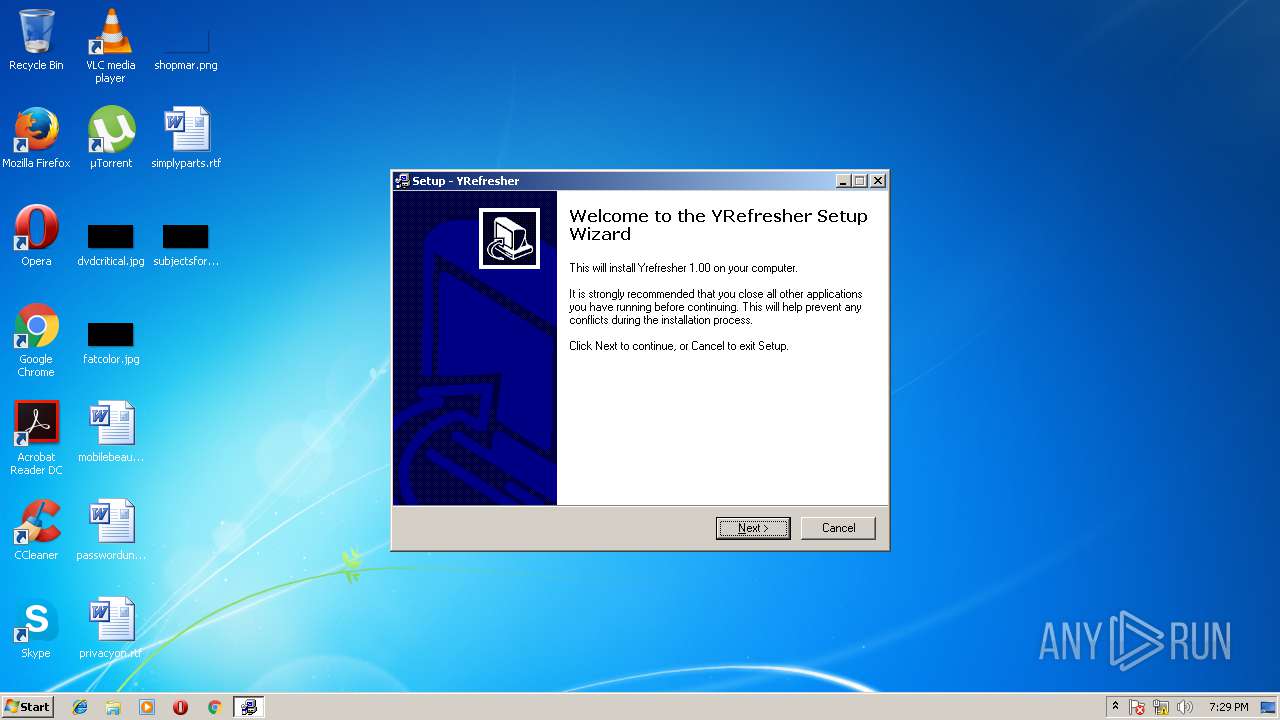
| File name: | yrsetup.exe |
| Full analysis: | https://app.any.run/tasks/b5dda70e-c6a8-4164-a773-f9292b21db54 |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2018, 19:28:57 |
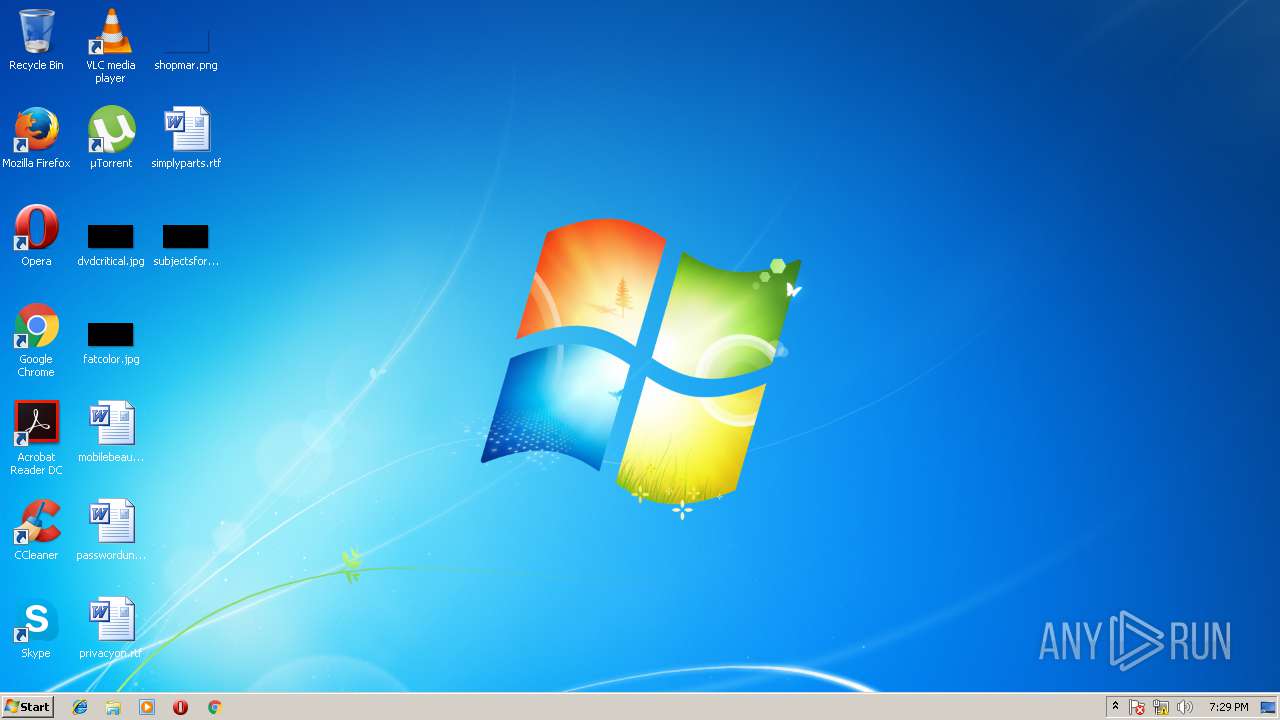
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InnoSetup self-extracting archive |
| MD5: | 9116B0834EDEDC2AC1E2A87CD1A0388C |
| SHA1: | FFBDC01C7FD0A3323BEB30051FCA84603C979987 |
| SHA256: | 200037707AEDA8DF446ED00A6F803948C2DEB306252DC464B81BA79086D174AE |
| SSDEEP: | 6144:k5zEGsNwNamuG4zke7nrthMQCQjaLbW/wC0VEelB7F+msUyNOvKMLA5DRJzifP3r:aD+kqnBhMQt2LCDelxFdsUyUZLmtJz2b |
MALICIOUS
Application loaded dropped or rewritten executable
- INSE55C.tmp (PID: 3168)
Application was dropped or rewritten from another process
- INSE55C.tmp (PID: 3168)
SUSPICIOUS
Starts application with an unusual extension
- yrsetup.exe (PID: 3212)
Creates files in the program directory
- INSE55C.tmp (PID: 3168)
Creates COM task schedule object
- INSE55C.tmp (PID: 3168)
Creates a software uninstall entry
- INSE55C.tmp (PID: 3168)
INFO
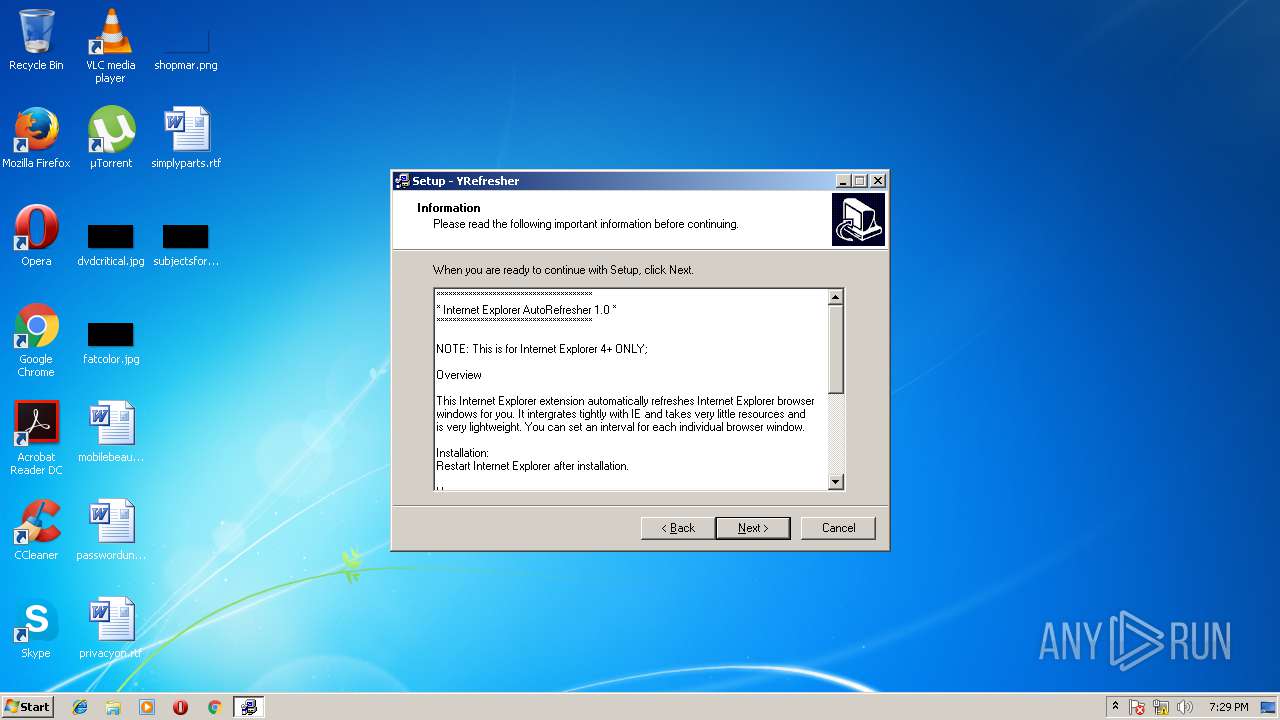
Dropped object may contain URL's
- yrsetup.exe (PID: 3212)
- INSE55C.tmp (PID: 3168)
Loads rich edit control libraries
- INSE55C.tmp (PID: 3168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (82.8) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.7) |
| .exe | | | Win32 Executable (generic) (3.4) |
| .exe | | | Generic Win/DOS Executable (1.5) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 46592 |
| InitializedDataSize: | 15872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbf34 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000B58C | 0x0000B600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49819 |
DATA | 0x0000D000 | 0x000017DC | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.26067 |
BSS | 0x0000F000 | 0x0000116C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000762 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.55225 |
.tls | 0x00012000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00013000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.210826 |
.reloc | 0x00014000 | 0x00000840 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00015000 | 0x00001200 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.65234 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.49889 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 3.17623 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
MAINICON | 2.42968 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
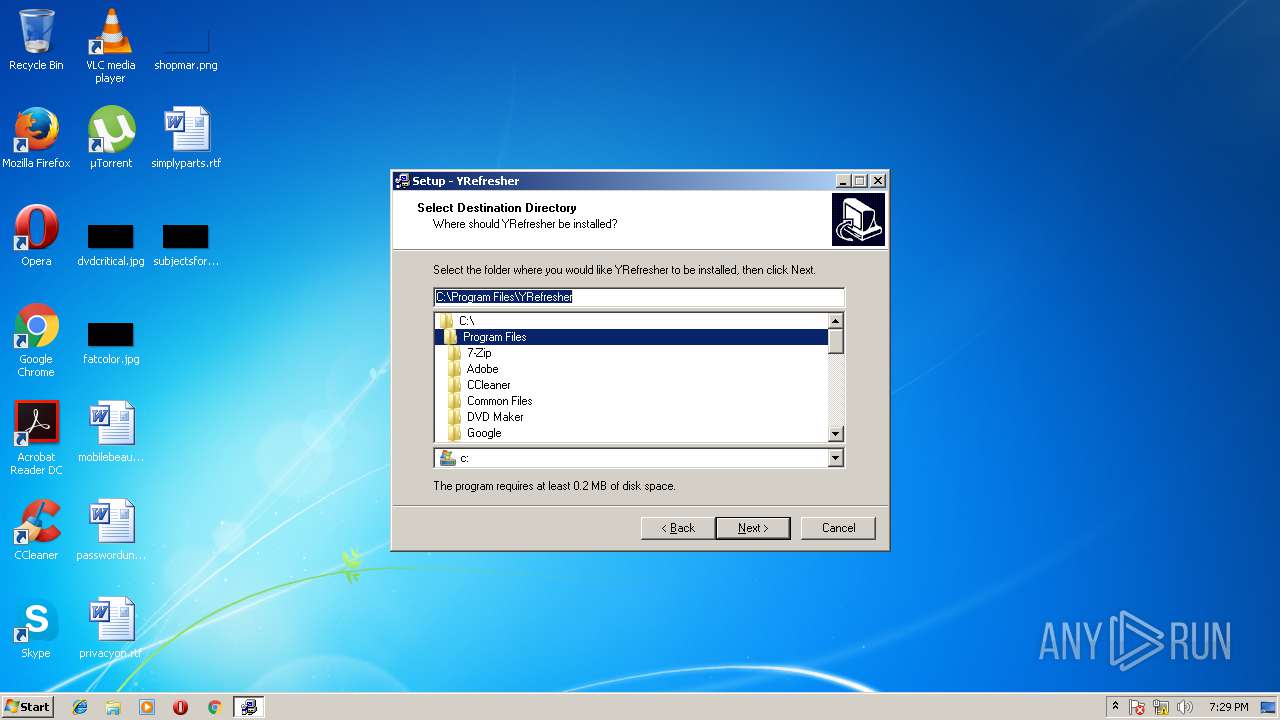
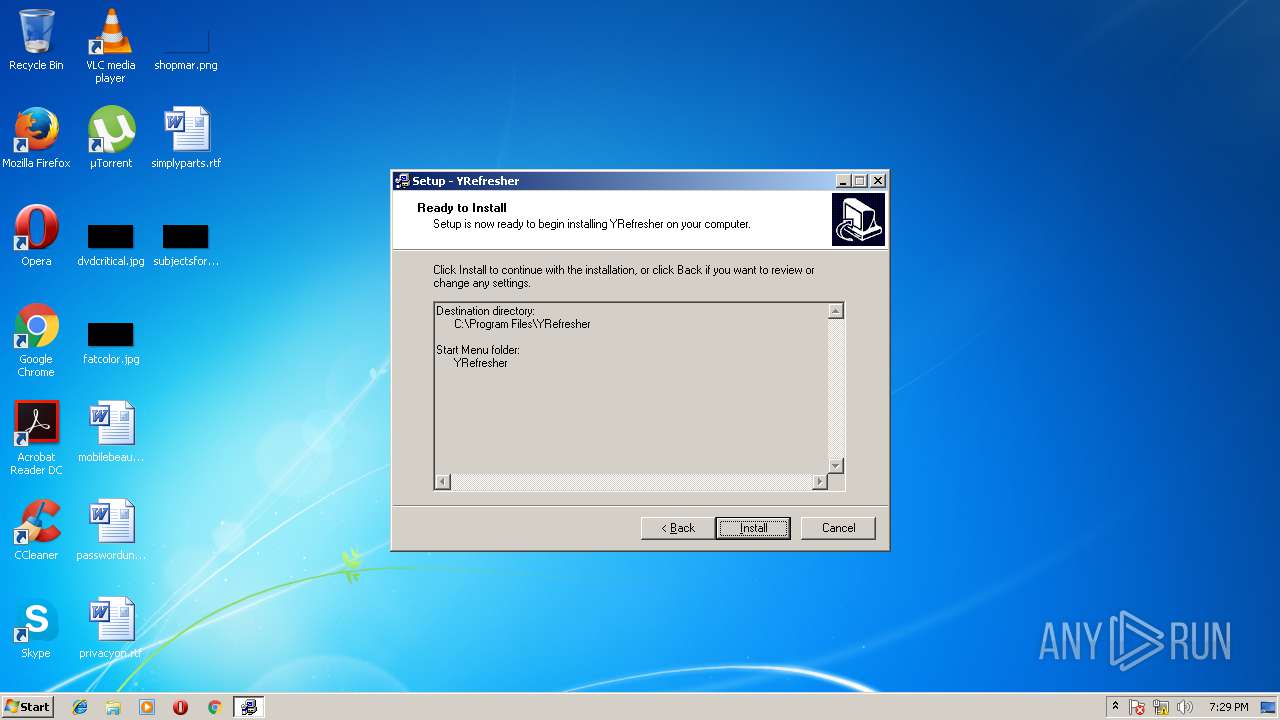
| 3064 | "C:\Users\admin\AppData\Local\Temp\yrsetup.exe" | C:\Users\admin\AppData\Local\Temp\yrsetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
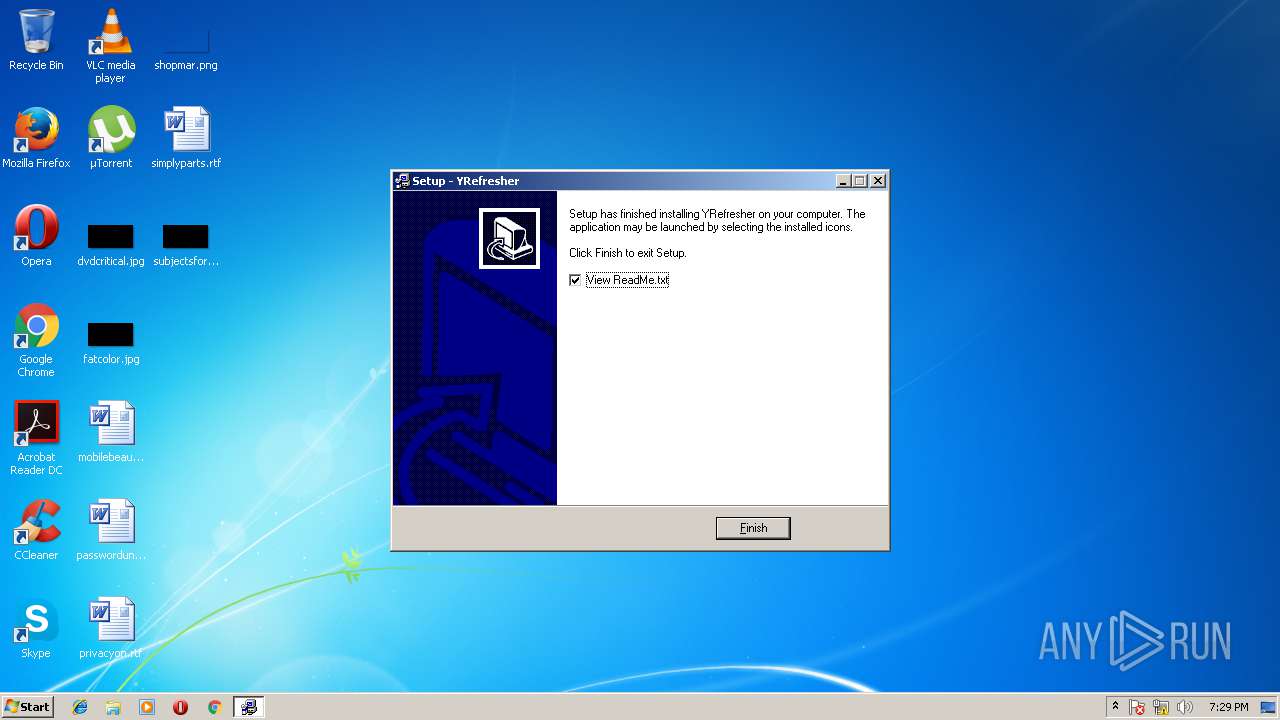
| 3168 | C:\Users\admin\AppData\Local\Temp\INSE55C.tmp /SL3 $80178 C:\Users\admin\AppData\Local\Temp\yrsetup.exe 309748 313084 60928 | C:\Users\admin\AppData\Local\Temp\INSE55C.tmp | yrsetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3212 | "C:\Users\admin\AppData\Local\Temp\yrsetup.exe" | C:\Users\admin\AppData\Local\Temp\yrsetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
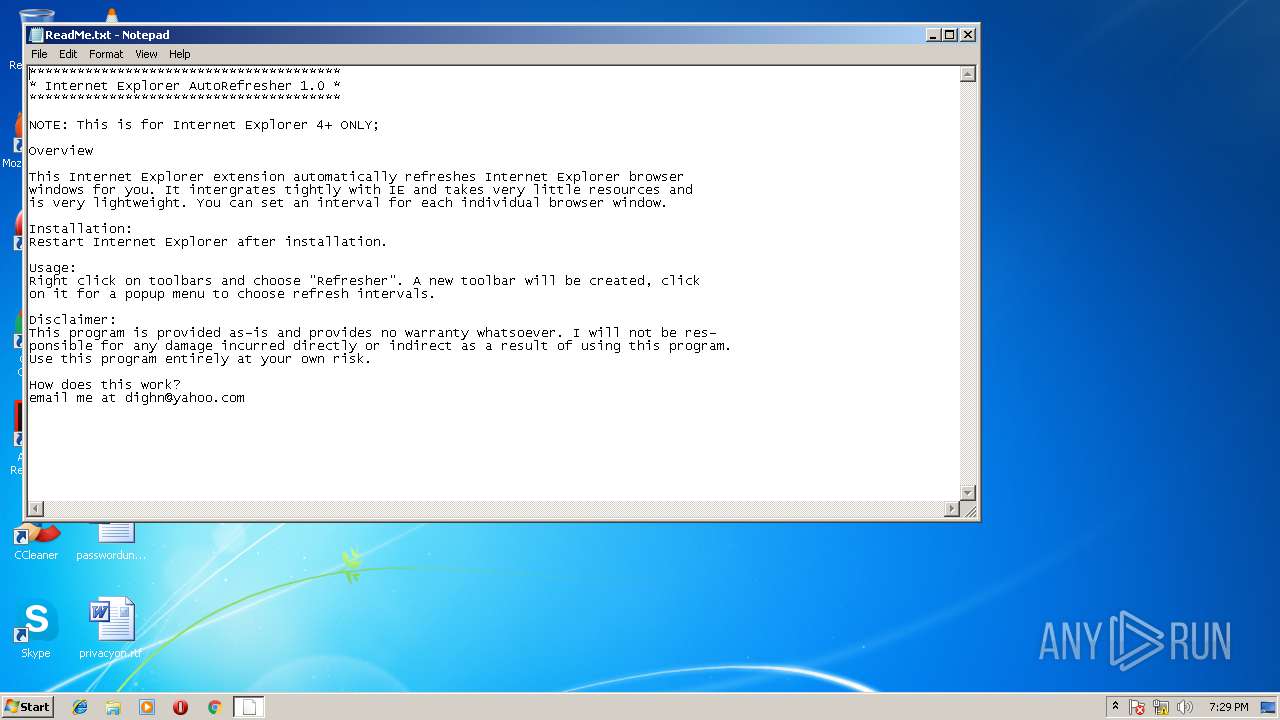
| 3852 | "C:\Windows\system32\NOTEPAD.EXE" C:\Program Files\YRefresher\ReadMe.txt | C:\Windows\system32\NOTEPAD.EXE | — | INSE55C.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
242
Read events
211
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3168) INSE55C.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\YRefresher.RefresherBand.1 |
| Operation: | write | Name: | |
Value: RefresherBand Class | |||
| (PID) Process: | (3168) INSE55C.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\YRefresher.RefresherBand.1\CLSID |
| Operation: | write | Name: | |
Value: {B24BA06E-FB7B-4757-95C2-DC01125F750E} | |||
| (PID) Process: | (3168) INSE55C.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\YRefresher.RefresherBand |
| Operation: | write | Name: | |
Value: RefresherBand Class | |||
| (PID) Process: | (3168) INSE55C.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\YRefresher.RefresherBand\CLSID |
| Operation: | write | Name: | |
Value: {B24BA06E-FB7B-4757-95C2-DC01125F750E} | |||
| (PID) Process: | (3168) INSE55C.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\YRefresher.RefresherBand\CurVer |
| Operation: | write | Name: | |
Value: YRefresher.RefresherBand.1 | |||
| (PID) Process: | (3168) INSE55C.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B24BA06E-FB7B-4757-95C2-DC01125F750E} |
| Operation: | write | Name: | |
Value: RefresherBand Class | |||
| (PID) Process: | (3168) INSE55C.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B24BA06E-FB7B-4757-95C2-DC01125F750E}\ProgID |
| Operation: | write | Name: | |
Value: YRefresher.RefresherBand.1 | |||
| (PID) Process: | (3168) INSE55C.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B24BA06E-FB7B-4757-95C2-DC01125F750E}\VersionIndependentProgID |
| Operation: | write | Name: | |
Value: YRefresher.RefresherBand | |||
| (PID) Process: | (3168) INSE55C.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B24BA06E-FB7B-4757-95C2-DC01125F750E}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\PROGRA~1\YREFRE~1\YREFRE~1.DLL | |||
| (PID) Process: | (3168) INSE55C.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B24BA06E-FB7B-4757-95C2-DC01125F750E}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
Executable files
5
Suspicious files
0
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | INSE55C.tmp | C:\Program Files\YRefresher\is-OUDKN.tmp | — | |
MD5:— | SHA256:— | |||
| 3168 | INSE55C.tmp | C:\Program Files\YRefresher\is-HC8H9.tmp | — | |
MD5:— | SHA256:— | |||
| 3168 | INSE55C.tmp | C:\Program Files\YRefresher\is-93SFC.tmp | — | |
MD5:— | SHA256:— | |||
| 3168 | INSE55C.tmp | C:\Program Files\YRefresher\ReadMe.txt | text | |
MD5:9C3E5A5DDDAE46A904249DBD146E95A5 | SHA256:30FEFCC7FEF4A205F873A602A0A31831D373D6F3802E602BA010CEB770D6850C | |||
| 3168 | INSE55C.tmp | C:\Program Files\YRefresher\unins000.exe | executable | |
MD5:C8CAD5D1805154D95D885E08C0DBA003 | SHA256:75069BA8FC6CDCD227BDCCB78ADE483CF8A2083C7CE401879875D95A3B128197 | |||
| 3168 | INSE55C.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\YRefresher\Readme.lnk | lnk | |
MD5:C5C5A9593AEE45B2E0B0D315B4B74BB4 | SHA256:E6DB0E5EB4008F1EBC3AF04C236BBAD1BD55181B53CB1DF153CBEF918EF02A11 | |||
| 3168 | INSE55C.tmp | C:\Program Files\YRefresher\unins000.dat | dat | |
MD5:0CDFAB1C17EDDE7E4C3AD4FA04823742 | SHA256:7F6B3E43B8997389A96C111748937B8E33C599261547AB436A28D4D6809473BB | |||
| 3168 | INSE55C.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\YRefresher\Uninstall YRefresher.lnk | lnk | |
MD5:3071EAB0E968123B056E74305292D317 | SHA256:DE5667B2D55D76B27F98B27FA4D863C23CEC1CE369ECEA272E43B0AC954F0C91 | |||
| 3168 | INSE55C.tmp | C:\Program Files\YRefresher\YRefresher.dll | executable | |
MD5:1FF389632D4AAD75A2AC6FE5AFCFFA94 | SHA256:981B3F657D7255B061EA1A2D64F010C5AA45EAE713B4BBF672CC2EAE2B471157 | |||
| 3212 | yrsetup.exe | C:\Users\admin\AppData\Local\Temp\INSE55C.tmp | executable | |
MD5:90C5909E6353FEA710D756E5C0D9F3AC | SHA256:279481D7CDC64AABC967ABE5F424CEEE6317B3AA48F0D3C785221BDAA2CBD2C5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report