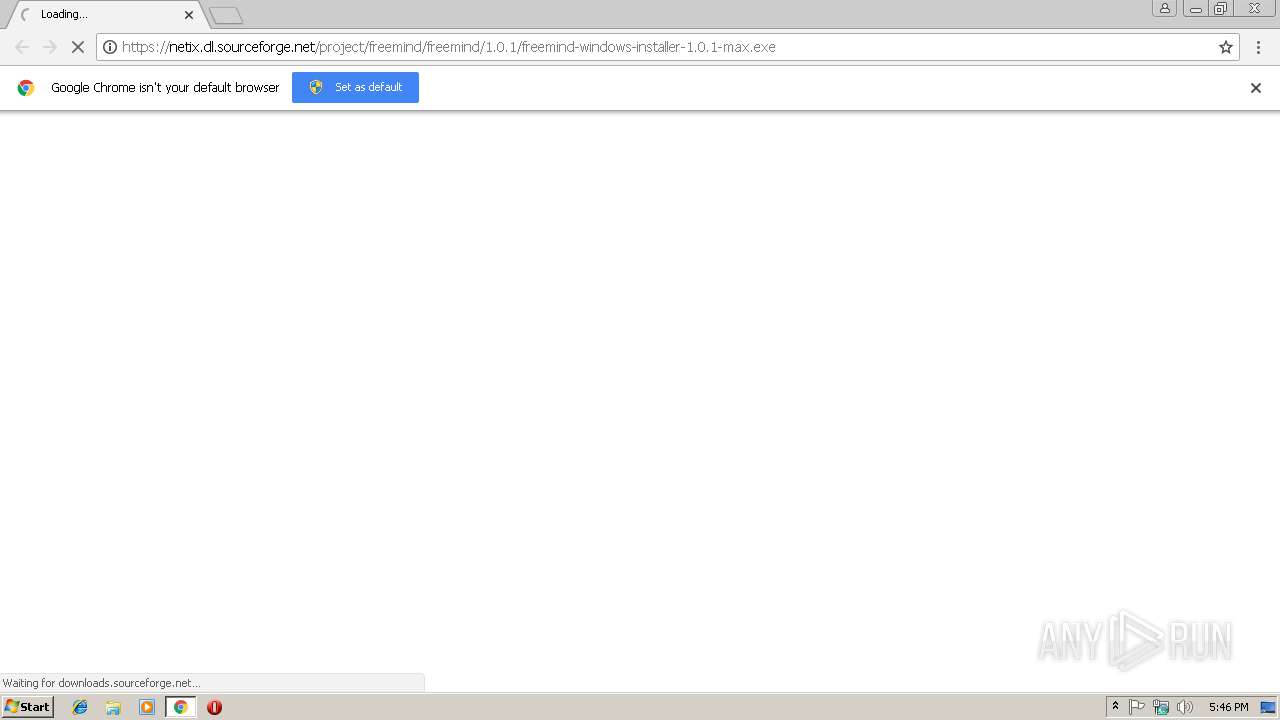
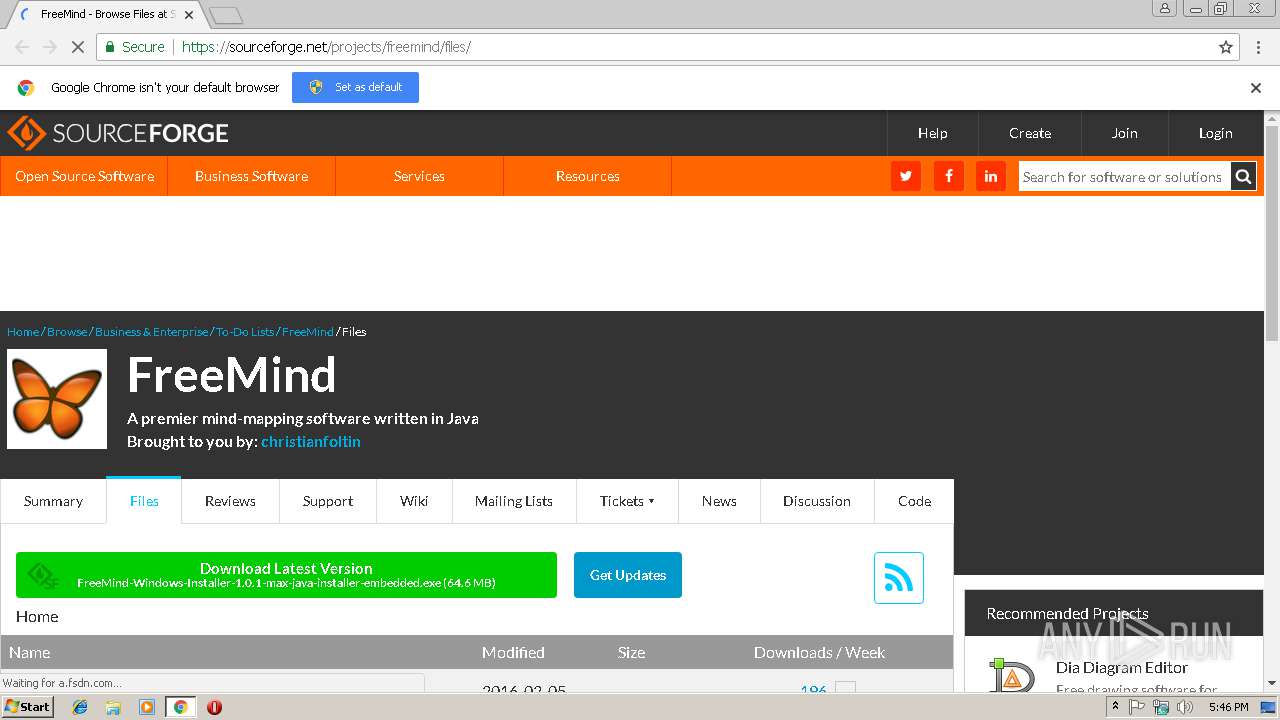
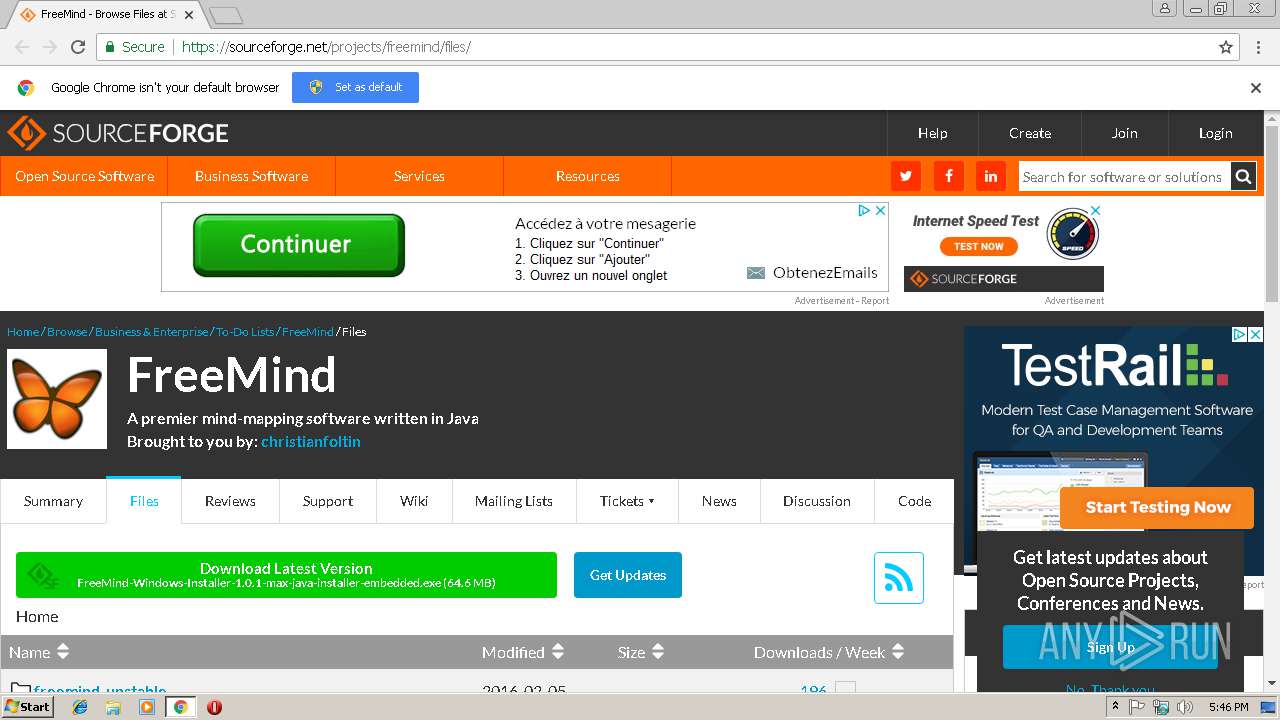
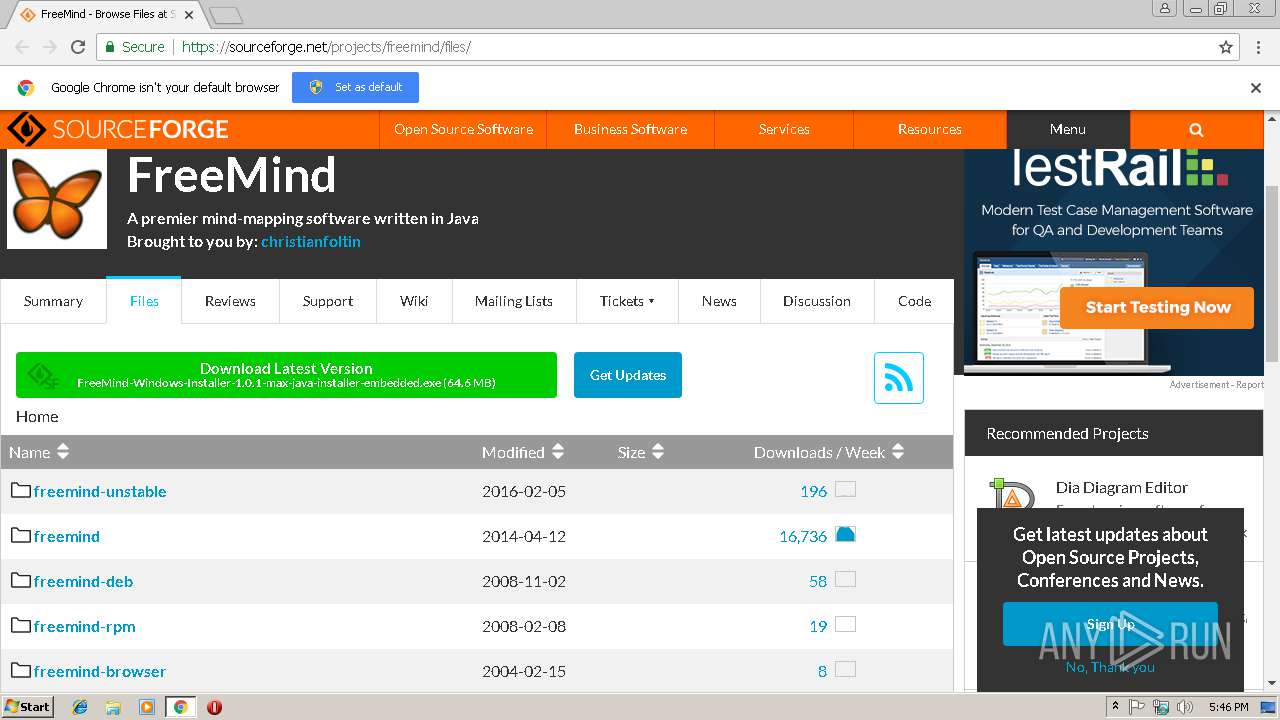
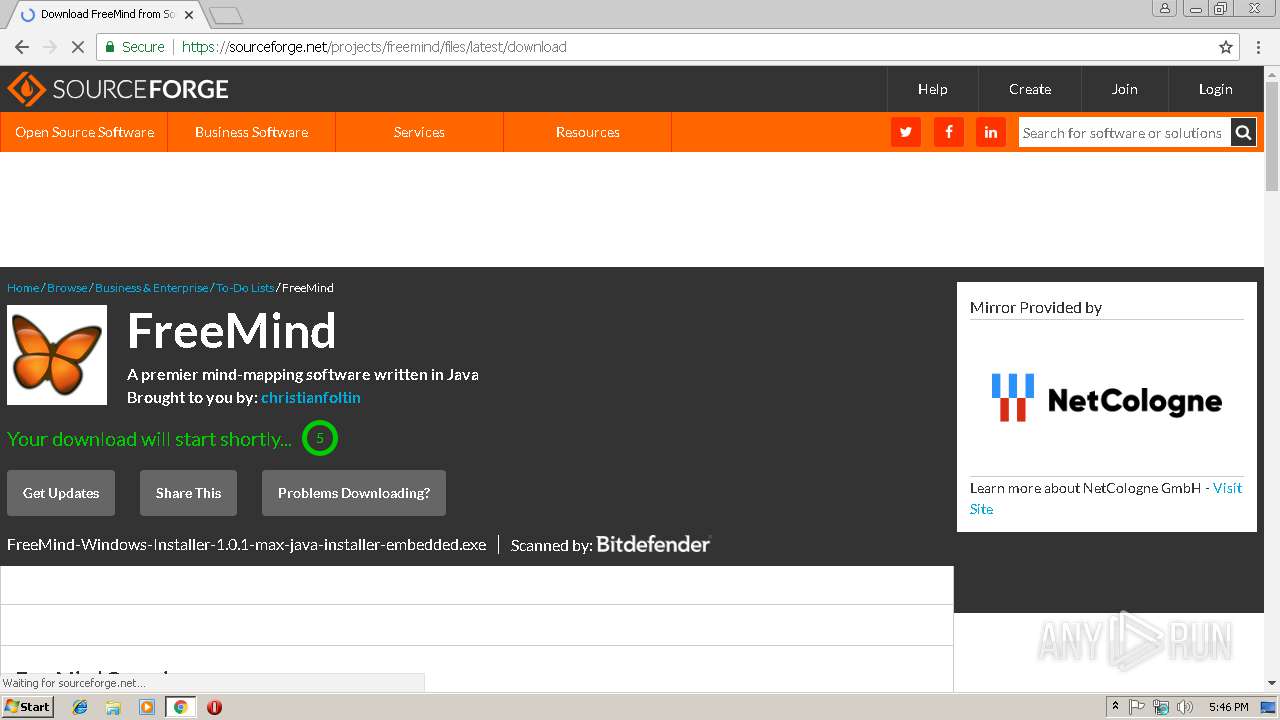
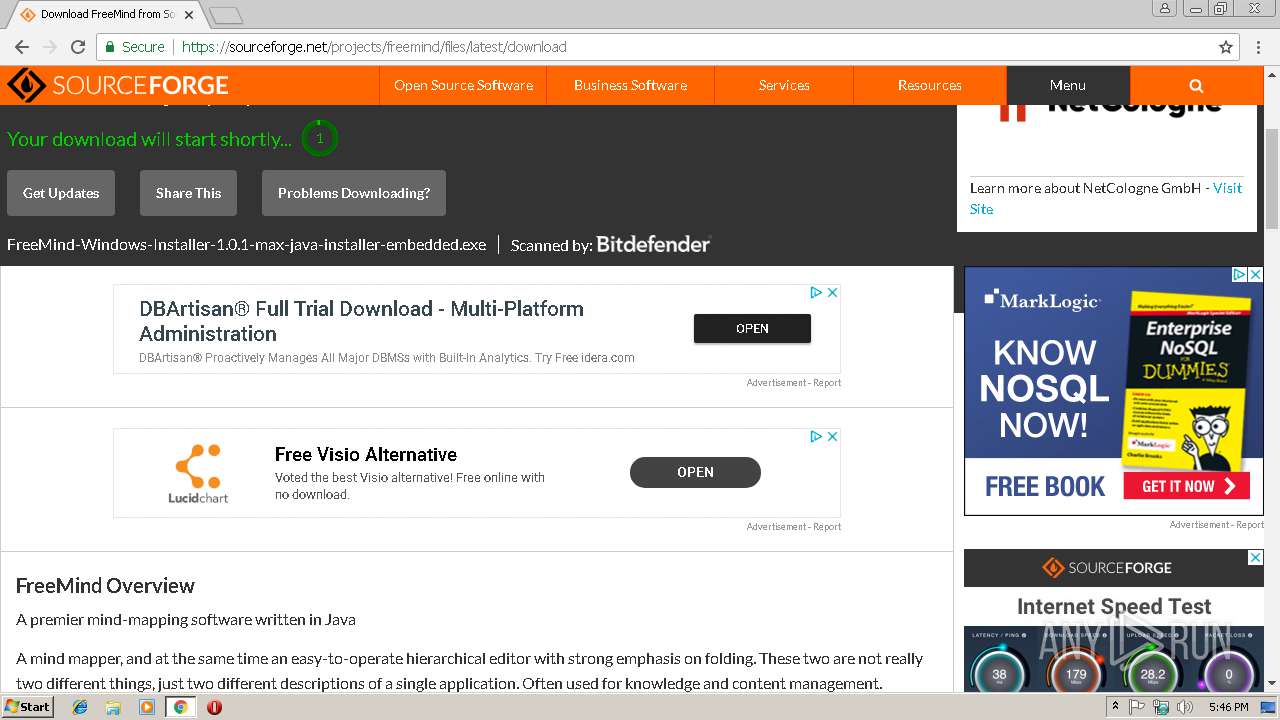
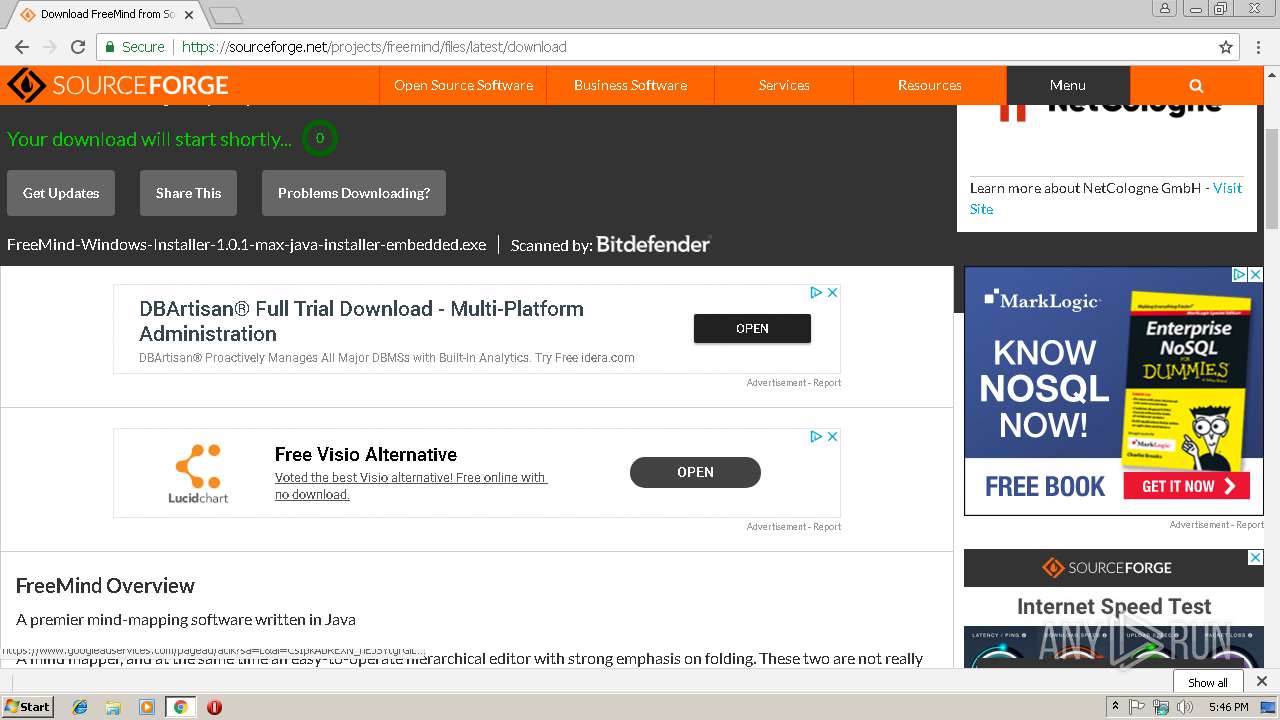
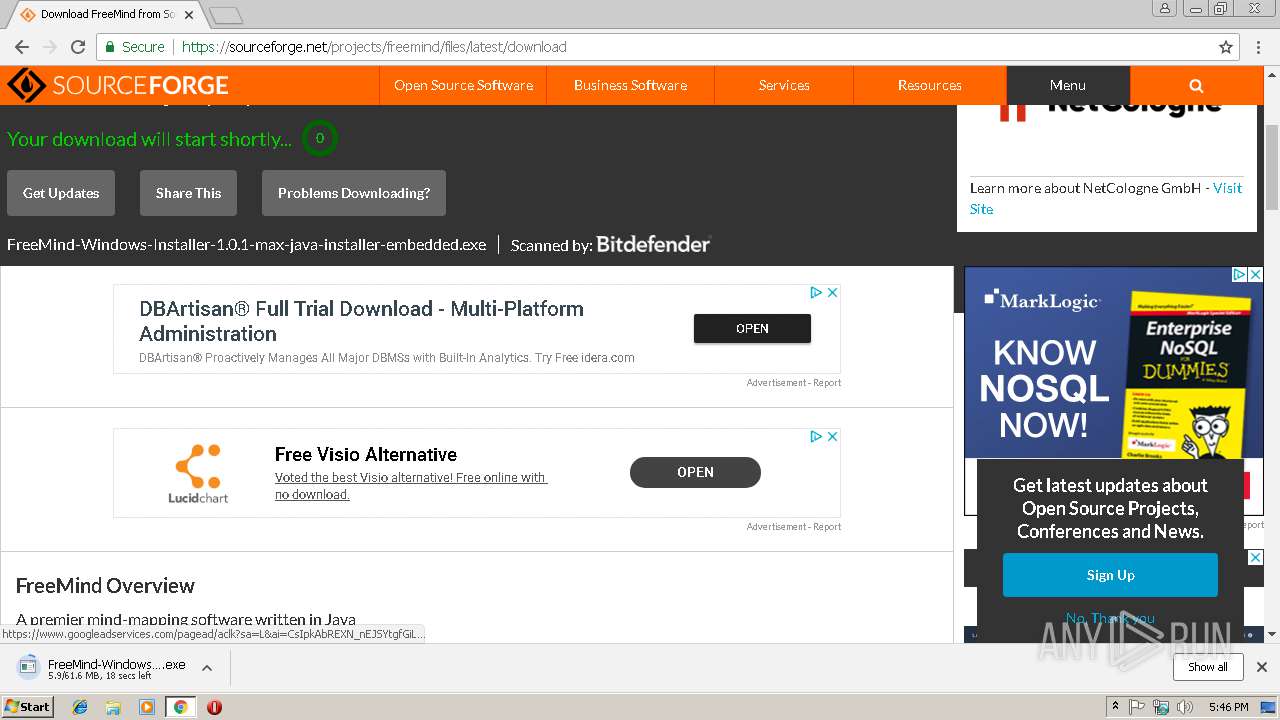
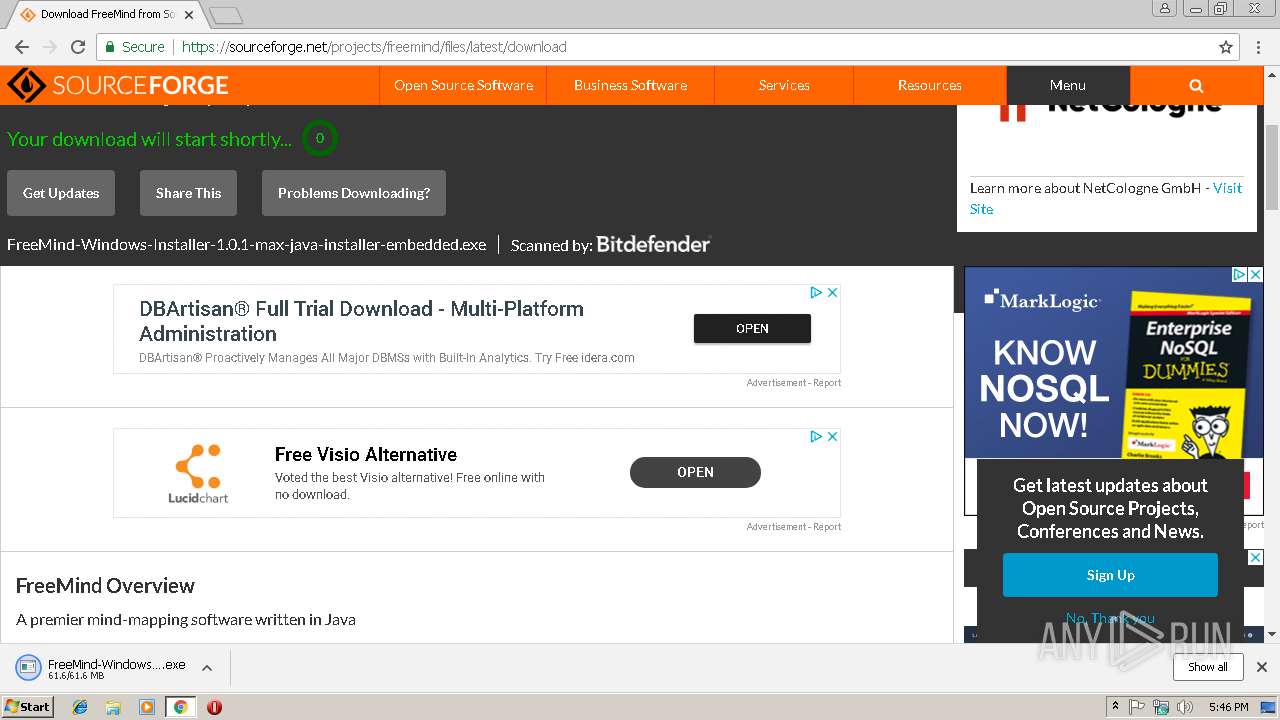
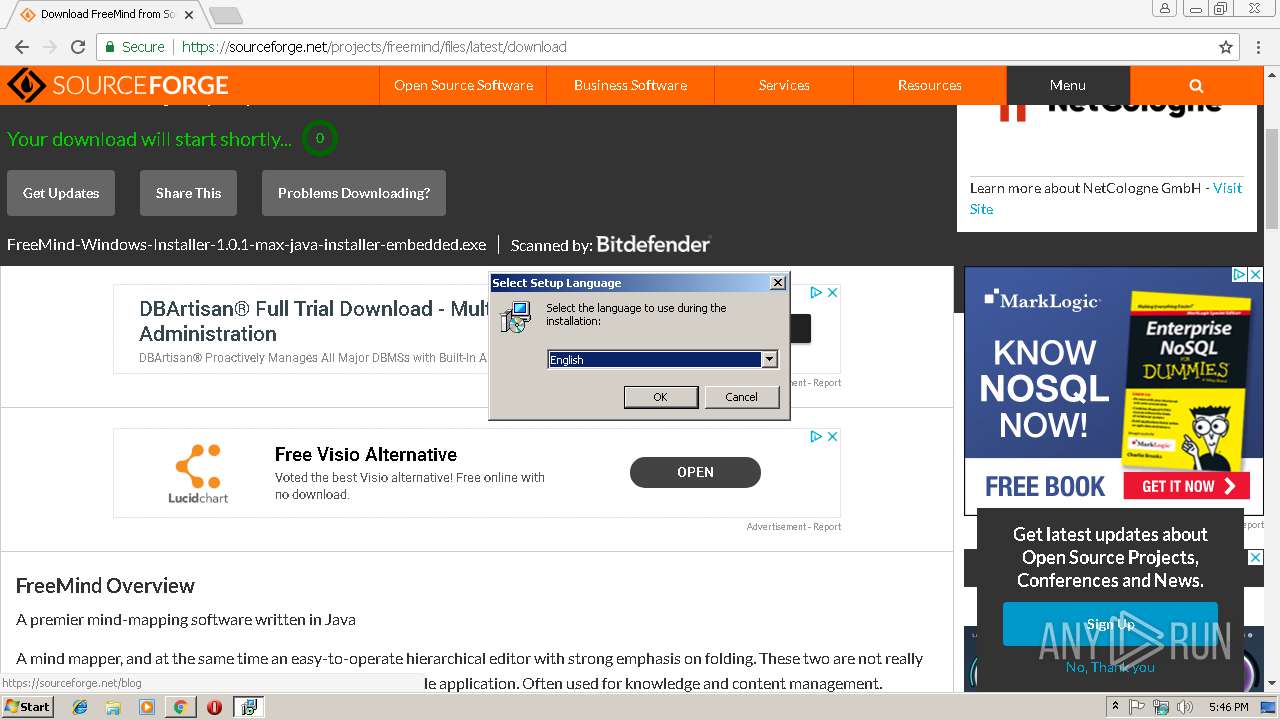
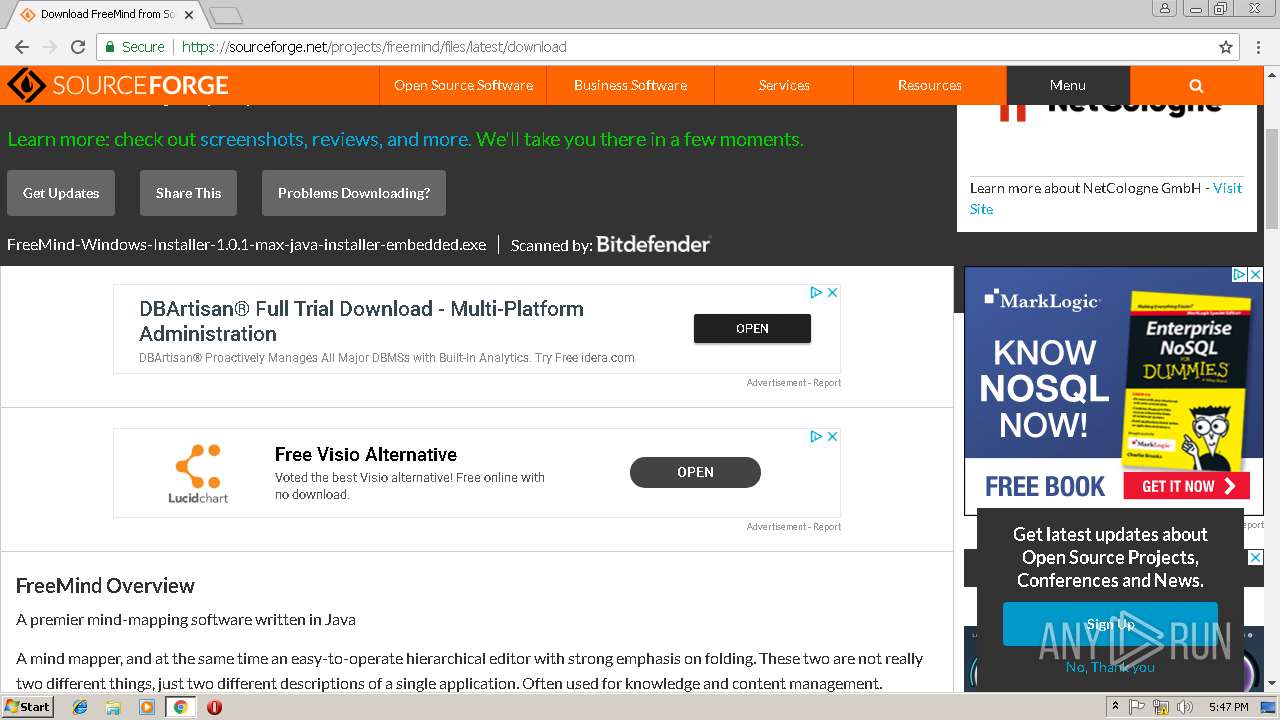
| URL: | https://netix.dl.sourceforge.net/project/freemind/freemind/1.0.1/freemind-windows-installer-1.0.1-max.exe |
| Full analysis: | https://app.any.run/tasks/6e1f2520-5fe3-4e46-b978-a1ce498e4e1d |
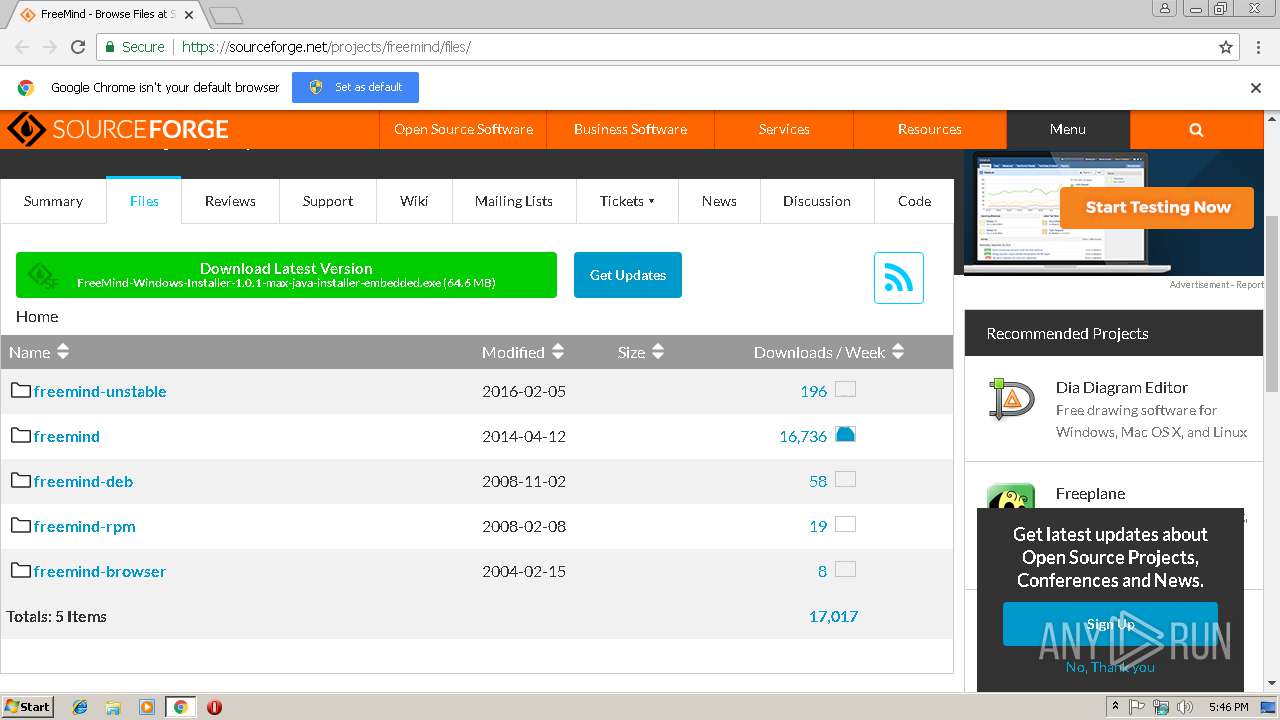
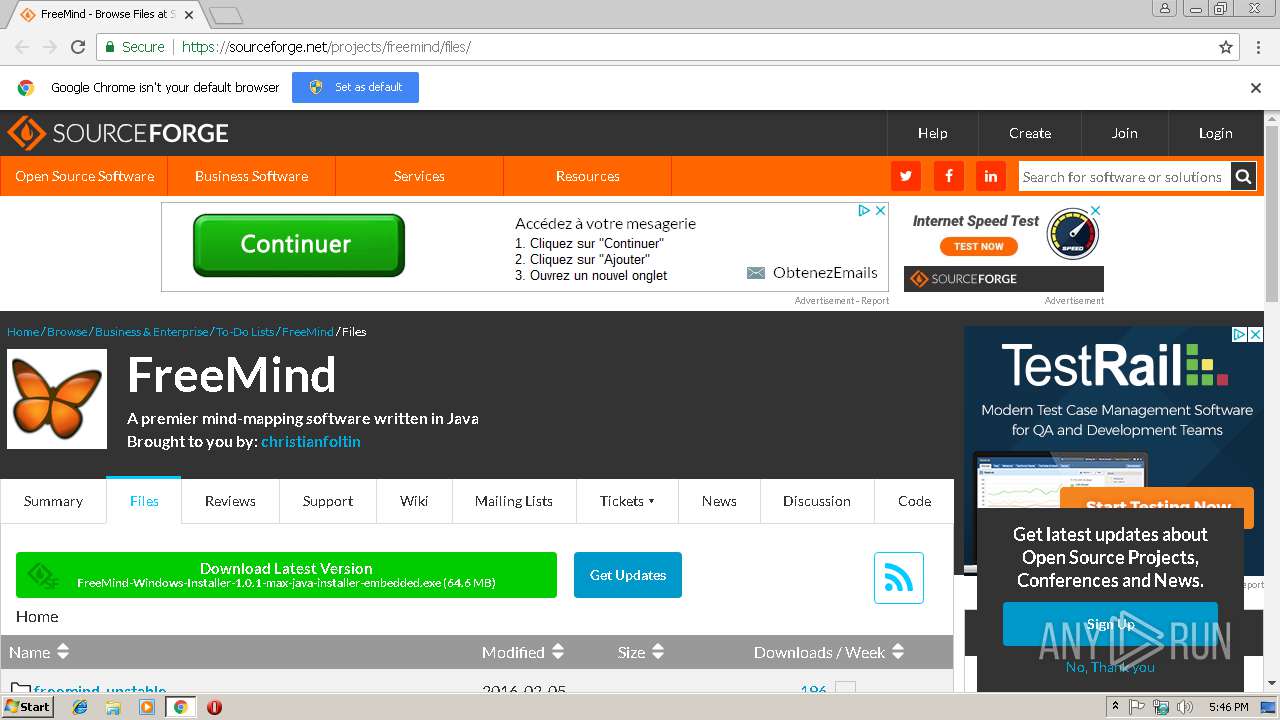
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2019, 17:45:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 457EFA3603F50F7850FE49FA0D50C46B |
| SHA1: | 3B7960B5015DABFCFBFF0AAED4A5A8D2AAF2AEE5 |
| SHA256: | 205FF8EA043BA2FF3989CEE783DC1768B6EA53460413BD94EF8B3A8EDD15587F |
| SSDEEP: | 3:N8HdL/iKQ2SuLAuUt6drtaPN5TvMASFTXIShUII0L4A:29GanCt6LiN57MASFTXlhR9 |
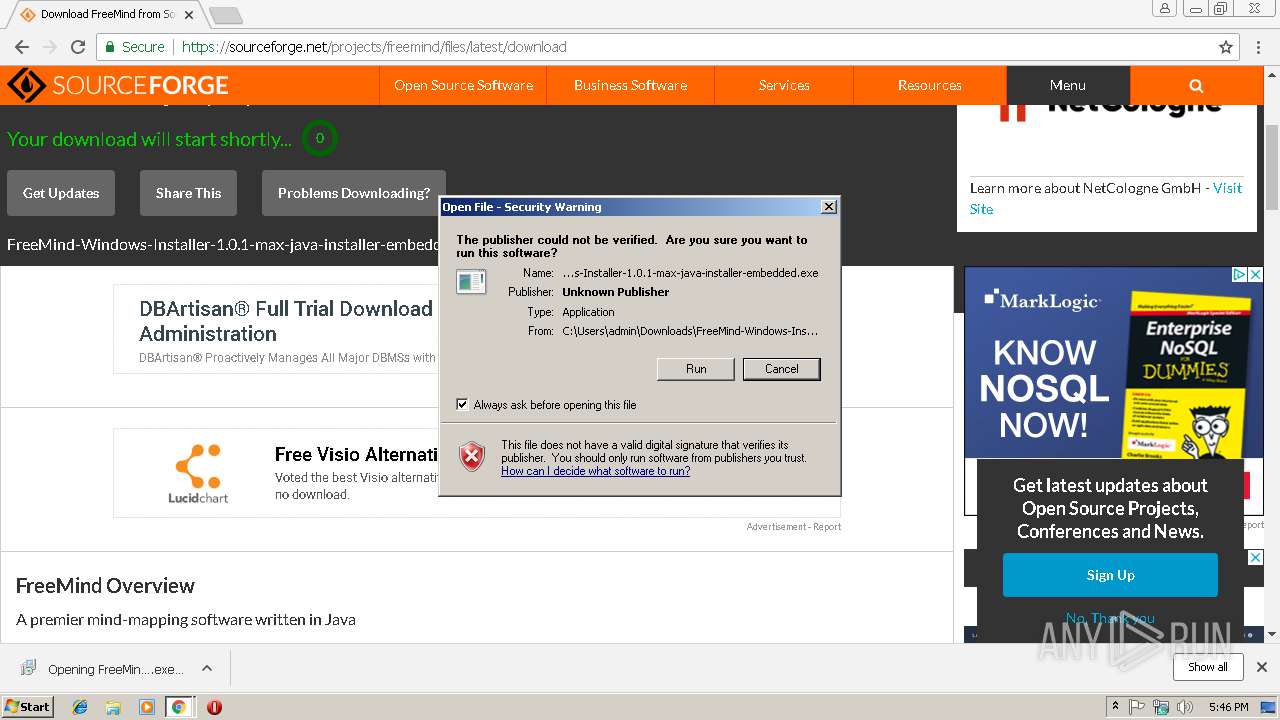
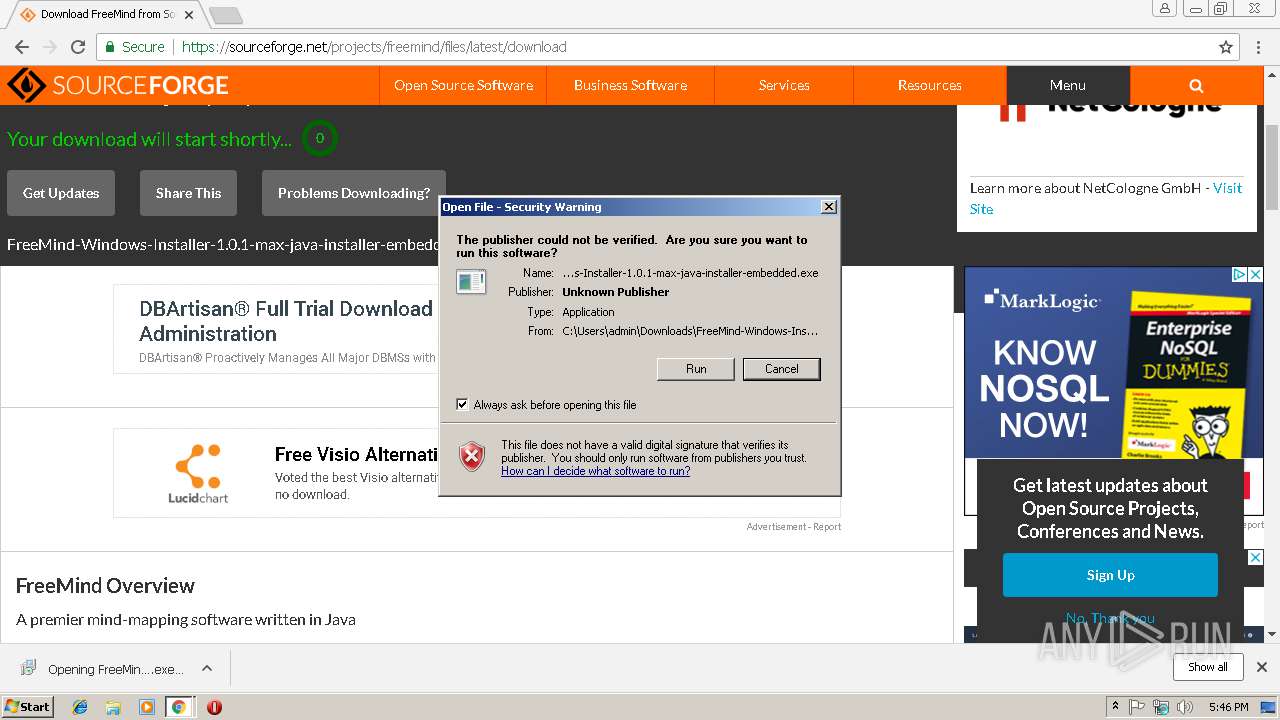
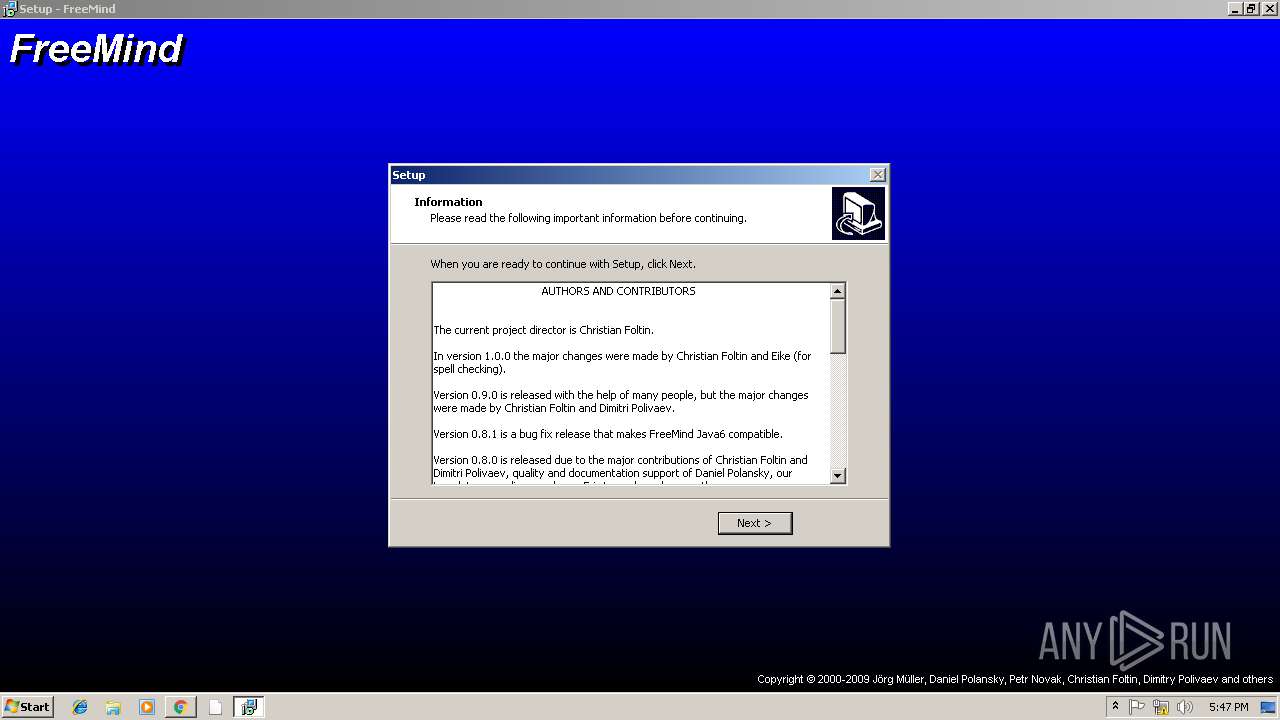
MALICIOUS
Application was dropped or rewritten from another process
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe (PID: 584)
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe (PID: 2552)
- FreeMind.exe (PID: 4000)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3024)
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe (PID: 584)
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp (PID: 2900)
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe (PID: 2552)
Modifies the open verb of a shell class
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp (PID: 2900)
Executes JAVA applets
- FreeMind.exe (PID: 4000)
Creates files in the user directory
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp (PID: 2900)
INFO
Changes settings of System certificates
- chrome.exe (PID: 3024)
Application launched itself
- chrome.exe (PID: 3024)
Reads settings of System Certificates
- chrome.exe (PID: 3024)
Reads Internet Cache Settings
- chrome.exe (PID: 3024)
Application was dropped or rewritten from another process
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp (PID: 2300)
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp (PID: 2900)
Loads dropped or rewritten executable
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp (PID: 2900)
Creates a software uninstall entry
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp (PID: 2900)
Creates files in the program directory
- FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
15
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
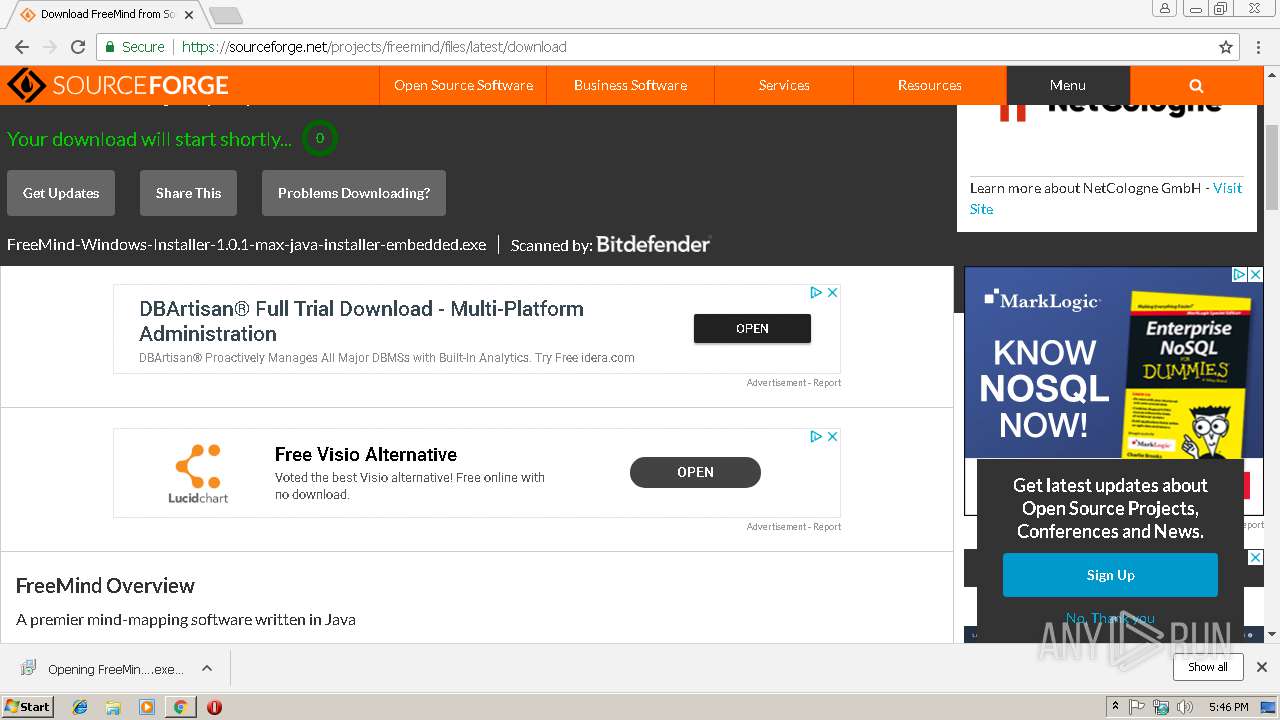
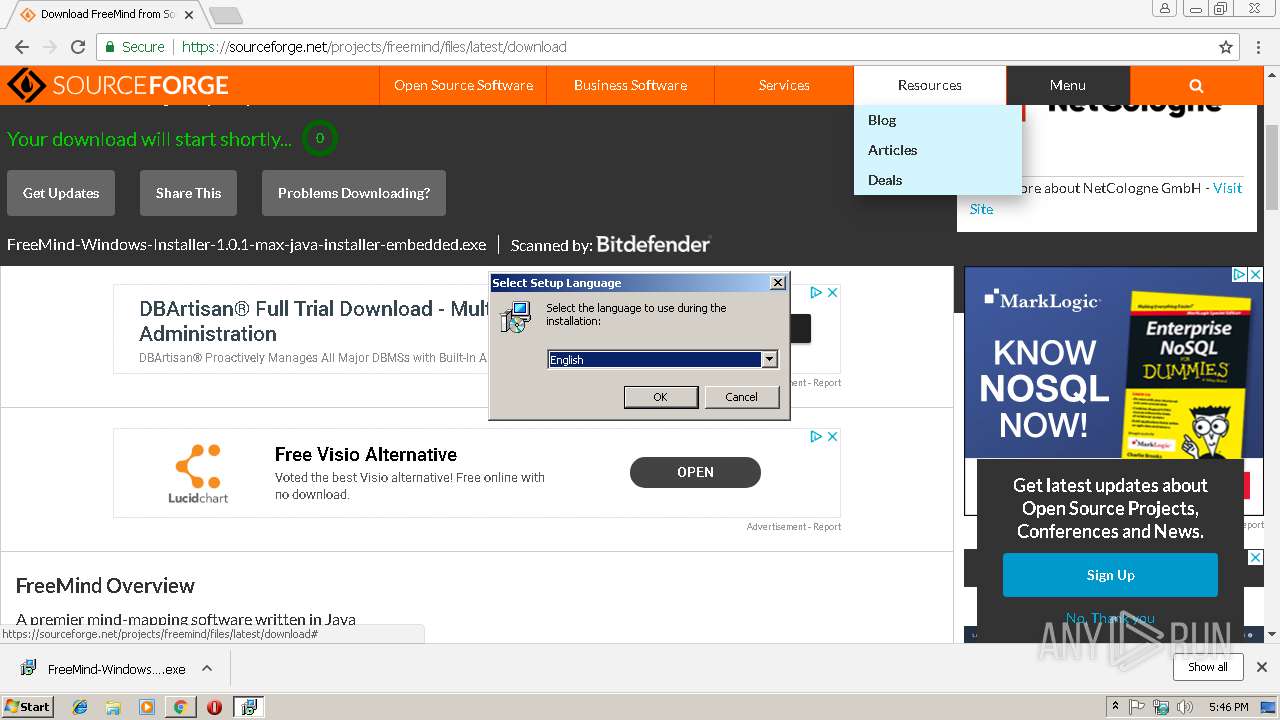
| 584 | "C:\Users\admin\Downloads\FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe" | C:\Users\admin\Downloads\FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe | chrome.exe | ||||||||||||
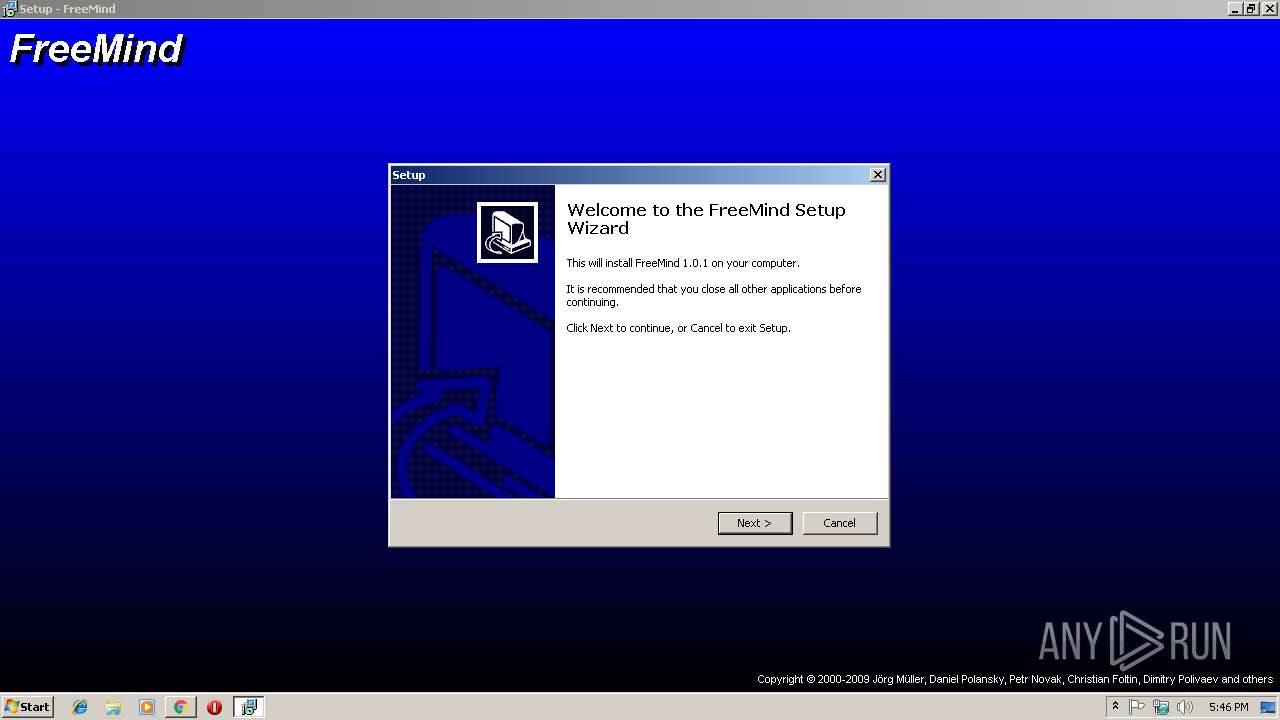
User: admin Company: Integrity Level: MEDIUM Description: FreeMind Setup Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=932,14626985881982110054,9530921386645269917,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=6575CC42F0B4E16380B6B08EDDB17655 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2300 | "C:\Users\admin\AppData\Local\Temp\is-NF44B.tmp\FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp" /SL5="$20142,64308110,56832,C:\Users\admin\Downloads\FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe" | C:\Users\admin\AppData\Local\Temp\is-NF44B.tmp\FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp | — | FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=932,14626985881982110054,9530921386645269917,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=27980BA74ABB9C02876435B03DD67D28 --mojo-platform-channel-handle=4056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2552 | "C:\Users\admin\Downloads\FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe" /SPAWNWND=$2015C /NOTIFYWND=$20142 | C:\Users\admin\Downloads\FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe | FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: FreeMind Setup Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,14626985881982110054,9530921386645269917,131072 --enable-features=PasswordImport --service-pipe-token=199BA151892DFACE2F2EA4ADA53A00DC --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=199BA151892DFACE2F2EA4ADA53A00DC --renderer-client-id=4 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\AppData\Local\Temp\is-MSG4H.tmp\FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp" /SL5="$3015A,64308110,56832,C:\Users\admin\Downloads\FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe" /SPAWNWND=$2015C /NOTIFYWND=$20142 | C:\Users\admin\AppData\Local\Temp\is-MSG4H.tmp\FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.tmp | FreeMind-Windows-Installer-1.0.1-max-java-installer-embedded.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3028 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
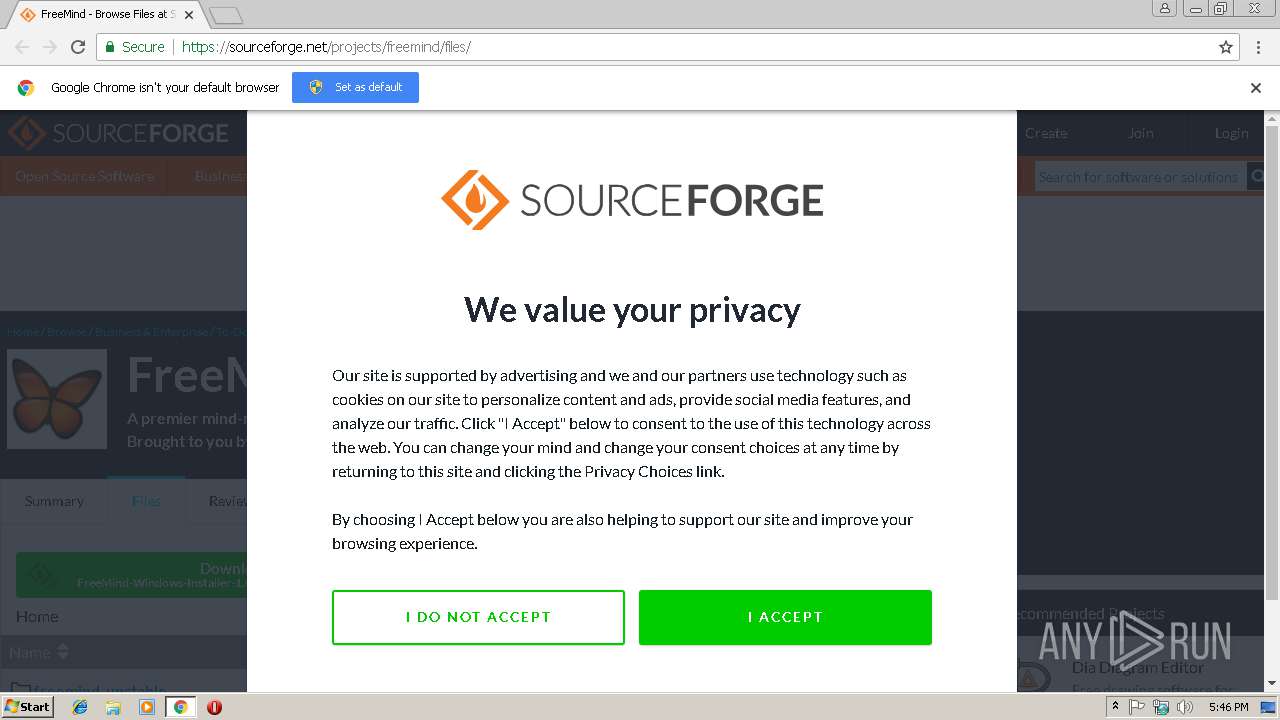
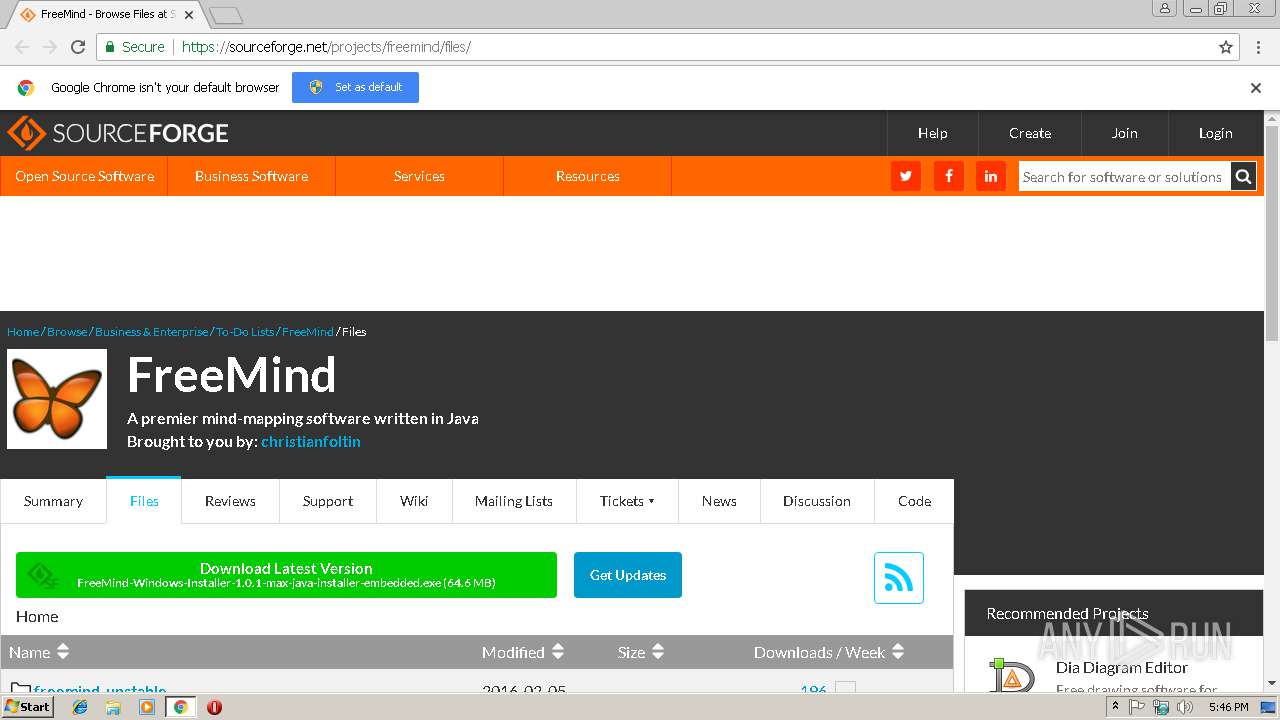
| 3024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://netix.dl.sourceforge.net/project/freemind/freemind/1.0.1/freemind-windows-installer-1.0.1-max.exe | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,14626985881982110054,9530921386645269917,131072 --enable-features=PasswordImport --service-pipe-token=0DD455A87F717C3681C3F40975F35618 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0DD455A87F717C3681C3F40975F35618 --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 497
Read events
1 394
Write events
94
Delete events
9
Modification events
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3024-13192479974357125 |
Value: 259 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3024-13192479974357125 |
Value: 259 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
44
Suspicious files
115
Text files
160
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1ec48c0b-c431-40ca-9230-c751c3a1a7c3.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3cc682f5-1847-49fe-80e6-68aaf07c2c79.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:92BE6B127E72365885AD4C3FB6534EE2 | SHA256:54302A2573ACC775720E7DB0AD85873276713302B4F72596A8DCC44B01C70E51 | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:197882774A7ECEC9046BC48F63189B66 | SHA256:27377B0D5F989997C2C3F74ACF163EED44B60631DDAA768F6655D7BE555742B2 | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:C10EBD4DB49249EFC8D112B2920D5F73 | SHA256:90A1B994CAFE902F22A88A22C0B6CC9CB5B974BF20F8964406DD7D6C9B8867D1 | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:1AA66EFDB743FB0A8DCC1CD79B0B6542 | SHA256:28D56532CCED7375A2A1C7731E57C1A1C2EC1AC9827F3E5BEEE7F8069A5F87DD | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF20e8ce.TMP | text | |
MD5:1AA66EFDB743FB0A8DCC1CD79B0B6542 | SHA256:28D56532CCED7375A2A1C7731E57C1A1C2EC1AC9827F3E5BEEE7F8069A5F87DD | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e8ce.TMP | text | |
MD5:92BE6B127E72365885AD4C3FB6534EE2 | SHA256:54302A2573ACC775720E7DB0AD85873276713302B4F72596A8DCC44B01C70E51 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
245
DNS requests
197
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3024 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODOECCAddTrustCA.crt | GB | der | 980 b | whitelisted |
3024 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/7E04DE896A3E666D00E687D33FFAD93BE83D349E.crt | US | der | 579 b | whitelisted |
3024 | chrome.exe | GET | 200 | 52.222.146.75:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3024 | chrome.exe | GET | 200 | 104.16.239.184:80 | http://cacerts.digicert.com/DigiCertSHA2SecureServerCA.crt | US | der | 1.15 Kb | whitelisted |
3024 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3024 | chrome.exe | GET | 200 | 188.121.36.237:80 | http://certificates.godaddy.com/repository/gdig2.crt | NL | der | 1.21 Kb | whitelisted |
3024 | chrome.exe | GET | 200 | 104.121.153.27:80 | http://ssl.trustwave.com/issuers/STCA.crt | NL | der | 956 b | whitelisted |
3024 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
3024 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/7E04DE896A3E666D00E687D33FFAD93BE83D349E.crt | US | der | 579 b | whitelisted |
3024 | chrome.exe | GET | 200 | 23.111.11.204:80 | http://repository.certum.pl/ctnca.cer | US | der | 959 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3024 | chrome.exe | 52.222.150.215:443 | api.quantcast.mgr.consensu.org | Amazon.com, Inc. | US | unknown |
3024 | chrome.exe | 87.121.121.2:443 | netix.dl.sourceforge.net | NetIX Communications Ltd. | BG | suspicious |
3024 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 216.105.38.13:443 | downloads.sourceforge.net | American Internet Services, LLC. | US | malicious |
3024 | chrome.exe | 104.20.117.11:443 | a.fsdn.com | Cloudflare Inc | US | shared |
3024 | chrome.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
3024 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
netix.dl.sourceforge.net |
| suspicious |
accounts.google.com |
| shared |
downloads.sourceforge.net |
| whitelisted |
sourceforge.net |
| whitelisted |
a.fsdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
crt.comodoca.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |