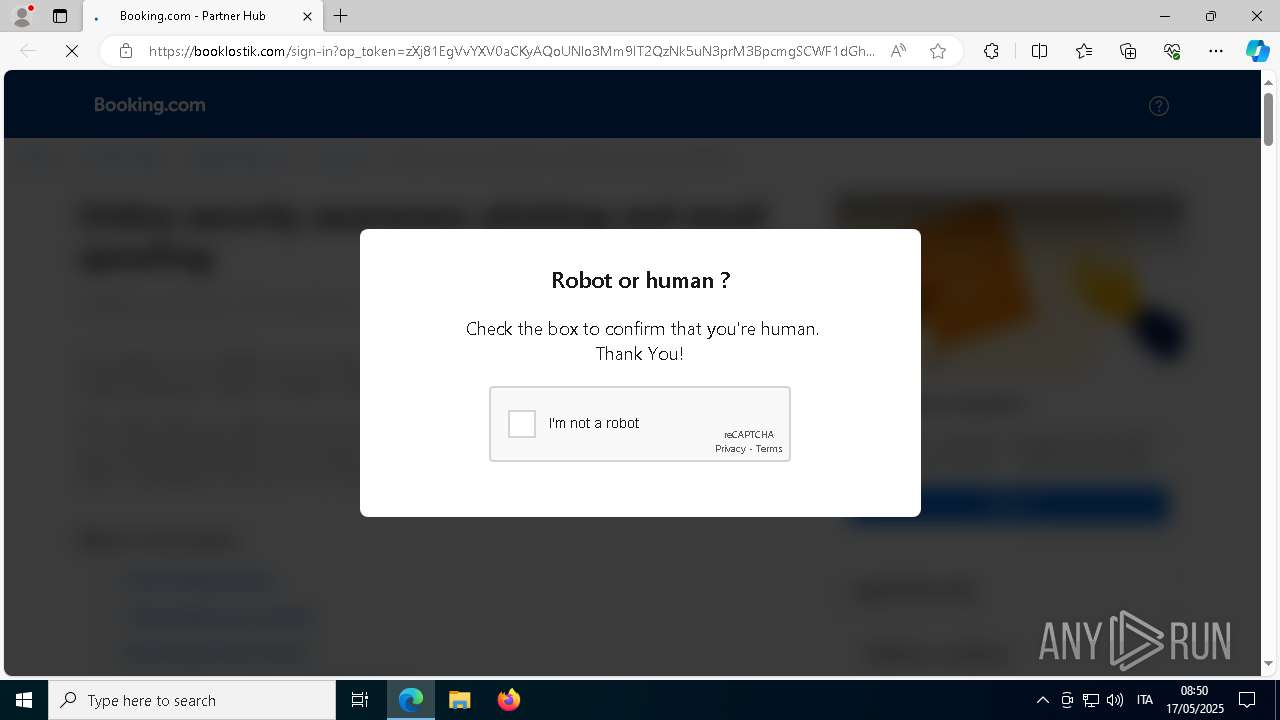
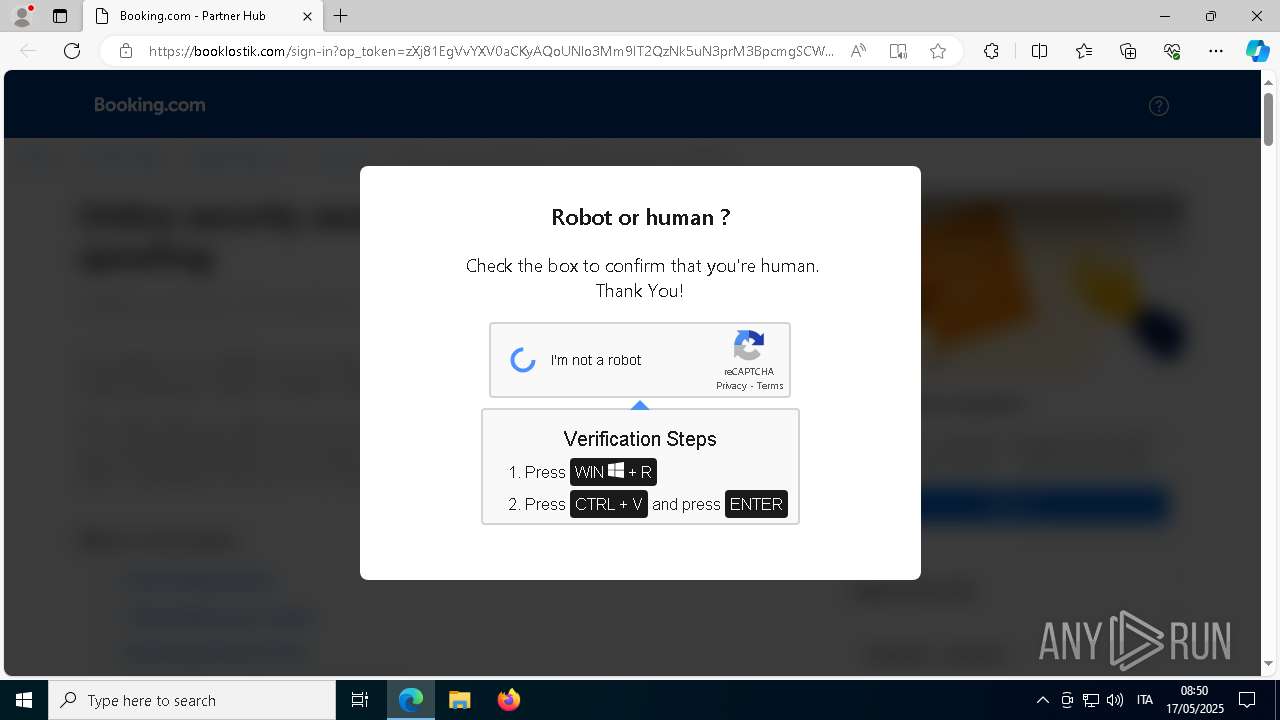
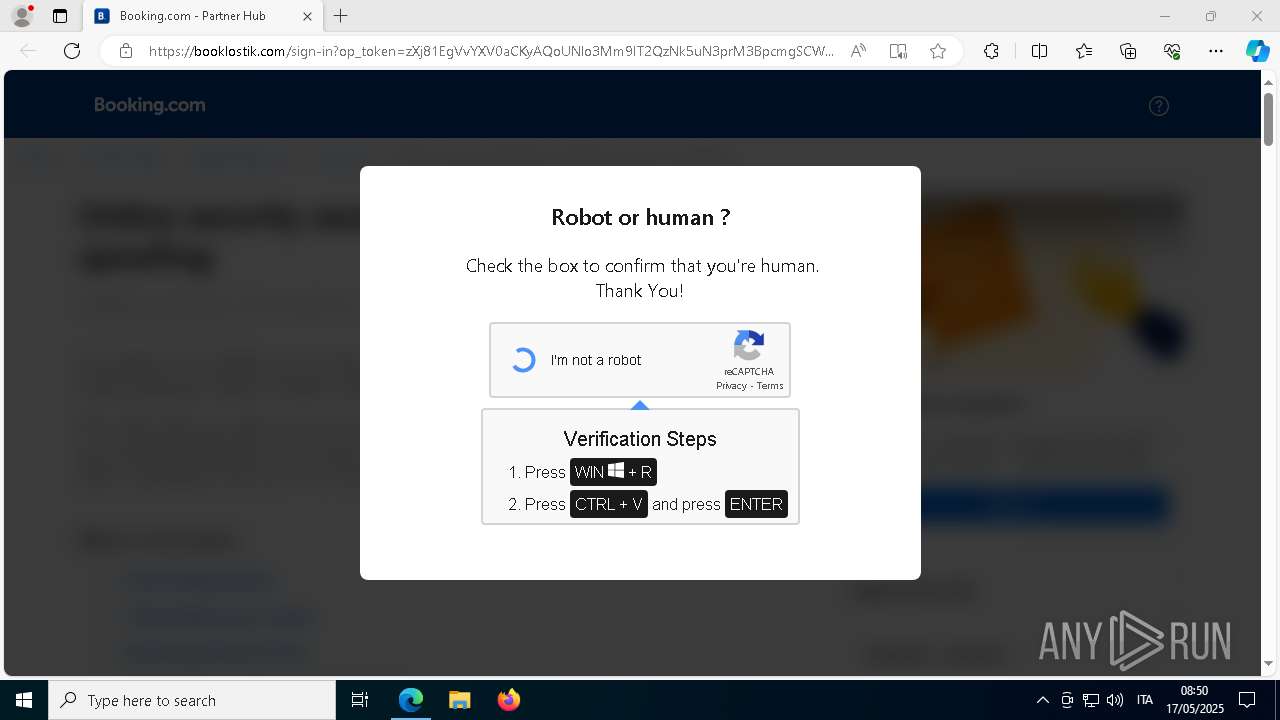
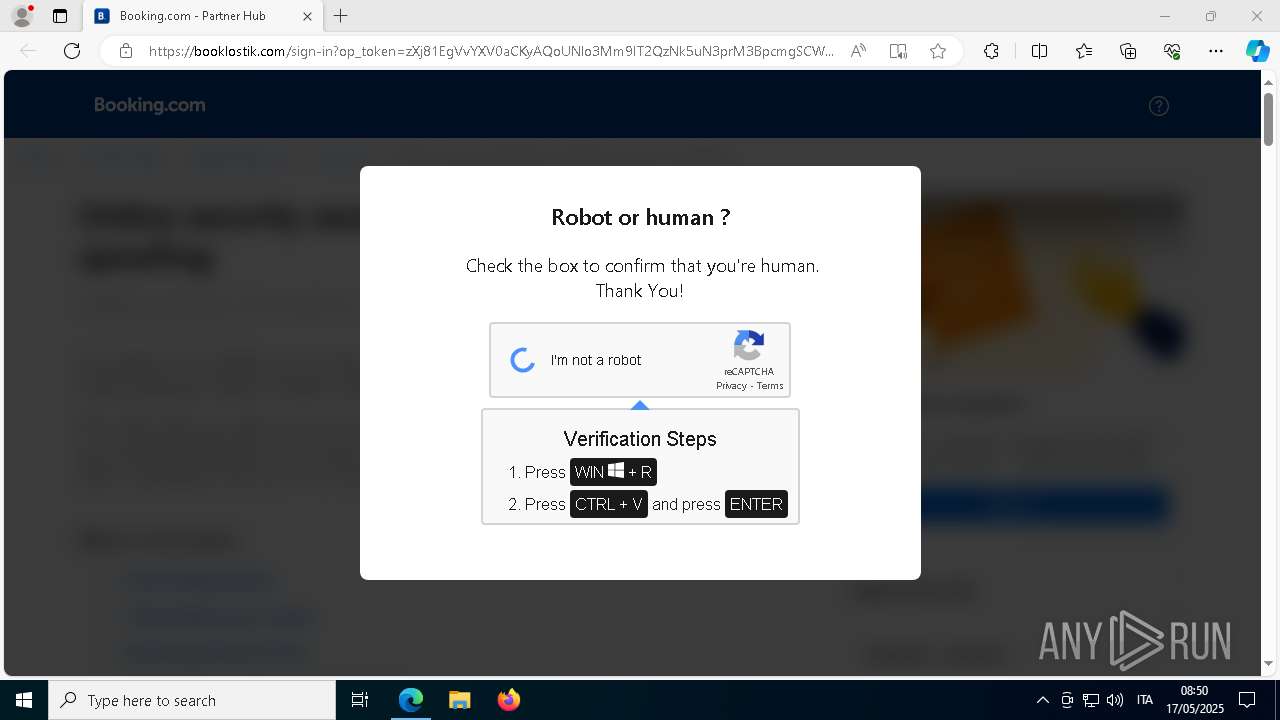
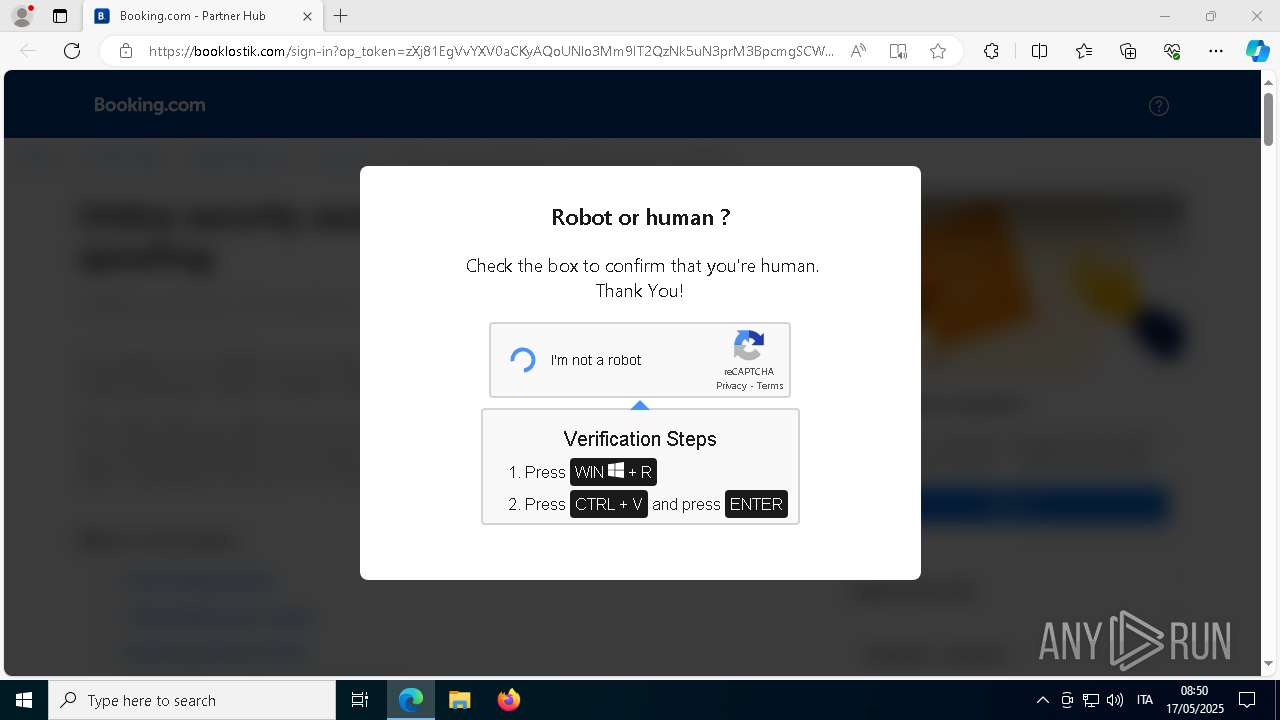
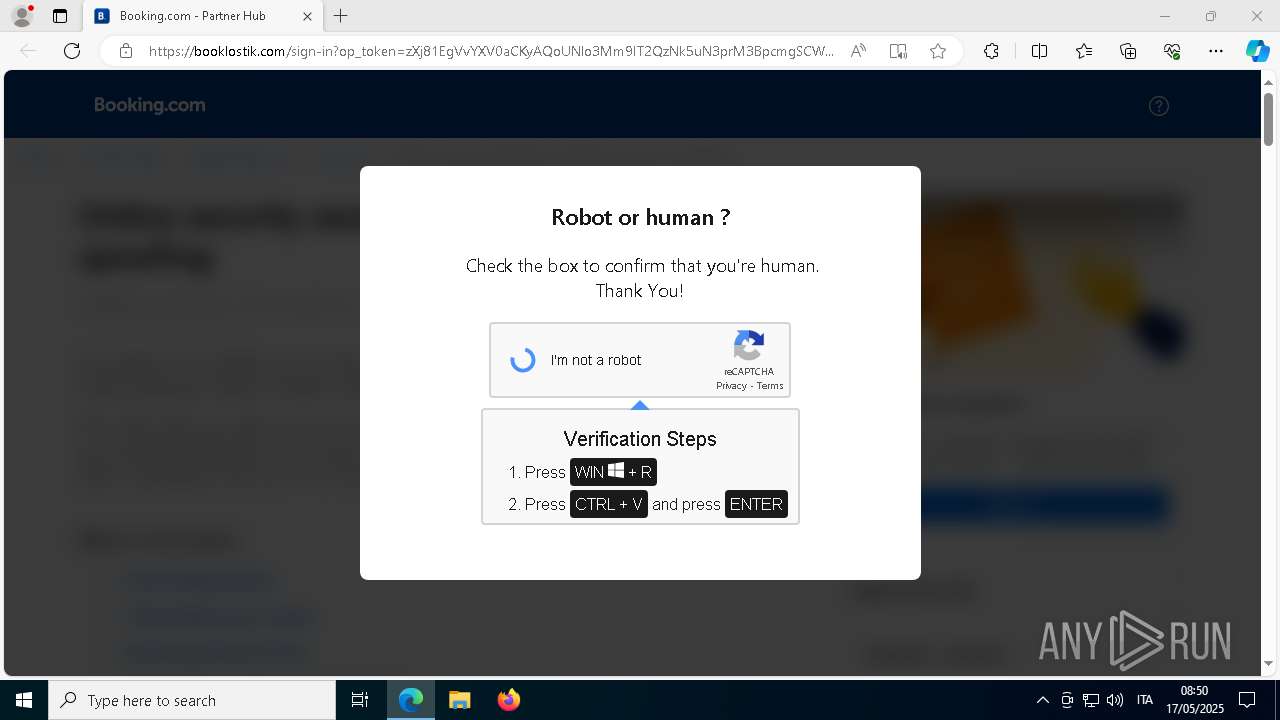
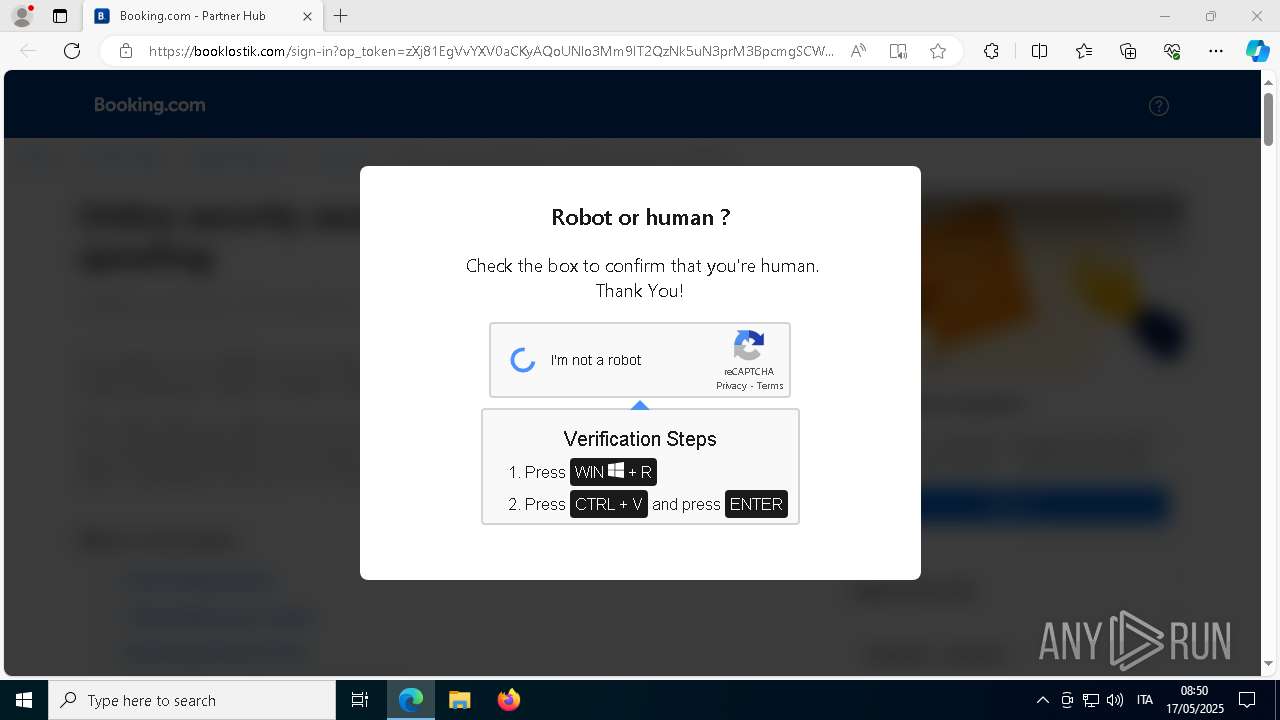
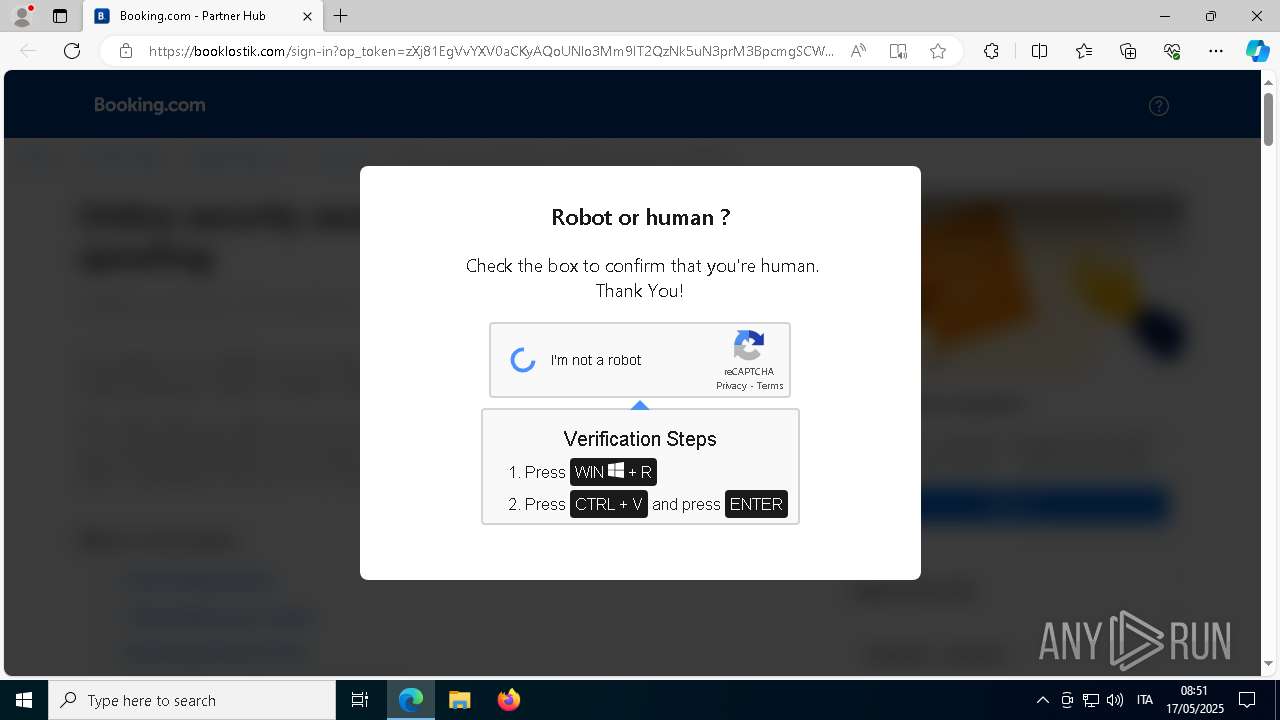
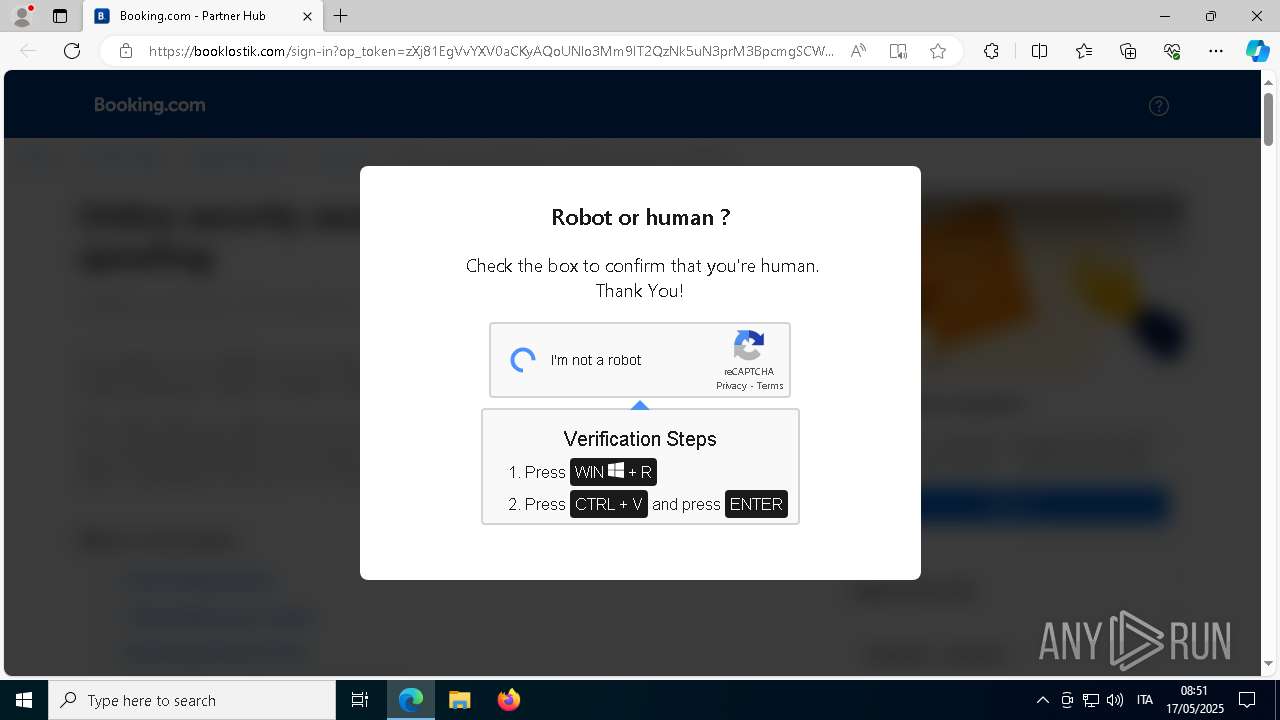
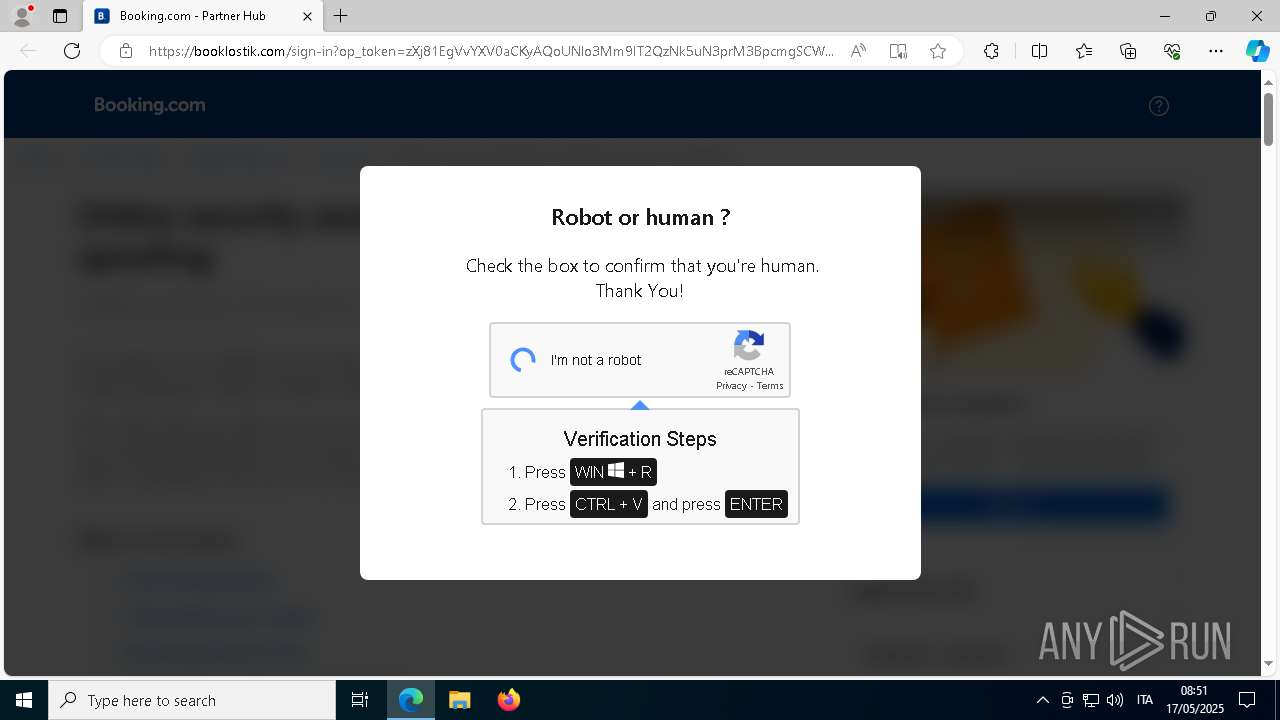
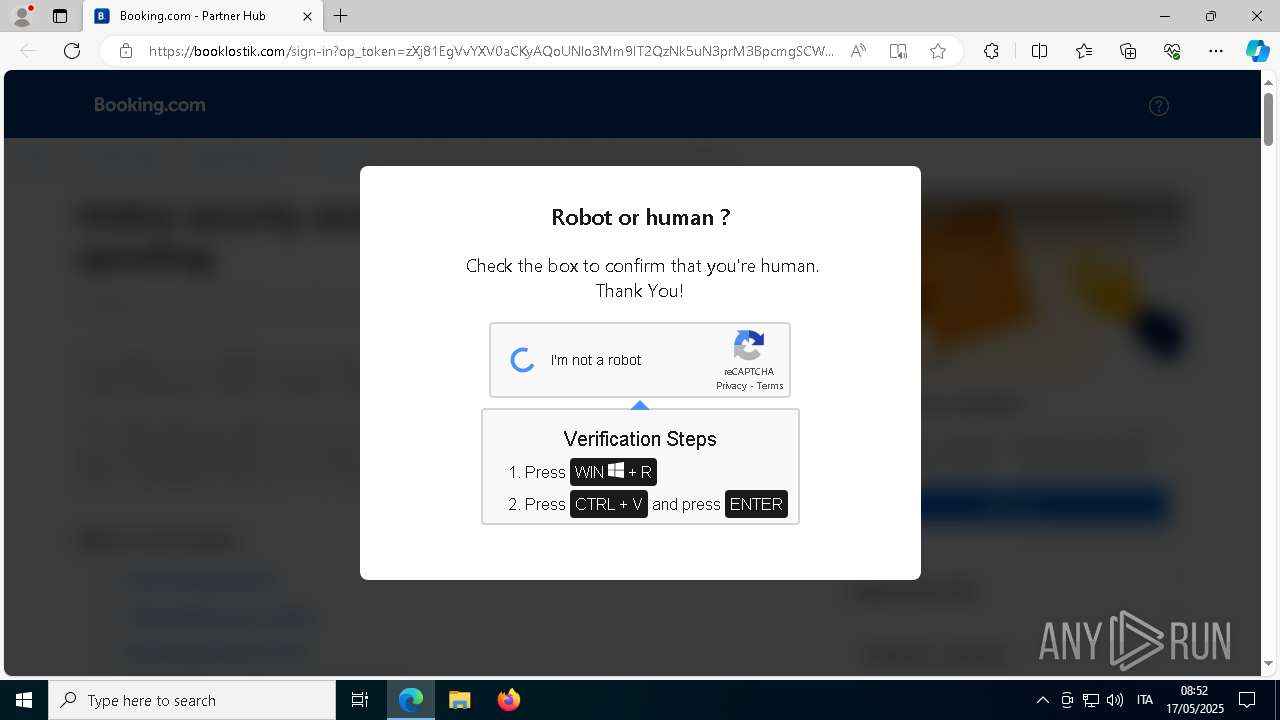
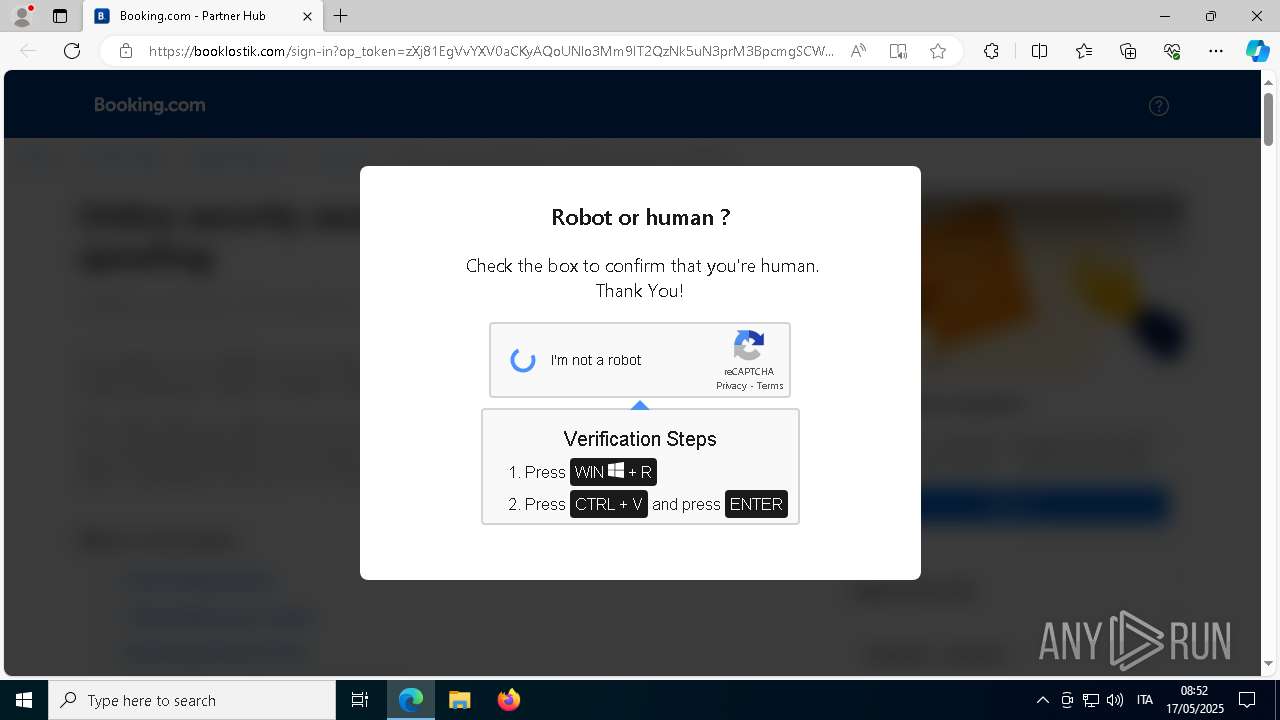
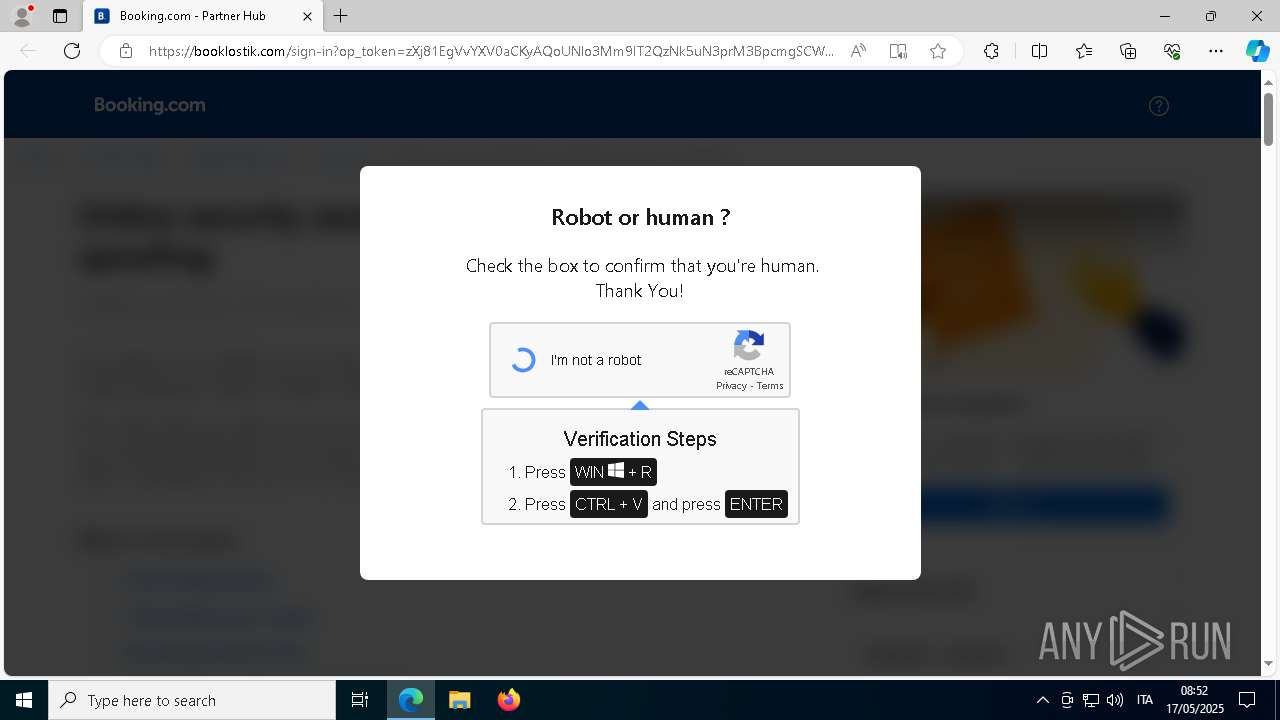
| URL: | https://booklostik.com |
| Full analysis: | https://app.any.run/tasks/beeeceb6-4c62-4145-adbd-9b1307458441 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 06:50:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | C0FBBA816F6B6E6481E7F1DF07848944 |
| SHA1: | 121D51F2E806E7727EC733EEB2A5E03CBF8205A2 |
| SHA256: | 2083F531CD5B1B8F60C89CE6DC00BE7FA6A22A3E5E03776CB0CEC019C92E0358 |
| SSDEEP: | 3:N8SELyI:2SyyI |
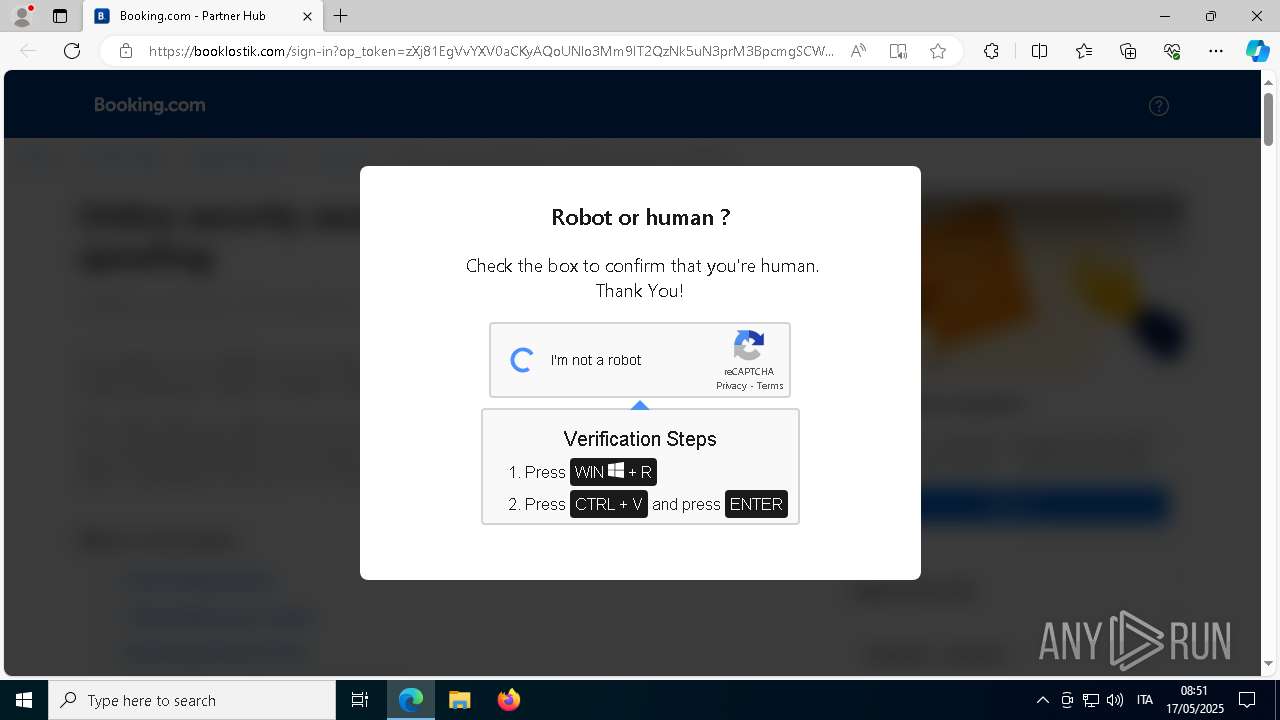
MALICIOUS
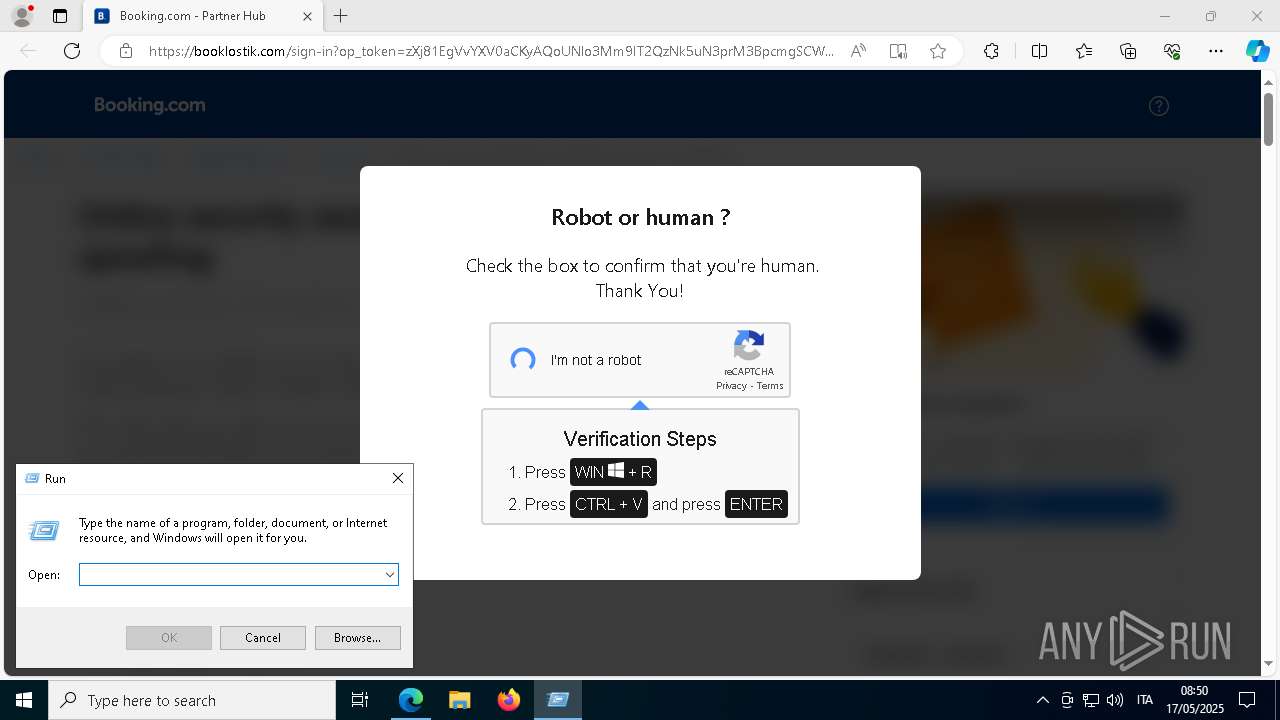
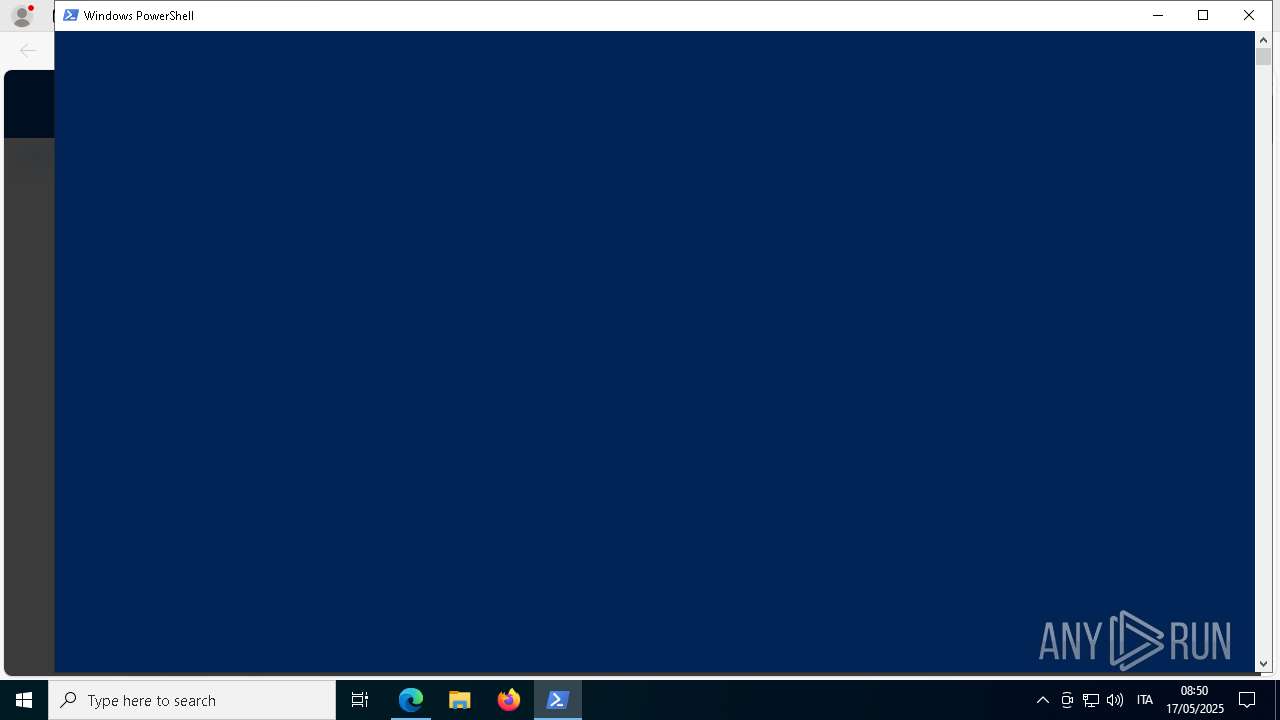
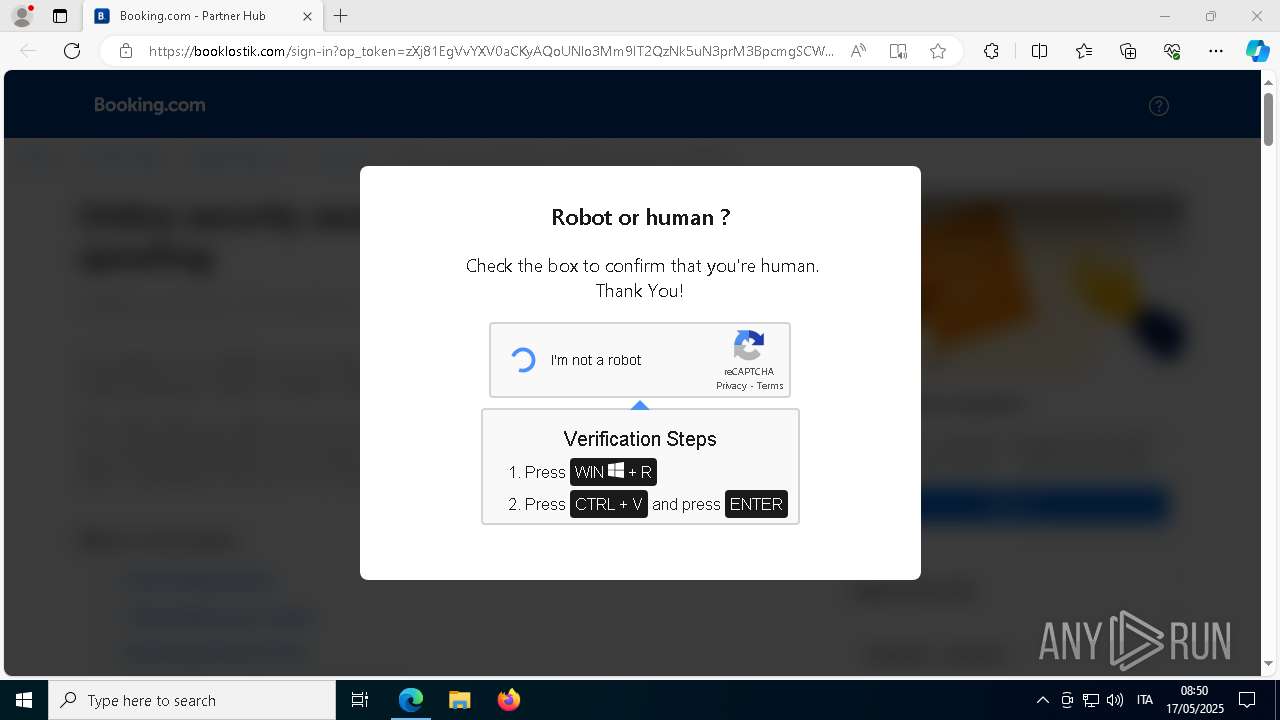
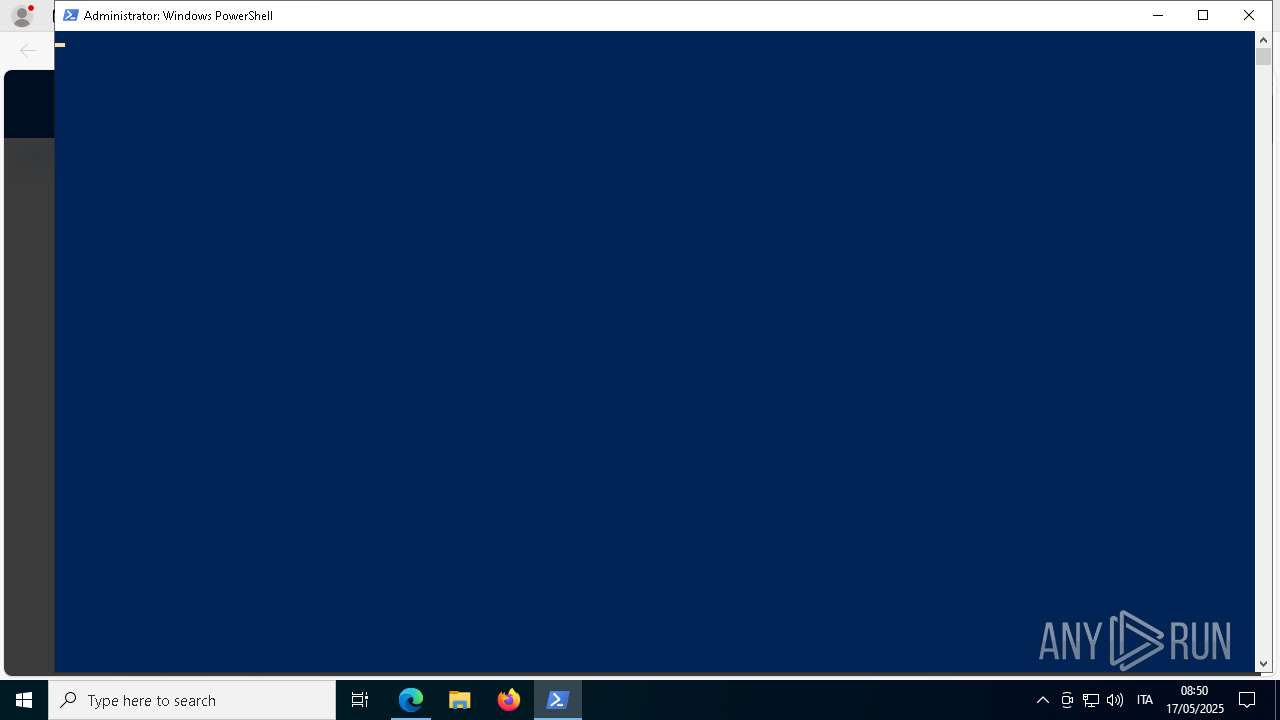
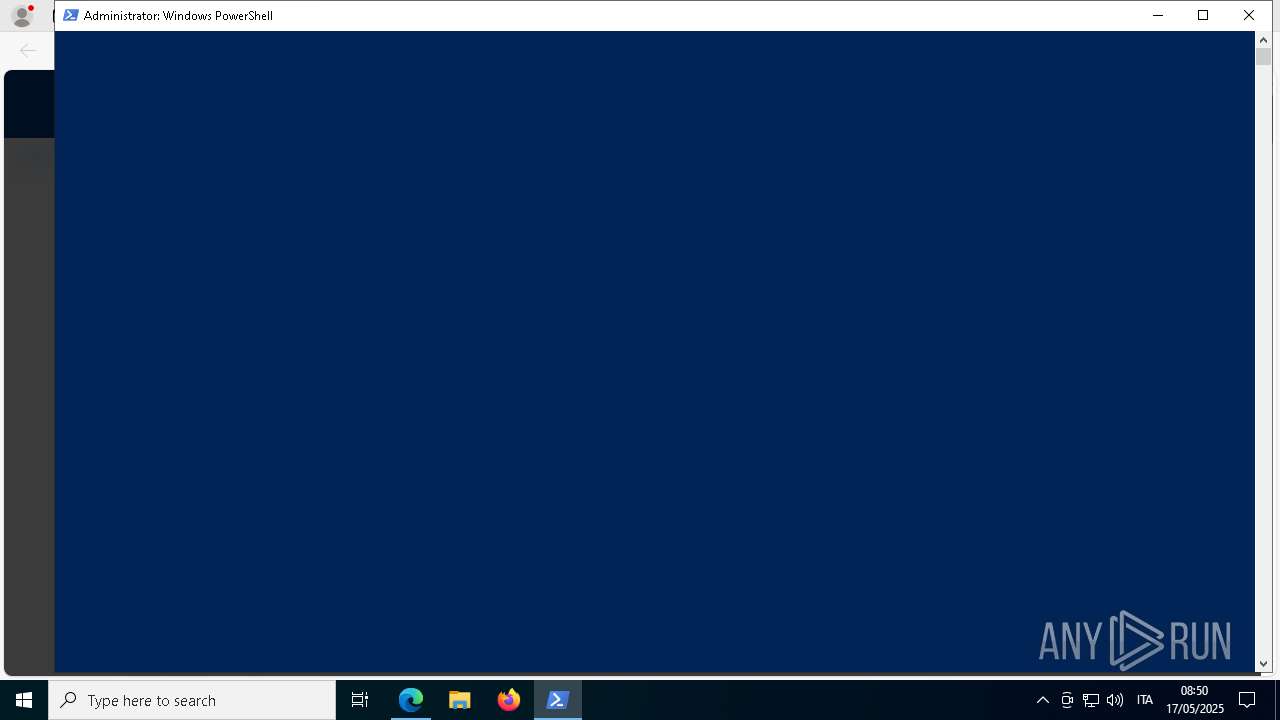
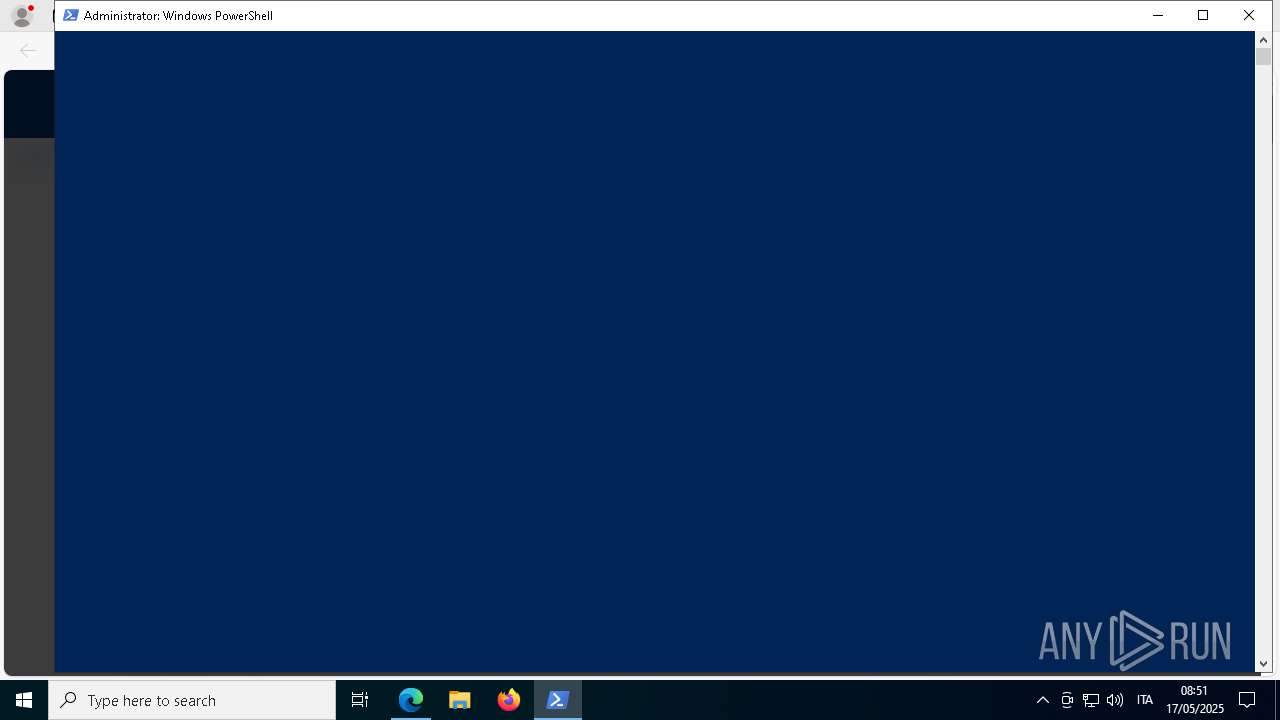
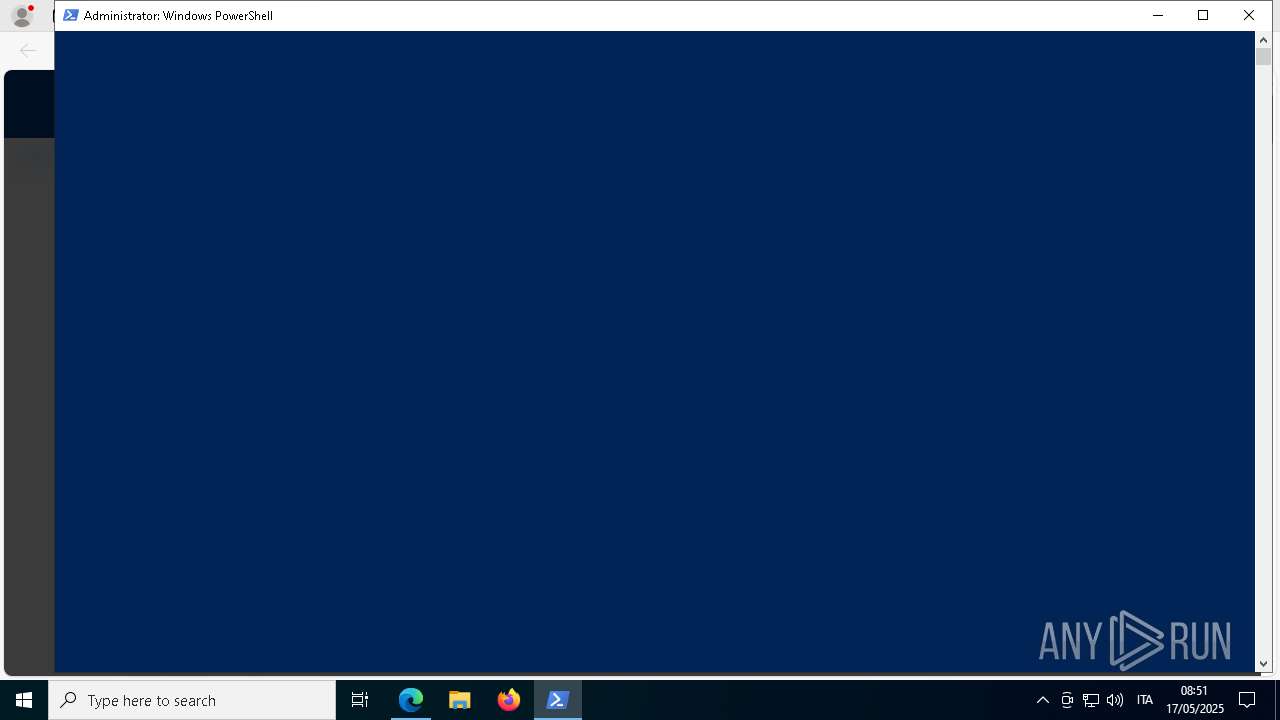
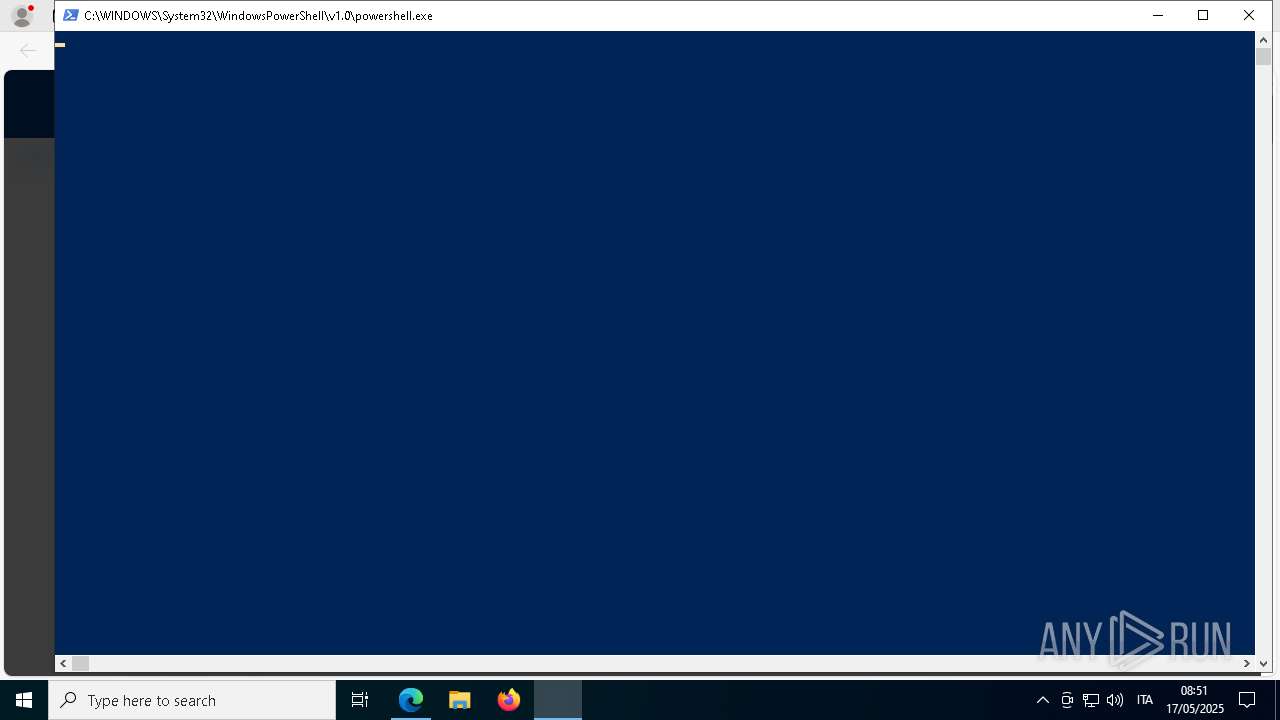
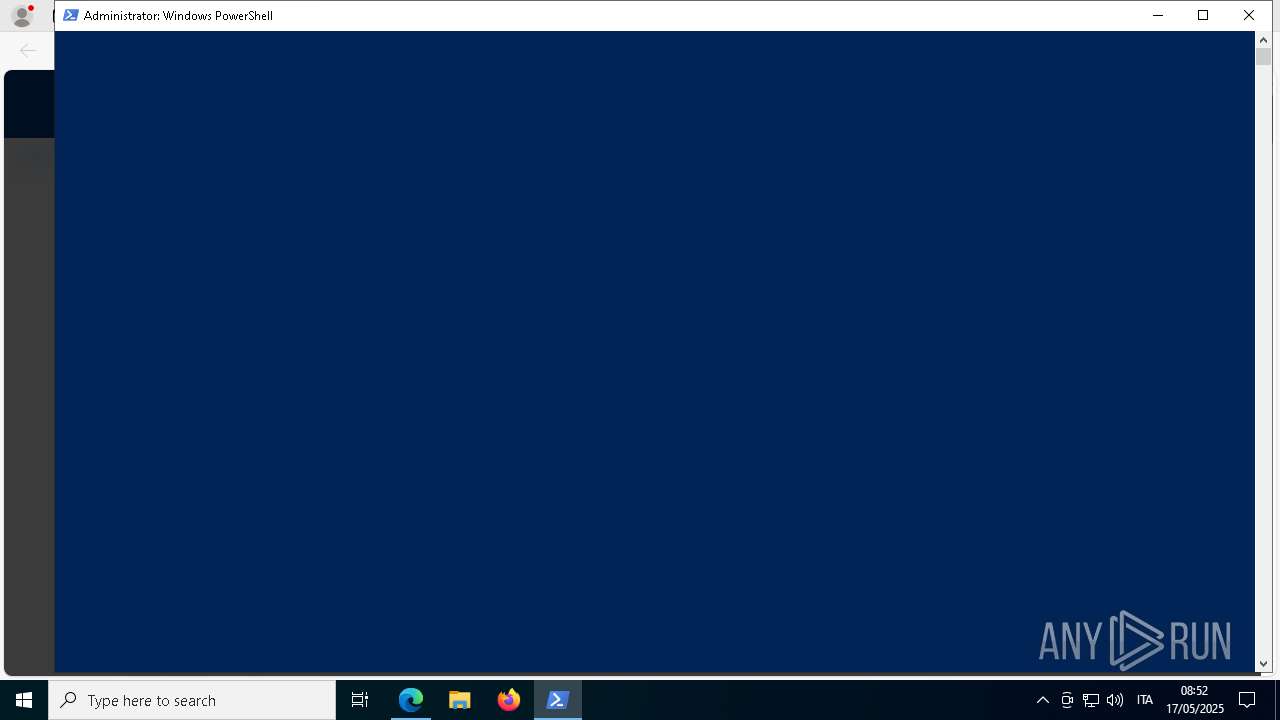
Bypass execution policy to execute commands
- powershell.exe (PID: 7496)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 8032)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4776)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 1328)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 968)
- powershell.exe (PID: 5756)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 3176)
- powershell.exe (PID: 6876)
- powershell.exe (PID: 736)
- powershell.exe (PID: 4056)
- powershell.exe (PID: 2568)
- powershell.exe (PID: 5408)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 7020)
- powershell.exe (PID: 8092)
- powershell.exe (PID: 2332)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 1004)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 3008)
- powershell.exe (PID: 7688)
- powershell.exe (PID: 6612)
- powershell.exe (PID: 300)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 2148)
- powershell.exe (PID: 6892)
- powershell.exe (PID: 2960)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7776)
- powershell.exe (PID: 5408)
- powershell.exe (PID: 8120)
- powershell.exe (PID: 5952)
- powershell.exe (PID: 5980)
- powershell.exe (PID: 6344)
- powershell.exe (PID: 5384)
- powershell.exe (PID: 2104)
- powershell.exe (PID: 5064)
- powershell.exe (PID: 1116)
- powershell.exe (PID: 7988)
Changes Windows Defender settings
- powershell.exe (PID: 7836)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 7836)
Adds path to the Windows Defender exclusion list
- powershell.exe (PID: 7836)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7836)
Application launched itself
- powershell.exe (PID: 7836)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 7836)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7836)
INFO
Manual execution by a user
- powershell.exe (PID: 7836)
Application launched itself
- msedge.exe (PID: 6972)
Checks proxy server information
- powershell.exe (PID: 7836)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 4776)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 7728)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 4776)
- powershell.exe (PID: 8052)
Reads Environment values
- identity_helper.exe (PID: 7616)
Checks supported languages
- identity_helper.exe (PID: 7616)
Disables trace logs
- powershell.exe (PID: 7836)
Reads the computer name
- identity_helper.exe (PID: 7616)
Executable content was dropped or overwritten
- msedge.exe (PID: 2772)
The sample compiled with english language support
- msedge.exe (PID: 2772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
309
Monitored processes
138
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1004 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
346 791
Read events
346 776
Write events
15
Delete events
0
Modification events
| (PID) Process: | (6972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9A88C298E5932F00 | |||
| (PID) Process: | (6972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262988 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E87C6477-5573-48CF-9861-614CB7FAE32F} | |||
| (PID) Process: | (6972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7BB5B998E5932F00 | |||
| (PID) Process: | (6972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262988 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CC7F7361-0E7B-48F5-ABA2-437AB2BD1B82} | |||
| (PID) Process: | (6972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262988 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A508EBE6-CDDF-426E-9E87-6A48925E39D9} | |||
| (PID) Process: | (6972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 81162499E5932F00 | |||
Executable files
10
Suspicious files
322
Text files
235
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10db6e.TMP | — | |
MD5:— | SHA256:— | |||
| 6972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10db7d.TMP | — | |
MD5:— | SHA256:— | |||
| 6972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10db7d.TMP | — | |
MD5:— | SHA256:— | |||
| 6972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10db7d.TMP | — | |
MD5:— | SHA256:— | |||
| 6972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10db9c.TMP | — | |
MD5:— | SHA256:— | |||
| 6972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
99
DNS requests
85
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5304 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1747939628&P2=404&P3=2&P4=MENPhXB1Ajxd2wVWOY7nAJWLudRp%2bNl5jFYqP7gTlCjM8C460ShSBjy0cAK%2fZ6JpbxUfJTLgsXU6zA31fywKYQ%3d%3d | unknown | — | — | whitelisted |
5304 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1747939628&P2=404&P3=2&P4=MENPhXB1Ajxd2wVWOY7nAJWLudRp%2bNl5jFYqP7gTlCjM8C460ShSBjy0cAK%2fZ6JpbxUfJTLgsXU6zA31fywKYQ%3d%3d | unknown | — | — | whitelisted |
5304 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1747939628&P2=404&P3=2&P4=MENPhXB1Ajxd2wVWOY7nAJWLudRp%2bNl5jFYqP7gTlCjM8C460ShSBjy0cAK%2fZ6JpbxUfJTLgsXU6zA31fywKYQ%3d%3d | unknown | — | — | whitelisted |
5304 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1747939628&P2=404&P3=2&P4=MENPhXB1Ajxd2wVWOY7nAJWLudRp%2bNl5jFYqP7gTlCjM8C460ShSBjy0cAK%2fZ6JpbxUfJTLgsXU6zA31fywKYQ%3d%3d | unknown | — | — | whitelisted |
5304 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1747705131&P2=404&P3=2&P4=fYmrk8AI0Ojgj6YC%2bKQjNT8Ysh0DEg%2bJuKXl6SsIpDgbbI1VWkTnHw3UaBJ%2b502daM826sIXdXDt9Cp%2fpTVl5A%3d%3d | unknown | — | — | whitelisted |
5304 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1747705131&P2=404&P3=2&P4=fYmrk8AI0Ojgj6YC%2bKQjNT8Ysh0DEg%2bJuKXl6SsIpDgbbI1VWkTnHw3UaBJ%2b502daM826sIXdXDt9Cp%2fpTVl5A%3d%3d | unknown | — | — | whitelisted |
5304 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1747939628&P2=404&P3=2&P4=MENPhXB1Ajxd2wVWOY7nAJWLudRp%2bNl5jFYqP7gTlCjM8C460ShSBjy0cAK%2fZ6JpbxUfJTLgsXU6zA31fywKYQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4220 | msedge.exe | 188.114.97.3:443 | booklostik.com | — | — | unknown |
4220 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
booklostik.com |
| unknown |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4220 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
4220 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
4220 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
4220 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
4220 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
4220 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7836 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7836 | powershell.exe | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |
7836 | powershell.exe | A Network Trojan was detected | LOADER [ANY.RUN] Gen.Powershell.Downloader Script Payload |
4220 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |