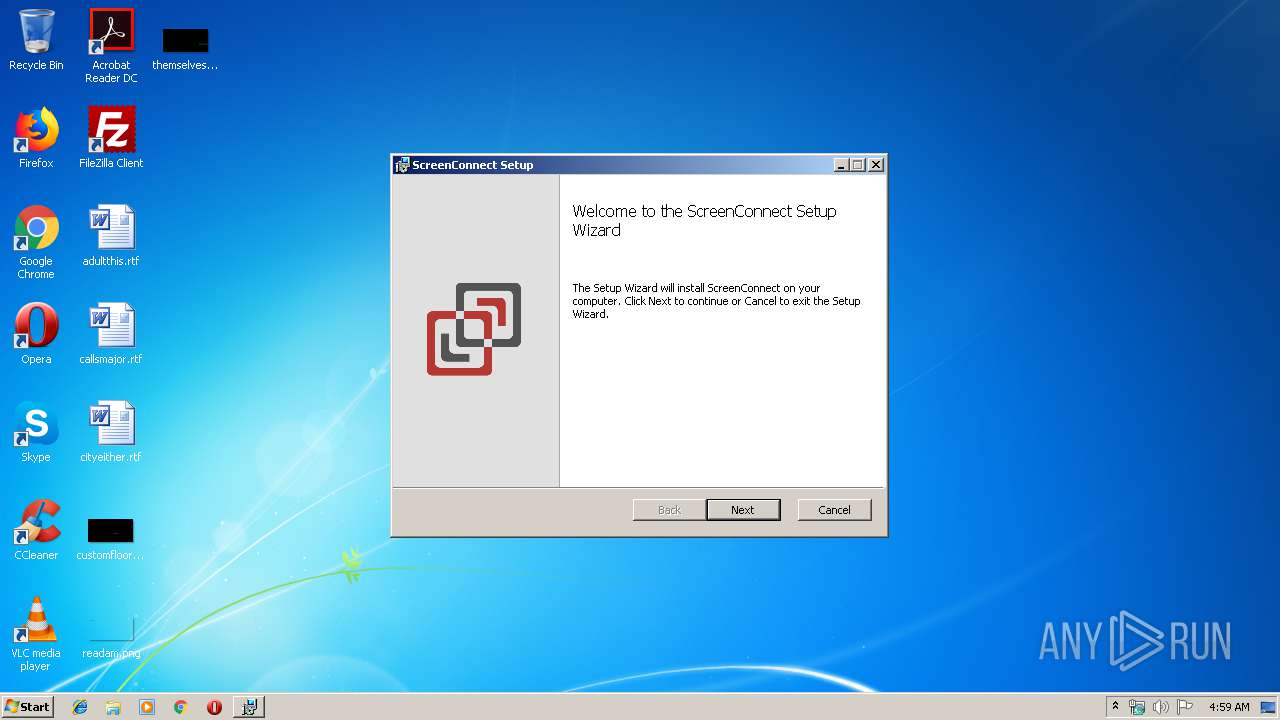
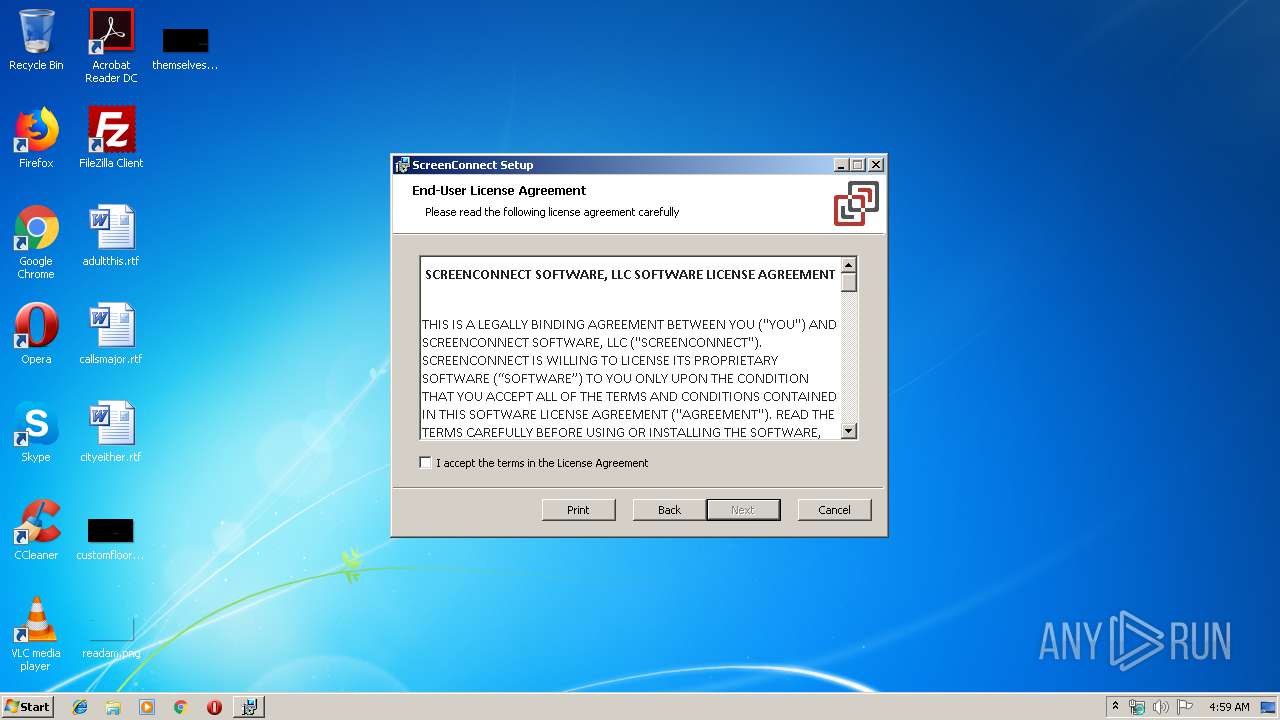
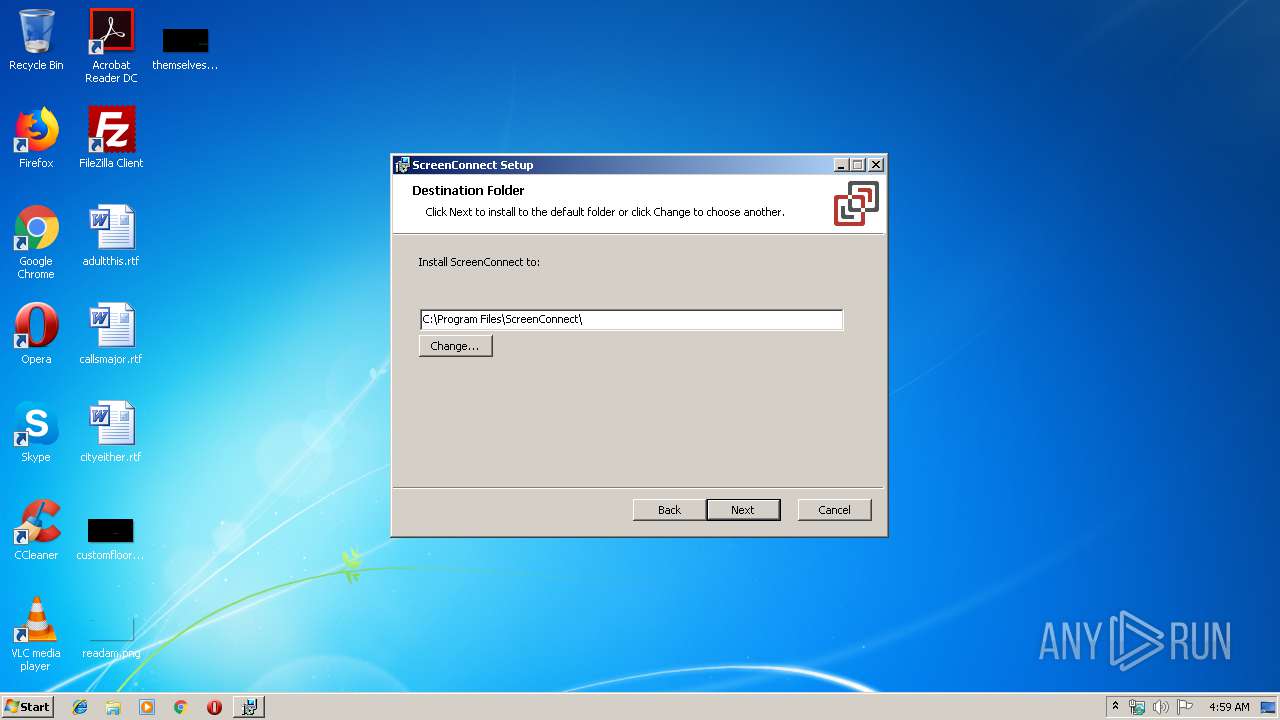
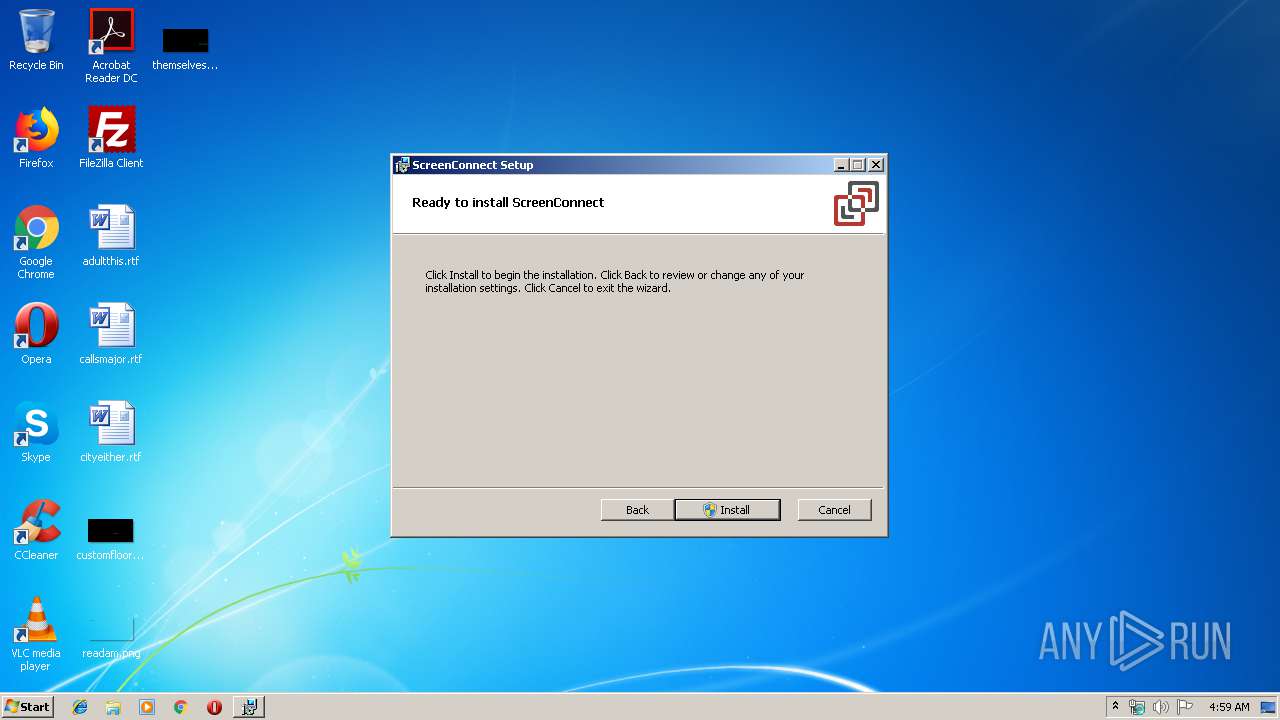
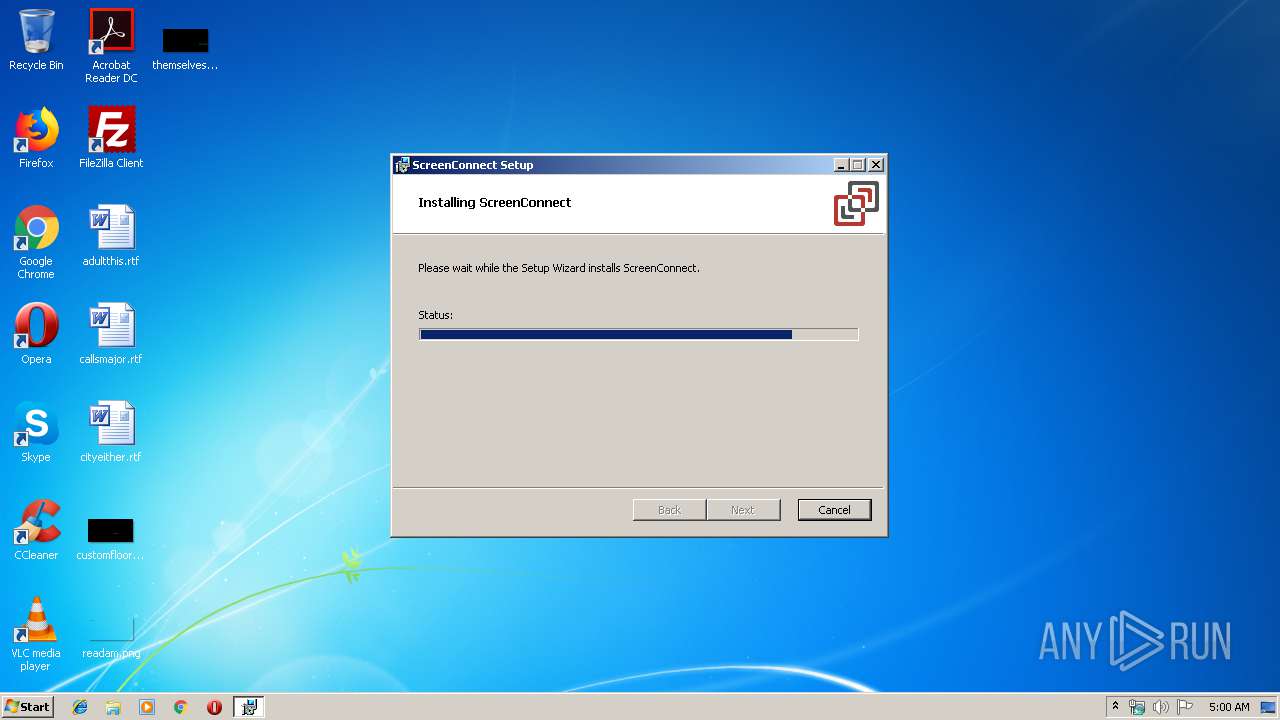
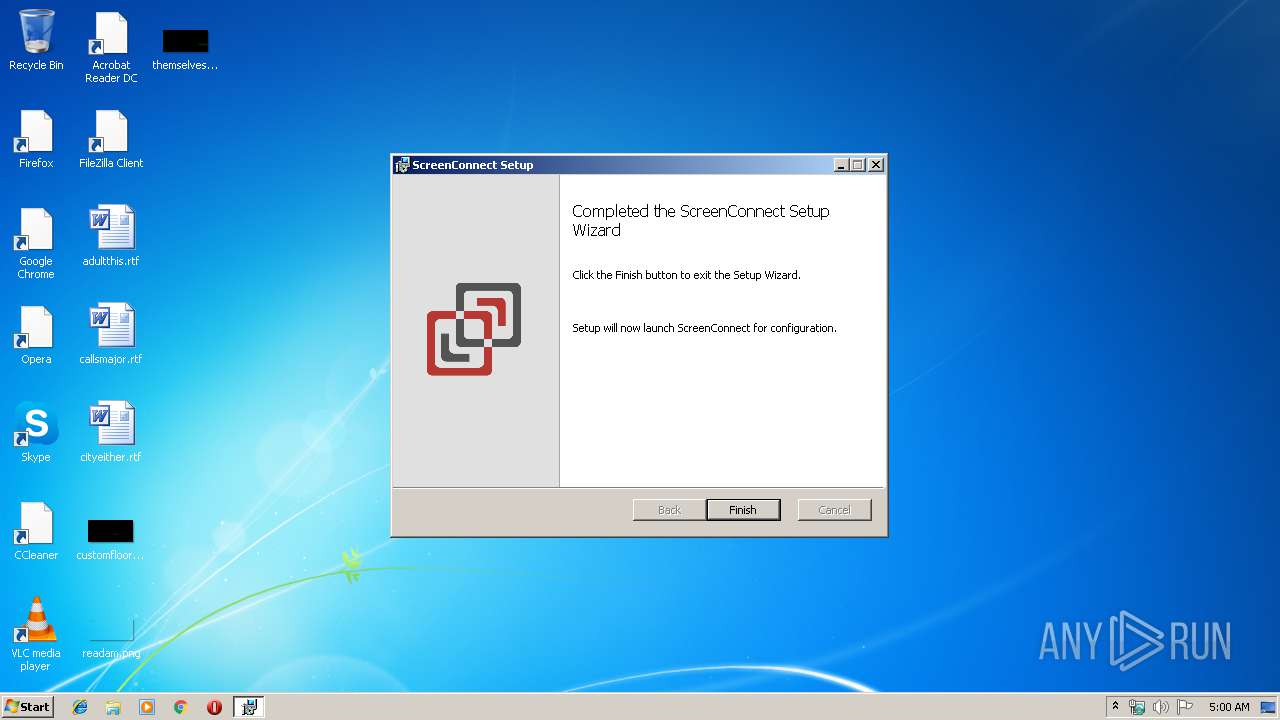
| download: | ScreenConnect_6.8.20124.6845_Release.msi |
| Full analysis: | https://app.any.run/tasks/94392781-f9ba-4bc0-b19f-5e1221bcf1b7 |
| Verdict: | Malicious activity |
| Analysis date: | August 28, 2019, 03:59:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: ScreenConnect, Author: ScreenConnect Software, Keywords: Installer, Comments: This installer database contains the logic and data required to install ScreenConnect., Template: Intel;1033, Revision Number: {55CE8F34-FE85-4C06-9439-34BEB111AD31}, Create Time/Date: Fri Sep 28 15:02:50 2018, Last Saved Time/Date: Fri Sep 28 15:02:50 2018, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.0.1701), Security: 2 |
| MD5: | E0E63BCAA3409176BAB90CC07A0B7825 |
| SHA1: | A03869A96FEBEAB45F90612DF3BFB2A89A35FA9D |
| SHA256: | 2023FFA5D0DFF7DCC23945446C702D3BDEE3FF4E72E1E403C2B0BC74EA4A927C |
| SSDEEP: | 786432:S08Y13ltm6wFzNuil7EspH4oSayCN3gQbBy3:S08YHHwFzoZs/SayNQ |
MALICIOUS
Changes settings of System certificates
- msiexec.exe (PID: 2188)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3996)
- ScreenConnect.Service.exe (PID: 2768)
- rundll32.exe (PID: 3988)
- rundll32.exe (PID: 2408)
- ScreenConnect.Service.exe (PID: 2372)
Application was dropped or rewritten from another process
- Xsl.exe (PID: 2540)
- ScreenConnect.Service.exe (PID: 2768)
- Xsl.exe (PID: 3016)
- Xsl.exe (PID: 3288)
- ScreenConnect.Service.exe (PID: 2372)
Starts Visual C# compiler
- ScreenConnect.Service.exe (PID: 2768)
- Xsl.exe (PID: 3016)
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 3824)
- ScreenConnect.Service.exe (PID: 2768)
Executed via COM
- DrvInst.exe (PID: 3968)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 2984)
- MsiExec.exe (PID: 3564)
Executable content was dropped or overwritten
- rundll32.exe (PID: 3996)
- msiexec.exe (PID: 2580)
- csc.exe (PID: 3228)
- csc.exe (PID: 3664)
- csc.exe (PID: 2472)
- csc.exe (PID: 2360)
Creates files in the program directory
- ScreenConnect.Service.exe (PID: 2768)
Reads Environment values
- ScreenConnect.Service.exe (PID: 2768)
Removes files from Windows directory
- ScreenConnect.Service.exe (PID: 2768)
- csc.exe (PID: 3228)
- csc.exe (PID: 3664)
- csc.exe (PID: 2472)
- csc.exe (PID: 2360)
Creates files in the Windows directory
- ScreenConnect.Service.exe (PID: 2768)
- csc.exe (PID: 3228)
- csc.exe (PID: 3664)
- csc.exe (PID: 2472)
- csc.exe (PID: 2360)
Starts CMD.EXE for commands execution
- MsiExec.exe (PID: 3564)
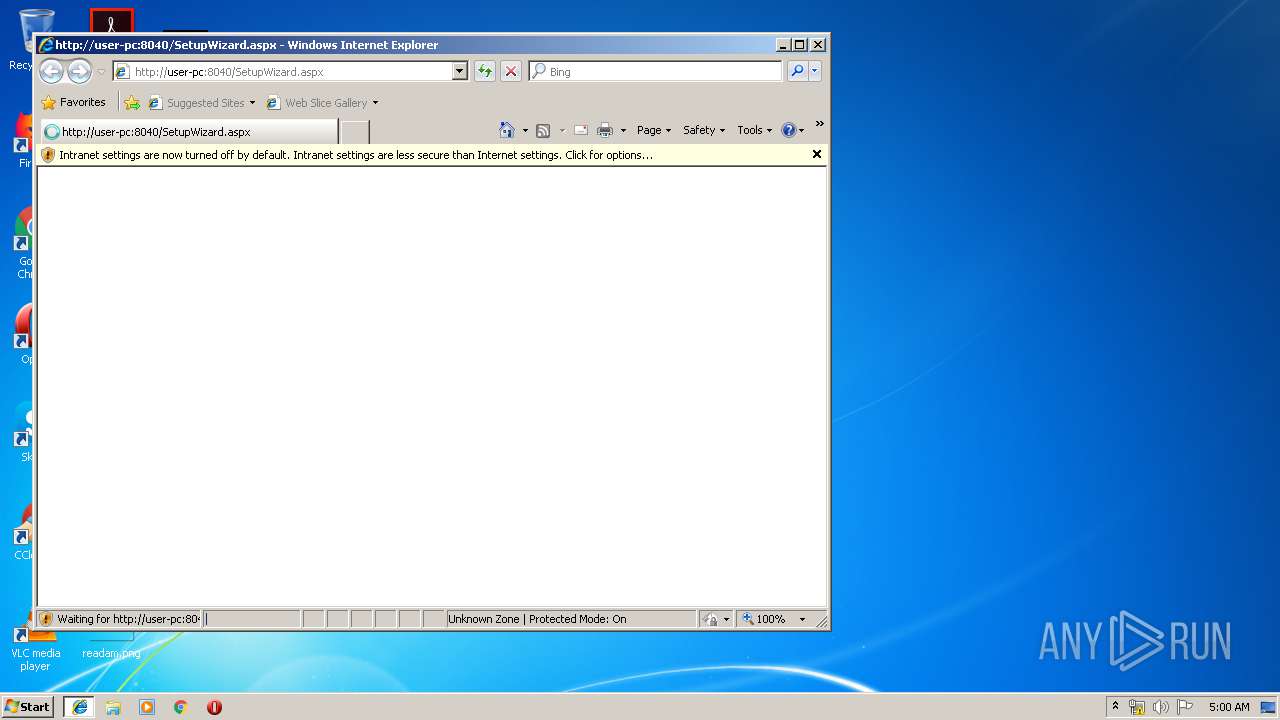
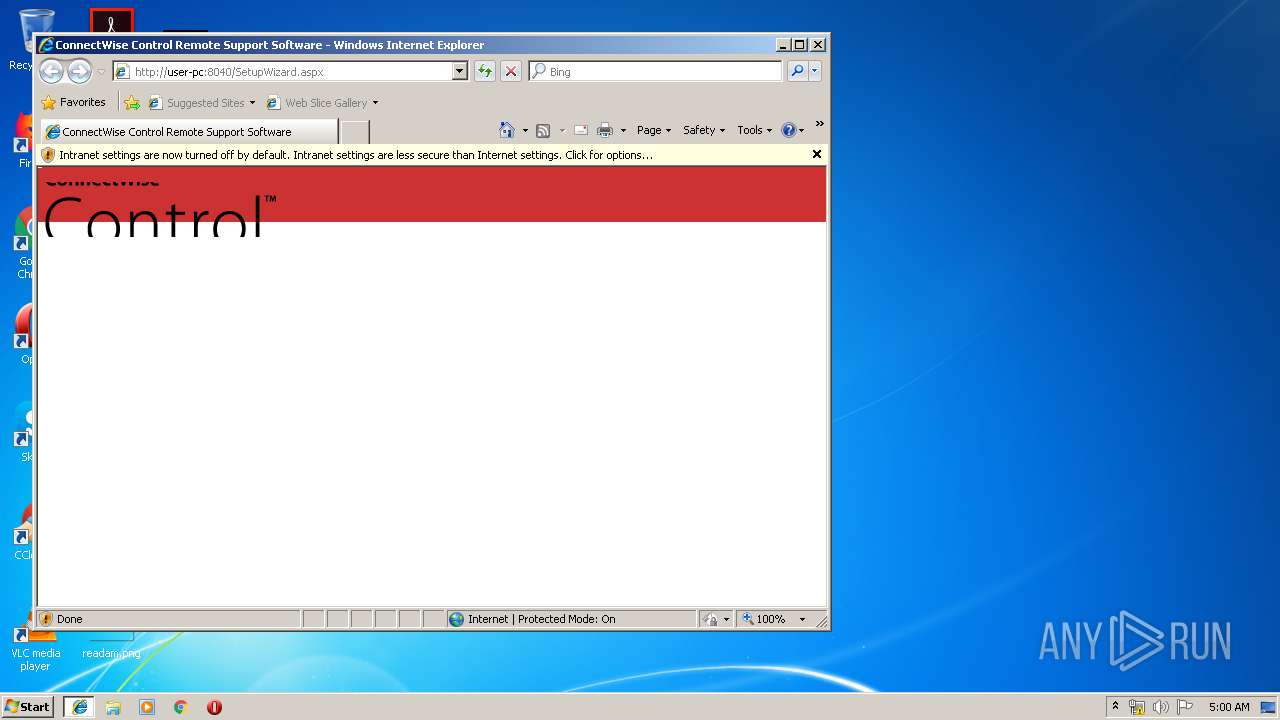
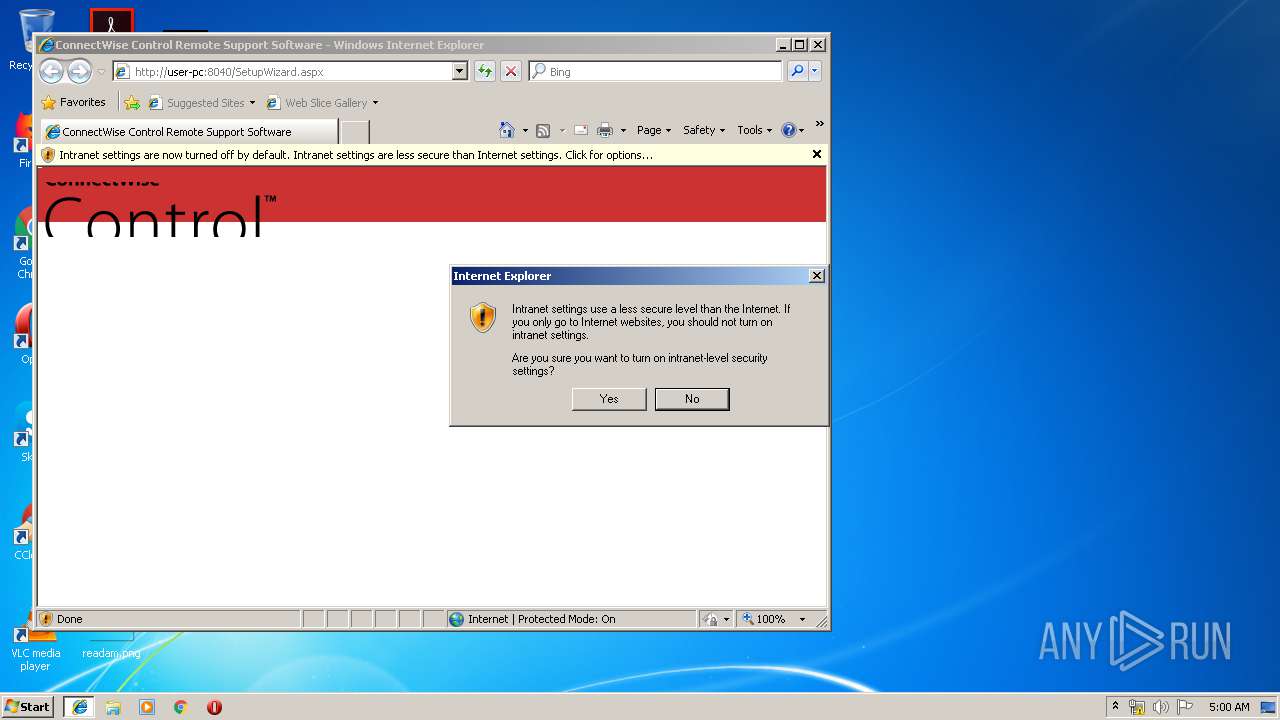
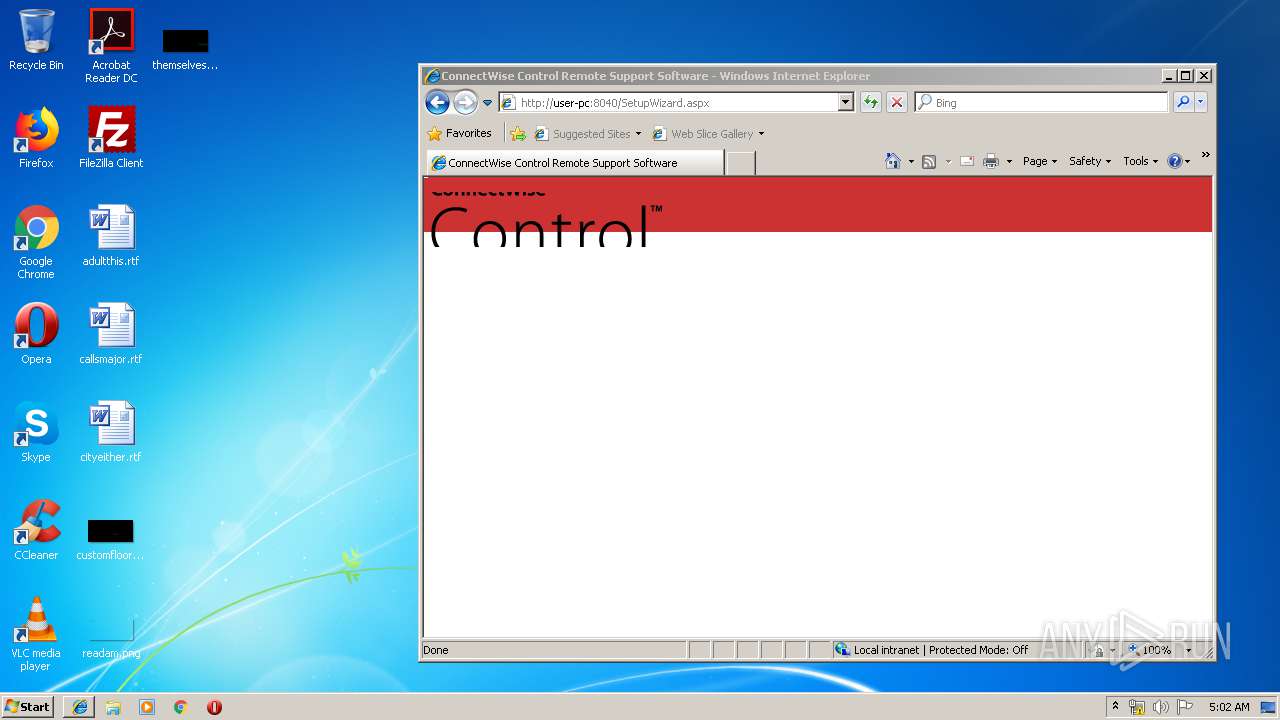
Starts Internet Explorer
- ScreenConnect.Service.exe (PID: 2372)
INFO
Changes settings of System certificates
- DrvInst.exe (PID: 3968)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3824)
Searches for installed software
- msiexec.exe (PID: 2580)
Application launched itself
- msiexec.exe (PID: 2580)
- iexplore.exe (PID: 2368)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2984)
- MsiExec.exe (PID: 3564)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3968)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2580)
Creates a software uninstall entry
- msiexec.exe (PID: 2580)
Reads internet explorer settings
- iexplore.exe (PID: 3288)
- iexplore.exe (PID: 3912)
Changes internet zones settings
- iexplore.exe (PID: 2368)
Reads Internet Cache Settings
- iexplore.exe (PID: 3288)
Manual execution by user
- opera.exe (PID: 1720)
Creates files in the program directory
- msiexec.exe (PID: 2580)
Creates files in the user directory
- iexplore.exe (PID: 2368)
- opera.exe (PID: 1720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | ScreenConnect |
| Author: | ScreenConnect Software |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install ScreenConnect. |
| Template: | Intel;1033 |
| RevisionNumber: | {55CE8F34-FE85-4C06-9439-34BEB111AD31} |
| CreateDate: | 2018:09:28 14:02:50 |
| ModifyDate: | 2018:09:28 14:02:50 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.0.1701) |
| Security: | Read-only recommended |
Total processes
69
Monitored processes
29
Malicious processes
8
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1720 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2168 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\bd4rlyau\bd4rlyau.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | Xsl.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2188 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect_6.8.20124.6845_Release.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Transform.cmd" "C:\Program Files\ScreenConnect\" "Release" "" "" "" """ | C:\Windows\system32\cmd.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2360 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Windows\Microsoft.NET\Framework\v4.0.30319\Temporary ASP.NET Files\root\28315708\1a0475de\nw4sdu3o.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | ScreenConnect.Service.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | ScreenConnect.Service.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | "C:\Program Files\ScreenConnect\Bin\ScreenConnect.Service.exe" launch administration | C:\Program Files\ScreenConnect\Bin\ScreenConnect.Service.exe | — | msiexec.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Service Exit code: 0 Version: 6.8.20124.6845 Modules
| |||||||||||||||
| 2408 | rundll32.exe "C:\Windows\Installer\MSI351C.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1521015 5 ScreenConnect.InstallerActions!ScreenConnect.InstallerActions.RestoreUpgradeableBackupFiles | C:\Windows\system32\rundll32.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Windows\Microsoft.NET\Framework\v4.0.30319\Temporary ASP.NET Files\root\28315708\1a0475de\4muancid.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | ScreenConnect.Service.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2540 | "C:\Users\admin\AppData\Local\Temp\Xsl.exe" "C:\Program Files\ScreenConnect\App_Data\Role.Xml" "C:\Users\admin\AppData\Local\Temp\TransformRoleXml.xsl" "C:\Program Files\ScreenConnect\App_Data\Role.Xml" "oldVersionMajor=""" "oldVersionMinor=""" "oldVersionBuild=""" "oldVersionRevision=""" | C:\Users\admin\AppData\Local\Temp\Xsl.exe | — | cmd.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
2 317
Read events
1 549
Write events
753
Delete events
15
Modification events
| (PID) Process: | (2188) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2188) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates\CA\Certificates\F5AD0BCC1AD56CD150725B1C866C30AD92EF21B0 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000F5AD0BCC1AD56CD150725B1C866C30AD92EF21B0140000000100000014000000BBAF7E023DFAA6F13C848EADEE3898ECD93232D40400000001000000100000001EDAF9AE99CE2920667D0E9A8B3F8C9C0F00000001000000300000007CE102D63C57CB48F80A65D1A5E9B350A7A618482AA5A36775323CA933DDFCB00DEF83796A6340DEC5EBF7596CFD8E5D19000000010000001000000082218FFB91733E64136BE5719F57C3A118000000010000001000000045ED9BBC5E43D3B9ECD63C060DB78E5C200000000100000078050000308205743082045CA00302010202102766EE56EB49F38EABD770A2FC84DE22300D06092A864886F70D01010C0500306F310B300906035504061302534531143012060355040A130B416464547275737420414231263024060355040B131D41646454727573742045787465726E616C20545450204E6574776F726B312230200603550403131941646454727573742045787465726E616C20434120526F6F74301E170D3030303533303130343833385A170D3230303533303130343833385A308185310B3009060355040613024742311B30190603550408131247726561746572204D616E636865737465723110300E0603550407130753616C666F7264311A3018060355040A1311434F4D4F444F204341204C696D69746564312B302906035504031322434F4D4F444F205253412043657274696669636174696F6E20417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A028202010091E85492D20A56B1AC0D24DDC5CF446774992B37A37D23700071BC53DFC4FA2A128F4B7F1056BD9F7072B7617FC94B0F17A73DE3B00461EEFF1197C7F4863E0AFA3E5CF993E6347AD9146BE79CB385A0827A76AF7190D7ECFD0DFA9C6CFADFB082F4147EF9BEC4A62F4F7F997FB5FC674372BD0C00D689EB6B2CD3ED8F981C14AB7EE5E36EFCD8A8E49224DA436B62B855FDEAC1BC6CB68BF30E8D9AE49B6C6999F878483045D5ADE10D3C4560FC32965127BC67C3CA2EB66BEA46C7C720A0B11F65DE4808BAA44EA9F283463784EBE8CC814843674E722A9B5CBD4C1B288A5C227BB4AB98D9EEE05183C309464E6D3E99FA9517DA7C3357413C8D51ED0BB65CAF2C631ADF57C83FBCE95DC49BAF4599E2A35A24B4BAA9563DCF6FAAFF4958BEF0A8FFF4B8ADE937FBBAB8F40B3AF9E843421E89D884CB13F1D9BBE18960B88C2856AC141D9C0AE771EBCF0EDD3DA996A148BD3CF7AFB50D224CC01181EC563BF6D3A2E25BB7B204225295809369E88E4C65F191032D707402EA8B671529695202BBD7DF506A5546BFA0A328617F70D0C3A2AA2C21AA47CE289C064576BF821827B4D5AEB4CB50E66BF44C867130E9A6DF1686E0D8FF40DDFBD042887FA3333A2E5C1E41118163CE18716B2BECA68AB7315C3A6A47E0C37959D6201AAFF26A98AA72BC574AD24B9DBB10FCB04C41E5ED1D3D5E289D9CCCBFB351DAA747E584530203010001A381F43081F1301F0603551D23041830168014ADBD987A34B426F7FAC42654EF03BDE024CB541A301D0603551D0E04160414BBAF7E023DFAA6F13C848EADEE3898ECD93232D4300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF30110603551D20040A300830060604551D200030440603551D1F043D303B3039A037A0358633687474703A2F2F63726C2E7573657274727573742E636F6D2F416464547275737445787465726E616C4341526F6F742E63726C303506082B0601050507010104293027302506082B060105050730018619687474703A2F2F6F6373702E7573657274727573742E636F6D300D06092A864886F70D01010C0500038201010064BF83F15F9A85D0CDB8A129570DE85AF7D1E93EF276046EF15270BB1E3CFF4D0D746ACC818225D3C3A02A5D4CF5BA8BA16DC4540975C7E3270E5D847937401377F5B4AC1CD03BAB1712D6EF34187E2BE979D3AB57450CAF28FAD0DBE5509588BBDF8557697D92D852CA7381BF1CF3E6B86E661105B31E942D7F91959259F14CCEA391714C7C470C3B0B19F6A1B16C863E5CAAC42E82CBF90796BA484D90F294C8A973A2EB067B239DDEA2F34D559F7A6145981868C75E406B23F5797AEF8CB56B8BB76F46F47BF13D4B04D89380595AE041241DB28F15605847DBEF6E46FD15F5D95F9AB3DBD8B8E440B3CD9739AE85BB1D8EBCDC879BD1A6EFF13B6F10386F | |||
| (PID) Process: | (2580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000404F5B09555DD501140A0000300E0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000404F5B09555DD501140A0000300E0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 24 | |||
| (PID) Process: | (2580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000AA0FBD09555DD501140A0000300E0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2580) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000000472BF09555DD501140A0000D40C0000E8030000010000000000000000000000C93BD7DEDCCEB34B8990421982D726870000000000000000 | |||
| (PID) Process: | (3824) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000006CFBC809555DD501F00E000064090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3824) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000006CFBC809555DD501F00E000050090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3824) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000006CFBC809555DD501F00E0000440D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
28
Suspicious files
55
Text files
338
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2188 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CabC568.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\TarC569.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CabC579.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\TarC57A.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CabC627.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\TarC628.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2580 | msiexec.exe | C:\Windows\Installer\1721c0.msi | — | |
MD5:— | SHA256:— | |||
| 3824 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2580 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFA64799EC55923886.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1720 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
2188 | msiexec.exe | GET | 200 | 92.122.213.201:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.6 Kb | whitelisted |
2368 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2188 | msiexec.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2188 | msiexec.exe | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
2368 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1720 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1720 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2188 | msiexec.exe | 92.122.213.201:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crt.comodoca.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.bing.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |