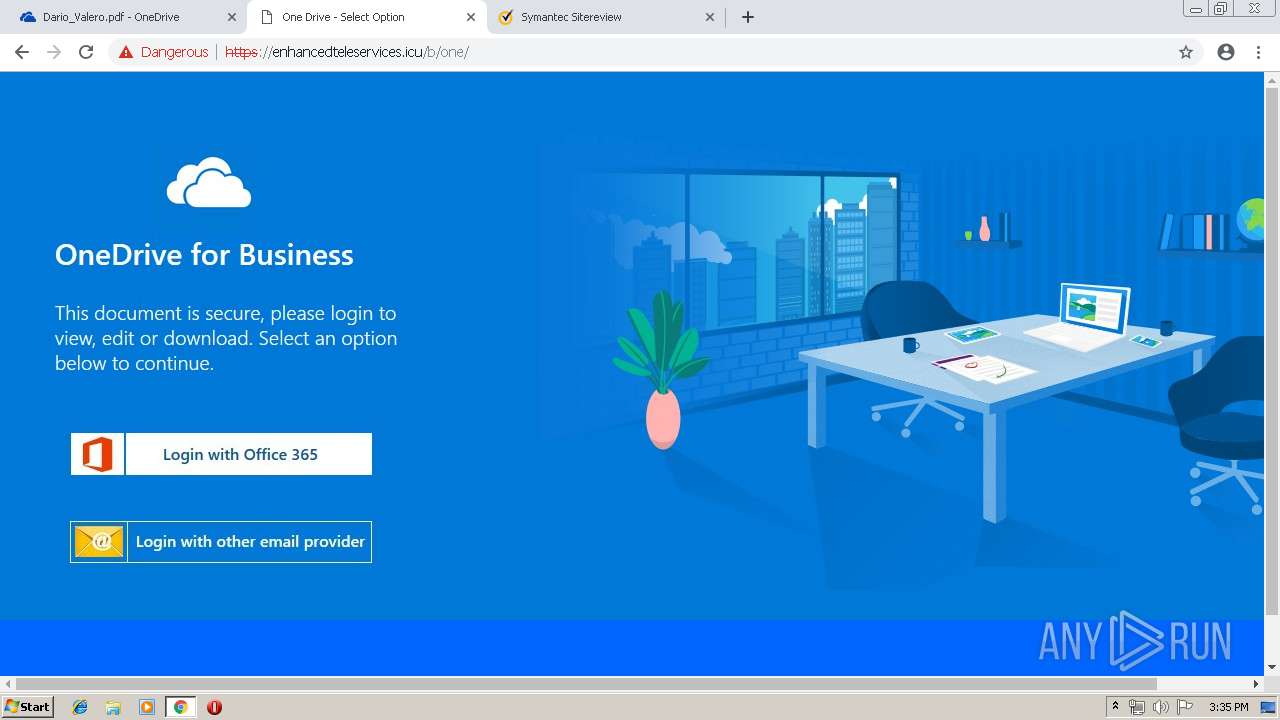
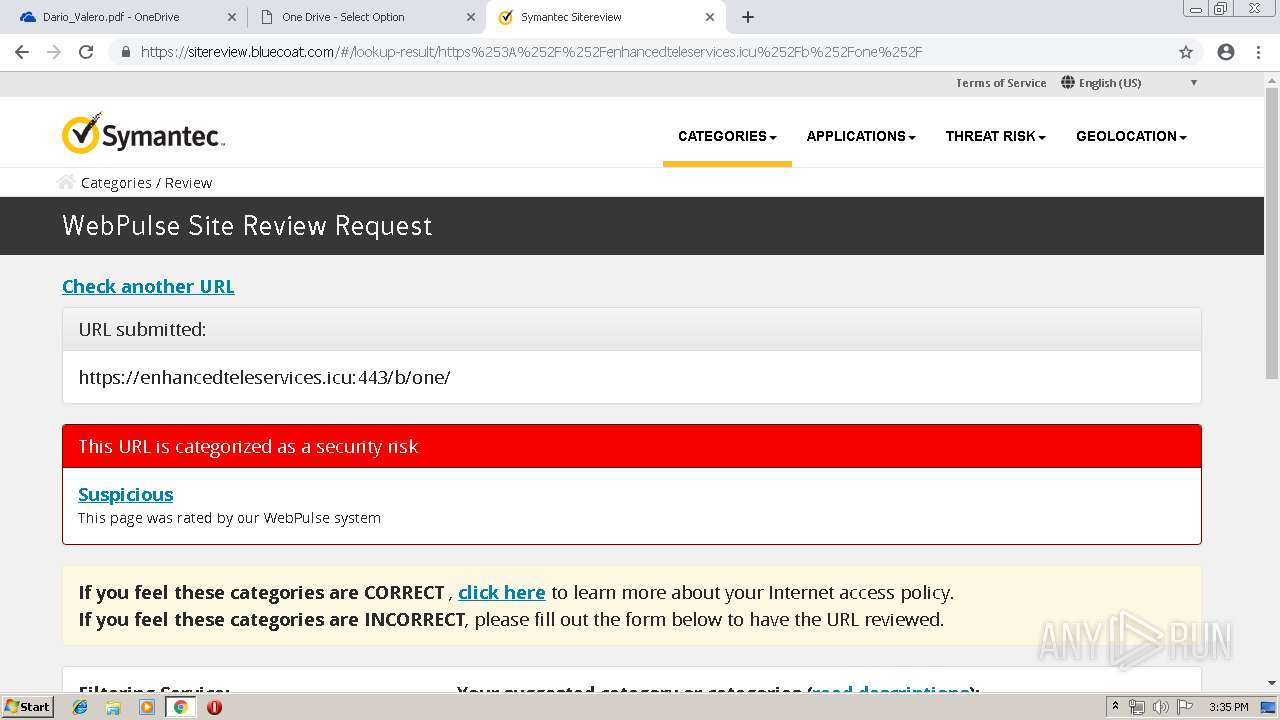
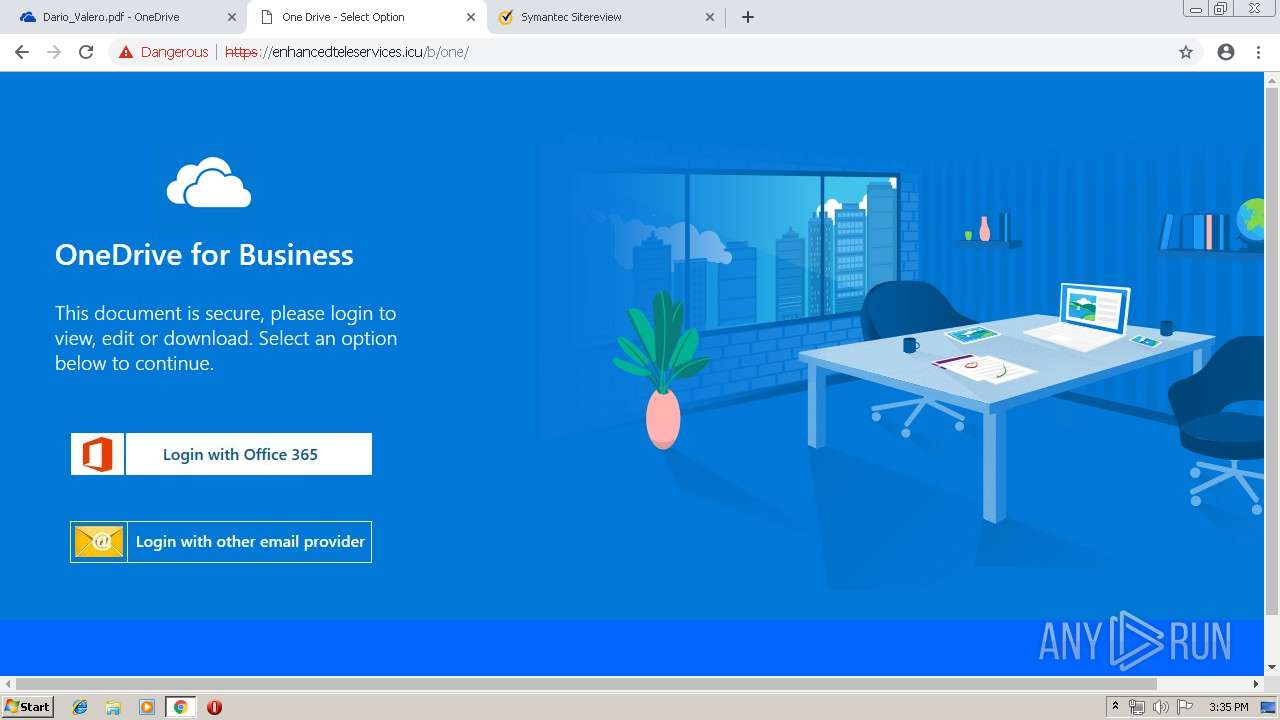
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 14:32:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E1E5463E9A38CB66BA80EB9E80E4A061 |
| SHA1: | E54DD7EF7A66859BD7C90026AA566945098059F3 |
| SHA256: | 208B393D480DA8B67C3DBB1D7AC859864AECF73BAF59C46EDECEF8A2ADDA3959 |
| SSDEEP: | 3:N8Ck3CTZxAXASgK/EG91XXdlgmDAYdXdlgmAXNpzKHJV:2CkSTfAXATK/v9VFDXFyLyb |
MALICIOUS
No malicious indicators.SUSPICIOUS
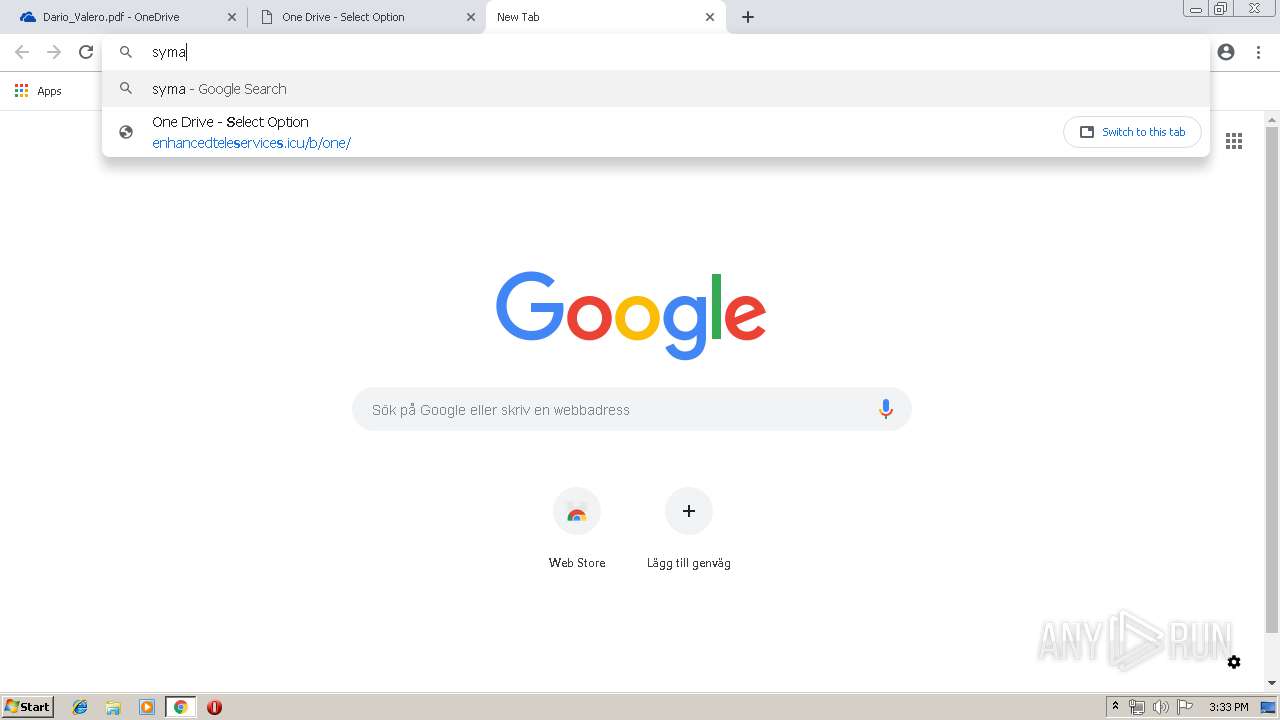
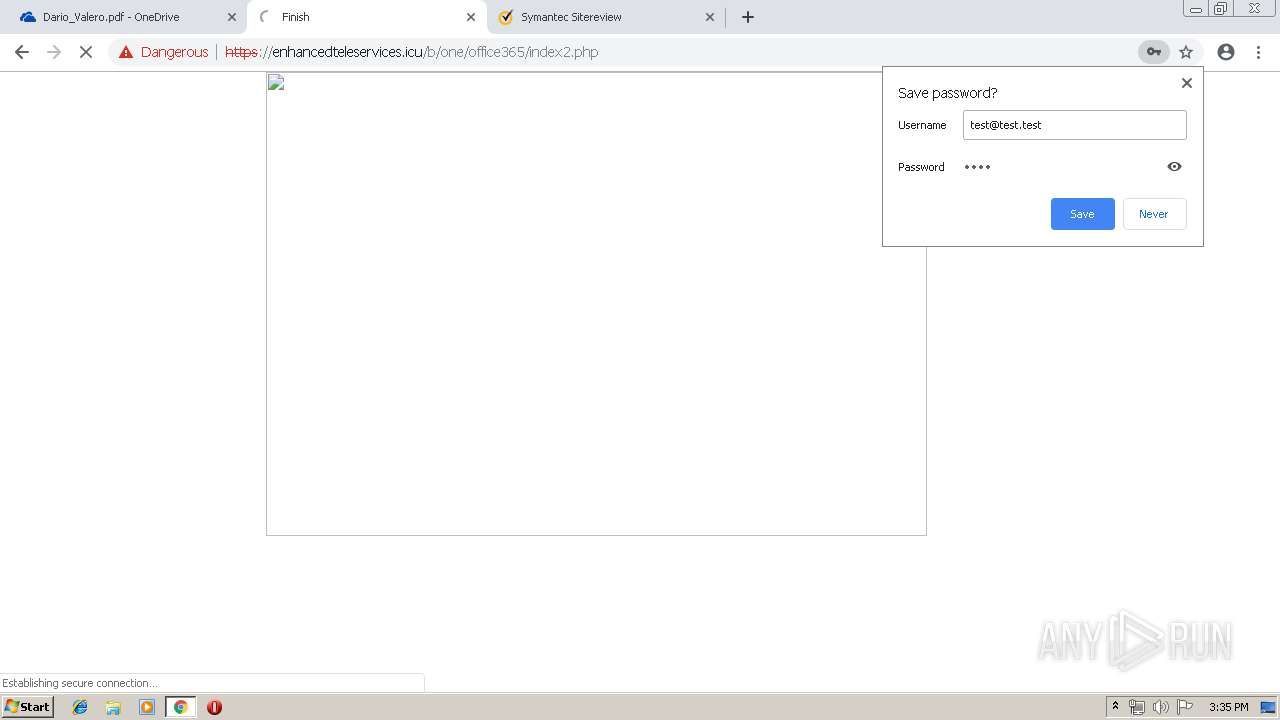
Modifies files in Chrome extension folder
- chrome.exe (PID: 3012)
INFO
Application launched itself
- chrome.exe (PID: 3012)
Reads settings of System Certificates
- chrome.exe (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,16607675865988117028,8973671915990232219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8064855916569101645 --mojo-platform-channel-handle=4524 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=908,16607675865988117028,8973671915990232219,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15919827797721946329 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,16607675865988117028,8973671915990232219,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17896057750504852816 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17896057750504852816 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,16607675865988117028,8973671915990232219,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14375841142580387073 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14375841142580387073 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,16607675865988117028,8973671915990232219,131072 --enable-features=PasswordImport --service-pipe-token=17506800253353317889 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17506800253353317889 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,16607675865988117028,8973671915990232219,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13898450572399788195 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13898450572399788195 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,16607675865988117028,8973671915990232219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7915272234539180001 --mojo-platform-channel-handle=4468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,16607675865988117028,8973671915990232219,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1970422599829001270 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1970422599829001270 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,16607675865988117028,8973671915990232219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7613577642474158675 --mojo-platform-channel-handle=4396 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,16607675865988117028,8973671915990232219,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8479389156255918621 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8479389156255918621 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
574
Read events
476
Write events
93
Delete events
5
Modification events
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3012-13200676334933250 |
Value: 259 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
192
Text files
225
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\de7873dd-f626-4b1c-892e-5bb0b52e0726.tmp | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
92
DNS requests
53
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3012 | chrome.exe | GET | 200 | 2.17.107.40:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT0MXB3rveIElndnl0j8v4md2bQRgQUOdr%2FyigUiqh0Ewi55A6p0vp%2BnWkCEGlUsfOxYNRhdX6ayZ24AMA%3D | unknown | der | 471 b | whitelisted |
3012 | chrome.exe | GET | 200 | 31.220.17.26:80 | http://shopget24.com/images/sampledata/hack-run.png | US | image | 24.2 Kb | malicious |
3012 | chrome.exe | GET | 200 | 2.17.107.40:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEAanQ4DU6%2F7UNbWj9%2BFqvdg%3D | unknown | der | 727 b | whitelisted |
3012 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
— | — | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
3012 | chrome.exe | GET | 200 | 2.16.106.80:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | unknown | der | 471 b | whitelisted |
3012 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/DF3C24F9BFD666761B268073FE06D1CC8D4F82A4.crt | US | der | 914 b | whitelisted |
3012 | chrome.exe | GET | 200 | 172.217.130.73:80 | http://r4---sn-2gb7sn7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.76.9.72&mm=28&mn=sn-2gb7sn7r&ms=nvh&mt=1556202579&mv=m&pl=25&shardbypass=yes | US | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3012 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
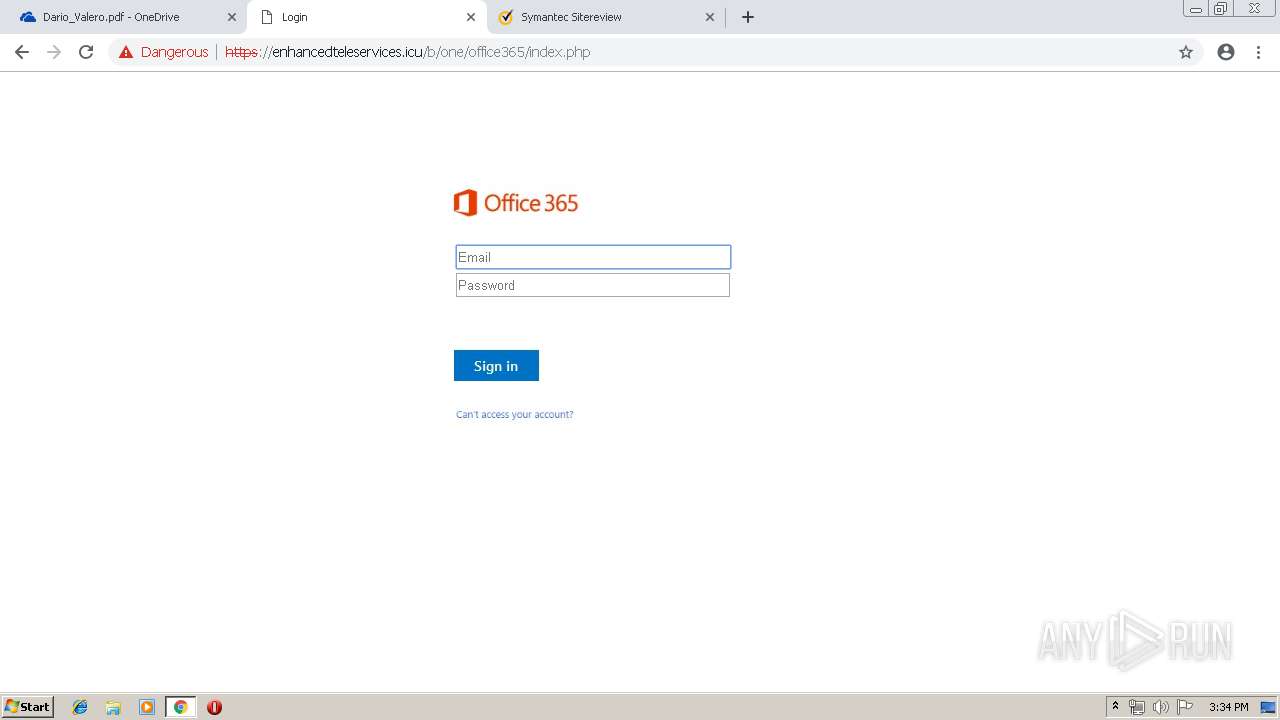
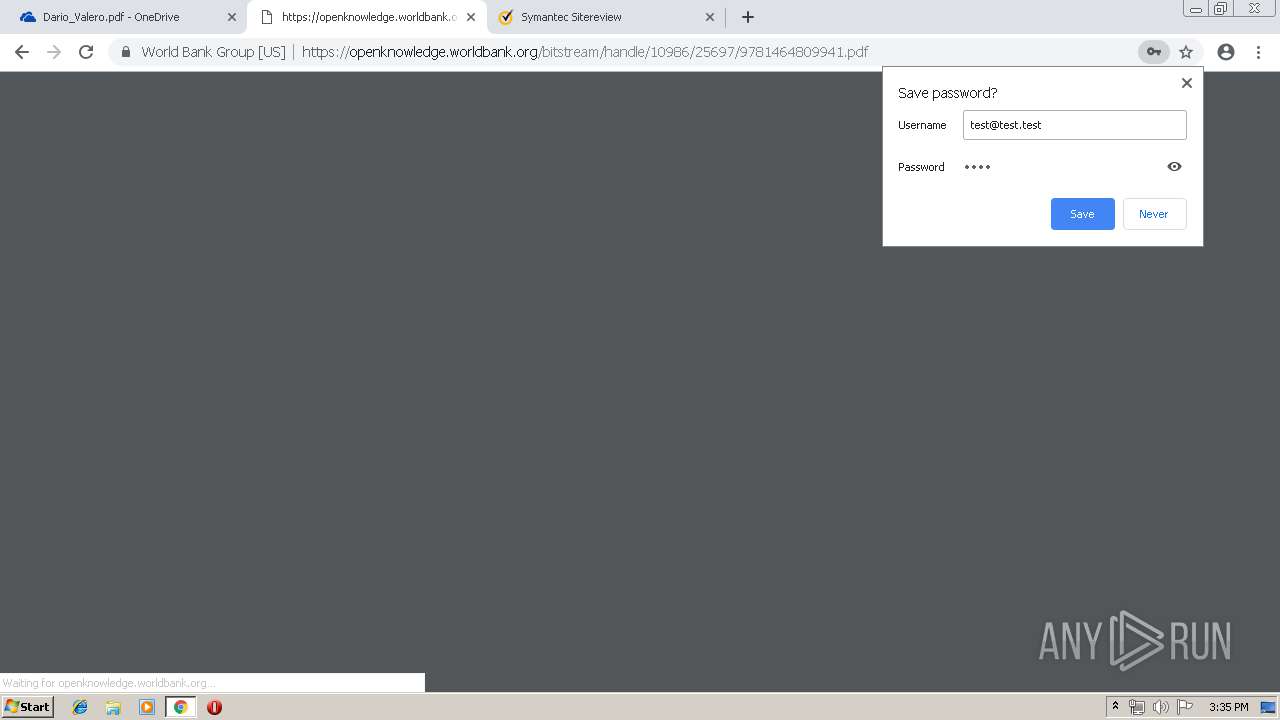
3012 | chrome.exe | 13.107.42.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
3012 | chrome.exe | 2.19.34.64:443 | static2.sharepointonline.com | Akamai International B.V. | — | whitelisted |
3012 | chrome.exe | 172.217.18.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 40.90.142.230:443 | skyapi.onedrive.live.com | Microsoft Corporation | US | whitelisted |
3012 | chrome.exe | 52.114.158.52:443 | browser.pipe.aria.microsoft.com | Microsoft Corporation | US | unknown |
3012 | chrome.exe | 172.227.86.106:443 | r3.res.outlook.com | Akamai Technologies, Inc. | US | whitelisted |
3012 | chrome.exe | 2.16.186.33:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
3012 | chrome.exe | 13.107.3.128:443 | b.config.skype.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
onedrive.live.com |
| shared |
accounts.google.com |
| shared |
spoprod-a.akamaihd.net |
| whitelisted |
static2.sharepointonline.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
skyapi.onedrive.live.com |
| shared |
browser.pipe.aria.microsoft.com |
| whitelisted |
r3.res.outlook.com |
| whitelisted |
www.google.com |
| malicious |
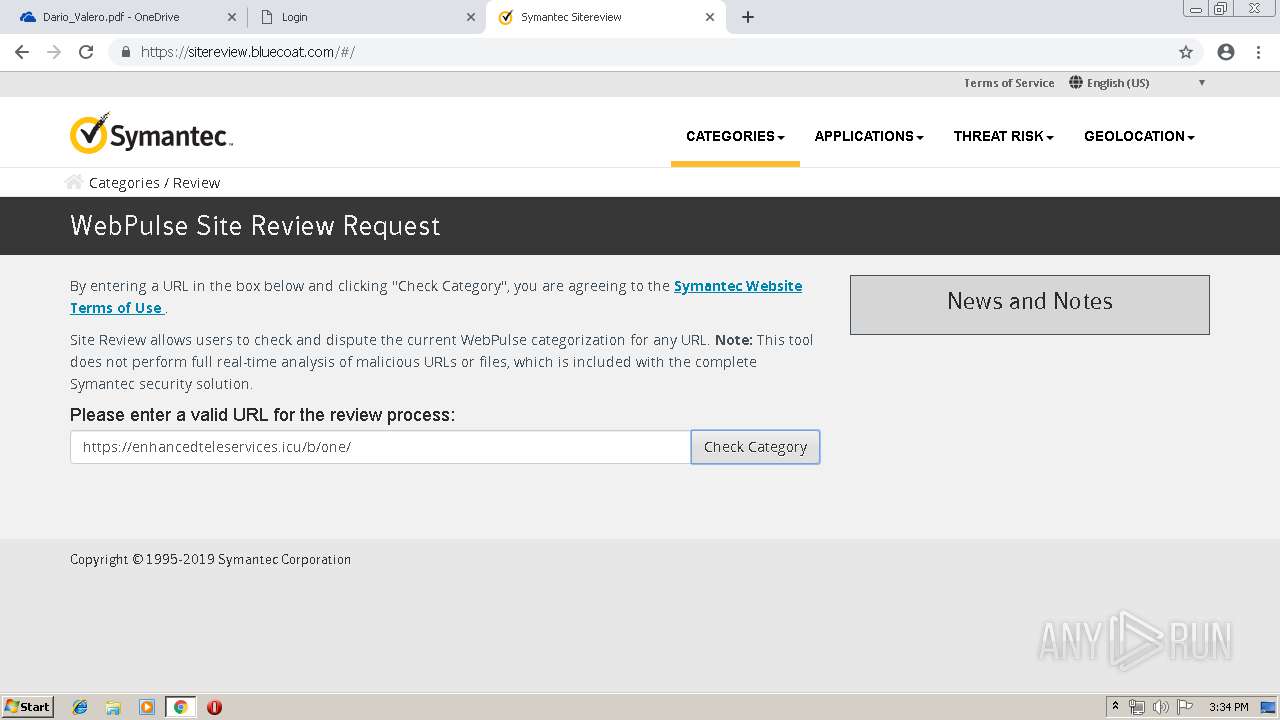
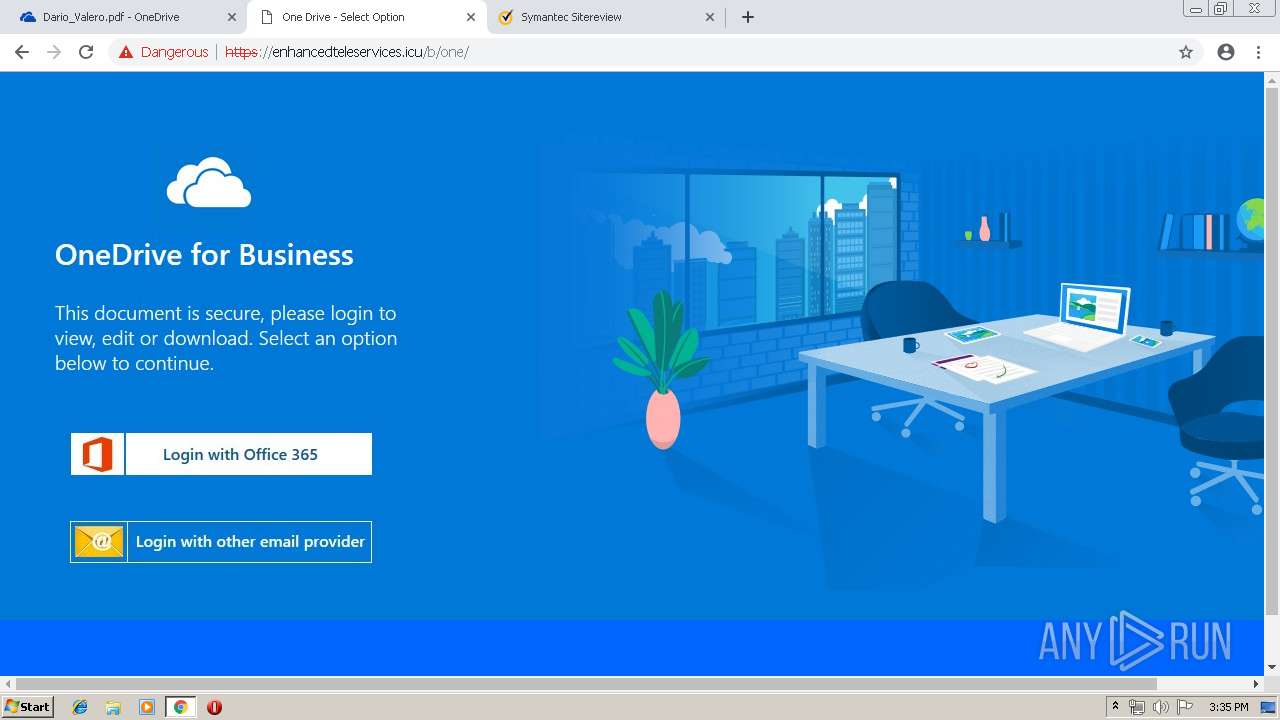
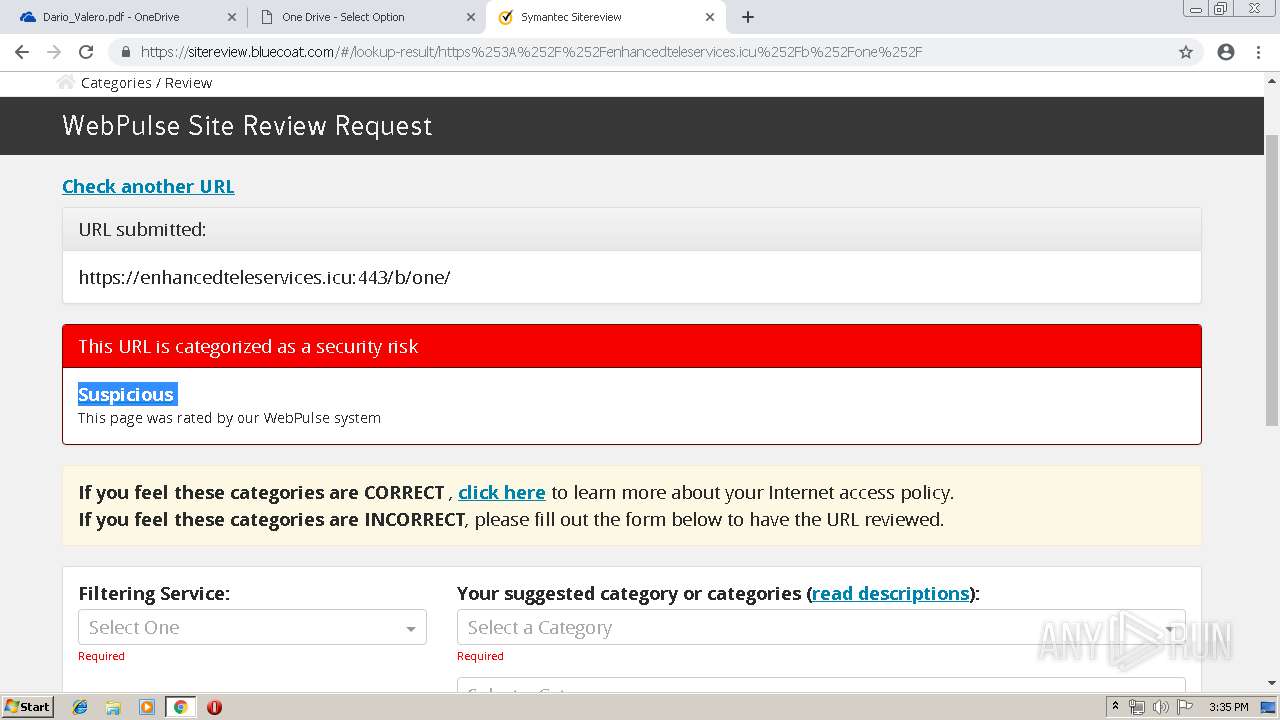
Threats
PID | Process | Class | Message |
|---|---|---|---|
3012 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
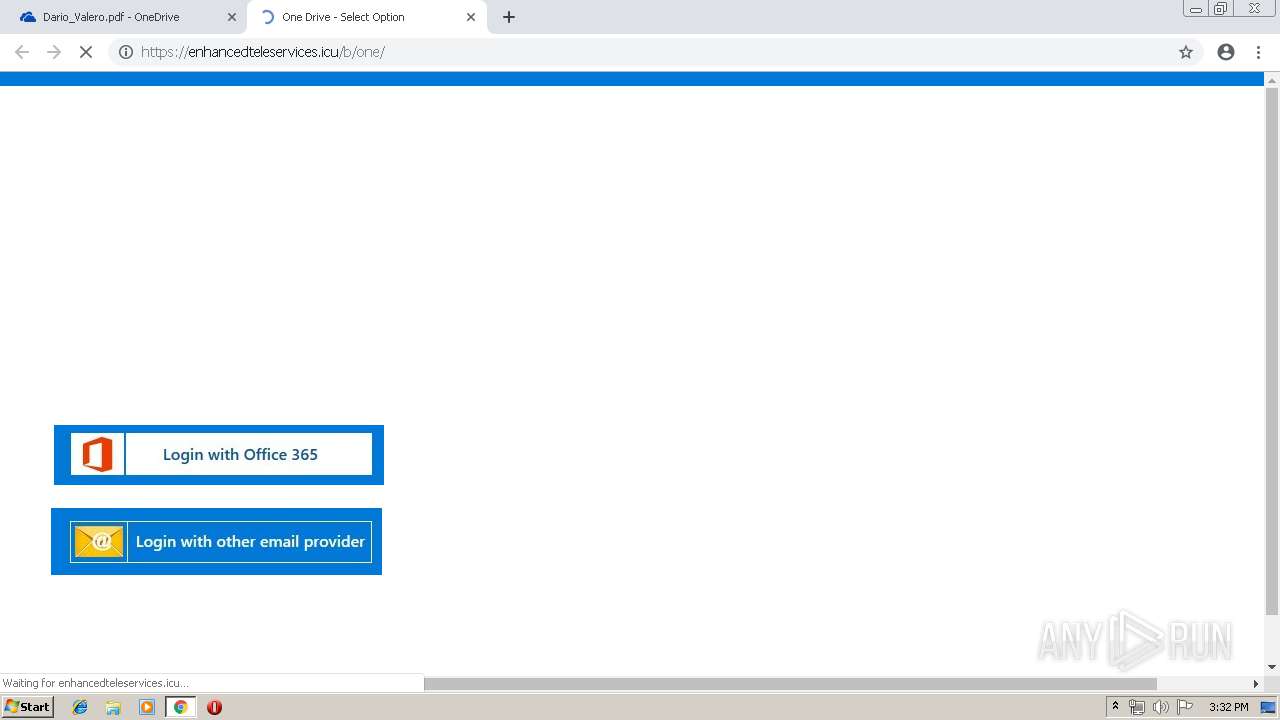
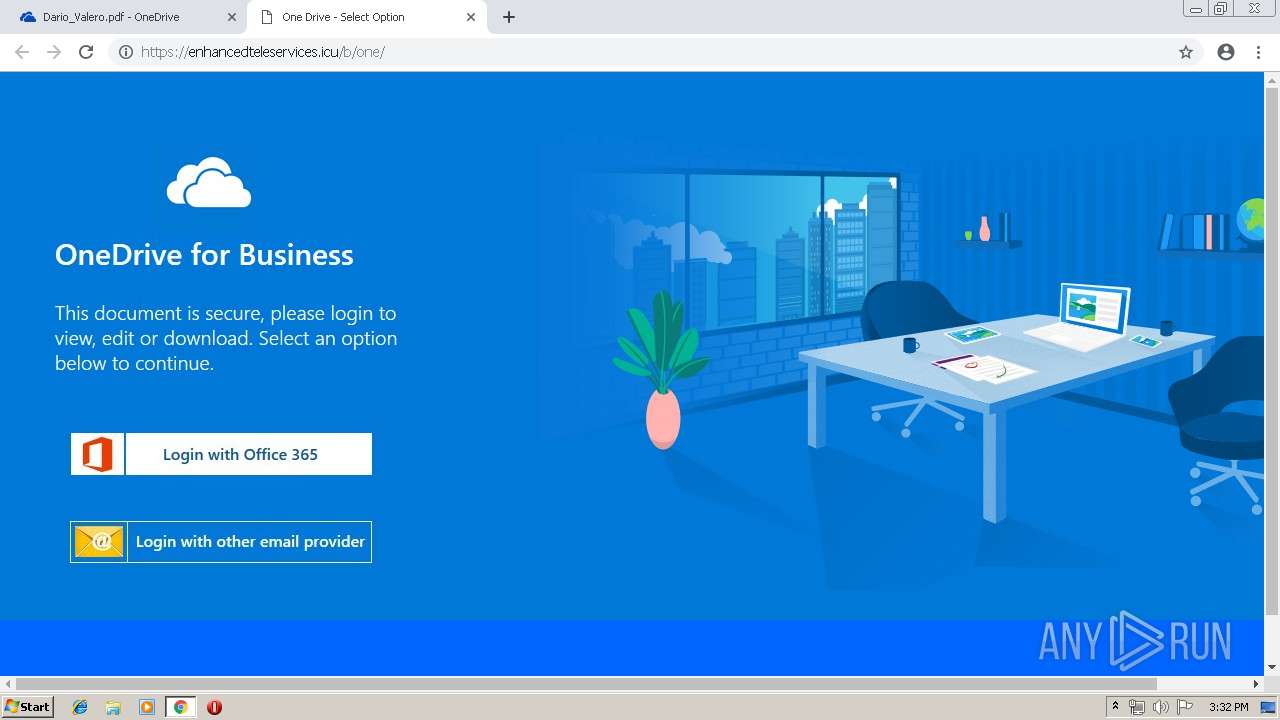
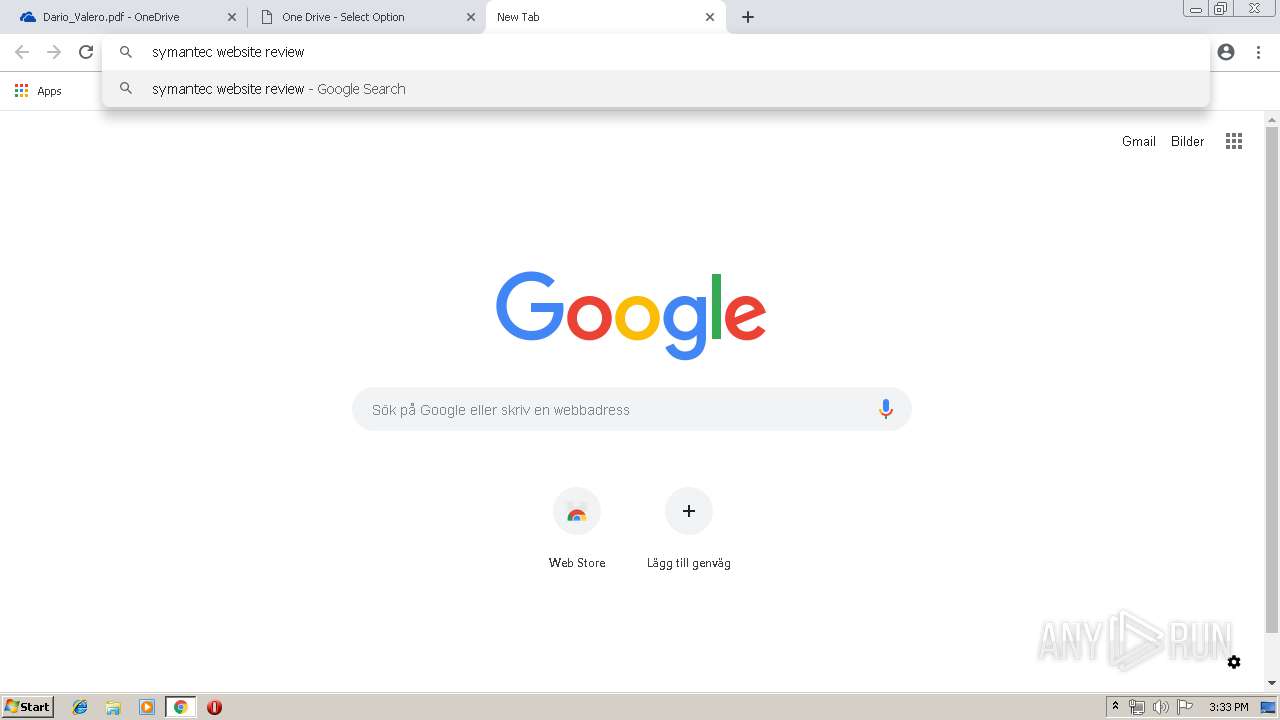
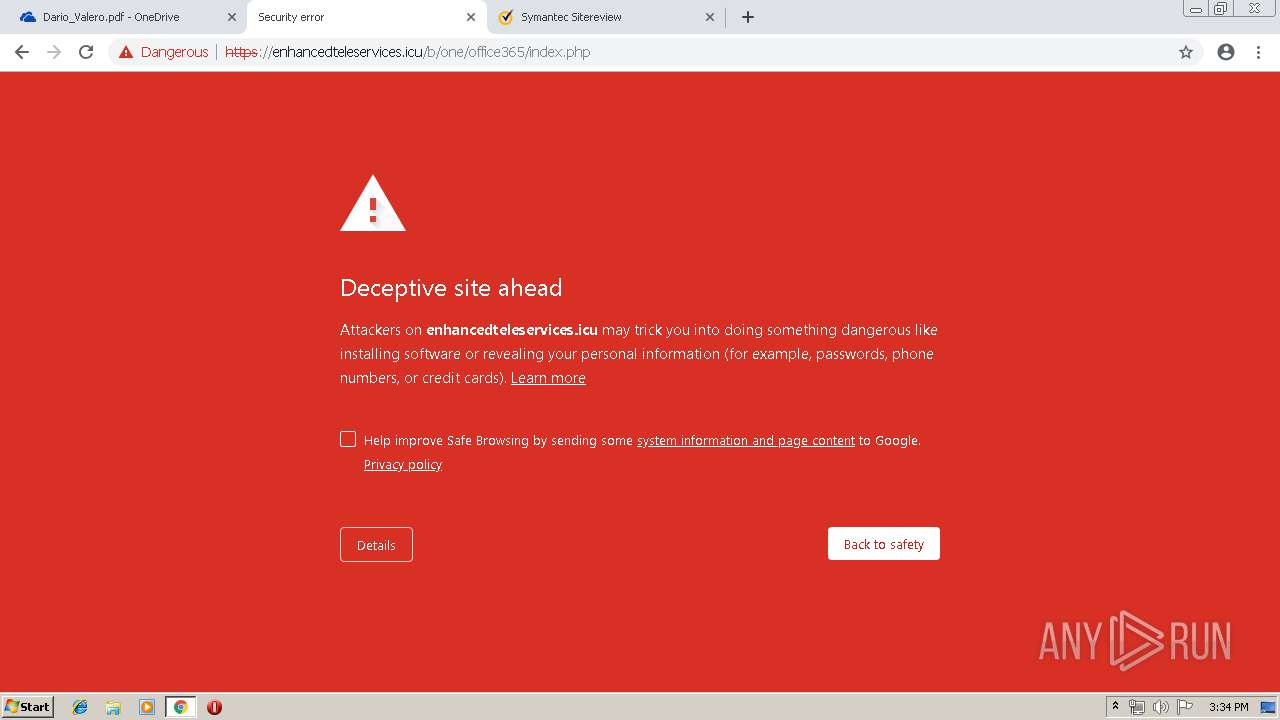
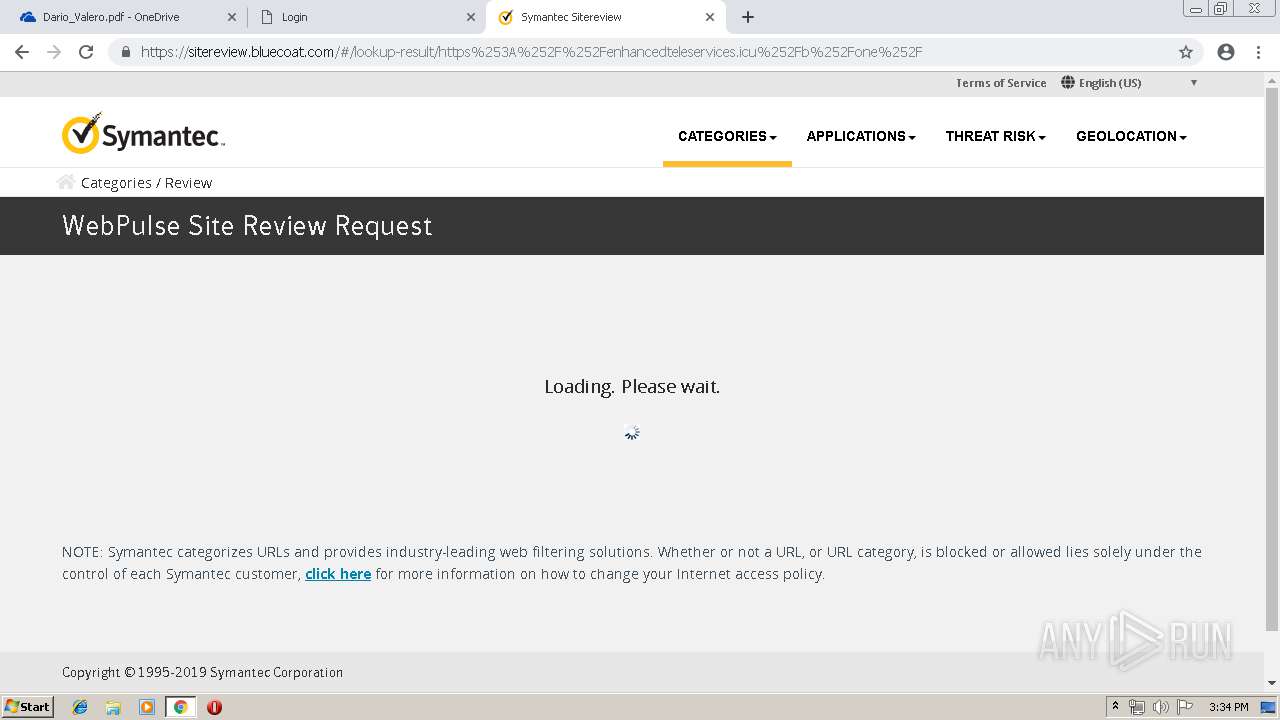
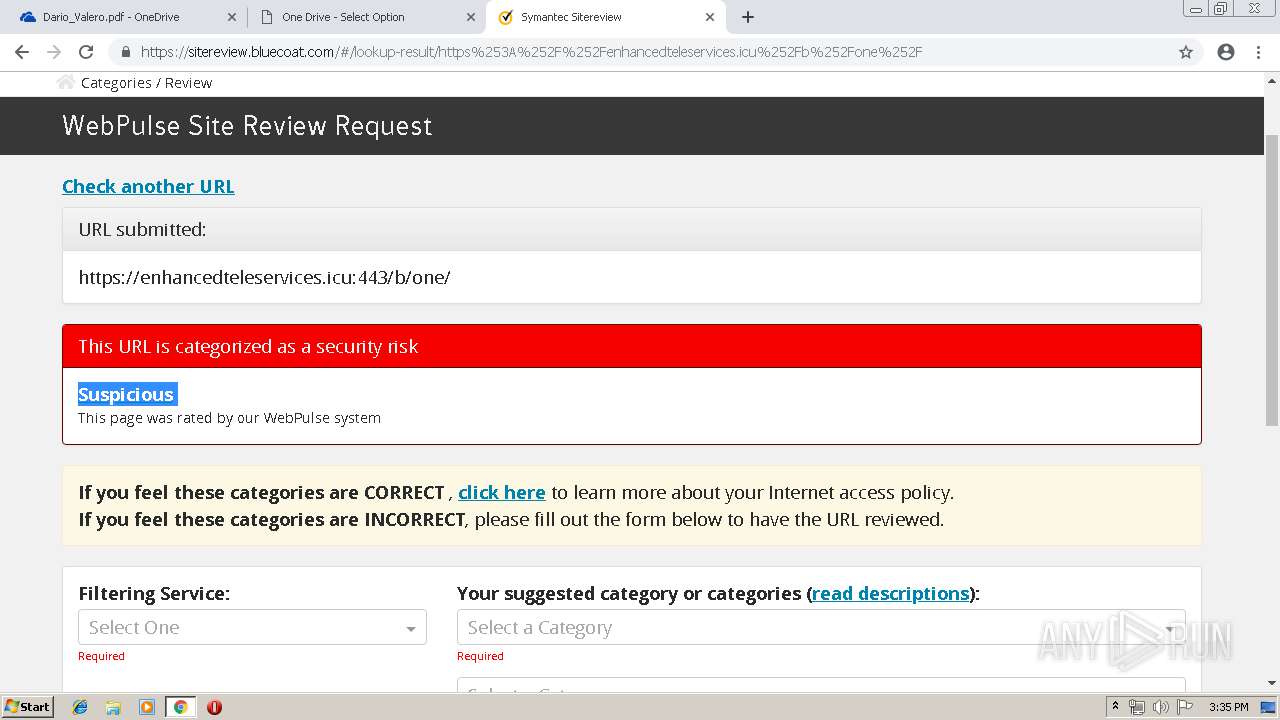
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
3012 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
3012 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3012 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |