| File name: | MEMESENSE.exe |
| Full analysis: | https://app.any.run/tasks/c6b185a2-66ca-46a1-bd21-d42eb13438cc |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | March 16, 2025, 17:48:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | FF3F0E9A9202FAC2B13DA6CC4A690526 |
| SHA1: | 51855F2B2073D49DF20CEDF5F4B6A280D3B4FF87 |
| SHA256: | 202693031F0C8D5B6014724F5B44AF8BEADAB162C2A378E210B492FFD3939E65 |
| SSDEEP: | 1536:SLVXLkuguCW9coVN4KHwxfHbQo1WtHiK6YJVDyOcFOdb6E:SxXz9cFKQxfHbQvEgVuOsOdWE |
MALICIOUS
Uses Task Scheduler to run other applications
- MEMESENSE.exe (PID: 1184)
XWORM has been detected
- MEMESENSE.exe (PID: 1184)
Changes the autorun value in the registry
- MEMESENSE.exe (PID: 1184)
- upeqhk.exe (PID: 5260)
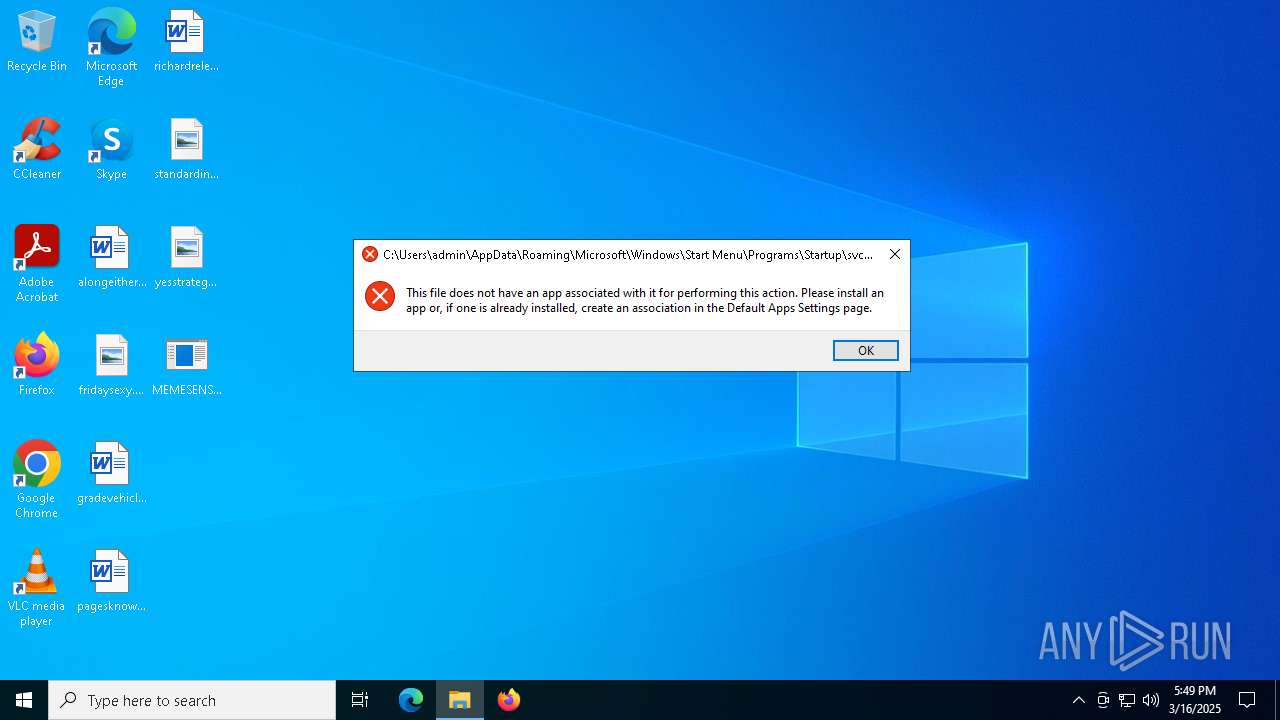
Create files in the Startup directory
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 208)
XWORM has been detected (YARA)
- MEMESENSE.exe (PID: 1184)
XWORM has been detected (SURICATA)
- MEMESENSE.exe (PID: 1184)
Adds path to the Windows Defender exclusion list
- eazzmz.exe (PID: 208)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 2656)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 2656)
Changes settings for real-time protection
- powershell.exe (PID: 2656)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 2656)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 2656)
Changes Controlled Folder Access settings
- powershell.exe (PID: 2656)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 2656)
Changes Windows Defender settings
- eazzmz.exe (PID: 208)
Actions looks like stealing of personal data
- eazzmz.exe (PID: 208)
DIVULGESTEALER has been detected (YARA)
- eazzmz.exe (PID: 208)
UMBRAL has been detected (YARA)
- eazzmz.exe (PID: 208)
DISCORDGRABBER has been detected (YARA)
- eazzmz.exe (PID: 208)
UMBRALSTEALER has been detected (YARA)
- eazzmz.exe (PID: 208)
Steals credentials from Web Browsers
- eazzmz.exe (PID: 208)
UMBRALSTEALER has been detected (SURICATA)
- eazzmz.exe (PID: 208)
Starts CMD.EXE for self-deleting
- eazzmz.exe (PID: 208)
SUSPICIOUS
The process creates files with name similar to system file names
- MEMESENSE.exe (PID: 1184)
Reads security settings of Internet Explorer
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 6876)
Reads the date of Windows installation
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 6876)
Checks for external IP
- svchost.exe (PID: 2196)
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 6876)
- eazzmz.exe (PID: 208)
Executable content was dropped or overwritten
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 208)
Connects to unusual port
- MEMESENSE.exe (PID: 1184)
Contacting a server suspected of hosting an CnC
- MEMESENSE.exe (PID: 1184)
The process executes via Task Scheduler
- svchost.exe (PID: 1348)
- svchost.exe (PID: 6132)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 6136)
- WMIC.exe (PID: 3304)
- WMIC.exe (PID: 5576)
Uses WMIC.EXE to obtain Windows Installer data
- eazzmz.exe (PID: 6876)
- eazzmz.exe (PID: 208)
Uses ATTRIB.EXE to modify file attributes
- eazzmz.exe (PID: 208)
Application launched itself
- eazzmz.exe (PID: 6876)
Script adds exclusion path to Windows Defender
- eazzmz.exe (PID: 208)
Script disables Windows Defender's real-time protection
- eazzmz.exe (PID: 208)
Script disables Windows Defender's IPS
- eazzmz.exe (PID: 208)
Starts POWERSHELL.EXE for commands execution
- eazzmz.exe (PID: 208)
Modifies hosts file to alter network resolution
- eazzmz.exe (PID: 208)
Uses WMIC.EXE to obtain computer system information
- eazzmz.exe (PID: 208)
Uses WMIC.EXE to obtain operating system information
- eazzmz.exe (PID: 208)
Possible usage of Discord/Telegram API has been detected (YARA)
- eazzmz.exe (PID: 208)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 5344)
Starts CMD.EXE for commands execution
- eazzmz.exe (PID: 208)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 4420)
Uses WMIC.EXE to obtain a list of video controllers
- eazzmz.exe (PID: 208)
The process connected to a server suspected of theft
- eazzmz.exe (PID: 208)
There is functionality for taking screenshot (YARA)
- upeqhk.exe (PID: 5260)
INFO
Reads Environment values
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 6876)
- eazzmz.exe (PID: 208)
Reads the computer name
- MEMESENSE.exe (PID: 1184)
- svchost.exe (PID: 1452)
- eazzmz.exe (PID: 6876)
- svchost.exe (PID: 1348)
- eazzmz.exe (PID: 208)
- upeqhk.exe (PID: 5260)
- svchost.exe (PID: 6132)
Disables trace logs
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 6876)
- eazzmz.exe (PID: 208)
Checks proxy server information
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 6876)
- eazzmz.exe (PID: 208)
- slui.exe (PID: 6272)
Creates files or folders in the user directory
- MEMESENSE.exe (PID: 1184)
Autorun file from Startup directory
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 208)
Process checks computer location settings
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 6876)
Autorun file from Registry key
- MEMESENSE.exe (PID: 1184)
- upeqhk.exe (PID: 5260)
Checks supported languages
- MEMESENSE.exe (PID: 1184)
- svchost.exe (PID: 1452)
- eazzmz.exe (PID: 6876)
- svchost.exe (PID: 1348)
- eazzmz.exe (PID: 208)
- upeqhk.exe (PID: 5260)
- svchost.exe (PID: 6132)
Reads the machine GUID from the registry
- MEMESENSE.exe (PID: 1184)
- svchost.exe (PID: 1452)
- eazzmz.exe (PID: 6876)
- svchost.exe (PID: 1348)
- eazzmz.exe (PID: 208)
- svchost.exe (PID: 6132)
Manual execution by a user
- svchost.exe (PID: 1452)
Create files in a temporary directory
- MEMESENSE.exe (PID: 1184)
- eazzmz.exe (PID: 208)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6136)
- WMIC.exe (PID: 3304)
- WMIC.exe (PID: 2288)
- WMIC.exe (PID: 5344)
- WMIC.exe (PID: 5576)
- WMIC.exe (PID: 4420)
Reads the software policy settings
- eazzmz.exe (PID: 6876)
- eazzmz.exe (PID: 208)
- slui.exe (PID: 6272)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4464)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4464)
- powershell.exe (PID: 2656)
- powershell.exe (PID: 5036)
- powershell.exe (PID: 1812)
Creates files in the program directory
- eazzmz.exe (PID: 208)
Compiled with Borland Delphi (YARA)
- eazzmz.exe (PID: 208)
- slui.exe (PID: 6272)
- upeqhk.exe (PID: 5260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(1184) MEMESENSE.exe
C2century-descriptions.gl.at.ply.gg:56555
Keys
AES123456789
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm V5.6
MutexpTKXNWQR7q52SsIw
ims-api
(PID) Process(208) eazzmz.exe
Discord-Webhook-Tokens (1)1337795979705057310/-AuGZrJ73Wlhcg6sqa2d8tjO7VOkmO4JlfI9eQ1rnNS49Q-ZG-mXghXafgbSYxIuhWJp
Discord-Info-Links
1337795979705057310/-AuGZrJ73Wlhcg6sqa2d8tjO7VOkmO4JlfI9eQ1rnNS49Q-ZG-mXghXafgbSYxIuhWJp
Get Webhook Infohttps://discord.com/api/webhooks/1337795979705057310/-AuGZrJ73Wlhcg6sqa2d8tjO7VOkmO4JlfI9eQ1rnNS49Q-ZG-mXghXafgbSYxIuhWJp
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:16 12:15:59+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 72704 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13b6e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | MEMESENSE.exe |
| LegalCopyright: | |
| OriginalFileName: | MEMESENSE.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
160
Monitored processes
38
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\AppData\Local\Temp\eazzmz.exe" | C:\Users\admin\AppData\Local\Temp\eazzmz.exe | eazzmz.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
ims-api(PID) Process(208) eazzmz.exe Discord-Webhook-Tokens (1)1337795979705057310/-AuGZrJ73Wlhcg6sqa2d8tjO7VOkmO4JlfI9eQ1rnNS49Q-ZG-mXghXafgbSYxIuhWJp Discord-Info-Links 1337795979705057310/-AuGZrJ73Wlhcg6sqa2d8tjO7VOkmO4JlfI9eQ1rnNS49Q-ZG-mXghXafgbSYxIuhWJp Get Webhook Infohttps://discord.com/api/webhooks/1337795979705057310/-AuGZrJ73Wlhcg6sqa2d8tjO7VOkmO4JlfI9eQ1rnNS49Q-ZG-mXghXafgbSYxIuhWJp | |||||||||||||||
| 536 | ping localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | "C:\Windows\System32\schtasks.exe" /create /f /sc minute /mo 1 /tn "svchost" /tr "C:\Users\admin\svchost.exe" | C:\Windows\System32\schtasks.exe | — | MEMESENSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "C:\Users\admin\Desktop\MEMESENSE.exe" | C:\Users\admin\Desktop\MEMESENSE.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 1.0.0.0 Modules
XWorm(PID) Process(1184) MEMESENSE.exe C2century-descriptions.gl.at.ply.gg:56555 Keys AES123456789 Options Splitter<Xwormmm> Sleep time3 USB drop nameXWorm V5.6 MutexpTKXNWQR7q52SsIw | |||||||||||||||
| 1348 | "C:\Users\admin\svchost.exe" | C:\Users\admin\svchost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1452 | "C:\Users\admin\svchost.exe" | C:\Users\admin\svchost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | "powershell.exe" Get-ItemPropertyValue -Path HKLN:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | eazzmz.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1968 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
36 484
Read events
36 452
Write events
32
Delete events
0
Modification events
| (PID) Process: | (1184) MEMESENSE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MEMESENSE_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1184) MEMESENSE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MEMESENSE_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1184) MEMESENSE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MEMESENSE_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1184) MEMESENSE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MEMESENSE_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1184) MEMESENSE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MEMESENSE_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1184) MEMESENSE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MEMESENSE_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1184) MEMESENSE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MEMESENSE_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1184) MEMESENSE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MEMESENSE_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1184) MEMESENSE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MEMESENSE_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1184) MEMESENSE.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MEMESENSE_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
4
Suspicious files
8
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4464 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4gdwx3xs.3uq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1184 | MEMESENSE.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\svchost.lnk | binary | |
MD5:D4E1F86FEBBBB1683B55138B36C18F27 | SHA256:C0292E8911A6484DBBF2282224377F0ECE0FFE43F6CB061C902ED8828E03AC64 | |||
| 4464 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mbzy20q0.5is.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1184 | MEMESENSE.exe | C:\Users\admin\AppData\Local\Temp\upeqhk.exe | executable | |
MD5:2D46646EE742BB8977E2E6F180015674 | SHA256:B563BB3D1FD04257C5BCFC73F3E030C61DDB7FEA1ACA5189355EB230B4312164 | |||
| 208 | eazzmz.exe | C:\Users\admin\AppData\Local\Temp\iHorWpr2EpHaM1O | binary | |
MD5:09A22B1BCD9725DF5B3591EBBD2CEBD6 | SHA256:4F81904A9B06C58572A0E5769B3B4FFB99E7BD4BE88EE8C2B64A804F483D9DC6 | |||
| 2656 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dxcozm1v.dln.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 208 | eazzmz.exe | C:\Users\admin\AppData\Local\Temp\YgI4IwZY5MKIfot | binary | |
MD5:46D9FCA6032297F8AEE08D73418312BA | SHA256:865856FA4C33C4AEE52E15FBB370B6611468FE947E76E197F0E50D0AD62CB1B4 | |||
| 5036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1434zemg.dij.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1812 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rrxbxm2w.tnv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 208 | eazzmz.exe | C:\Users\admin\AppData\Local\Temp\WB9FWjxTOORN2th | binary | |
MD5:06AD9E737639FDC745B3B65312857109 | SHA256:C8925892CA8E213746633033AE95ACFB8DD9531BC376B82066E686AC6F40A404 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
32
DNS requests
9
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.184.195:443 | https://gstatic.com/generate_204 | unknown | — | — | unknown |
208 | eazzmz.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | whitelisted |
1184 | MEMESENSE.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
— | — | POST | 404 | 162.159.137.232:443 | https://discord.com/api/webhooks/1337795979705057310/-AuGZrJ73Wlhcg6sqa2d8tjO7VOkmO4JlfI9eQ1rnNS49Q-ZG-mXghXafgbSYxIuhWJp | unknown | binary | 45 b | whitelisted |
— | — | POST | 404 | 162.159.135.232:443 | https://discord.com/api/webhooks/1337795979705057310/-AuGZrJ73Wlhcg6sqa2d8tjO7VOkmO4JlfI9eQ1rnNS49Q-ZG-mXghXafgbSYxIuhWJp | unknown | binary | 45 b | whitelisted |
— | — | POST | 500 | 52.161.91.37:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | GET | 204 | 142.250.184.195:443 | https://gstatic.com/generate_204 | unknown | — | — | unknown |
— | — | POST | 500 | 52.161.91.37:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
6876 | eazzmz.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
208 | eazzmz.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1184 | MEMESENSE.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
1184 | MEMESENSE.exe | 147.185.221.25:56555 | century-descriptions.gl.at.ply.gg | PLAYIT-GG | US | malicious |
5216 | slui.exe | 52.161.91.37:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6876 | eazzmz.exe | 142.250.185.227:443 | gstatic.com | GOOGLE | US | whitelisted |
6876 | eazzmz.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
208 | eazzmz.exe | 142.250.185.227:443 | gstatic.com | GOOGLE | US | whitelisted |
208 | eazzmz.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ip-api.com |
| whitelisted |
century-descriptions.gl.at.ply.gg |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
gstatic.com |
| whitelisted |
discord.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
1184 | MEMESENSE.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
1184 | MEMESENSE.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
1184 | MEMESENSE.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm TCP Packet |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |