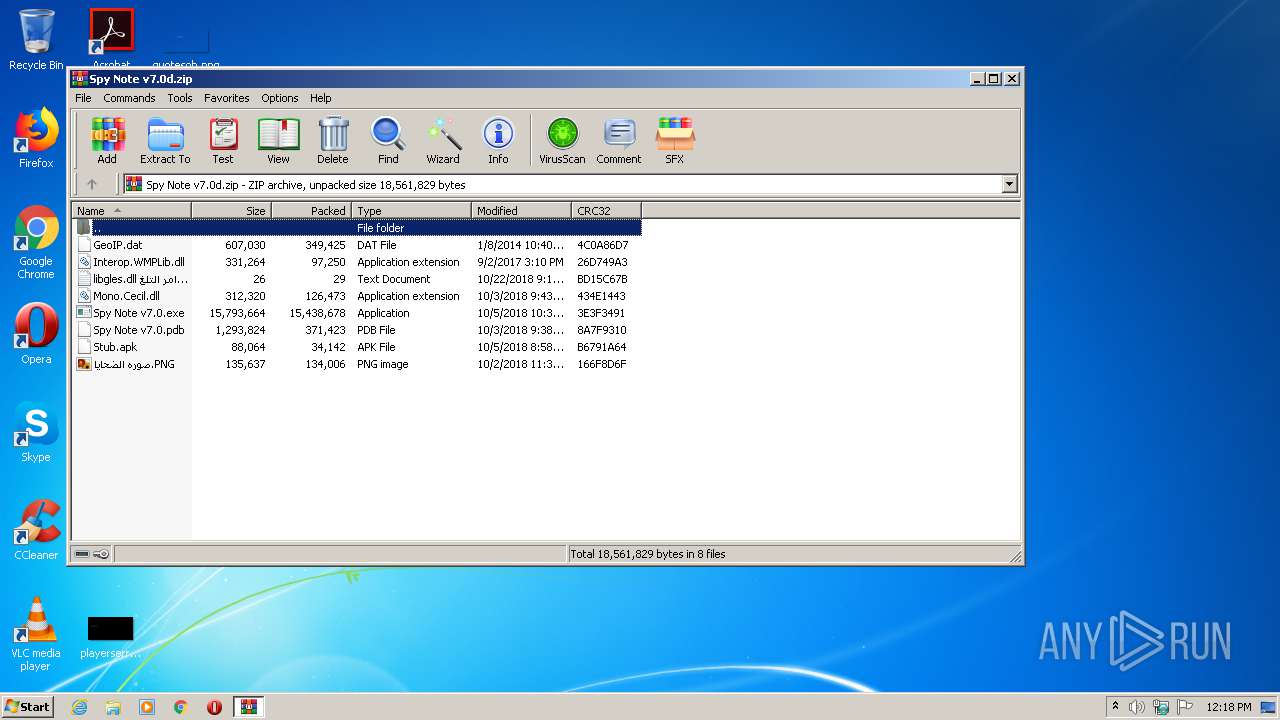
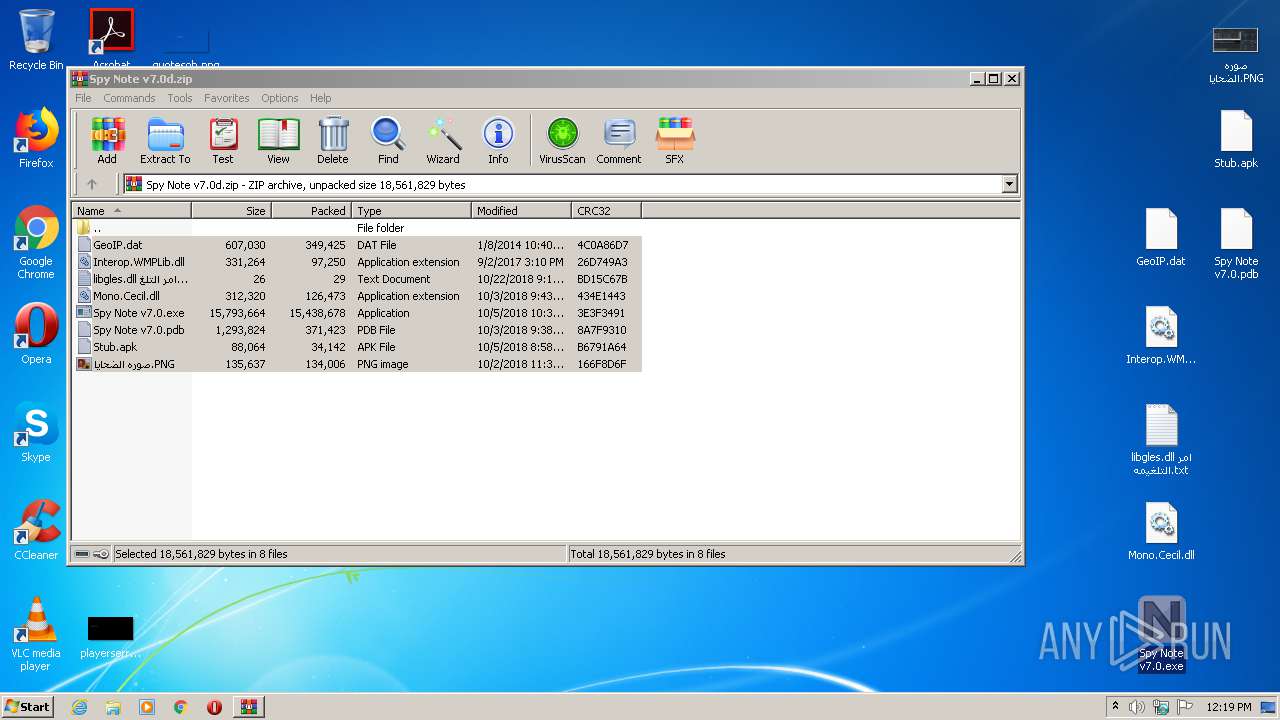
| File name: | Spy Note v7.0d.zip |
| Full analysis: | https://app.any.run/tasks/945ee4c0-0c4d-4bd0-a336-ff653fffab80 |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2020, 11:18:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 0507AAD7019DD0E356163F98778A01D9 |
| SHA1: | FD108BC802B6D35D5526CD22CB792C31A89EAC07 |
| SHA256: | 2067E16208CA66268FE9022910709DBC4714638DE1881B58DEC25F3033ADB5A7 |
| SSDEEP: | 393216:Ztej9D4PlBvBOTfT9RPrR09rKGjGOxe5s9SHDdzJuGmoLdu7:uj9sPjvBS7LEu07eK9SHuGW7 |
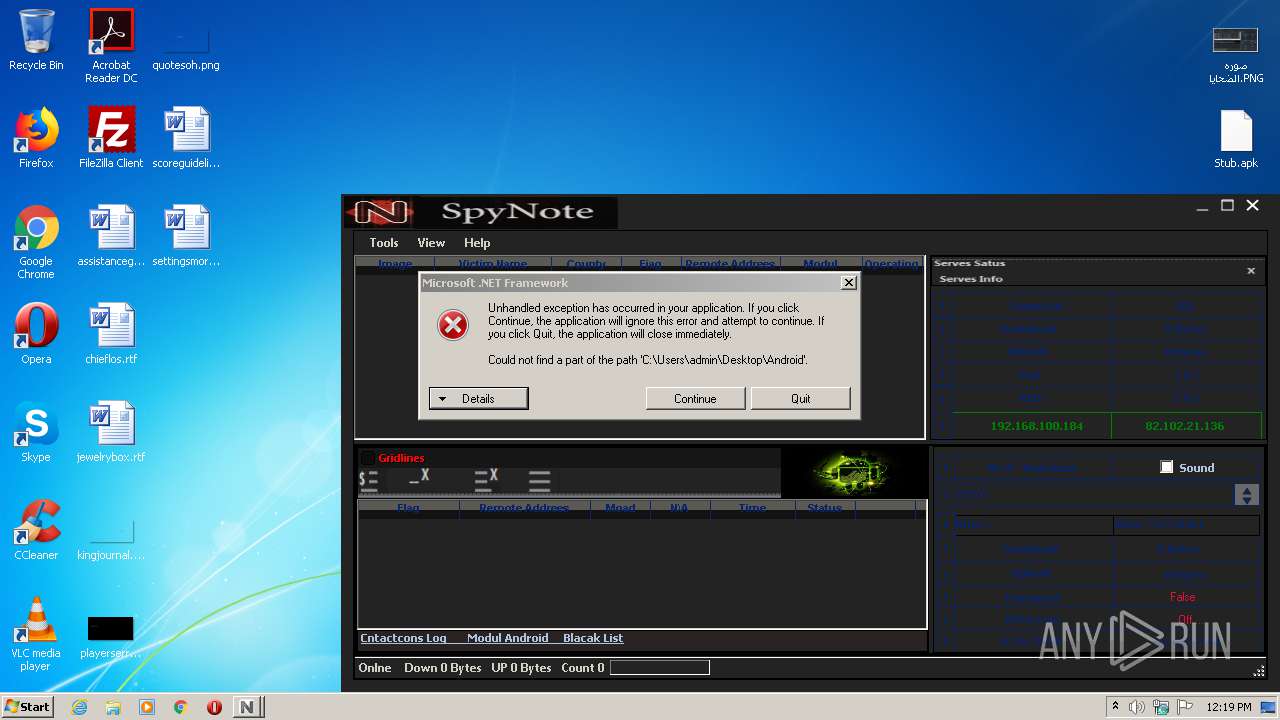
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3440)
Application was dropped or rewritten from another process
- Spy Note v7.0.exe (PID: 3804)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 552)
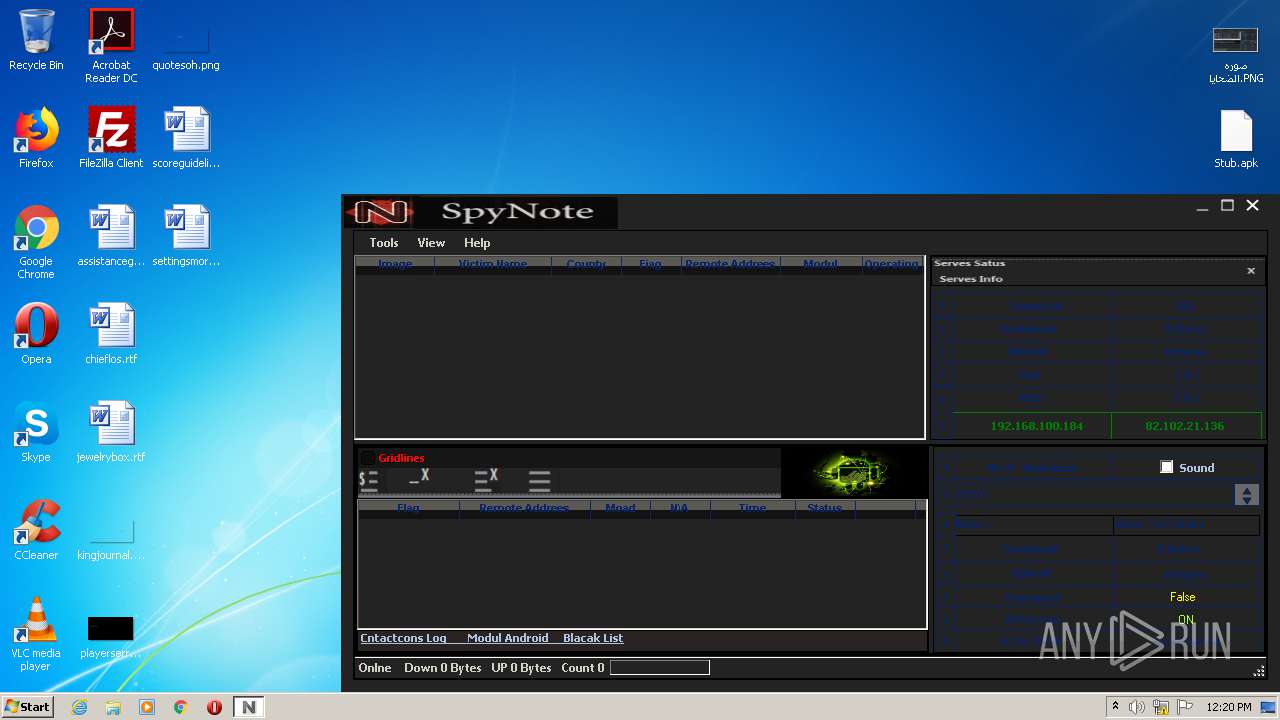
Checks for external IP
- Spy Note v7.0.exe (PID: 3804)
INFO
Manual execution by user
- Spy Note v7.0.exe (PID: 3804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2014:01:08 22:40:13 |
| ZipCRC: | 0x4c0a86d7 |
| ZipCompressedSize: | 349425 |
| ZipUncompressedSize: | 607030 |
| ZipFileName: | GeoIP.dat |
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Spy Note v7.0d.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3440 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3804 | "C:\Users\admin\Desktop\Spy Note v7.0.exe" | C:\Users\admin\Desktop\Spy Note v7.0.exe | explorer.exe | ||||||||||||
User: admin Company: Spy Note v7.0 Integrity Level: MEDIUM Description: Spy Note v7.0 Exit code: 0 Version: 1.3.6.0 Modules
| |||||||||||||||
Total events
477
Read events
441
Write events
36
Delete events
0
Modification events
| (PID) Process: | (552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Spy Note v7.0d.zip | |||
| (PID) Process: | (552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
2
Suspicious files
1
Text files
1
Unknown types
0
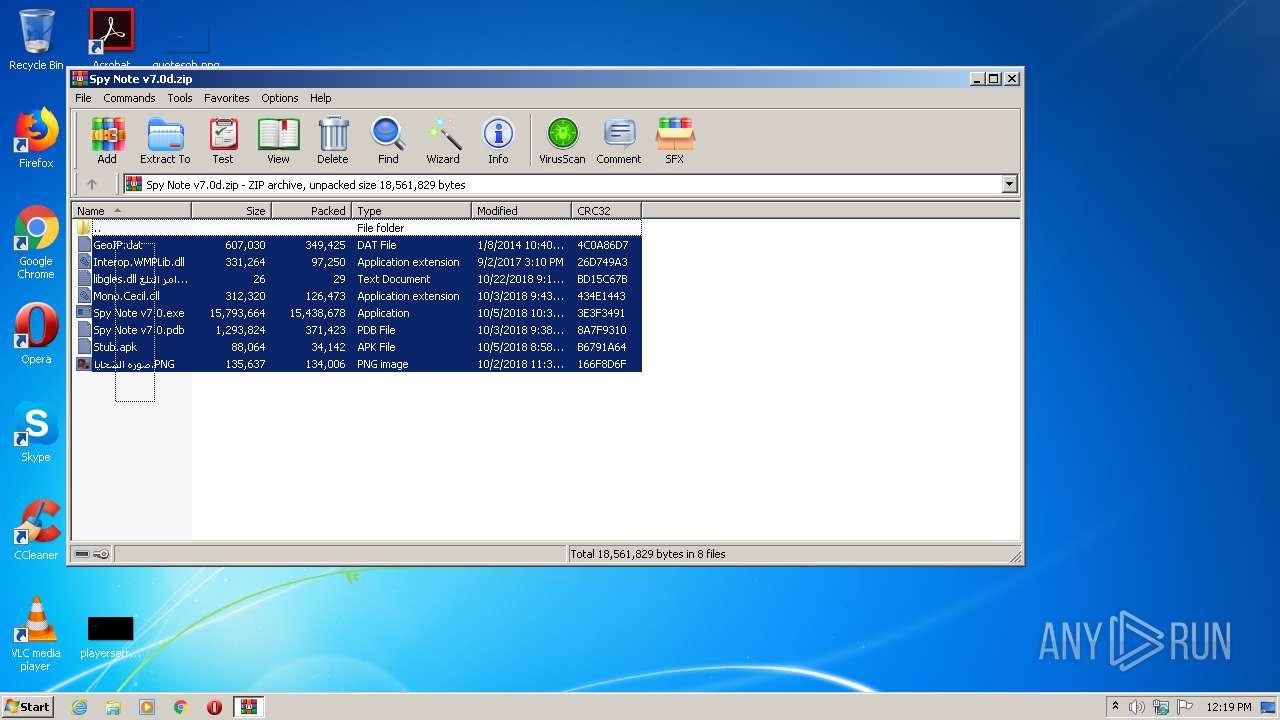
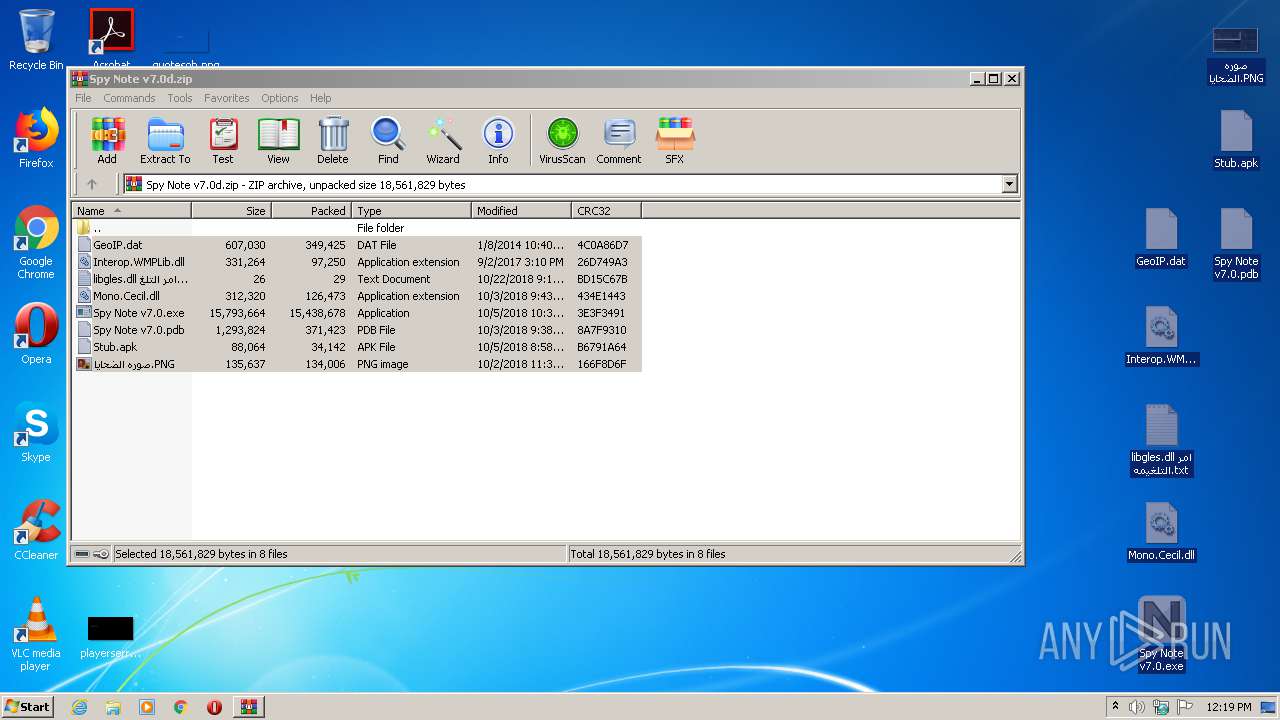
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa552.17102\Spy Note v7.0.exe | — | |
MD5:— | SHA256:— | |||
| 552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa552.17102\Spy Note v7.0.pdb | — | |
MD5:— | SHA256:— | |||
| 552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa552.17102\Stub.apk | — | |
MD5:— | SHA256:— | |||
| 552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa552.17102\صوره الضحايا.PNG | — | |
MD5:— | SHA256:— | |||
| 552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa552.17102\libgles.dll امر التلغيمه.txt | text | |
MD5:— | SHA256:— | |||
| 552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa552.17102\Interop.WMPLib.dll | executable | |
MD5:C43B99F3B6F45FE8E07365C4C9390873 | SHA256:E000C2F02C93F4B9F438CA9B5C6179F393FFDB8EF98F4B60B195E1D2035785D6 | |||
| 552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa552.17102\Mono.Cecil.dll | executable | |
MD5:851EC9D84343FBD089520D420348A902 | SHA256:CDADC26C09F869E21053EE1A0ACF3B2D11DF8EDD599FE9C377BD4D3CE1C9CDA9 | |||
| 552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa552.17102\GeoIP.dat | binary | |
MD5:1F897B5825CF91799831862620911AFF | SHA256:5F85518CF71E7B53544E0BD0C1874D1F89A0D6DE7A6AD50683517575AAA56301 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3804 | Spy Note v7.0.exe | GET | 200 | 216.58.212.132:80 | http://www.google.com/ | US | html | 45.7 Kb | malicious |
3804 | Spy Note v7.0.exe | GET | 200 | 131.186.113.70:80 | http://checkip.dyndns.org/ | US | html | 105 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3804 | Spy Note v7.0.exe | 216.58.212.132:80 | www.google.com | Google Inc. | US | whitelisted |
3804 | Spy Note v7.0.exe | 131.186.113.70:80 | checkip.dyndns.org | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
checkip.dyndns.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
1048 | svchost.exe | Misc activity | AV INFO Query to checkip.dyndns. Domain |
3804 | Spy Note v7.0.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
3804 | Spy Note v7.0.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] External IP Check checkip.dyndns.org |
3804 | Spy Note v7.0.exe | Potentially Bad Traffic | ET POLICY DynDNS CheckIp External IP Address Server Response |
1 ETPRO signatures available at the full report