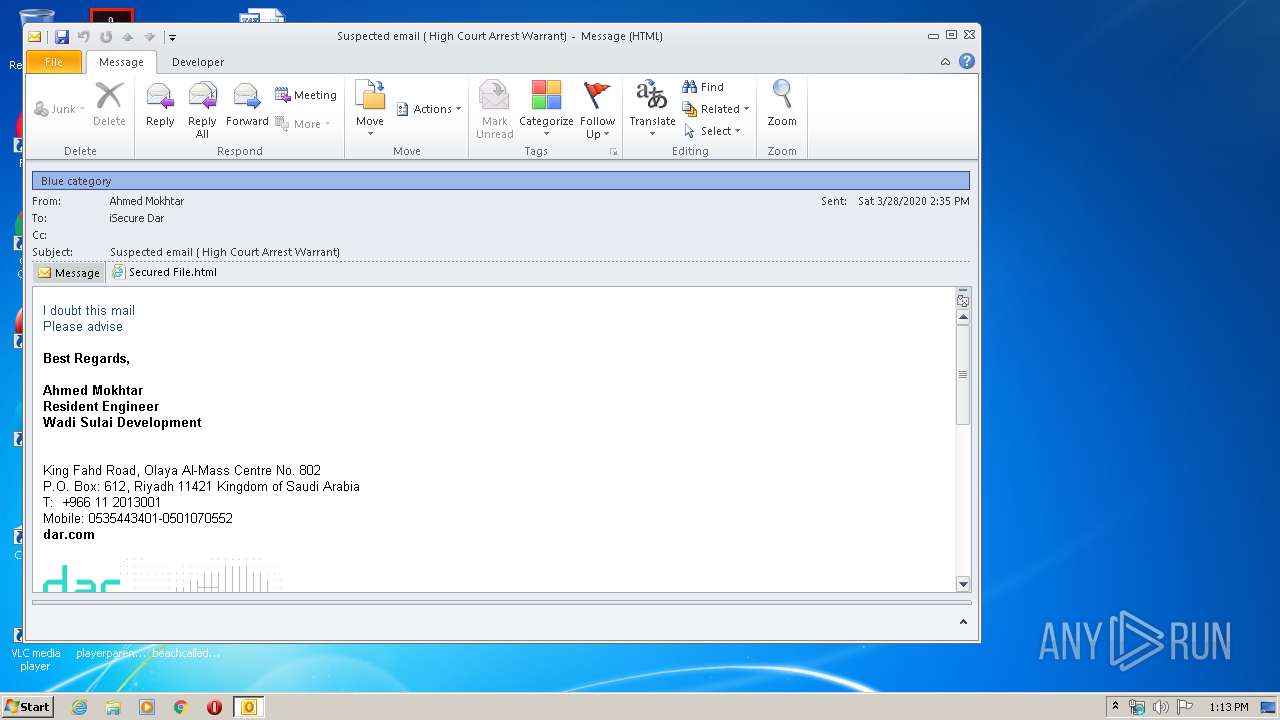
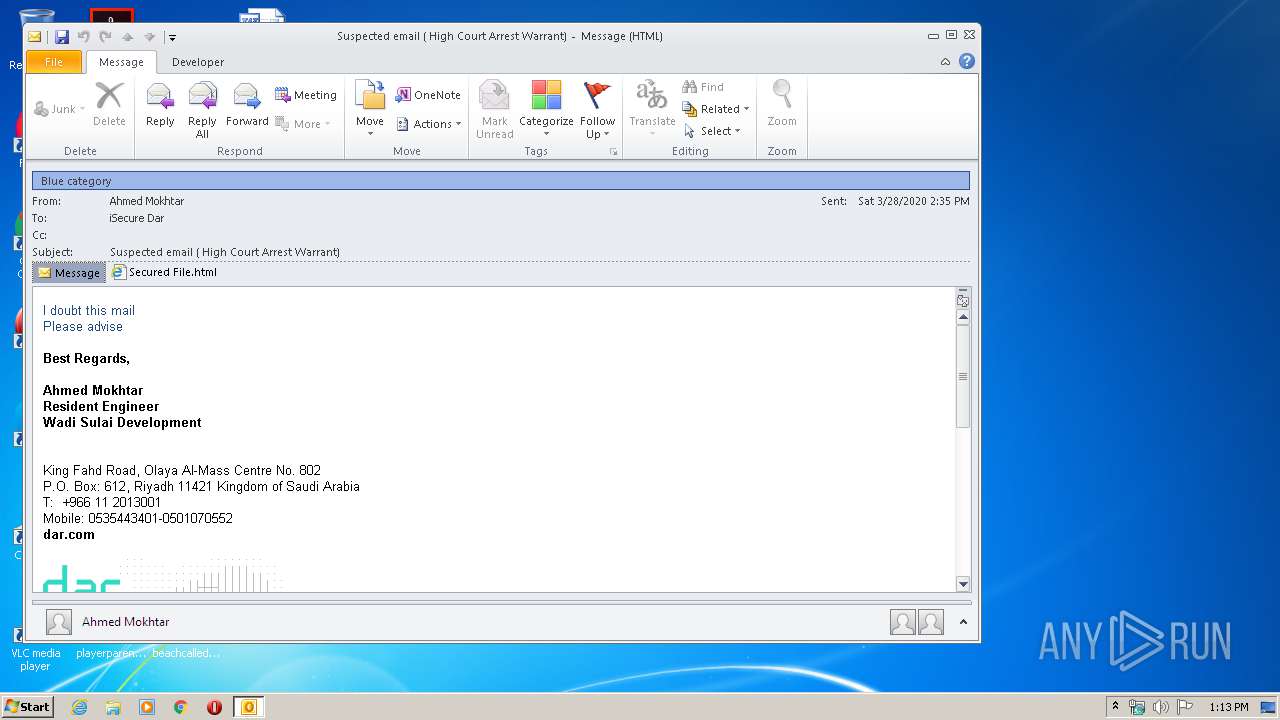
| File name: | Suspected email ( High Court Arrest Warrant).msg |
| Full analysis: | https://app.any.run/tasks/4615c555-021d-48af-8465-0f809238e0b8 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 12:13:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 31A337B836376E6B114AD4F41B58FE91 |
| SHA1: | B865EE2347C00969038C42318EBB48B7B3766CA3 |
| SHA256: | 206B5538A0F9809A7EA46D55AA5DDE2D7EDB6EFB6933286D8186B12379BADA81 |
| SSDEEP: | 49152:mjOLurLEkWVWjMaO/QYvzT9MmMd3sDgBs9v5flzRq:qxLEkWVW6QY1MmMpsGsZ5f |
MALICIOUS
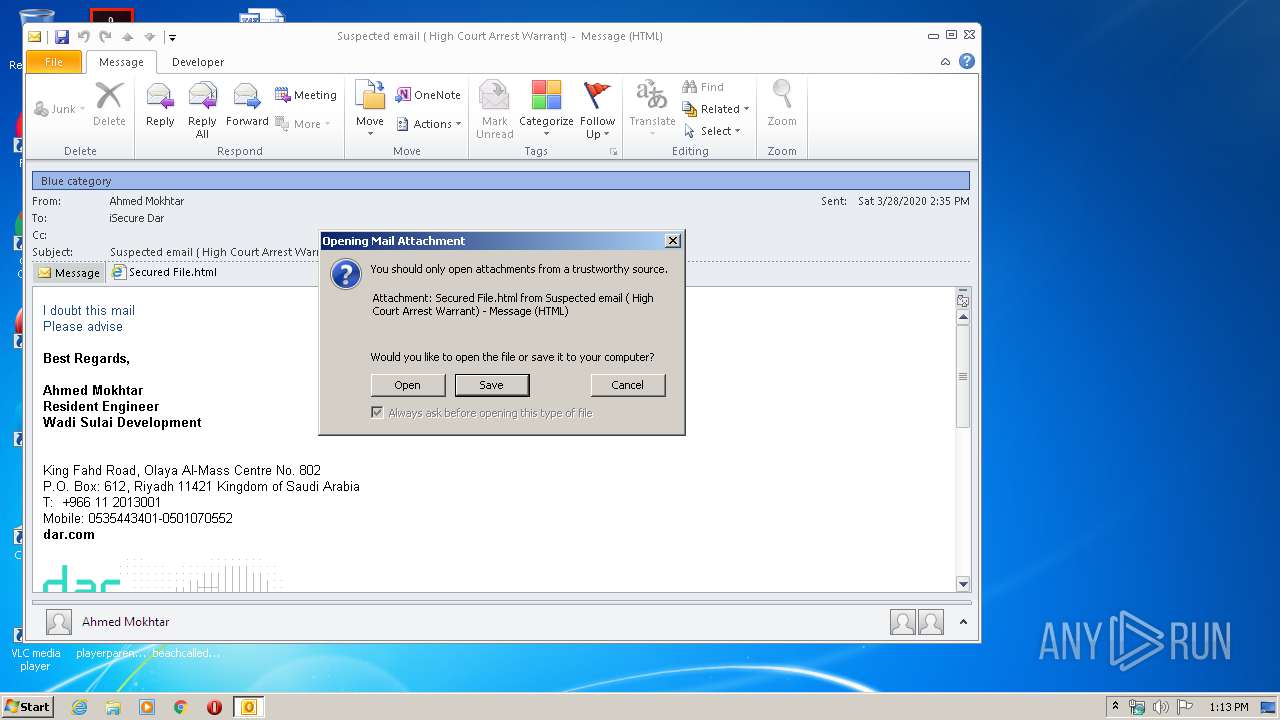
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3848)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3848)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3848)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3848)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3848)
- iexplore.exe (PID: 2656)
- iexplore.exe (PID: 2668)
Changes internet zones settings
- iexplore.exe (PID: 2668)
Application launched itself
- iexplore.exe (PID: 2668)
Reads internet explorer settings
- iexplore.exe (PID: 2656)
Reads settings of System Certificates
- iexplore.exe (PID: 2656)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2668)
Changes settings of System certificates
- iexplore.exe (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2656 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2668 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
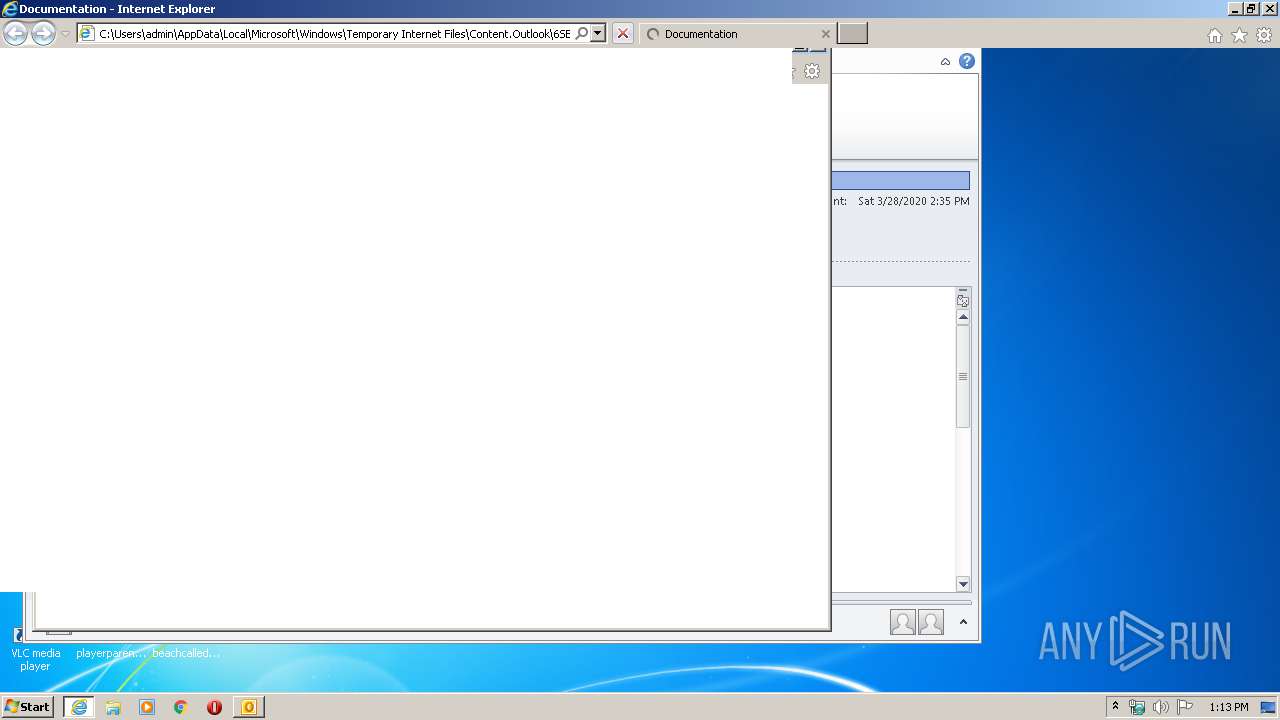
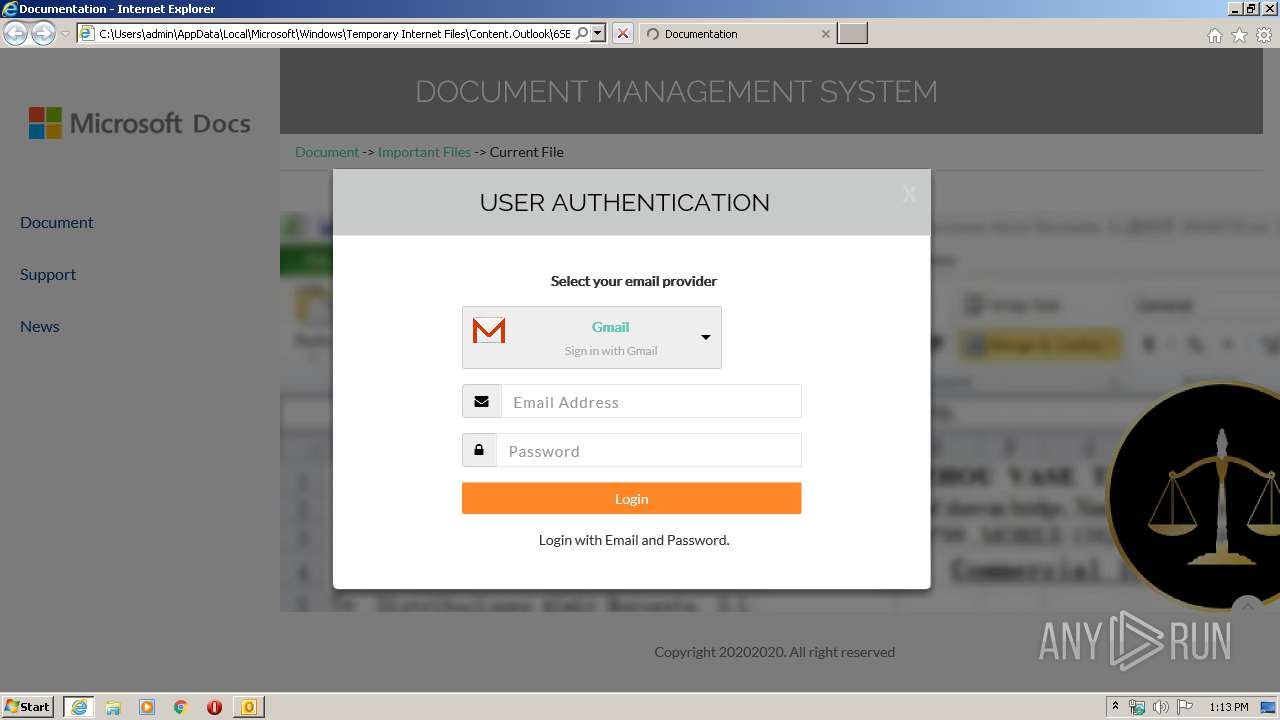
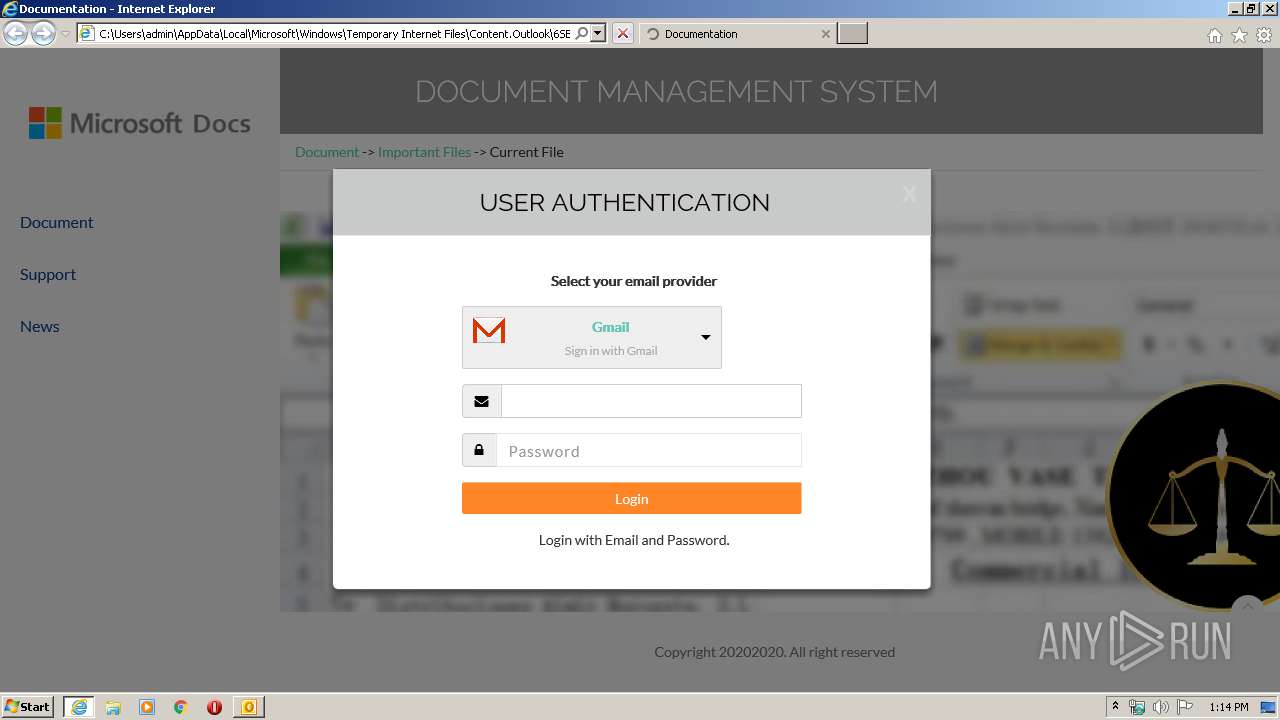
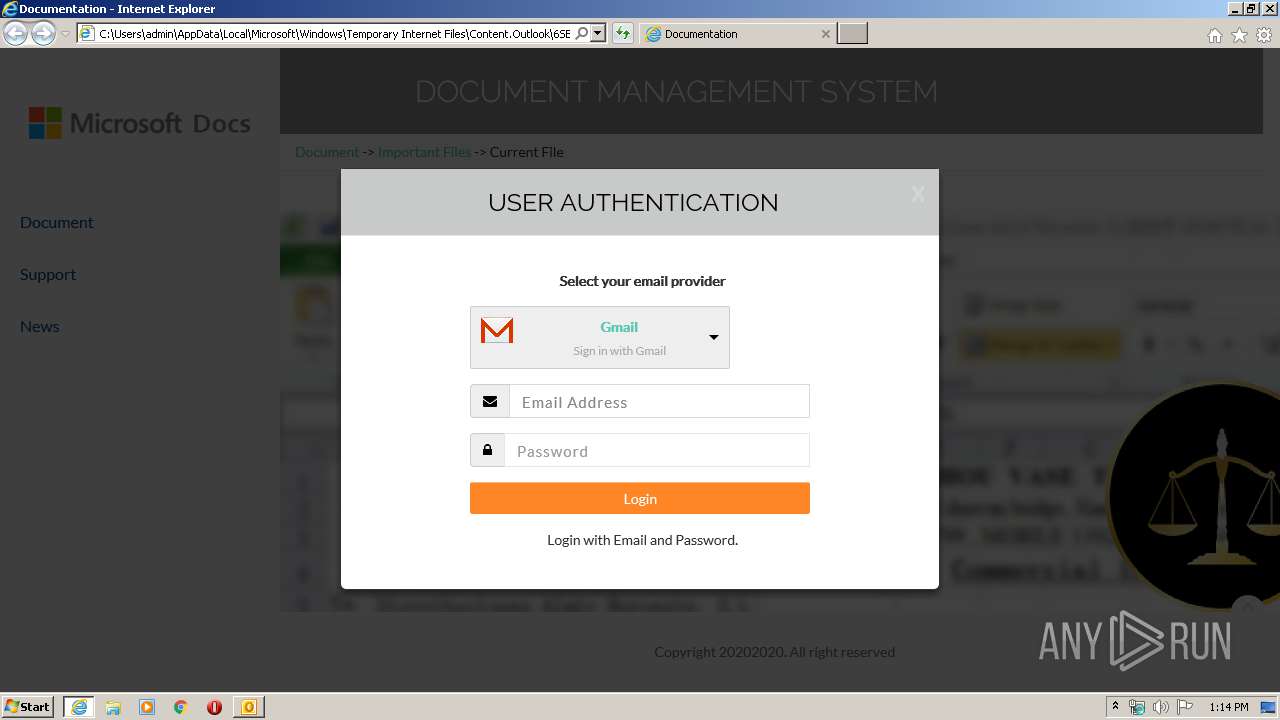
| 2668 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\6SEAFRQ4\Secured File.html | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3848 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Suspected email ( High Court Arrest Warrant).msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
2 410
Read events
1 524
Write events
782
Delete events
104
Modification events
| (PID) Process: | (3848) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3848) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3848) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3848) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3848) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3848) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3848) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3848) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3848) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3848) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
11
Text files
38
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3848 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR7269.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3848 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\6SEAFRQ4\Secured File (2).html\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3848 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3848 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\6SEAFRQ4\Secured File.html | text | |
MD5:— | SHA256:— | |||
| 3848 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\6SEAFRQ4\Secured File (2).html | text | |
MD5:— | SHA256:— | |||
| 2656 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabACD2.tmp | — | |
MD5:— | SHA256:— | |||
| 2656 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarACD3.tmp | — | |
MD5:— | SHA256:— | |||
| 2656 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9EC3B71635F8BA3FC68DE181A104A0EF_F6C39EF89D8A3A72327D8412589658B2 | der | |
MD5:— | SHA256:— | |||
| 2656 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
26
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3848 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2656 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://fonts.gstatic.com/s/raleway/v14/1Ptrg8zYS_SKggPNwIYqWqZPBg.woff | US | woff | 24.7 Kb | whitelisted |
2656 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://fonts.gstatic.com/s/lato/v16/S6u9w4BMUTPHh7USSwiPHw.woff | US | woff | 29.3 Kb | whitelisted |
2656 | iexplore.exe | GET | — | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEC4G%2Bv2mHN8jAgAAAABcZ3g%3D | US | — | — | whitelisted |
2656 | iexplore.exe | GET | 301 | 172.217.21.238:80 | http://google.com/? | US | html | 219 b | malicious |
2656 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://fonts.gstatic.com/s/raleway/v14/1Ptrg8zYS_SKggPNwN4rWqZPBg.woff | US | woff | 24.9 Kb | whitelisted |
2656 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | US | der | 471 b | whitelisted |
2656 | iexplore.exe | GET | 200 | 216.58.207.42:80 | http://fonts.googleapis.com/css?family=Raleway:100,300,400,500%7CLato:300,400 | US | text | 349 b | whitelisted |
2656 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2656 | iexplore.exe | GET | 200 | 172.217.23.163:80 | http://fonts.gstatic.com/s/raleway/v14/1Ptsg8zYS_SKggPNwE44TYFs.woff | US | woff | 23.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2656 | iexplore.exe | 104.17.65.4:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
2656 | iexplore.exe | 151.139.128.14:80 | ocsp.trust-provider.com | Highwinds Network Group, Inc. | US | suspicious |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 216.58.207.42:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.163:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2656 | iexplore.exe | 172.217.23.163:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2656 | iexplore.exe | 172.217.21.238:80 | google.com | Google Inc. | US | whitelisted |
2656 | iexplore.exe | 216.58.208.36:80 | www.google.com | Google Inc. | US | whitelisted |
2656 | iexplore.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ocsp.trust-provider.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
google.com |
| malicious |
www.google.com |
| malicious |