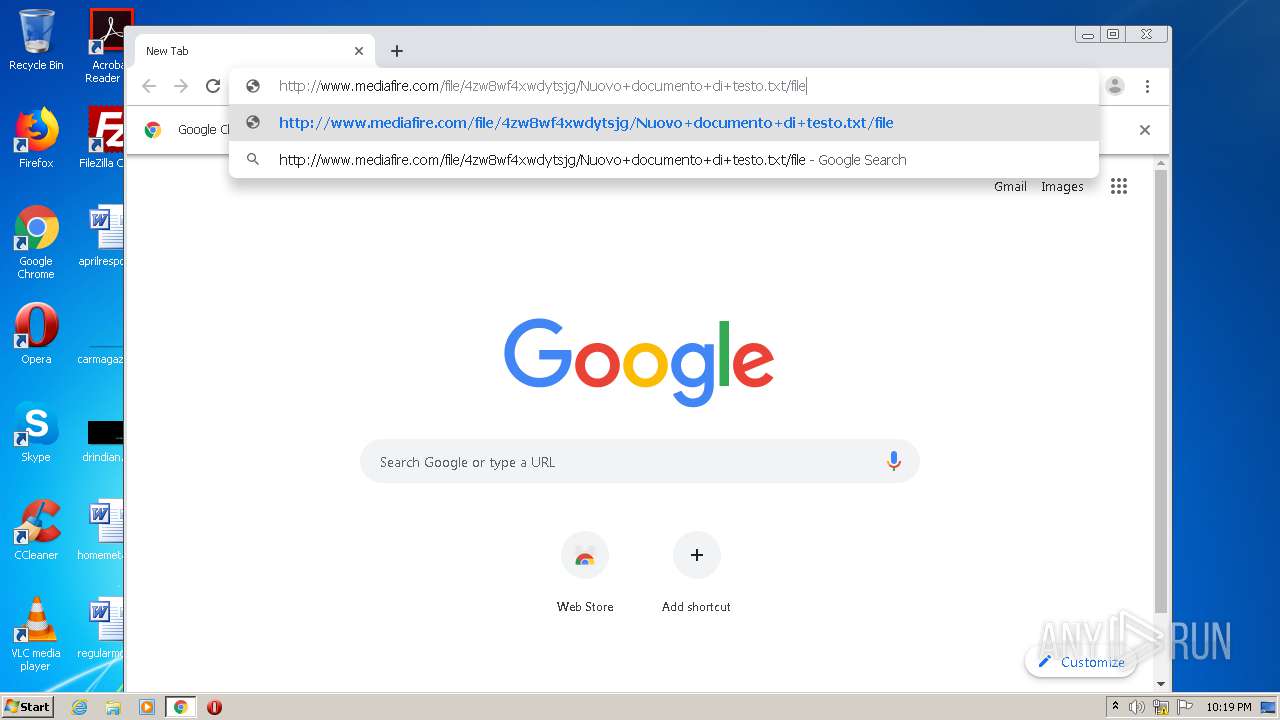
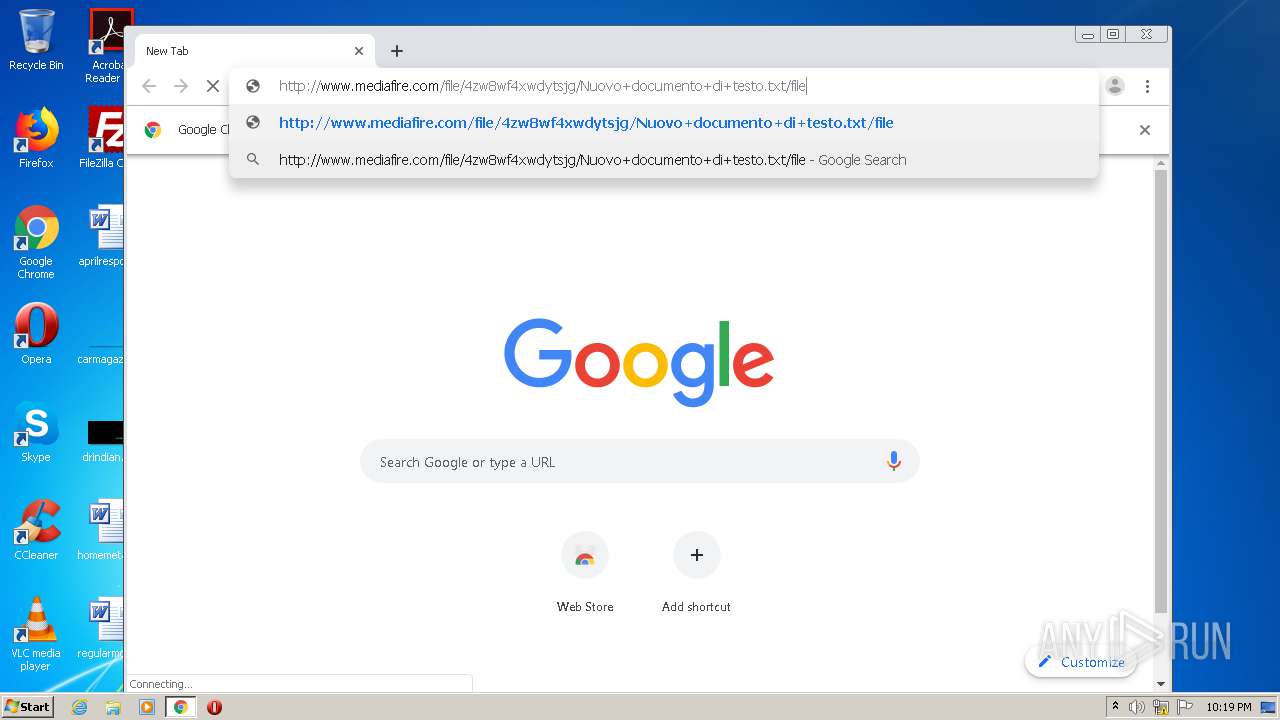
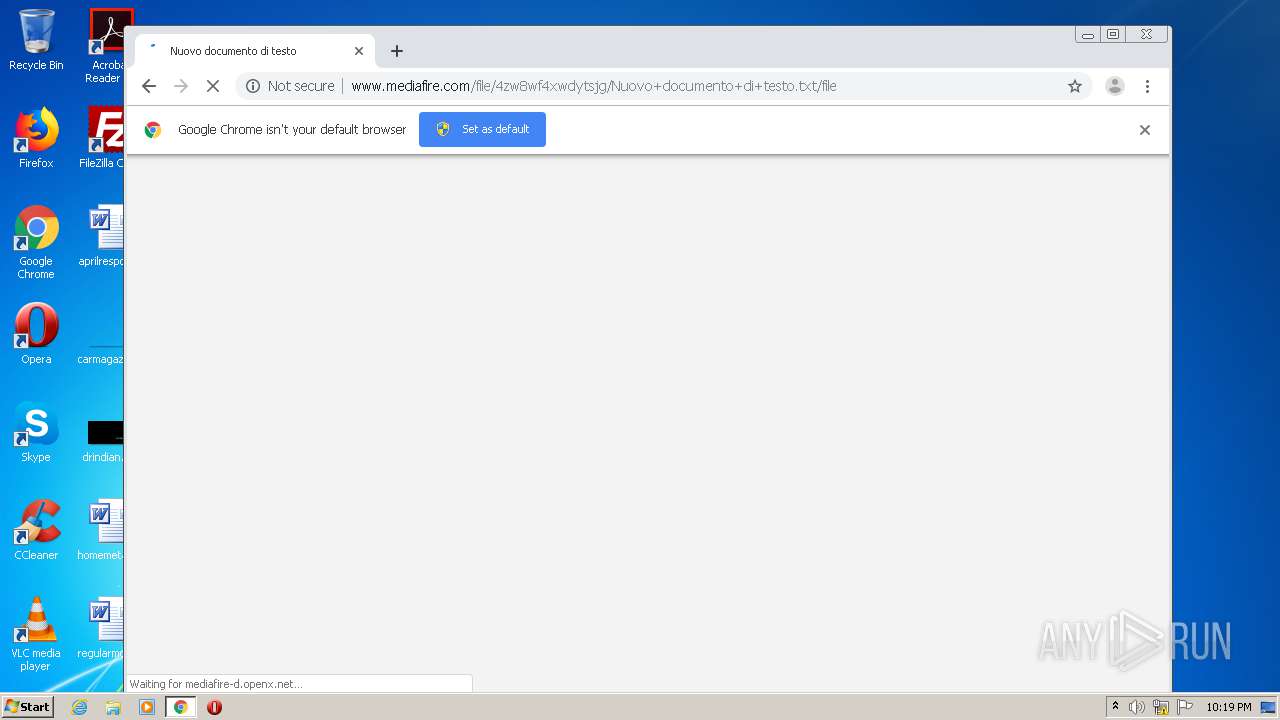
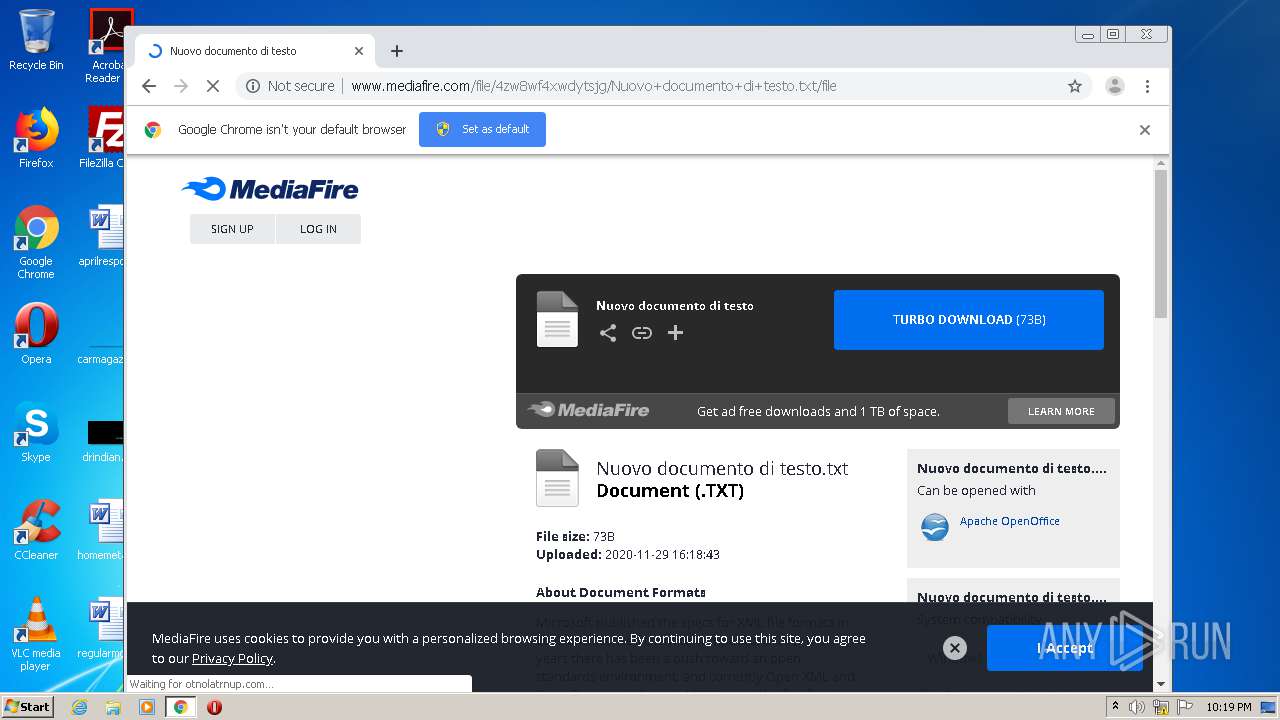
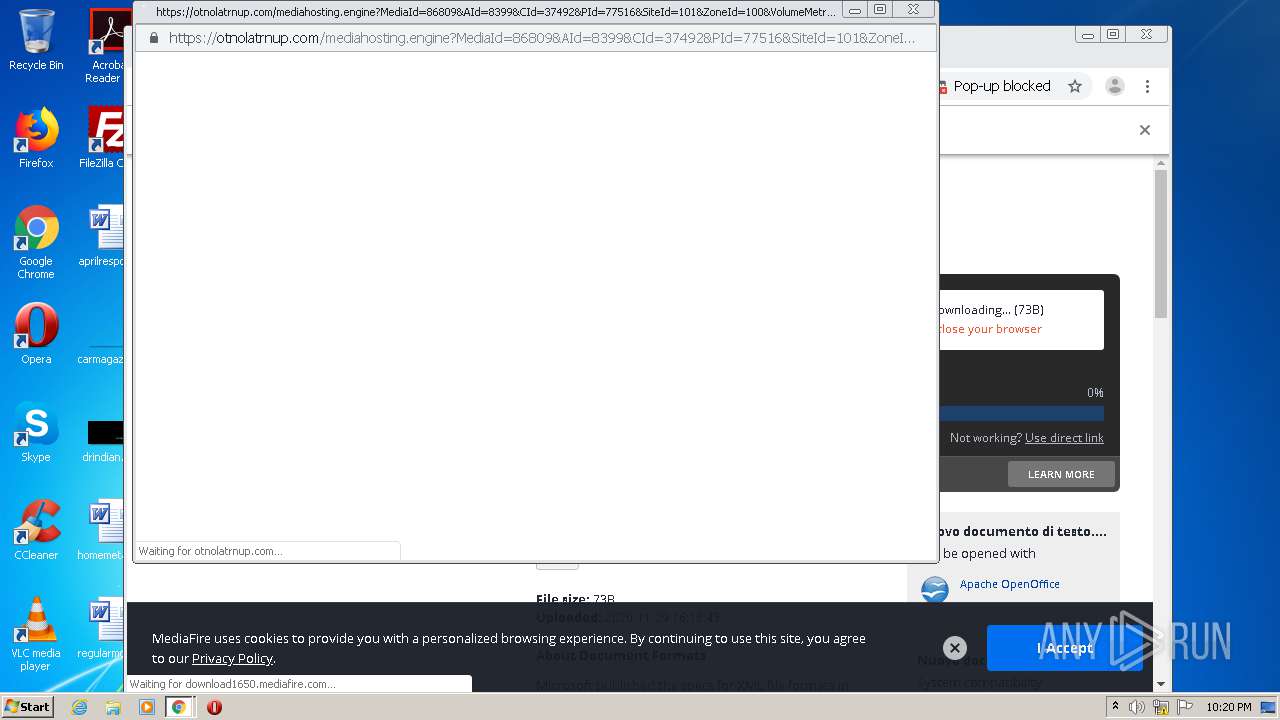
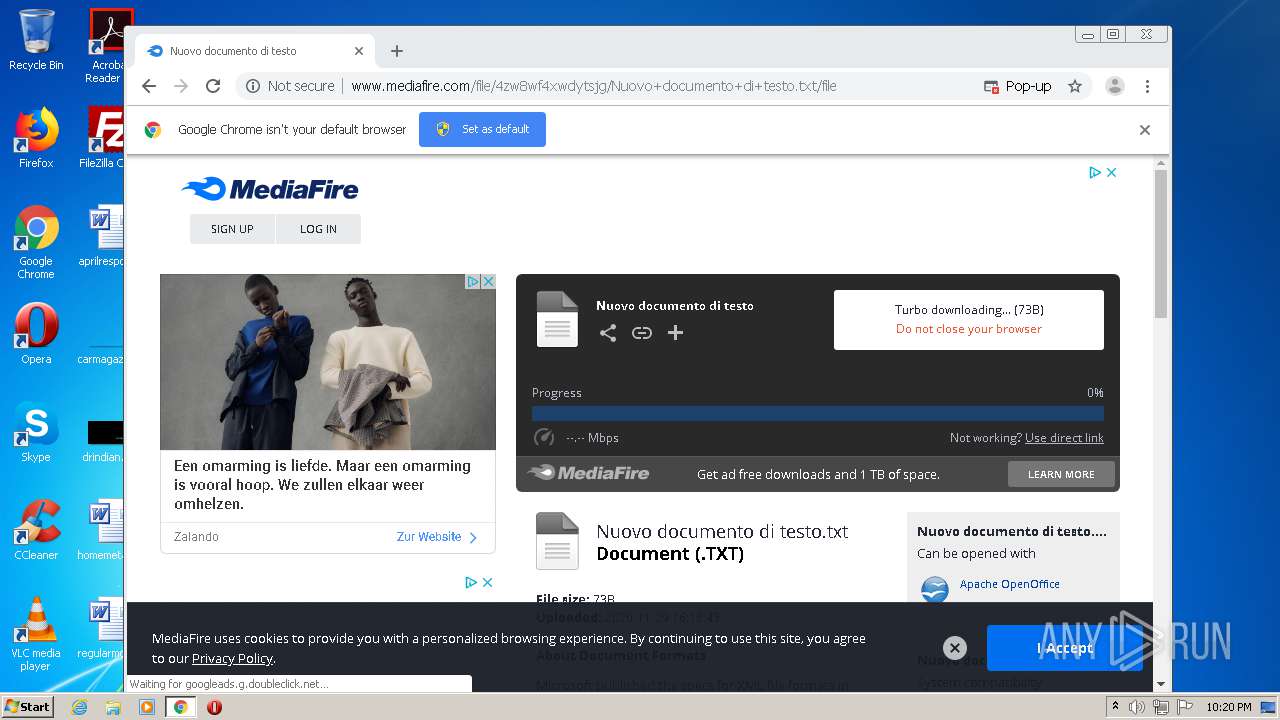
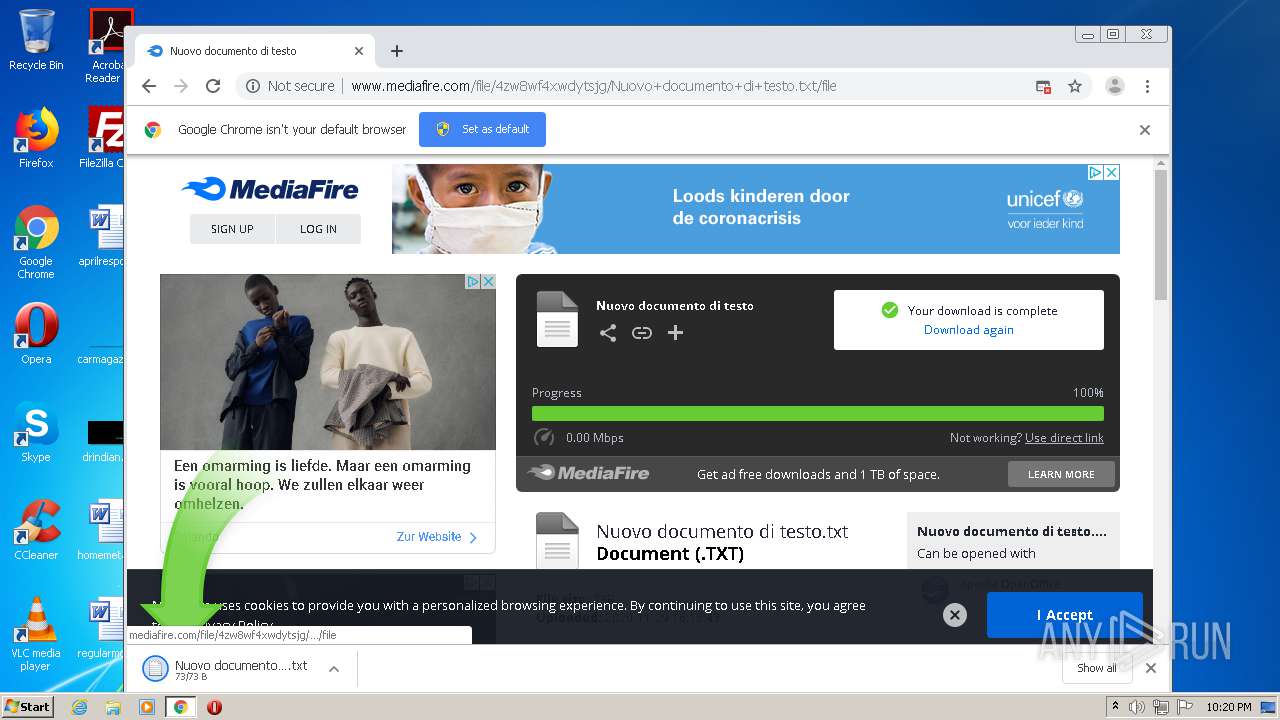
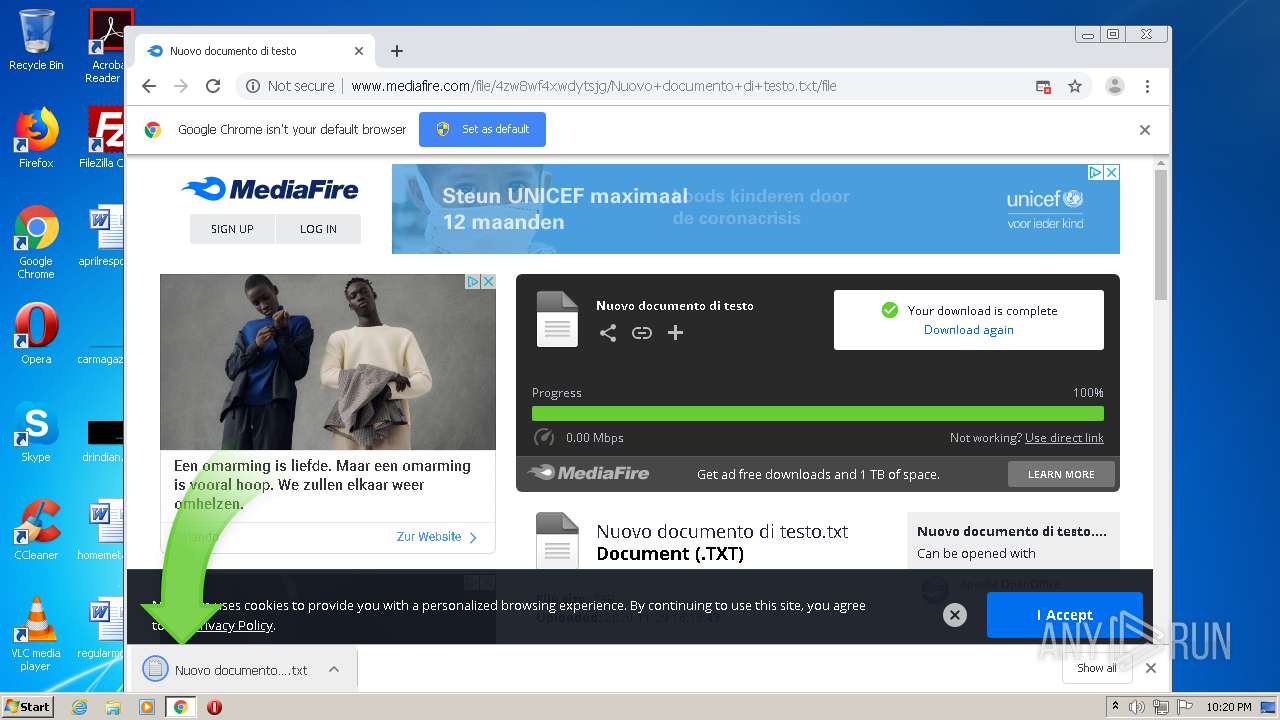
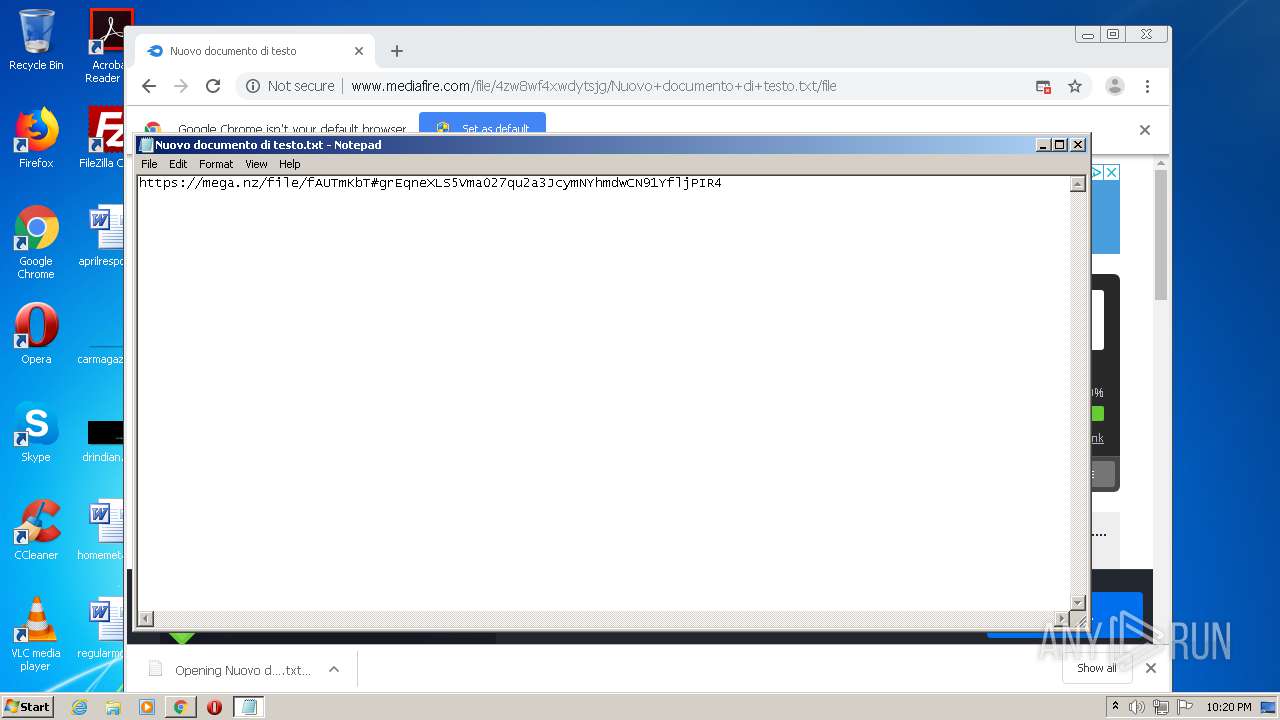
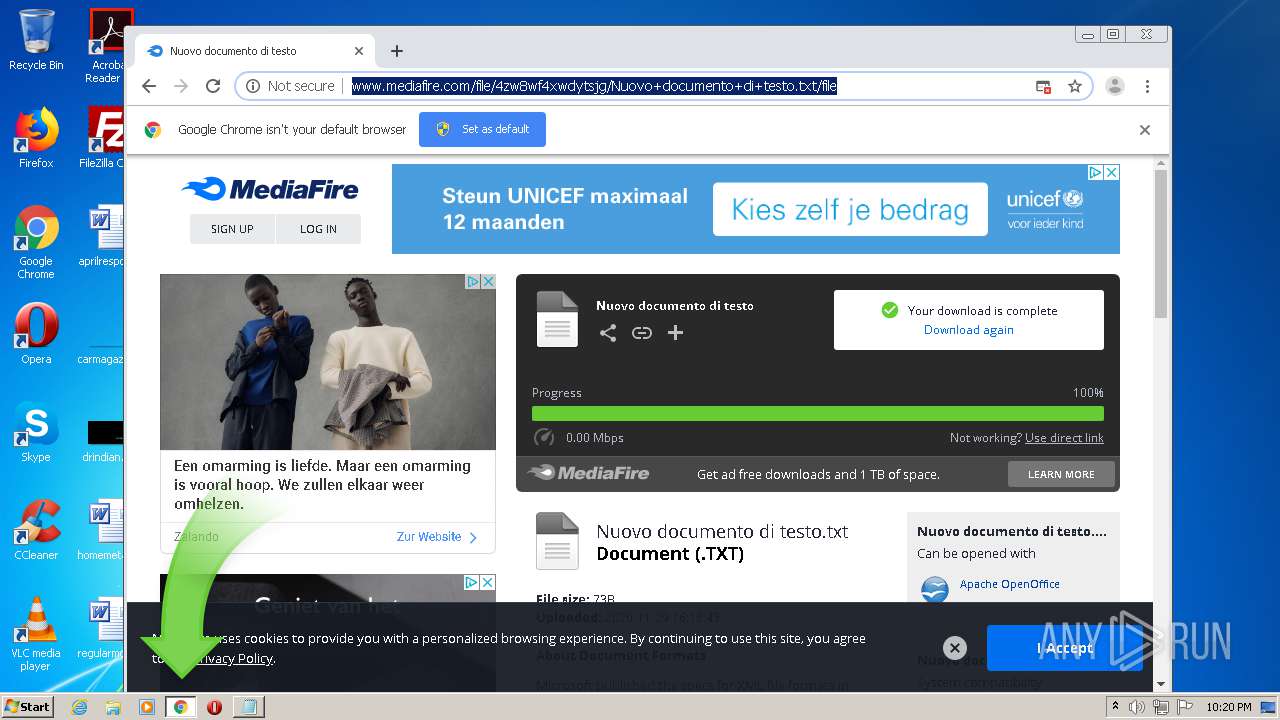
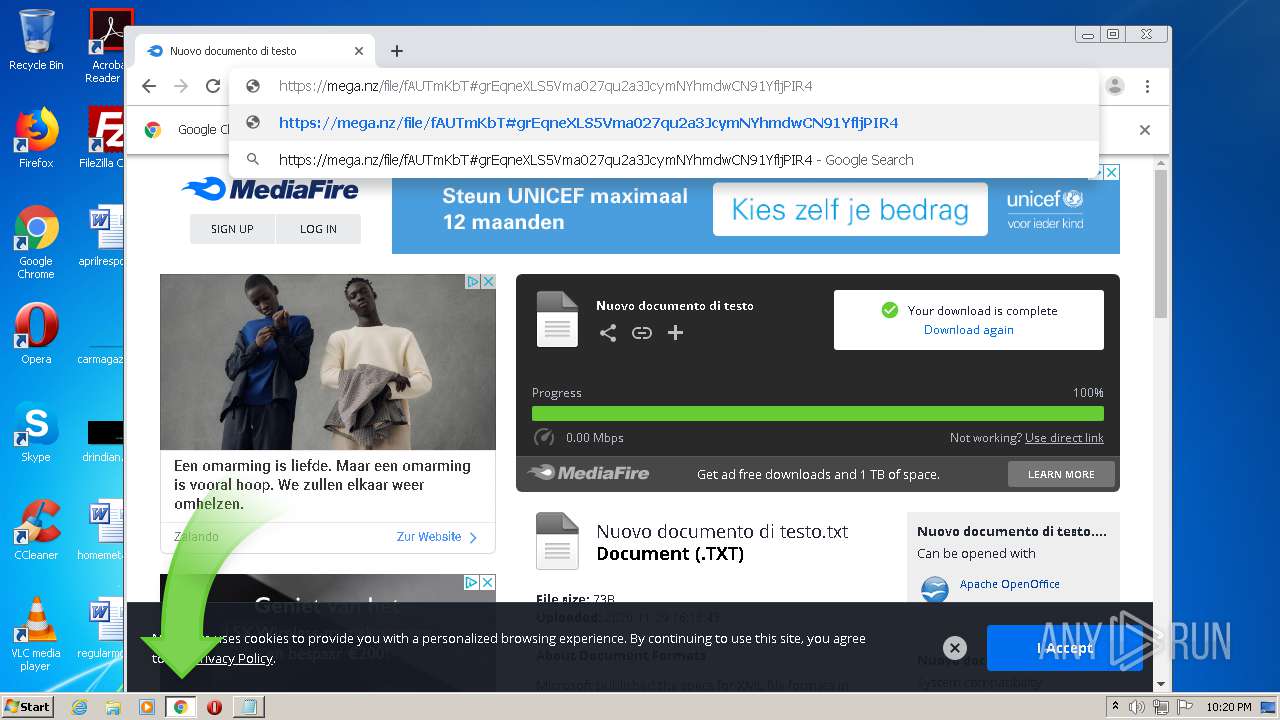
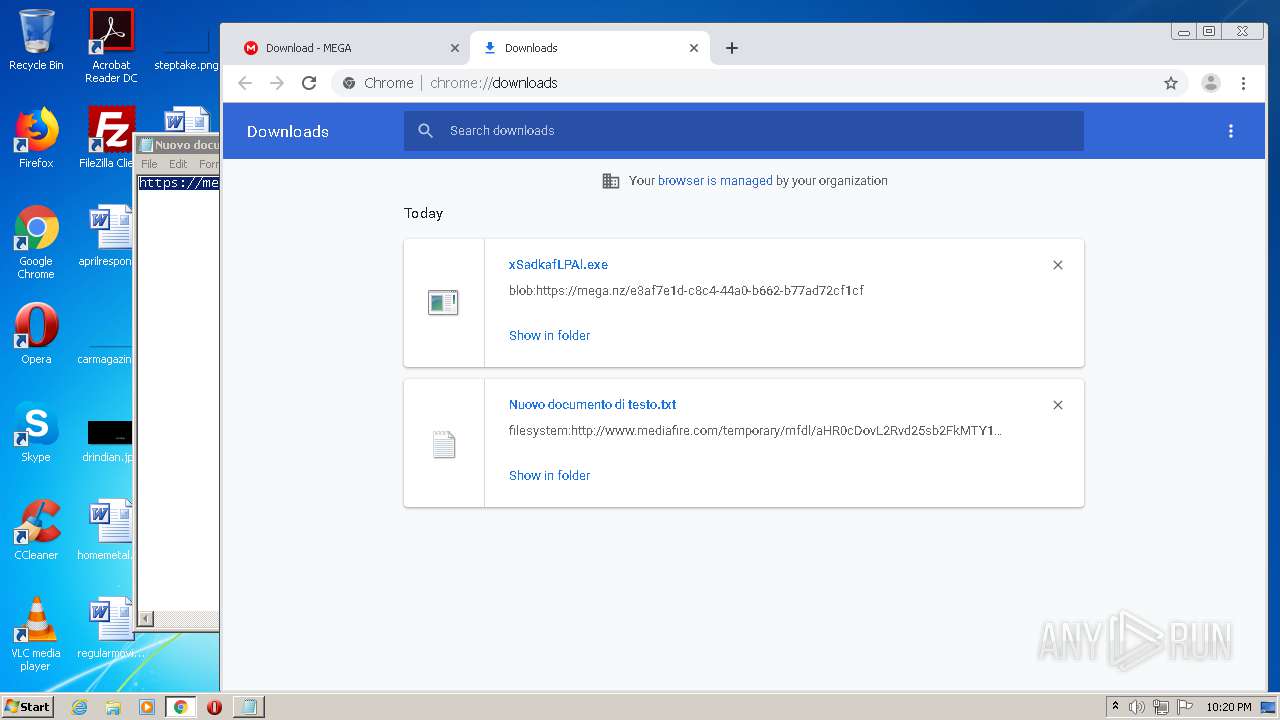
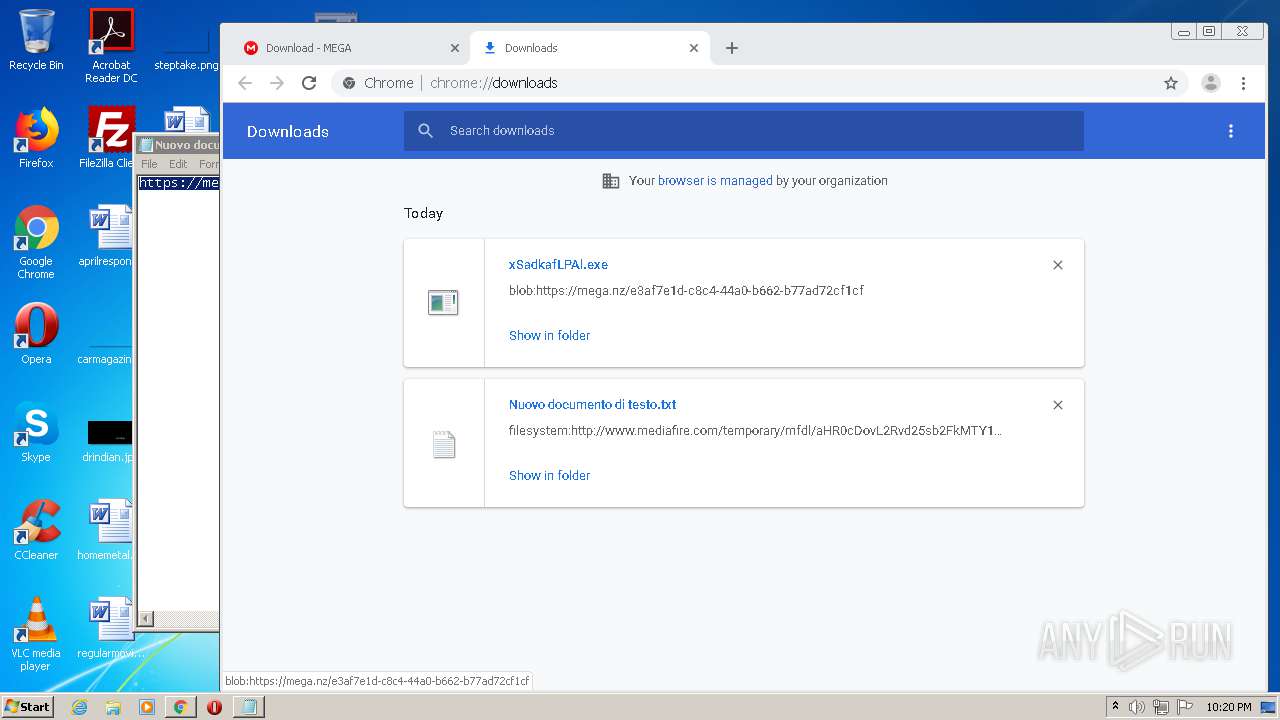
| URL: | http://www.mediafire.com/file/4zw8wf4xwdytsjg/Nuovo+documento+di+testo.txt/file |
| Full analysis: | https://app.any.run/tasks/f94b6ca9-ddb1-4348-88e4-ce38e3b65ce8 |
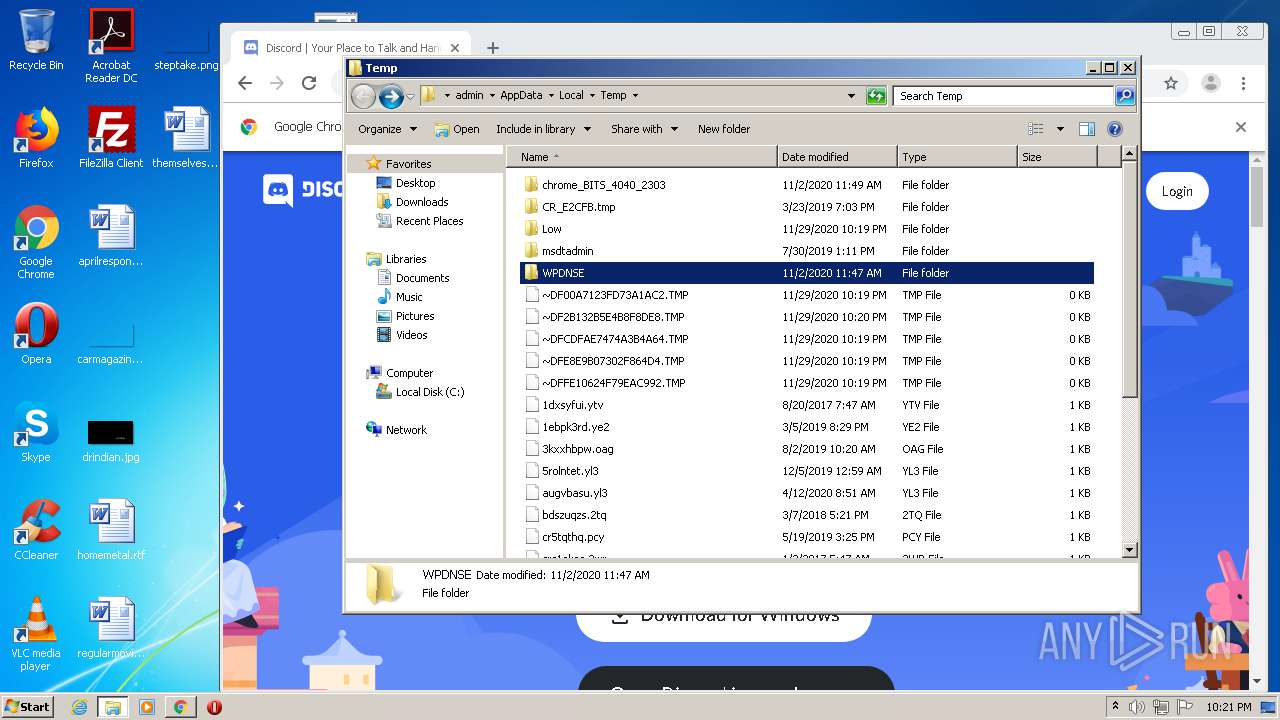
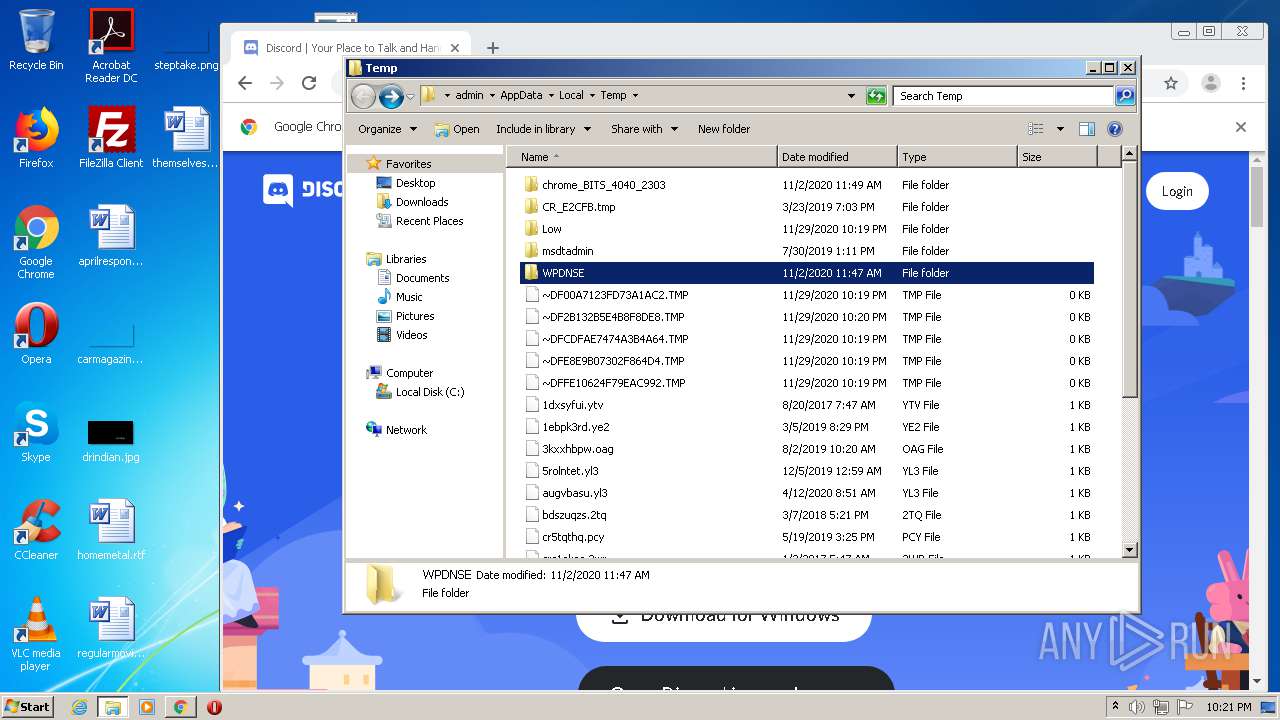
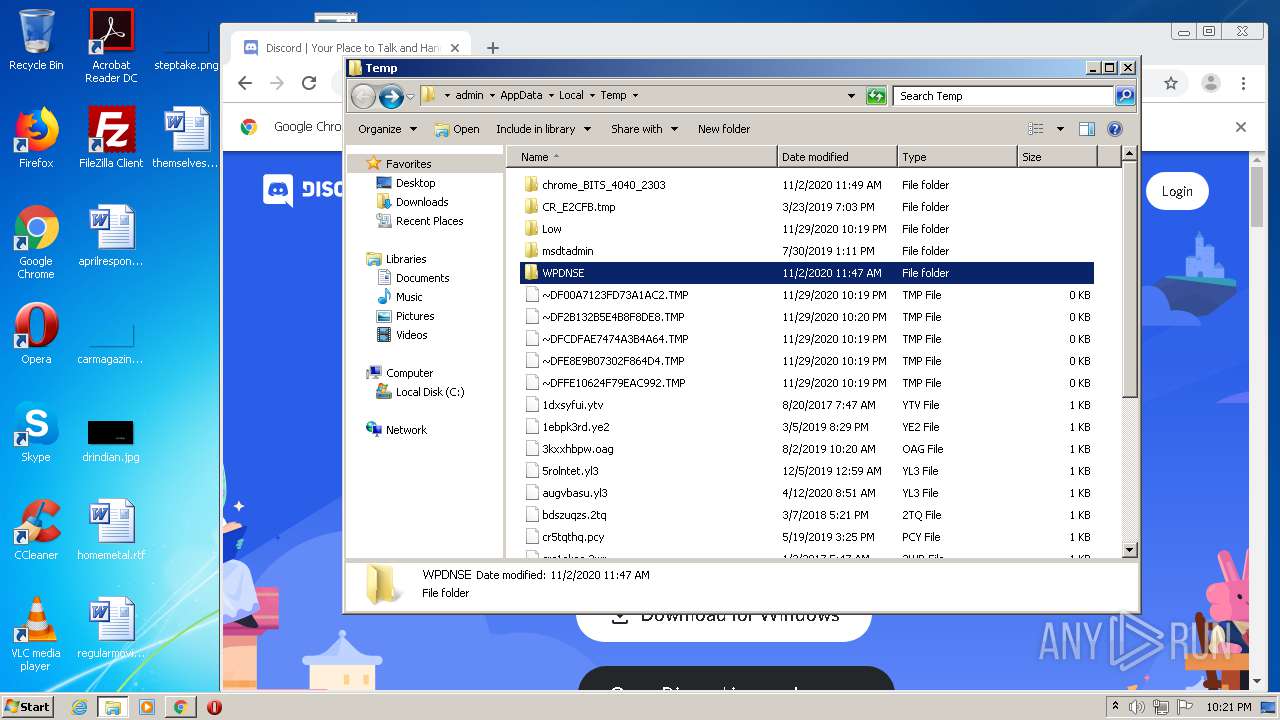
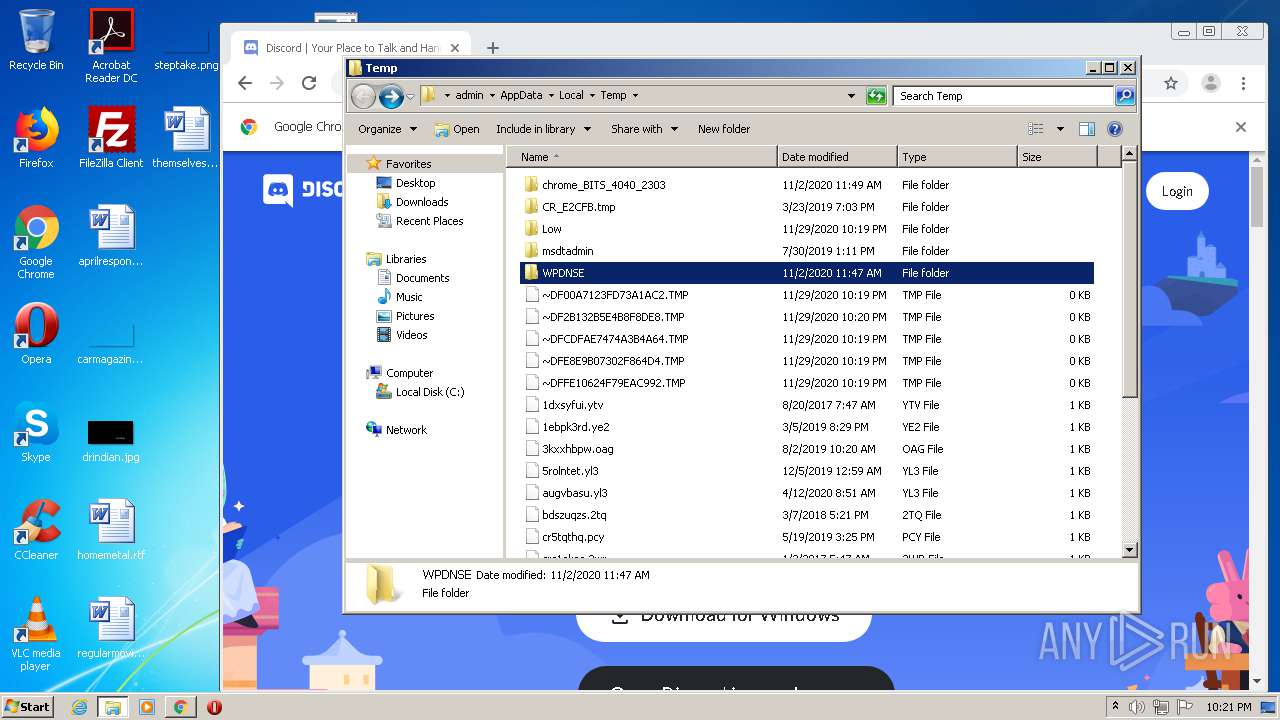
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 22:19:10 |
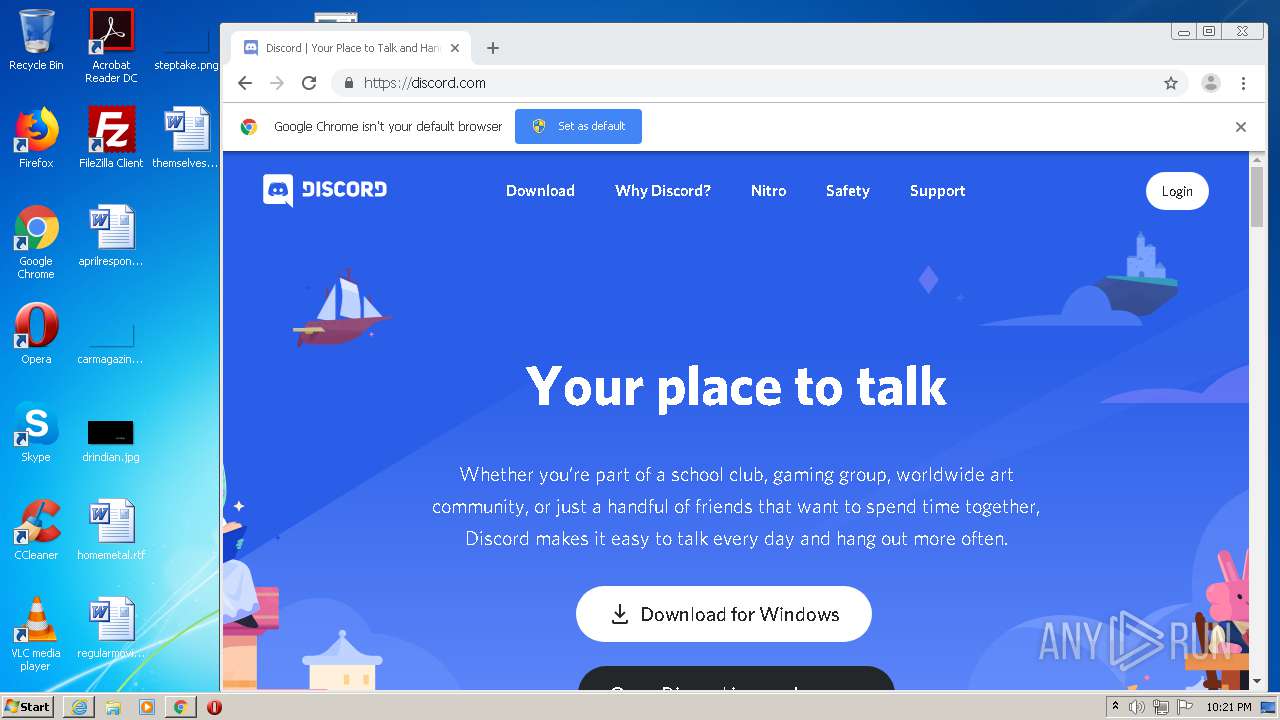
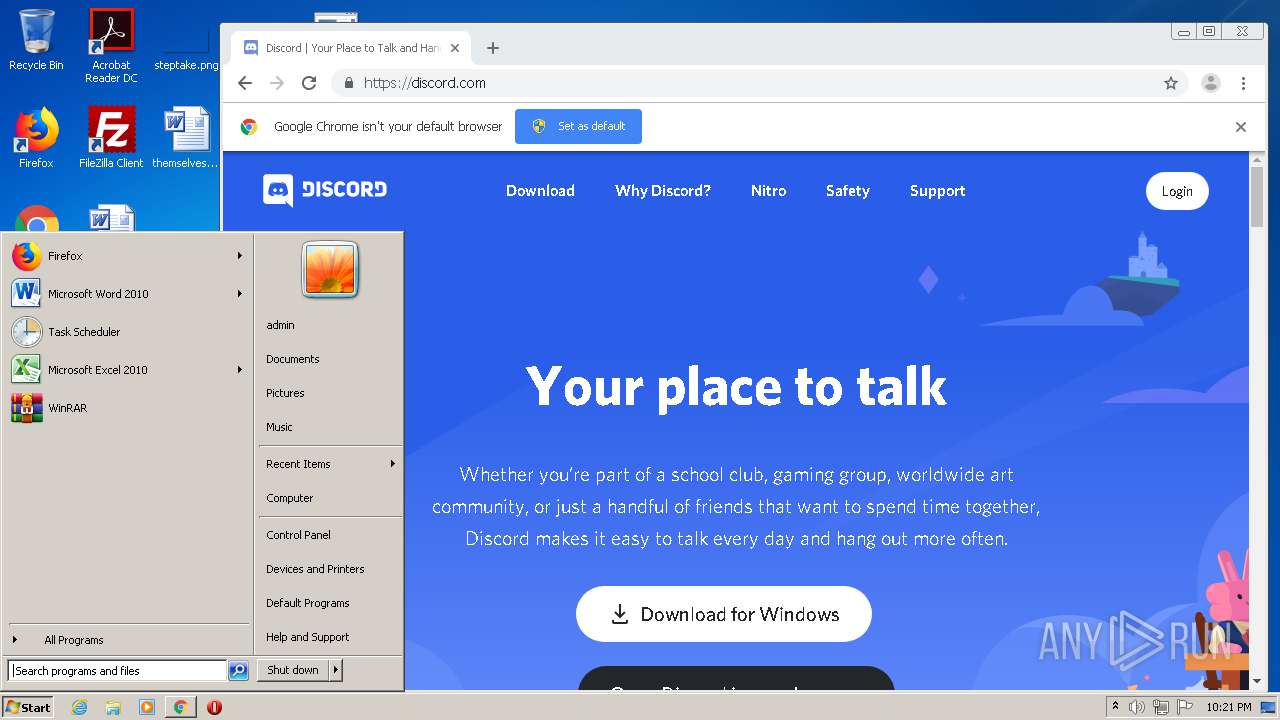
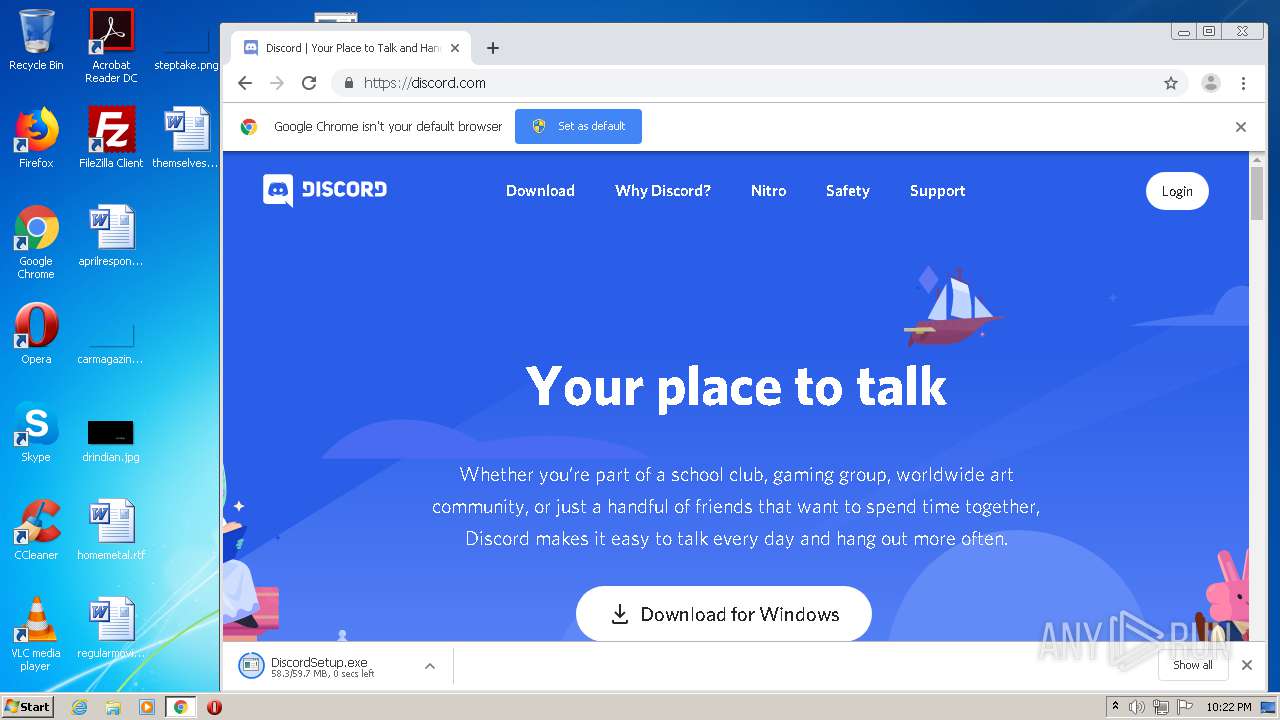
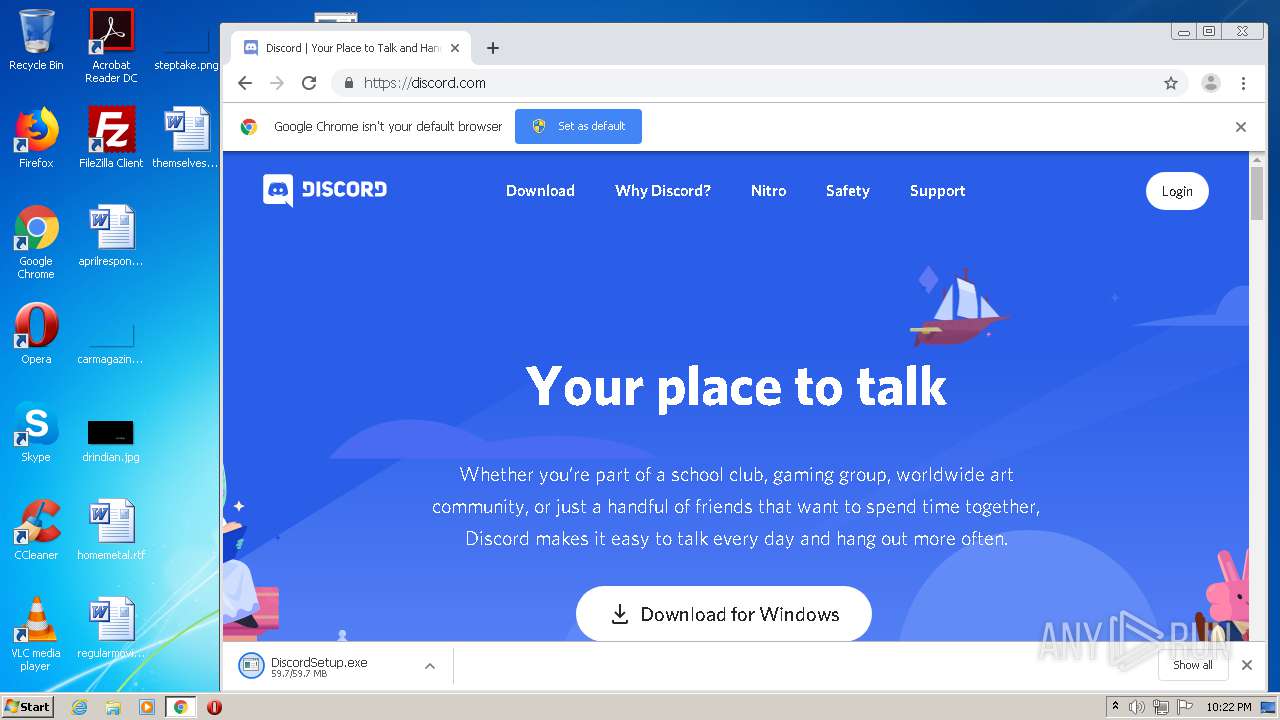
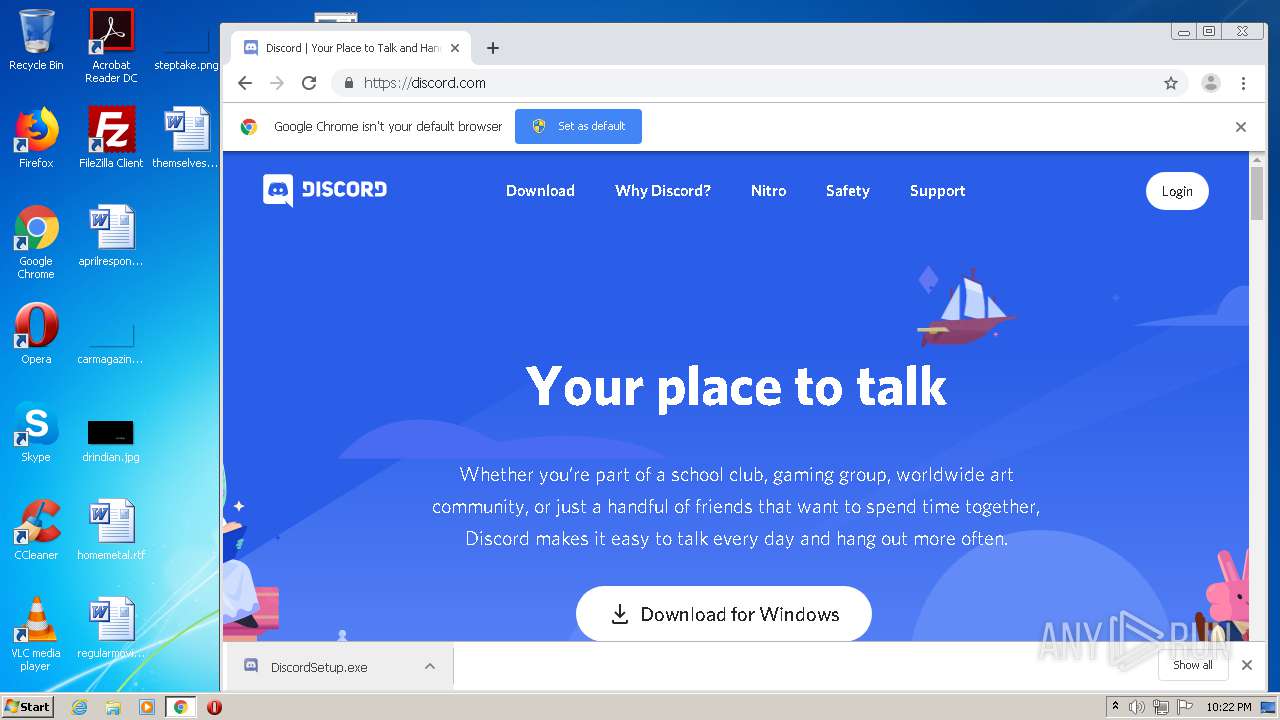
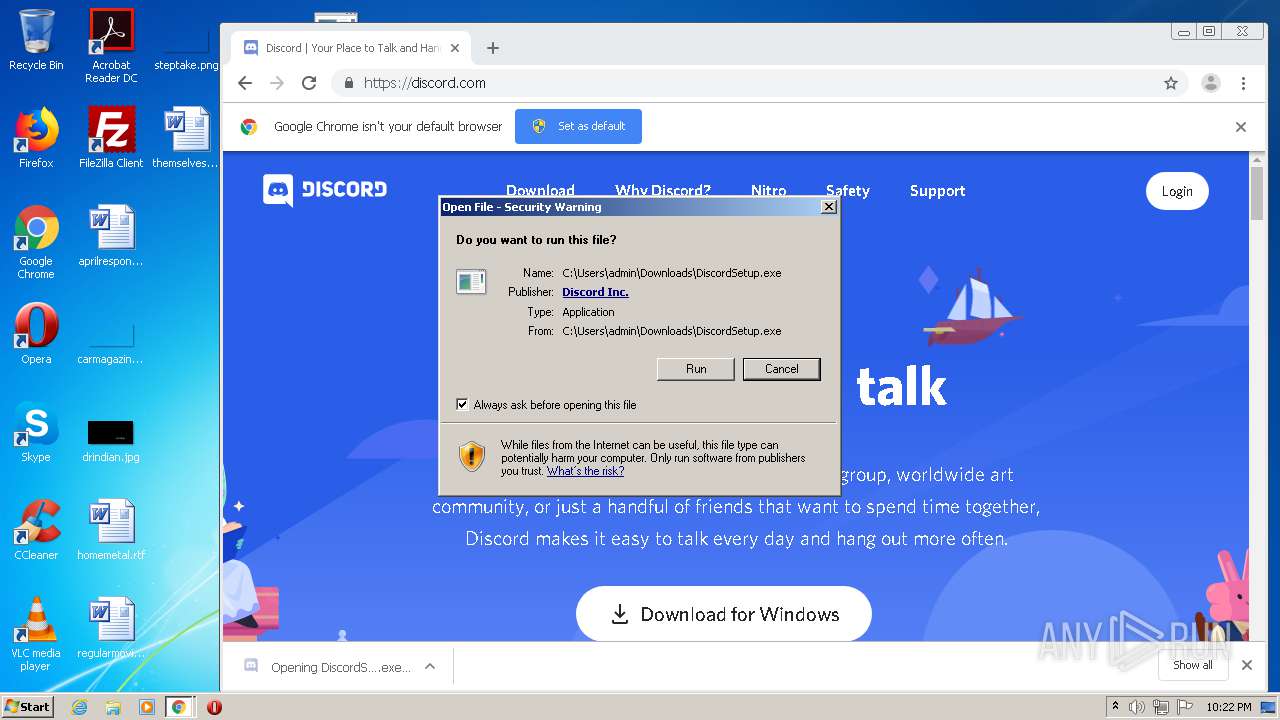
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 217803832E5666E861420DAFE3140068 |
| SHA1: | AF89E2A4F4929048812CA0A7DCB7E0A97E5A19E9 |
| SHA256: | 20494707109C6E177EA43660B9AE06E188B6D804B8C83D8D3639B596D0E4A77A |
| SSDEEP: | 3:N1KJS4w3eGUoR1PSq6MpRjmW0RfA:Cc4w3eG1Yq6MpdmU |
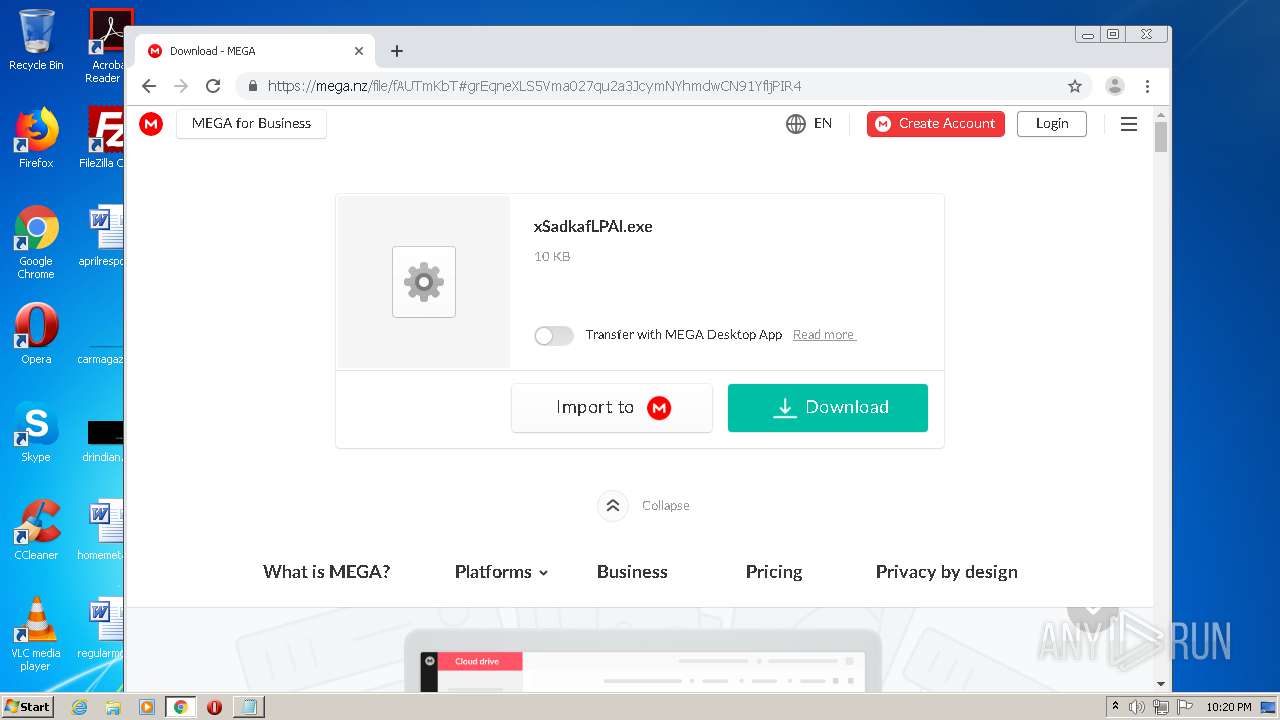
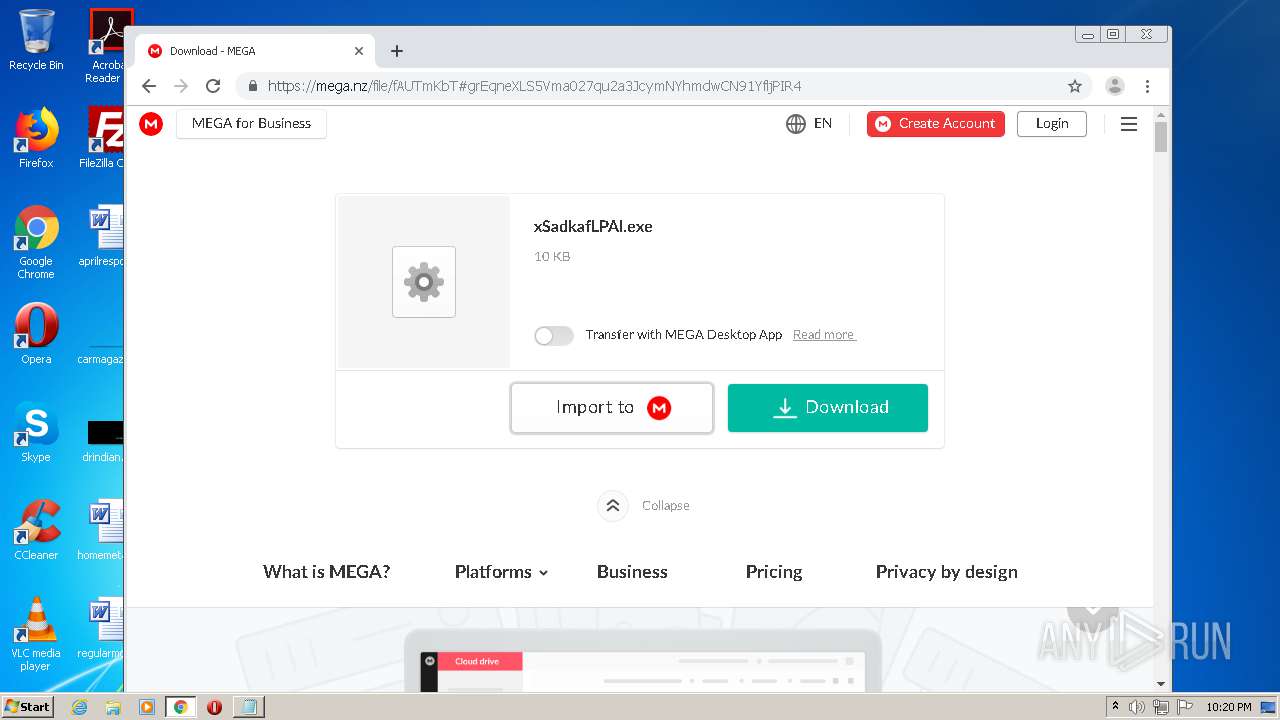
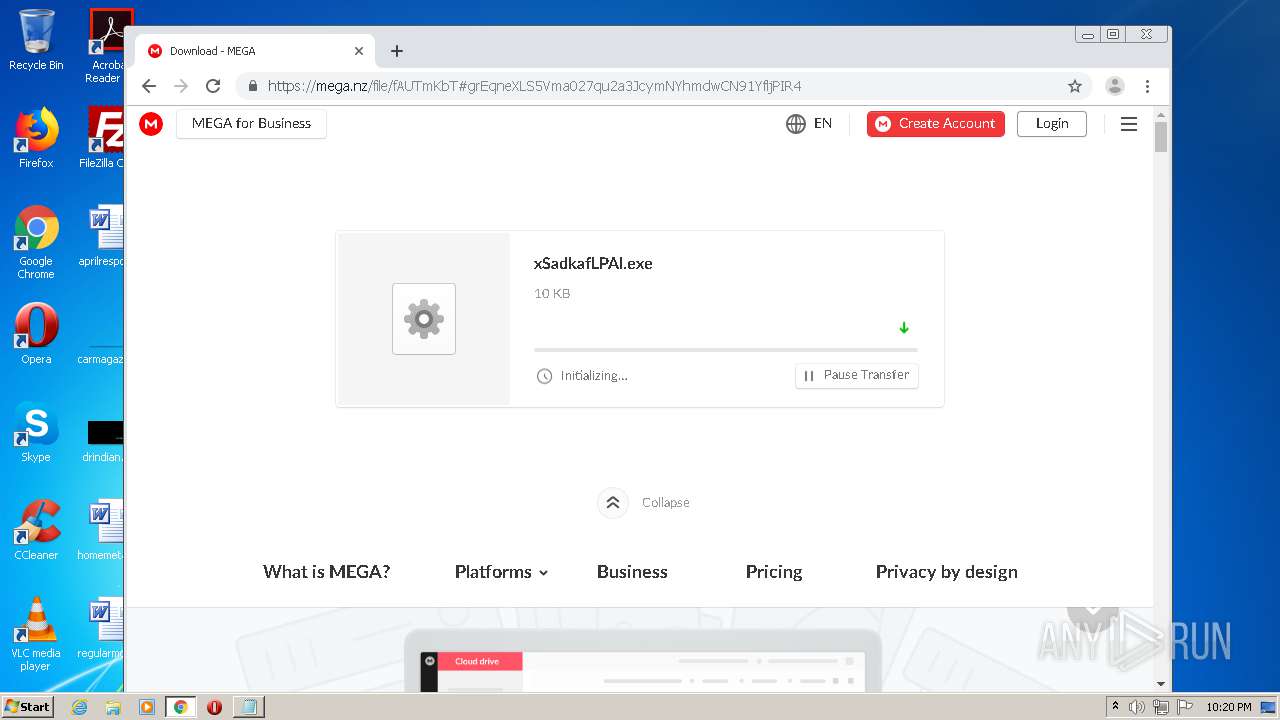
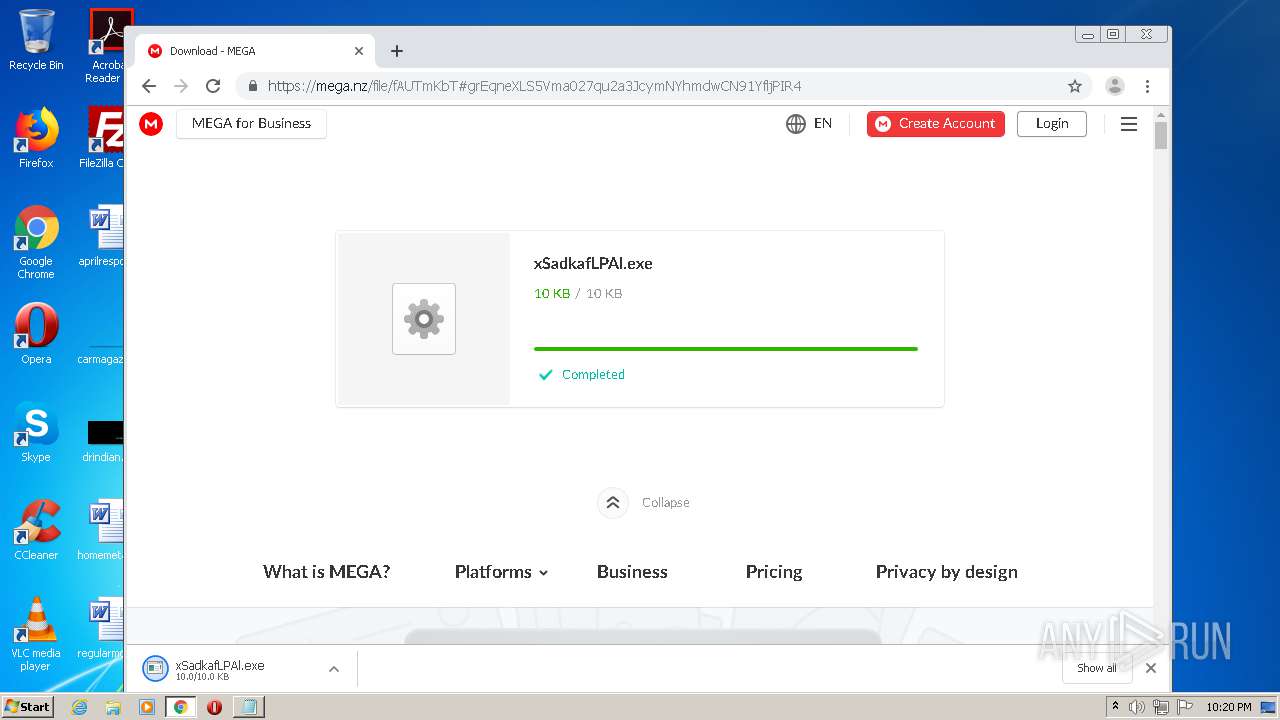
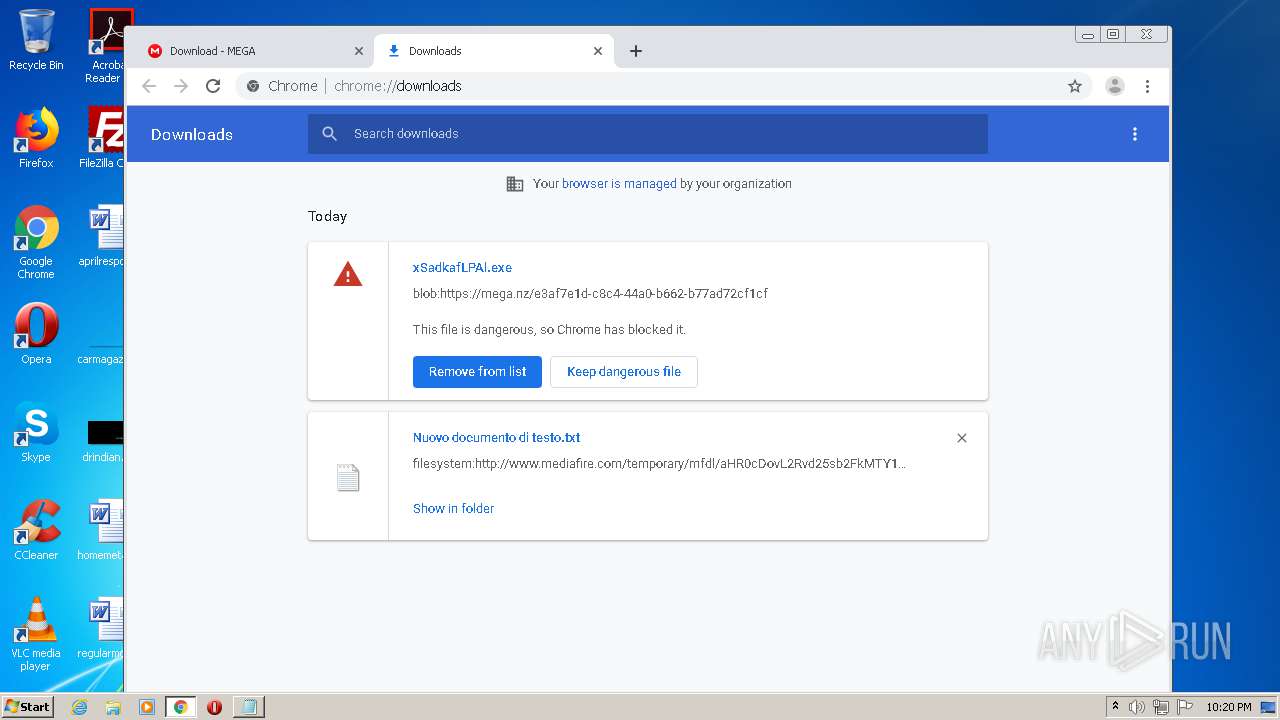
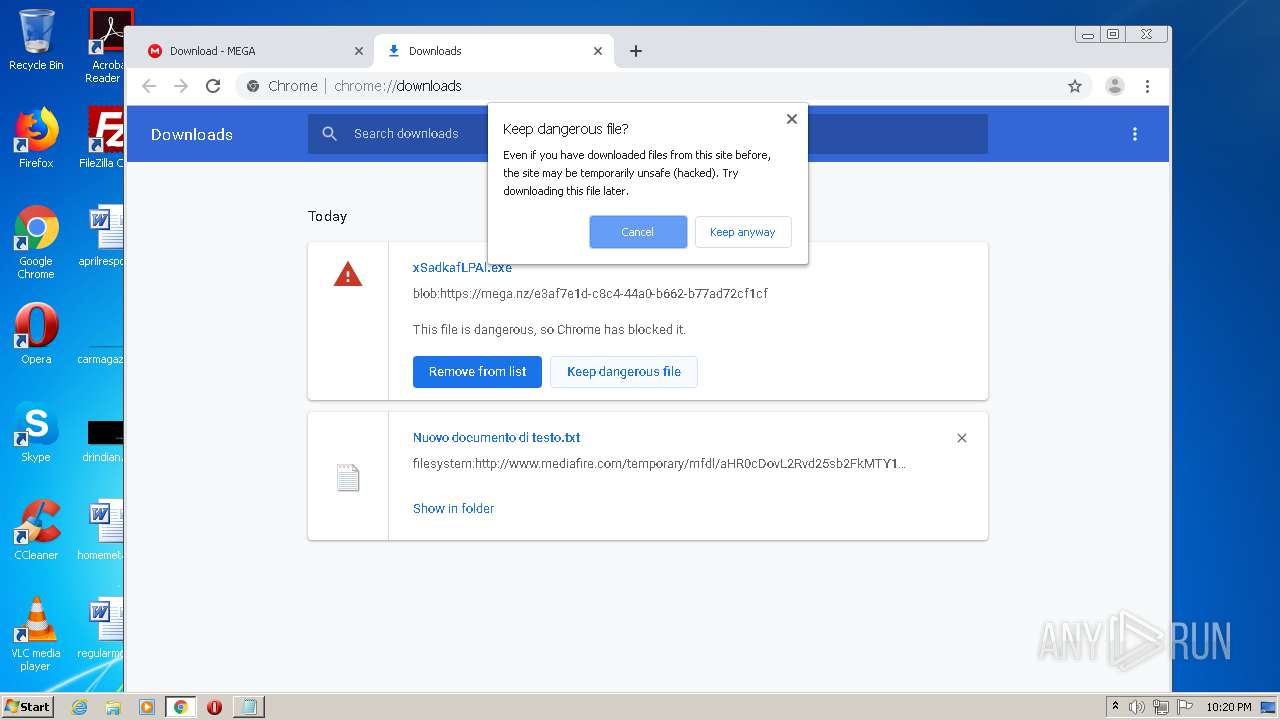
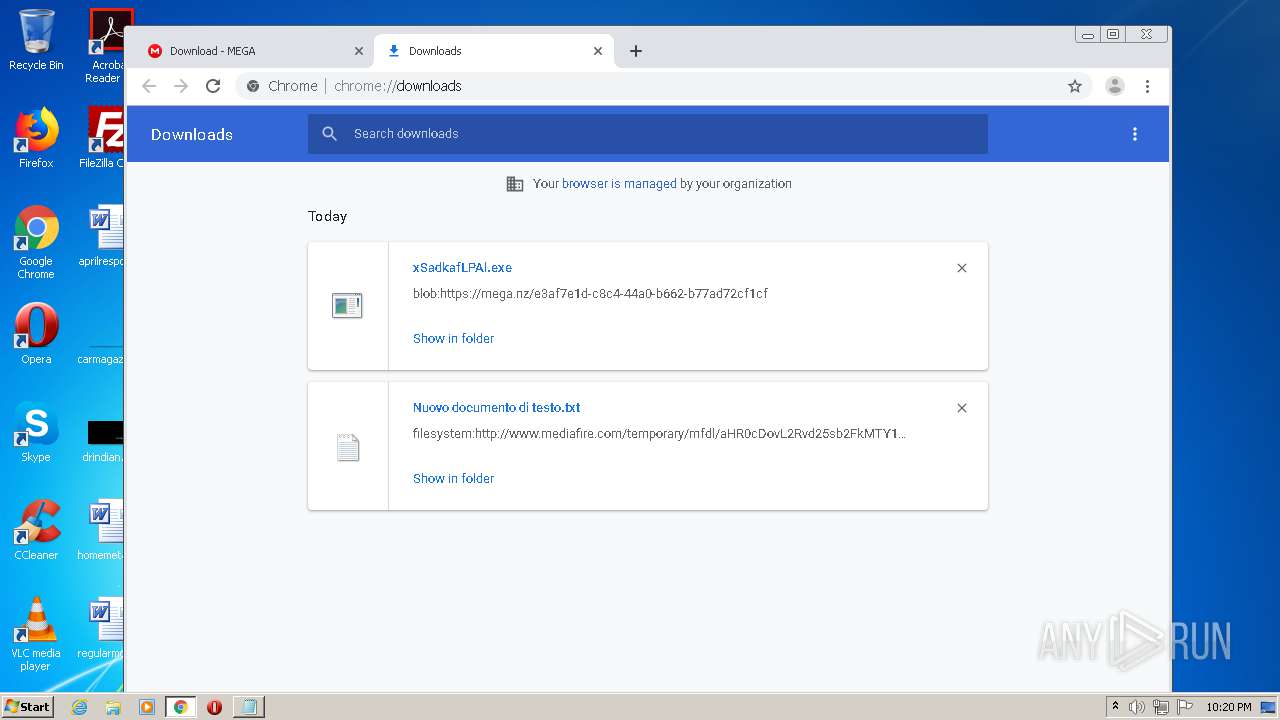
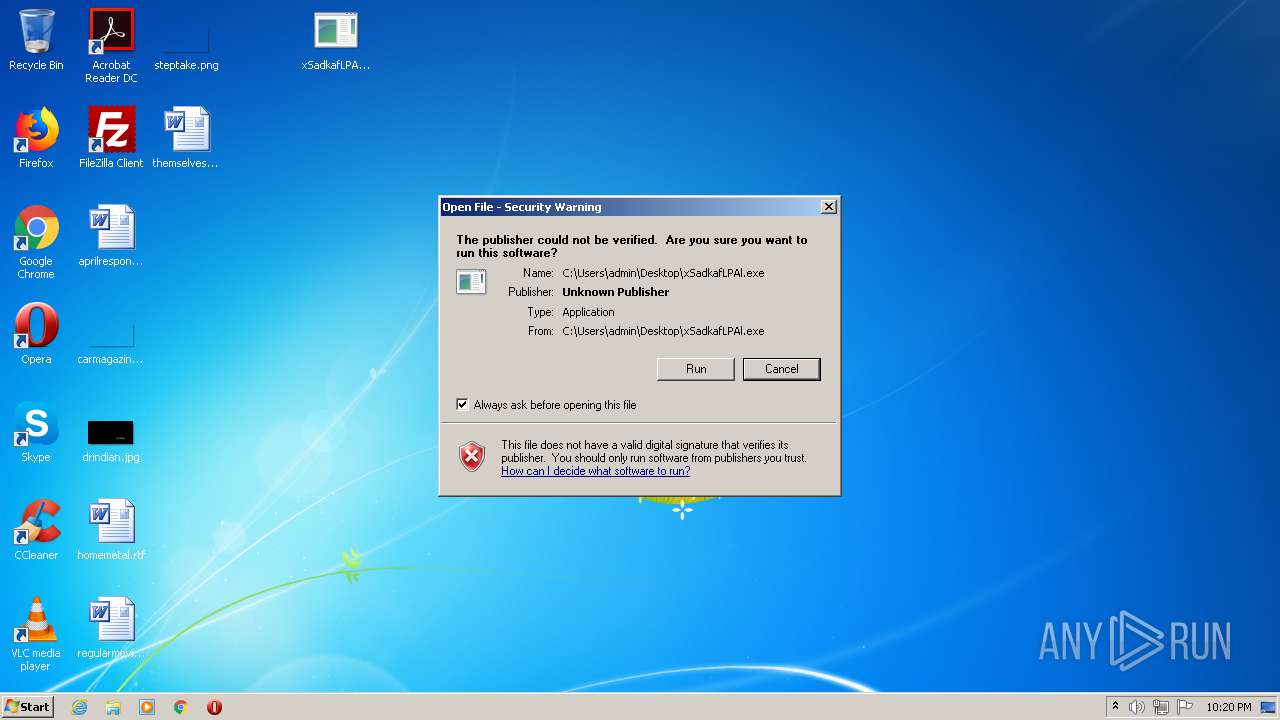
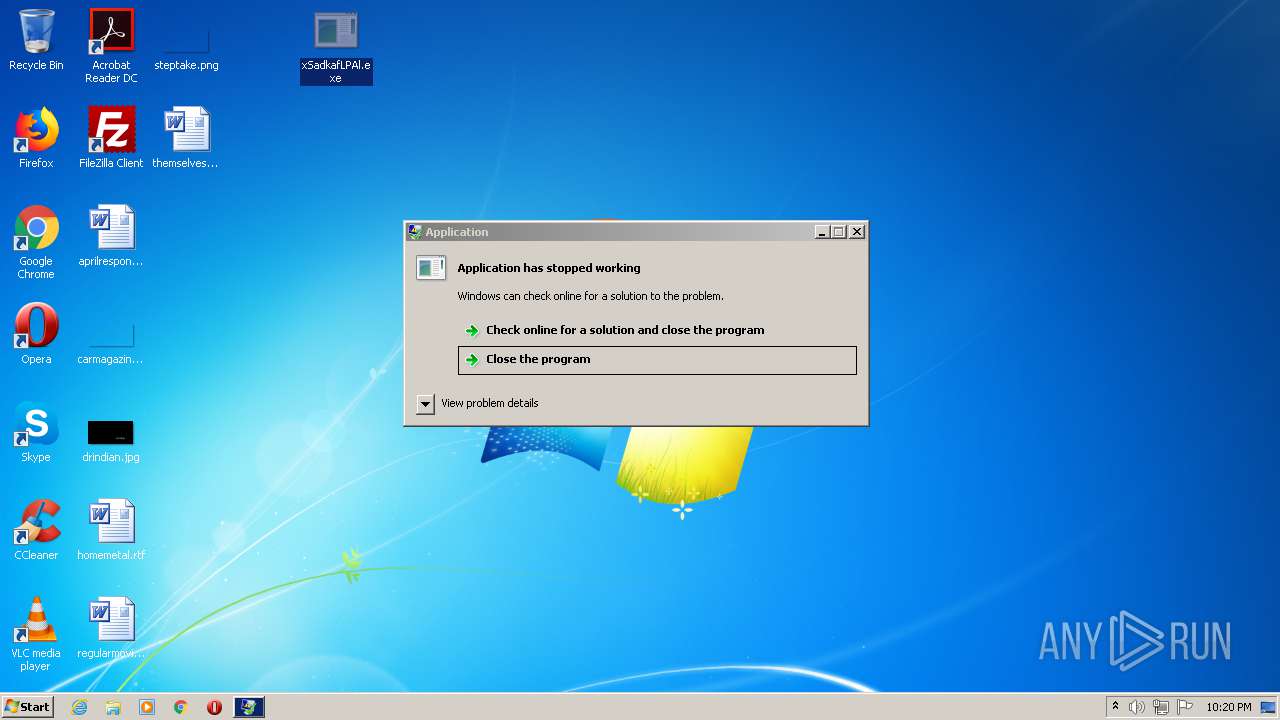
MALICIOUS
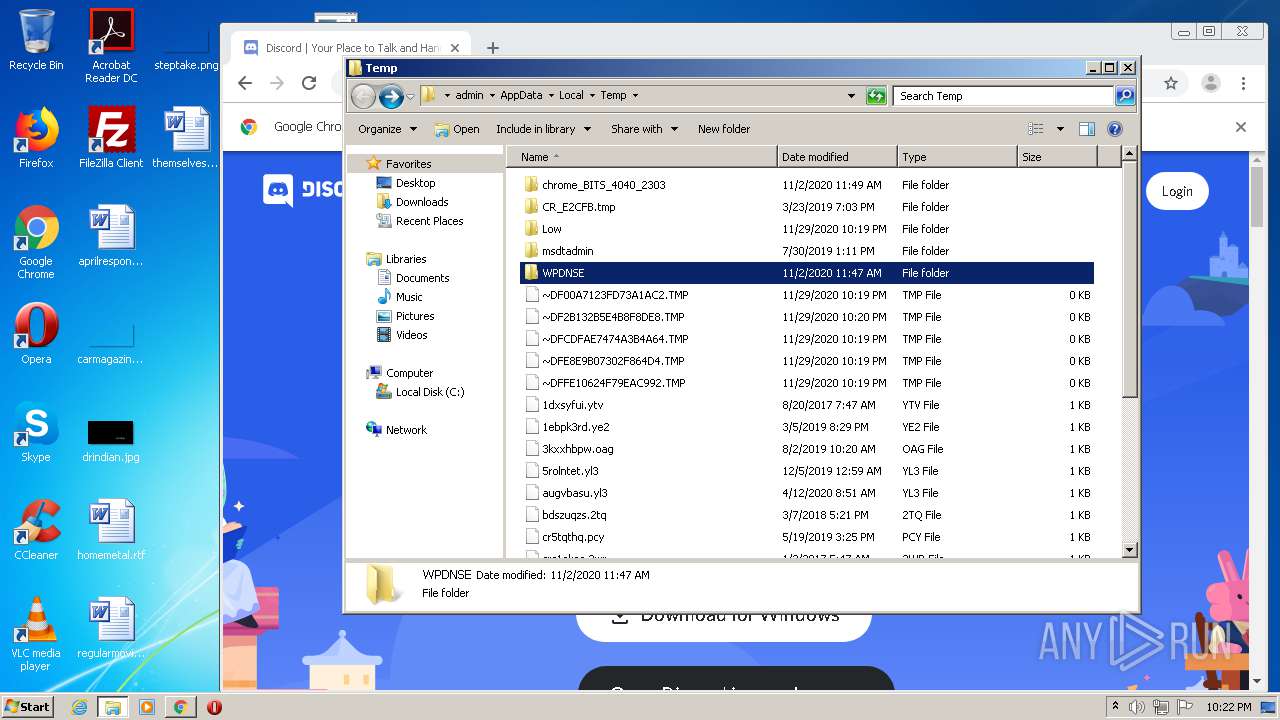
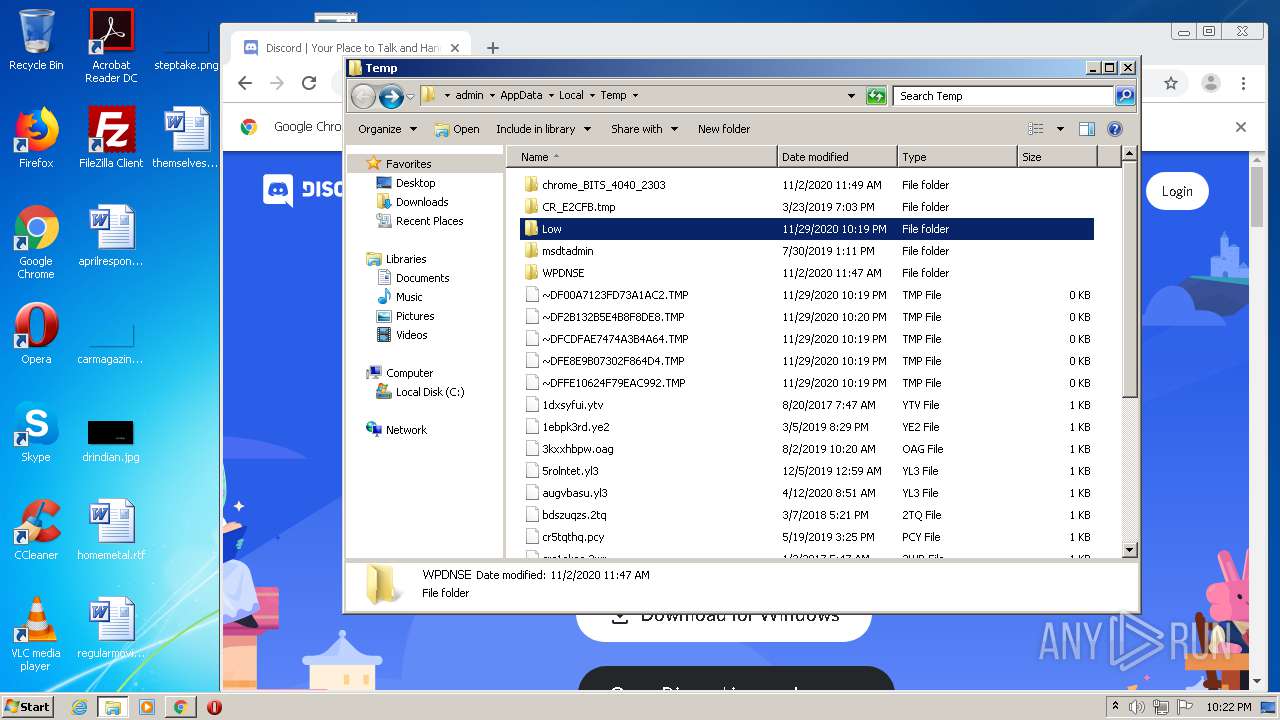
Application was dropped or rewritten from another process
- xSadkafLPAl.exe (PID: 3548)
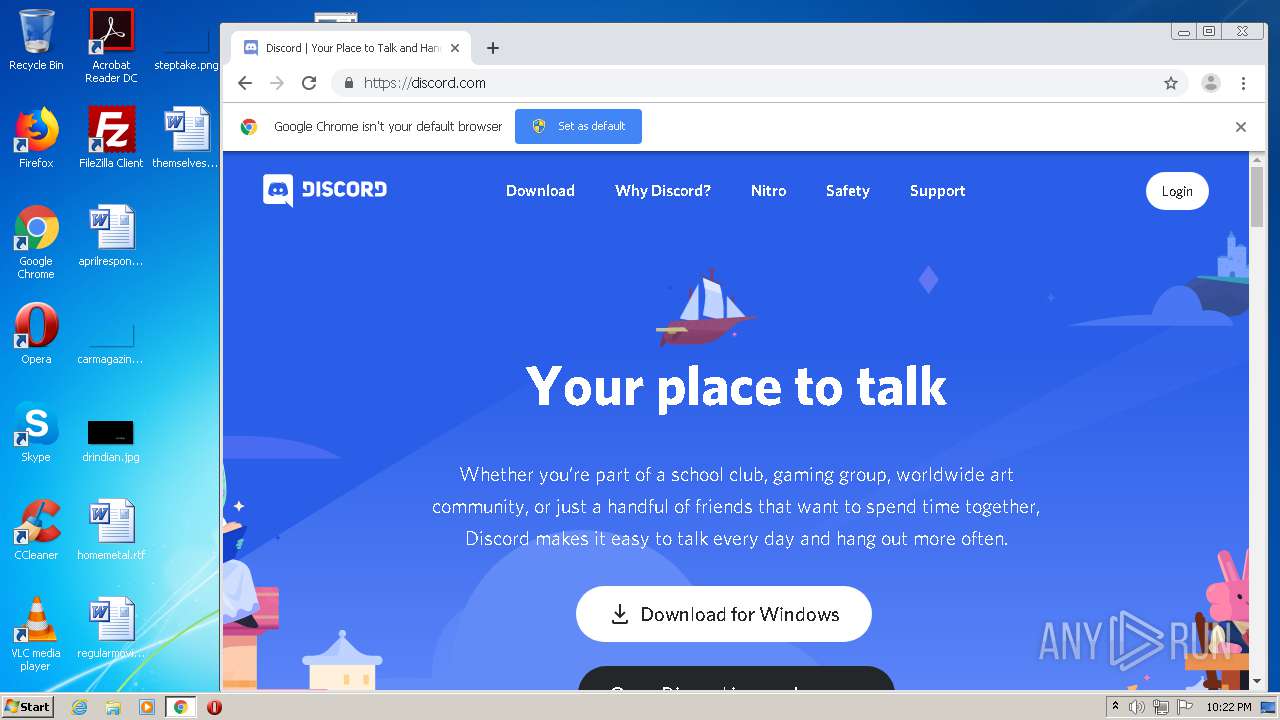
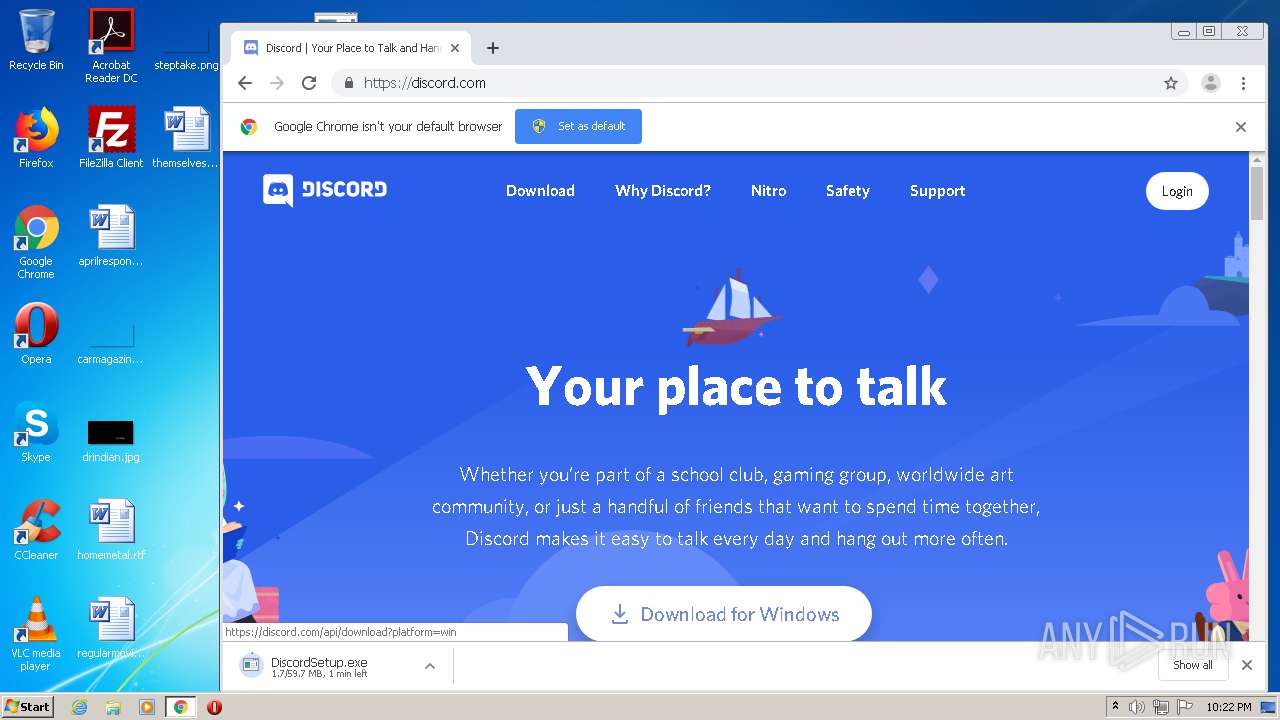
- DiscordSetup.exe (PID: 3348)
- Update.exe (PID: 3632)
- Squirrel.exe (PID: 3764)
- Update.exe (PID: 3104)
- Update.exe (PID: 1564)
- Update.exe (PID: 1328)
- Update.exe (PID: 3436)
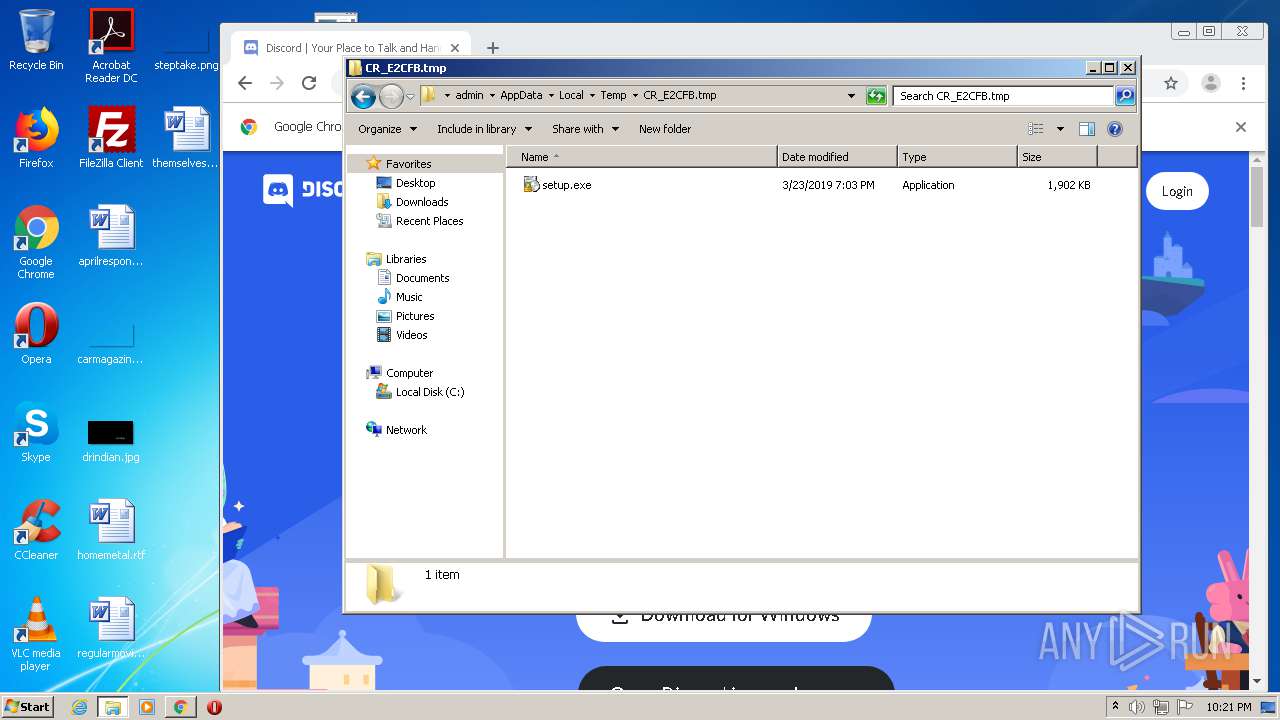
Drops executable file immediately after starts
- Update.exe (PID: 3632)
Loads dropped or rewritten executable
- Discord.exe (PID: 2908)
- Discord.exe (PID: 1152)
- Discord.exe (PID: 3688)
- Discord.exe (PID: 1788)
- Discord.exe (PID: 3576)
- Discord.exe (PID: 2724)
- Discord.exe (PID: 3516)
- Discord.exe (PID: 980)
- Discord.exe (PID: 2484)
- Discord.exe (PID: 620)
- Discord.exe (PID: 3020)
- Discord.exe (PID: 3208)
- Discord.exe (PID: 3228)
- Discord.exe (PID: 1792)
- Discord.exe (PID: 3388)
- Discord.exe (PID: 3708)
Changes the autorun value in the registry
- reg.exe (PID: 1908)
SUSPICIOUS
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2996)
- chrome.exe (PID: 3048)
- Update.exe (PID: 3632)
- Discord.exe (PID: 1788)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2996)
Drops a file with a compile date too recent
- chrome.exe (PID: 2996)
- Update.exe (PID: 3632)
- Discord.exe (PID: 1788)
Executable content was dropped or overwritten
- chrome.exe (PID: 2996)
- chrome.exe (PID: 3048)
- DiscordSetup.exe (PID: 3348)
- Update.exe (PID: 3632)
- Discord.exe (PID: 1788)
Executed via COM
- DllHost.exe (PID: 3736)
Starts itself from another location
- Update.exe (PID: 3632)
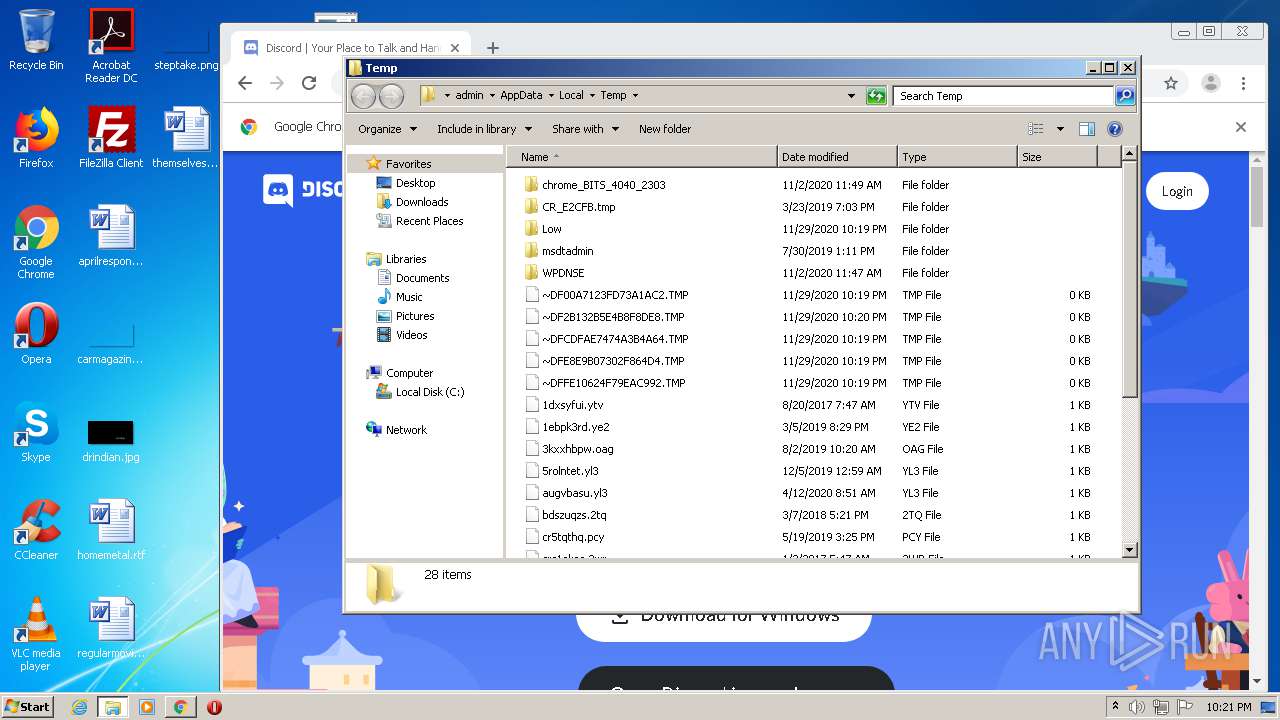
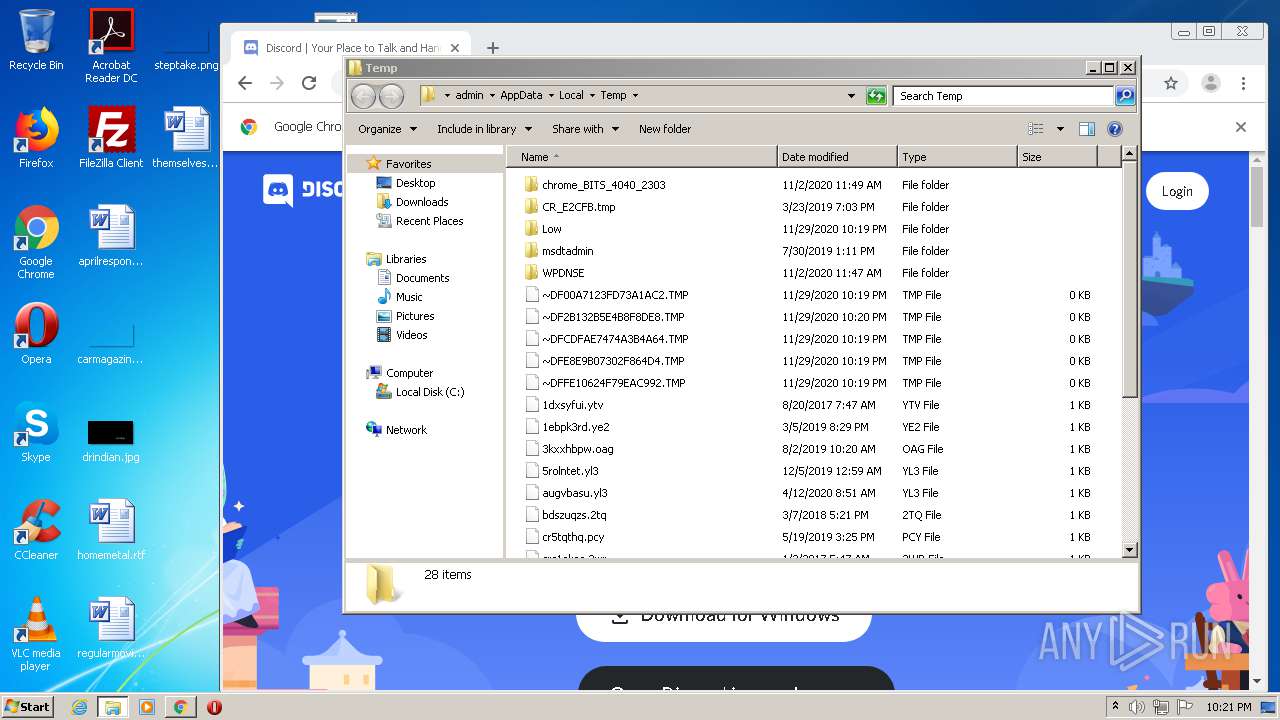
Creates files in the user directory
- Discord.exe (PID: 2908)
- Update.exe (PID: 3104)
- Discord.exe (PID: 1788)
- Discord.exe (PID: 620)
Application launched itself
- Discord.exe (PID: 2908)
- Discord.exe (PID: 1788)
- Discord.exe (PID: 3516)
Uses REG.EXE to modify Windows registry
- Discord.exe (PID: 2908)
Modifies the open verb of a shell class
- reg.exe (PID: 852)
Creates a software uninstall entry
- Update.exe (PID: 3632)
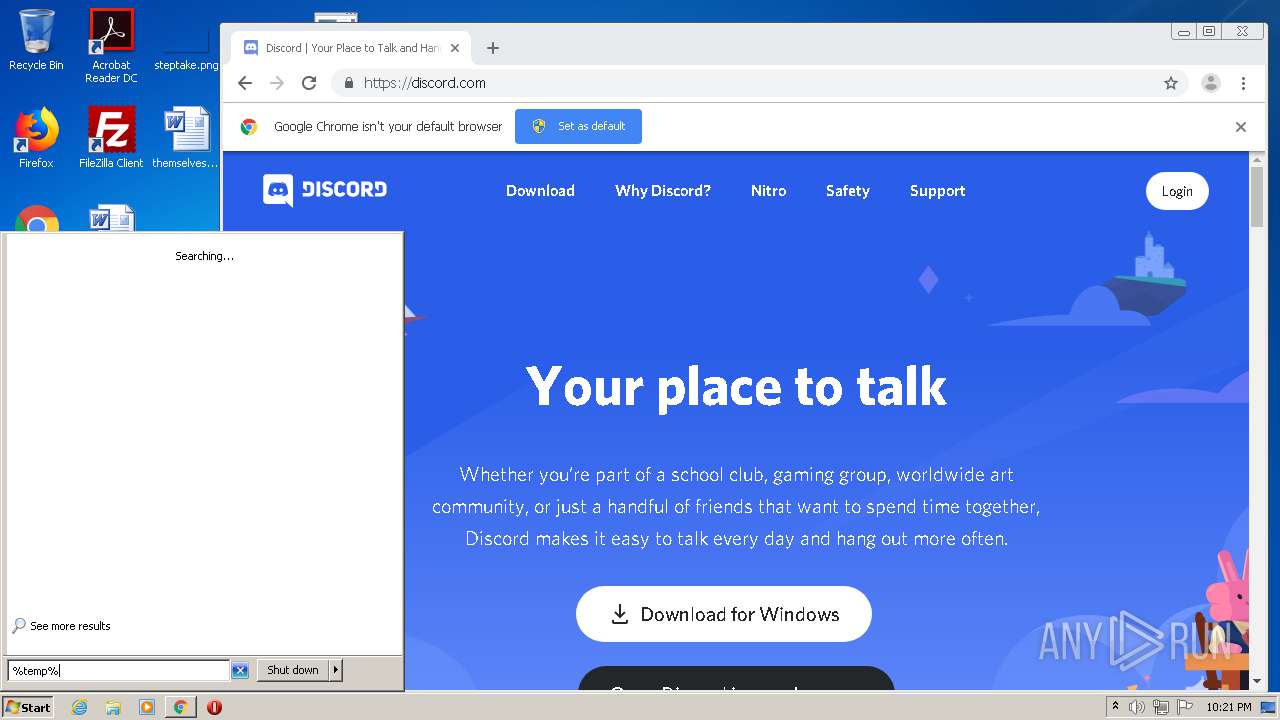
Reads Environment values
- Update.exe (PID: 1328)
- Update.exe (PID: 3436)
Starts CMD.EXE for commands execution
- Discord.exe (PID: 1792)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2592)
Reads internet explorer settings
- iexplore.exe (PID: 1796)
Application launched itself
- iexplore.exe (PID: 2592)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 3048)
Creates files in the user directory
- iexplore.exe (PID: 1796)
- iexplore.exe (PID: 2592)
Reads settings of System Certificates
- iexplore.exe (PID: 1796)
- iexplore.exe (PID: 2592)
- chrome.exe (PID: 3048)
Changes settings of System certificates
- iexplore.exe (PID: 2592)
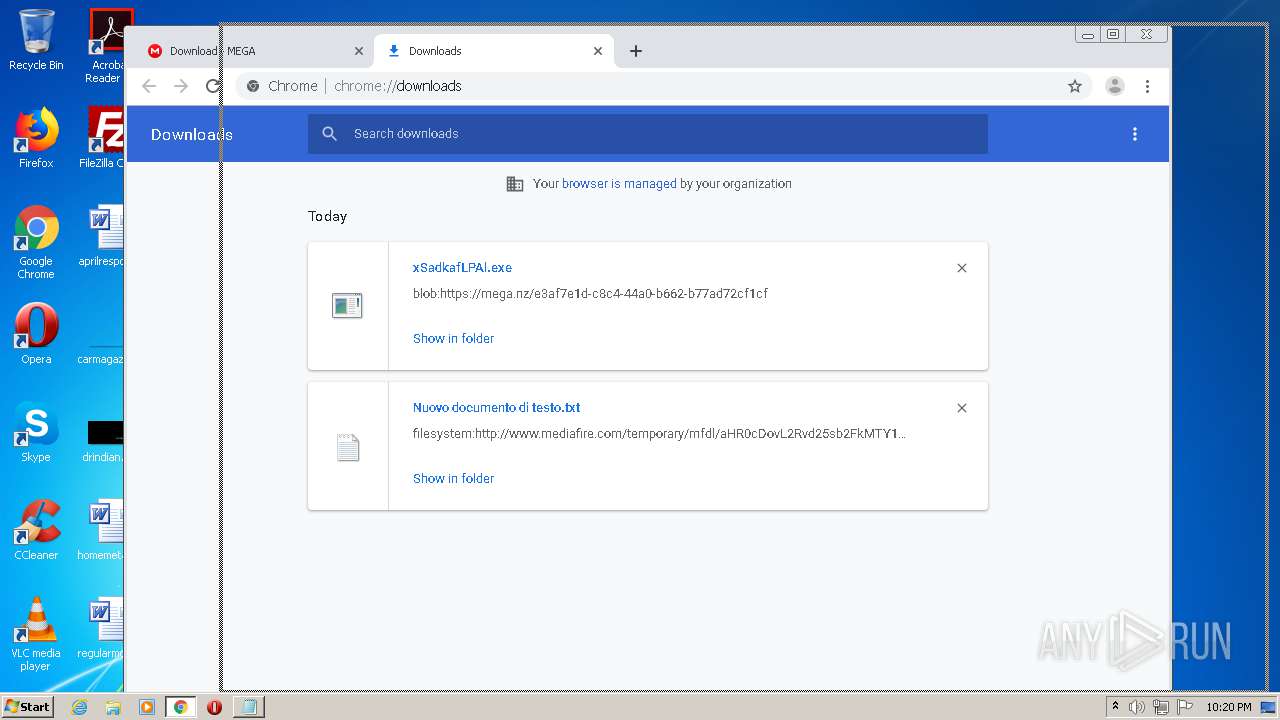
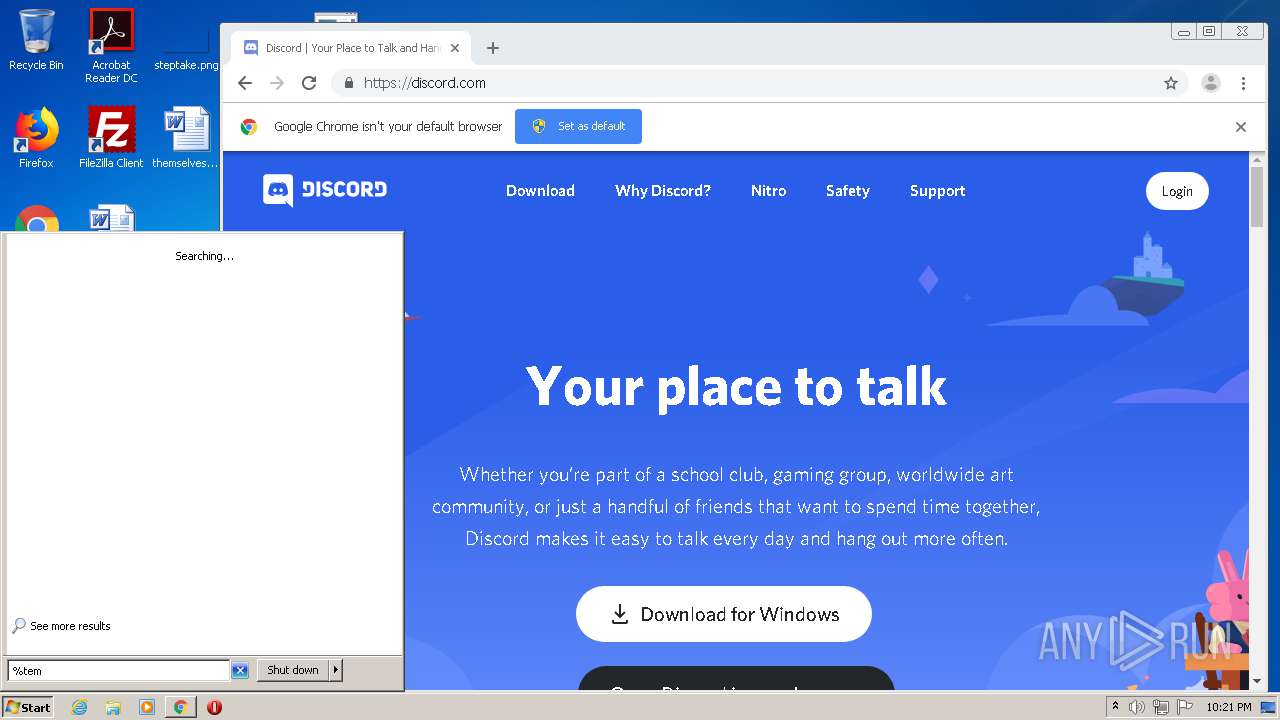
Manual execution by user
- chrome.exe (PID: 2996)
- xSadkafLPAl.exe (PID: 3548)
- chrome.exe (PID: 3048)
- verclsid.exe (PID: 3668)
- Update.exe (PID: 1564)
Reads the hosts file
- chrome.exe (PID: 1700)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 3012)
- Discord.exe (PID: 2908)
- Discord.exe (PID: 3688)
- Discord.exe (PID: 620)
- Discord.exe (PID: 3516)
- Discord.exe (PID: 1788)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2592)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2996)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
101
Malicious processes
9
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1940849587793134589,14779519805004638824,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3944112432683775438 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,1940849587793134589,14779519805004638824,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1951844588688371354 --mojo-platform-channel-handle=2532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
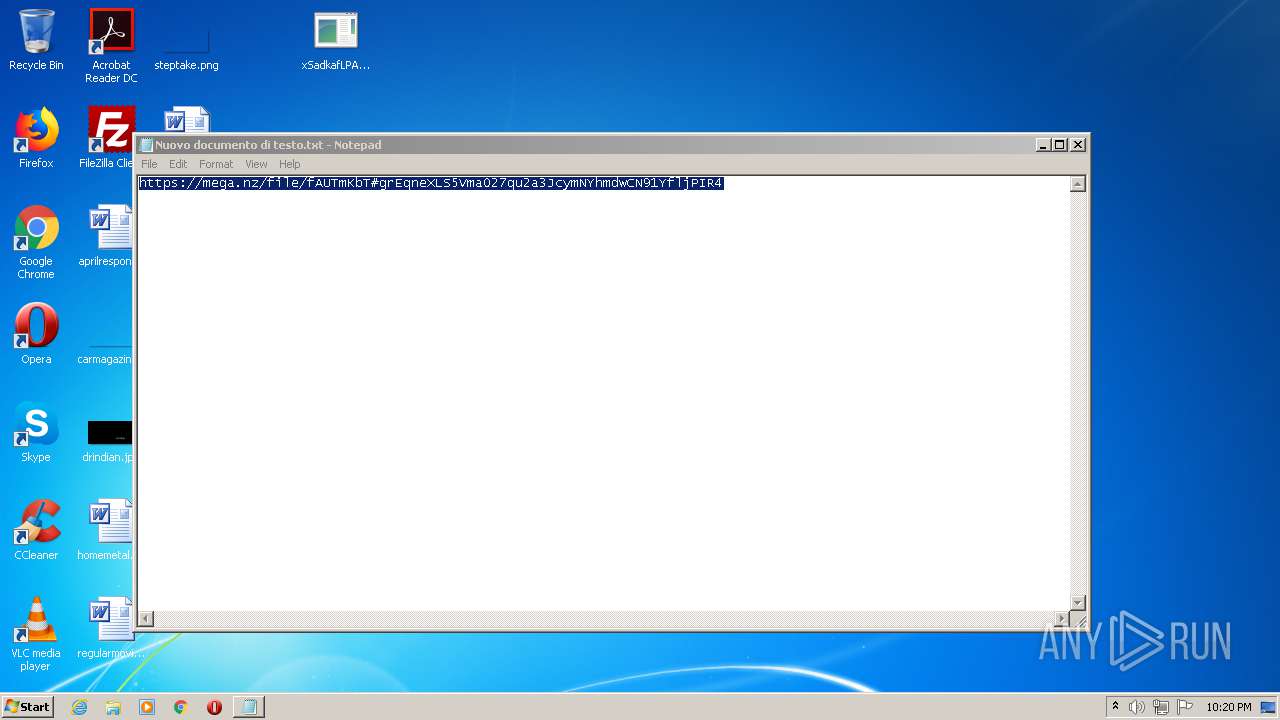
| 384 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\Nuovo documento di testo.txt | C:\Windows\system32\NOTEPAD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8744333202472194093,15836194675246238821,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15557207531621667451 --mojo-platform-channel-handle=4256 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | C:\Windows\System32\reg.exe add HKCU\Software\Classes\Discord /ve /d "URL:Discord Protocol" /f | C:\Windows\System32\reg.exe | — | Discord.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 620 | "C:\Users\admin\AppData\Local\Discord\app-0.0.308\Discord.exe" --type=utility --field-trial-handle=1052,2734229037090498247,9513519964586113635,131072 --disable-features=SpareRendererForSitePerProcess --lang=en-US --service-sandbox-type=network --service-request-channel-token=6535486337732550697 --mojo-platform-channel-handle=1424 /prefetch:8 | C:\Users\admin\AppData\Local\Discord\app-0.0.308\Discord.exe | Discord.exe | ||||||||||||
User: admin Company: Discord Inc. Integrity Level: MEDIUM Description: Discord Exit code: 0 Version: 0.0.308 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8744333202472194093,15836194675246238821,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4958465863117353136 --mojo-platform-channel-handle=3376 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8744333202472194093,15836194675246238821,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17408252457631209938 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8744333202472194093,15836194675246238821,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8413193205741709069 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,1940849587793134589,14779519805004638824,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10562041757467211872 --mojo-platform-channel-handle=1888 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 122
Read events
3 664
Write events
447
Delete events
11
Modification events
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3293166560 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30852765 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
27
Suspicious files
338
Text files
1 835
Unknown types
138
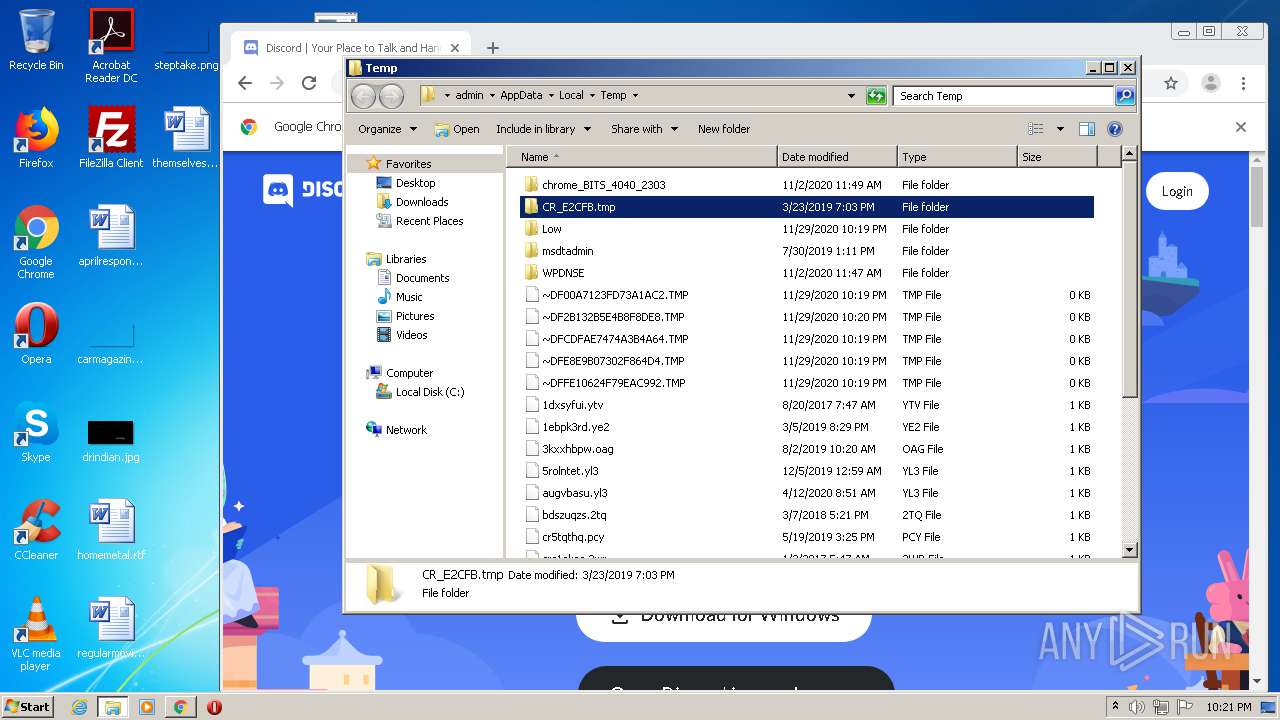
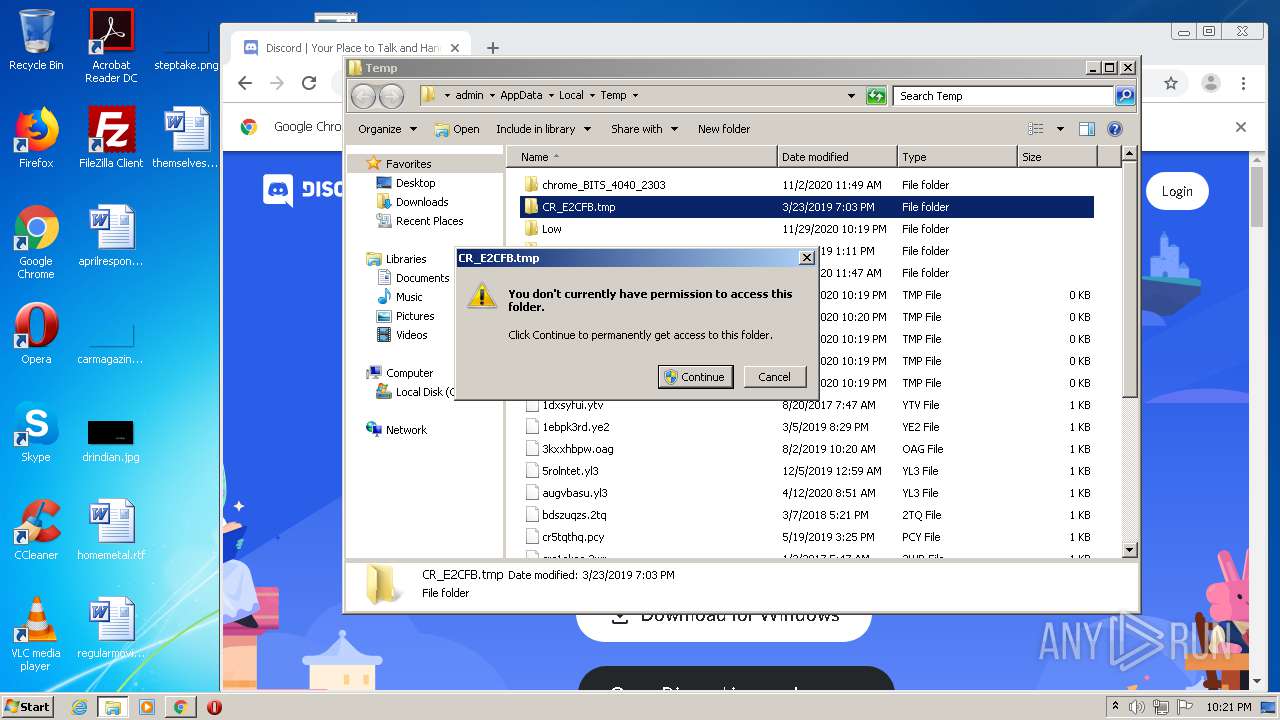
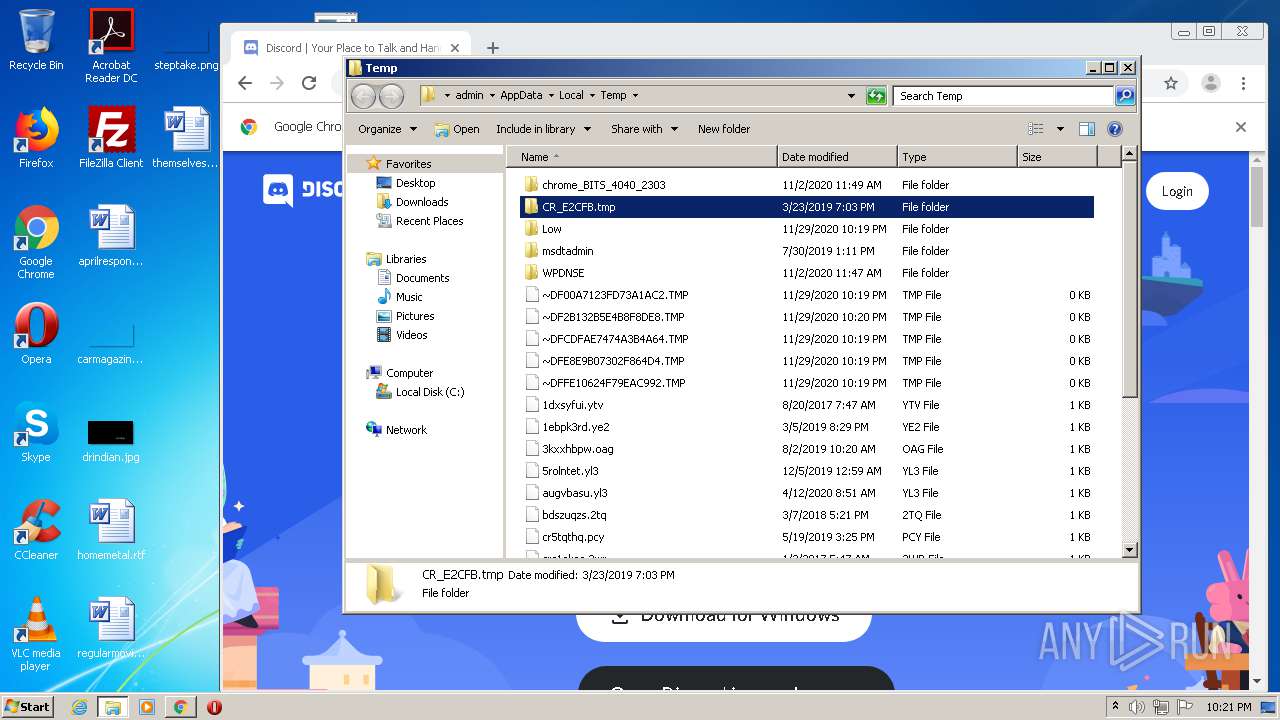
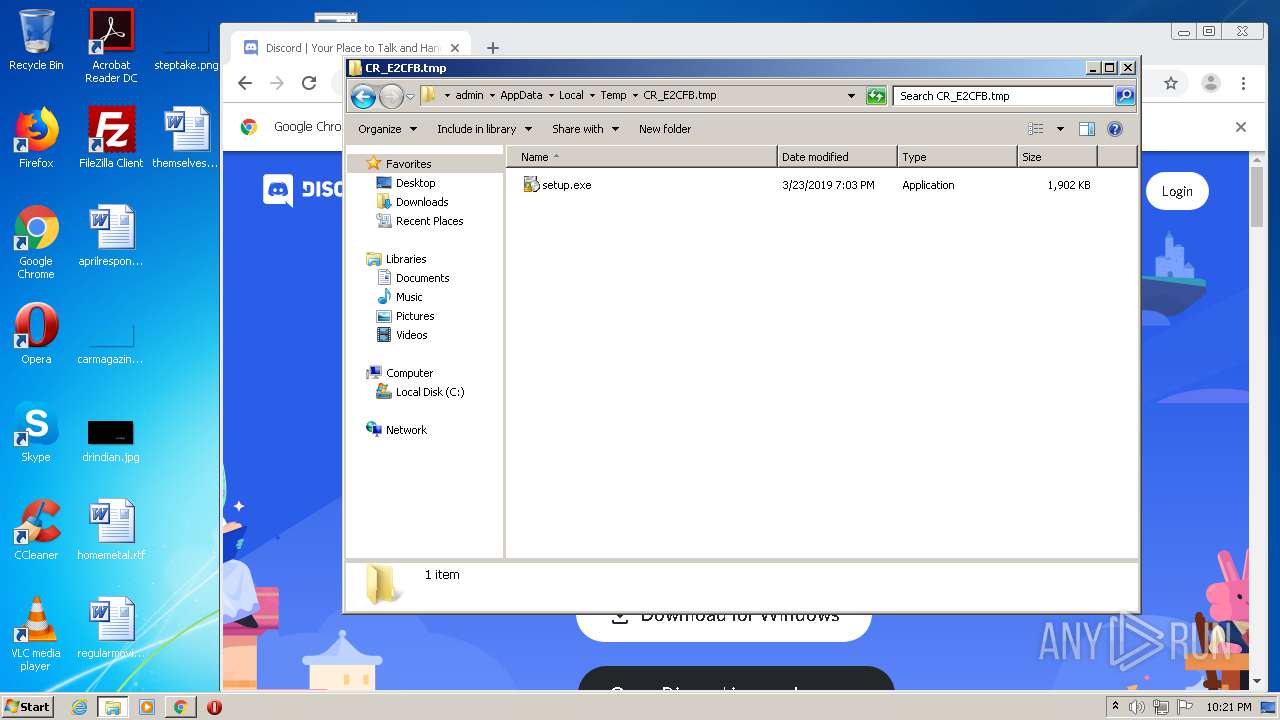
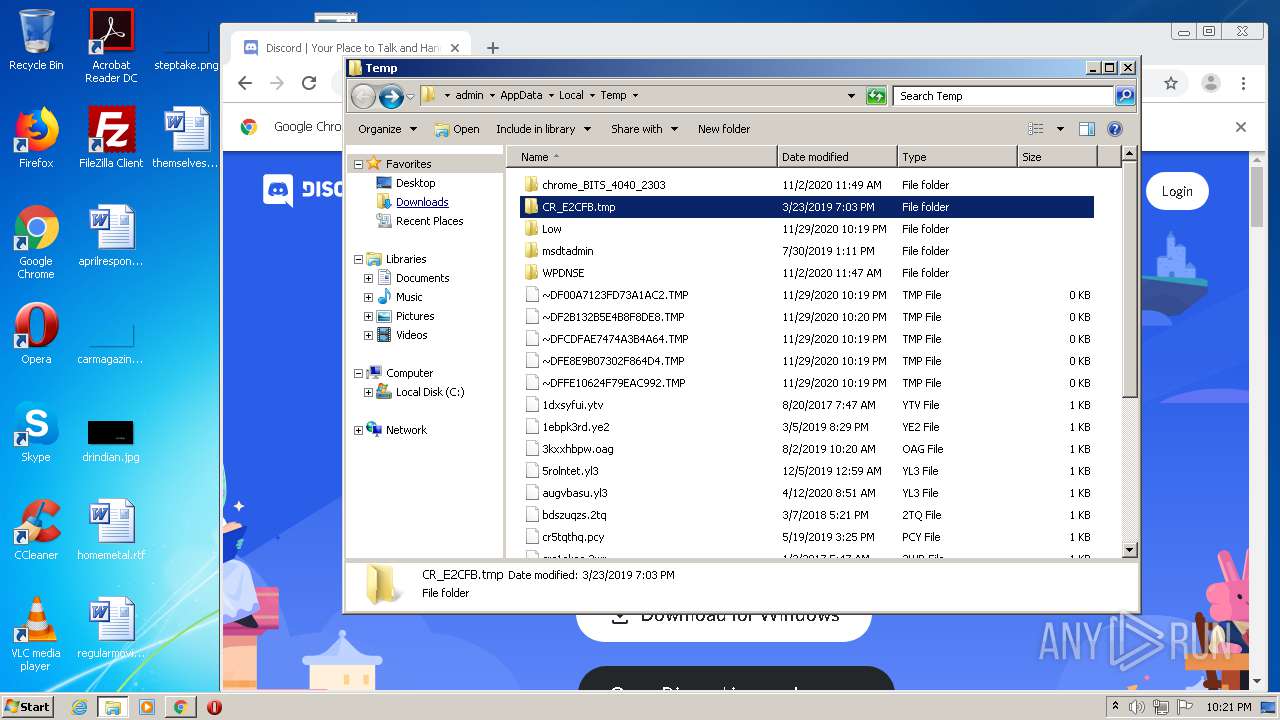
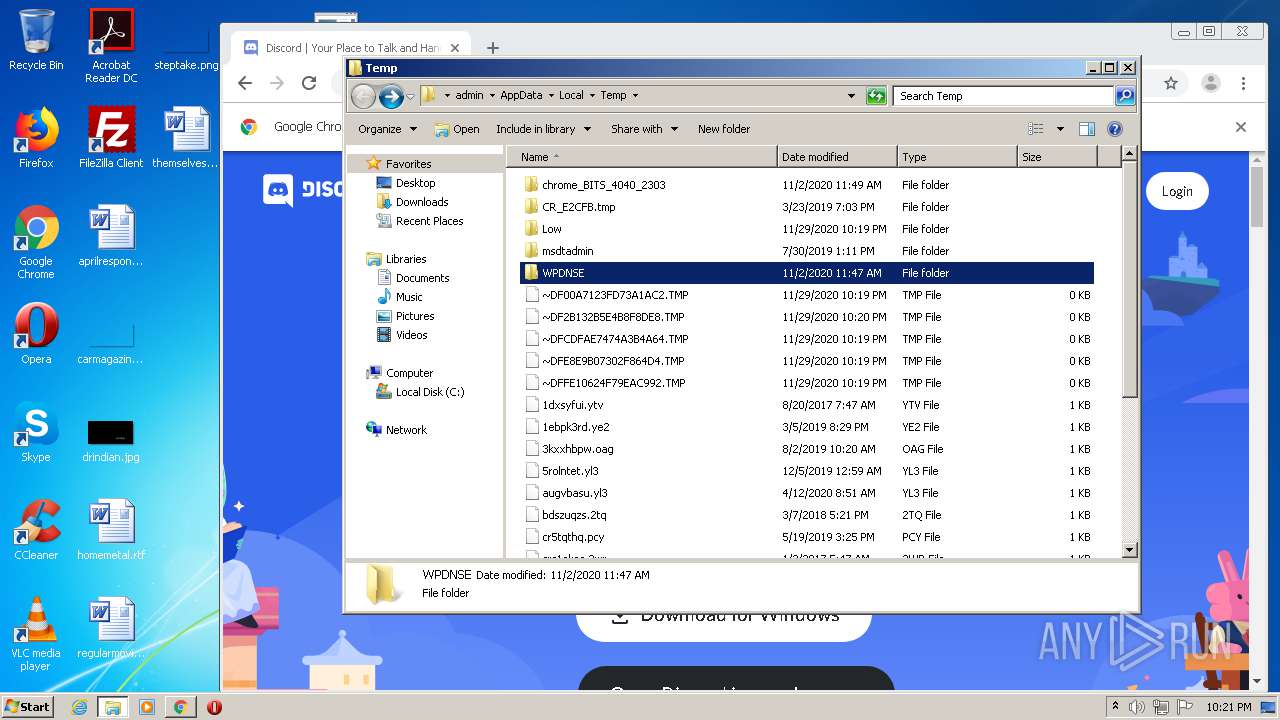
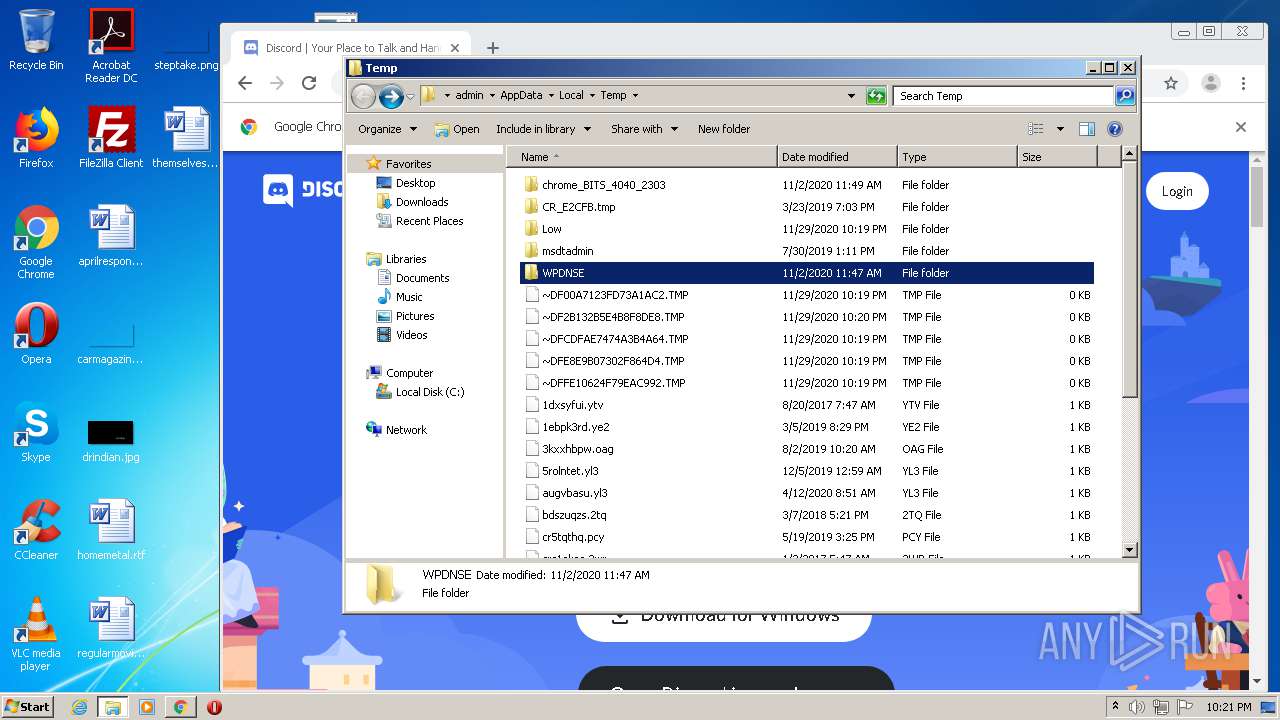
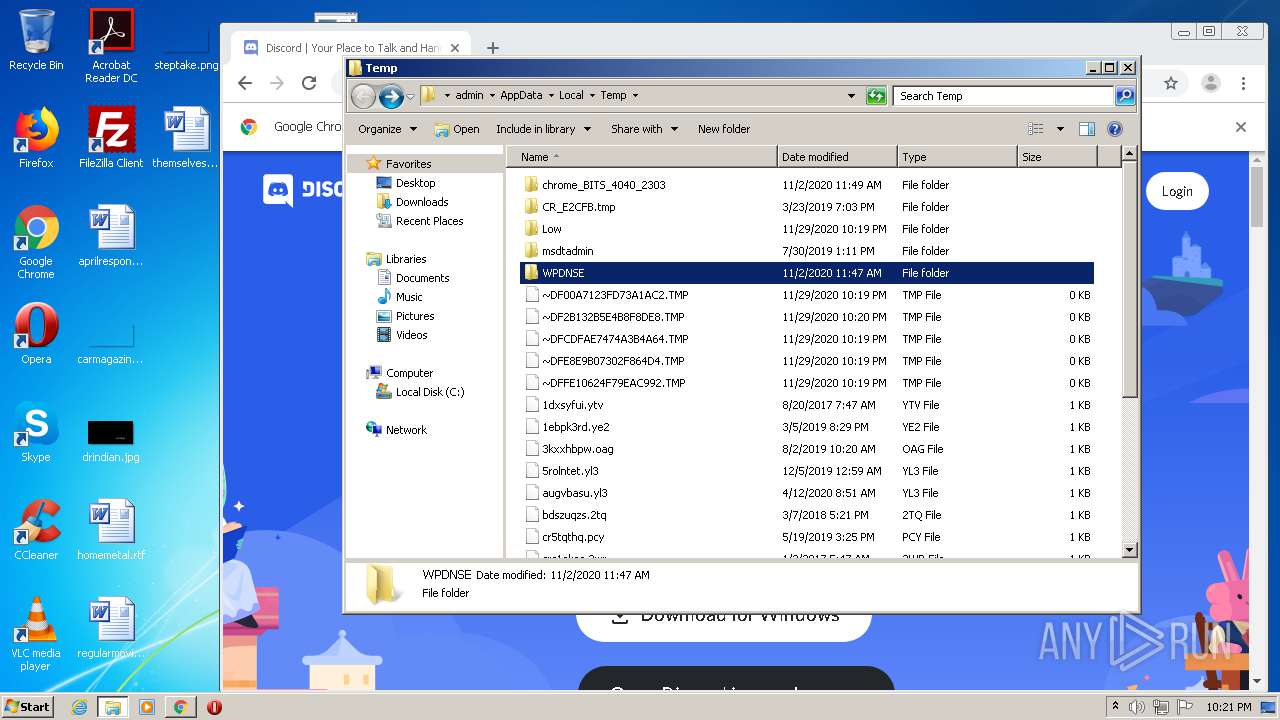
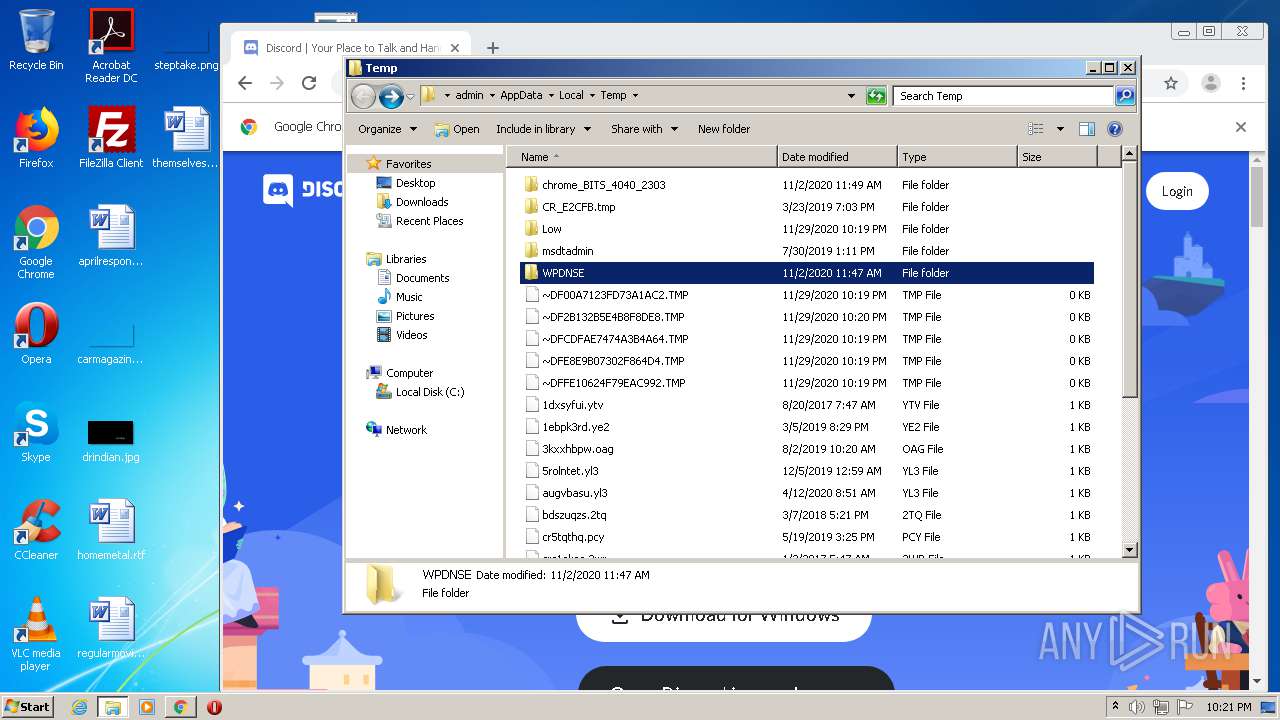
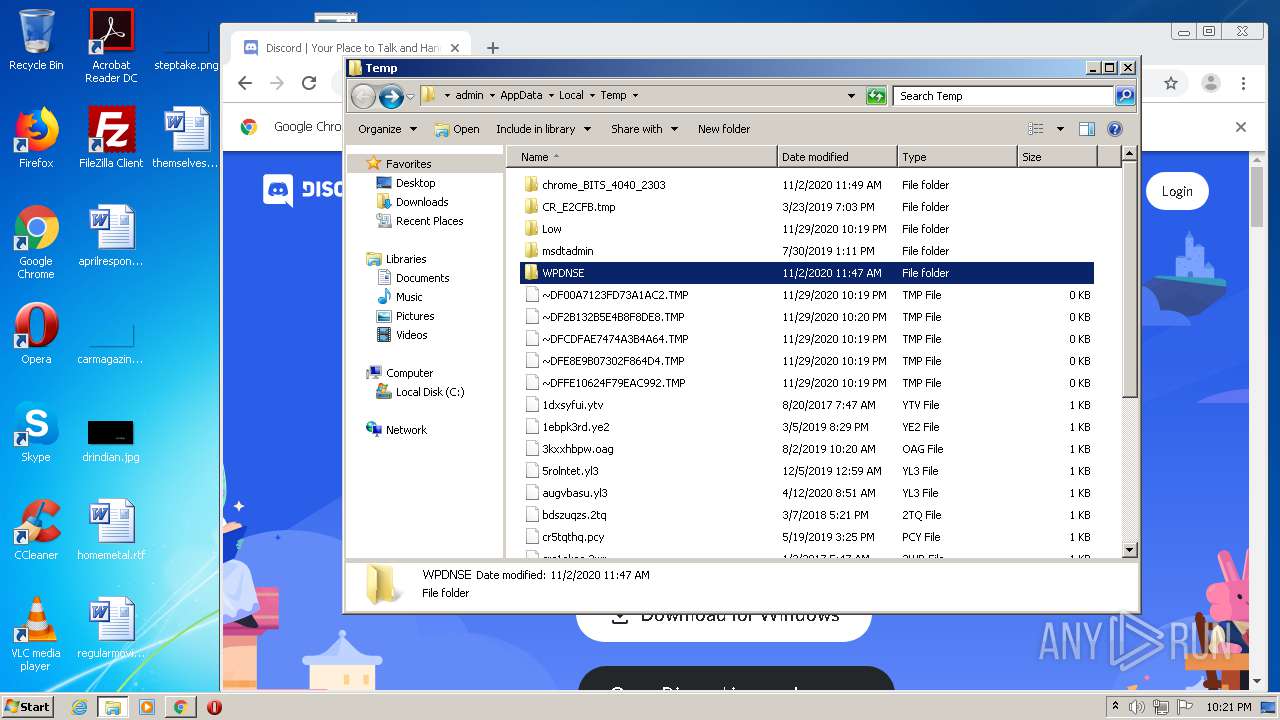
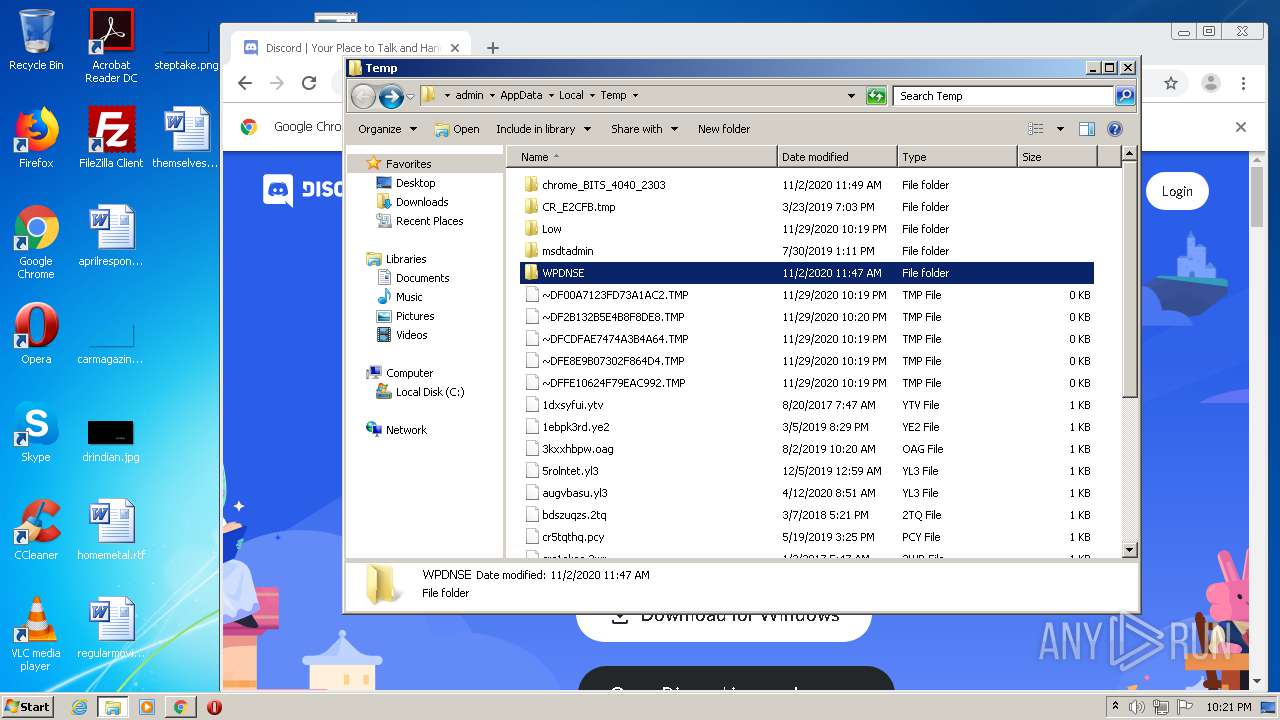
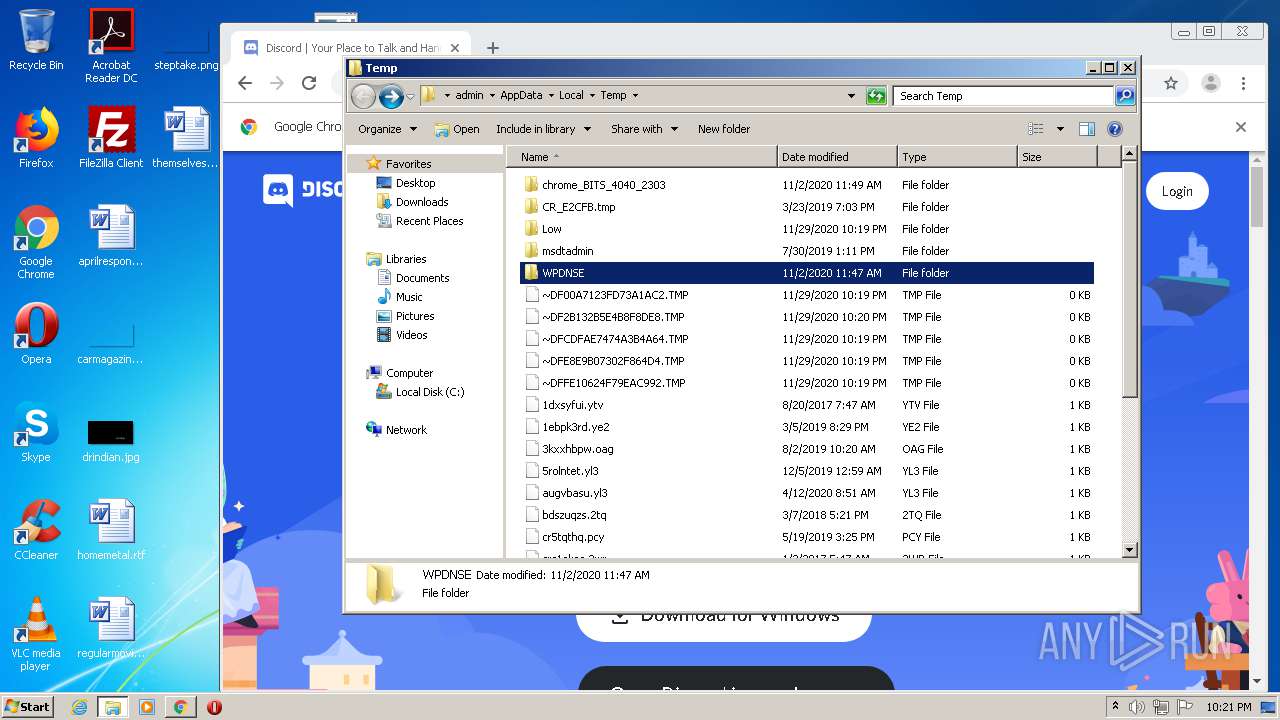
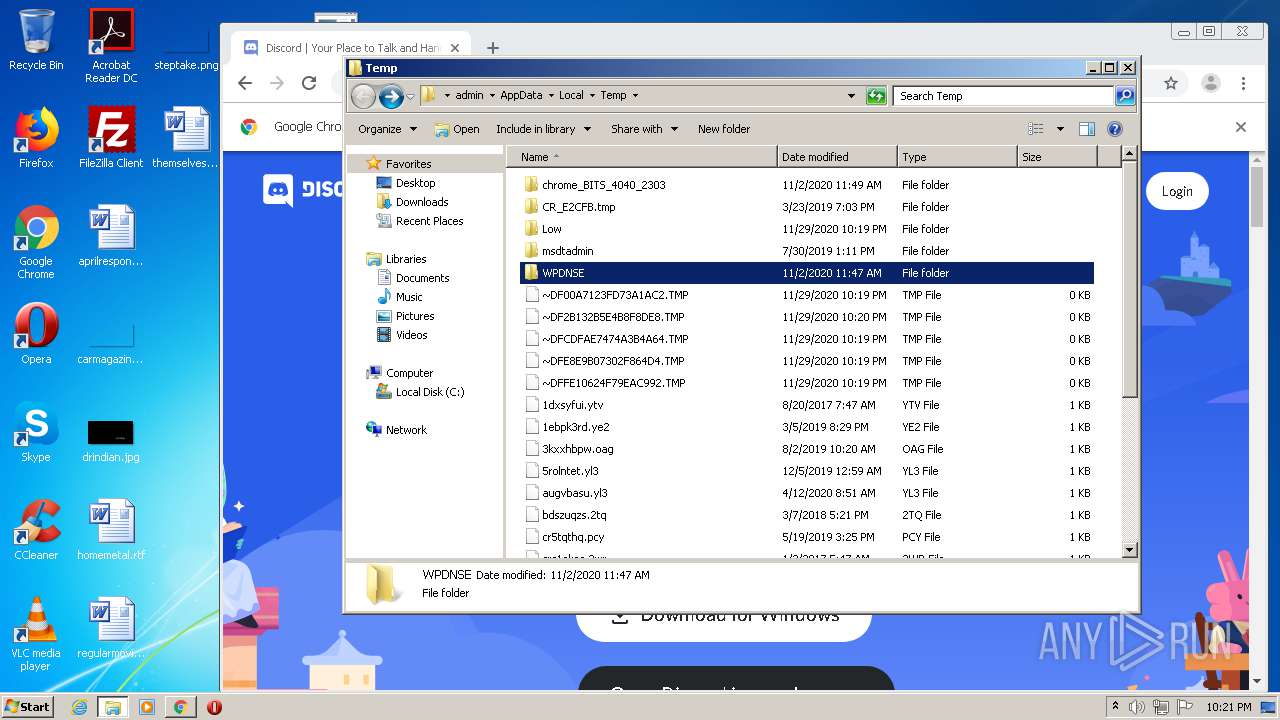
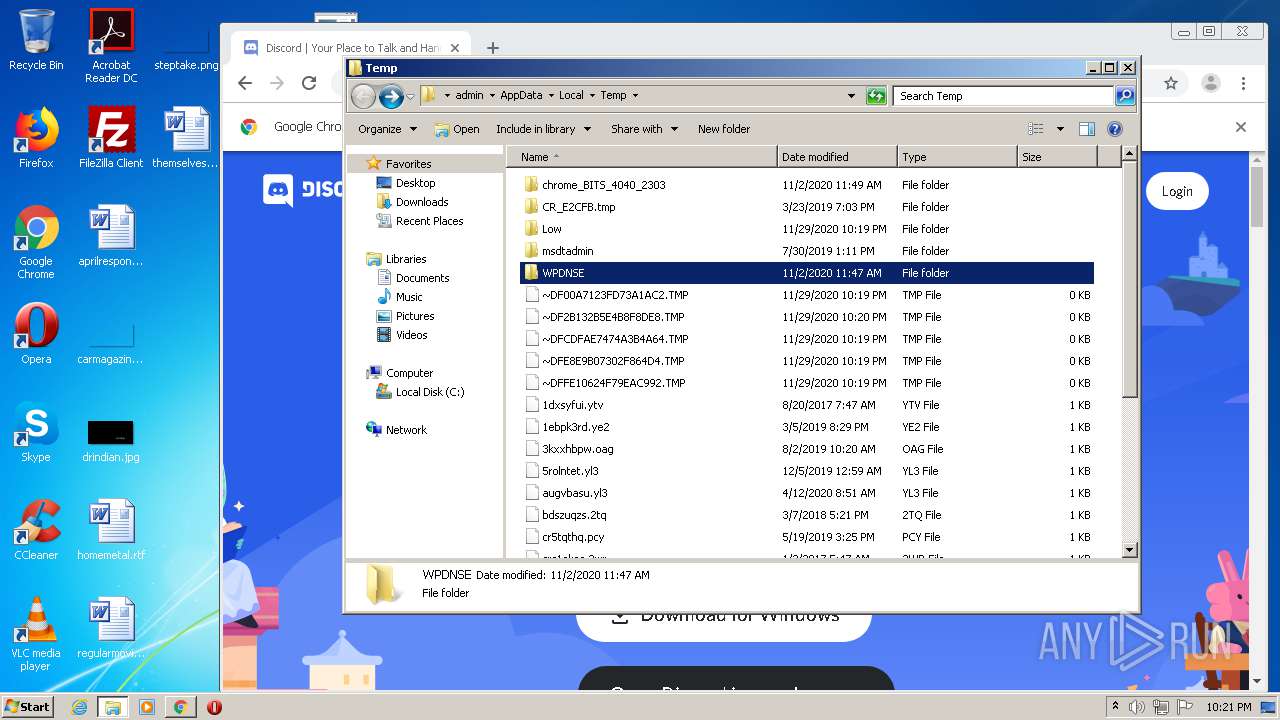
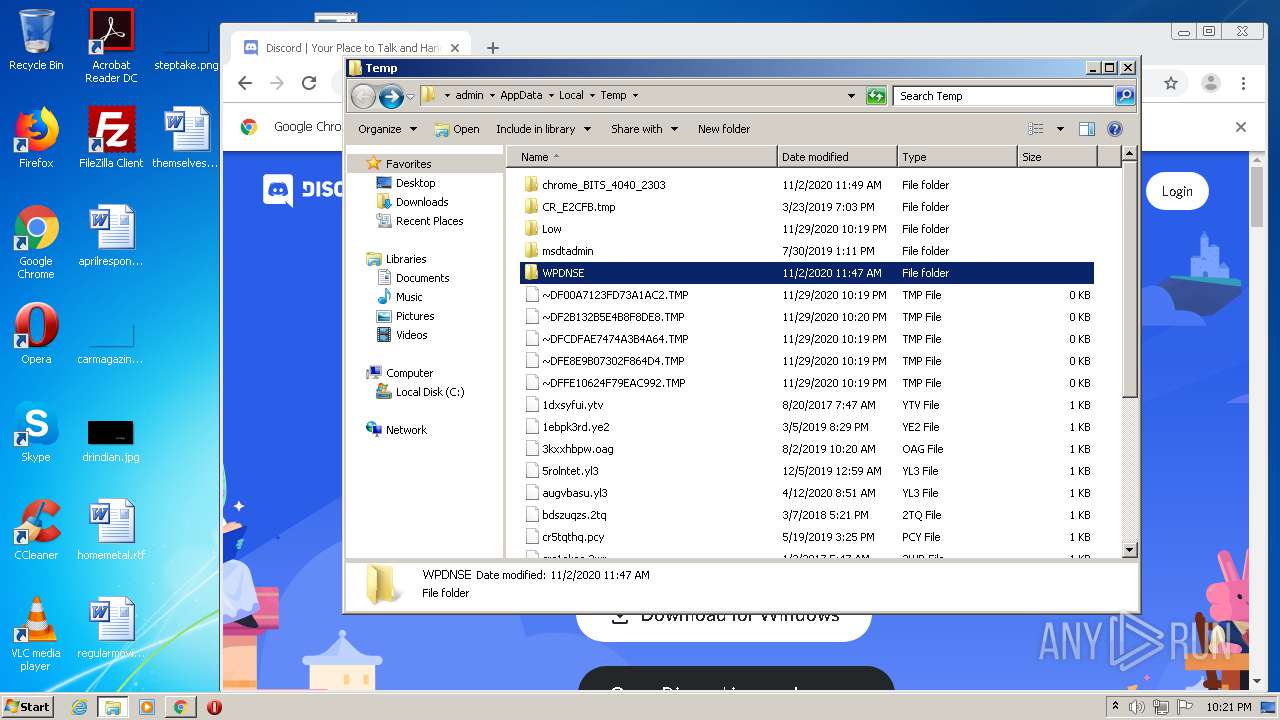
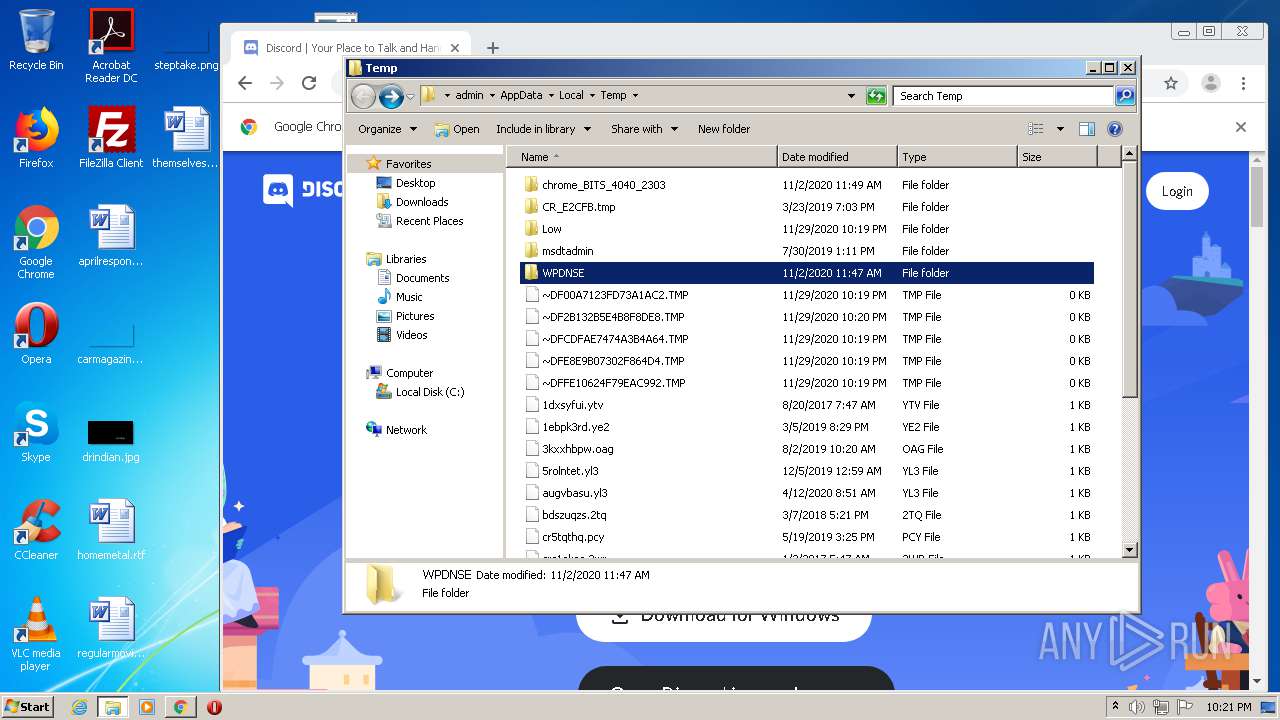
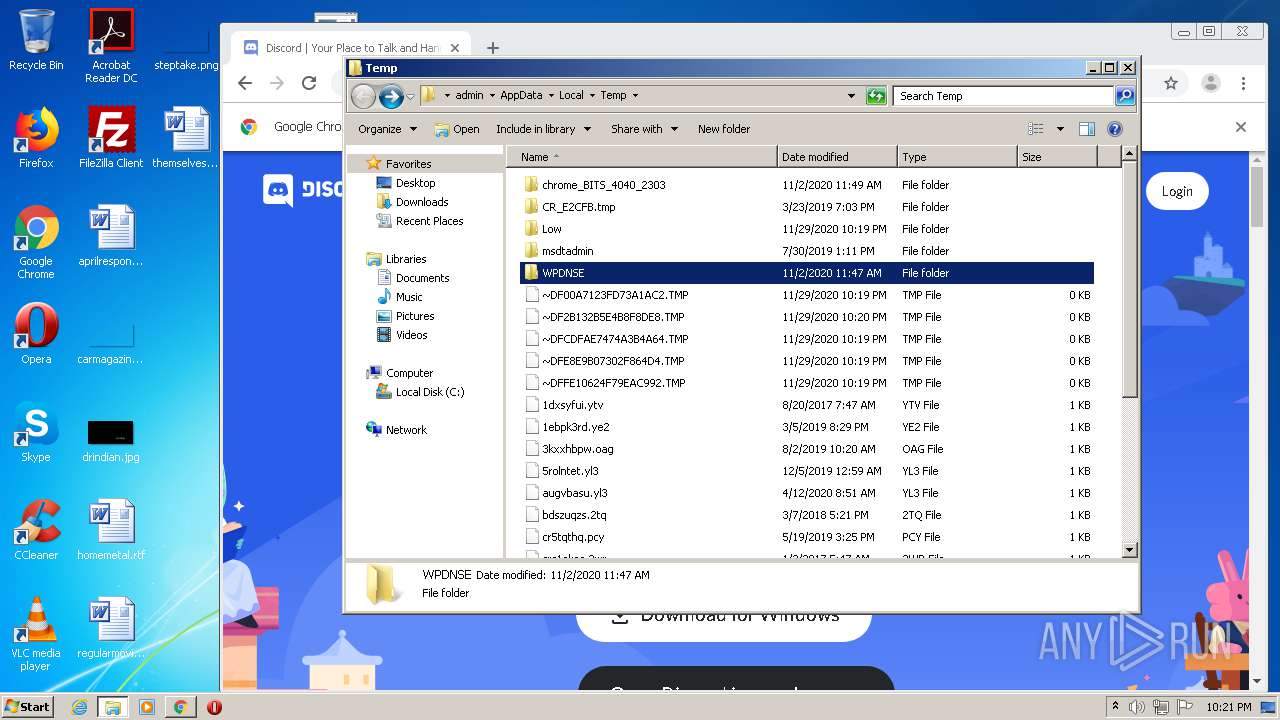
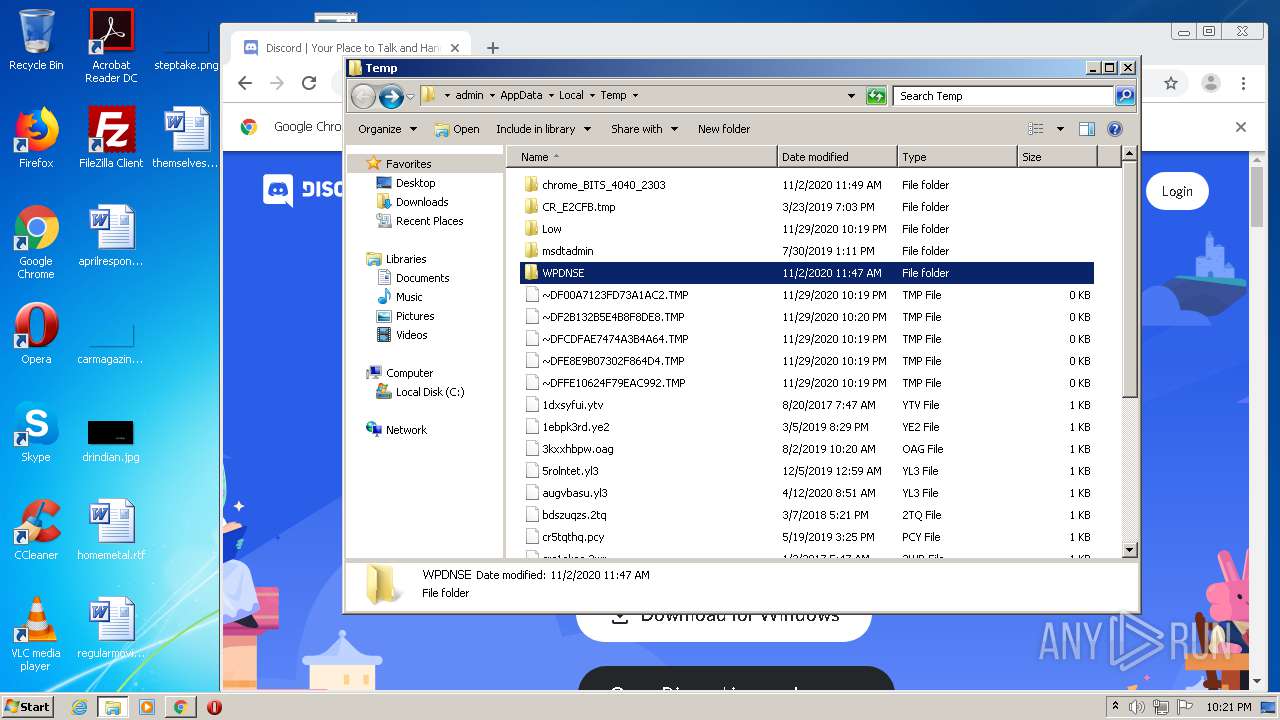
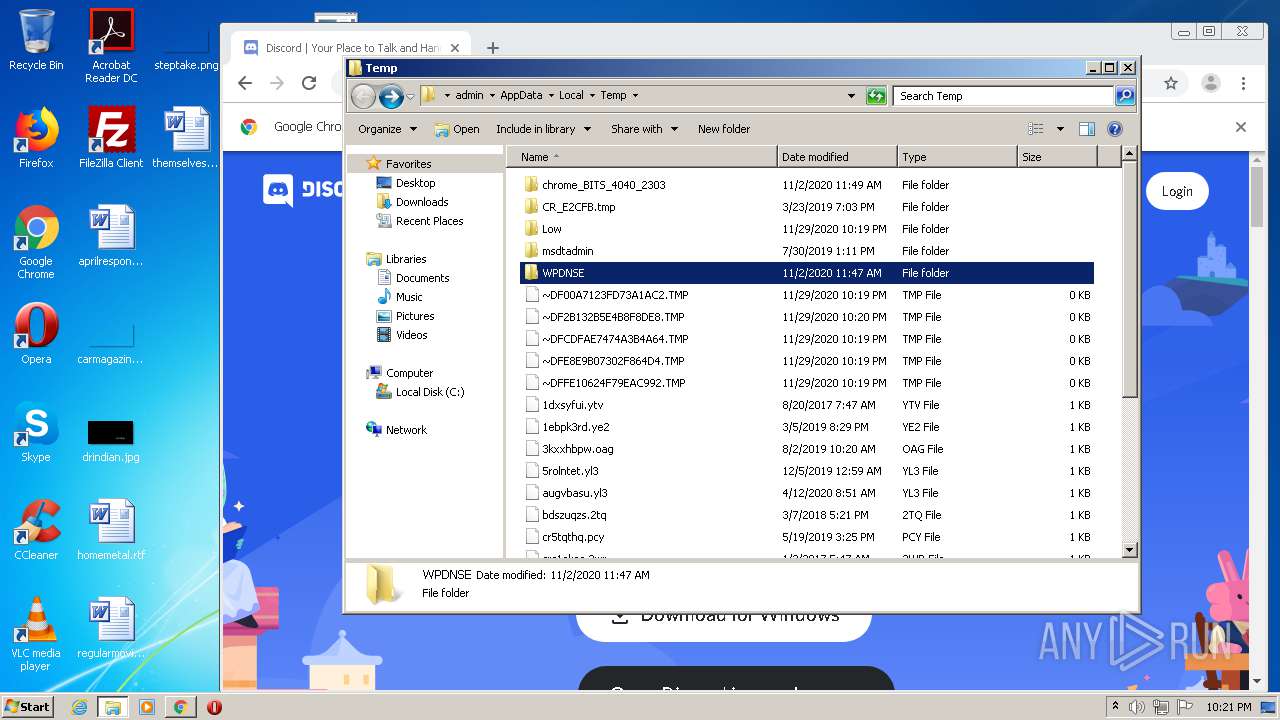
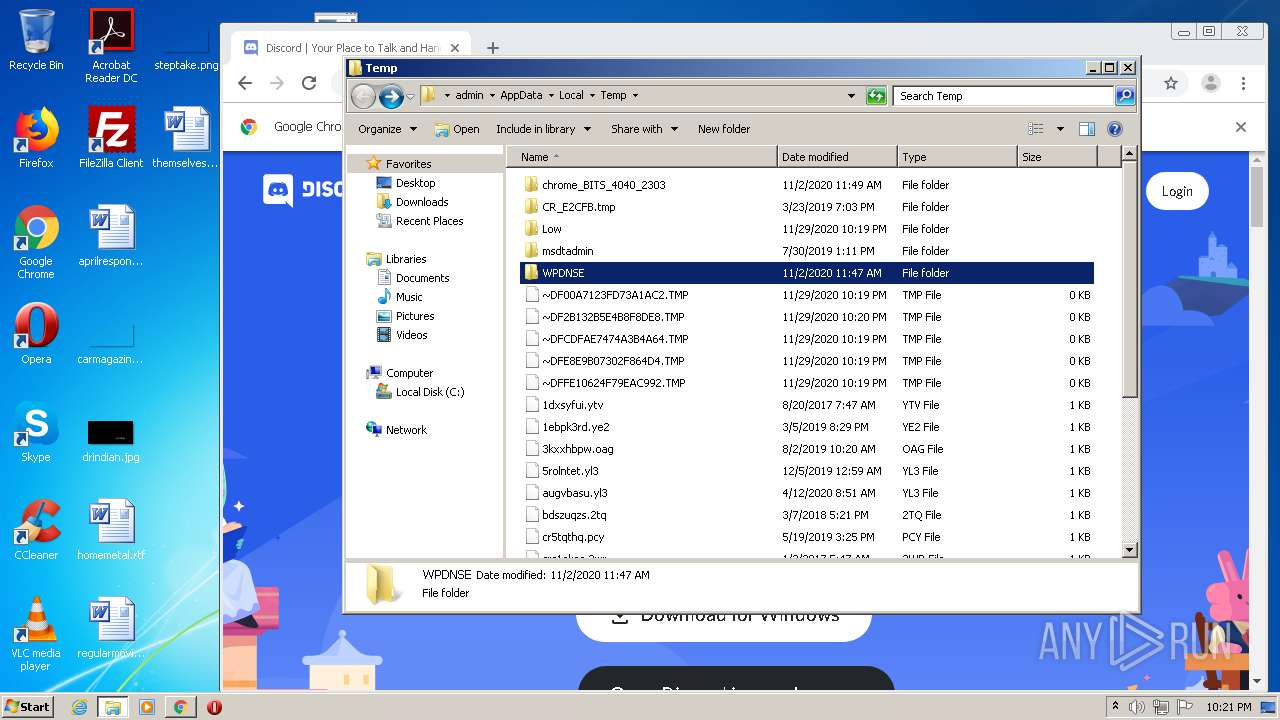
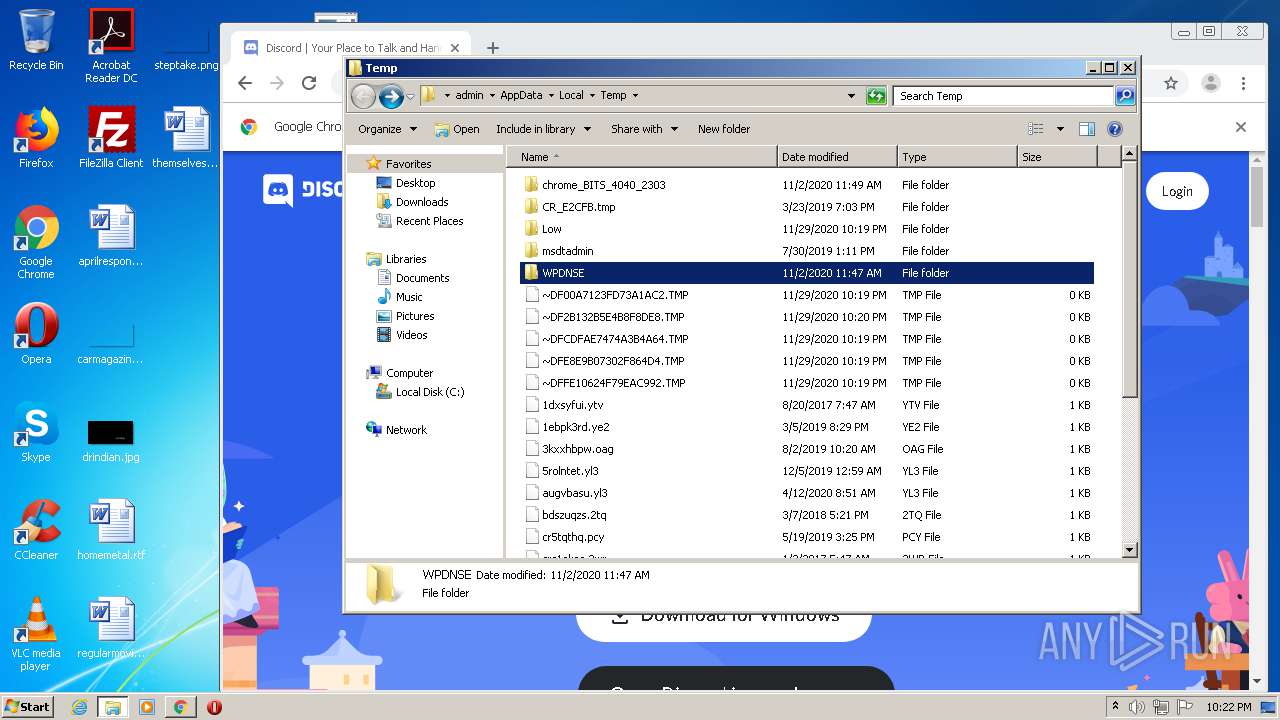
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1796 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\4NJQZ63K.txt | — | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EWU6NWKG.txt | — | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabD9AD.tmp | — | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD9AE.tmp | — | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\f[1].txt | text | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\prebid2.44.1[1].js | text | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\R9X6747D.txt | text | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\file[1].htm | html | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_5FDD03068CBBD8A96F3AB9595BA10093 | binary | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\infinity.js[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
87
TCP/UDP connections
226
DNS requests
147
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1796 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
1796 | iexplore.exe | GET | 200 | 216.58.205.238:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 1.84 Kb | whitelisted |
1796 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1796 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
1796 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDa2MTpyZrzlQgAAAAAYth4 | US | der | 472 b | whitelisted |
1796 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDa2MTpyZrzlQgAAAAAYth4 | US | der | 472 b | whitelisted |
1796 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1796 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFcLuT0XSrlKAgAAAACAVZE%3D | US | der | 471 b | whitelisted |
1796 | iexplore.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/download/apps_list_sprite-v4.png | US | image | 6.78 Kb | shared |
1796 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1796 | iexplore.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
1796 | iexplore.exe | 172.217.16.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1796 | iexplore.exe | 216.58.207.34:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
1796 | iexplore.exe | 216.58.205.238:80 | translate.google.com | Google Inc. | US | whitelisted |
1796 | iexplore.exe | 216.58.205.238:443 | translate.google.com | Google Inc. | US | whitelisted |
1796 | iexplore.exe | 2.20.168.110:443 | c.aaxads.com | Akamai Technologies, Inc. | — | unknown |
1796 | iexplore.exe | 172.217.22.42:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
1796 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1796 | iexplore.exe | 216.58.212.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1796 | iexplore.exe | 185.33.221.53:80 | ib.adnxs.com | AppNexus, Inc | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
c.aaxads.com |
| whitelisted |
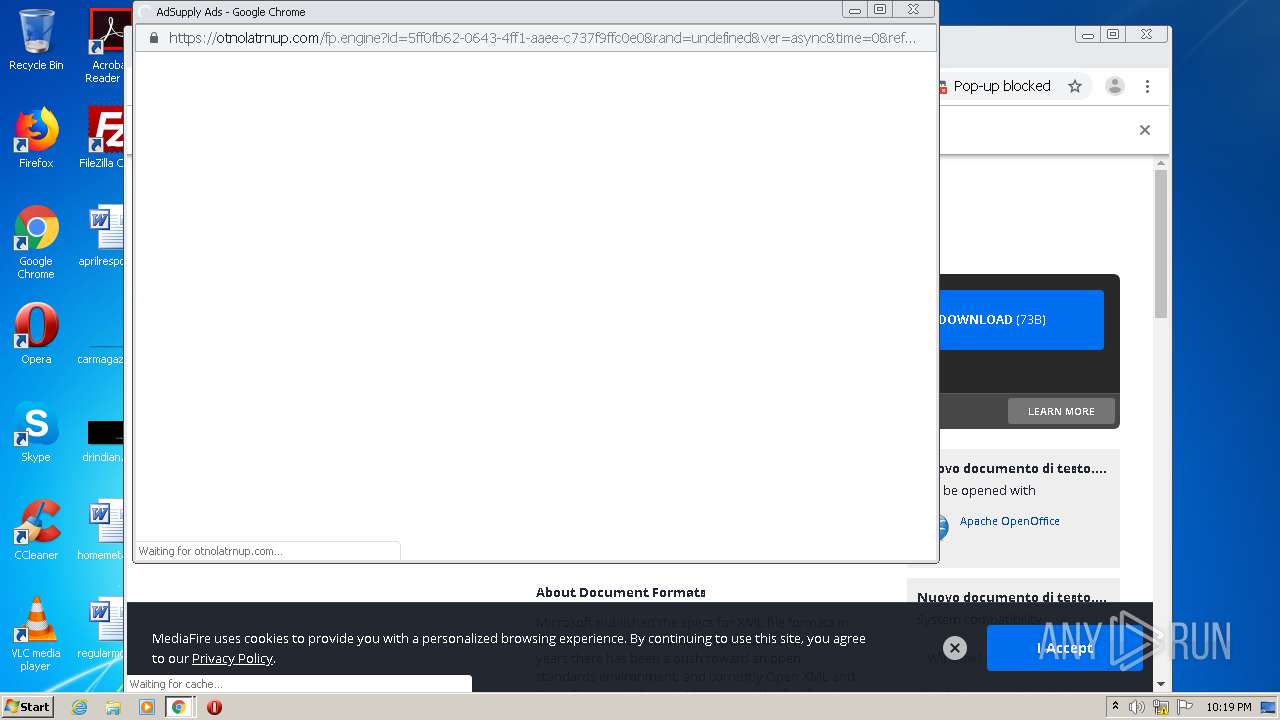
cdn.otnolatrnup.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1700 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1700 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
Process | Message |
|---|---|
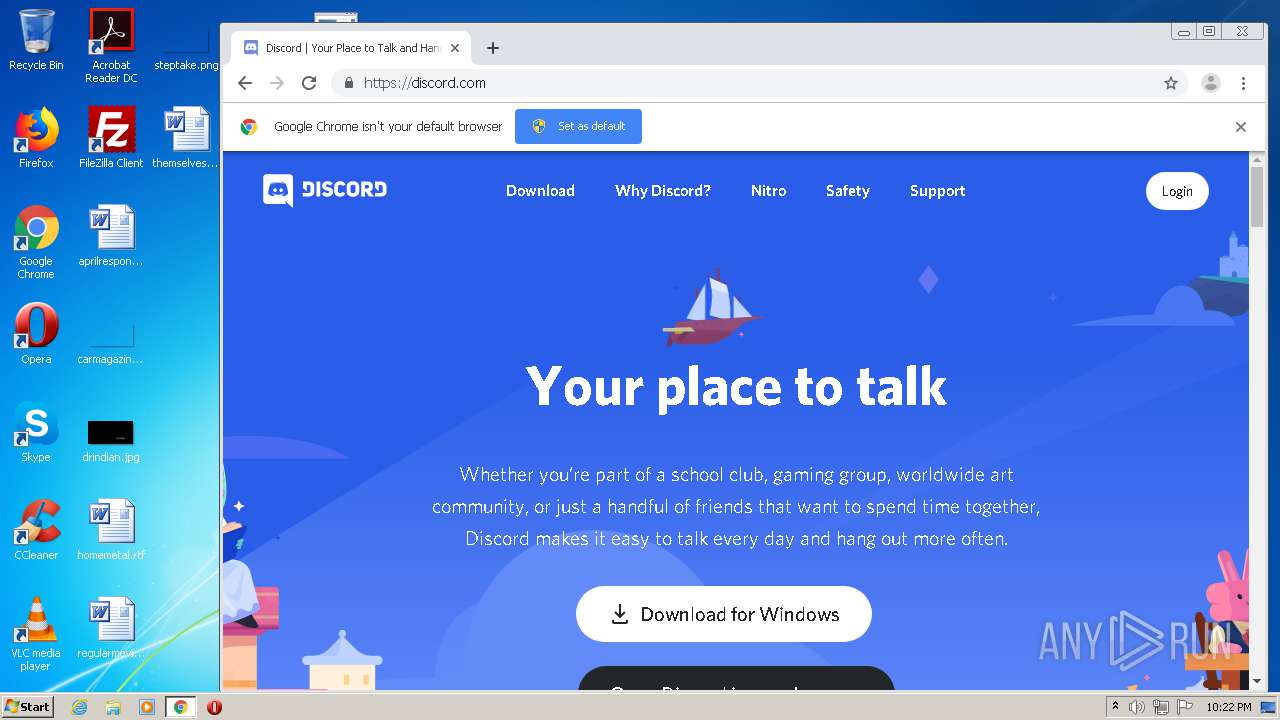
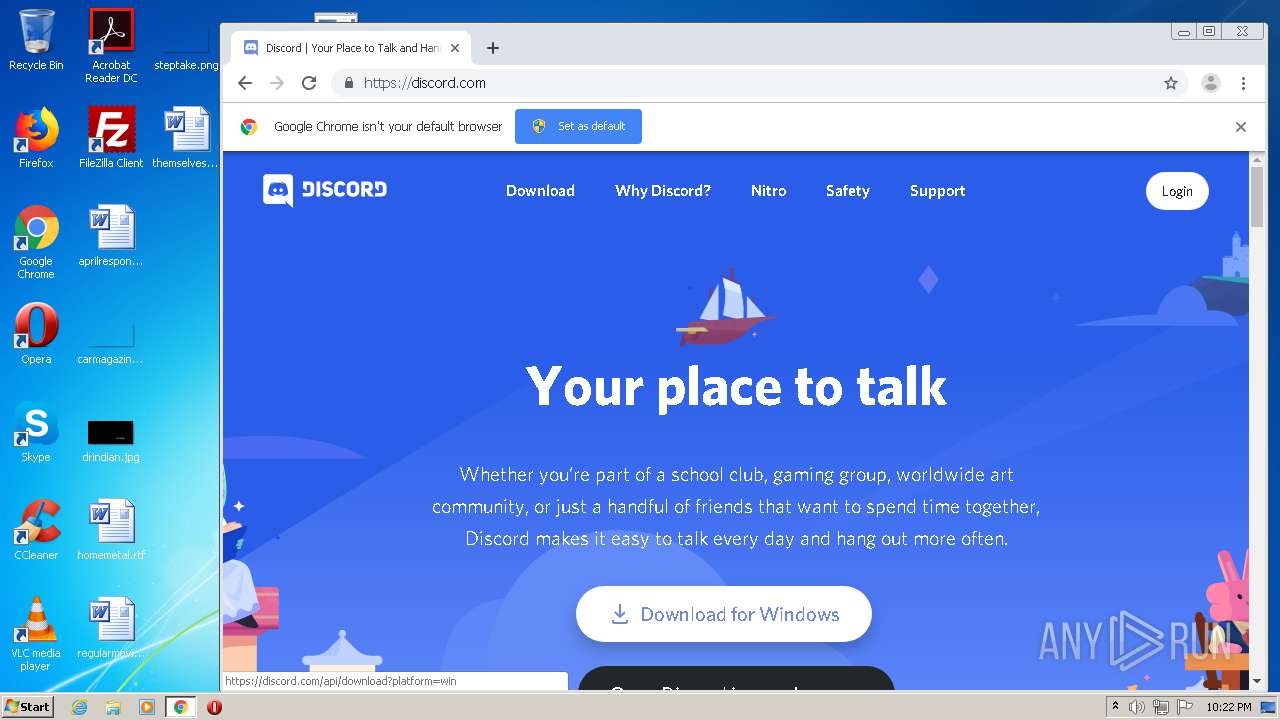
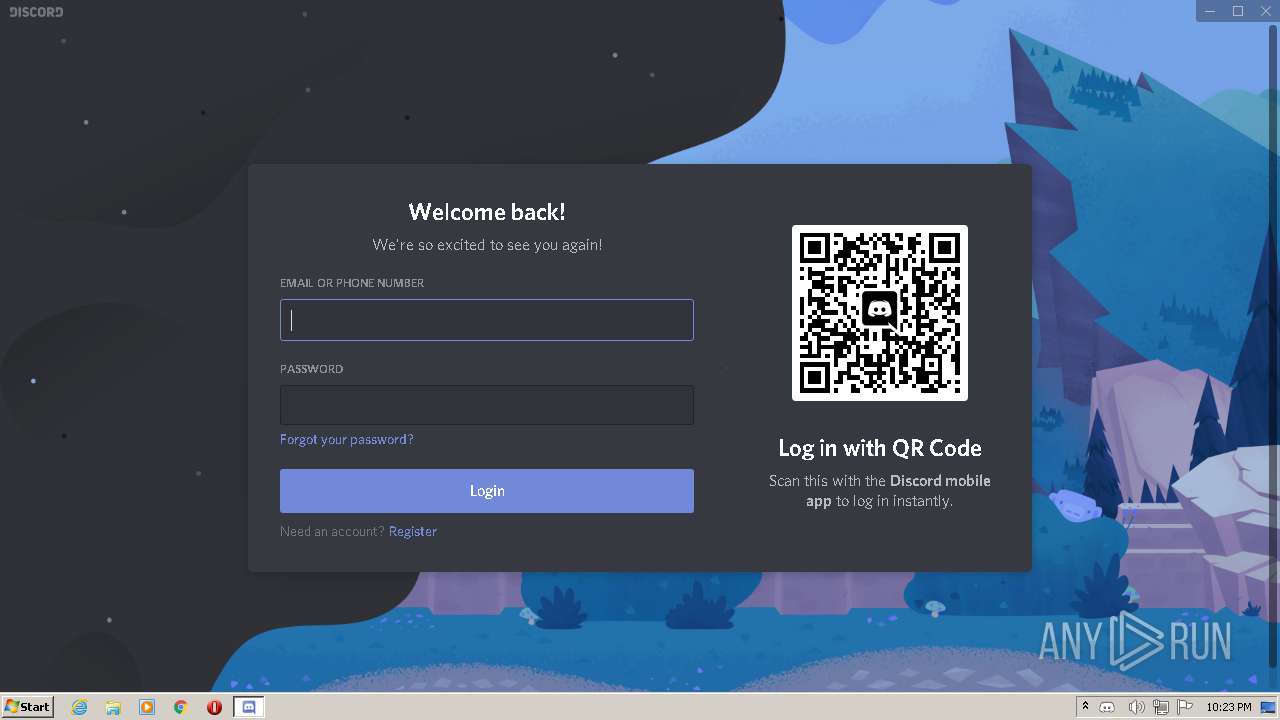
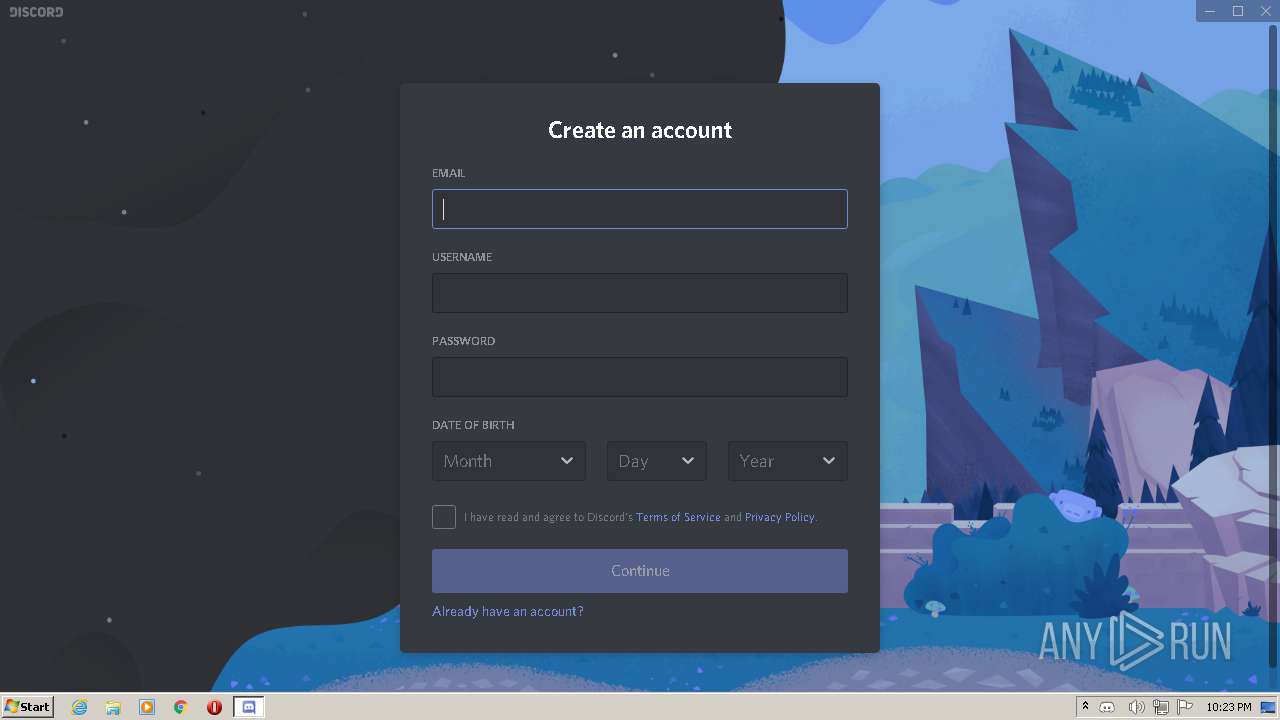
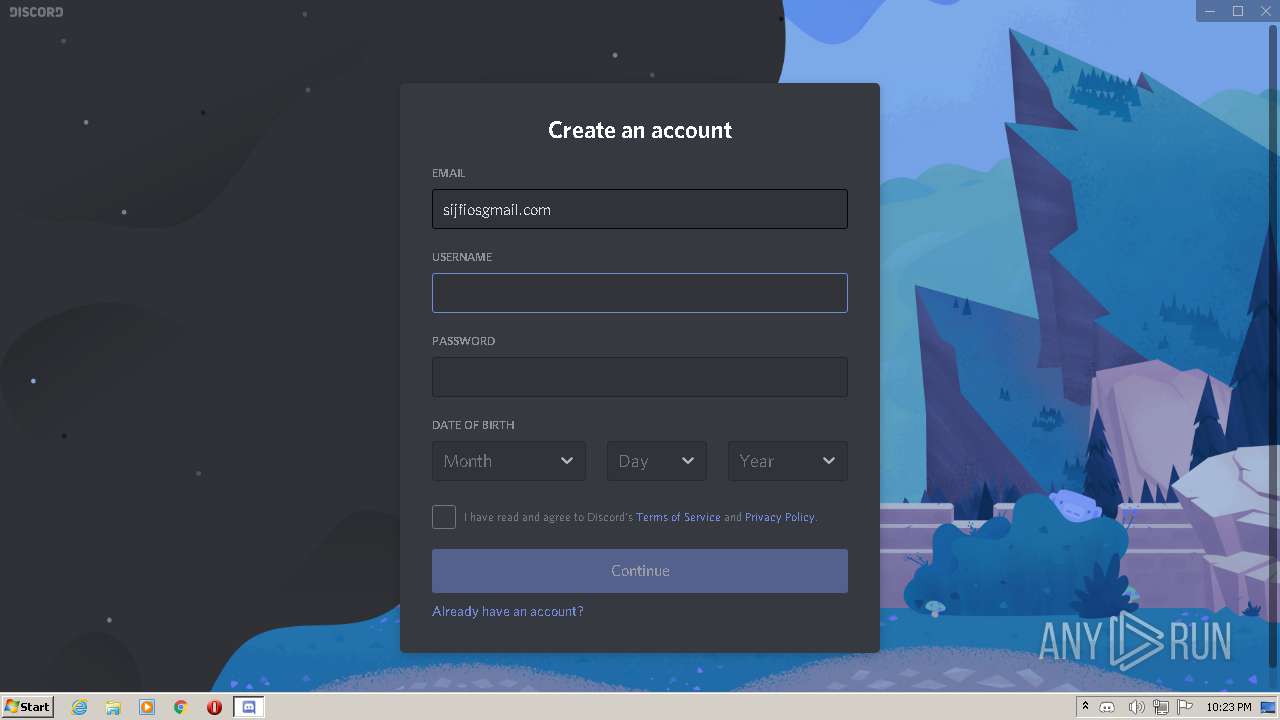
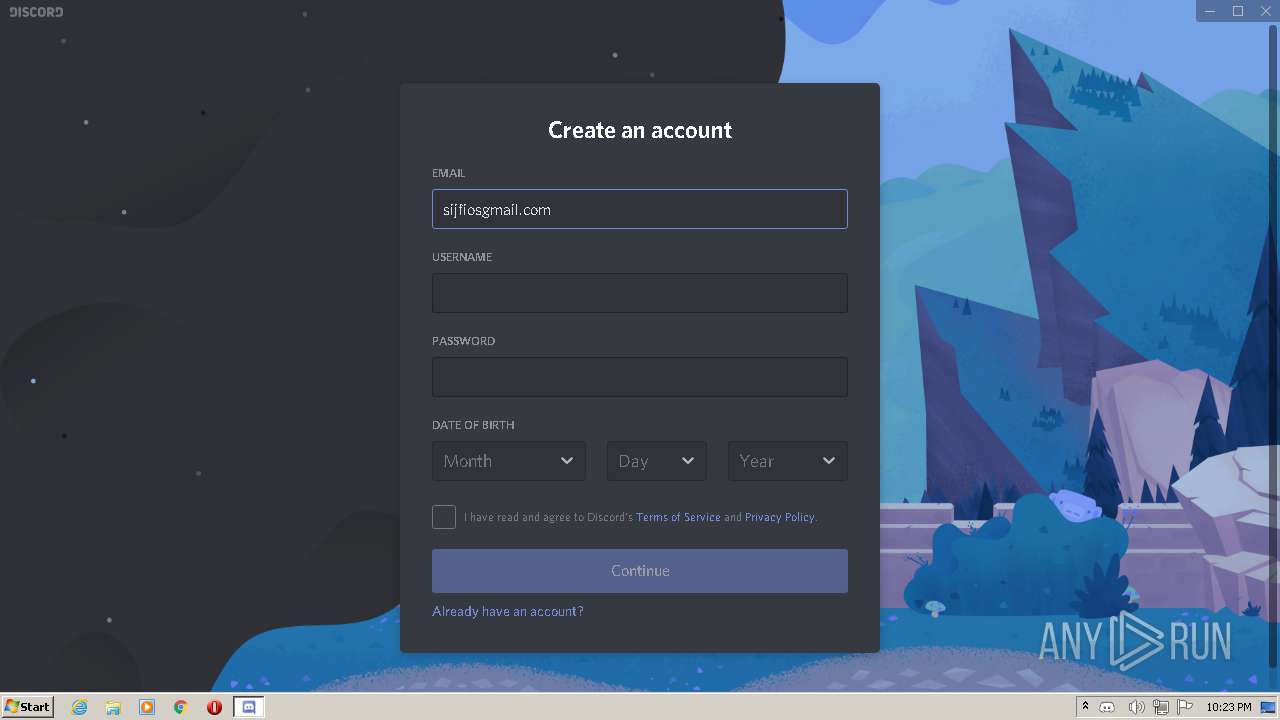
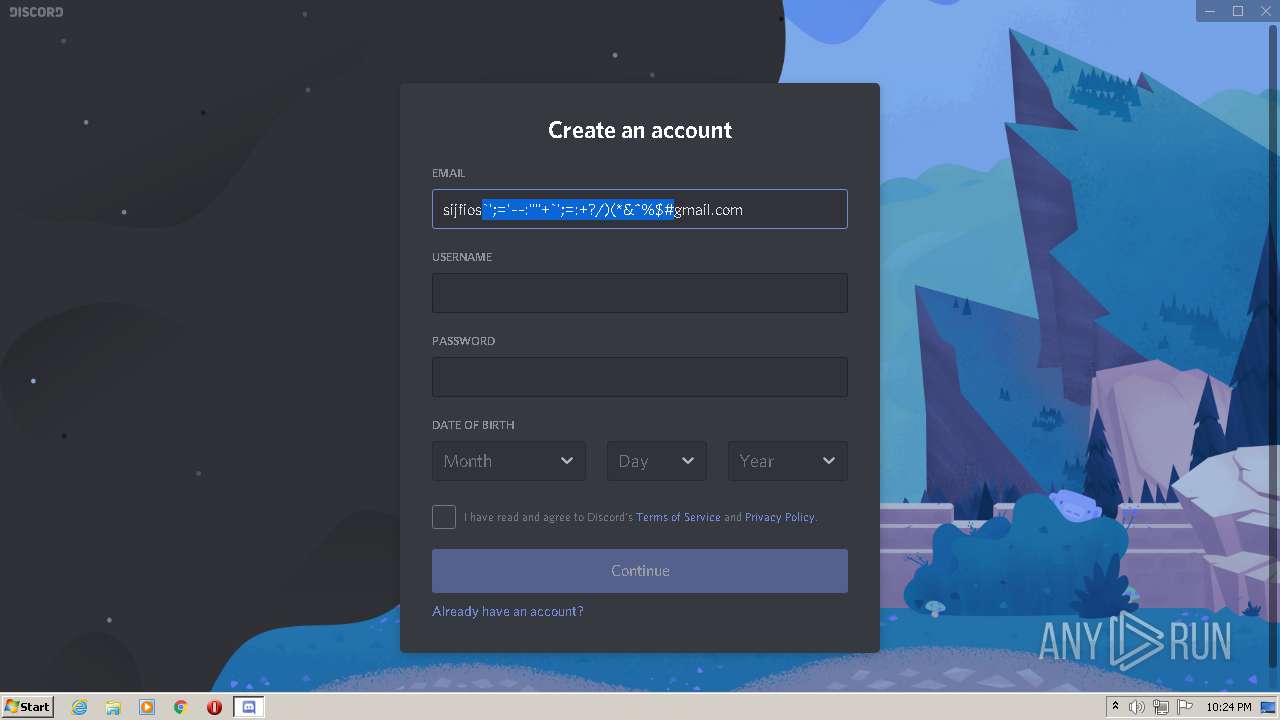
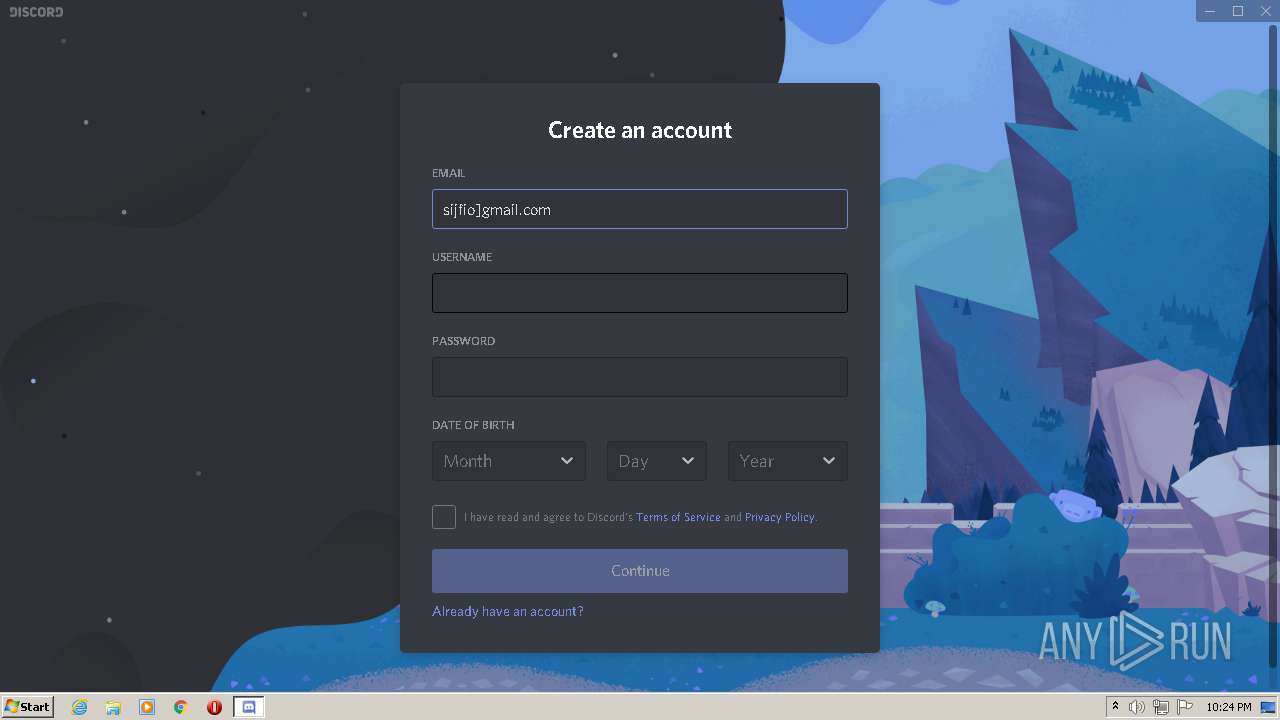
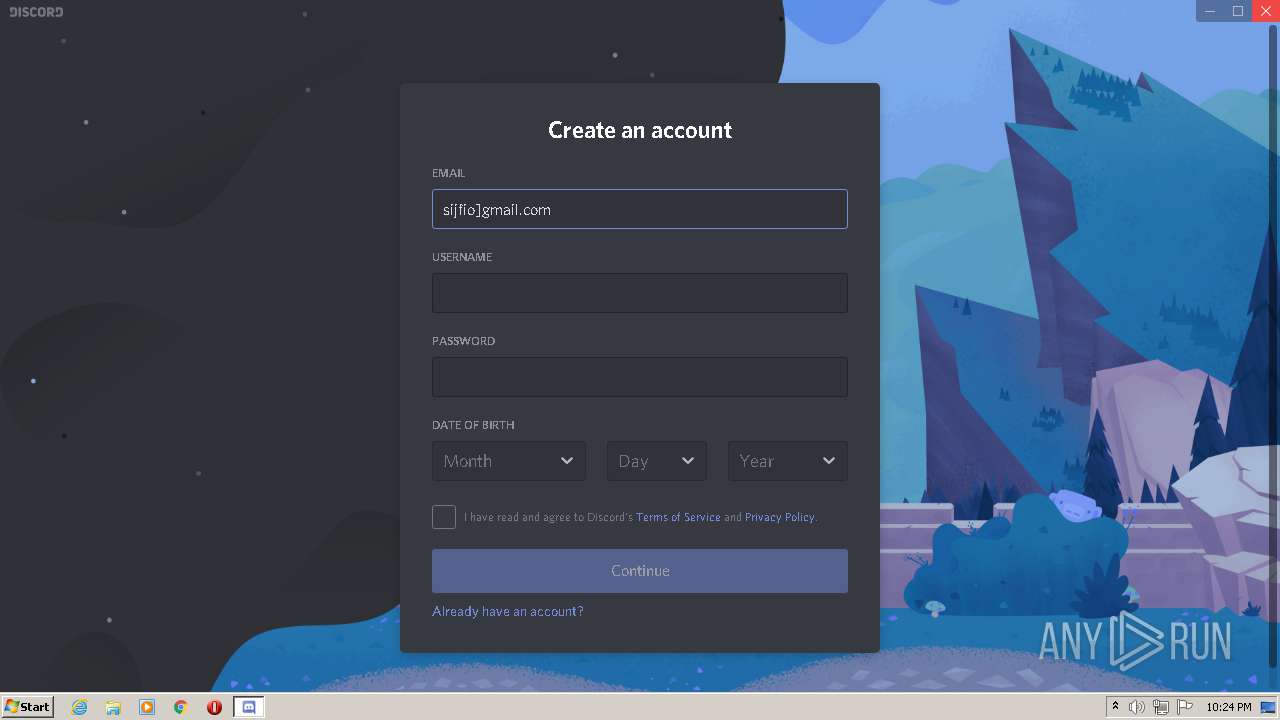
DiscordSetup.exe | Start up installer: |
DiscordSetup.exe | Elevated process: ?
|
DiscordSetup.exe | Want standard install |