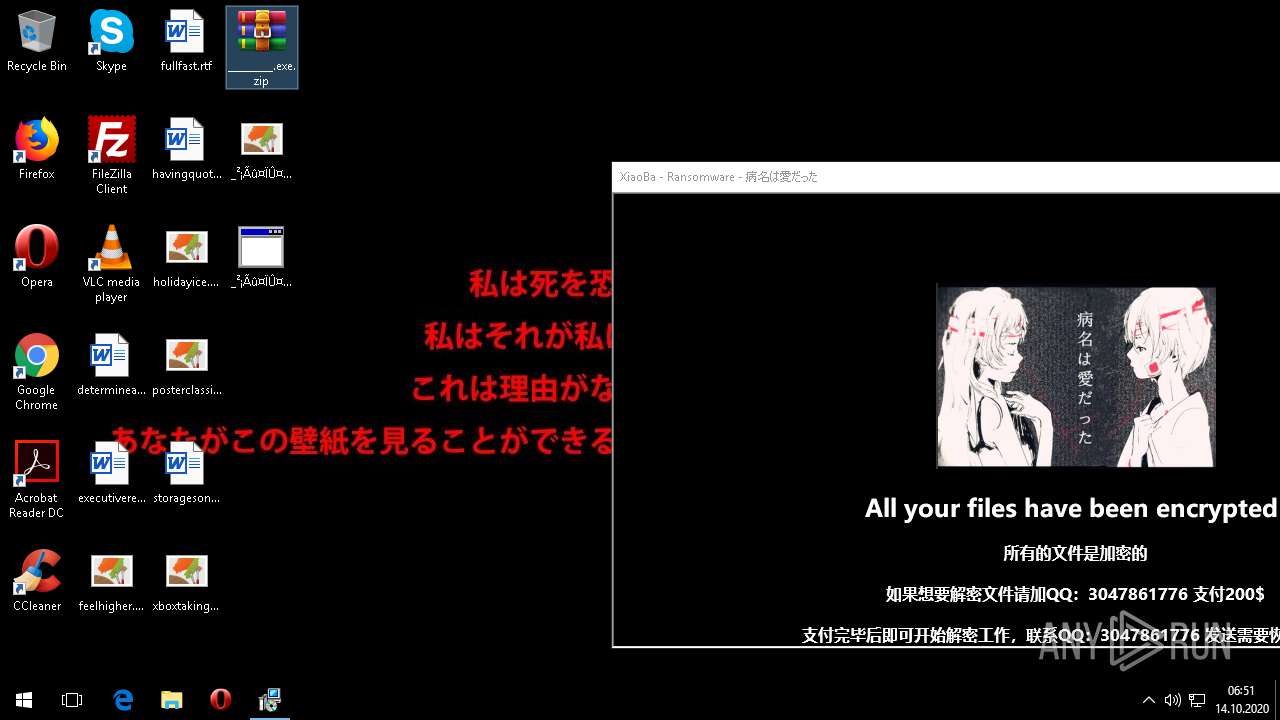
| File name: | _________.exe.zip |
| Full analysis: | https://app.any.run/tasks/f293c9a1-ef17-4c0c-85a0-261802a1cd10 |
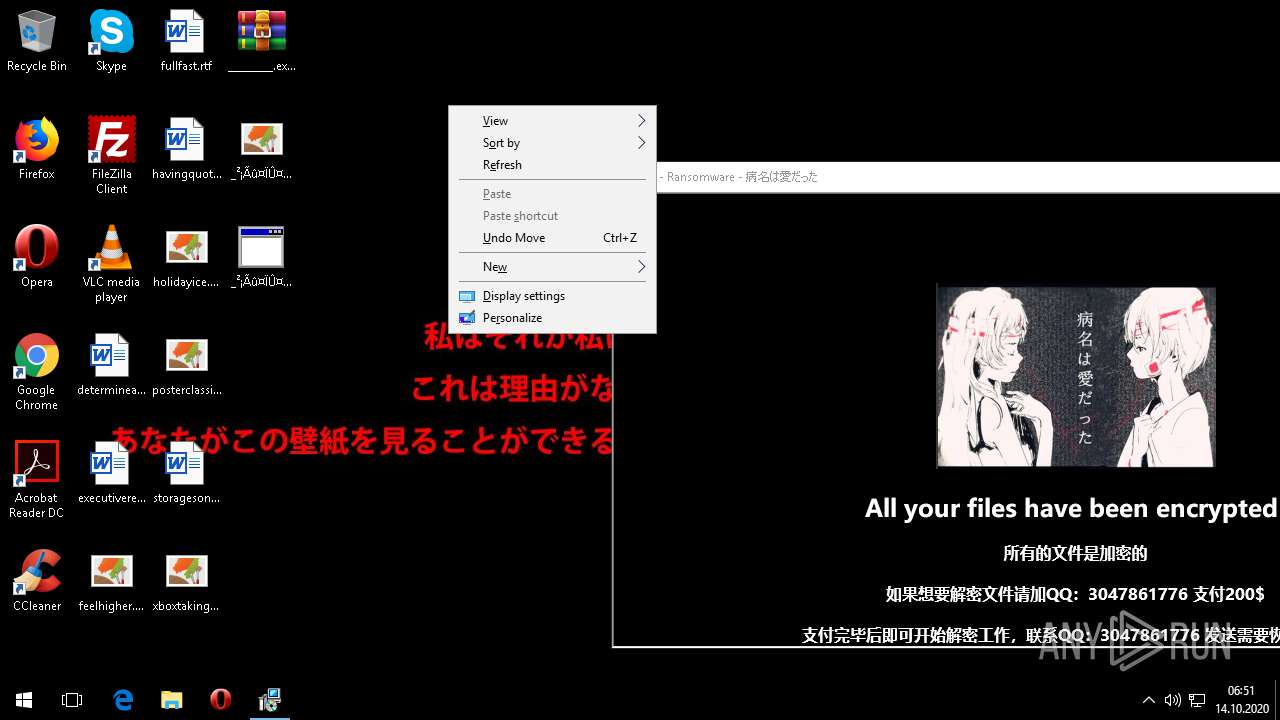
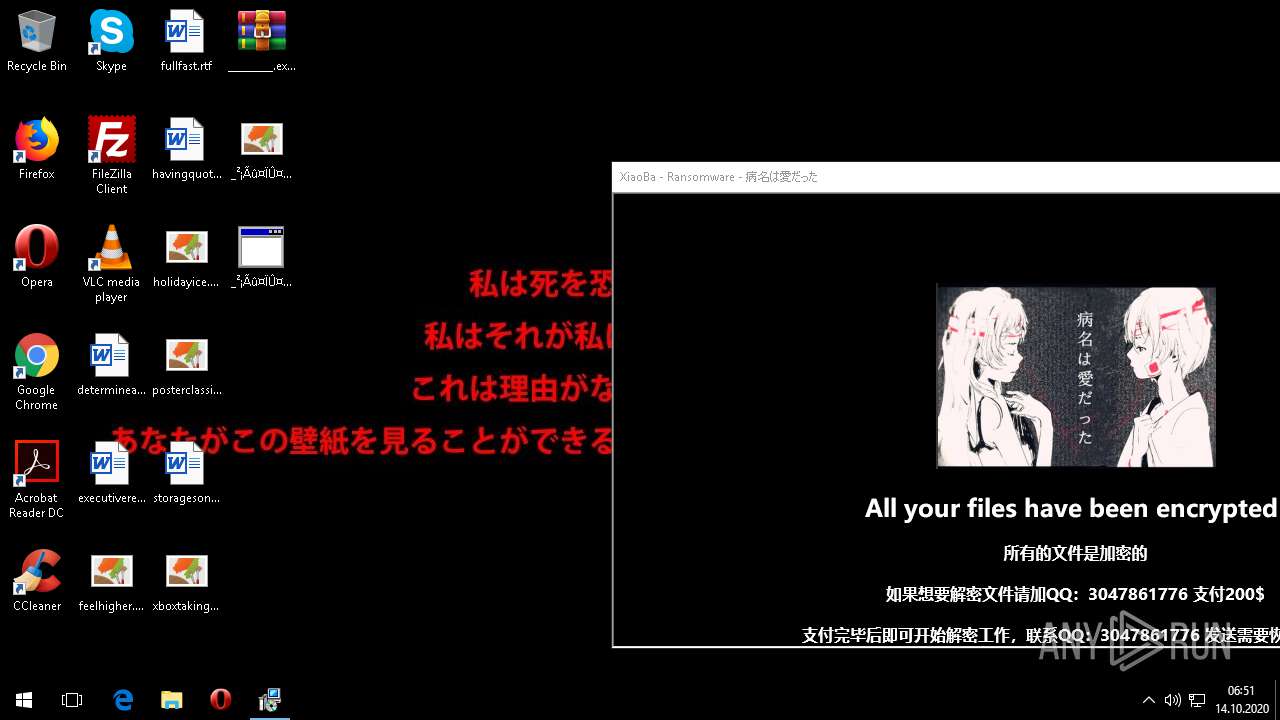
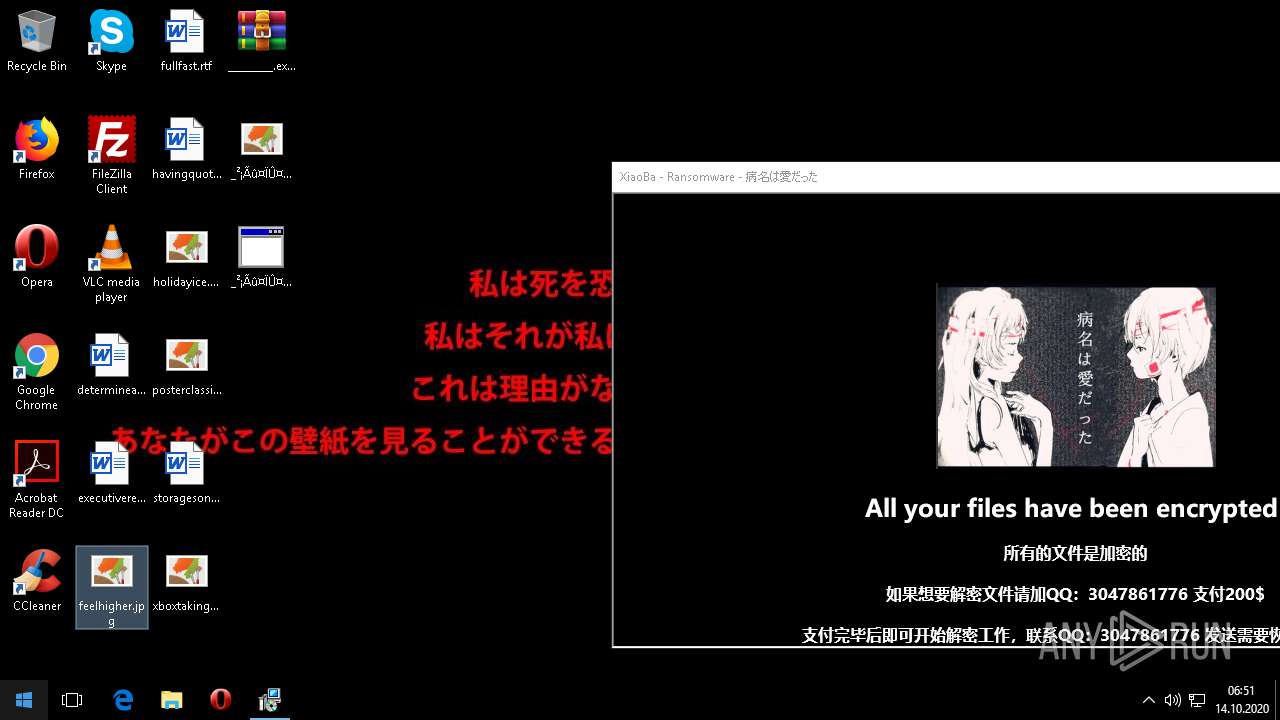
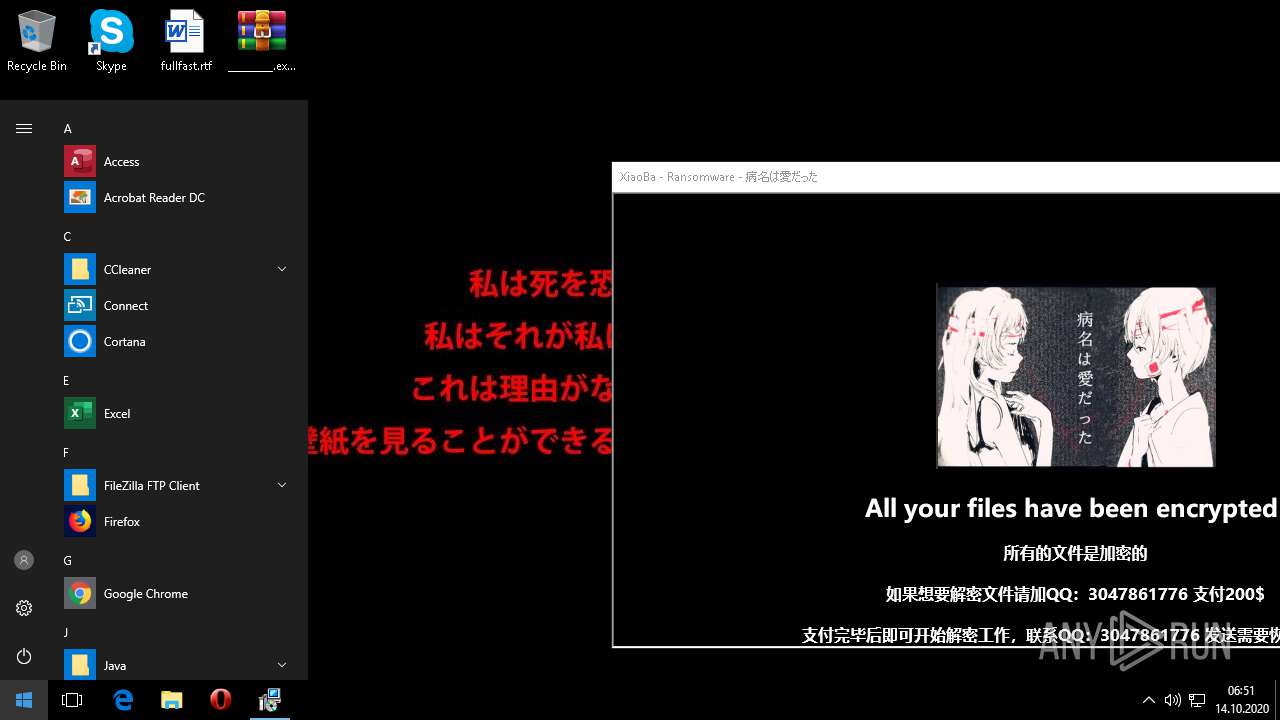
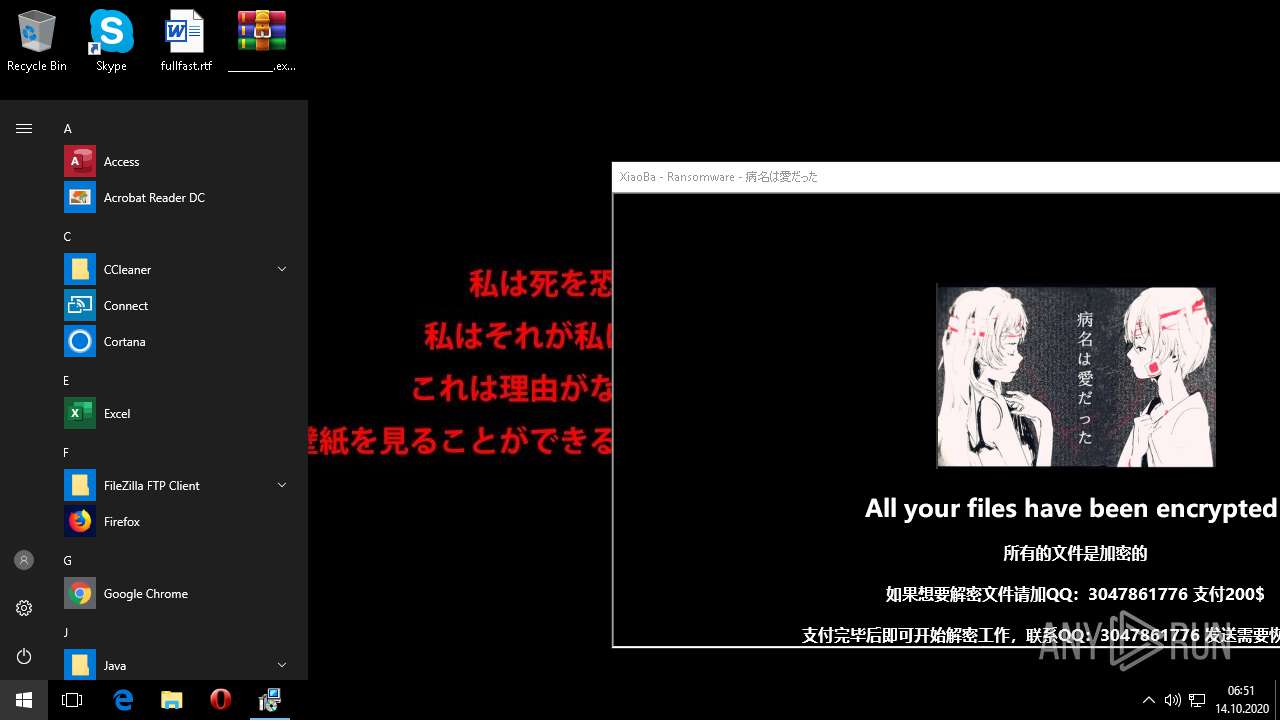
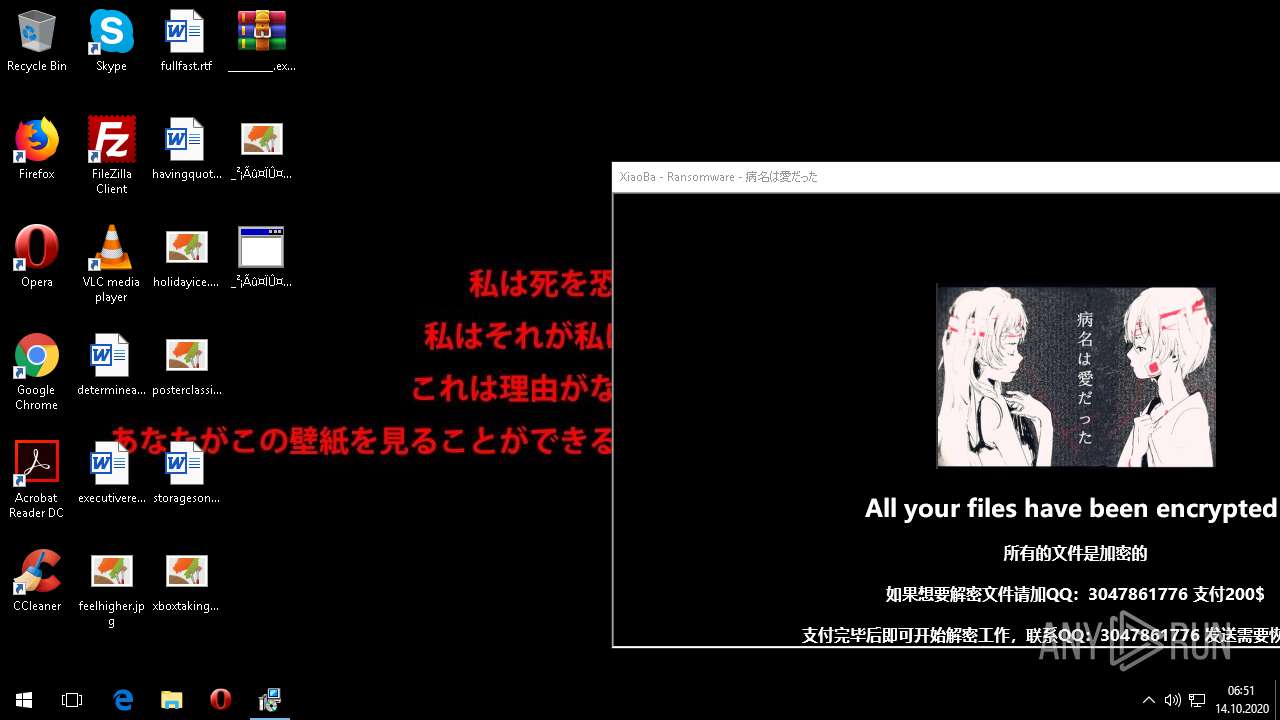
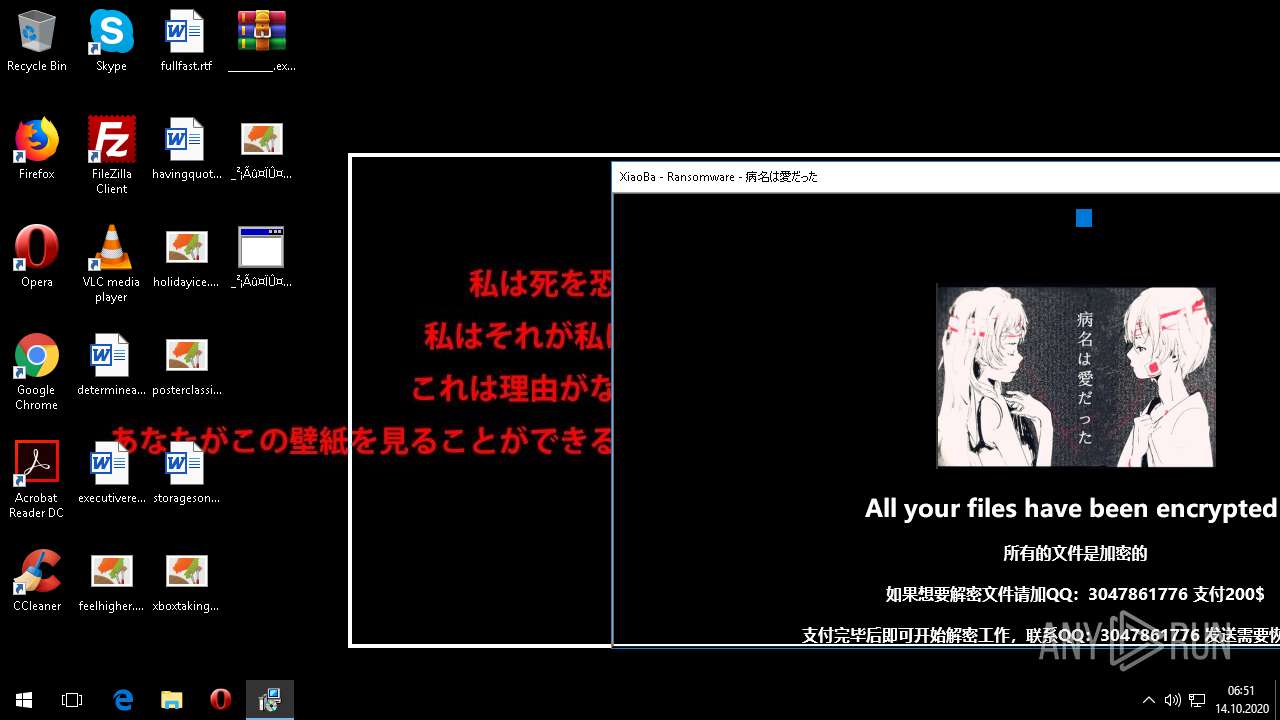
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2020, 06:44:27 |
| OS: | Windows 10 Professional (build: 16299, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6A5DC03007018B334EAC4DED68FD6818 |
| SHA1: | 7F1037B269FBE20712D788476BAD17BC5709BC67 |
| SHA256: | 201AFF50BB482133FE41657CF92C0A48CC7C5FD674E4680BB49D6A3FF2F0B09A |
| SSDEEP: | 98304:V9X8Y6ZjPF0N02AD3OiFZgtGdjPh39s84FeATMxJea90:j8VTGNi3HZgto7xJ/0 |
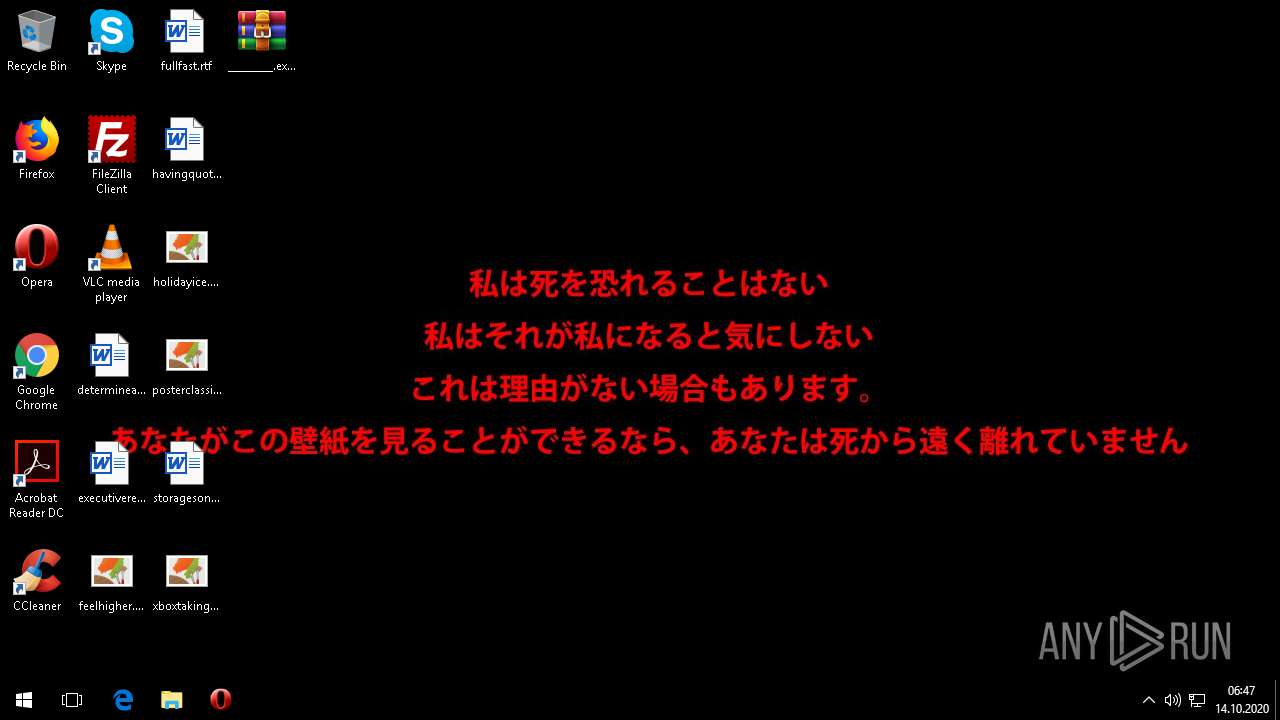
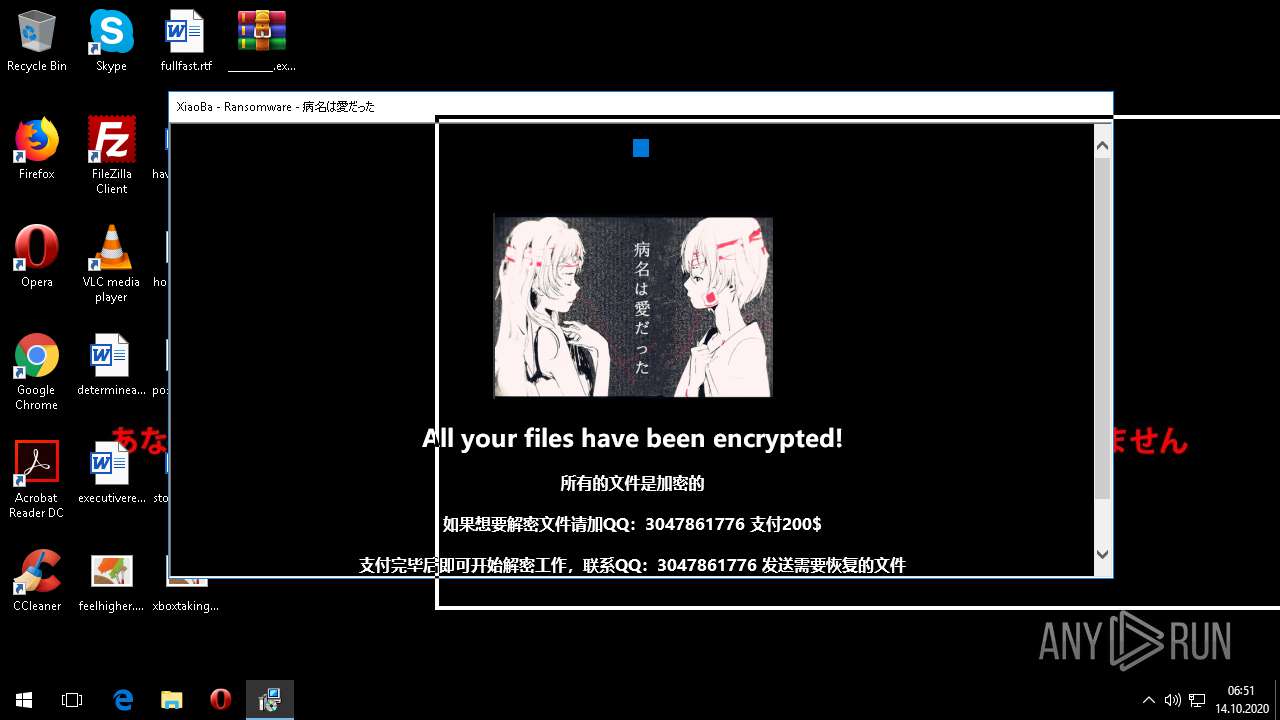
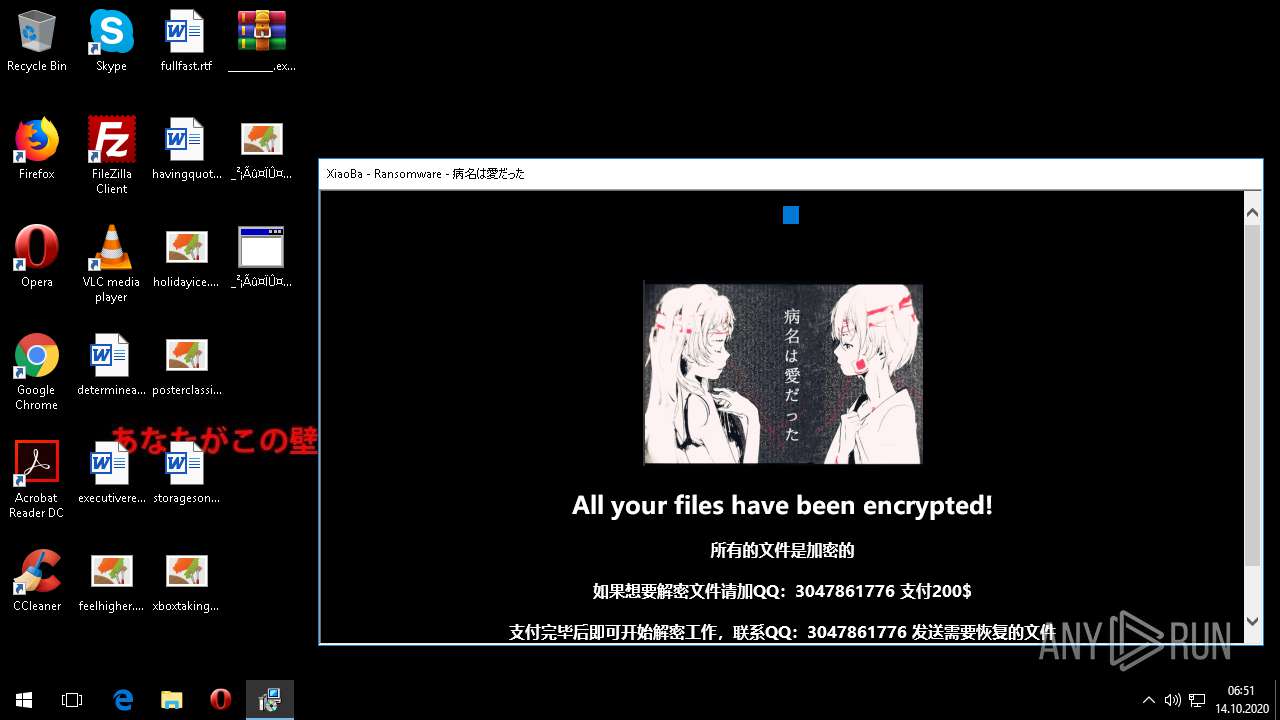
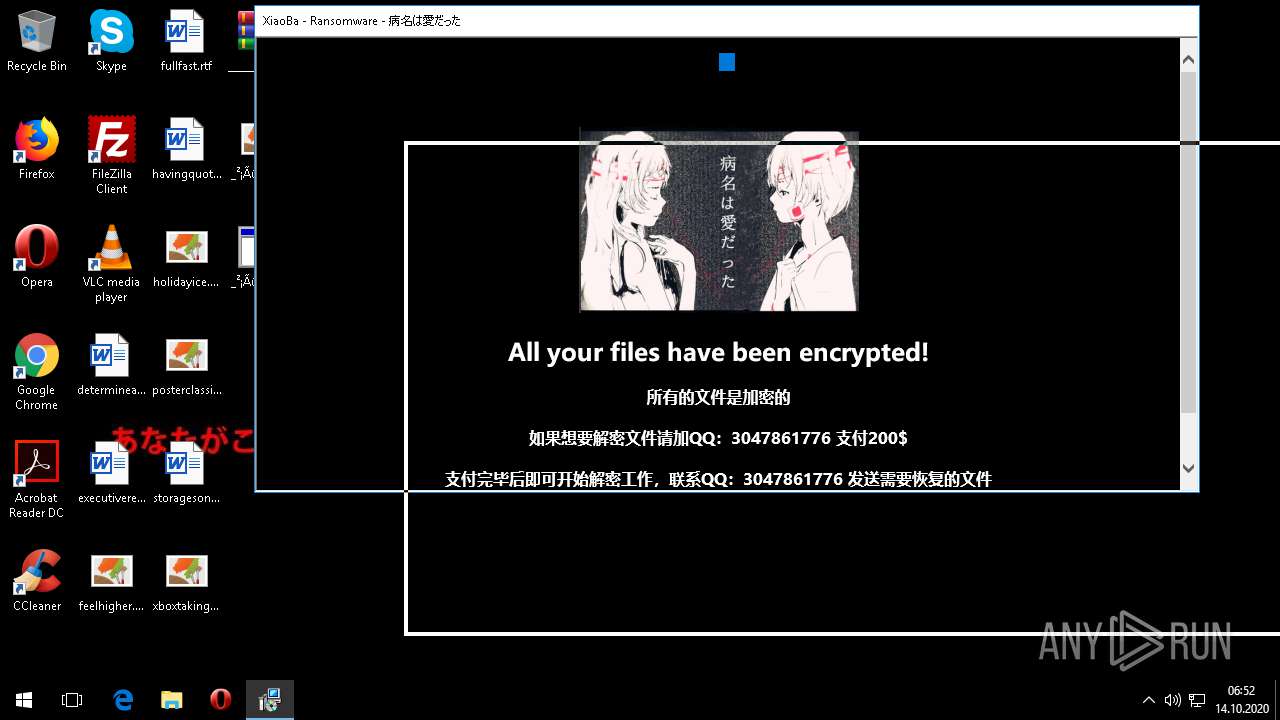
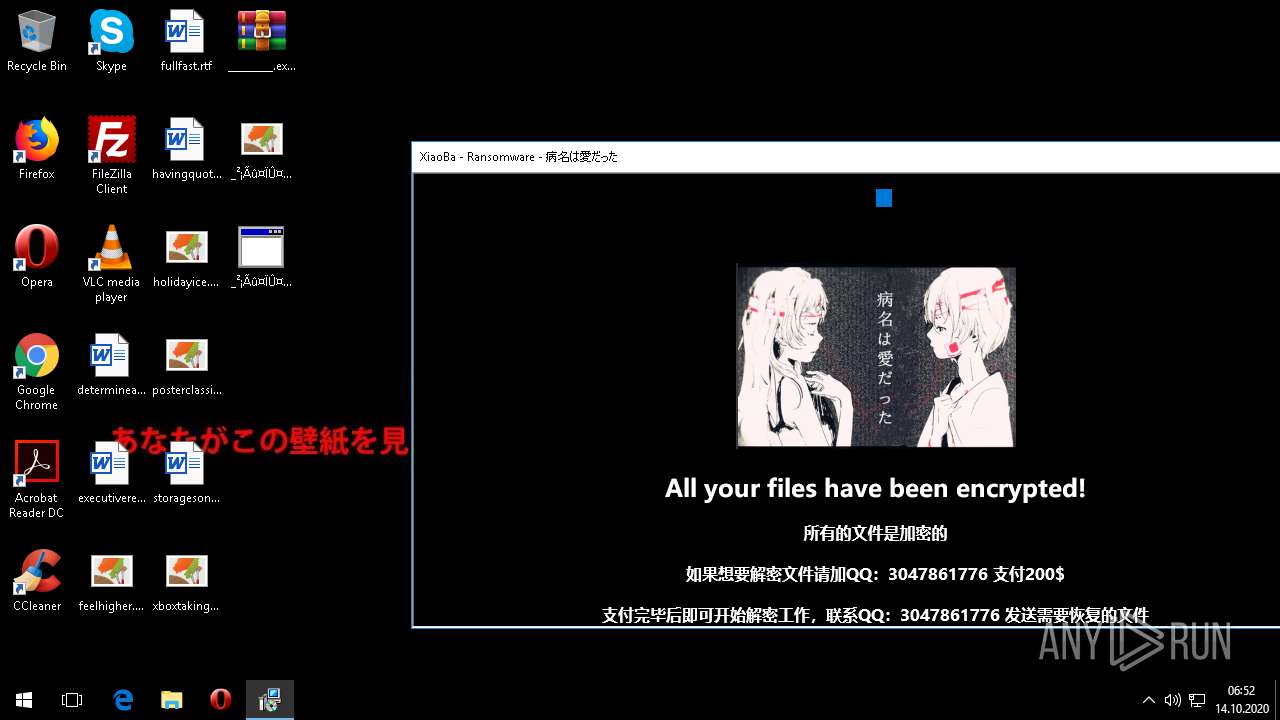
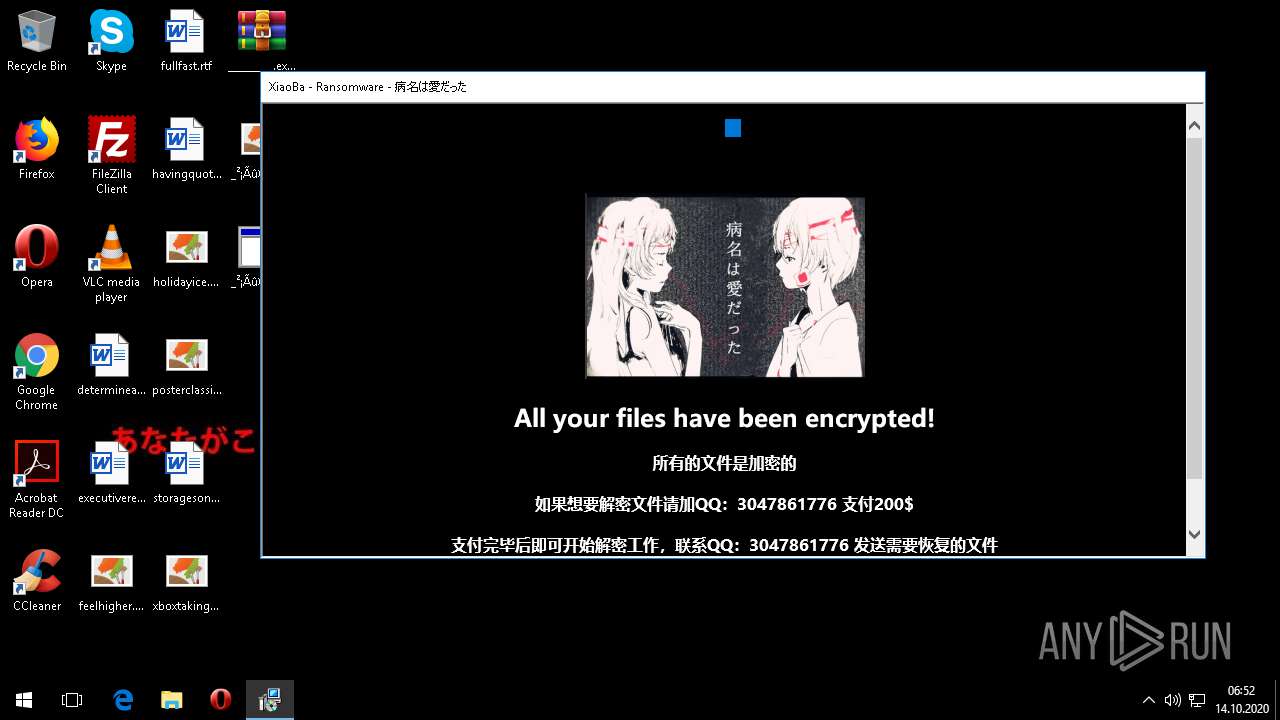
MALICIOUS
Application was dropped or rewritten from another process
- _________.exe (PID: 1740)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1804)
Writes to a desktop.ini file (may be used to cloak folders)
- _________.exe (PID: 1740)
Starts MSHTA.EXE for opening HTA or HTMLS files
- _________.exe (PID: 1740)
Creates files in the program directory
- _________.exe (PID: 1740)
Starts CMD.EXE for commands execution
- _________.exe (PID: 1740)
INFO
Manual execution by user
- _________.exe (PID: 1740)
Reads internet explorer settings
- mshta.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:10:09 05:55:27 |
| ZipCRC: | 0xfd341637 |
| ZipCompressedSize: | 3934898 |
| ZipUncompressedSize: | 4205056 |
| ZipFileName: | _________.exe |
Total processes
67
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
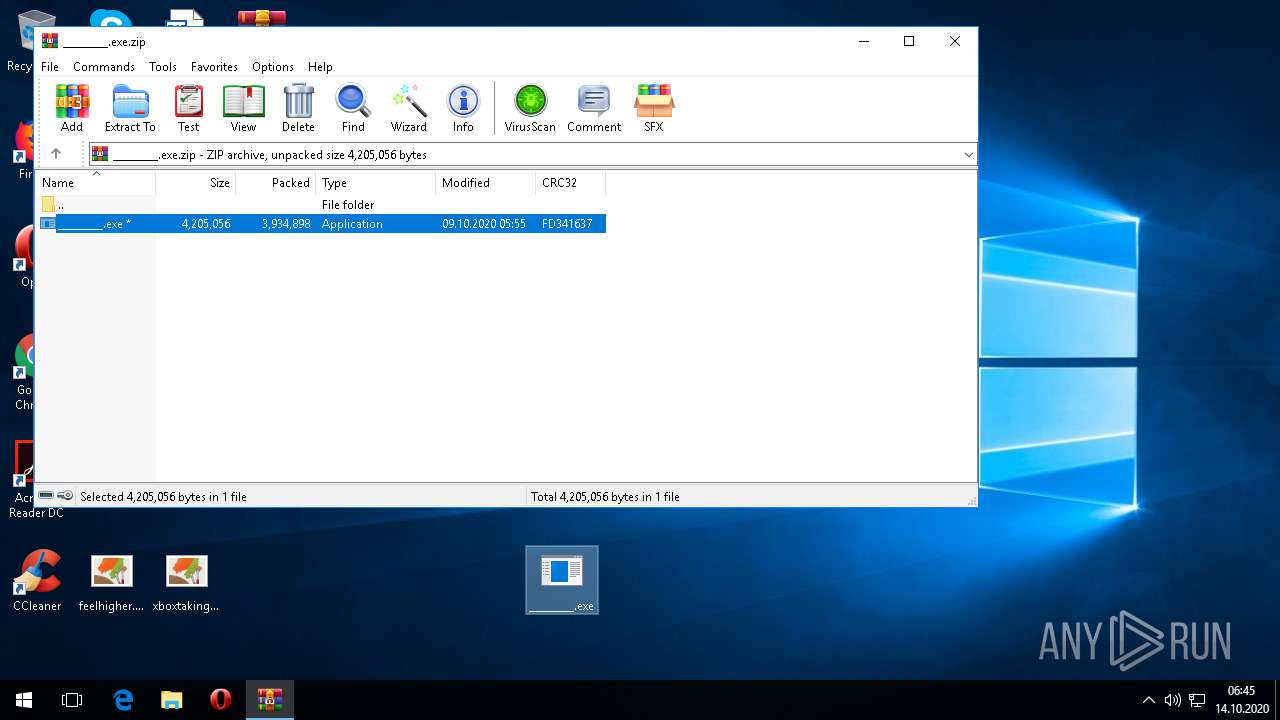
| 1740 | "C:\Users\admin\Desktop\_________.exe" | C:\Users\admin\Desktop\_________.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226356 Modules
| |||||||||||||||
| 1804 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\_________.exe.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2992 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\_²¡Ãû¤ÏÛ¤À¤Ã¤¿_.hta" | C:\Windows\System32\mshta.exe | — | _________.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3432 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4068 | cmd.exe /c del "C:\Users\admin\Desktop\_________.exe" | C:\WINDOWS\SYSTEM32\cmd.exe | — | _________.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
980
Read events
917
Write events
63
Delete events
0
Modification events
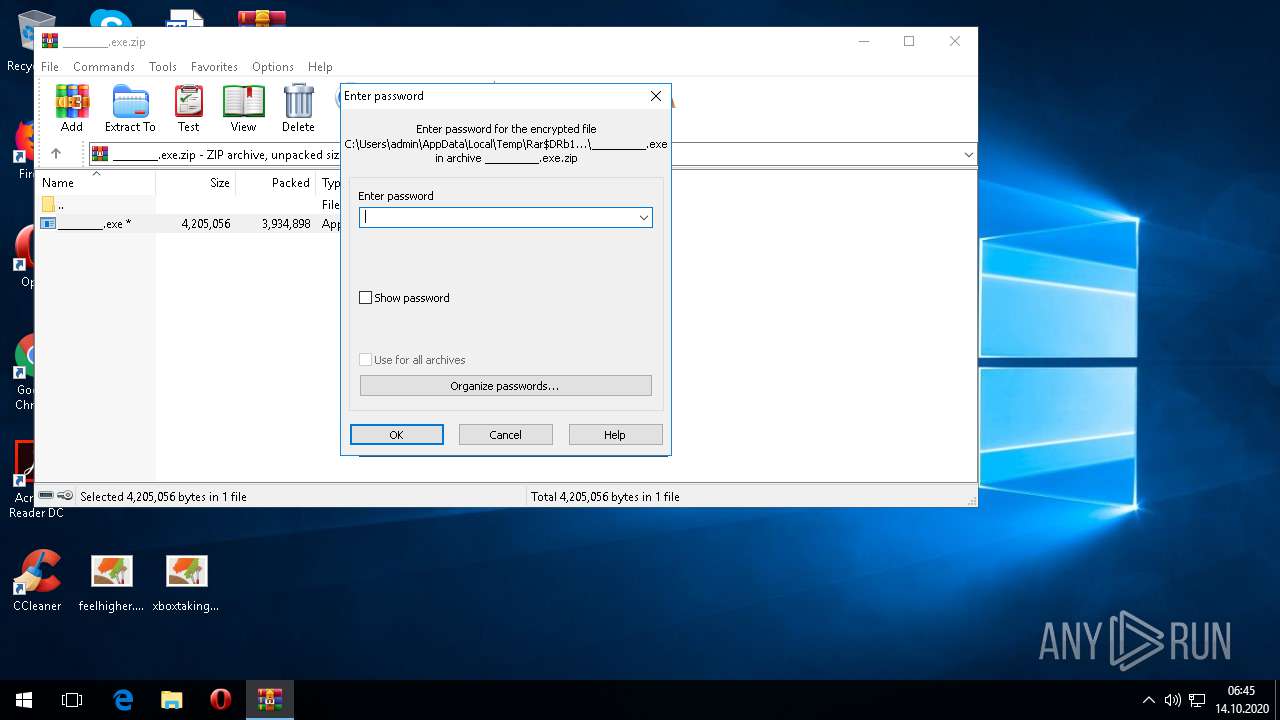
| (PID) Process: | (1804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1804) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\69\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\_________.exe.zip | |||
| (PID) Process: | (1804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1804) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF1A0000001A000000DA03000003020000 | |||
Executable files
1
Suspicious files
1
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1740 | _________.exe | C:\BOOTNXT.²¡Ãû¤ÏÛ¤À¤Ã¤¿[QQ-3047861776].XiaoBa | — | |
MD5:— | SHA256:— | |||
| 1740 | _________.exe | C:\Program Files\desktop.ini.²¡Ãû¤ÏÛ¤À¤Ã¤¿[QQ-3047861776].XiaoBa | — | |
MD5:— | SHA256:— | |||
| 1740 | _________.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Benioku.htm | — | |
MD5:— | SHA256:— | |||
| 1740 | _________.exe | C:\Program Files\Adobe\Acrobat Reader DC\Benioku.htm.²¡Ãû¤ÏÛ¤À¤Ã¤¿[QQ-3047861776].XiaoBa | — | |
MD5:— | SHA256:— | |||
| 1740 | _________.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Berime.htm | — | |
MD5:— | SHA256:— | |||
| 1740 | _________.exe | C:\Program Files\Adobe\Acrobat Reader DC\Berime.htm.²¡Ãû¤ÏÛ¤À¤Ã¤¿[QQ-3047861776].XiaoBa | — | |
MD5:— | SHA256:— | |||
| 1740 | _________.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm | — | |
MD5:— | SHA256:— | |||
| 1740 | _________.exe | C:\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm.²¡Ãû¤ÏÛ¤À¤Ã¤¿[QQ-3047861776].XiaoBa | — | |
MD5:— | SHA256:— | |||
| 1740 | _________.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leame.htm | — | |
MD5:— | SHA256:— | |||
| 1740 | _________.exe | C:\Program Files\Adobe\Acrobat Reader DC\Leame.htm.²¡Ãû¤ÏÛ¤À¤Ã¤¿[QQ-3047861776].XiaoBa | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1708 | svchost.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | der | 1.11 Kb | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.90.23.154:443 | login.live.com | Microsoft Corporation | US | unknown |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1708 | svchost.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
2480 | w32tm.exe | 51.105.208.173:123 | time.windows.com | Microsoft Corporation | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
config.edge.skype.com |
| malicious |
crl.microsoft.com |
| whitelisted |
time.windows.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |