| File name: | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23 |
| Full analysis: | https://app.any.run/tasks/9ed66e9b-fee8-4958-8d51-d09b606c5ef7 |
| Verdict: | Suspicious activity |
| Analysis date: | October 02, 2020, 13:34:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D45B50A9E0F23CCA547F2AA488779229 |
| SHA1: | E0C4470E55AE0CB01CABA9D7395E93BA10705A79 |
| SHA256: | 204C81F347A77E436B18409CA893CF2EAF408659E990763C8F82FD7C476D5B23 |
| SSDEEP: | 98304:ZTyxs2N2NhF6OlE7gzvr1J9eW1xwumAjCUFlxmMX:C4d9sKr9eW1xwufjC2jLX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads internet explorer settings
- 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe (PID: 2908)
Reads Environment values
- 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe (PID: 2908)
Changes tracing settings of the file or console
- 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe (PID: 2908)
INFO
Reads the hosts file
- 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe (PID: 2908)
Reads settings of System Certificates
- 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe (PID: 2908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:27 15:15:12+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 53248 |
| InitializedDataSize: | 3969536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3dc00a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
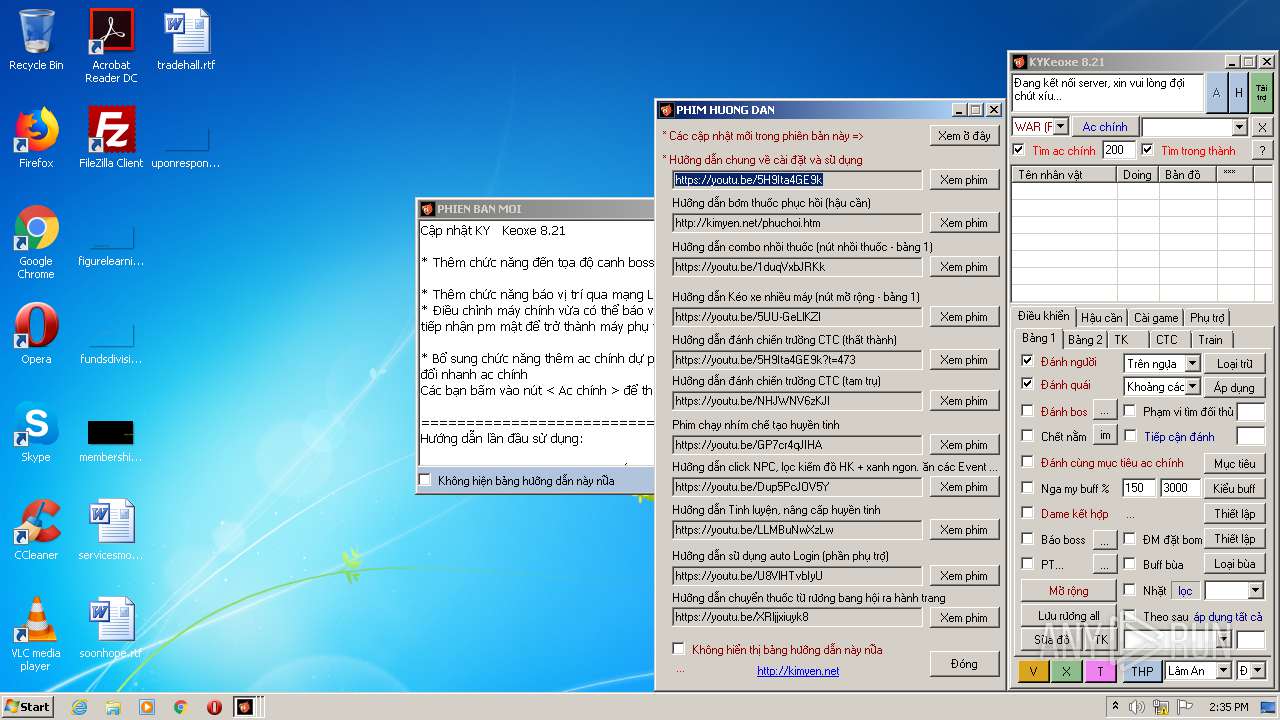
| Comments: | KYKeoxe (Auto Keoxe Kim Yen) |
| CompanyName: | http://vltool.blogspot.com |
| FileDescription: | KYKeoxe (Auto Keoxe Kim Yen) |
| FileVersion: | 1.0.0.0 |
| InternalName: | KYKeoxe.exe |
| LegalCopyright: | Kim Yen Tran |
| OriginalFileName: | KYKeoxe.exe |
| ProductName: | KYKeoxe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Dec-2018 14:15:12 |
| Comments: | KYKeoxe (Auto Keoxe Kim Yen) |
| CompanyName: | http://vltool.blogspot.com |
| FileDescription: | KYKeoxe (Auto Keoxe Kim Yen) |
| FileVersion: | 1.0.0.0 |
| InternalName: | KYKeoxe.exe |
| LegalCopyright: | Kim Yen Tran |
| OriginalFilename: | KYKeoxe.exe |
| ProductName: | KYKeoxe |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Dec-2018 14:15:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
{<-\x0a\x14",Z\xcc{< | 0x00002000 | 0x003C7BCC | 0x003C7C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99995 |
.text | 0x003CA000 | 0x0000CCA8 | 0x0000CE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.75217 |
.rsrc | 0x003D8000 | 0x00001298 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.75851 |
.reloc | 0x003DA000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
0x003DC000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.142636 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.17686 | 3064 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.0815 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
35
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2908 | "C:\Users\admin\AppData\Local\Temp\204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe" | C:\Users\admin\AppData\Local\Temp\204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | explorer.exe | ||||||||||||
User: admin Company: http://vltool.blogspot.com Integrity Level: MEDIUM Description: KYKeoxe (Auto Keoxe Kim Yen) Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
68
Read events
45
Write events
23
Delete events
0
Modification events
| (PID) Process: | (2908) 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\USERS\ADMIN\APPDATA\LOCAL\TEMP\204C81F347A77E436B18409CA893CF2EAF408659E990763C8F82FD7C476D5B23.EXE |
Value: RUNASADMIN | |||
| (PID) Process: | (2908) 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2908) 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2908) 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2908) 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2908) 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2908) 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2908) 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2908) 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2908) 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
14
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | HEAD | — | 210.211.111.85:80 | http://jxbisu.net/images/jxbisu_us.gif | VN | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | 193.204.114.105:13 | time.ien.it | Consortium GARR | IT | unknown |
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | 128.138.140.44:13 | utcnist.colorado.edu | University of Colorado at Boulder | US | unknown |
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | 128.138.141.172:13 | time.nist.gov | University of Colorado at Boulder | US | unknown |
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | 192.53.103.108:13 | ptbtime1.ptb.de | Verein zur Foerderung eines Deutschen Forschungsnetzes e.V. | NL | unknown |
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | 103.255.237.239:80 | kimyen.net | VNPT Corp | VN | suspicious |
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | 112.213.89.26:21 | — | SUPERDATA | VN | malicious |
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | 210.211.111.85:80 | jxbisu.net | CHT Compamy Ltd | VN | suspicious |
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | 151.101.65.176:80 | free.timeanddate.com | Fastly | US | unknown |
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | 151.101.1.176:80 | free.timeanddate.com | Fastly | US | suspicious |
2908 | 204c81f347a77e436b18409ca893cf2eaf408659e990763c8f82fd7c476d5b23.exe | 104.27.164.69:443 | jxtrungnguyen2005.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
time.ien.it |
| unknown |
utcnist.colorado.edu |
| whitelisted |
time.nist.gov |
| whitelisted |
ptbtime1.ptb.de |
| unknown |
free.timeanddate.com |
| suspicious |
kimyen.net |
| suspicious |
kimyen.club |
| suspicious |
jxbisu.net |
| unknown |
jxtrungnguyen2005.com |
| suspicious |
volamvidieu.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report