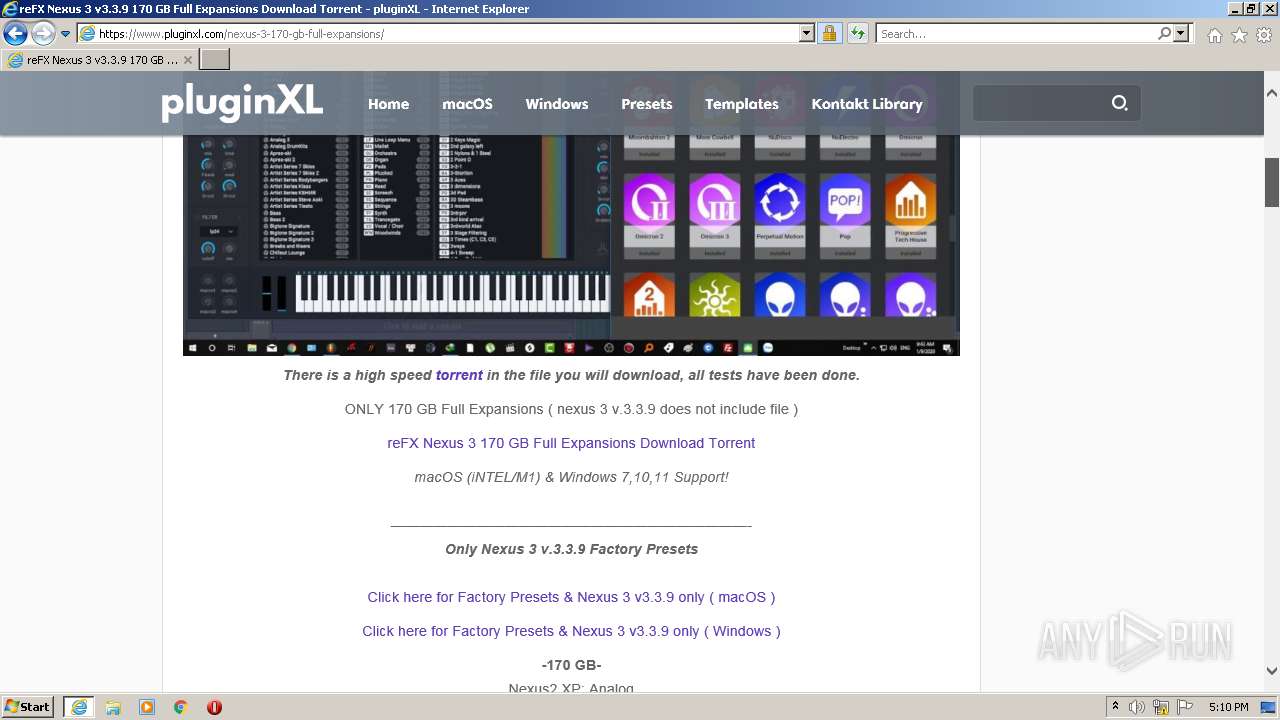
| URL: | https://www.pluginxl.com/refx-nexus-3/ |
| Full analysis: | https://app.any.run/tasks/c7712a37-a911-42a4-9a75-2e85fddf3d83 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2022, 17:09:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F2EC753588C7438CA2F8468C2029C488 |
| SHA1: | 977B580E660693AE687F34B00F8C171EA9F19386 |
| SHA256: | 1FFE1A715151CA9D5C41375EC972F4BAD56330AB0991B6C840BA0D55674C46D3 |
| SSDEEP: | 3:N8DSLjMLGAASWrK:2OLjUPF |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2200)
- iexplore.exe (PID: 3220)
INFO
Checks supported languages
- iexplore.exe (PID: 3220)
- iexplore.exe (PID: 2200)
Reads the computer name
- iexplore.exe (PID: 3220)
- iexplore.exe (PID: 2200)
Application launched itself
- iexplore.exe (PID: 3220)
Changes internet zones settings
- iexplore.exe (PID: 3220)
Reads settings of System Certificates
- iexplore.exe (PID: 2200)
- iexplore.exe (PID: 3220)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2200)
Reads internet explorer settings
- iexplore.exe (PID: 2200)
Checks Windows Trust Settings
- iexplore.exe (PID: 3220)
- iexplore.exe (PID: 2200)
Creates files in the user directory
- iexplore.exe (PID: 2200)
- iexplore.exe (PID: 3220)
Changes settings of System certificates
- iexplore.exe (PID: 3220)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2200 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3220 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.pluginxl.com/refx-nexus-3/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
24 267
Read events
23 801
Write events
462
Delete events
4
Modification events
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30942643 | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30942643 | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
54
Text files
246
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2200 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:F99742A644F9461898B49CA13E928EEE | SHA256:6344ACA957138E23DE7897416A2481C4BB7DAE706C460972EFAECEC623A3641D | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:D08BA6C03724AB25AF11AAF5D37B2262 | SHA256:7C80216CD30A1488C84EA5A8E90929754E7AD9DDDB3E329AD91F1FDE16F9EC50 | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style[1].css | text | |
MD5:F1D3A41FCB587AD1C122BAE5E1F6FD66 | SHA256:AF0B1F09C15A0AE4A3669EAB086E781817386359108F27EE8DD0714C80799838 | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:4E3AD3A2E14579FDB80EDD1DD7E3747D | SHA256:684A22AC5BD3C43A2290F6CD910C9AEB7A57CA7FA9F9418022E977BD91FE94C4 | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\refx-nexus-3[1].htm | html | |
MD5:416B79037EA6FCDEE8E0057E85E6F808 | SHA256:85DA583728A864F632A018051860C719863E4D31055518AC14FEDD2448307495 | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\front_end_style[1].css | text | |
MD5:E7B66C6BA6683D2C7EB6F8549E99A95D | SHA256:5B44AF283D341DA30C6C04D222D6470EA87C3FF9178E6BB10AE651241EFB1F5A | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:9E1D1F90DA322999D6D0C29C7E035342 | SHA256:794A922B3140709DFA8751E568862EE77CA02B2E8E3CC202FA6F51C0C49C9D16 | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\renk5[1].css | text | |
MD5:B2EFF8BBBC48B4484FCDA557944F698D | SHA256:8C2B2739F810E0F93216C0CF4B814ECC5C288C452DC391836C7E8882B51FE6D3 | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:A648D8A78DDA7D3EE0E03D1371D8C12D | SHA256:BA852B716CFF6AEEC0FD3444B1454657314244862D2BA86C1426E36CA1938E3A | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\jquery.fancybox[1].css | text | |
MD5:1A526DC03D5CB066FDC2089A31CAE966 | SHA256:0FC7148B2B5162DDF84D60C2E9D3032FBF4603D536FD2DB348354F5DEECFC461 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
183
DNS requests
69
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2200 | iexplore.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c7e1f7930a058e5f | US | compressed | 4.70 Kb | whitelisted |
2200 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2200 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2200 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2200 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2200 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEJSUTLL3p2xCgAAAAEz%2BUQ%3D | US | der | 471 b | whitelisted |
2200 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEC5GLYwFefbxEgAAAAAAYIc%3D | US | der | 471 b | whitelisted |
2200 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCYyccBU%2BO5JwoAAAABM%2FlK | US | der | 472 b | whitelisted |
2200 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA9bw6F2y3ieICDHiTyBZ7Q%3D | US | der | 1.47 Kb | whitelisted |
3220 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.67.187.73:443 | www.pluginxl.com | — | US | suspicious |
2200 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3220 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3220 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2200 | iexplore.exe | 104.21.80.220:443 | www.pluginxl.com | Cloudflare Inc | US | unknown |
2200 | iexplore.exe | 104.212.67.234:443 | www.clarity.ms | Microsoft Corporation | US | unknown |
2200 | iexplore.exe | 77.88.21.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
2200 | iexplore.exe | 142.250.181.226:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2200 | iexplore.exe | 104.126.37.35:80 | subca.ocsp-certum.com | GTT Communications Inc. | US | suspicious |
2200 | iexplore.exe | 172.67.187.73:443 | www.pluginxl.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.pluginxl.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
ajax.aspnetcdn.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2200 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |