| download: | JRT.exe |
| Full analysis: | https://app.any.run/tasks/5ecf5770-ffaf-4982-a926-cd2d05be9f22 |
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2020, 14:21:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E40542C4CC75E658A4615BFEFB308570 |
| SHA1: | 961A8C8C332494201E4F275FE1F50ABAE99140B3 |
| SHA256: | 2000ACF98EF0AC1A2D75C91586B5F30A2BC3ECE6E92388B324614C93A0645CF5 |
| SSDEEP: | 49152:CpOGq7u6FjTz2ulU08Su6pvC0oGsVKxmL1p:CpG7uaU0juCa0oGYKxm5p |
MALICIOUS
Application was dropped or rewritten from another process
- WGET.DAT (PID: 3728)
- CreateRestorePoint.exe (PID: 1916)
- SED.DAT (PID: 2776)
- GREP.DAT (PID: 2860)
- GREP.DAT (PID: 2688)
- GREP.DAT (PID: 2668)
- GREP.DAT (PID: 2876)
- SORT_.DAT (PID: 2012)
- SED.DAT (PID: 2852)
- GREP.DAT (PID: 3176)
- GREP.DAT (PID: 3740)
- GREP.DAT (PID: 3032)
- GREP.DAT (PID: 3536)
- SED.DAT (PID: 3420)
- GREP.DAT (PID: 2300)
- GREP.DAT (PID: 3984)
- GREP.DAT (PID: 4076)
- GREP.DAT (PID: 3200)
- GREP.DAT (PID: 2868)
- GREP.DAT (PID: 2688)
- GREP.DAT (PID: 3576)
- GREP.DAT (PID: 3388)
- GREP.DAT (PID: 3880)
- GREP.DAT (PID: 620)
- GREP.DAT (PID: 1328)
- GREP.DAT (PID: 392)
- GREP.DAT (PID: 2248)
- GREP.DAT (PID: 3284)
- GREP.DAT (PID: 3176)
- GREP.DAT (PID: 3020)
- GREP.DAT (PID: 3336)
- GREP.DAT (PID: 2608)
- GREP.DAT (PID: 3620)
- GREP.DAT (PID: 2740)
- GREP.DAT (PID: 4020)
- GREP.DAT (PID: 3528)
- GREP.DAT (PID: 1468)
- GREP.DAT (PID: 3484)
- GREP.DAT (PID: 3040)
- GREP.DAT (PID: 2780)
- GREP.DAT (PID: 3044)
- GREP.DAT (PID: 3284)
- GREP.DAT (PID: 3624)
- GREP.DAT (PID: 2276)
- GREP.DAT (PID: 2616)
- GREP.DAT (PID: 572)
- GREP.DAT (PID: 2820)
- GREP.DAT (PID: 2872)
- SORT_.DAT (PID: 2920)
- GREP.DAT (PID: 3804)
- SORT_.DAT (PID: 1564)
- GREP.DAT (PID: 3992)
- GREP.DAT (PID: 3360)
- SORT_.DAT (PID: 1692)
- GREP.DAT (PID: 2420)
- GREP.DAT (PID: 3288)
- GREP.DAT (PID: 2008)
- SORT_.DAT (PID: 4044)
- GREP.DAT (PID: 3188)
- GREP.DAT (PID: 1748)
- GREP.DAT (PID: 1860)
- GREP.DAT (PID: 3444)
- GREP.DAT (PID: 2560)
- GREP.DAT (PID: 2104)
- CUT.DAT (PID: 772)
- GREP.DAT (PID: 2244)
- GREP.DAT (PID: 1028)
- GREP.DAT (PID: 2820)
- GREP.DAT (PID: 1800)
Loads dropped or rewritten executable
- GREP.DAT (PID: 2860)
- GREP.DAT (PID: 2688)
- GREP.DAT (PID: 2876)
- GREP.DAT (PID: 2668)
- GREP.DAT (PID: 3740)
- GREP.DAT (PID: 3176)
- SORT_.DAT (PID: 2012)
- GREP.DAT (PID: 3536)
- GREP.DAT (PID: 3576)
- GREP.DAT (PID: 2300)
- GREP.DAT (PID: 4076)
- GREP.DAT (PID: 3200)
- GREP.DAT (PID: 3984)
- GREP.DAT (PID: 3032)
- GREP.DAT (PID: 2868)
- GREP.DAT (PID: 2688)
- GREP.DAT (PID: 3284)
- GREP.DAT (PID: 3388)
- GREP.DAT (PID: 620)
- GREP.DAT (PID: 392)
- GREP.DAT (PID: 1328)
- GREP.DAT (PID: 2248)
- GREP.DAT (PID: 3880)
- GREP.DAT (PID: 1468)
- GREP.DAT (PID: 3176)
- GREP.DAT (PID: 3020)
- GREP.DAT (PID: 3336)
- GREP.DAT (PID: 2608)
- GREP.DAT (PID: 2740)
- GREP.DAT (PID: 3620)
- GREP.DAT (PID: 4020)
- GREP.DAT (PID: 3528)
- GREP.DAT (PID: 2616)
- GREP.DAT (PID: 3040)
- GREP.DAT (PID: 2780)
- GREP.DAT (PID: 3044)
- GREP.DAT (PID: 3484)
- GREP.DAT (PID: 3284)
- GREP.DAT (PID: 3624)
- GREP.DAT (PID: 572)
- GREP.DAT (PID: 2872)
- GREP.DAT (PID: 2276)
- GREP.DAT (PID: 2820)
- SORT_.DAT (PID: 2920)
- GREP.DAT (PID: 3804)
- SORT_.DAT (PID: 1564)
- GREP.DAT (PID: 1860)
- GREP.DAT (PID: 3992)
- GREP.DAT (PID: 1748)
- SORT_.DAT (PID: 1692)
- GREP.DAT (PID: 2420)
- GREP.DAT (PID: 2008)
- GREP.DAT (PID: 3288)
- GREP.DAT (PID: 3360)
- GREP.DAT (PID: 3188)
- GREP.DAT (PID: 2820)
- GREP.DAT (PID: 1800)
- GREP.DAT (PID: 2104)
- GREP.DAT (PID: 3444)
- GREP.DAT (PID: 2560)
- SORT_.DAT (PID: 4044)
- GREP.DAT (PID: 2244)
- GREP.DAT (PID: 1028)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2620)
- JRT.exe (PID: 2604)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3776)
- cmd.exe (PID: 2888)
- cmd.exe (PID: 2620)
Executable content was dropped or overwritten
- JRT.exe (PID: 2604)
Reads the computer name
- reg.exe (PID: 2532)
Executed as Windows Service
- vssvc.exe (PID: 2132)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2620)
Executed via COM
- DllHost.exe (PID: 608)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2620)
Application launched itself
- cmd.exe (PID: 2620)
Starts application with an unusual extension
- cmd.exe (PID: 2620)
Removes files from Windows directory
- cmd.exe (PID: 2620)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 2132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:06:27 09:06:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 70656 |
| InitializedDataSize: | 52224 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11def |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.1.4.0 |
| ProductVersionNumber: | 8.1.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
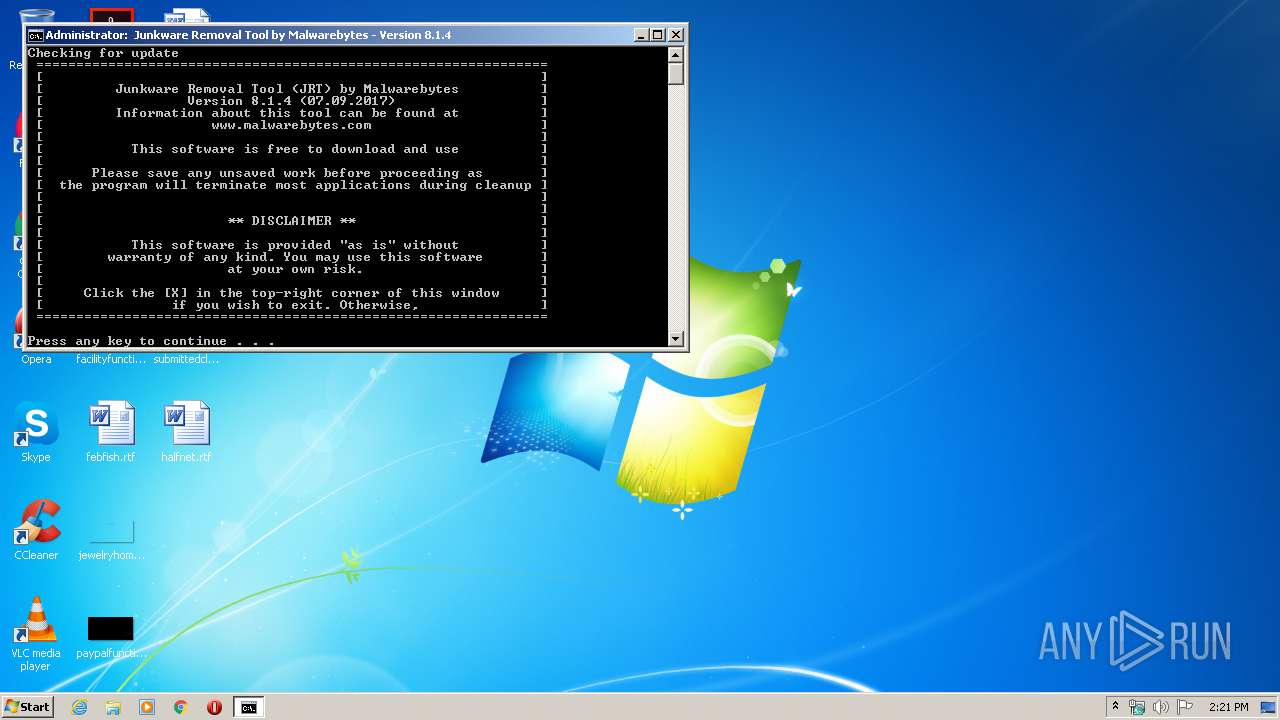
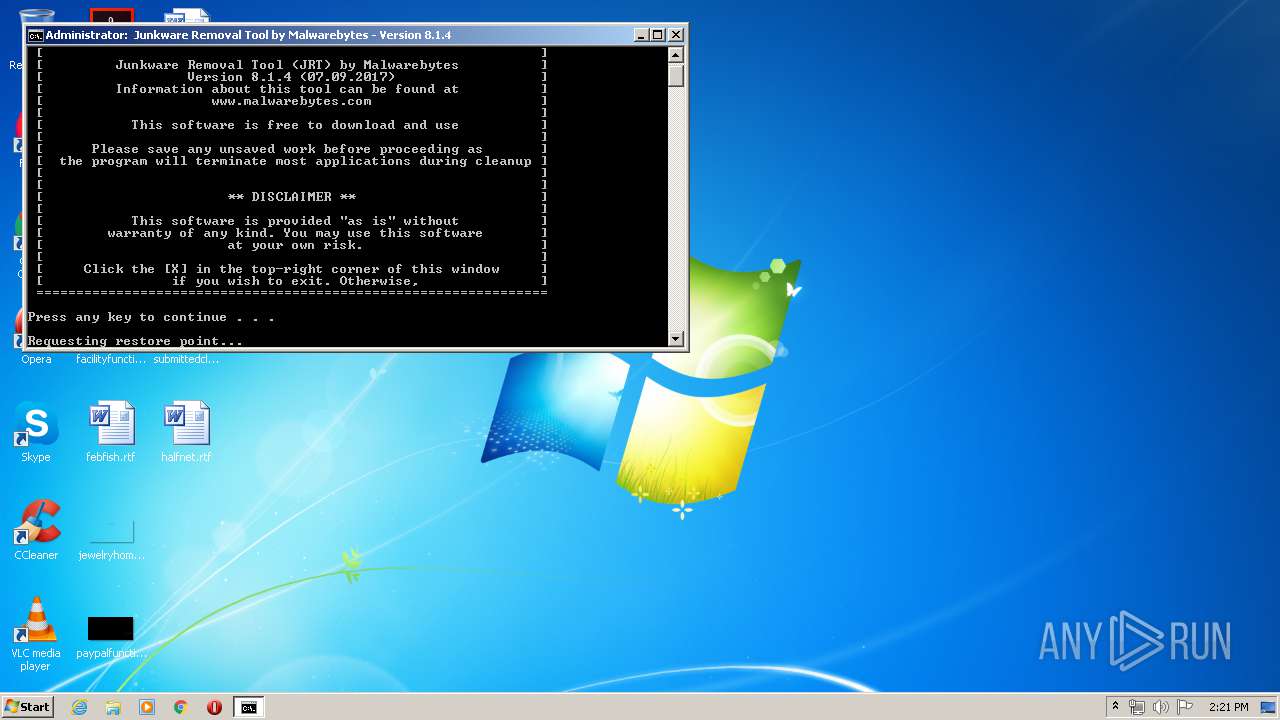
| CompanyName: | Malwarebytes |
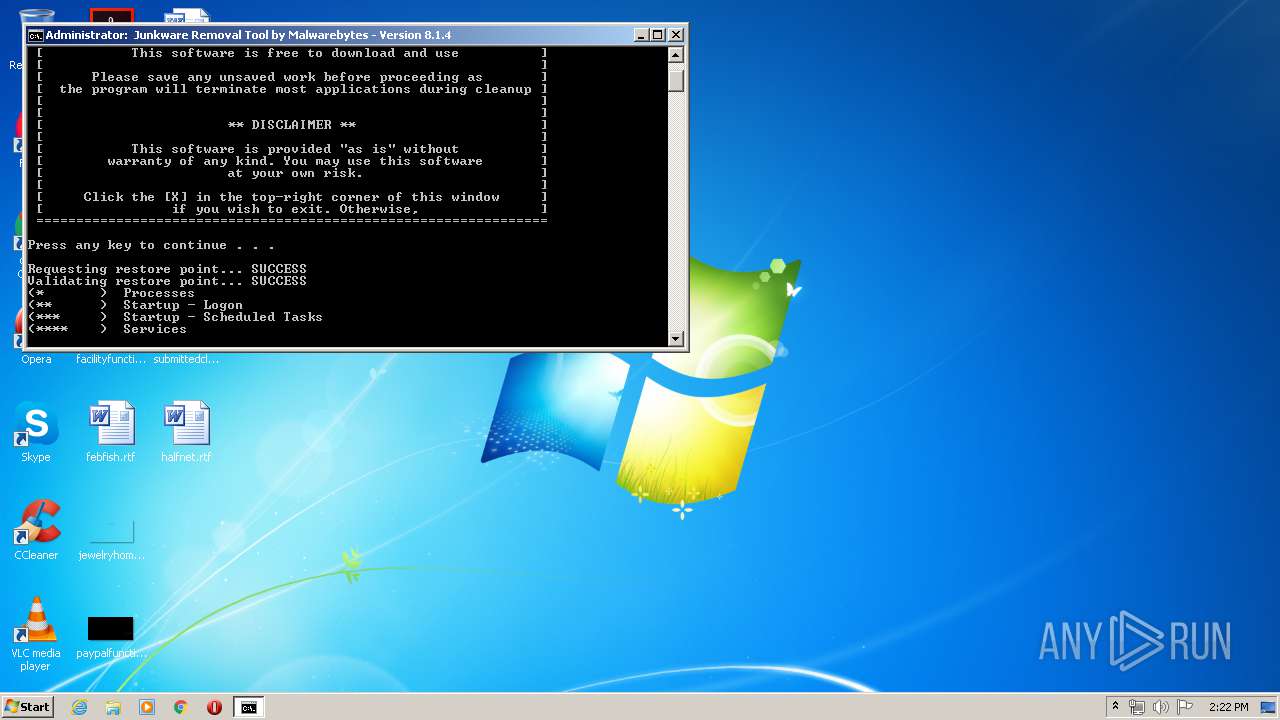
| FileDescription: | Junkware Removal Tool |
| FileVersion: | 8.1.4 |
| ProductVersion: | 8.1.4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Jun-2010 07:06:38 |
| Detected languages: |
|
| CompanyName: | Malwarebytes |
| FileDescription: | Junkware Removal Tool |
| FileVersion: | 8.1.4 |
| ProductVersion: | 8.1.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 27-Jun-2010 07:06:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00011317 | 0x00011400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57699 |
.rdata | 0x00013000 | 0x000030EA | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.54943 |
.data | 0x00017000 | 0x0000292C | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.65832 |
.rsrc | 0x0001A000 | 0x0000905B | 0x00009200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.7856 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04909 | 635 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.17891 | 744 | UNKNOWN | Russian - Russia | RT_ICON |
3 | 3.18262 | 296 | UNKNOWN | Russian - Russia | RT_ICON |
4 | 3.0817 | 3752 | UNKNOWN | Russian - Russia | RT_ICON |
5 | 2.86951 | 2216 | UNKNOWN | Russian - Russia | RT_ICON |
6 | 2.2296 | 1384 | UNKNOWN | Russian - Russia | RT_ICON |
7 | 7.92185 | 9913 | UNKNOWN | Russian - Russia | RT_ICON |
8 | 4.02945 | 9640 | UNKNOWN | Russian - Russia | RT_ICON |
9 | 3.69357 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
10 | 4.5478 | 1128 | UNKNOWN | Russian - Russia | RT_ICON |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
432
Monitored processes
389
Malicious processes
63
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | REG QUERY HKLM\Software\Microsoft\Windows\CurrentVersion\Run | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 256 | REG QUERY "HKLM\Software\Microsoft\Internet Explorer\AboutURLs" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | FC "C:\Users\admin\AppData\Local\Temp\jrt\TEMP\COMMONPROGRAMFILES_D_SUSPECT_H" "C:\Users\admin\AppData\Local\Temp\jrt\null" | C:\Windows\system32\fc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS 5 File Compare Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 348 | REG QUERY "HKLM\Software\MozillaPlugins\@marineaquarium3free_57.com/plugin" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | REG QUERY "HKLM\Software\MozillaPlugins\@couponalert_2p.com/plugin" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | REG QUERY "HKLM\Software\MozillaPlugins\@qq.com/txsso" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Users\admin\AppData\Local\Temp\jrt\GREP.DAT" -P "^[A-Z]{4,8}\.exe$|^BackUp\d{9}\.exe$|^~[a-z]{7}\.exef7f81a39-5f63-5b42-9efd-1f13b5431005quot; "C:\Users\admin\AppData\Local\Temp\jrt\TEMP\APPDATA_F_SUSPECT" | C:\Users\admin\AppData\Local\Temp\jrt\GREP.DAT | — | cmd.exe | |||||||||||
User: admin Company: GnuWin32 <http://gnuwin32.sourceforge.net> Integrity Level: HIGH Description: Grep: print lines matching a pattern Exit code: 1 Version: 2.5.4.3331 Modules
| |||||||||||||||
| 392 | REG QUERY "HKCU\Software\Google\Chrome\Extensions\abdkniaobnpabjjmlnkhgleeacekgdda" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 528 | REG QUERY "HKLM\Software\MozillaPlugins\@qq.com/qqpcmgr" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 536 | REG QUERY "HKLM\Software\Microsoft\Internet Explorer\Main" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
692
Read events
532
Write events
160
Delete events
0
Modification events
| (PID) Process: | (2604) JRT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2604) JRT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
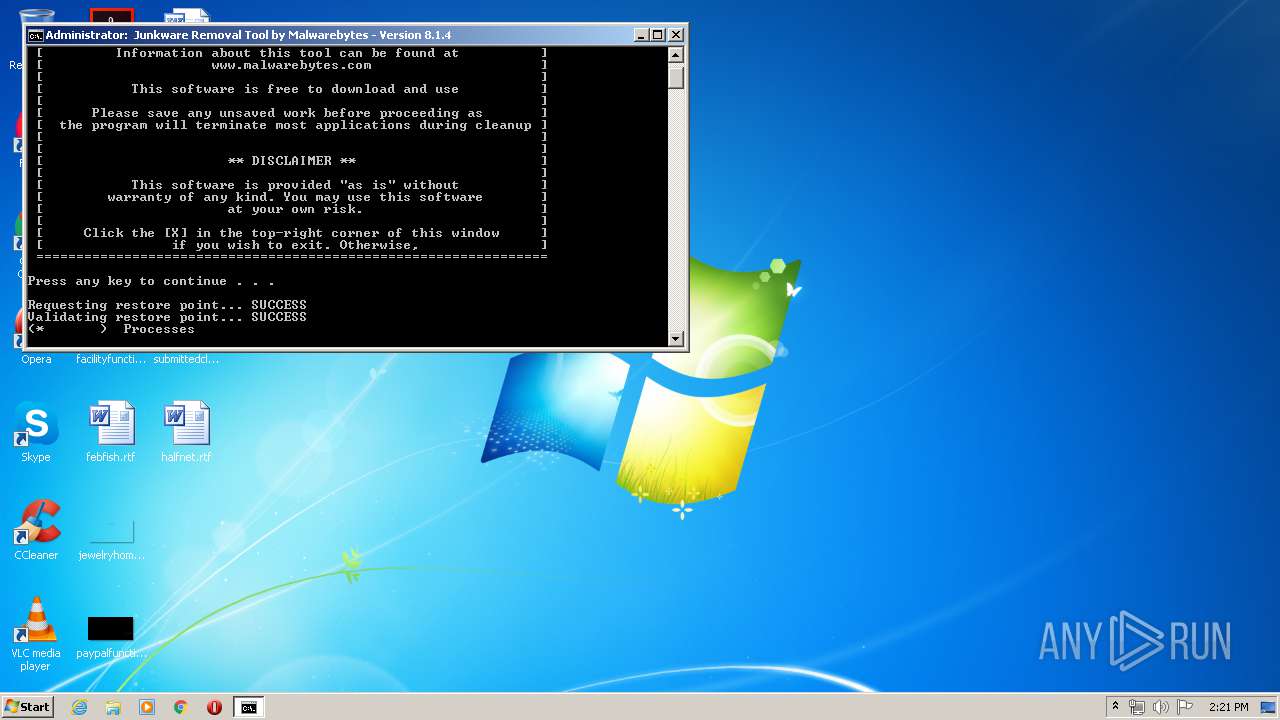
| (PID) Process: | (1916) CreateRestorePoint.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000605828191DD5D5017C0700006C0E0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1916) CreateRestorePoint.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000605828191DD5D5017C0700006C0E0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AECA7B191DD5D50154080000180C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AECA7B191DD5D50154080000200A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AECA7B191DD5D50154080000CC0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AECA7B191DD5D5015408000024080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2132) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000628F80191DD5D50154080000CC0F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1916) CreateRestorePoint.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 34 | |||
Executable files
13
Suspicious files
2
Text files
100
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2604 | JRT.exe | C:\Users\admin\AppData\Local\Temp\jrt\bl_ffxpi.cfg | text | |
MD5:385DBFC80E63F0CF3CBFCA1247F72F02 | SHA256:B12A7A3A5BF8F63E4016A56931D7EA0F575CEE0CC679913BF17BED1C23E91899 | |||
| 2604 | JRT.exe | C:\Users\admin\AppData\Local\Temp\jrt\get.bat | text | |
MD5:6142E0A5C78FA8B63993357AF48D7AB9 | SHA256:F793FA295E1598556A6B91EB73B68D825D5EDBCB0A764D9D58A570A6A4B5BF0F | |||
| 2604 | JRT.exe | C:\Users\admin\AppData\Local\Temp\jrt\nfo\sed.txt | text | |
MD5:13171419A6D180FDD8B52CEAE16DDADF | SHA256:C8A8A4818146DD8960849C2B028E565A94C8D4E036E01E1E28E0FA91D42C7E43 | |||
| 2604 | JRT.exe | C:\Users\admin\AppData\Local\Temp\jrt\nfo\shortcut.txt | text | |
MD5:3A26827485C683AACD1E0194F34A0CFA | SHA256:094E2FA2C6DF5FEE039BA345067BA5B2C22E8C54CA4A8D7B35E86A91C1E8E320 | |||
| 2604 | JRT.exe | C:\Users\admin\AppData\Local\Temp\jrt\jrtcurrentmd5 | text | |
MD5:36D3663C87C5B5E7A1093AFD56824A43 | SHA256:FB5A9A5C71A54D055C3A66FD0D1B404A04A6C5AD5E36CA571C7EC88C16701057 | |||
| 2604 | JRT.exe | C:\Users\admin\AppData\Local\Temp\jrt\nfo\wget.txt | text | |
MD5:A541C96318F0FE10D90415E7B6A57080 | SHA256:1ACBF2A4A53DB8597CC3774B6D312F207AC2011FD4CEEECA9523452D016A9315 | |||
| 2604 | JRT.exe | C:\Users\admin\AppData\Local\Temp\jrt\bl_appinit.cfg | text | |
MD5:CC6A968CCDA289BE7B69E039646D0BC9 | SHA256:95691814D105108152B96E41D0F0FF30462D0A060AF32431089C312604C235B6 | |||
| 2604 | JRT.exe | C:\Users\admin\AppData\Local\Temp\jrt\bl_chrstrg.cfg | text | |
MD5:EBDFDE9F11720DFC627933F37E8AE319 | SHA256:613DEC5AE47C9FCC4EFF4E50FE811FD41A9442796A57DBB0E63FBE36178C0663 | |||
| 2604 | JRT.exe | C:\Users\admin\AppData\Local\Temp\jrt\bl_ffext.cfg | text | |
MD5:3E03ED48DAA500AC767092B38B8A5E28 | SHA256:47241BF6935755524E8FC3C781718630278C2AD1F1BA81790A35B5D4CBEA8DAB | |||
| 2604 | JRT.exe | C:\Users\admin\AppData\Local\Temp\jrt\bl_ffxml.cfg | text | |
MD5:CDEF3ABCAE8AD1B6B6CAAFC7BA8C5D73 | SHA256:DE626B2E02DB7539121A83BA38F760A875F124D9C3DD05CCC7BBC589F298B00A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3728 | WGET.DAT | GET | 200 | 72.247.224.184:80 | http://data-cdn.mbamupdates.com/v1/tools/jrt/jrtnewmd5 | US | text | 13 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3728 | WGET.DAT | 72.247.224.184:80 | data-cdn.mbamupdates.com | Akamai Technologies, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
data-cdn.mbamupdates.com |
| whitelisted |
Threats
Process | Message |
|---|---|
GREP.DAT | Invalid parameter passed to C runtime function.
|
GREP.DAT | Invalid parameter passed to C runtime function.
|
GREP.DAT | Invalid parameter passed to C runtime function.
|
GREP.DAT | Invalid parameter passed to C runtime function.
|
GREP.DAT | Invalid parameter passed to C runtime function.
|
GREP.DAT | Invalid parameter passed to C runtime function.
|
GREP.DAT | Invalid parameter passed to C runtime function.
|
GREP.DAT | Invalid parameter passed to C runtime function.
|
GREP.DAT | Invalid parameter passed to C runtime function.
|
GREP.DAT | Invalid parameter passed to C runtime function.
|