| File name: | Symulacja.exe |
| Full analysis: | https://app.any.run/tasks/89c45324-bb68-492c-b530-4dd1ac747fa0 |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2025, 19:58:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A1FE51BA742D1F5635F7F980A5466B4 |
| SHA1: | 868EE89C8FCCE466FC5BCDC310D52317E1FC958A |
| SHA256: | 207C7A6112398CC8FB41034560353C1285DAAA75C6355AE94B32AEB3A59815CE |
| SSDEEP: | 768:gjidrLkKgYoN9OzOOjrjeM41v1lbVMesmnMlcw5o:gjiHgYoN9OzOOjfSZ+ejM5o |
MALICIOUS
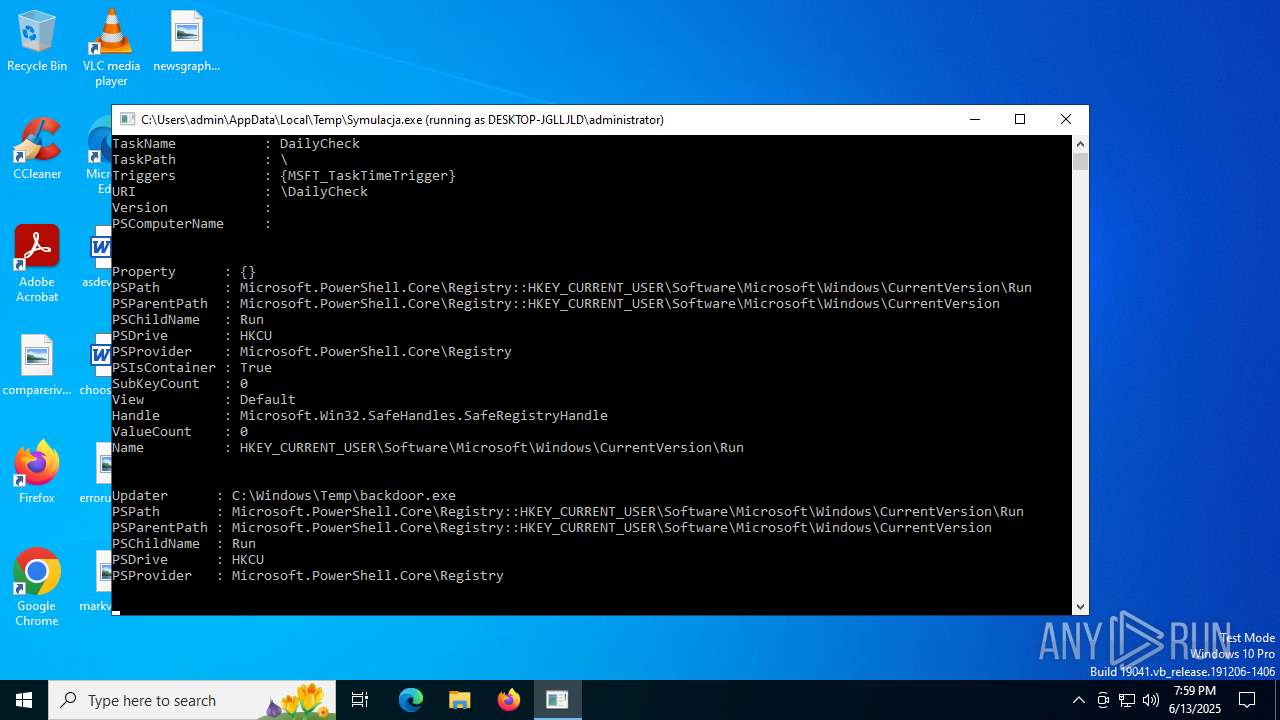
Changes the autorun value in the registry
- Symulacja.exe (PID: 5060)
SUSPICIOUS
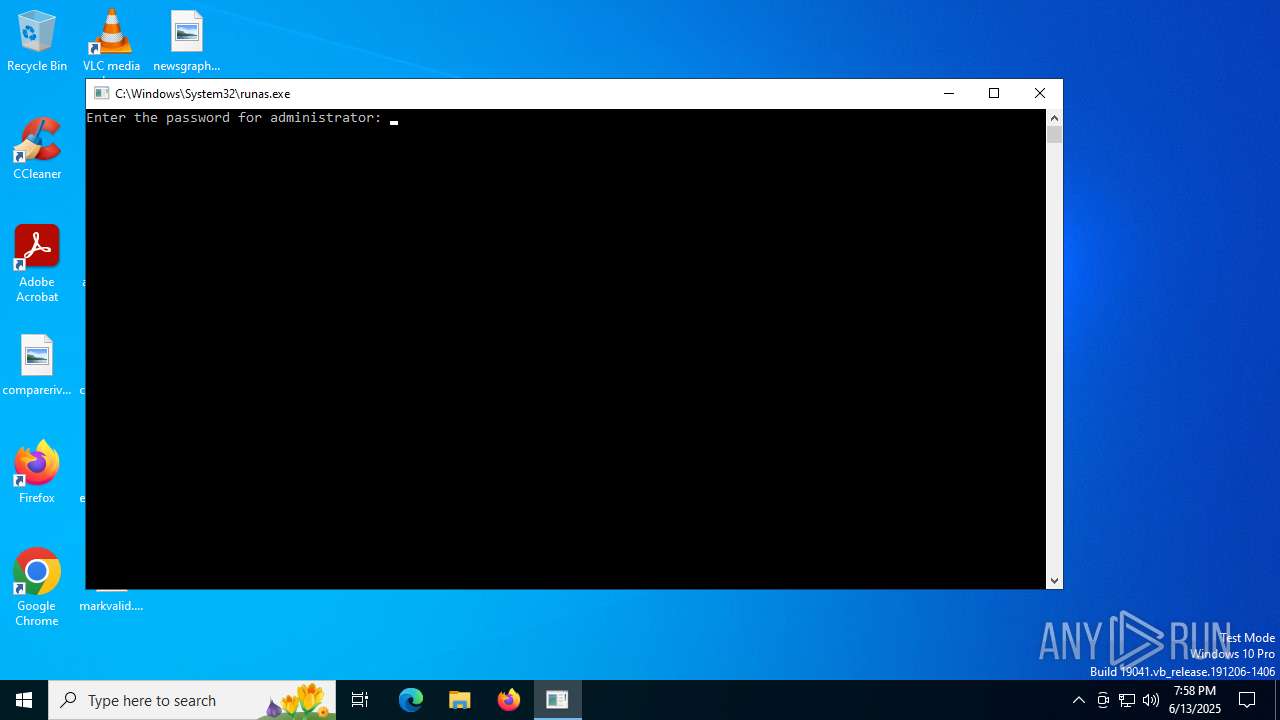
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 3756)
Reads security settings of Internet Explorer
- Symulacja.exe (PID: 5060)
Uses ATTRIB.EXE to modify file attributes
- Symulacja.exe (PID: 5060)
INFO
Checks supported languages
- Symulacja.exe (PID: 5060)
Reads the computer name
- Symulacja.exe (PID: 5060)
Reads the machine GUID from the registry
- Symulacja.exe (PID: 5060)
Reads Environment values
- Symulacja.exe (PID: 5060)
Checks if a key exists in the options dictionary (POWERSHELL)
- Symulacja.exe (PID: 5060)
Reads the software policy settings
- Symulacja.exe (PID: 5060)
- slui.exe (PID: 2976)
Launching a file from a Registry key
- Symulacja.exe (PID: 5060)
Disables trace logs
- Symulacja.exe (PID: 5060)
Checks proxy server information
- Symulacja.exe (PID: 5060)
- slui.exe (PID: 2976)
Creates files in the program directory
- Symulacja.exe (PID: 5060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:03 23:10:28+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 25088 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x814e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | Symulacja.exe |
| LegalCopyright: | |
| OriginalFileName: | Symulacja.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
142
Monitored processes
6
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2976 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
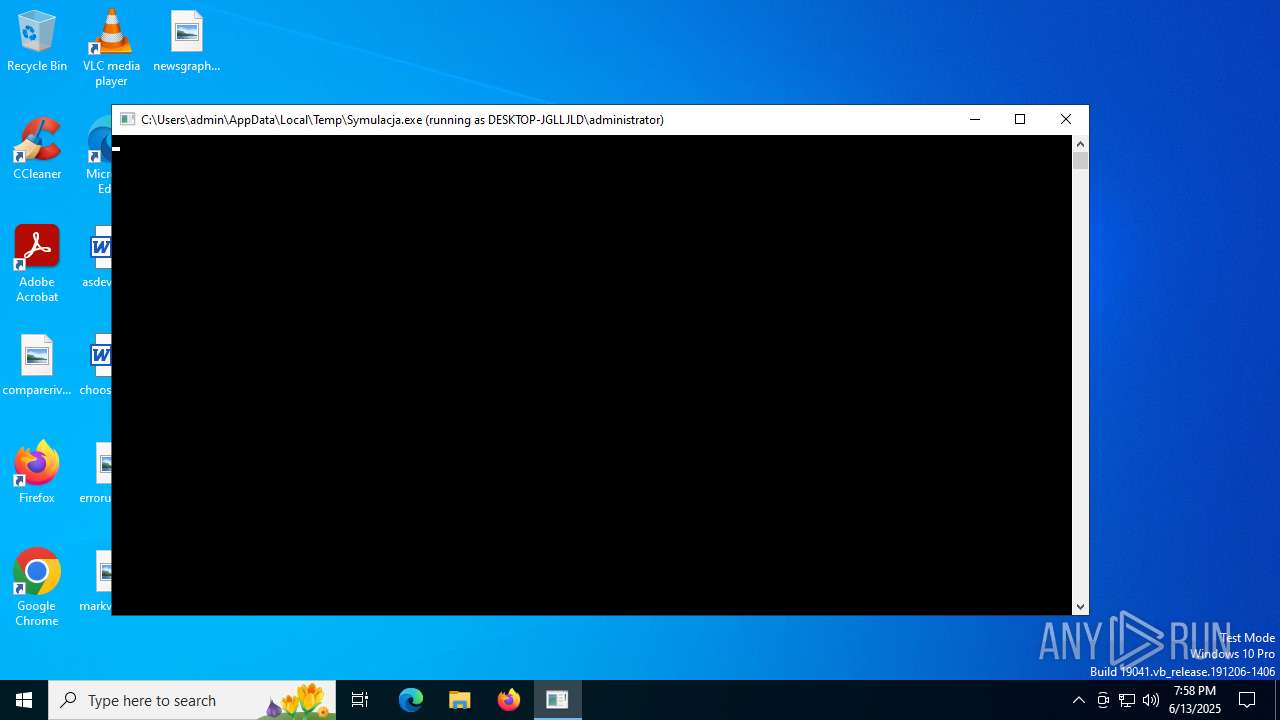
| 3756 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\AppData\Local\Temp\Symulacja.exe | C:\Windows\System32\runas.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3836 | "C:\WINDOWS\system32\attrib.exe" +h C:\ProgramData\HiddenLogs | C:\Windows\System32\attrib.exe | — | Symulacja.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4156 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Symulacja.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5060 | C:\Users\admin\AppData\Local\Temp\Symulacja.exe | C:\Users\admin\AppData\Local\Temp\Symulacja.exe | runas.exe | ||||||||||||
User: Administrator Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 6852 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runas.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 911
Read events
8 895
Write events
15
Delete events
1
Modification events
| (PID) Process: | (5060) Symulacja.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Updater |
Value: C:\Windows\Temp\backdoor.exe | |||
| (PID) Process: | (5060) Symulacja.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Symulacja_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5060) Symulacja.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Symulacja_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5060) Symulacja.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Symulacja_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5060) Symulacja.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Symulacja_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5060) Symulacja.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Symulacja_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5060) Symulacja.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Symulacja_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5060) Symulacja.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Symulacja_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5060) Symulacja.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5060) Symulacja.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Symulacja_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5060 | Symulacja.exe | C:\Users\Administrator\Downloads\backdoor.exe | text | |
MD5:A18152BA6FCABD3E0A9ACFB4DEEE68F6 | SHA256:60A7BF088A191BC6FA6F58B18043FACE1E0B189771DADB5A51BE1B806EDA86F9 | |||
| 5060 | Symulacja.exe | C:\Users\Administrator\AppData\Local\Temp\__PSScriptPolicyTest_zx323f3o.qas.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5060 | Symulacja.exe | C:\Users\Administrator\AppData\Local\Temp\__PSScriptPolicyTest_m5gxh22v.l4o.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5060 | Symulacja.exe | C:\Users\Administrator\AppData\Local\Temp\__PSScriptPolicyTest_ouev15tw.oam.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5060 | Symulacja.exe | C:\Users\Administrator\AppData\Local\Temp\__PSScriptPolicyTest_4ubrg0if.q5a.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5060 | Symulacja.exe | C:\ProgramData\HiddenLogs\keylogs.txt | text | |
MD5:5F4323A38ABC6A9BAAB57E02113D6F0B | SHA256:BFE55383B569E73C1C01BAA7480D2335A3B9EA48AFEAA5F219EC08FB3C6CA189 | |||
| 5060 | Symulacja.exe | C:\Users\Administrator\AppData\Local\Temp\webtest.html | html | |
MD5:84238DFC8092E5D9C0DAC8EF93371A07 | SHA256:EA8FAC7C65FB589B0D53560F5251F74F9E9B243478DCB6B3EA79B5E36449C8D9 | |||
| 5060 | Symulacja.exe | C:\Users\Administrator\Desktop\ransom_note.txt | text | |
MD5:CCD88C737E34C42B96E5470024D4DFB9 | SHA256:AD913647F9053469142058D2022F53B4E5E1054CF02AACA9240D50A9C987EF6C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
25
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5620 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5060 | Symulacja.exe | GET | 200 | 23.192.228.84:80 | http://example.com/ | unknown | — | — | whitelisted |
2632 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5620 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.19.105.127:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4868 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5060 | Symulacja.exe | 23.192.228.84:80 | example.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
example.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5060 | Symulacja.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |