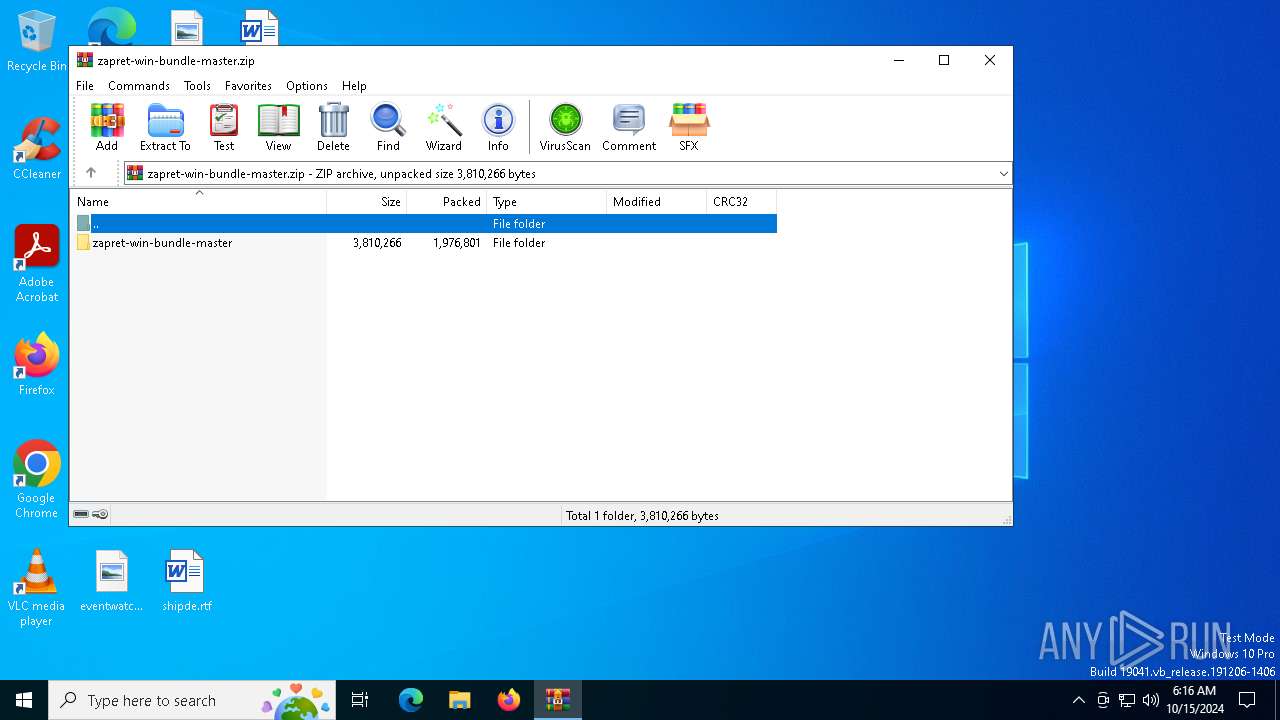
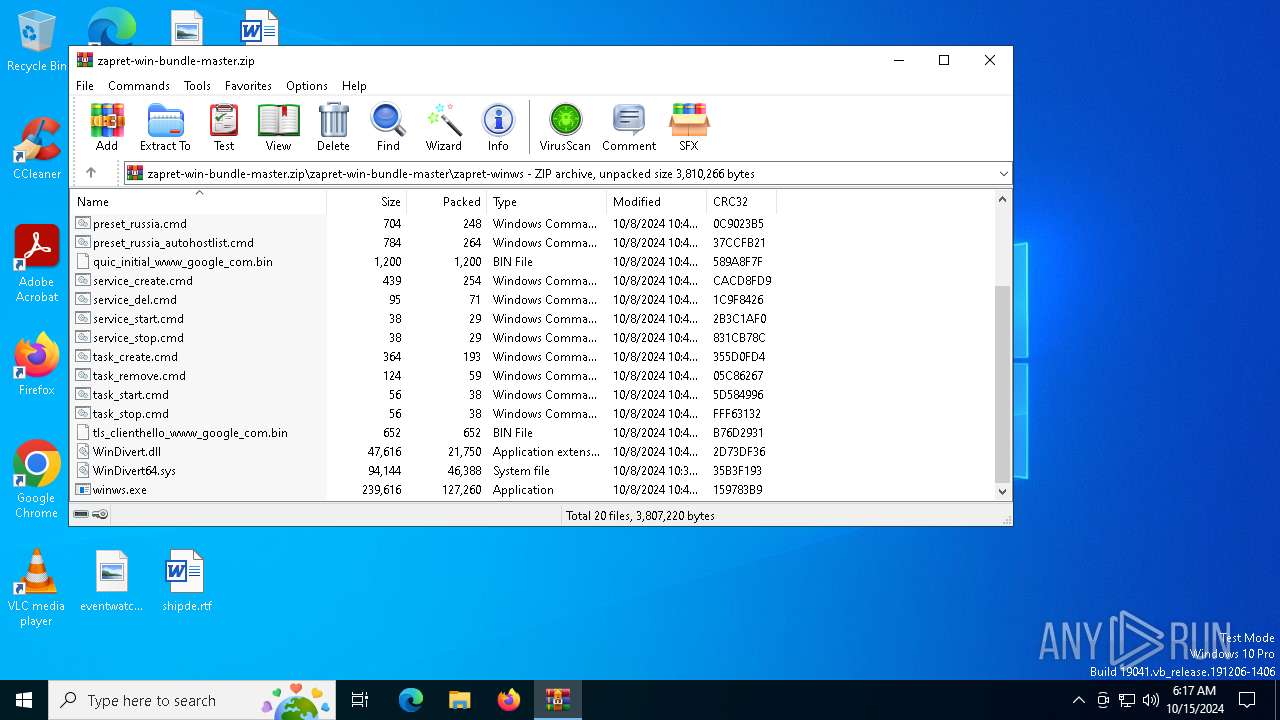
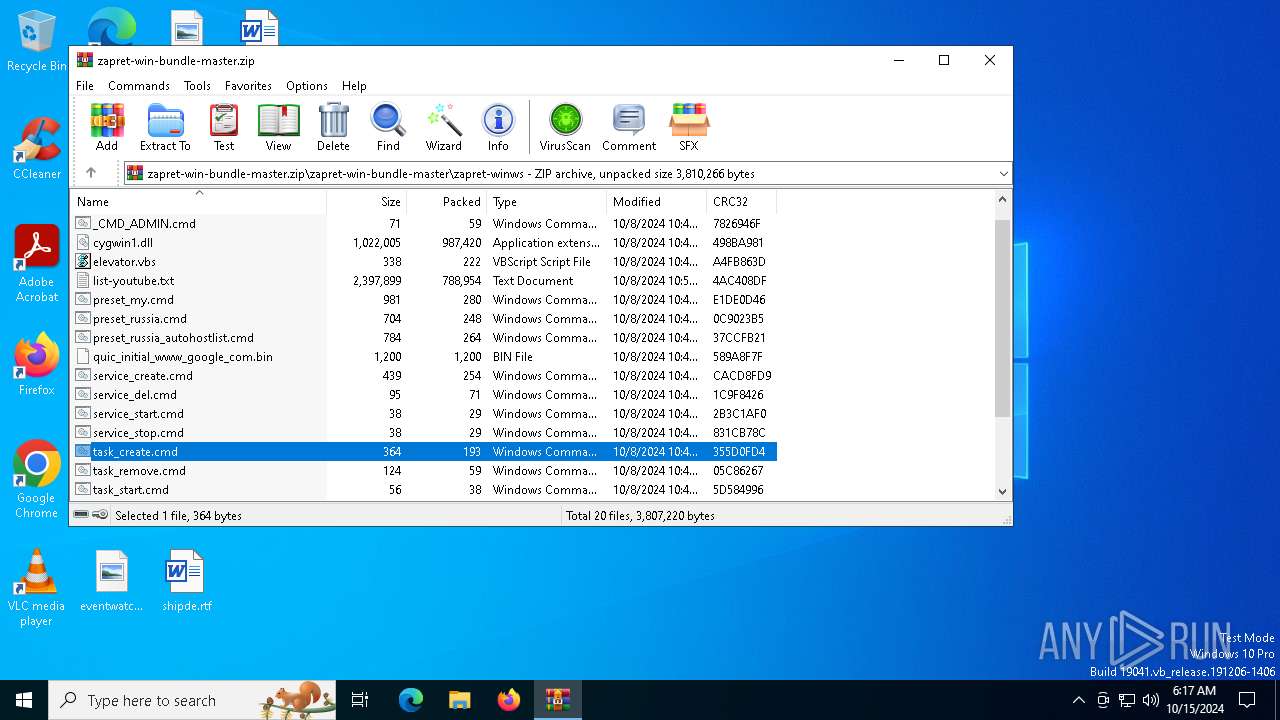
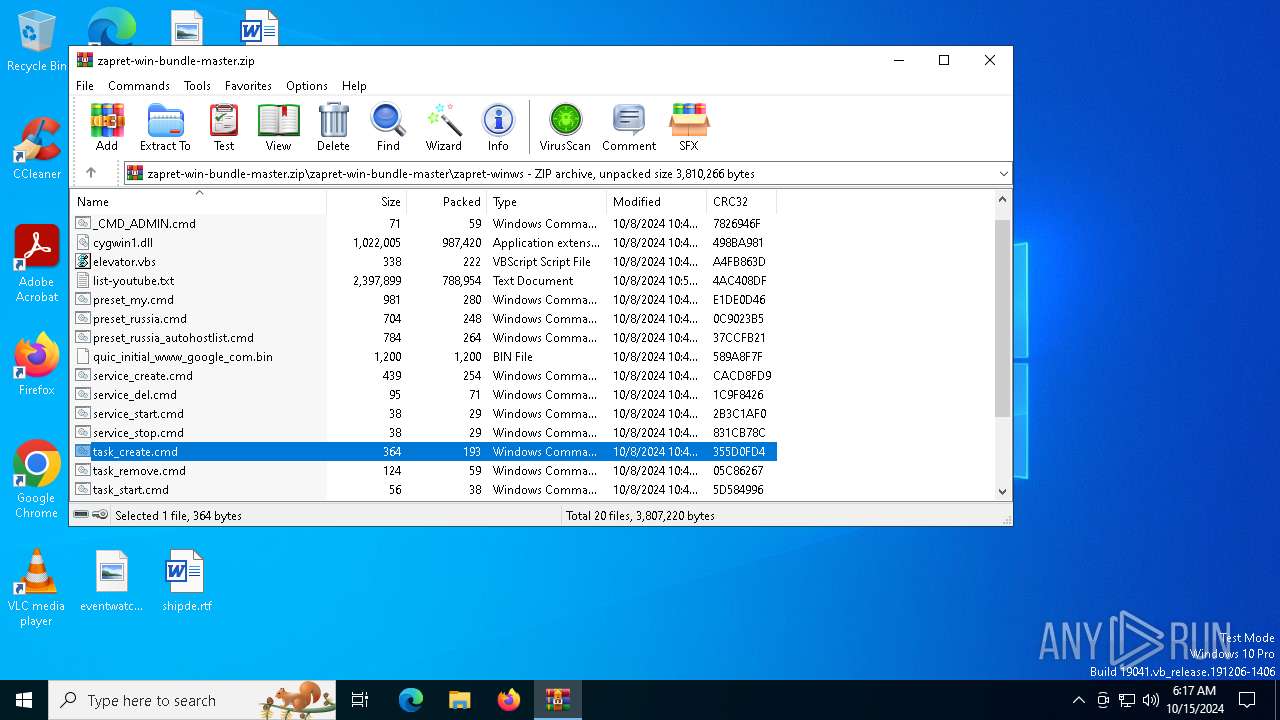
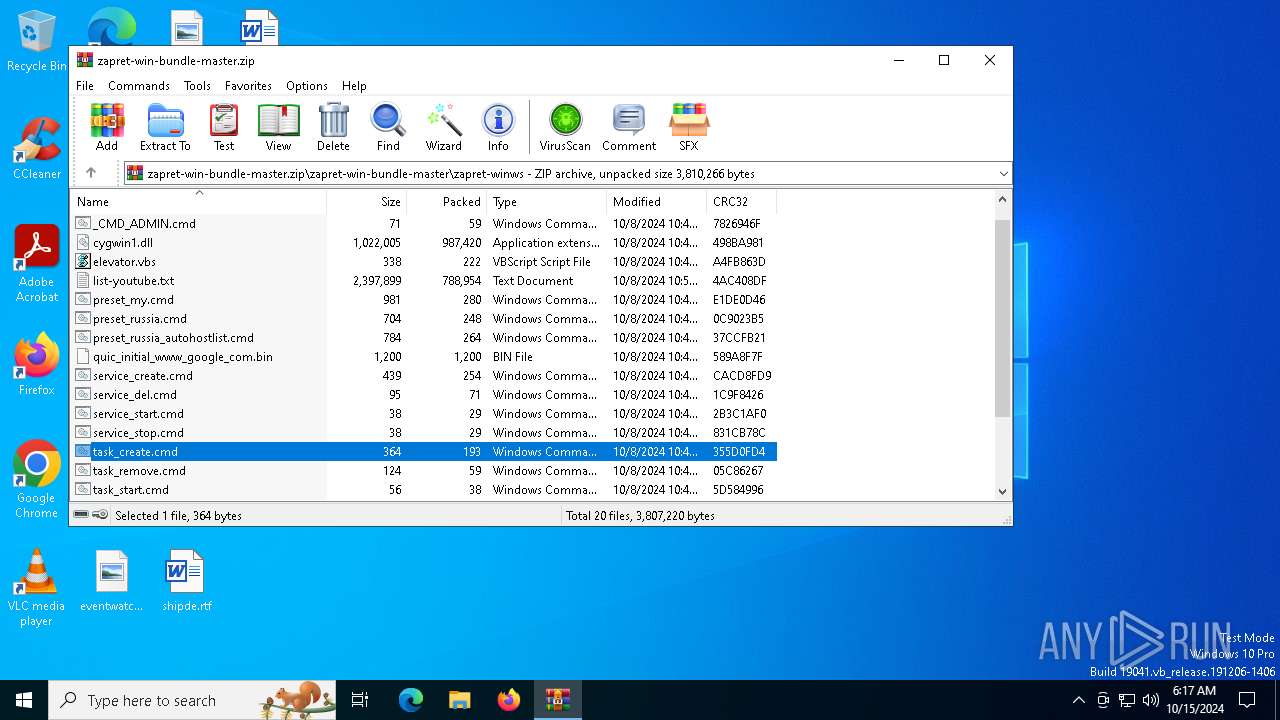
| File name: | zapret-win-bundle-master.zip |
| Full analysis: | https://app.any.run/tasks/4e3fa63f-1567-4cf7-a312-c9e6613b914a |
| Verdict: | Malicious activity |
| Analysis date: | October 15, 2024, 06:16:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | E1D1BA1D7C3B2023558FB6FCC12710C9 |
| SHA1: | CBF6912447EF391DF54A36D9F7A1938A50A45812 |
| SHA256: | 203F7D94C1D1BF2B68E299CFC954B805F7AFD3569A14D931150AE132175D66FB |
| SSDEEP: | 98304:Ok0Sf4zkaBpza1FtNTXG68il8LhYssJNnidJn5N4F14j32Szt3dLndFd+Qj3Ao2j:pOa |
MALICIOUS
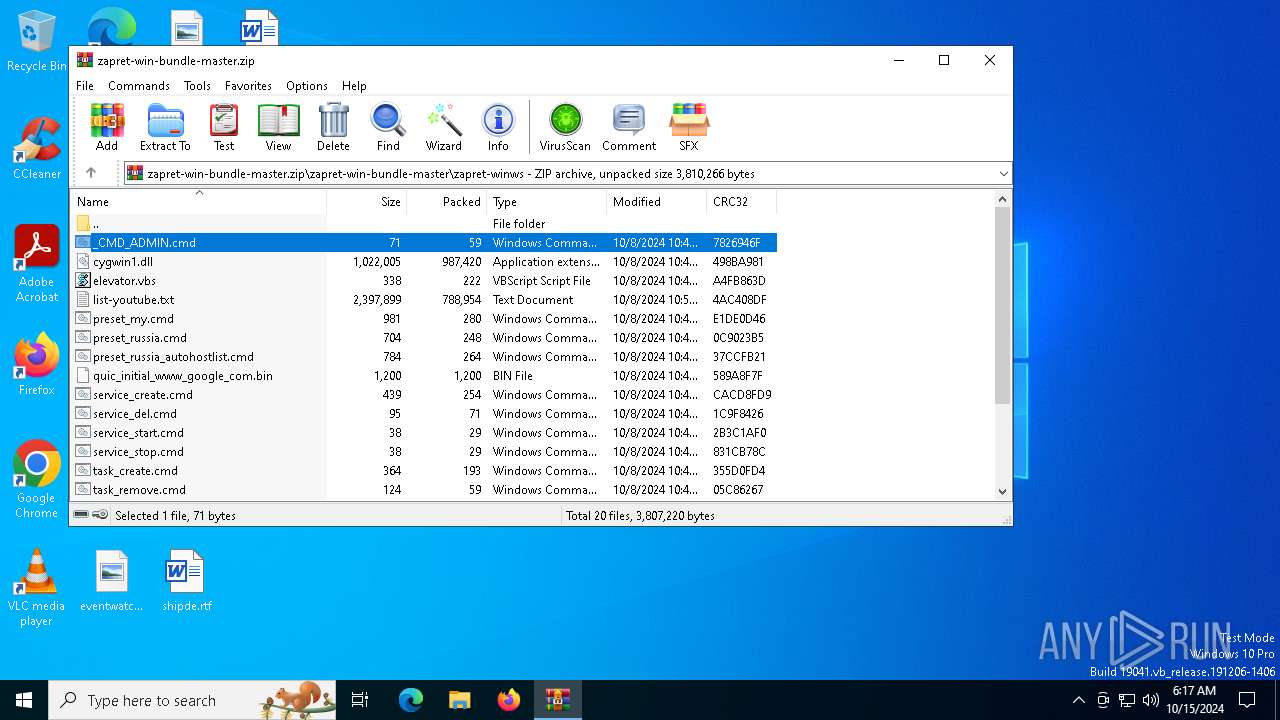
Generic archive extractor
- WinRAR.exe (PID: 6024)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1160)
- cmd.exe (PID: 4568)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6024)
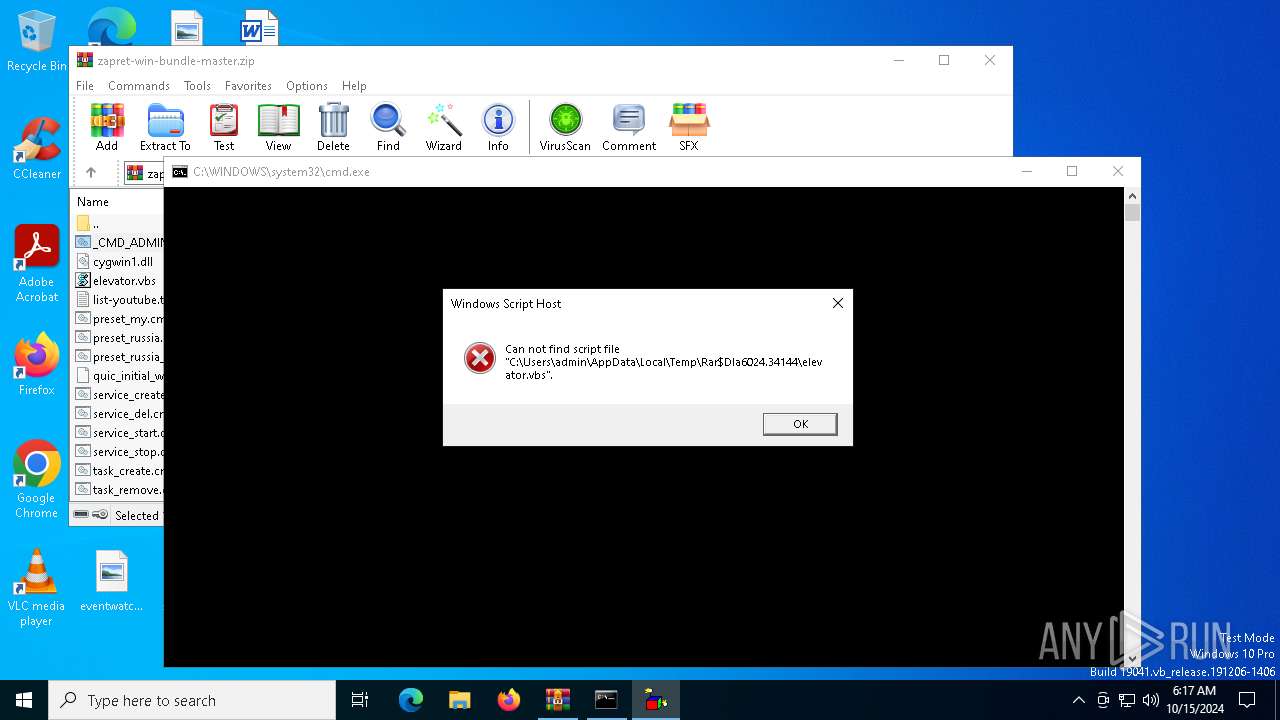
The process executes VB scripts
- cmd.exe (PID: 7124)
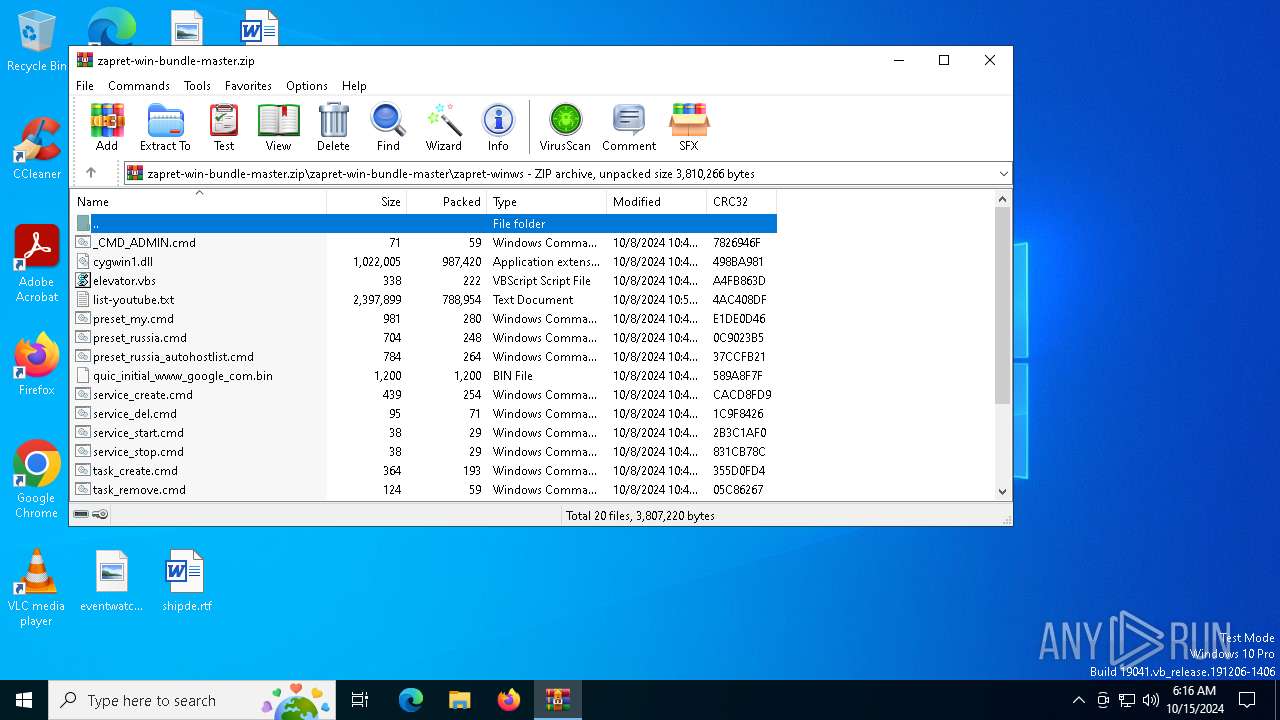
Executing commands from ".cmd" file
- WinRAR.exe (PID: 6024)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 6024)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:08 22:49:34 |
| ZipCRC: | 0x119954d1 |
| ZipCompressedSize: | 47 |
| ZipUncompressedSize: | 69 |
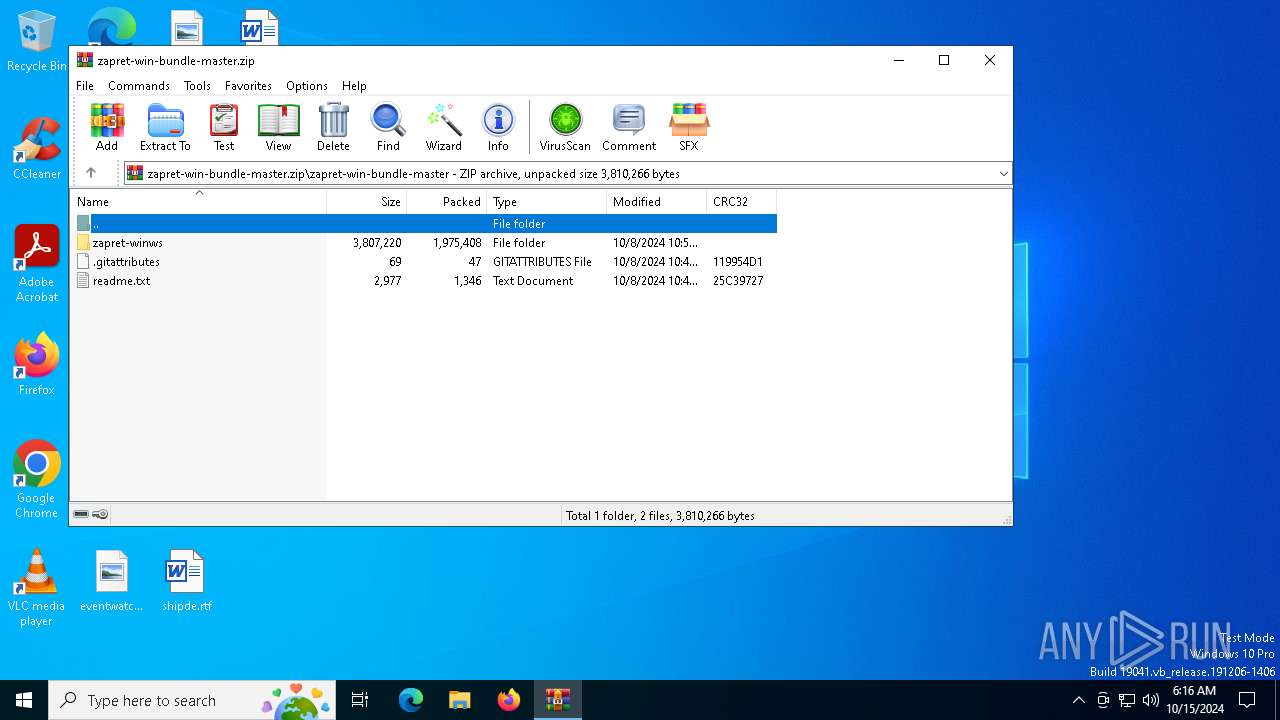
| ZipFileName: | zapret-win-bundle-master/.gitattributes |
Total processes
150
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
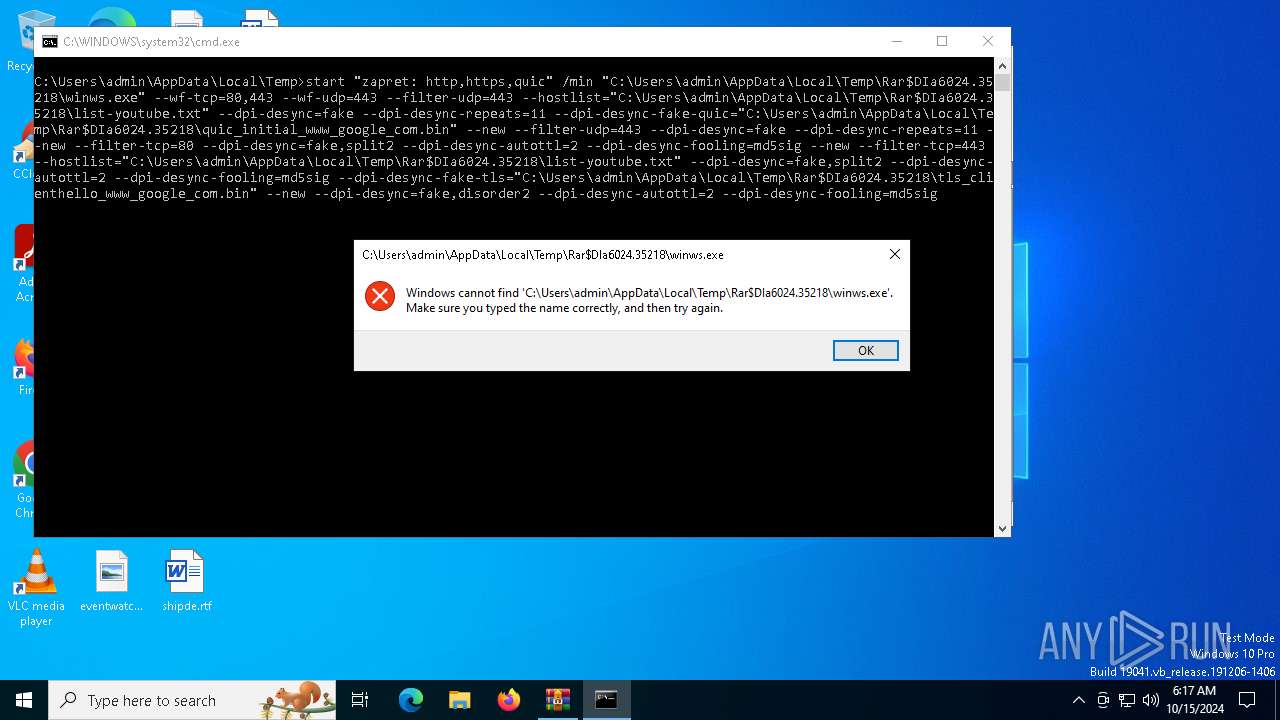
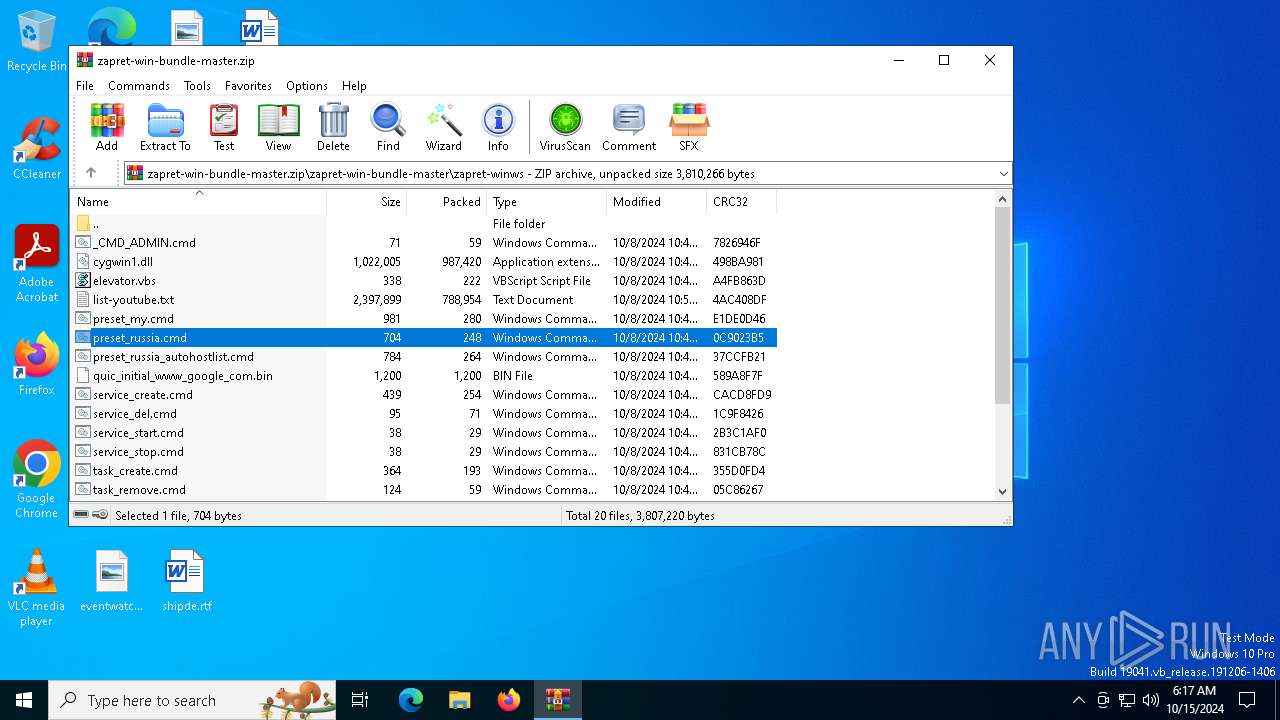
| 1084 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa6024.35218\preset_russia.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa6024.36249\task_create.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1372 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1584 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | wscript elevator.vbs cmd /k cd /d "C:\Users\admin\AppData\Local\Temp\Rar$DIa6024.34144\" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 3604 | schtasks /Create /F /TN winws1 /NP /RU "" /SC onstart /TR "\"C:\Users\admin\AppData\Local\Temp\Rar$DIa6024.36249\winws.exe\" --wf-l3=ipv4,ipv6 --wf-tcp=80,443 --dpi-desync=fake,split --dpi-desync-ttl=7 --dpi-desync-fooling=md5sig" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4476 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4568 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa6024.37101\task_create.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 365
Read events
3 356
Write events
9
Delete events
0
Modification events
| (PID) Process: | (6024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zapret-win-bundle-master.zip | |||
| (PID) Process: | (6024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6820) winws.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Cygwin\Installations |
| Operation: | write | Name: | c08f040f3b5d3f50 |
Value: \??\C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master | |||
| (PID) Process: | (6024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (6024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 0 | |||
Executable files
4
Suspicious files
2
Text files
20
Unknown types
0
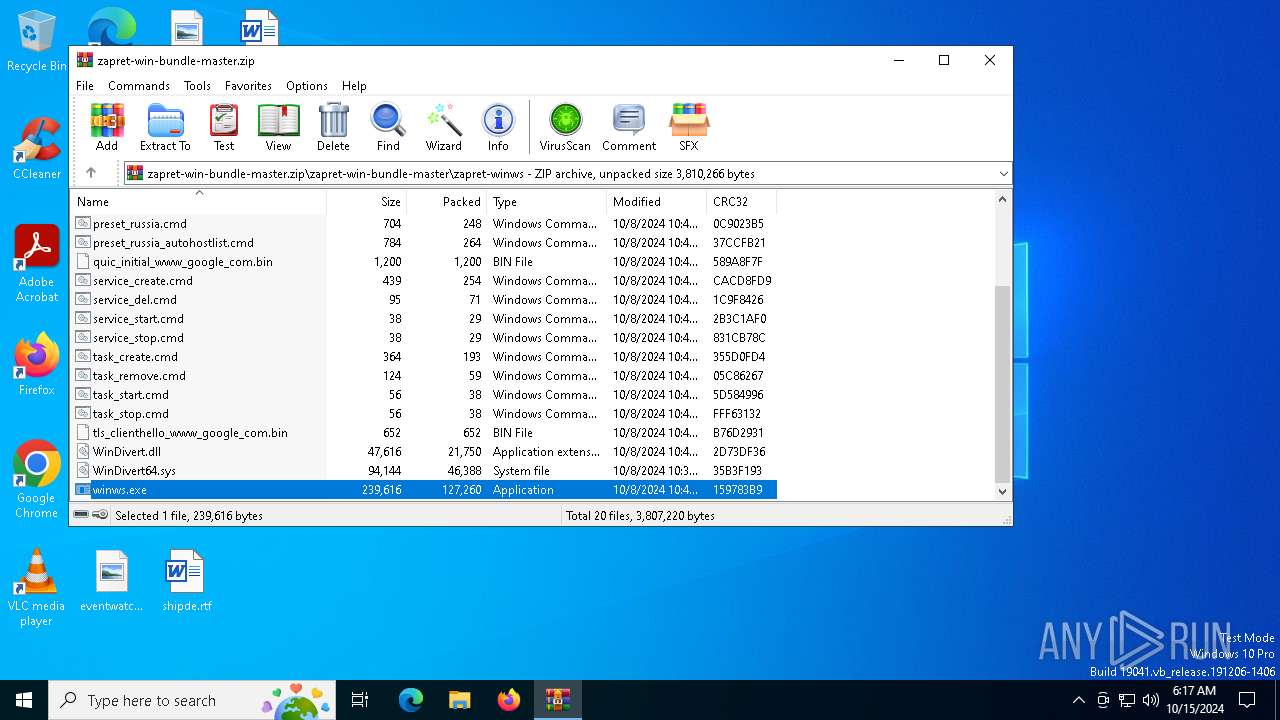
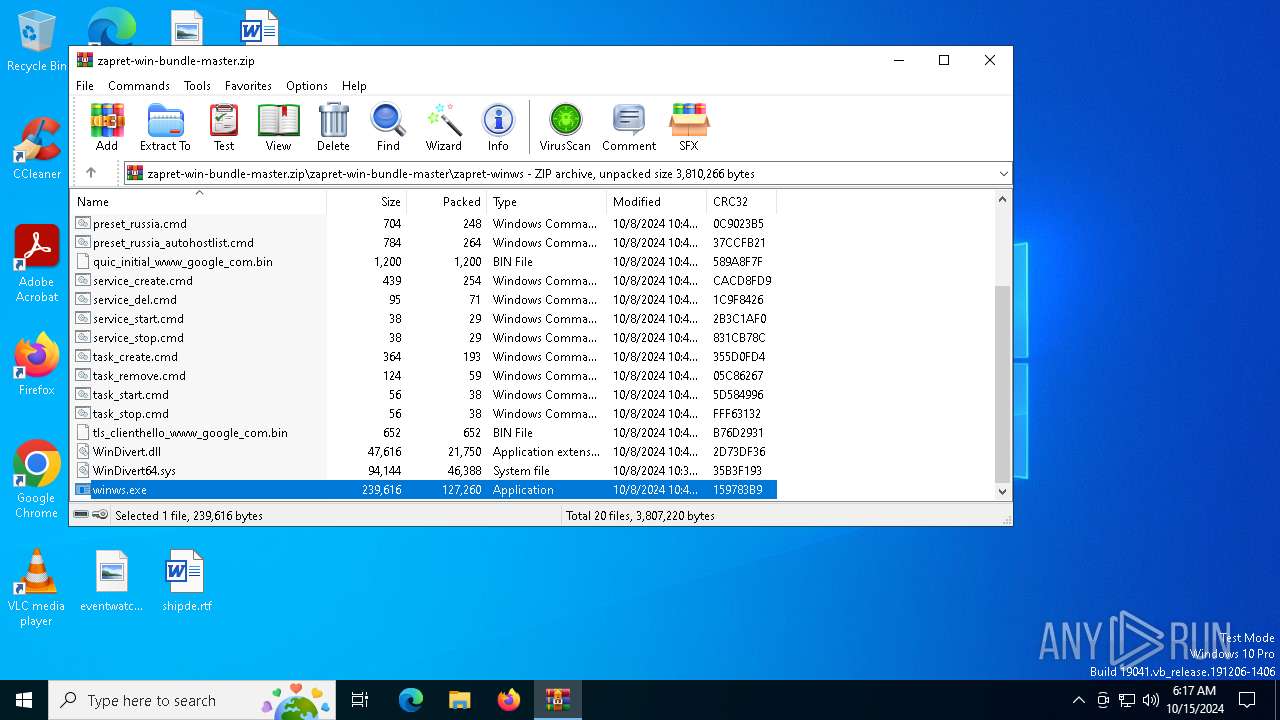
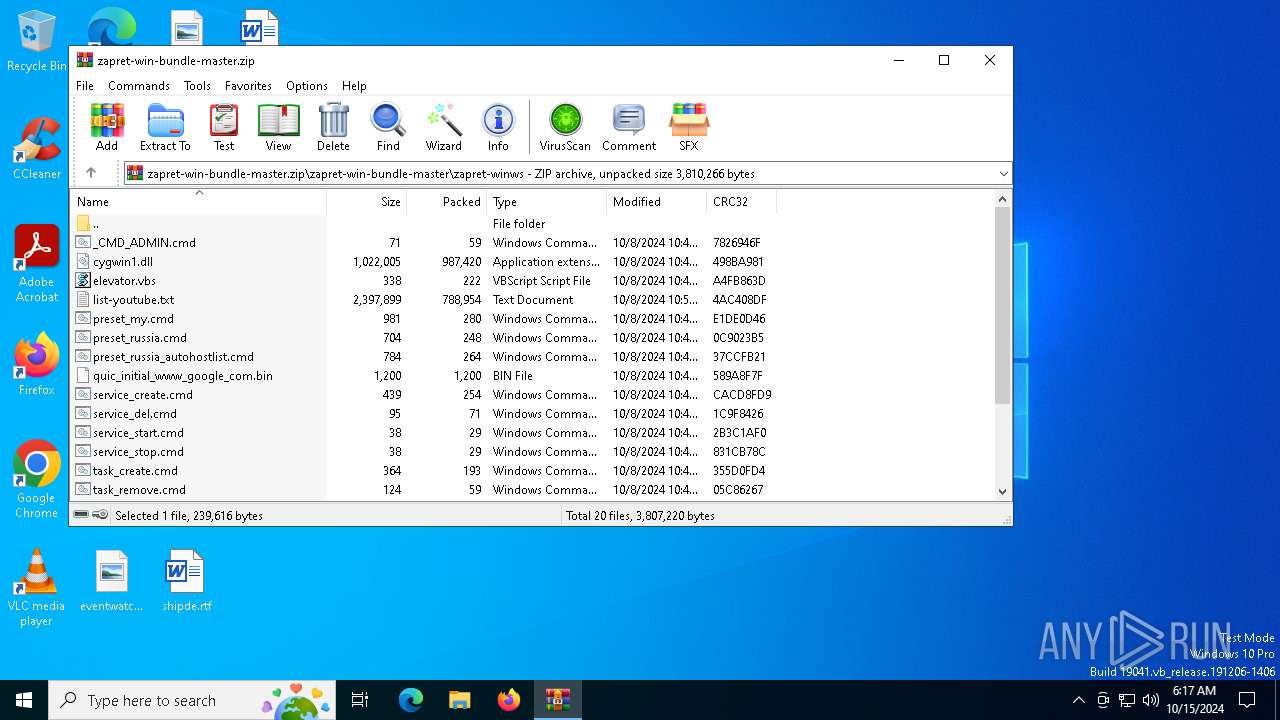
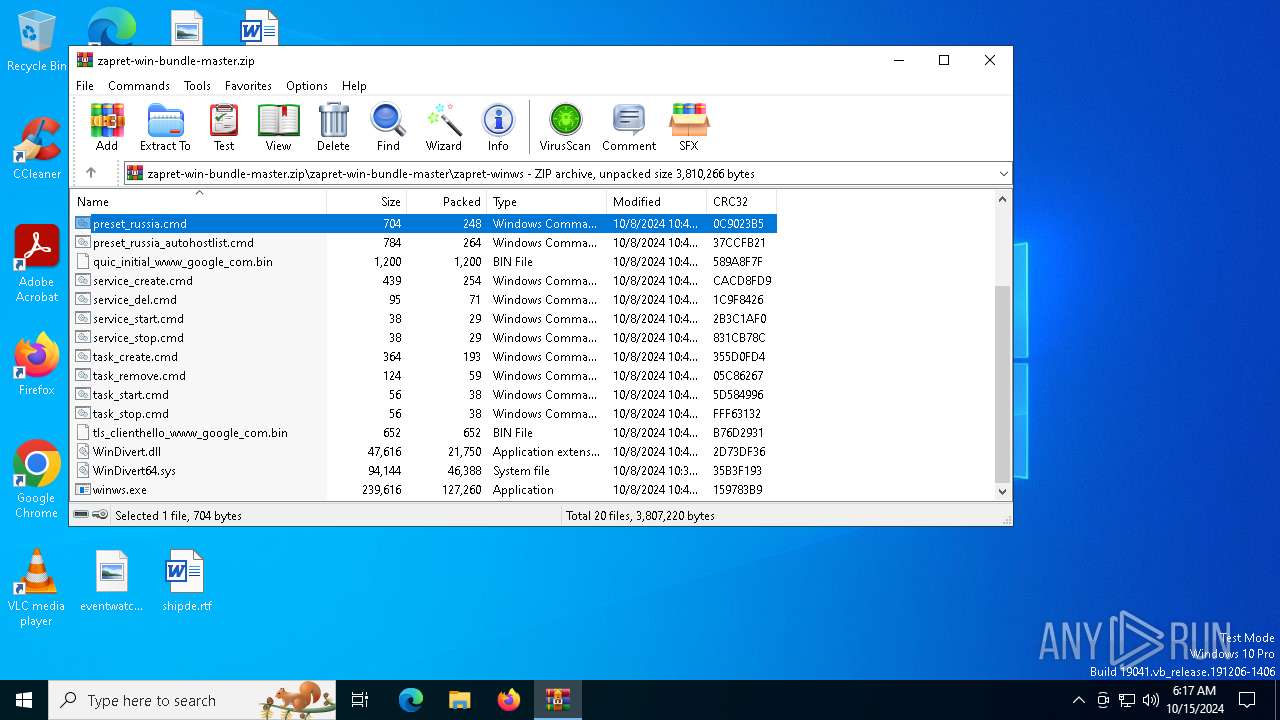
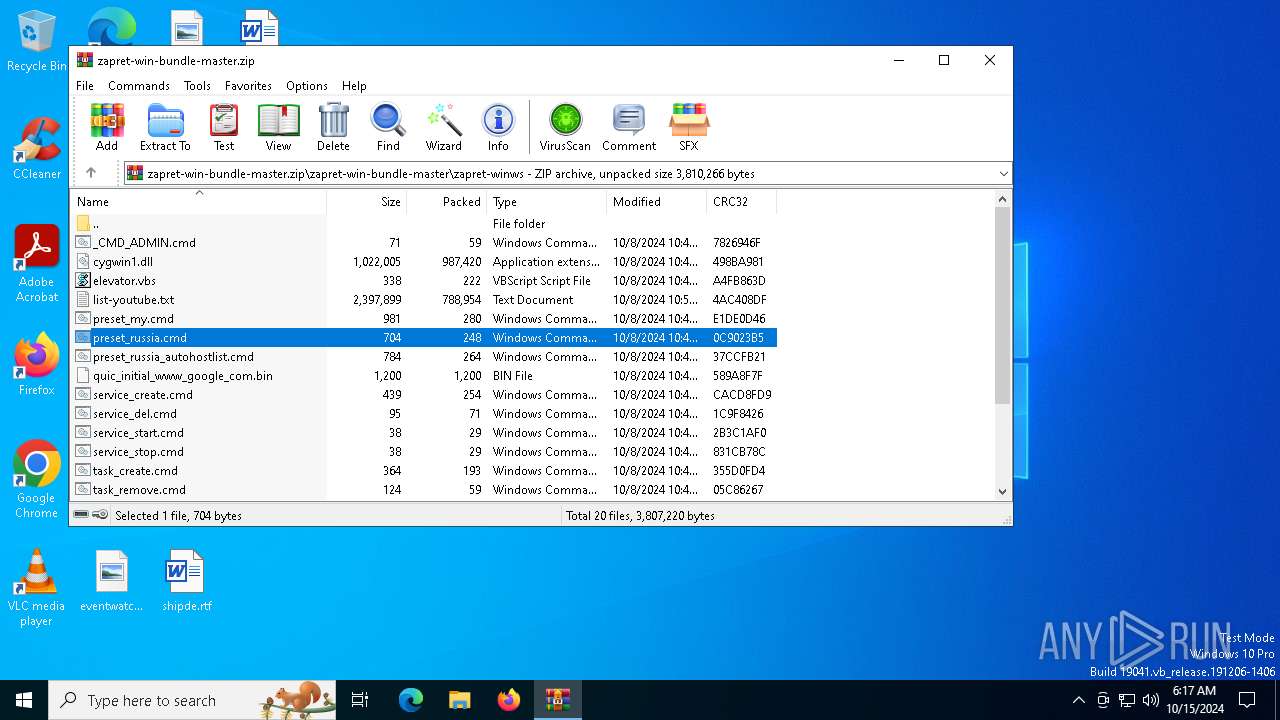
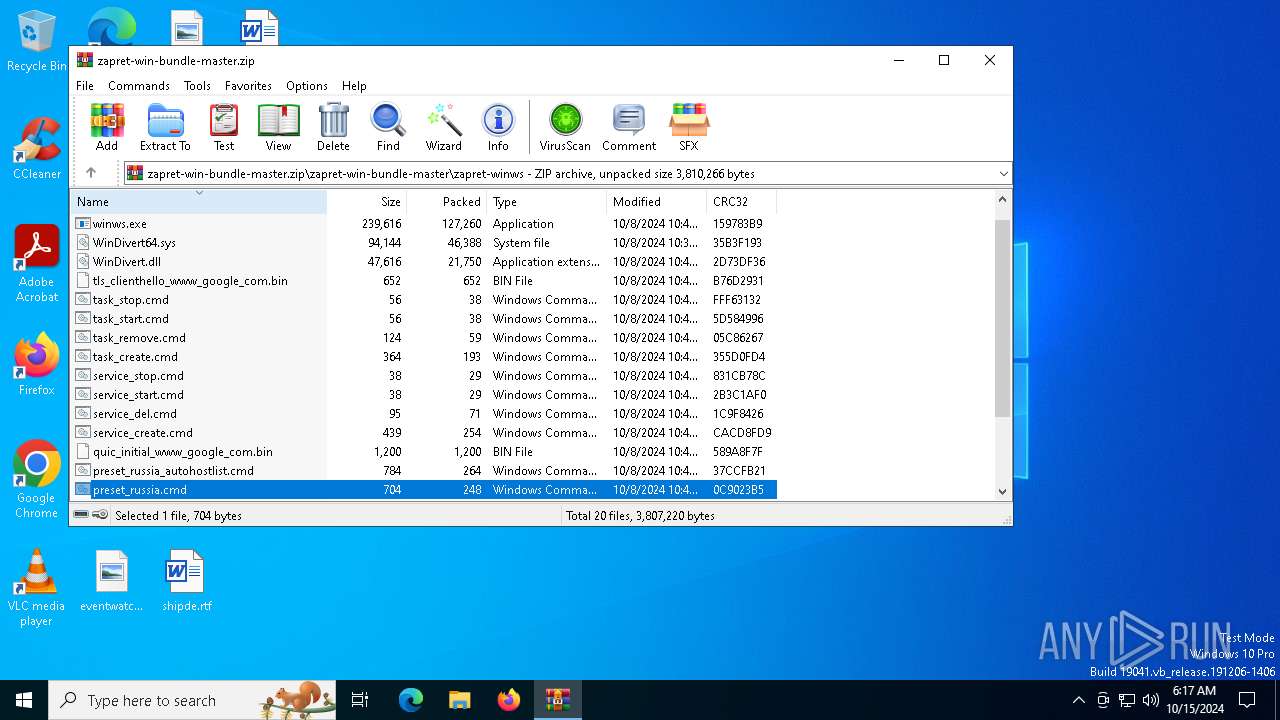
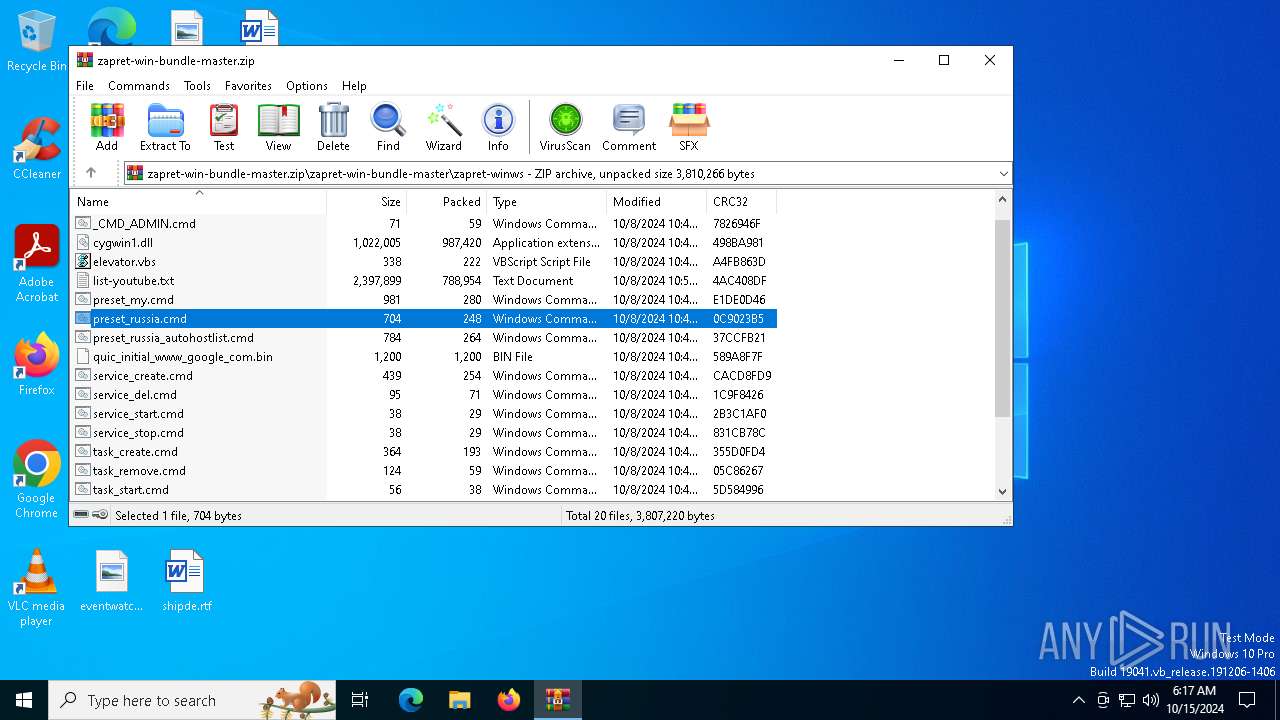
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master\readme.txt | text | |
MD5:6A68792C6E6FB60B72899F061D9F237E | SHA256:954C5FC8C8814B6C93DA4C9B4D619B6497A0D50BD756D7FC23B654F031EB5212 | |||
| 6024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master\.gitattributes | text | |
MD5:847ED55B058F99CA654DAA2F0363711A | SHA256:9CB902885C6862F5C4D719B24D0A795EE0B67F6A4EF5E6B75286DE914F33A81E | |||
| 6024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master\zapret-winws\_CMD_ADMIN.cmd | text | |
MD5:A85EC8EE1DF1E3446A93CF49A255A6A0 | SHA256:F2F154D70DA09B50A5B98D99521B1C827CA3118833CF025D332D5F196B5E2F7C | |||
| 6024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master\zapret-winws\cygwin1.dll | executable | |
MD5:C50B50303FAE4AFE7248307339A00D13 | SHA256:712C39A069541AFA69CFCBE01B422BD67B4201EEE7E94CC1327D4ED8B4FA2167 | |||
| 6024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master\zapret-winws\task_start.cmd | text | |
MD5:BD5E60DC6BCBBF7172BFAE77EBA9C79C | SHA256:62191A8A552EAFDAAB7AEECC7BB4D6A39EDD311AC3D1DE513414980C5CC7619A | |||
| 6024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master\zapret-winws\preset_russia.cmd | text | |
MD5:5C26D17967B7A5F9418381036B186250 | SHA256:75331E1C64004866BA5634B58D4A237DD9BF50516CCD2D99071BEE4704A4D3A9 | |||
| 6024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master\zapret-winws\list-youtube.txt | text | |
MD5:5F7FEBD86271CE67627D48402956FC33 | SHA256:AC4BABC3DCDBFE92741125DC7DA055F3239A94FEB8B69EE2839531E92806B753 | |||
| 6024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master\zapret-winws\preset_russia_autohostlist.cmd | text | |
MD5:260C8B9613747AD616A4E9955DF3002E | SHA256:802DD99D42533800204573913B40D1A9C113DA8175DB0C37BEA4BEA38AE1473D | |||
| 6024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master\zapret-winws\service_stop.cmd | text | |
MD5:5533593BF6AAE9330B67E0AE8C68B3F4 | SHA256:1D5DD1EF31643BC269BBFA3886CEB45ACDE1612840C3501535B09E6240B8C7D5 | |||
| 6024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6024.33427\zapret-win-bundle-master\zapret-winws\elevator.vbs | text | |
MD5:A0771738725F59E58C1827F393B28BD3 | SHA256:510EB28EF36BCAB2E83D57FF5E3A5FDA79303EC9AA2442B39FE9A8790B0C138C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
59
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5824 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6400 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6996 | SIHClient.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6996 | SIHClient.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1332 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.23.209.132:443 | — | Akamai International B.V. | GB | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |