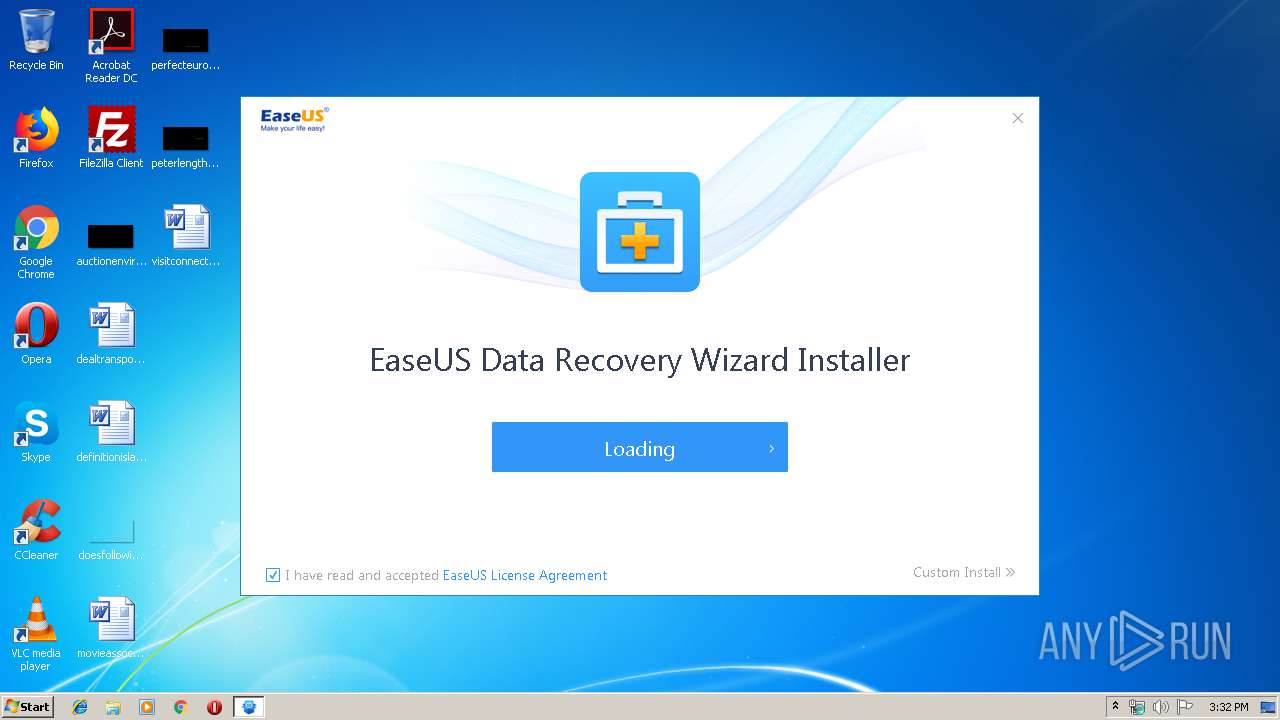
| File name: | DRW_trial_Installer_20190717.226.exe |
| Full analysis: | https://app.any.run/tasks/3ee15cb0-c0d8-4c03-8c4a-3e5a13d4dfdc |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 14:31:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | FAA09818F36A2C5E14B44059624E8DB3 |
| SHA1: | 2995D9863EF182B3BFF06AF4C717DD65B8073EF1 |
| SHA256: | 201576D57395E27F930213E9146E0B330DCA9DDE628D8C00EB9E8274C74652A4 |
| SSDEEP: | 24576:Yyh/56rH5kYFYnJMKrkjjCD5VPtSXKzeV1WtMGNvEN/AazUFdvUl9145smBXsdDp:z/gb5kYFYhrkjjCN5tMKzxMGiibdvUtr |
MALICIOUS
Application was dropped or rewritten from another process
- InfoForSetup.exe (PID: 4084)
- InfoForSetup.exe (PID: 2848)
- AliyunWrapExe.Exe (PID: 3340)
- EDownloader.exe (PID: 3468)
- InfoForSetup.exe (PID: 3628)
- InfoForSetup.exe (PID: 3416)
- InfoForSetup.exe (PID: 2792)
- InfoForSetup.exe (PID: 2556)
- InfoForSetup.exe (PID: 3688)
- InfoForSetup.exe (PID: 2608)
- InfoForSetup.exe (PID: 2528)
- InfoForSetup.exe (PID: 3116)
- InfoForSetup.exe (PID: 3164)
- EuSendMessage.exe (PID: 3036)
- EUSetXMLValue.exe (PID: 452)
- EUinApp.exe (PID: 3532)
- InfoForSetup.exe (PID: 3704)
- InfoForSetup.exe (PID: 1720)
- DRW.exe (PID: 2980)
- DRWUI.exe (PID: 3660)
- EuDownloader.exe (PID: 2416)
- EUinApp.exe (PID: 2840)
- EuDownloader.exe (PID: 3848)
- EuDownloader.exe (PID: 3688)
- EUUnZip.exe (PID: 356)
Loads dropped or rewritten executable
- AliyunWrapExe.Exe (PID: 3340)
- InfoForSetup.exe (PID: 2848)
- InfoForSetup.exe (PID: 2792)
- InfoForSetup.exe (PID: 3416)
- InfoForSetup.exe (PID: 2608)
- InfoForSetup.exe (PID: 3628)
- InfoForSetup.exe (PID: 4084)
- InfoForSetup.exe (PID: 2556)
- InfoForSetup.exe (PID: 3688)
- InfoForSetup.exe (PID: 2528)
- InfoForSetup.exe (PID: 3116)
- InfoForSetup.exe (PID: 3164)
- InfoForSetup.exe (PID: 3704)
- InfoForSetup.exe (PID: 1720)
- DRWUI.exe (PID: 3660)
- DRW.exe (PID: 2980)
Downloads executable files from the Internet
- EDownloader.exe (PID: 3468)
SUSPICIOUS
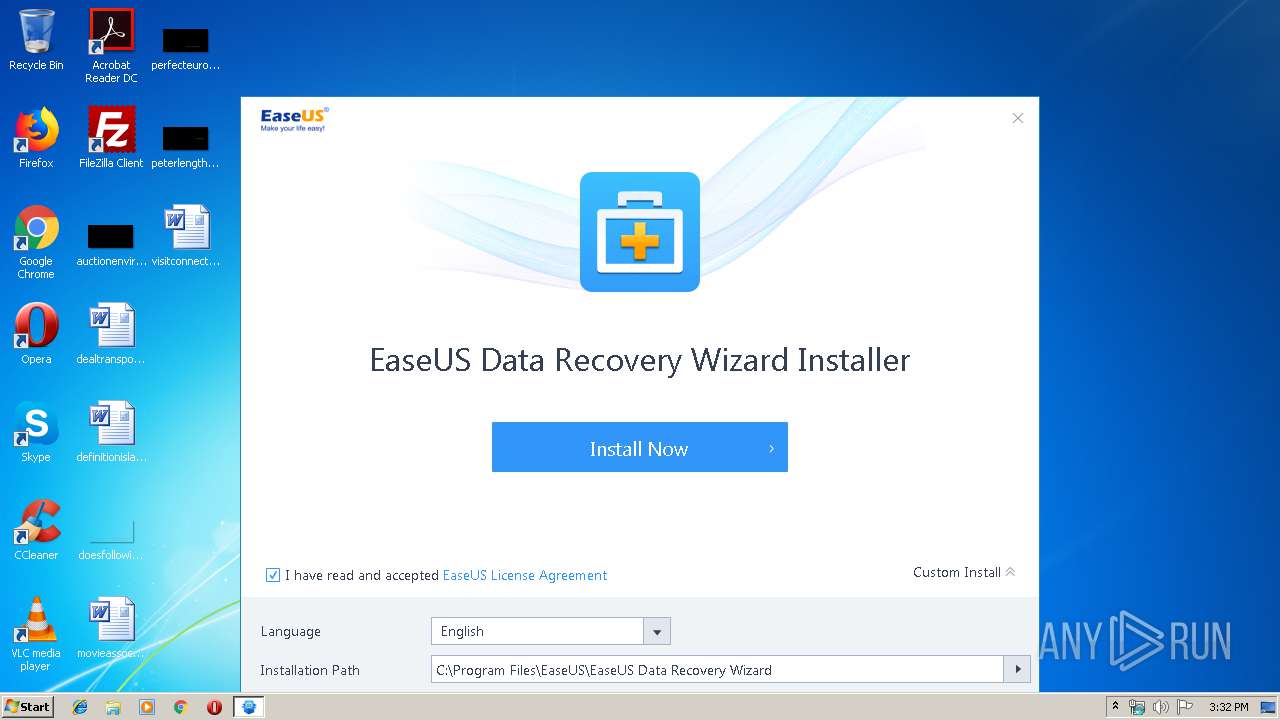
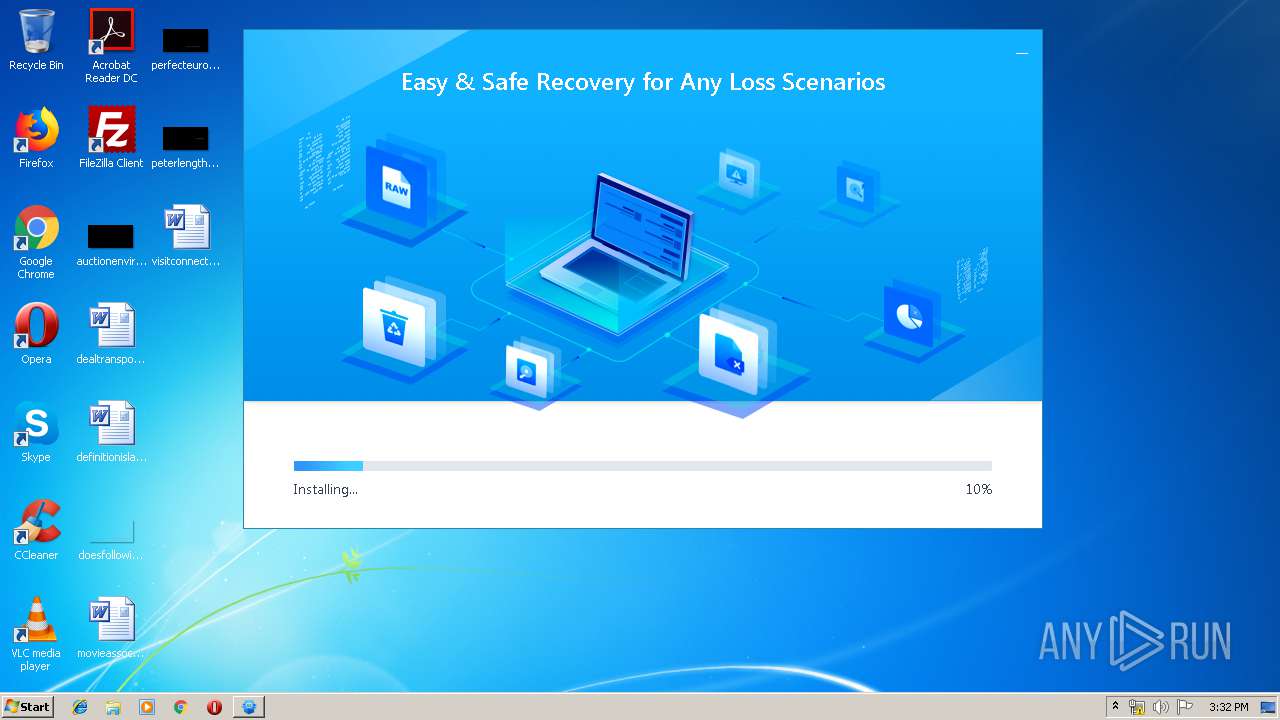
Executable content was dropped or overwritten
- DRW_trial_Installer_20190717.226.exe (PID: 988)
- DRW_trial_easeus.exe (PID: 3556)
- DRW_trial_easeus.tmp (PID: 2692)
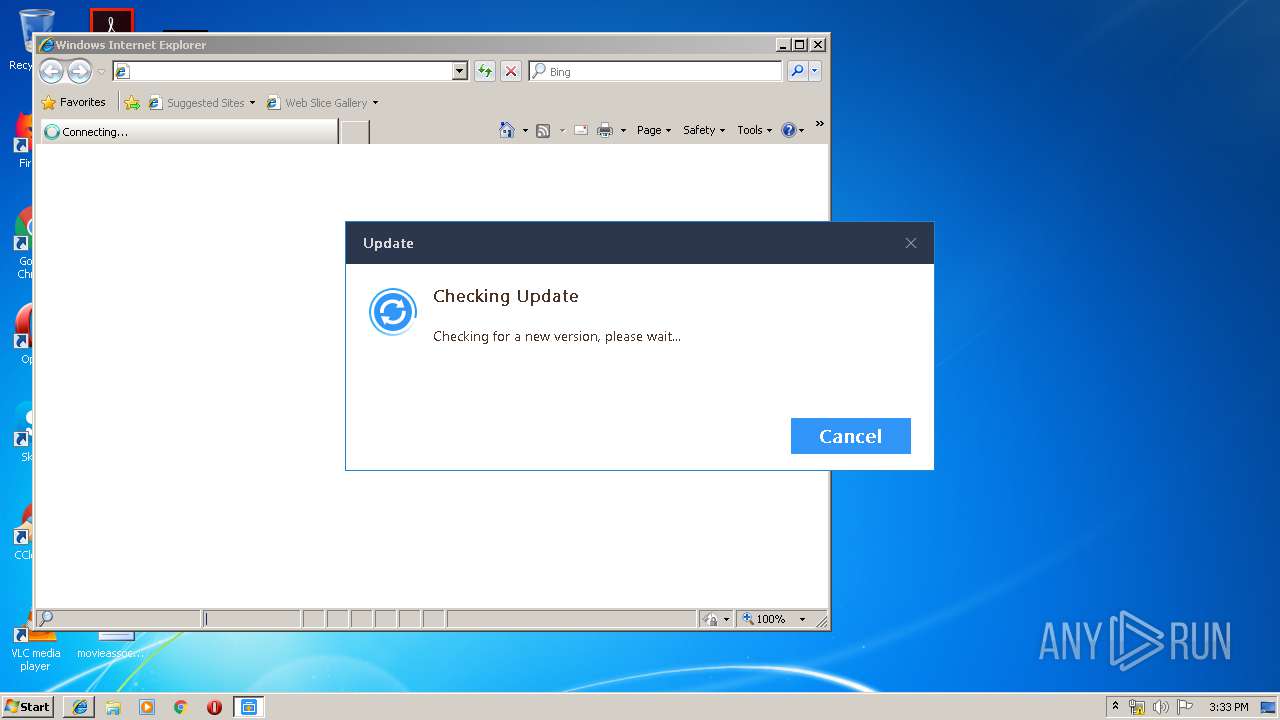
Reads internet explorer settings
- EDownloader.exe (PID: 3468)
Reads Windows owner or organization settings
- DRW_trial_easeus.tmp (PID: 2692)
Reads the Windows organization settings
- DRW_trial_easeus.tmp (PID: 2692)
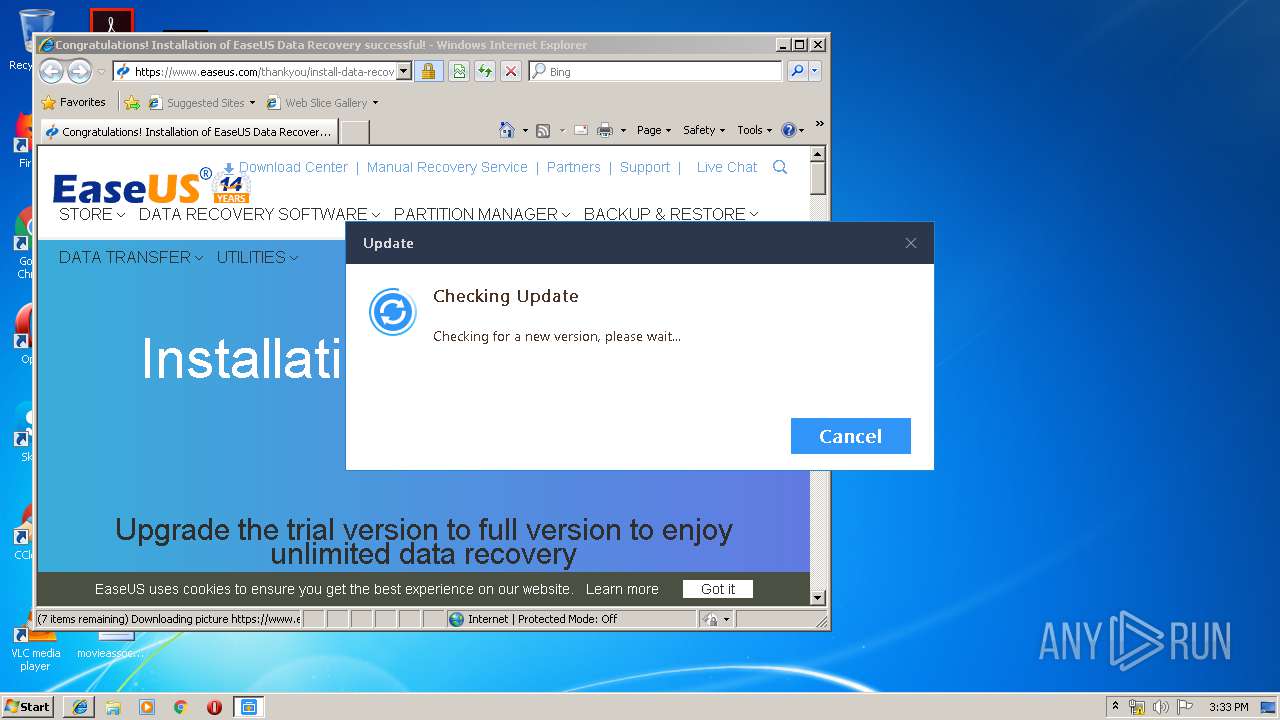
Changes IE settings (feature browser emulation)
- EUinApp.exe (PID: 3532)
- EUinApp.exe (PID: 2840)
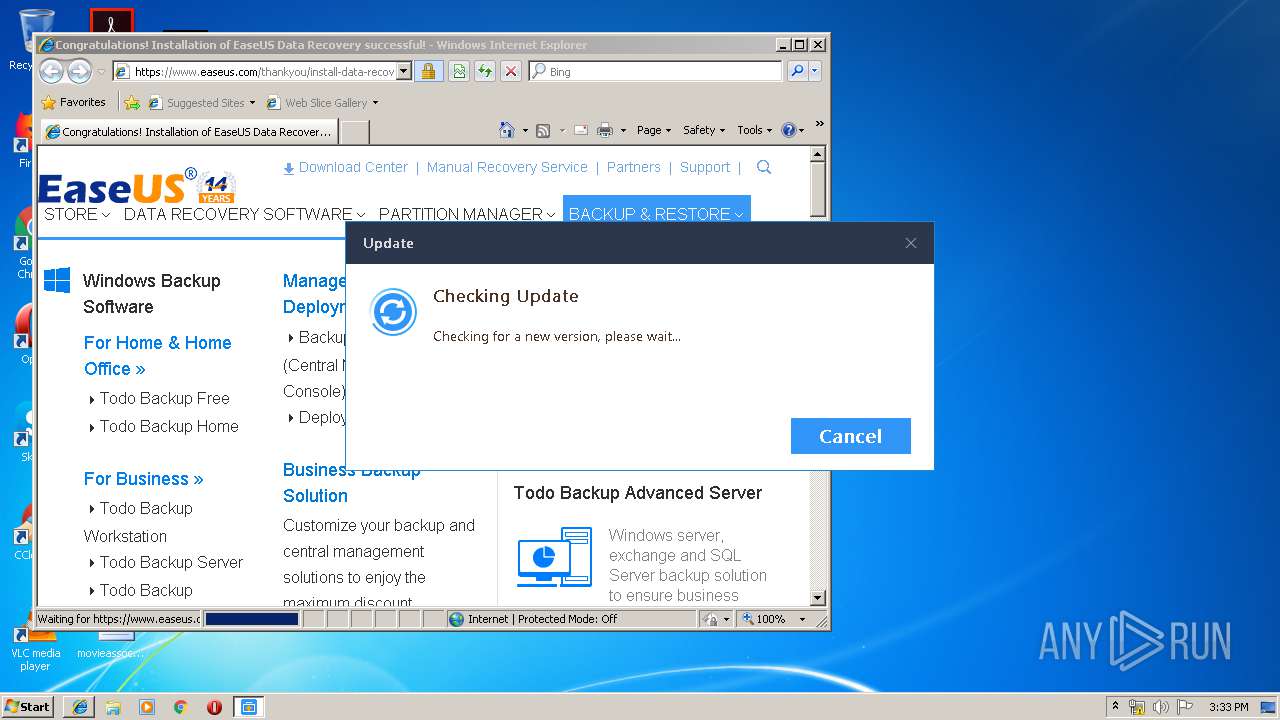
Starts Internet Explorer
- EDownloader.exe (PID: 3468)
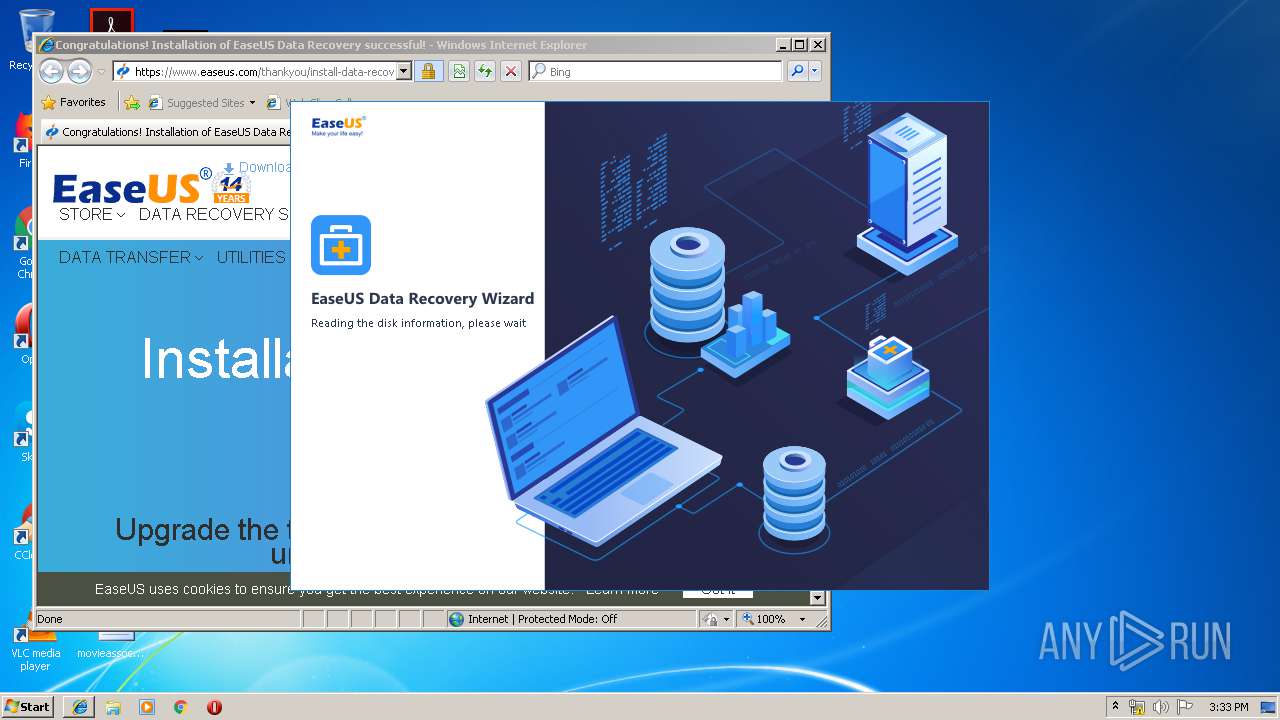
Creates files in the program directory
- DRW.exe (PID: 2980)
- EuDownloader.exe (PID: 2416)
- EuDownloader.exe (PID: 3848)
- EuDownloader.exe (PID: 3688)
- DRWUI.exe (PID: 3660)
- EUUnZip.exe (PID: 356)
Low-level read access rights to disk partition
- DRWUI.exe (PID: 3660)
INFO
Application was dropped or rewritten from another process
- DRW_trial_easeus.tmp (PID: 2692)
Loads dropped or rewritten executable
- DRW_trial_easeus.tmp (PID: 2692)
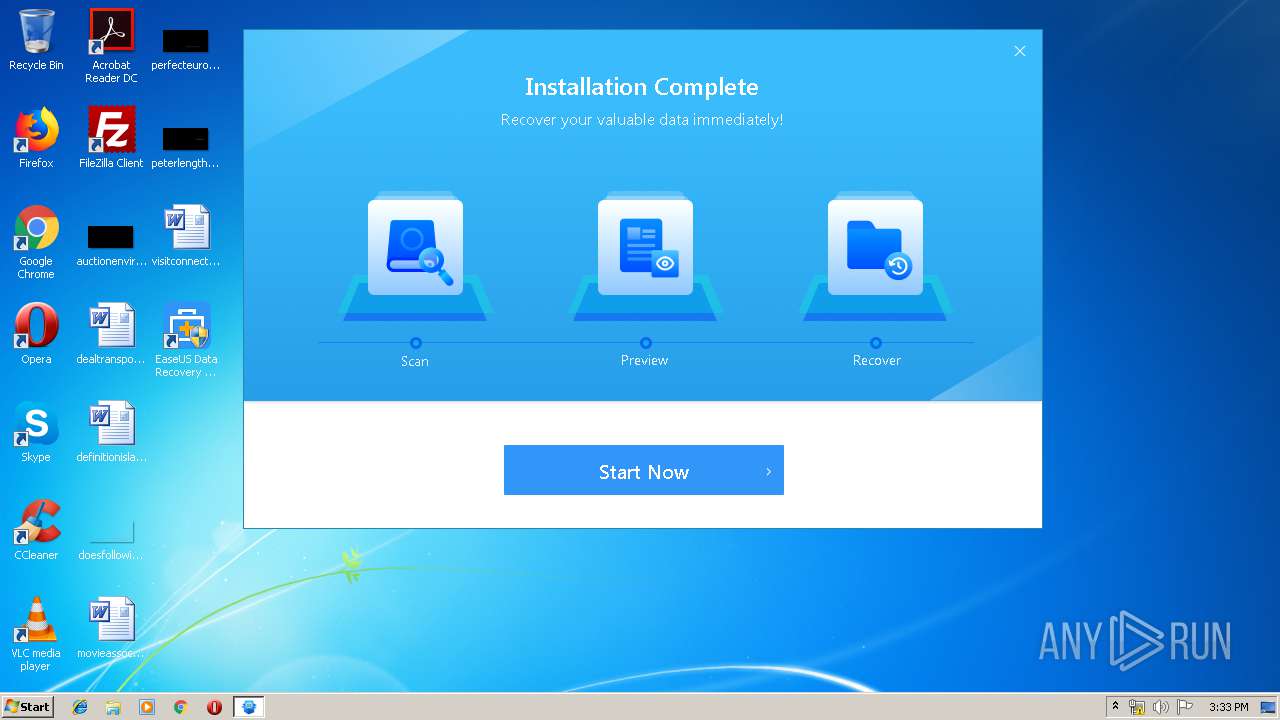
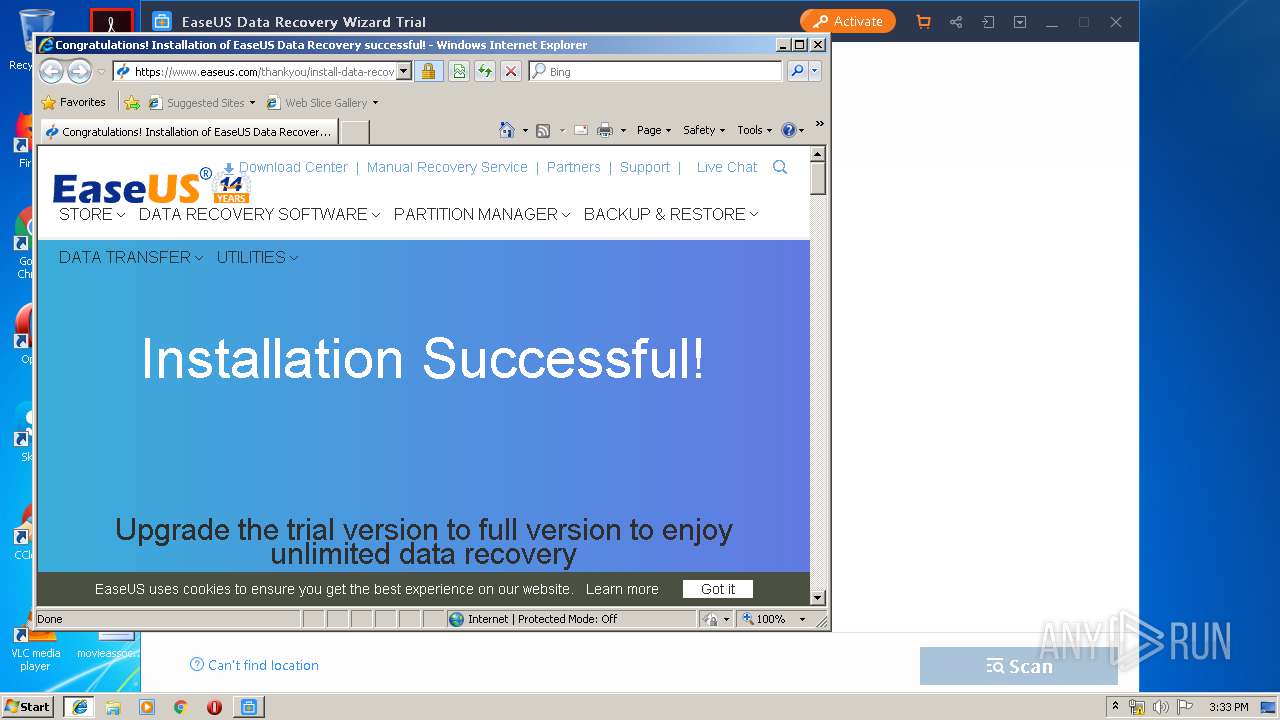
Creates a software uninstall entry
- DRW_trial_easeus.tmp (PID: 2692)
Changes internet zones settings
- iexplore.exe (PID: 3716)
Creates files in the program directory
- DRW_trial_easeus.tmp (PID: 2692)
Creates files in the user directory
- iexplore.exe (PID: 3416)
Reads Internet Cache Settings
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 3716)
Reads internet explorer settings
- iexplore.exe (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:48+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:48 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006627 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45224 |
.rdata | 0x00008000 | 0x0000149A | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00708 |
.data | 0x0000A000 | 0x0002AFF8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03532 |
.ndata | 0x00035000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00045000 | 0x00010D40 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.14037 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28733 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.86193 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.0916 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 3.68334 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 3.86293 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 3.67461 | 1640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.5329 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 5.22737 | 1128 | UNKNOWN | English - United States | RT_ICON |
9 | 3.99637 | 744 | UNKNOWN | English - United States | RT_ICON |
10 | 3.53259 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
76
Monitored processes
31
Malicious processes
5
Suspicious processes
12
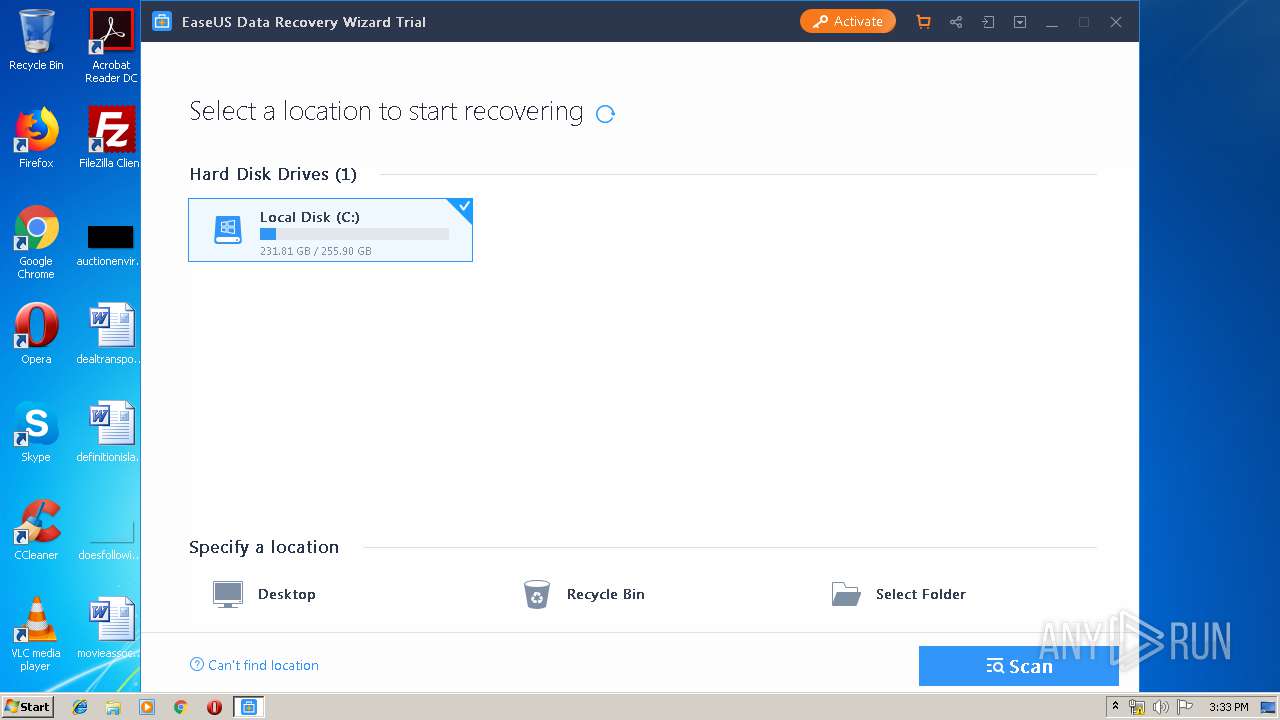
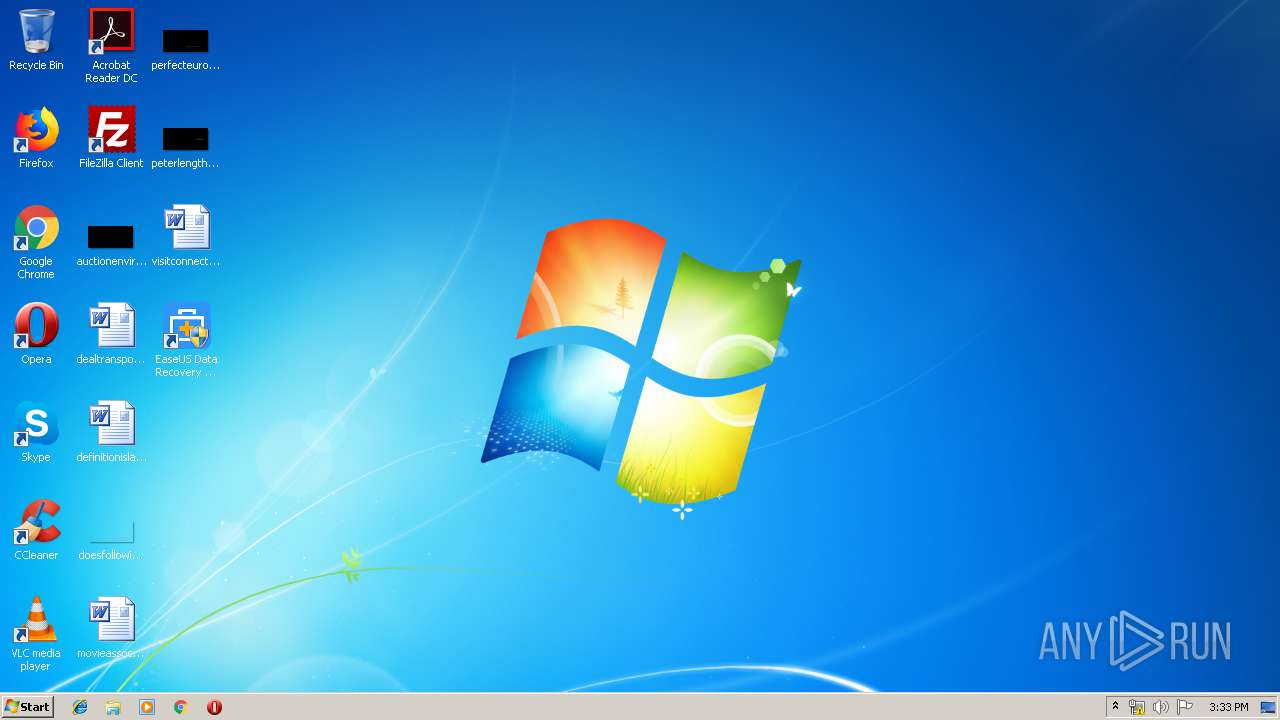
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\EUUnZip.exe" "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\InnerBuy.zip" "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\InnerBuy" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\EUUnZip.exe | — | DRWUI.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 452 | "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\EUSetXMLValue.exe" "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\Resource.xml" Resource Purchase buyTrialCompareTec_0 url &x-url=201907152-226 1 | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\EUSetXMLValue.exe | — | DRW_trial_easeus.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 988 | "C:\Users\admin\AppData\Local\Temp\DRW_trial_Installer_20190717.226.exe" | C:\Users\admin\AppData\Local\Temp\DRW_trial_Installer_20190717.226.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1720 | /SendInfo Window "Install_Finish" Activity "Click_Startnow" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\EuDownloader.exe" "https://update.easeus.com/update/drw_eng/drw.ini?time=132078512022820000" "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\Upgrade.ini" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\EuDownloader.exe | DRWUI.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2528 | /SendInfo Window "Downloading" Activity "Trigger_cdnswitch" Attribute "{\"Cdn\":\"http://download.easeus.com/trial/drw_trial.exe\",\"Result\":\"Success\",\"err\":\"0\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2556 | /SendInfo Window "Home_Installer" Activity "Click_Uncheck_Infocollect" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2608 | /Disable | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2692 | "C:\Users\admin\AppData\Local\Temp\is-TR2HN.tmp\DRW_trial_easeus.tmp" /SL5="$30196,42362212,192512,C:\Users\admin\AppData\Local\Temp\DRW_trial_easeus.exe" /verysilent /DIR="C:\Program Files\EaseUS\EaseUS Data Recovery Wizard" /LANG=en agreeImprove=false GUID=E70C41AC-A186-4df8-B2F4-F662BDD91B29 xurlID=226 /LOG=C:\Users\admin\AppData\Local\Temp\\easeusproductsetup.log | C:\Users\admin\AppData\Local\Temp\is-TR2HN.tmp\DRW_trial_easeus.tmp | DRW_trial_easeus.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2792 | /SendInfo Window "Home_Installer" Activity "Trigger_cdnswitch" Attribute "{\"Cdn\":\"http://download.easeus.com/api/index.php/Home/Index/productInstall/\",\"Result\":\"Success\",\"err\":\"0\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 230
Read events
1 089
Write events
133
Delete events
8
Modification events
| (PID) Process: | (3468) EDownloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\EASEUS\DownLoadInstall |
| Operation: | write | Name: | GUID |
Value: E70C41AC-A186-4df8-B2F4-F662BDD91B29 | |||
| (PID) Process: | (3340) AliyunWrapExe.Exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AliyunWrapExe_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3340) AliyunWrapExe.Exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AliyunWrapExe_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3340) AliyunWrapExe.Exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AliyunWrapExe_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3340) AliyunWrapExe.Exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AliyunWrapExe_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3340) AliyunWrapExe.Exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AliyunWrapExe_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3340) AliyunWrapExe.Exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AliyunWrapExe_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3340) AliyunWrapExe.Exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AliyunWrapExe_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3340) AliyunWrapExe.Exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AliyunWrapExe_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3340) AliyunWrapExe.Exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AliyunWrapExe_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
58
Suspicious files
11
Text files
978
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 988 | DRW_trial_Installer_20190717.226.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\EDownloader.exe | executable | |
MD5:— | SHA256:— | |||
| 988 | DRW_trial_Installer_20190717.226.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\Dutch.ini | text | |
MD5:— | SHA256:— | |||
| 988 | DRW_trial_Installer_20190717.226.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\skin.zip | compressed | |
MD5:— | SHA256:— | |||
| 988 | DRW_trial_Installer_20190717.226.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\Chinese.ini | text | |
MD5:— | SHA256:— | |||
| 988 | DRW_trial_Installer_20190717.226.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\Japanese.ini | text | |
MD5:— | SHA256:— | |||
| 988 | DRW_trial_Installer_20190717.226.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\Danish.ini | text | |
MD5:— | SHA256:— | |||
| 988 | DRW_trial_Installer_20190717.226.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\Arabic.ini | text | |
MD5:— | SHA256:— | |||
| 988 | DRW_trial_Installer_20190717.226.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\German.ini | text | |
MD5:— | SHA256:— | |||
| 988 | DRW_trial_Installer_20190717.226.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\French.ini | text | |
MD5:— | SHA256:— | |||
| 988 | DRW_trial_Installer_20190717.226.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2trial\Norwegian.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
52
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3468 | EDownloader.exe | GET | — | 205.185.216.10:80 | http://download.easeus.com/trial/drw_trial.exe | US | — | — | malicious |
3340 | AliyunWrapExe.Exe | POST | — | 47.89.169.181:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_noip/shards/lb | US | — | — | malicious |
3340 | AliyunWrapExe.Exe | POST | 200 | 47.89.169.181:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_noip/shards/lb | US | — | — | malicious |
3468 | EDownloader.exe | POST | 200 | 216.92.47.198:80 | http://track.easeus.com/product/index.php/?a=statistics&p_type=m_drw_user_base_infos | US | — | — | suspicious |
3340 | AliyunWrapExe.Exe | POST | 200 | 47.89.169.181:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_noip/shards/lb | US | — | — | malicious |
2692 | DRW_trial_easeus.tmp | POST | 200 | 216.92.47.198:80 | http://track.easeus.com/product/index.php/?a=statistics&p_type=m_drw_user_base_infos | US | — | — | suspicious |
3340 | AliyunWrapExe.Exe | POST | 200 | 47.89.169.181:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_noip/shards/lb | US | — | — | malicious |
3340 | AliyunWrapExe.Exe | POST | 200 | 47.89.169.181:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_noip/shards/lb | US | — | — | malicious |
3340 | AliyunWrapExe.Exe | POST | 200 | 47.89.169.181:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_noip/shards/lb | US | — | — | malicious |
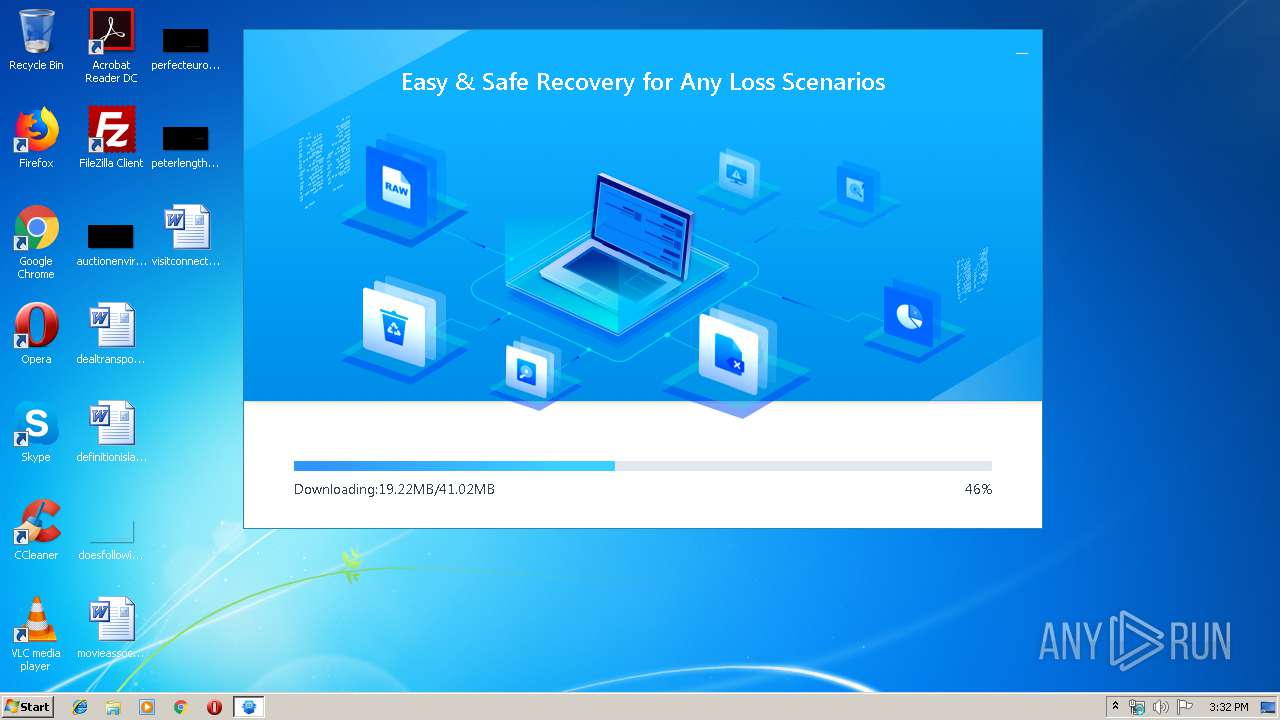
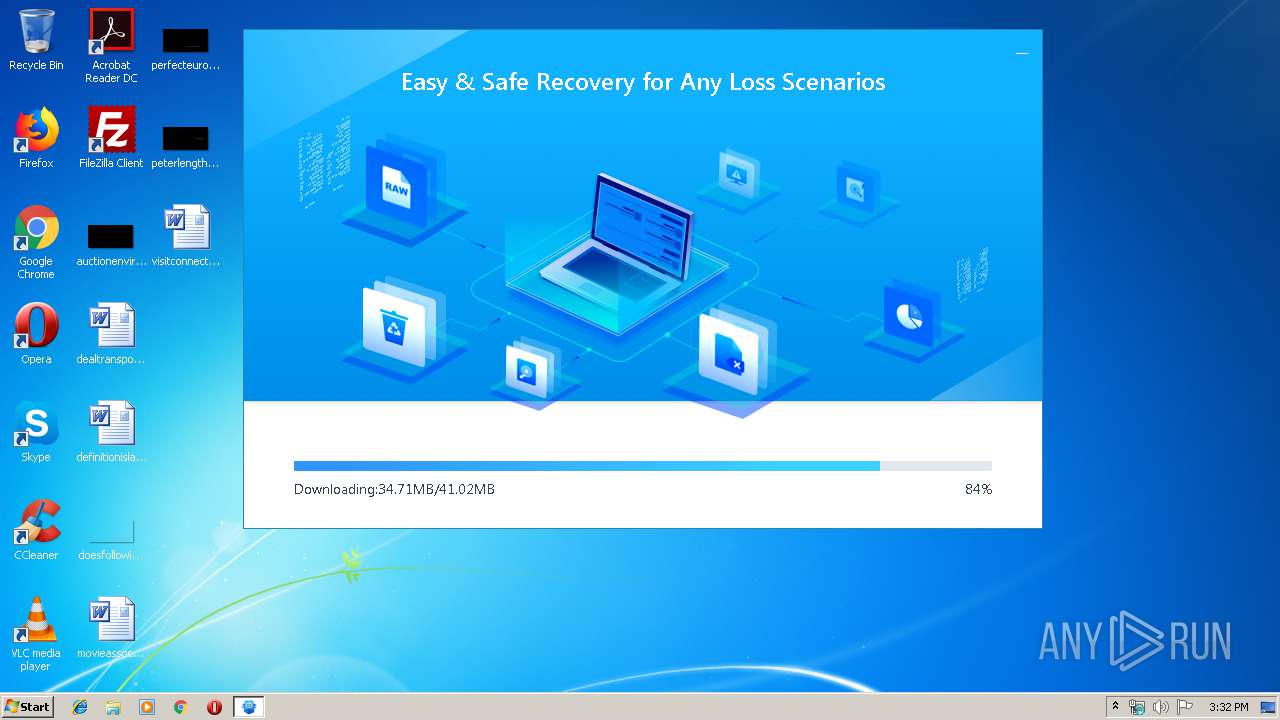
3468 | EDownloader.exe | GET | 206 | 205.185.216.42:80 | http://download.easeus.com/trial/drw_trial.exe | US | executable | 13.6 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3468 | EDownloader.exe | 205.185.216.42:80 | download.easeus.com | Highwinds Network Group, Inc. | US | whitelisted |
3340 | AliyunWrapExe.Exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
3468 | EDownloader.exe | 205.185.216.10:80 | download.easeus.com | Highwinds Network Group, Inc. | US | whitelisted |
3340 | AliyunWrapExe.Exe | 47.89.169.181:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
2692 | DRW_trial_easeus.tmp | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
3468 | EDownloader.exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
3716 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3416 | iexplore.exe | 163.171.132.119:80 | www.easeus.com | — | US | malicious |
3416 | iexplore.exe | 163.171.132.119:443 | www.easeus.com | — | US | malicious |
3416 | iexplore.exe | 172.217.21.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.easeus.com |
| malicious |
track.easeus.com |
| suspicious |
easeusinfo.us-east-1.log.aliyuncs.com |
| unknown |
www.easeus.com |
| whitelisted |
www.bing.com |
| whitelisted |
update.easeus.com |
| whitelisted |
dn-growing.qbox.me |
| unknown |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3468 | EDownloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
DRW_trial_easeus.tmp | 2019-07-17 15:33:04:907[UE] --Info. log level=3
|
DRW_trial_easeus.tmp | 2019-07-17 15:33:04:907[UE] --Warning. InitFields Faild. @ line=171, func=CSmartSpy::Init.
|
DRW_trial_easeus.tmp | 2019-07-17 15:33:04:923[UE] --Info. log level=3
|
DRW_trial_easeus.tmp | 2019-07-17 15:33:04:923[UE] --Info. join=1
|
DRW_trial_easeus.tmp | 2019-07-17 15:33:04:923[UE] --Info. top num =0
|
DRW_trial_easeus.tmp | 2019-07-17 15:33:04:923[UE] --Info. try send=1
|
DRW_trial_easeus.tmp | 2019-07-17 15:33:04:923[UE] --Info. SetText. id=0x3 (3), text=1, inst=6F3E0158
|
DRW_trial_easeus.tmp | 2019-07-17 15:33:04:923[UE] --Info. SetText. id=0x3 (3), text=1, inst=6F3E0158
|
DRW_trial_easeus.tmp | 2019-07-17 15:33:04:923[UE] --Info. SetValue. id=0x2 (2), val=0, inst=6F3E0158
|
DRW_trial_easeus.tmp | 2019-07-17 15:33:04:923[UE] --Info. SetText. id=0x1004 (4100), text=1, inst=6F3E0158
|