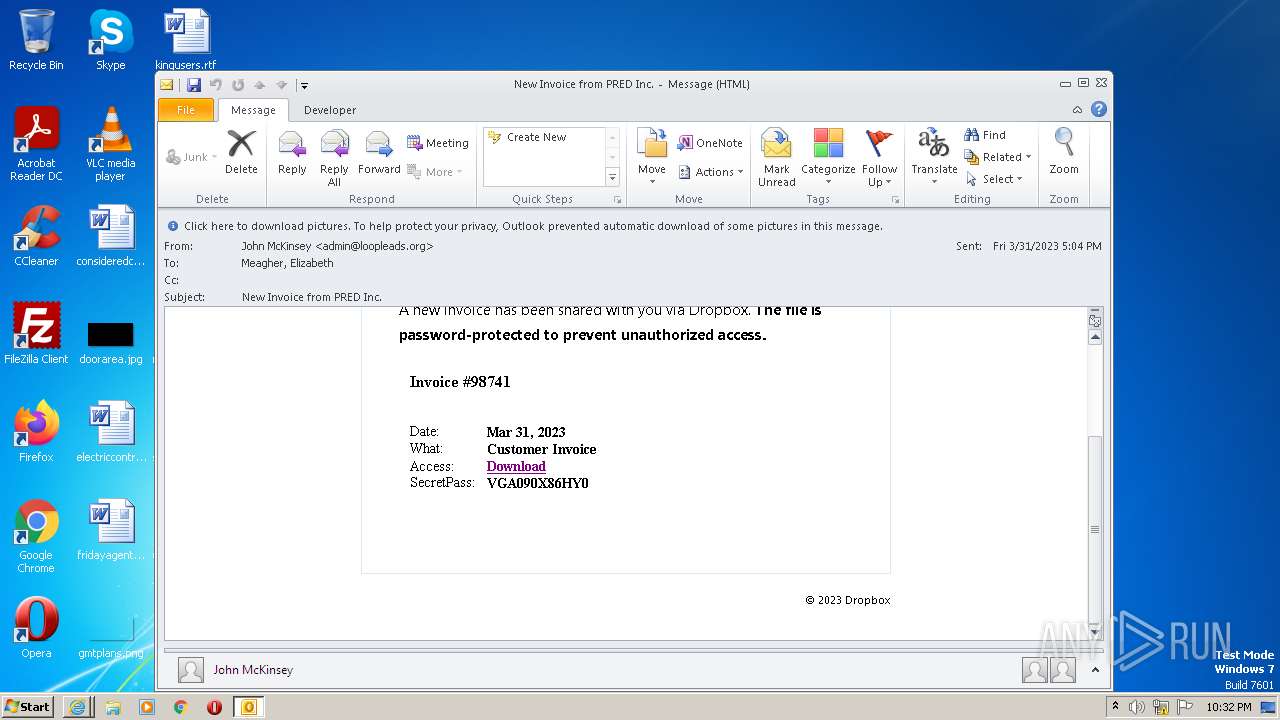
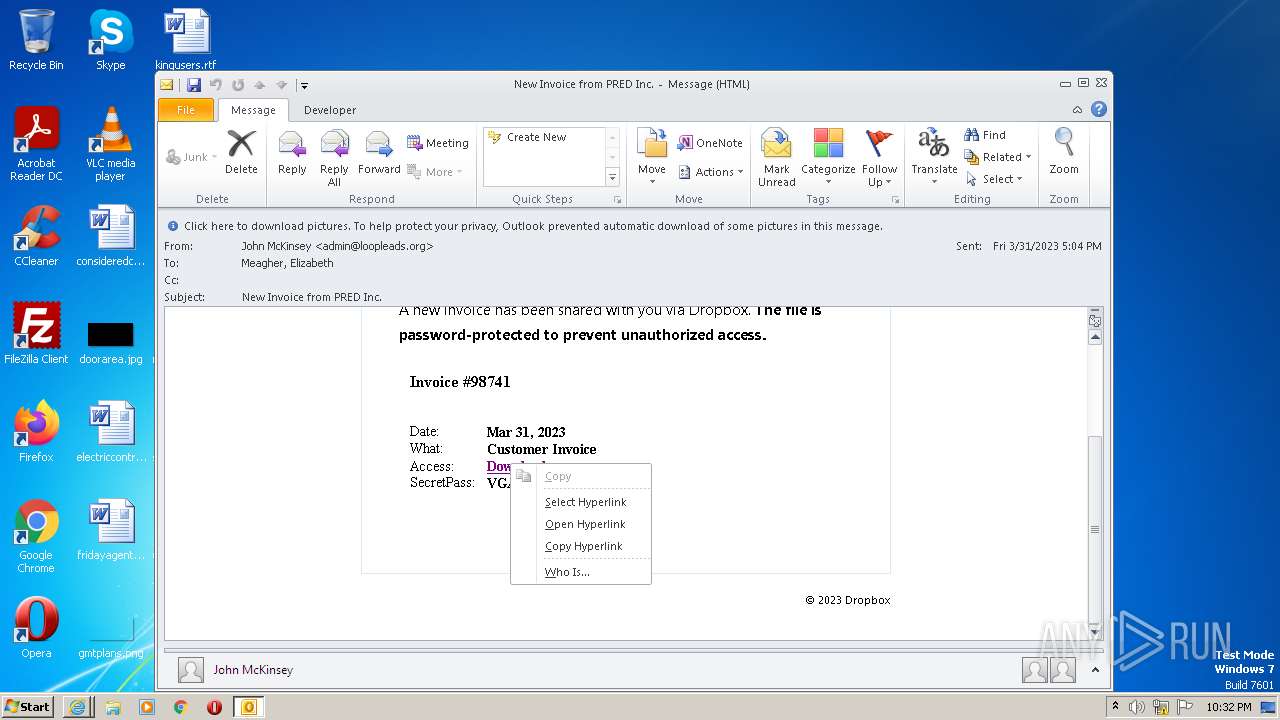
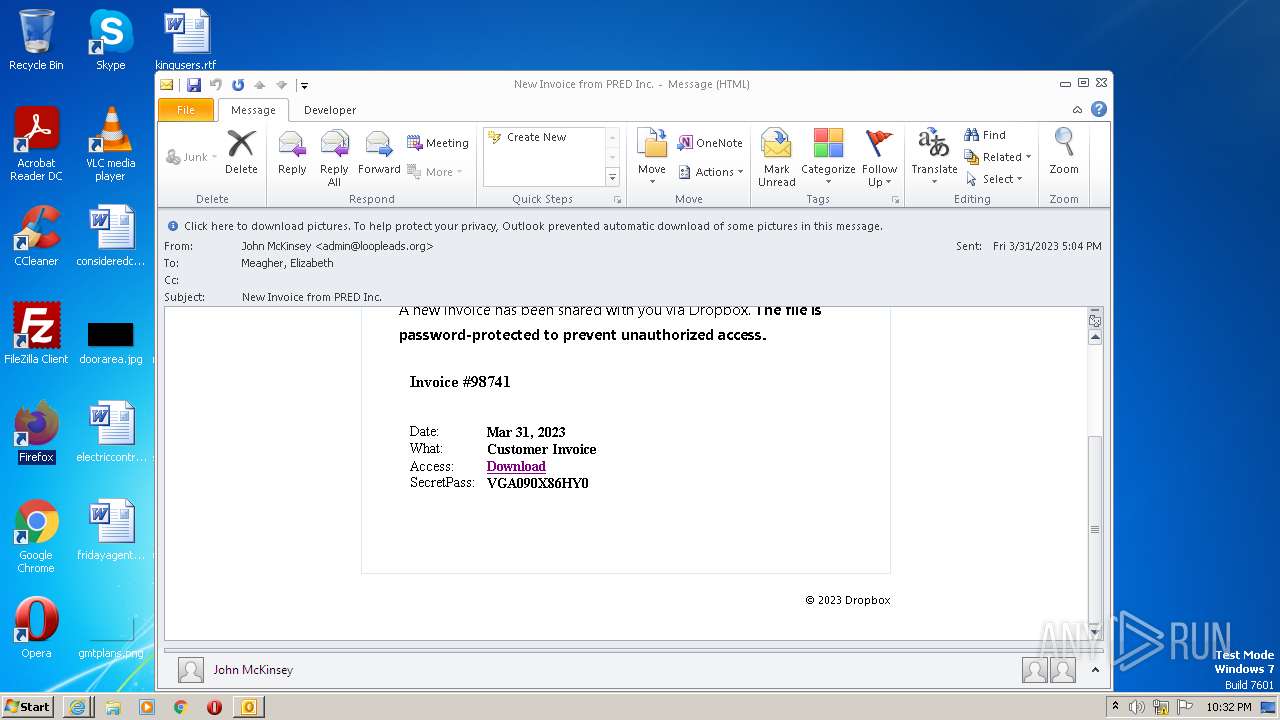
| File name: | message (13).eml |
| Full analysis: | https://app.any.run/tasks/175f101f-1e2c-4d08-adbf-279c727812be |
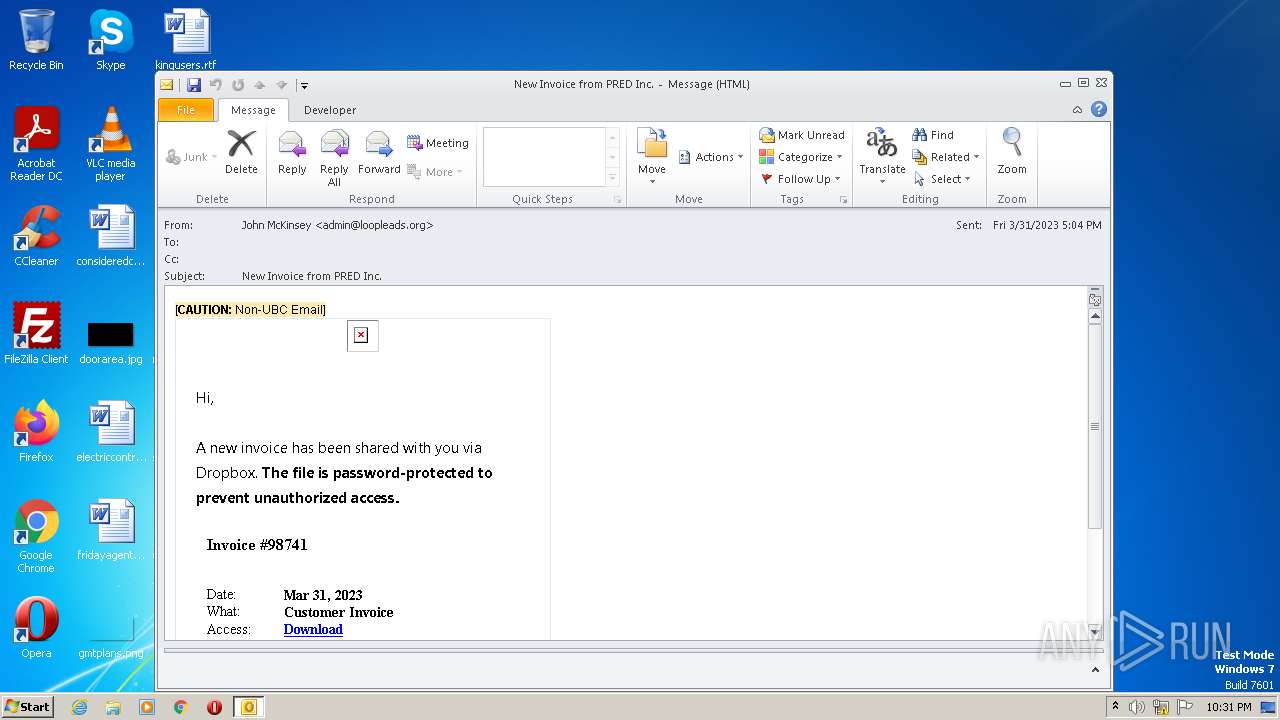
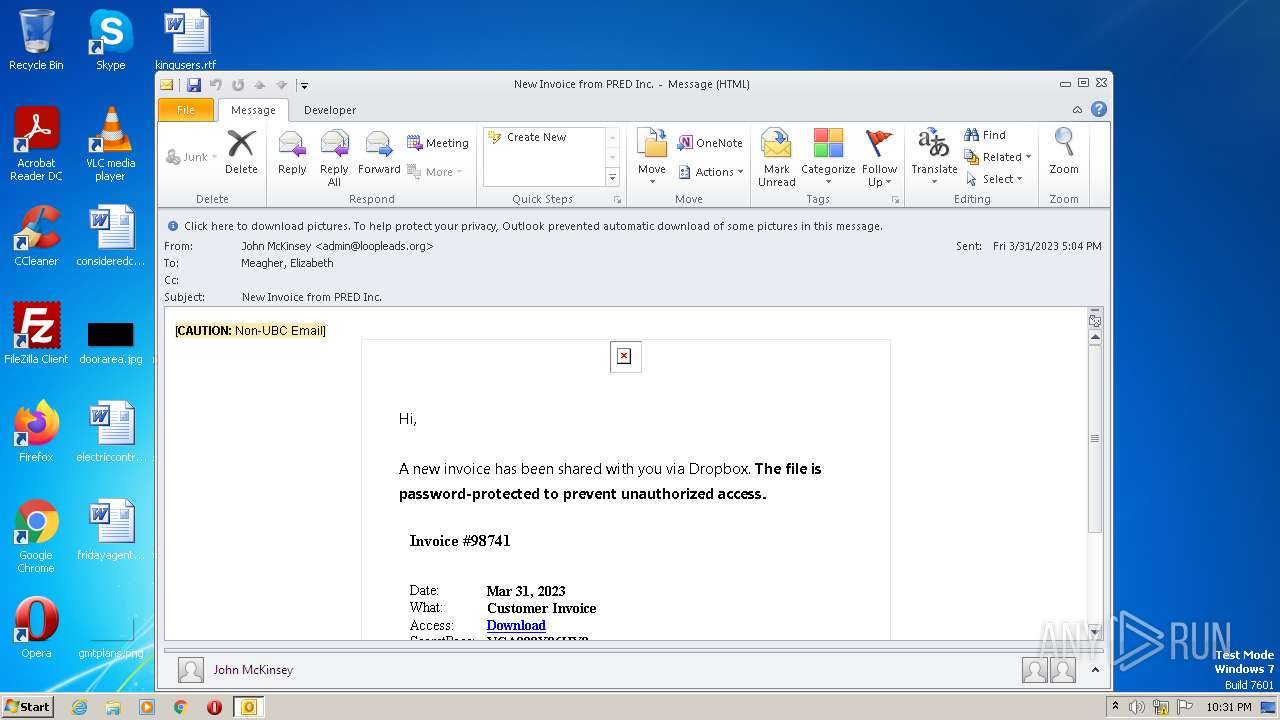
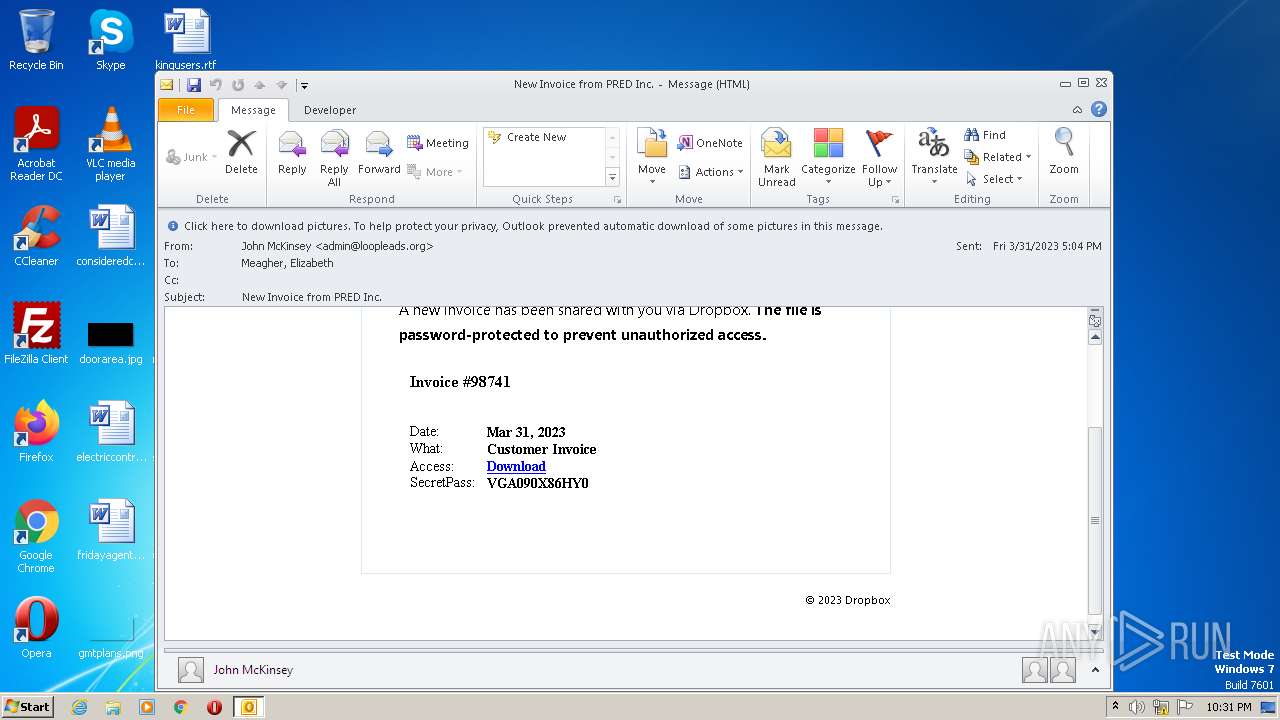
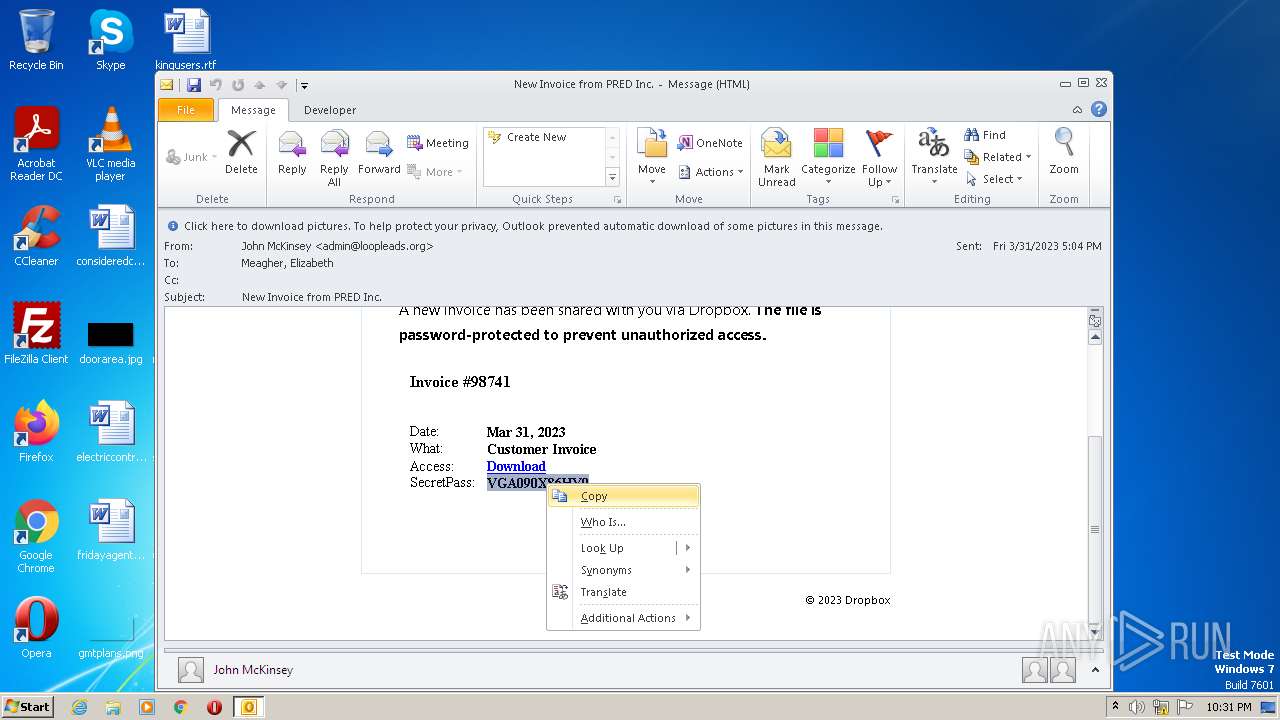
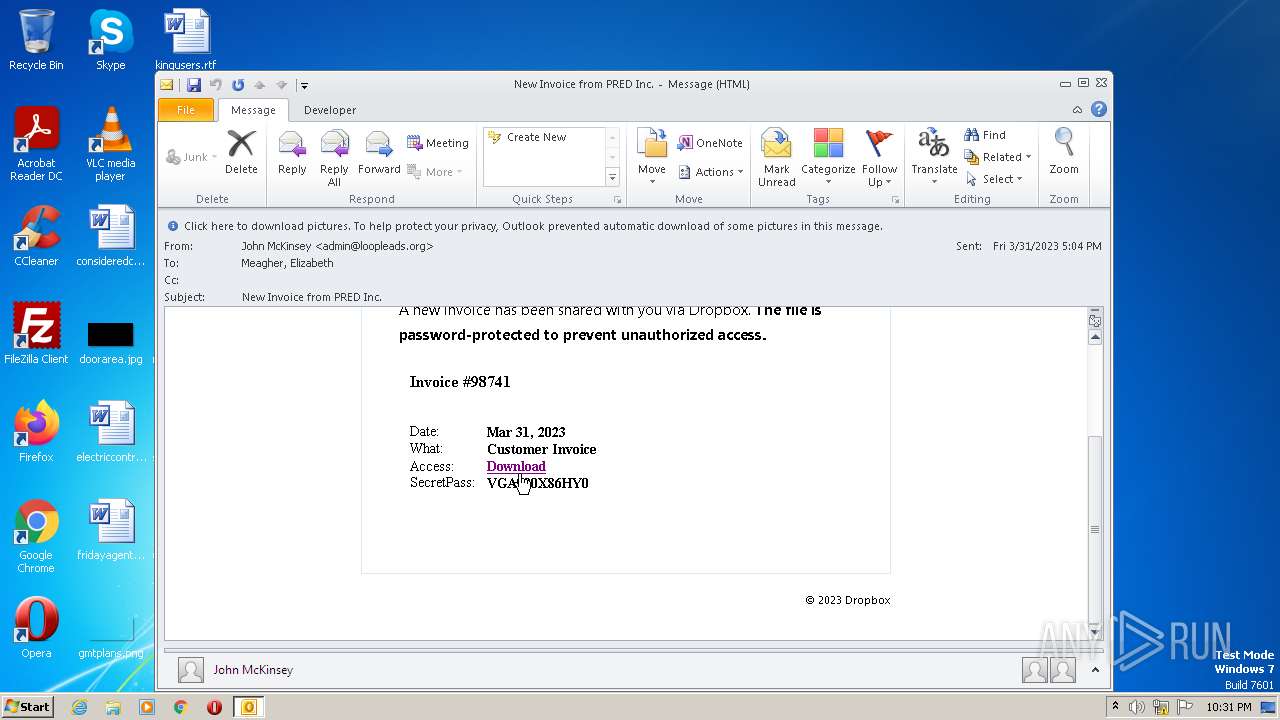
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2023, 21:31:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | A4F9E6A4B03DCE5B49ABFD6AF388EEAF |
| SHA1: | C2EC990B37F7FD5B9C5E1C83C20E6E41BE0EAC6F |
| SHA256: | 202101F95143EEFD5938E488FACC4C8E79F1CE53F232550508BC25EF2194ED13 |
| SSDEEP: | 192:nSUcTl5AfuMD7987NKKy0eZvCqr861MlKHvdm56Pa:SzTMmm9T0ei |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- OUTLOOK.EXE (PID: 2824)
Searches for installed software
- OUTLOOK.EXE (PID: 2824)
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 2824)
Checks Windows Trust Settings
- OUTLOOK.EXE (PID: 2824)
Reads security settings of Internet Explorer
- OUTLOOK.EXE (PID: 2824)
INFO
Checks supported languages
- OUTLOOK.EXE (PID: 2824)
- Reader_sl.exe (PID: 4108)
The process checks LSA protection
- OUTLOOK.EXE (PID: 2824)
Create files in a temporary directory
- OUTLOOK.EXE (PID: 2824)
- iexplore.exe (PID: 976)
- firefox.exe (PID: 2472)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2824)
Reads the machine GUID from the registry
- OUTLOOK.EXE (PID: 2824)
Reads the computer name
- OUTLOOK.EXE (PID: 2824)
Process checks computer location settings
- OUTLOOK.EXE (PID: 2824)
Application launched itself
- iexplore.exe (PID: 976)
- firefox.exe (PID: 2472)
- firefox.exe (PID: 884)
- RdrCEF.exe (PID: 964)
- AcroRd32.exe (PID: 3896)
Creates files or folders in the user directory
- OUTLOOK.EXE (PID: 2824)
Checks proxy server information
- OUTLOOK.EXE (PID: 2824)
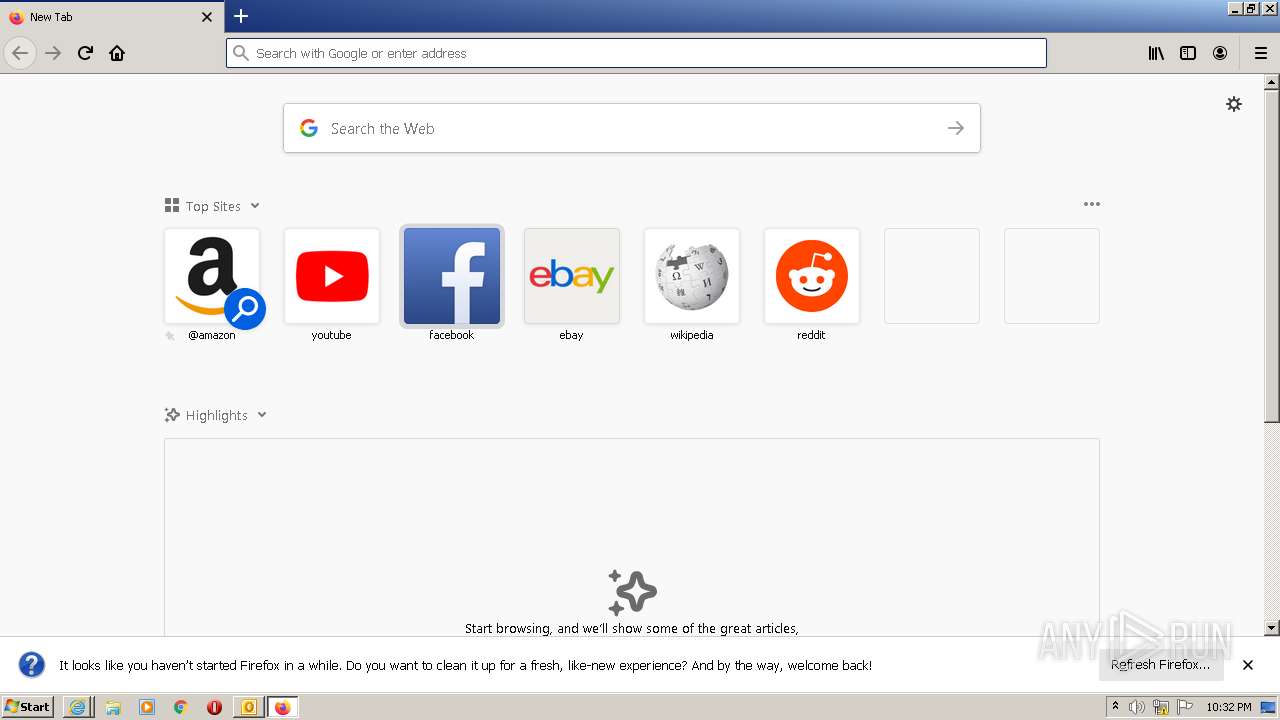
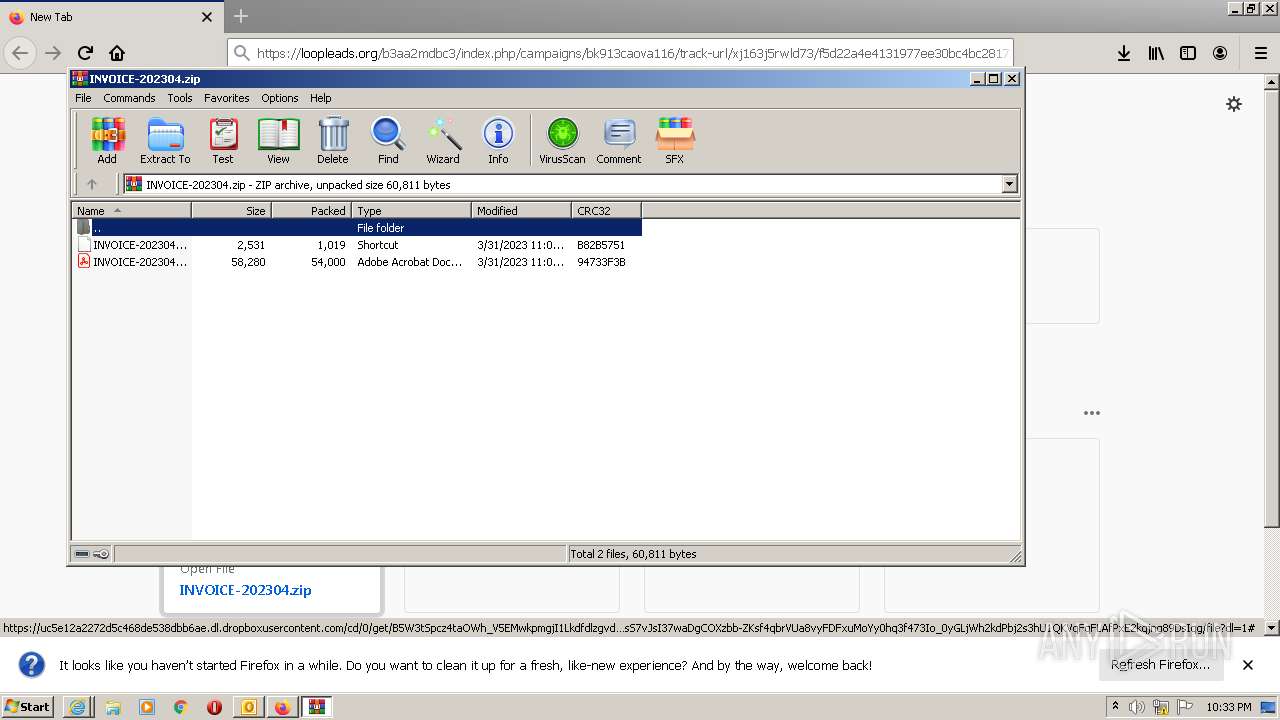
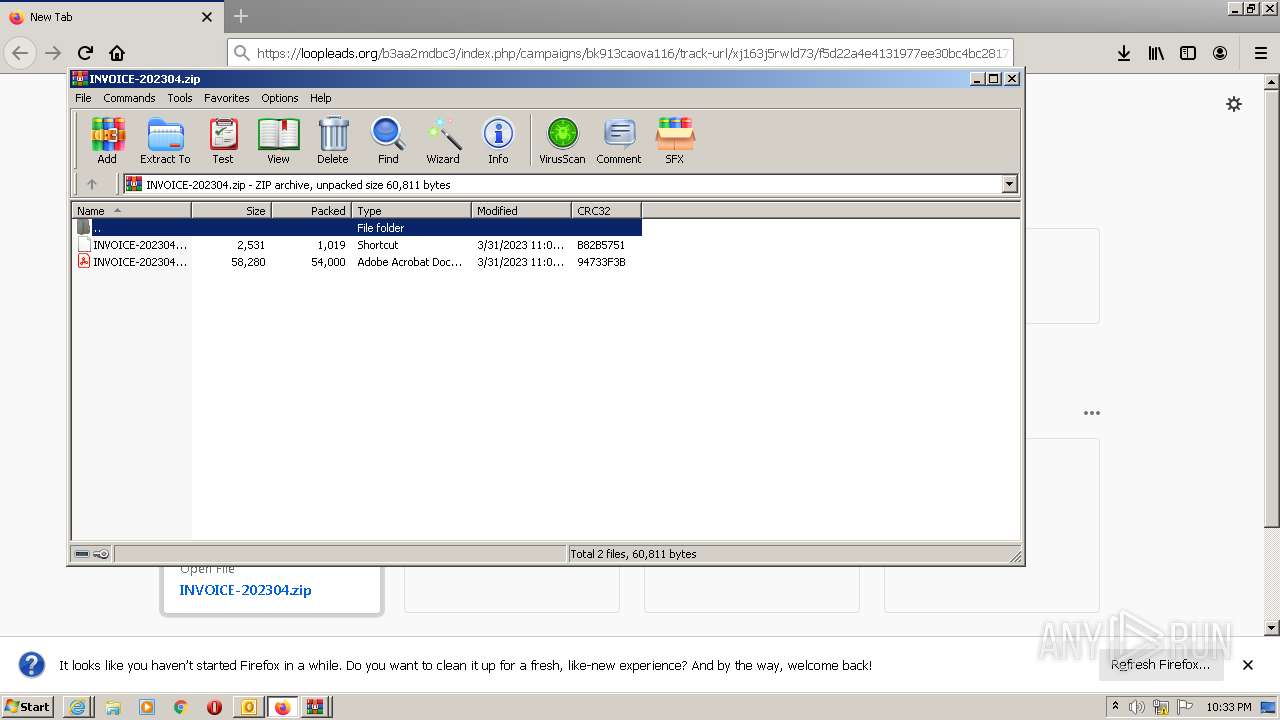
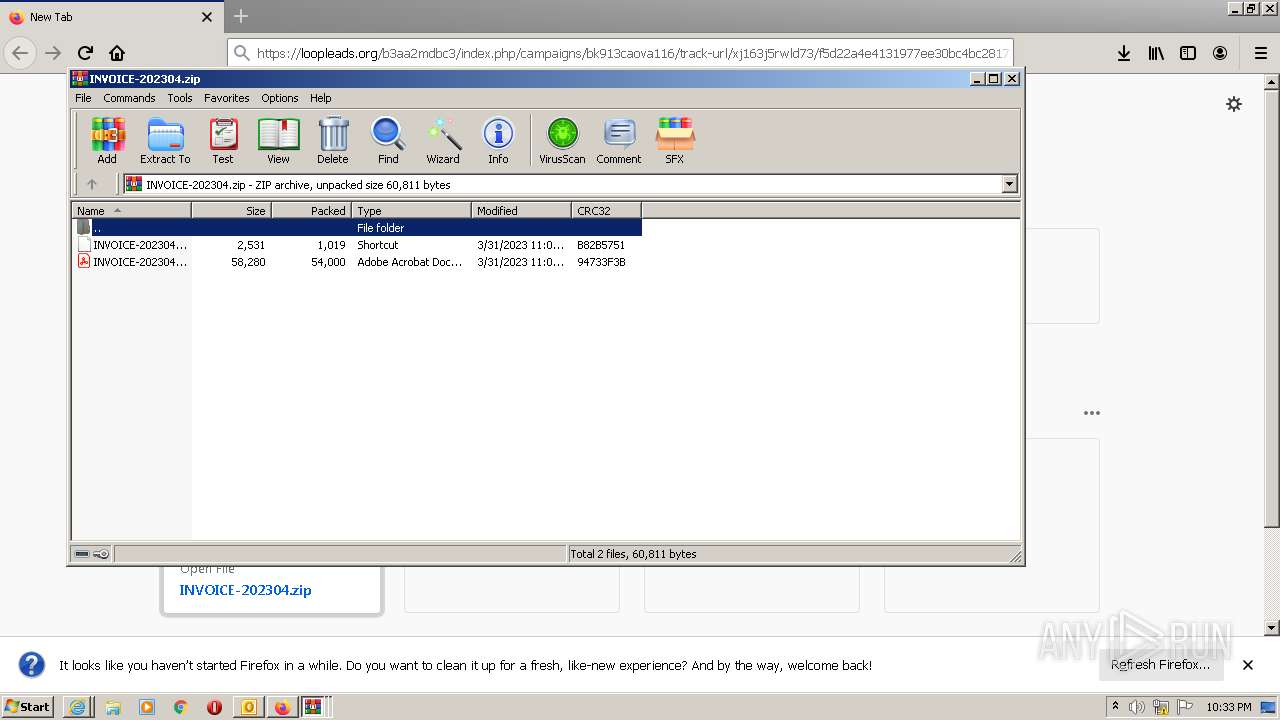
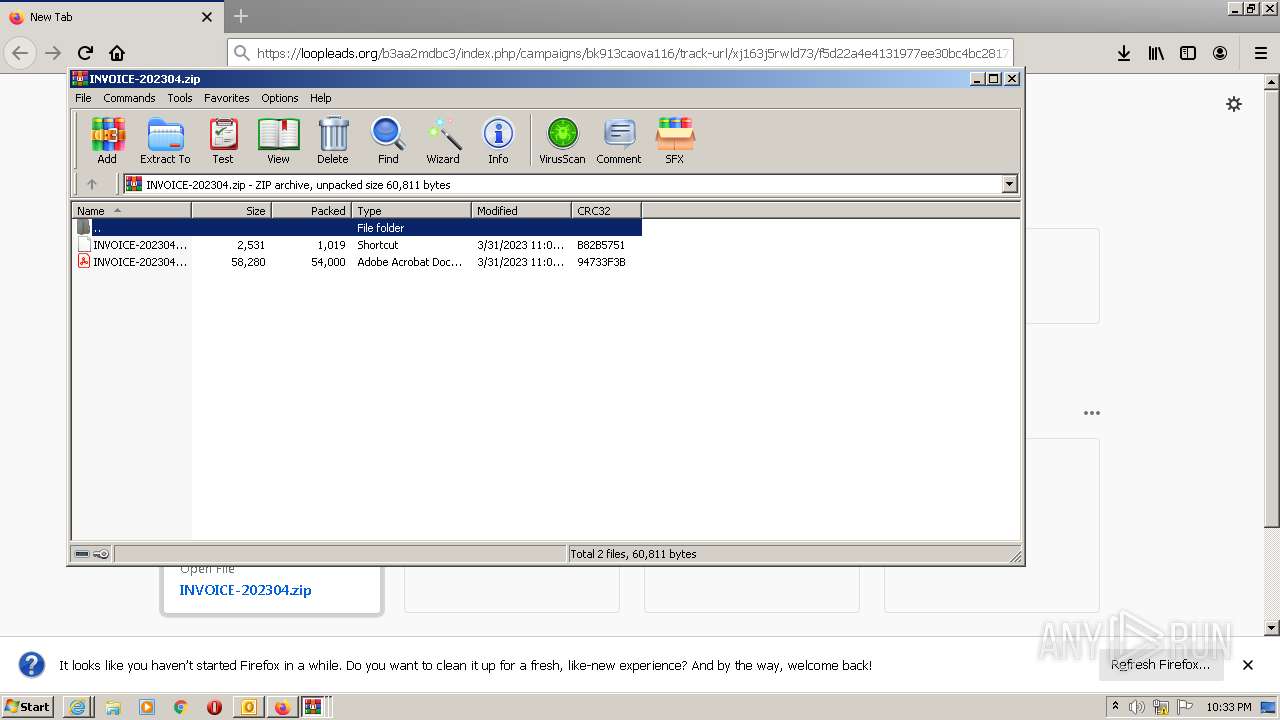
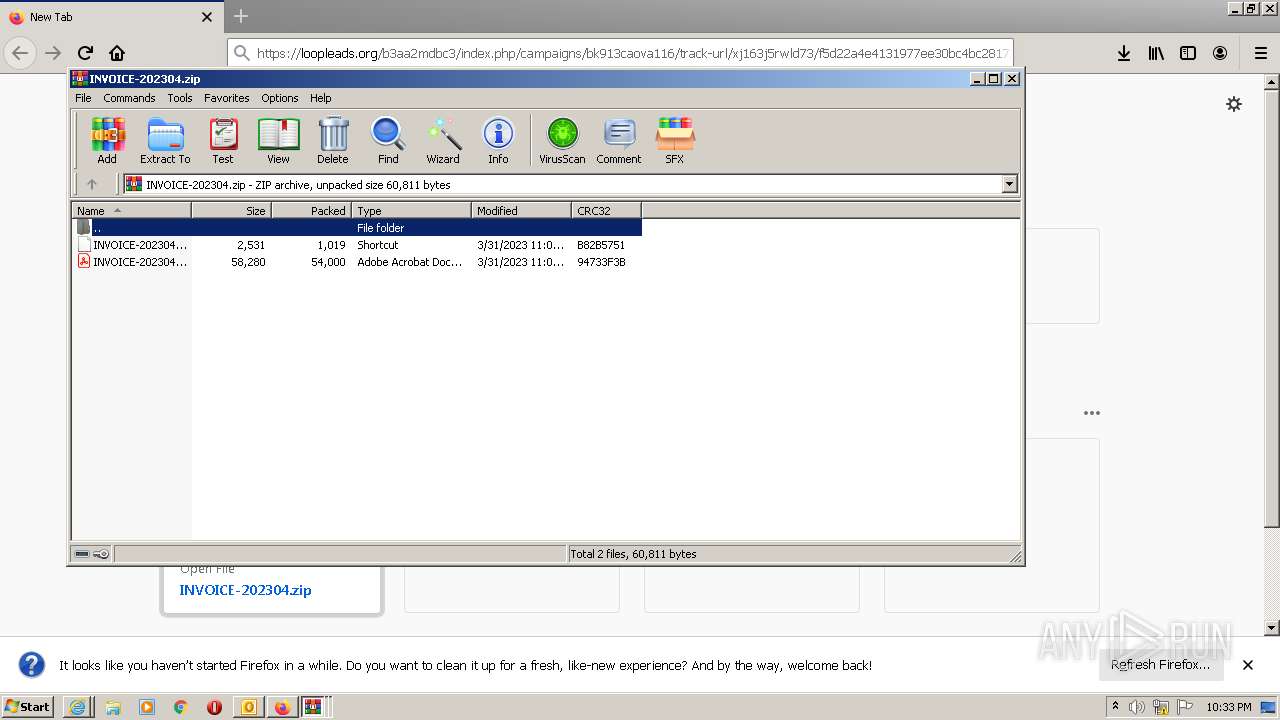
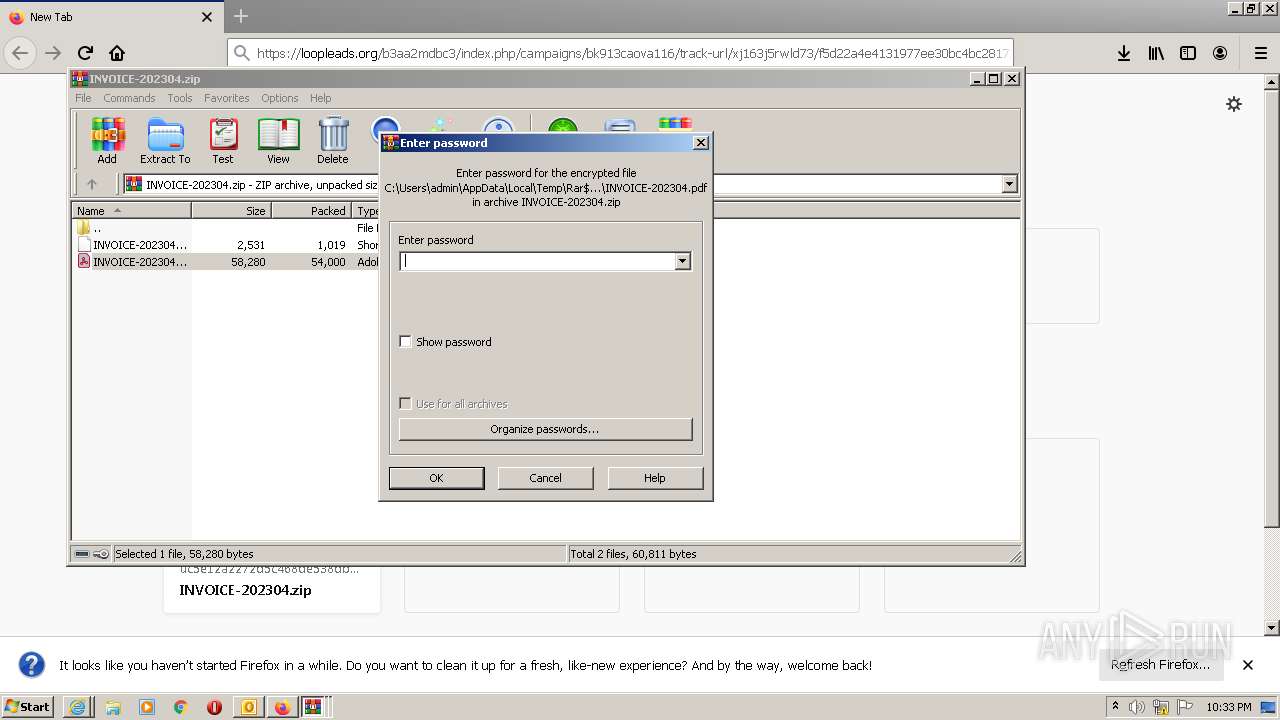
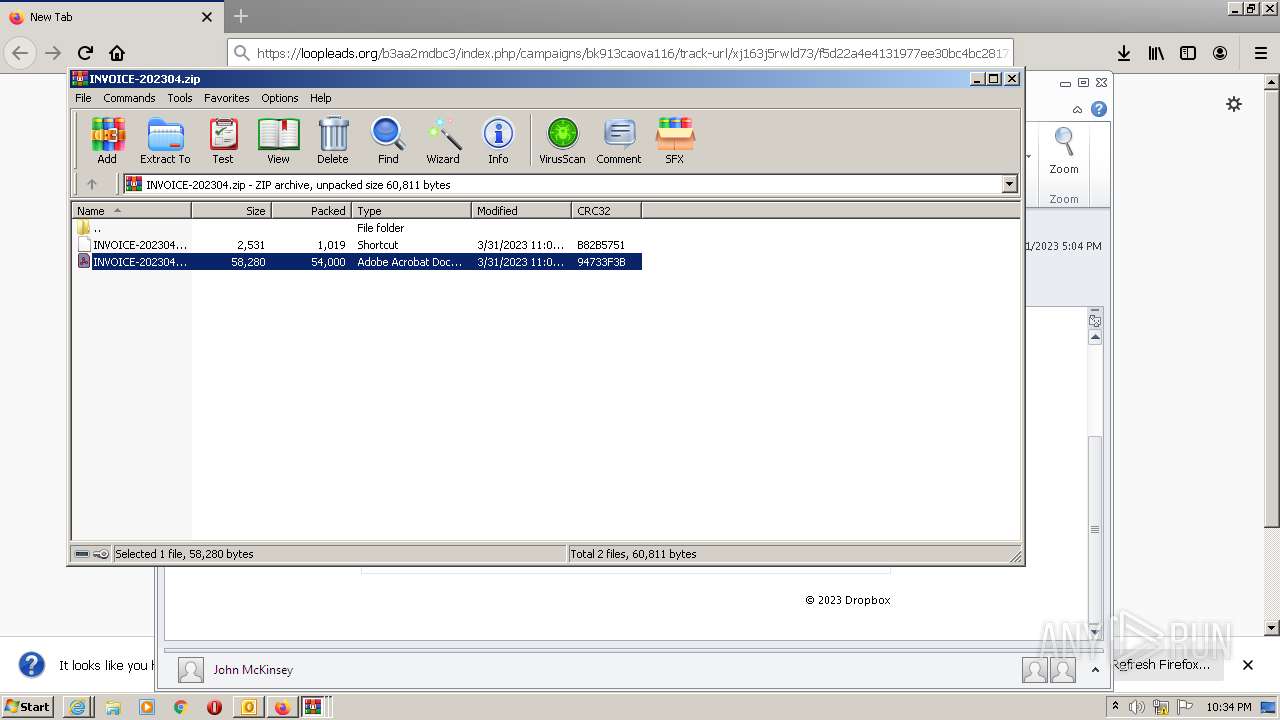
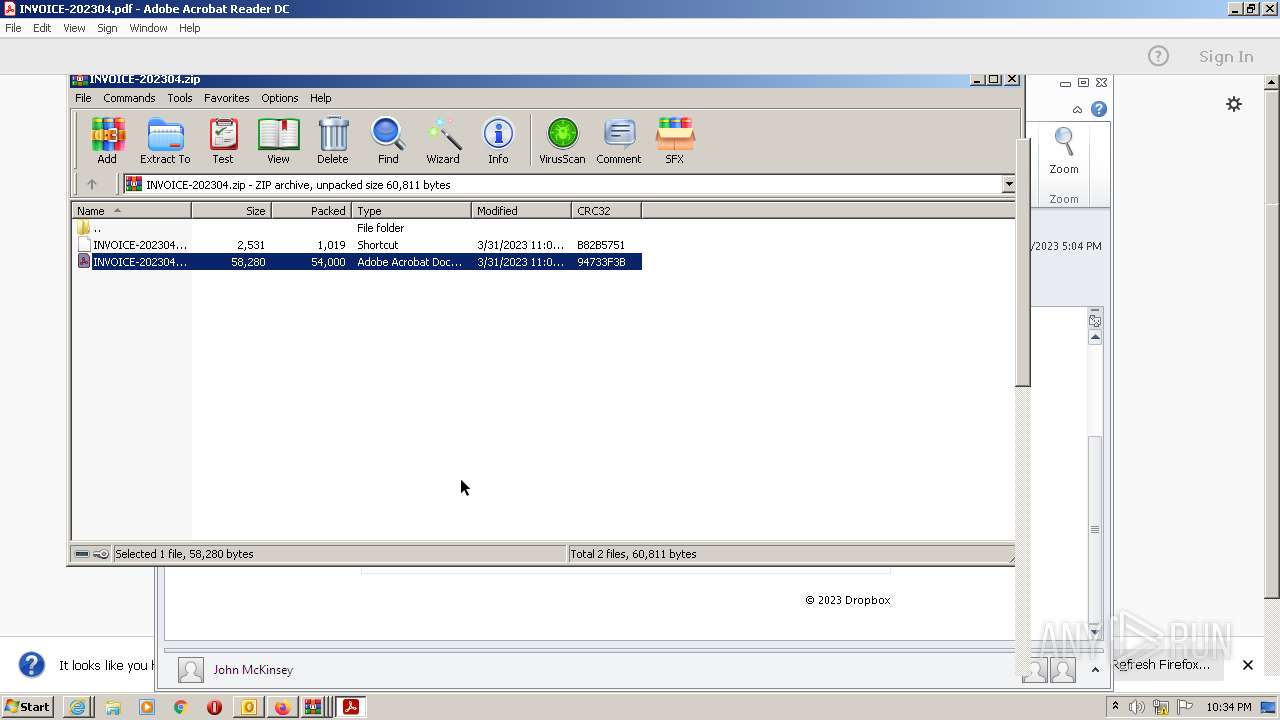
Manual execution by a user
- firefox.exe (PID: 884)
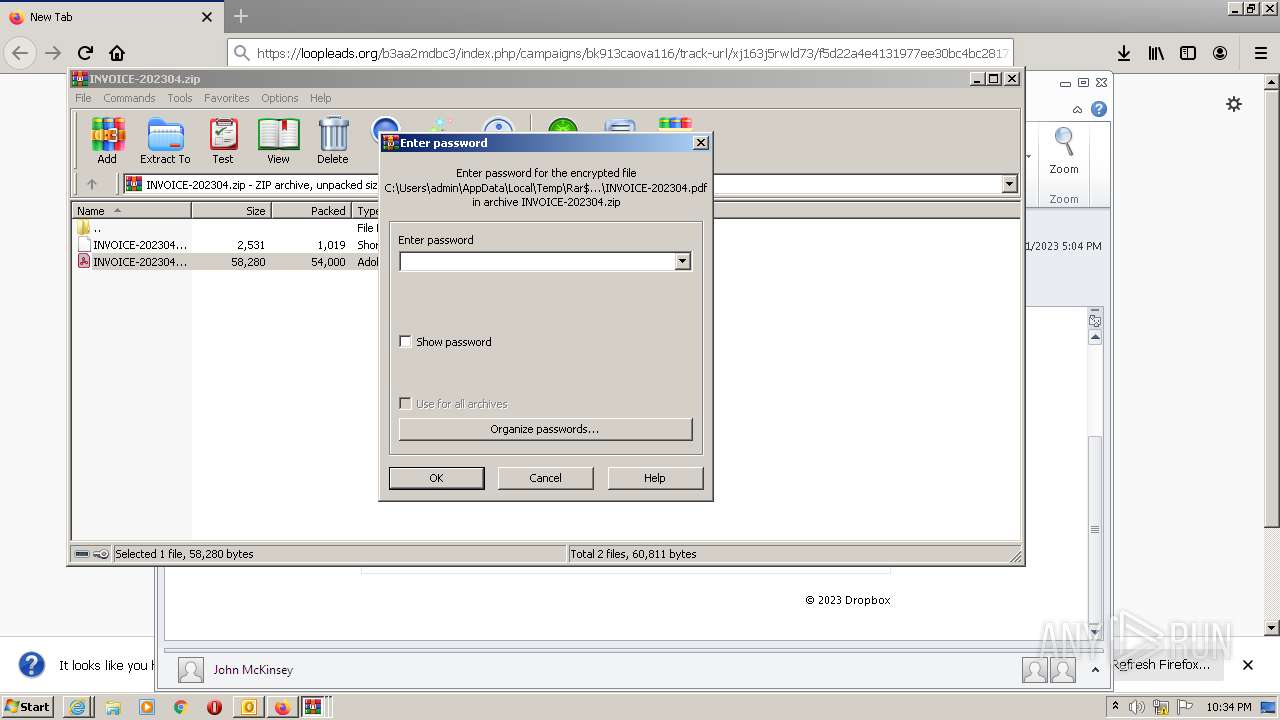
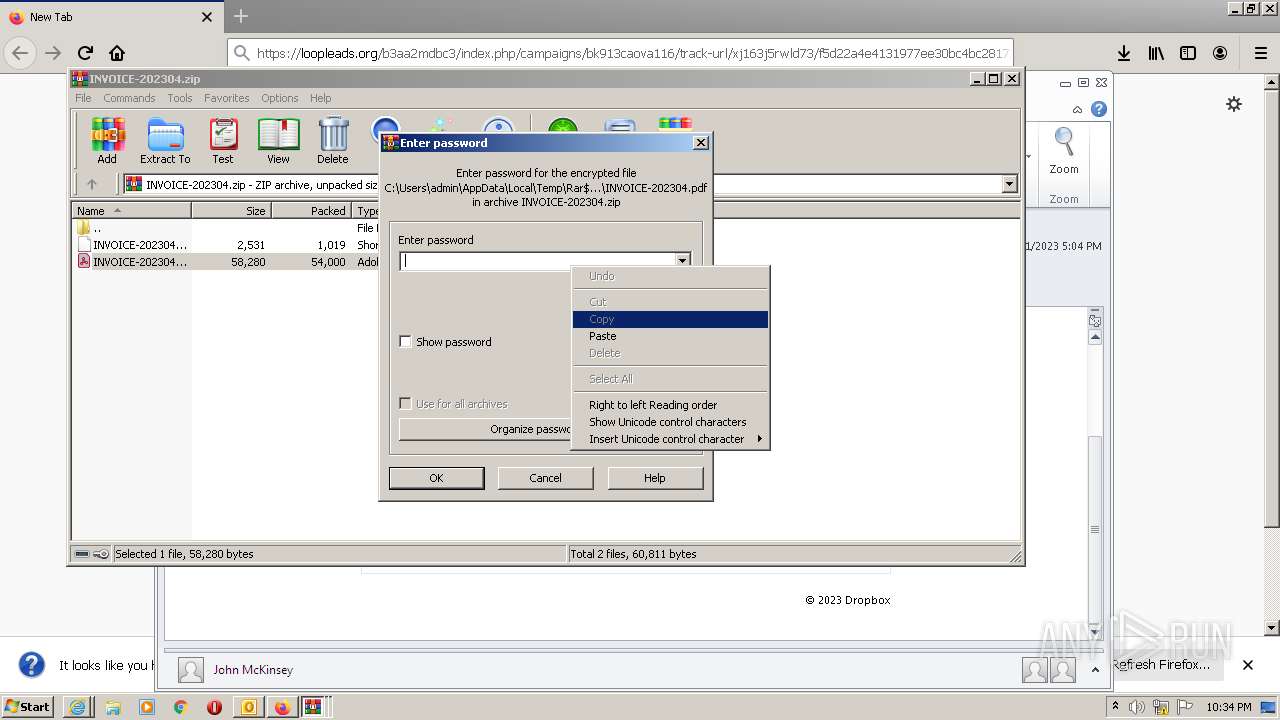
- WinRAR.exe (PID: 2552)
- WinRAR.exe (PID: 2800)
- WinRAR.exe (PID: 2748)
- WinRAR.exe (PID: 2416)
- WinRAR.exe (PID: 3028)
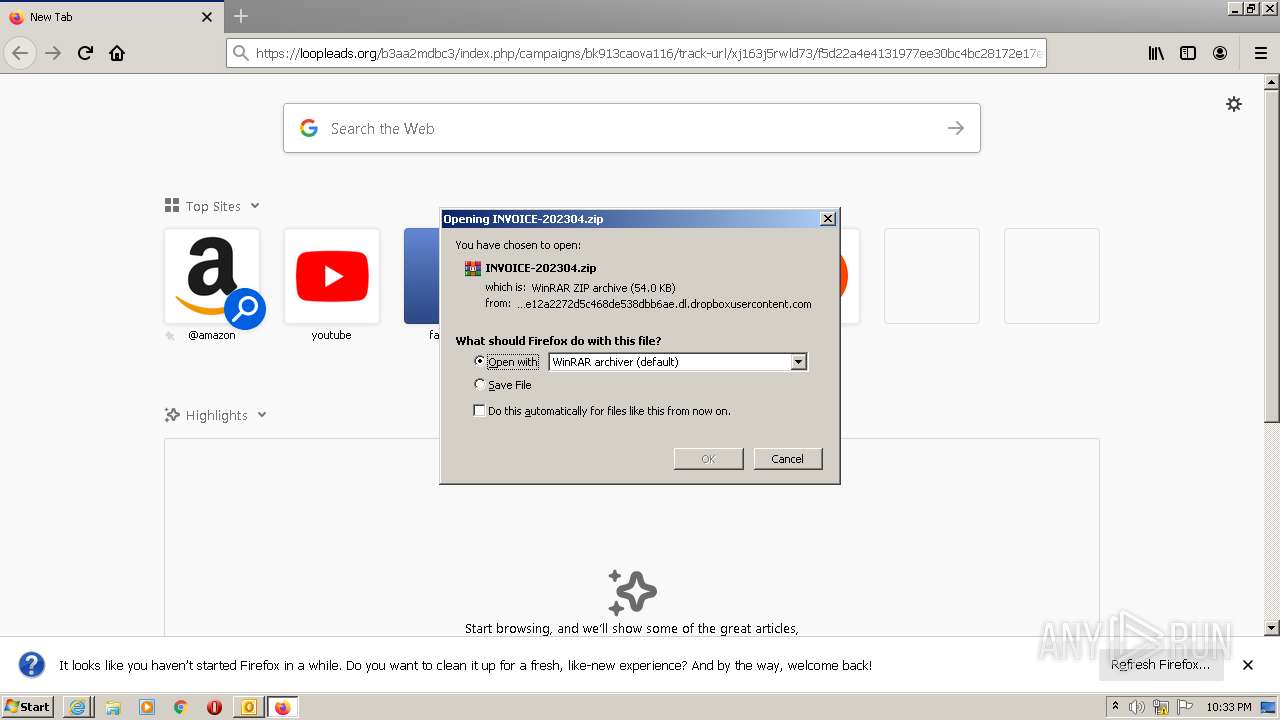
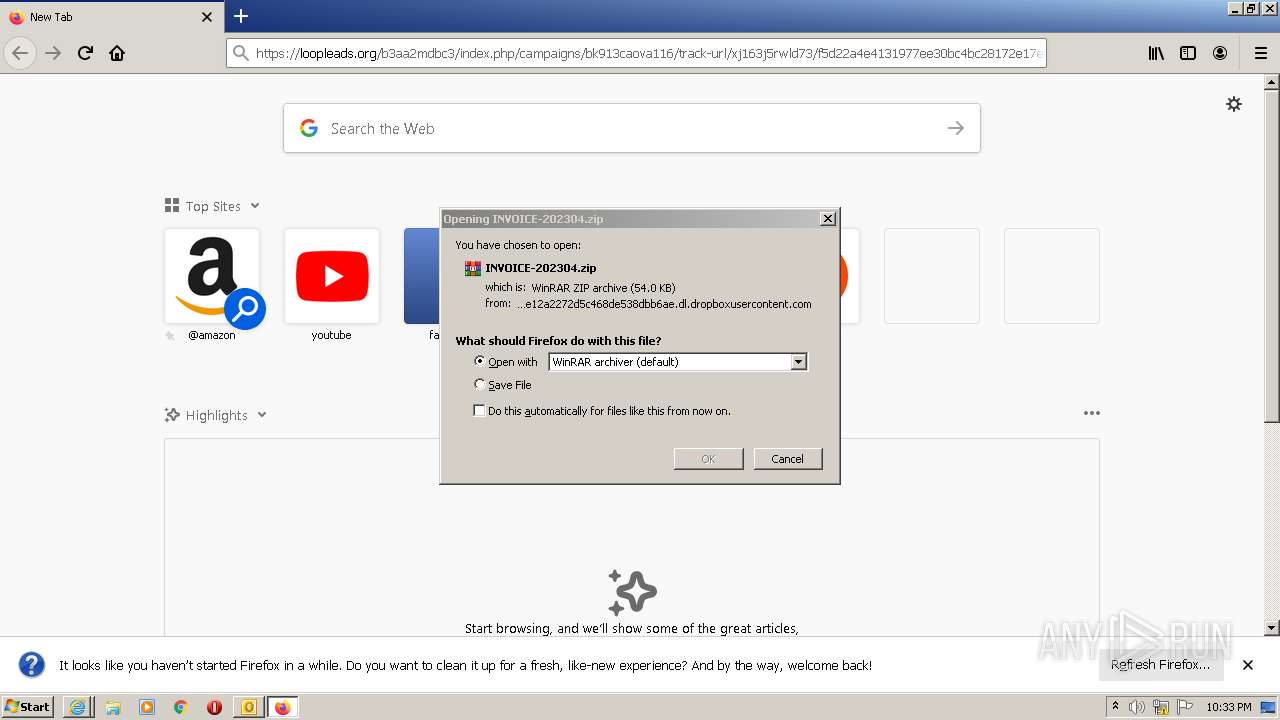
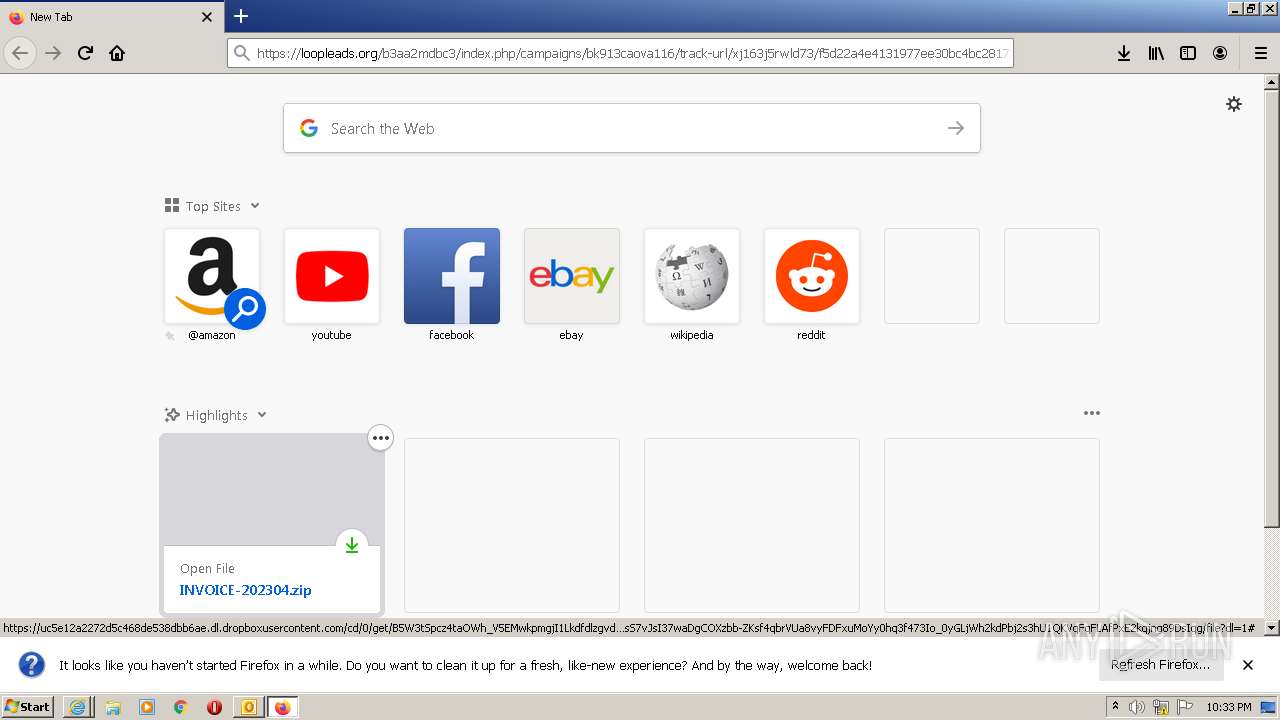
The process uses the downloaded file
- firefox.exe (PID: 2472)
- WinRAR.exe (PID: 3028)
Executable content was dropped or overwritten
- firefox.exe (PID: 2472)
- AdobeARM.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
73
Monitored processes
27
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 884 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
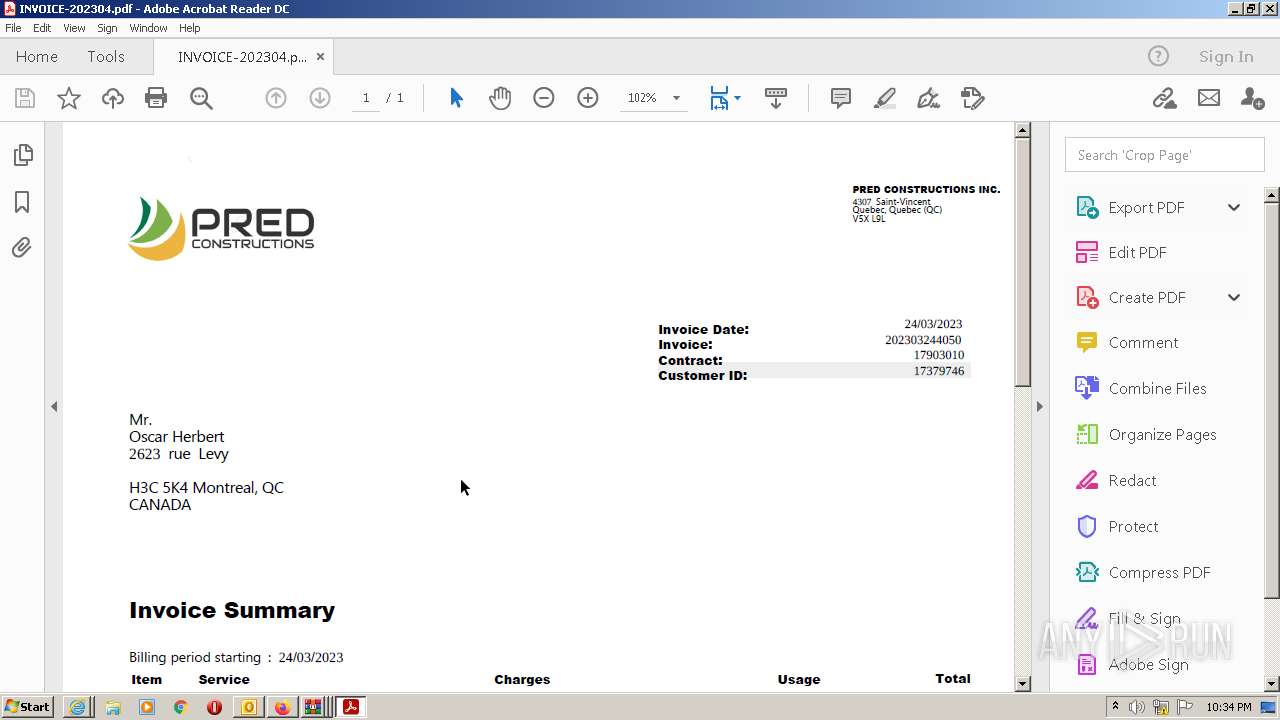
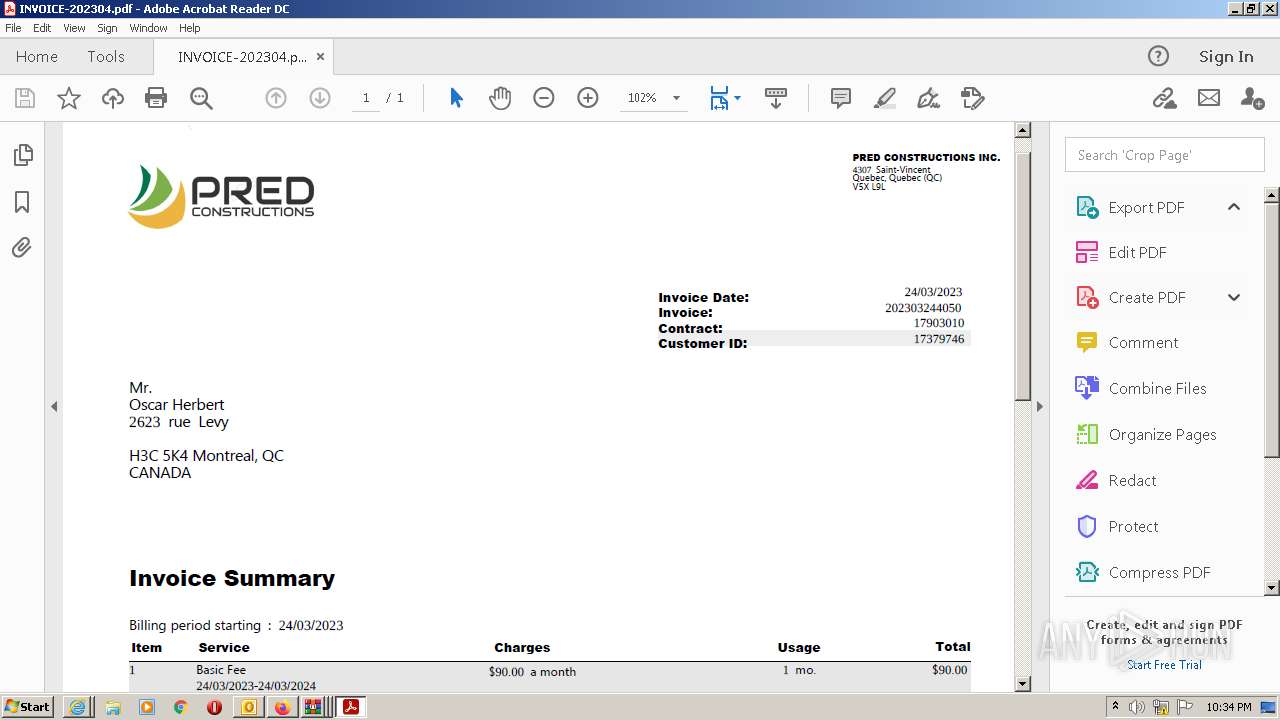
| 964 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16514043 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
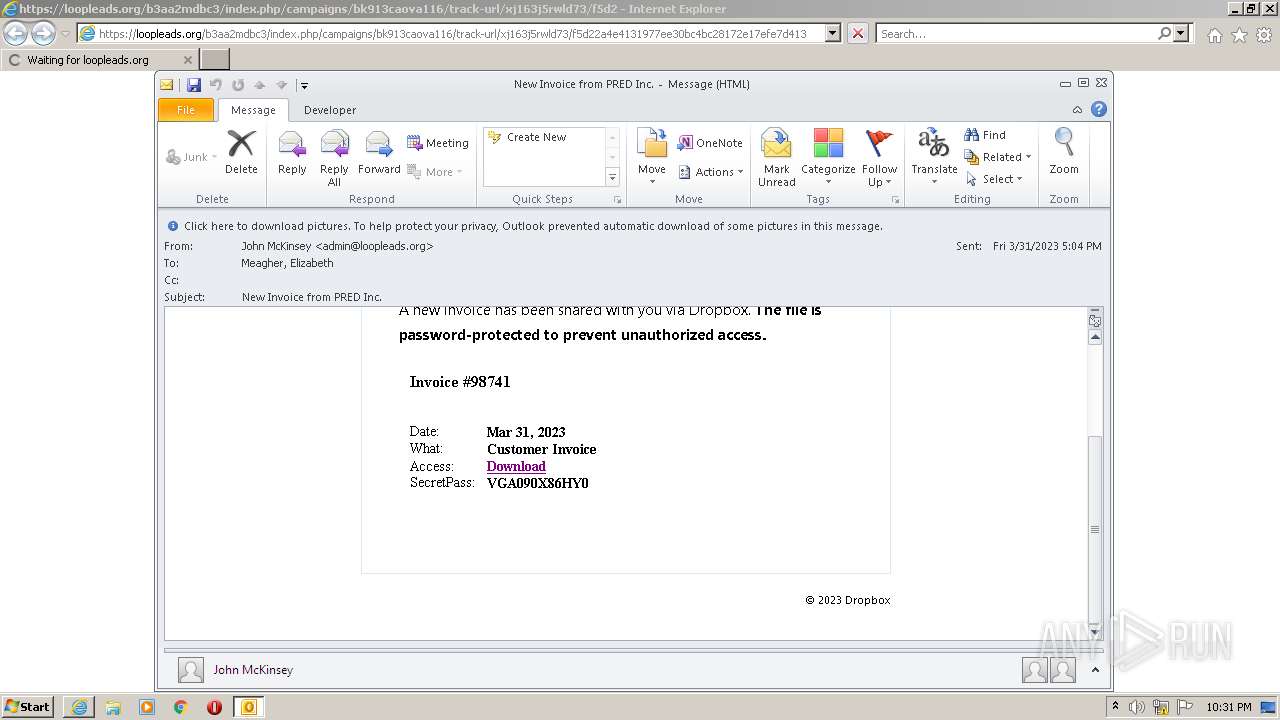
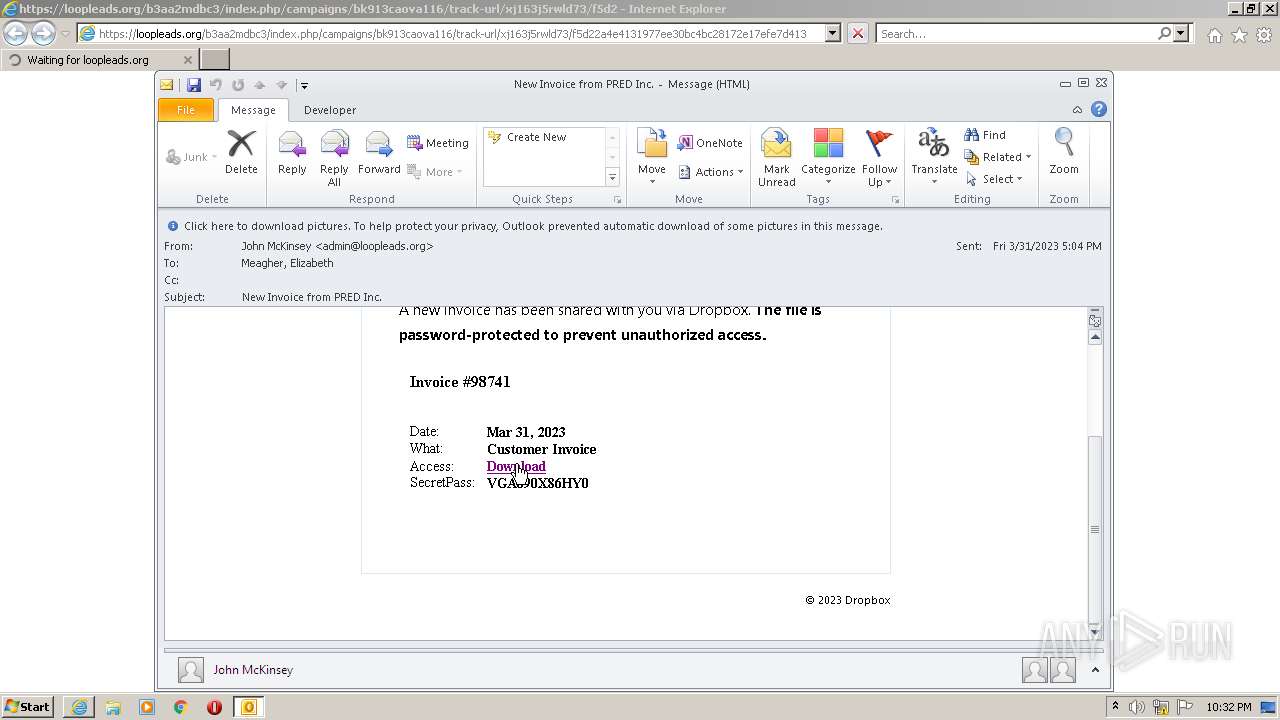
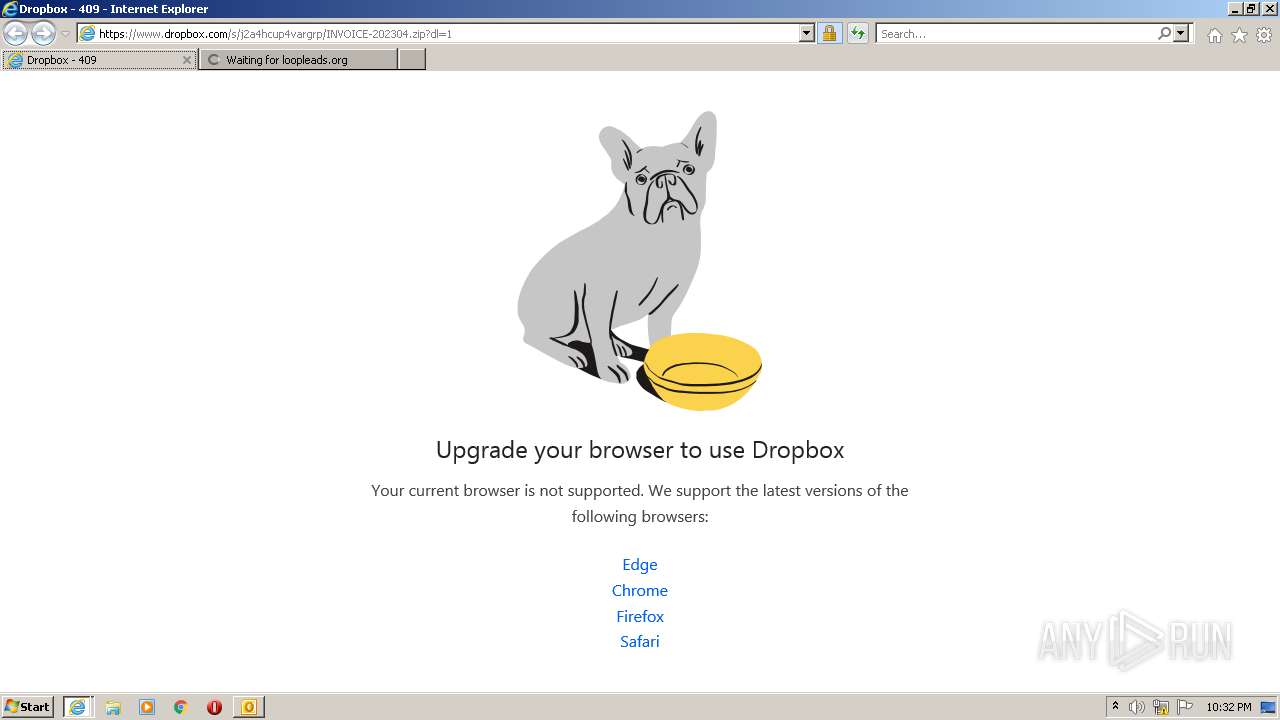
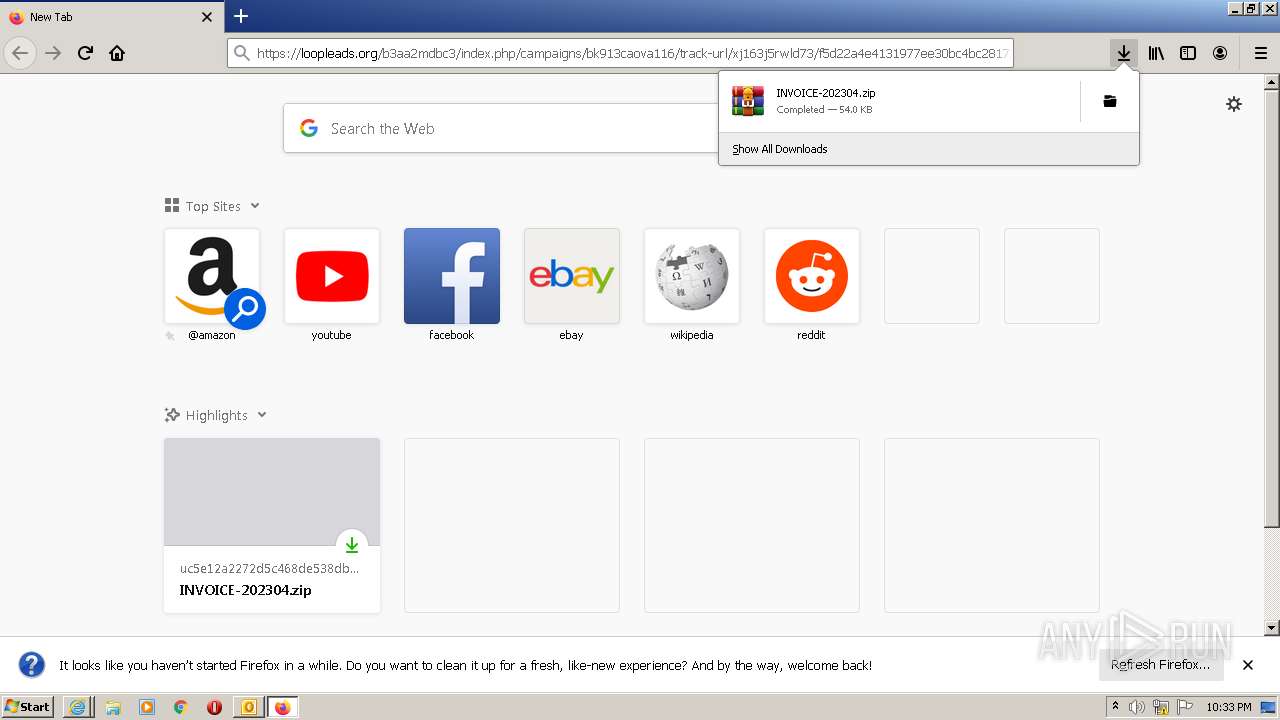
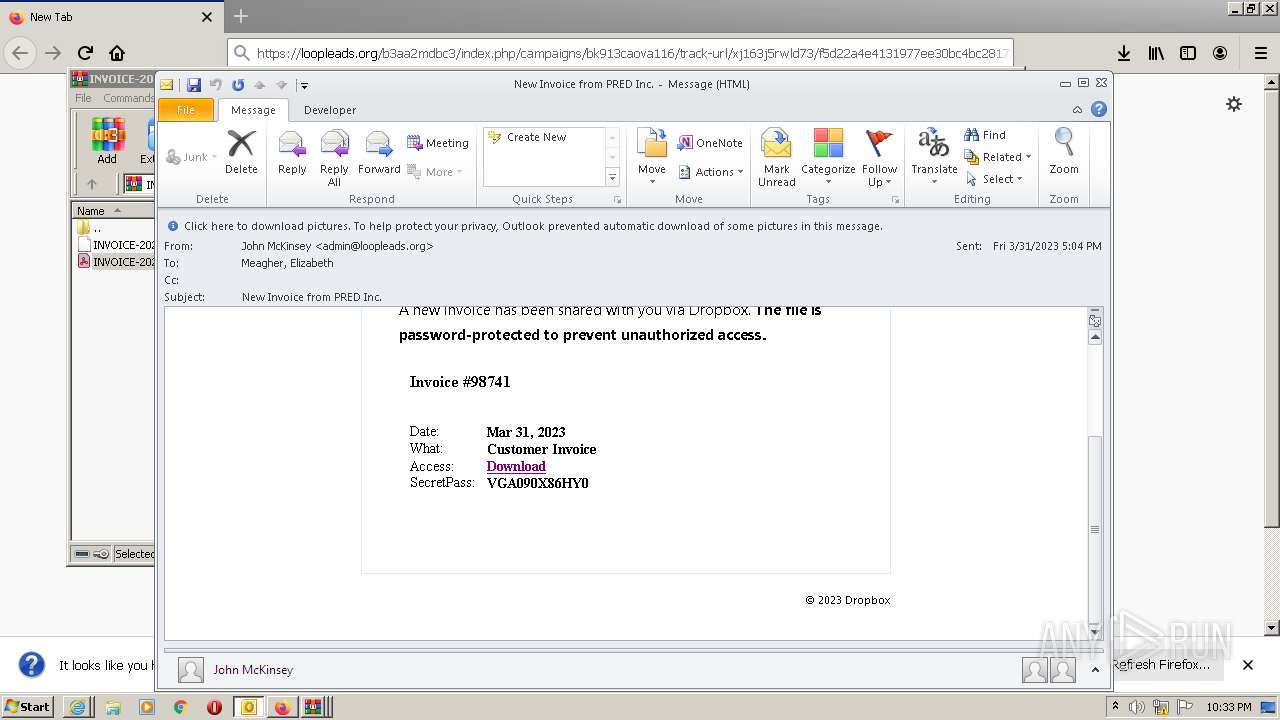
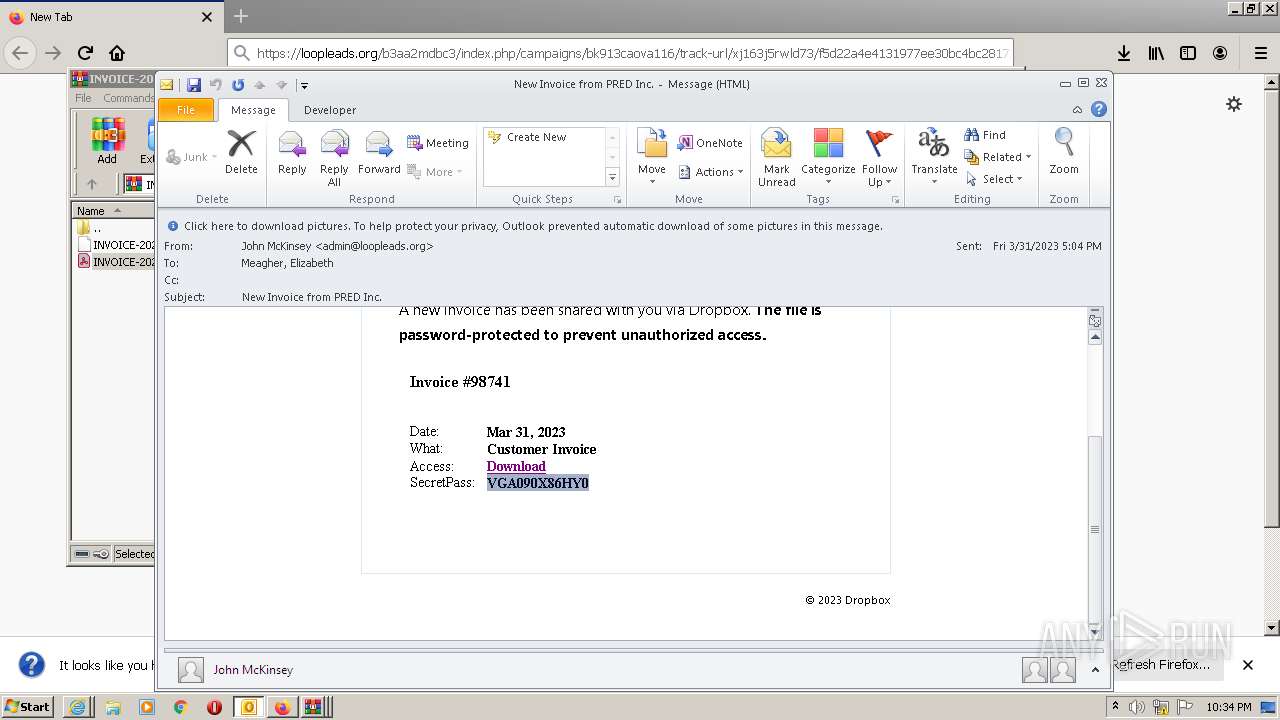
| 976 | "C:\Program Files\Internet Explorer\iexplore.exe" https://loopleads.org/b3aa2mdbc3/index.php/campaigns/bk913caova116/track-url/xj163j5rwld73/f5d22a4e4131977ee30bc4bc28172e17efe7d413 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1188,15022590665661183919,14929512109183595278,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10790288446895611309 --renderer-client-id=6 --mojo-platform-channel-handle=1628 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2472.0.697116314\1530375454" -parentBuildID 20201112153044 -prefsHandle 1120 -prefMapHandle 1028 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2472 "\\.\pipe\gecko-crash-server-pipe.2472" 1208 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
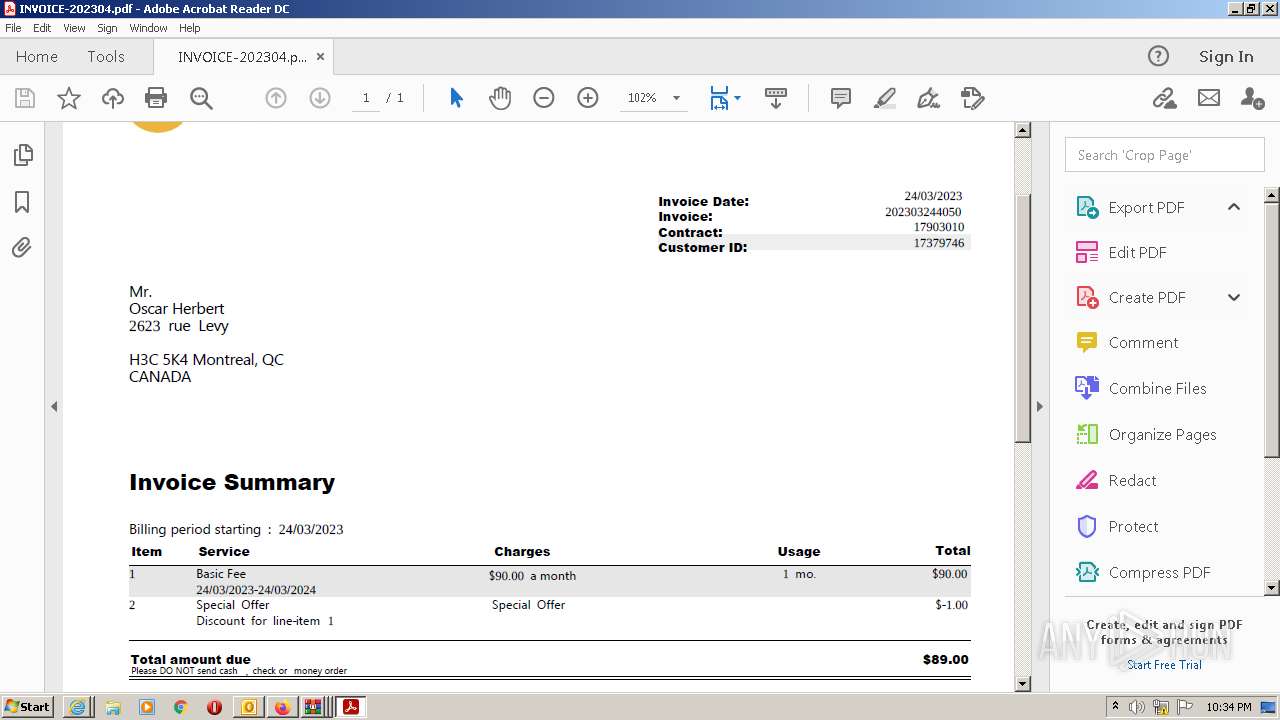
| 2416 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\INVOICE-202304.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\INVOICE-202304.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2472.13.1206321646\1055039631" -childID 2 -isForBrowser -prefsHandle 2632 -prefMapHandle 3288 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2472 "\\.\pipe\gecko-crash-server-pipe.2472" 3096 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\INVOICE-202304.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
153 696
Read events
133 066
Write events
20 580
Delete events
50
Modification events
| (PID) Process: | (2824) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2824) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (2824) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (2824) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (2824) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (2824) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (2824) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (2824) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (2824) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (2824) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
10
Suspicious files
570
Text files
232
Unknown types
118
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2824 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF53E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2824 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 2824 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2824 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2824 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\config14[1].xml | xml | |
MD5:— | SHA256:— | |||
| 976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2824 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\ONetConfig\54946941a2b45a5ba7f3e1b905b42959.sig | binary | |
MD5:— | SHA256:— | |||
| 976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 2824 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_D1BF03277A156247A0465442E3EE7E35.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
126
DNS requests
127
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCXh%2B17FzWzVgrisikgAGpW | US | der | 472 b | whitelisted |
976 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGuOw5S%2FgZeuCs2W38ctSDs%3D | US | der | 471 b | whitelisted |
3116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDTHapPXttJahK0MpJdGmyD | US | der | 472 b | whitelisted |
3116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDvFt7VlIyLVBLYlWb5uNY9 | US | der | 472 b | whitelisted |
3116 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2824 | OUTLOOK.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
3116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD%2FB2zZ7cy1JAocIdUzcD8Q | US | der | 472 b | whitelisted |
2824 | OUTLOOK.EXE | GET | 200 | 52.109.88.191:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={CFF13DD8-6EF2-49EB-B265-E3BFC6501C1D}&build=14.0.6023 | NL | xml | 1.96 Kb | whitelisted |
3116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFwMawXF47e0CuAYa1GCMjM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2824 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3116 | iexplore.exe | 104.21.61.77:443 | loopleads.org | CLOUDFLARENET | — | unknown |
2824 | OUTLOOK.EXE | 52.109.88.191:80 | office14client.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
976 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
976 | iexplore.exe | 67.26.75.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
976 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3116 | iexplore.exe | 172.67.207.98:443 | loopleads.org | CLOUDFLARENET | US | unknown |
2824 | OUTLOOK.EXE | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
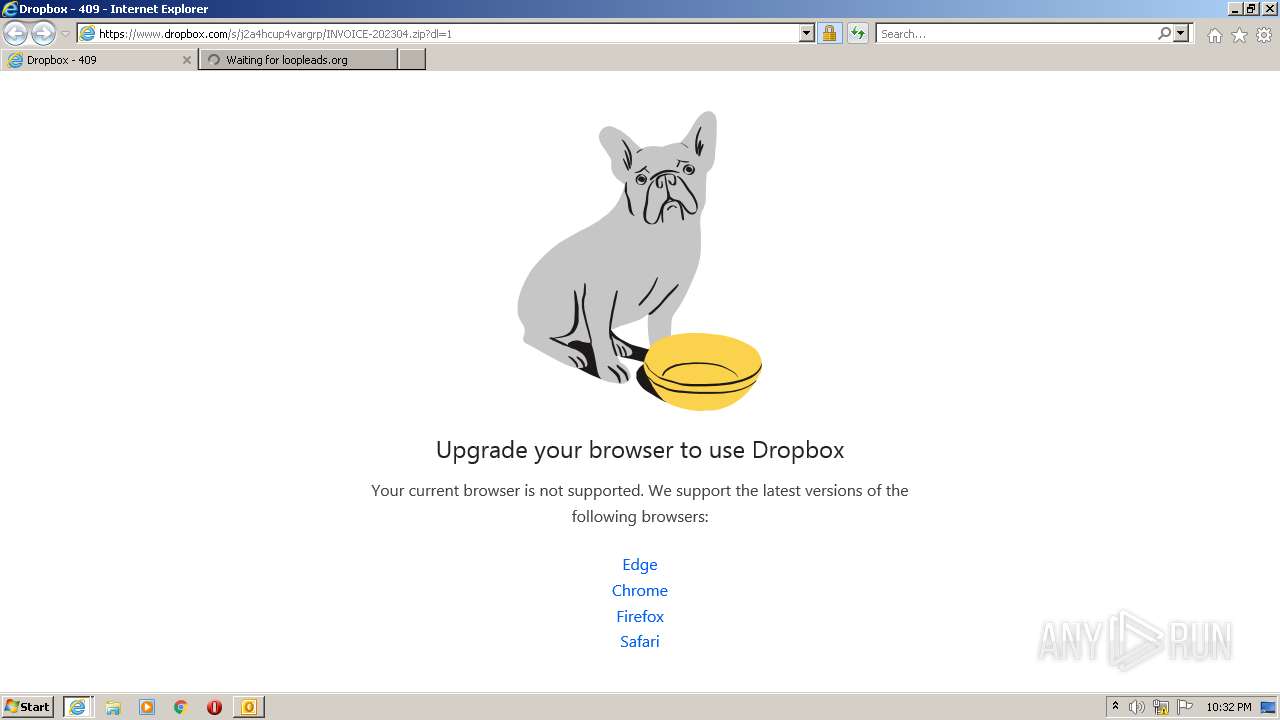
3116 | iexplore.exe | 162.125.66.18:443 | www.dropbox.com | DROPBOX | DE | suspicious |
3116 | iexplore.exe | 142.250.185.195:80 | crl.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
office14client.microsoft.com |
| whitelisted |
loopleads.org |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
rr.office.microsoft.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3116 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
2472 | firefox.exe | Misc activity | ET INFO DropBox User Content Download Access over SSL M2 |
860 | svchost.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |