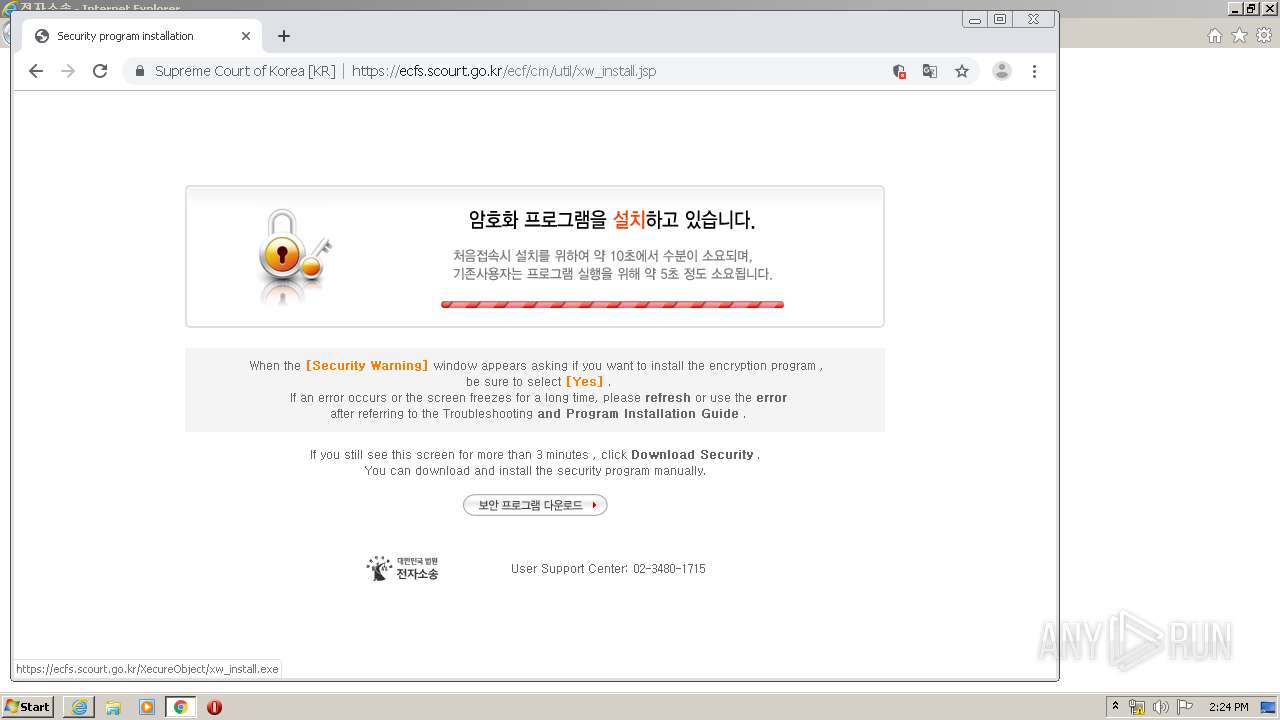
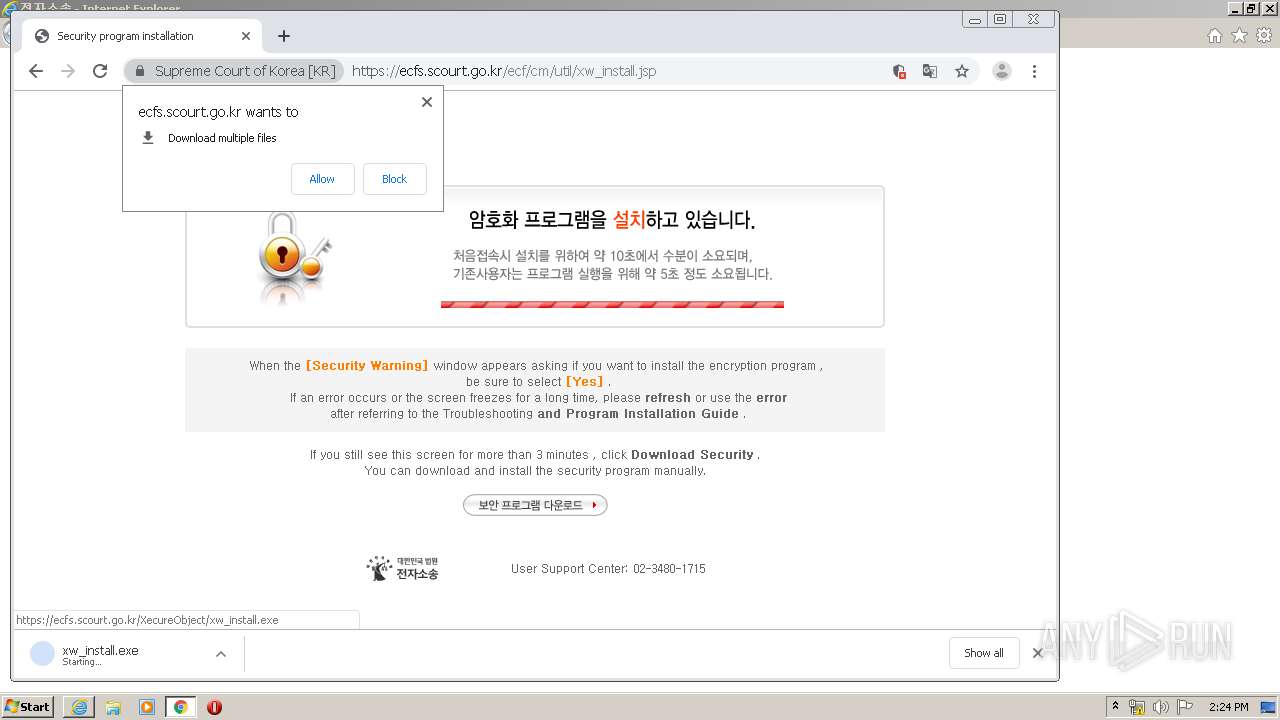
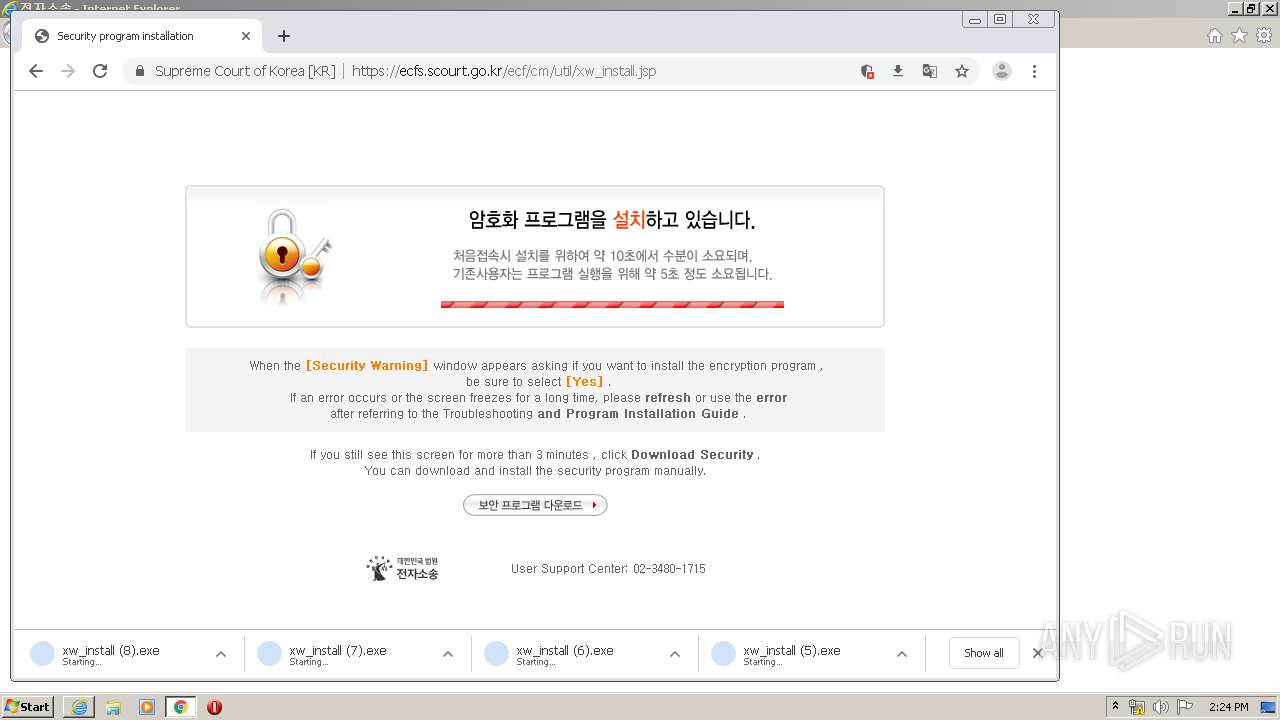
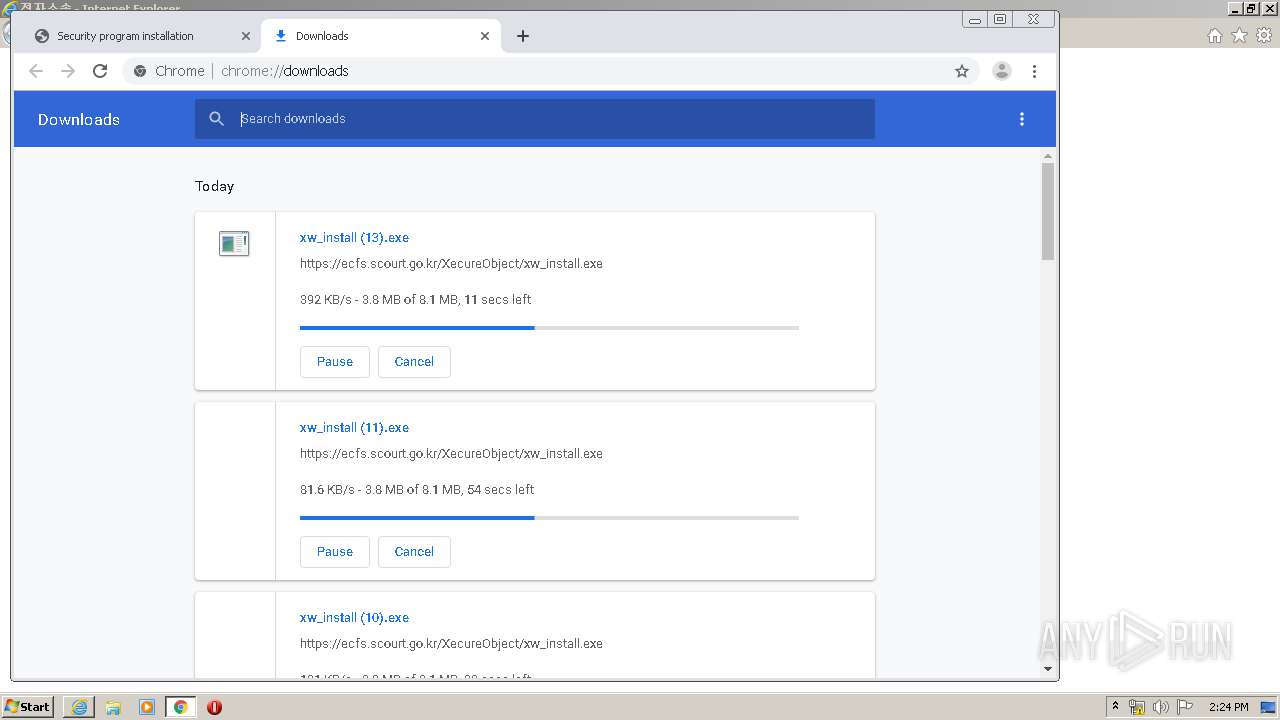
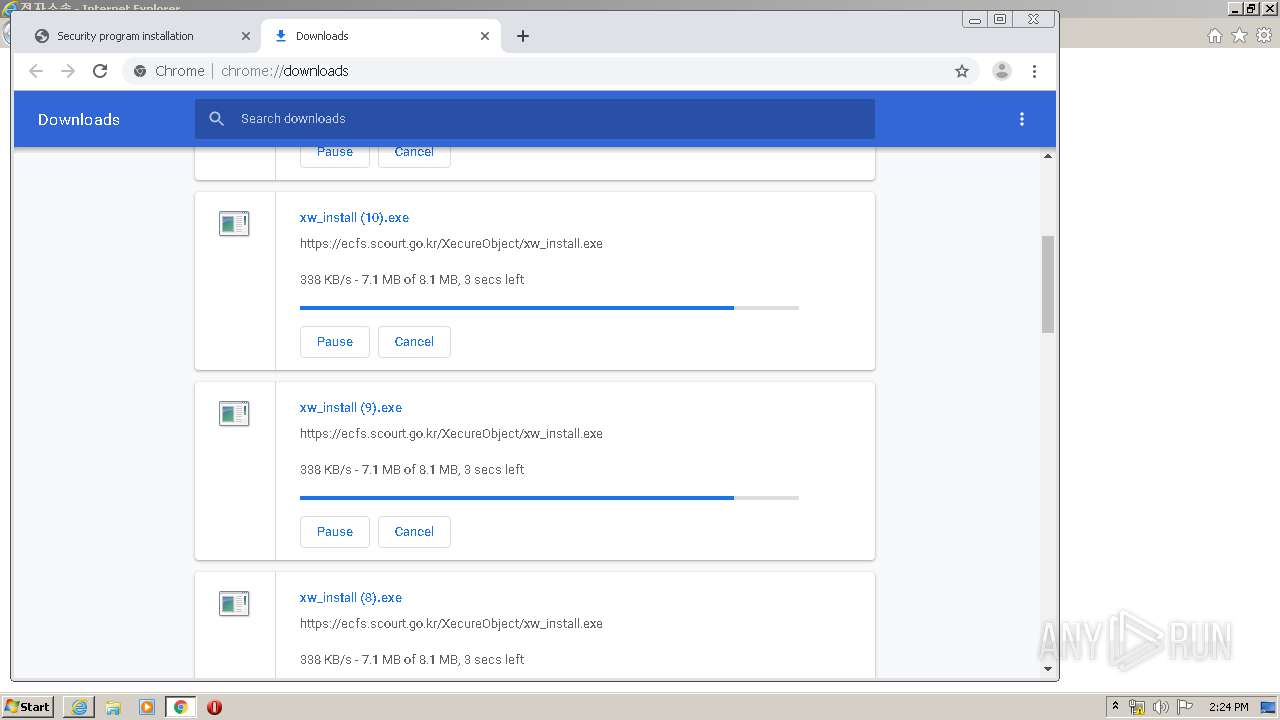
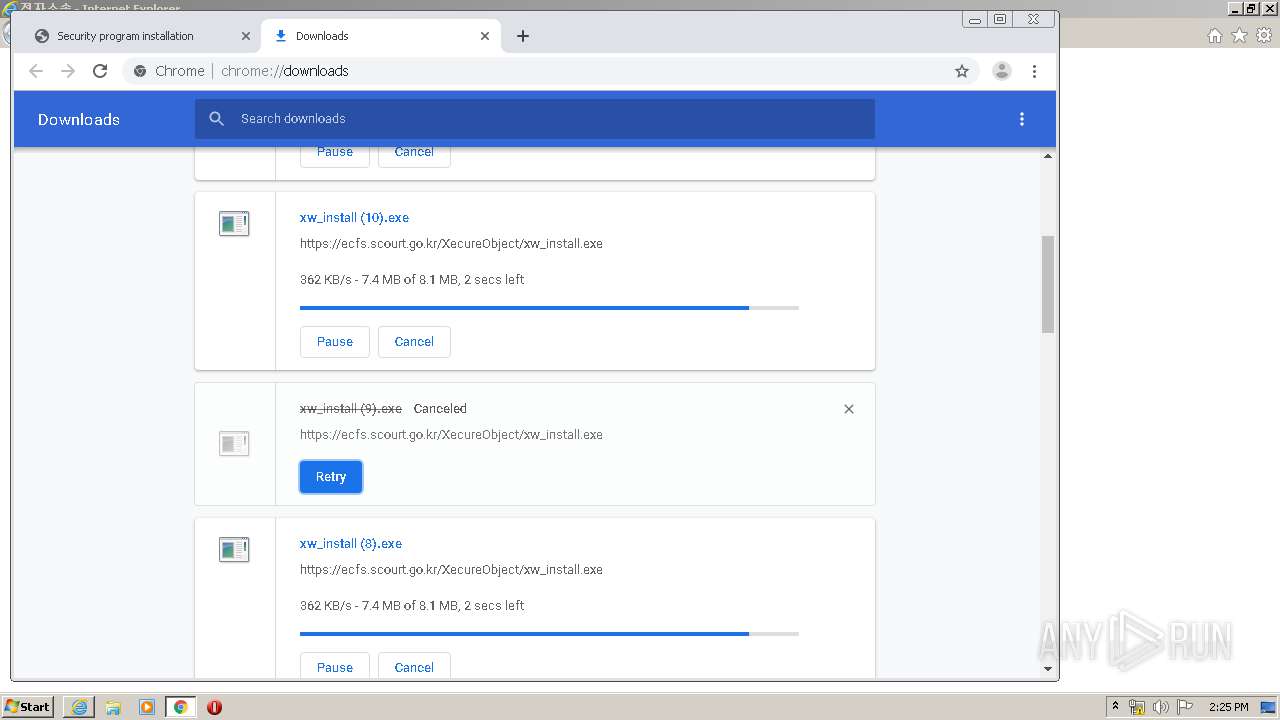
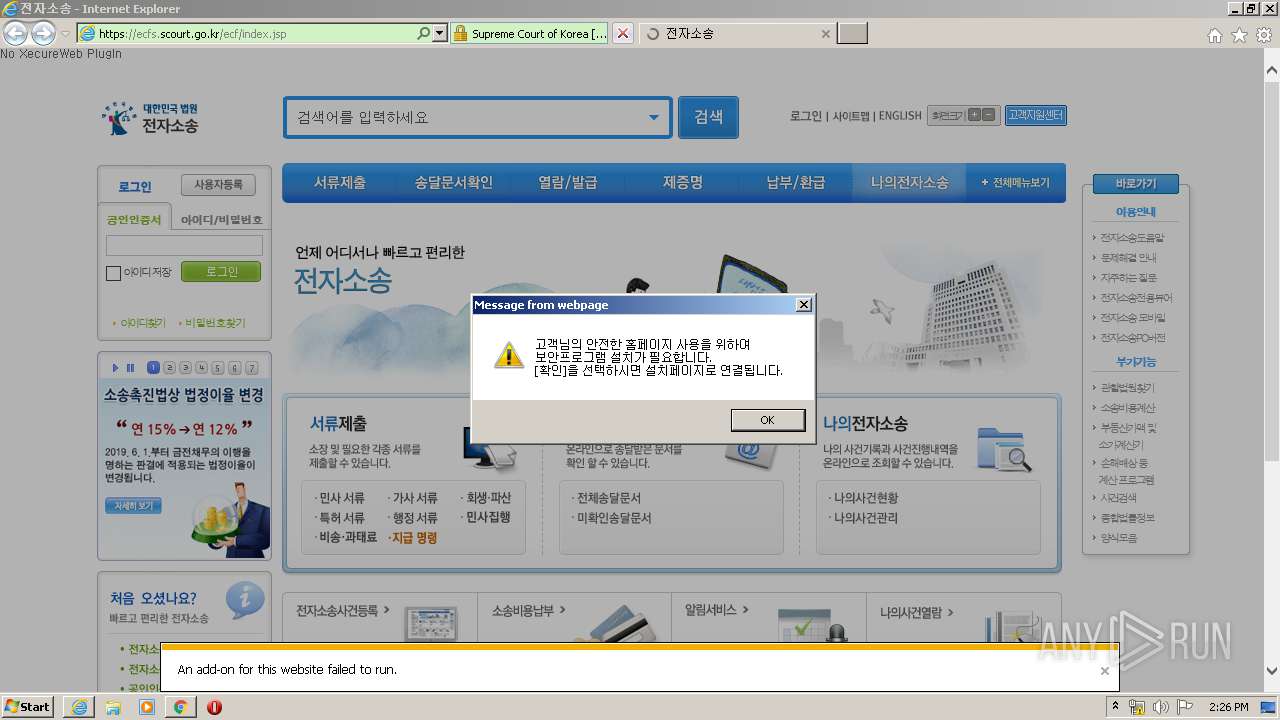
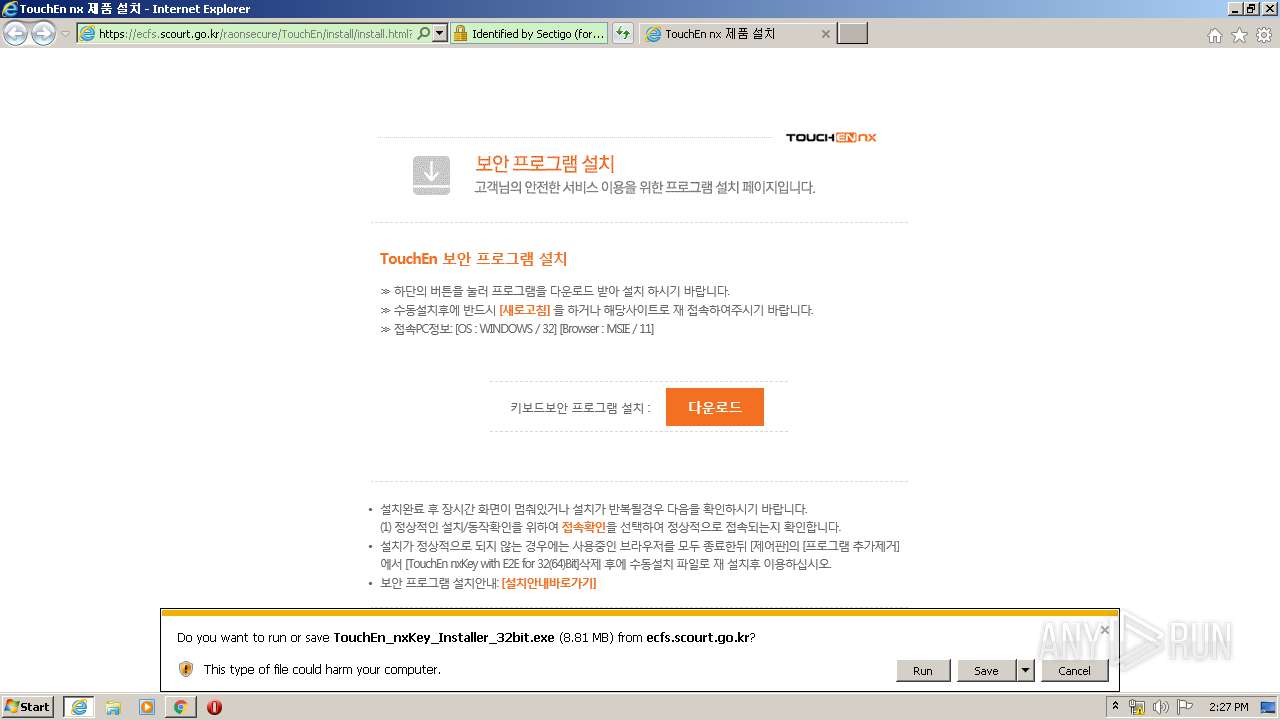
| URL: | http://ecfs.scourt.go.kr |
| Full analysis: | https://app.any.run/tasks/b37a8e24-f183-4ef2-a742-9c4da834ce23 |
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2020, 14:23:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 517B614A30A4E51DA59B158FAD84E110 |
| SHA1: | 02B670C2763D70841ED904C795B9040D4AD6CC21 |
| SHA256: | 1FF920E512BF950312ECC6B942A5F9D6A6B2CFCF6CAF32F9E2ACD00A234E6226 |
| SSDEEP: | 3:N1KbUXGczn:CC |
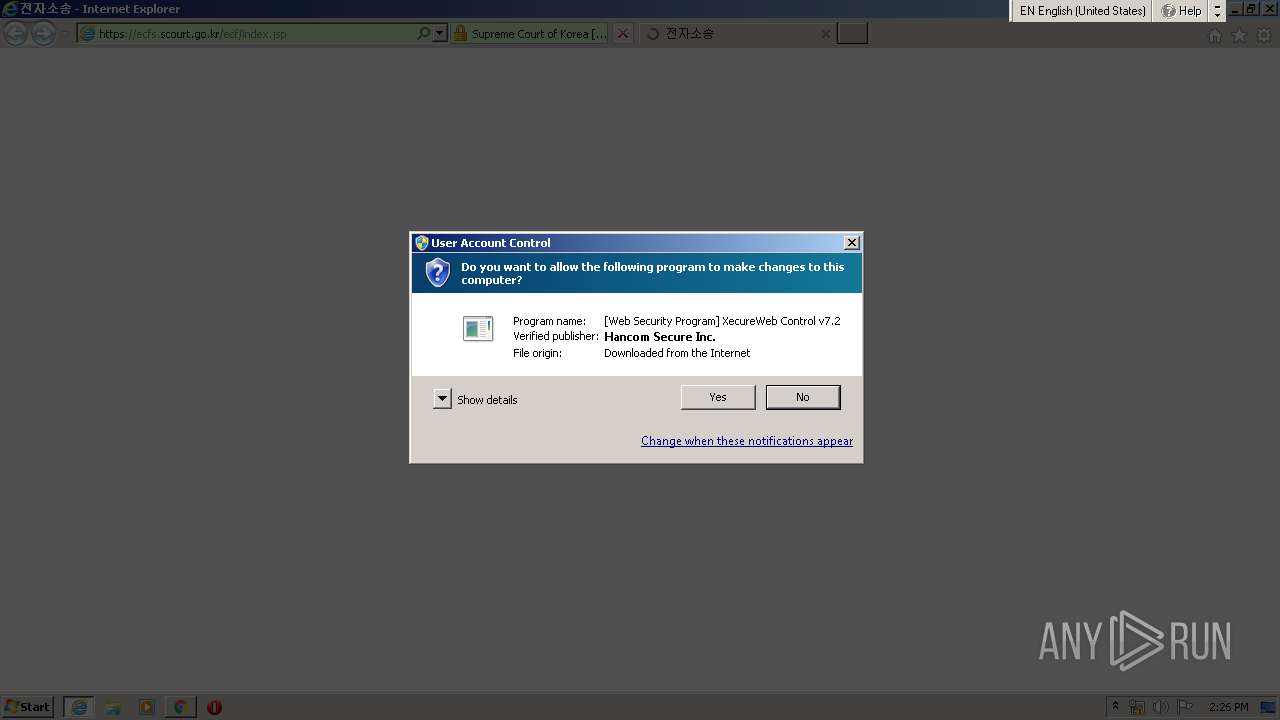
MALICIOUS
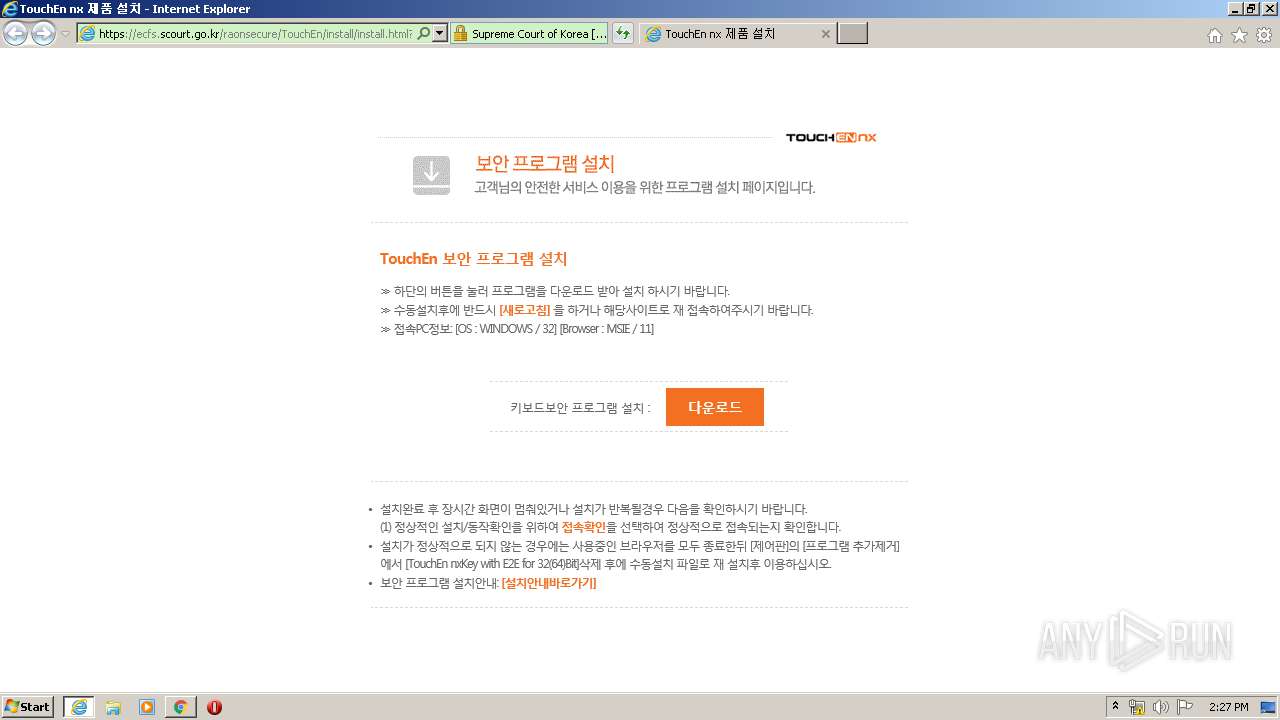
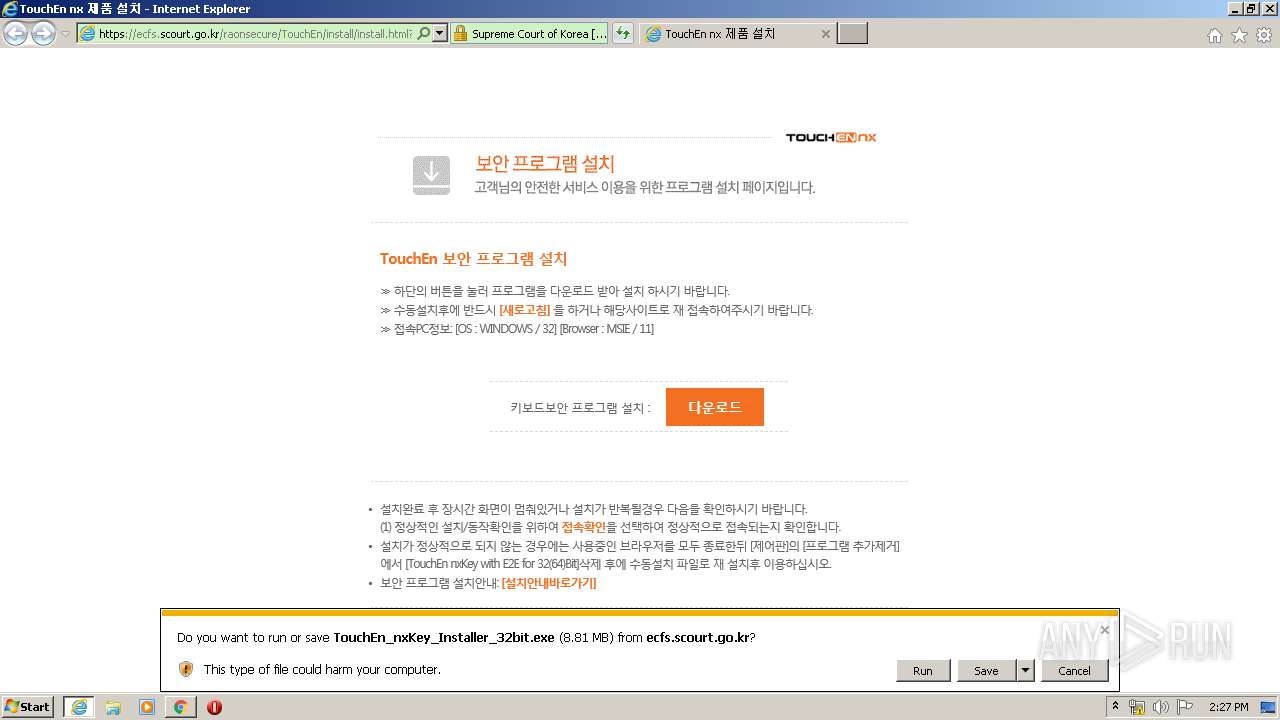
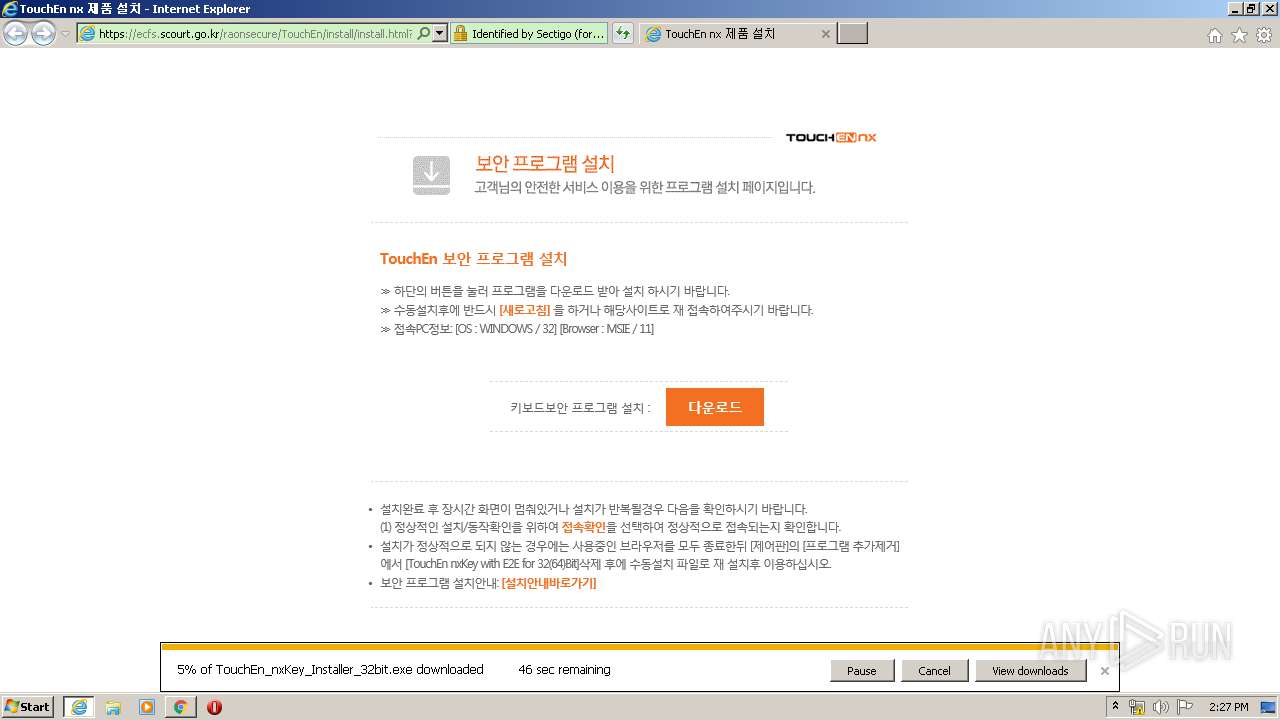
Loads dropped or rewritten executable
- raon_touchenex_Install.exe (PID: 3912)
- iexplore.exe (PID: 2988)
- TouchEn_nxKey_Installer_32bit.exe (PID: 1728)
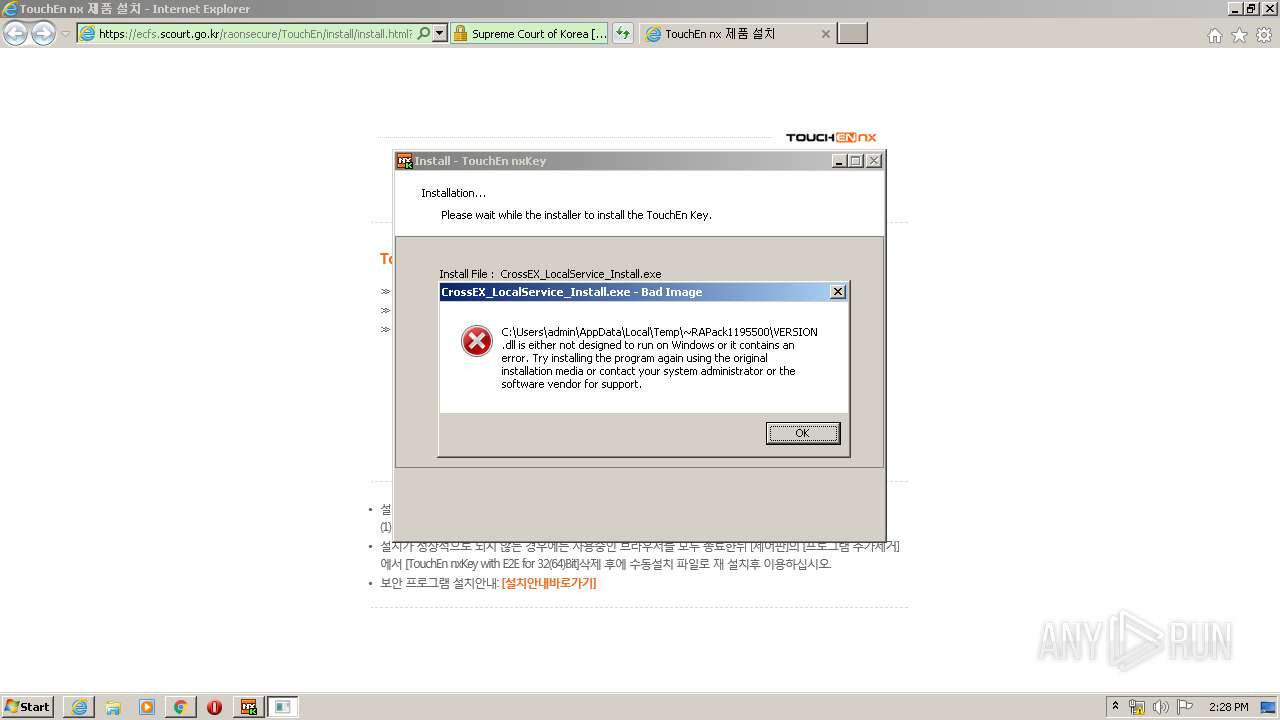
Application was dropped or rewritten from another process
- TouchEn_nxKey_Installer_32bit.exe (PID: 3180)
- CKSetup32.exe (PID: 1672)
- TouchEn_nxKey_Installer_32bit.exe (PID: 1728)
- CrossEX_LocalService_Install.exe (PID: 2776)
Changes settings of System certificates
- IEInstal.exe (PID: 3468)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3200)
Executable content was dropped or overwritten
- chrome.exe (PID: 3200)
- chrome.exe (PID: 2360)
- iexplore.exe (PID: 2872)
- CKSetup32.exe (PID: 1672)
- raon_touchenex_Install.exe (PID: 3912)
- TouchEn_nxKey_Installer_32bit.exe (PID: 1728)
Executed via COM
- IEInstal.exe (PID: 3468)
Reads Internet Cache Settings
- IEInstal.exe (PID: 3468)
Removes files from Windows directory
- CKSetup32.exe (PID: 1672)
Creates files in the Windows directory
- CKSetup32.exe (PID: 1672)
- TouchEn_nxKey_Installer_32bit.exe (PID: 1728)
Creates a software uninstall entry
- CKSetup32.exe (PID: 1672)
Creates files in the program directory
- raon_touchenex_Install.exe (PID: 3912)
Creates COM task schedule object
- raon_touchenex_Install.exe (PID: 3912)
- TouchEn_nxKey_Installer_32bit.exe (PID: 1728)
Adds / modifies Windows certificates
- IEInstal.exe (PID: 3468)
INFO
Application launched itself
- chrome.exe (PID: 3200)
- iexplore.exe (PID: 2872)
Reads Internet Cache Settings
- iexplore.exe (PID: 2872)
- iexplore.exe (PID: 2988)
- chrome.exe (PID: 3200)
Reads the hosts file
- chrome.exe (PID: 3200)
- chrome.exe (PID: 2360)
Changes internet zones settings
- iexplore.exe (PID: 2872)
Reads internet explorer settings
- iexplore.exe (PID: 2988)
Reads settings of System Certificates
- iexplore.exe (PID: 2988)
- IEInstal.exe (PID: 3468)
- iexplore.exe (PID: 2872)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 3200)
Manual execution by user
- chrome.exe (PID: 3200)
Creates files in the user directory
- iexplore.exe (PID: 2872)
- iexplore.exe (PID: 2988)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2872)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2872)
Changes settings of System certificates
- iexplore.exe (PID: 2872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
41
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2645801533404314906,11539777688616125608,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11550982486716470650 --mojo-platform-channel-handle=3744 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,2645801533404314906,11539777688616125608,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6981165736043195650 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2645801533404314906,11539777688616125608,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14382932340903869468 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
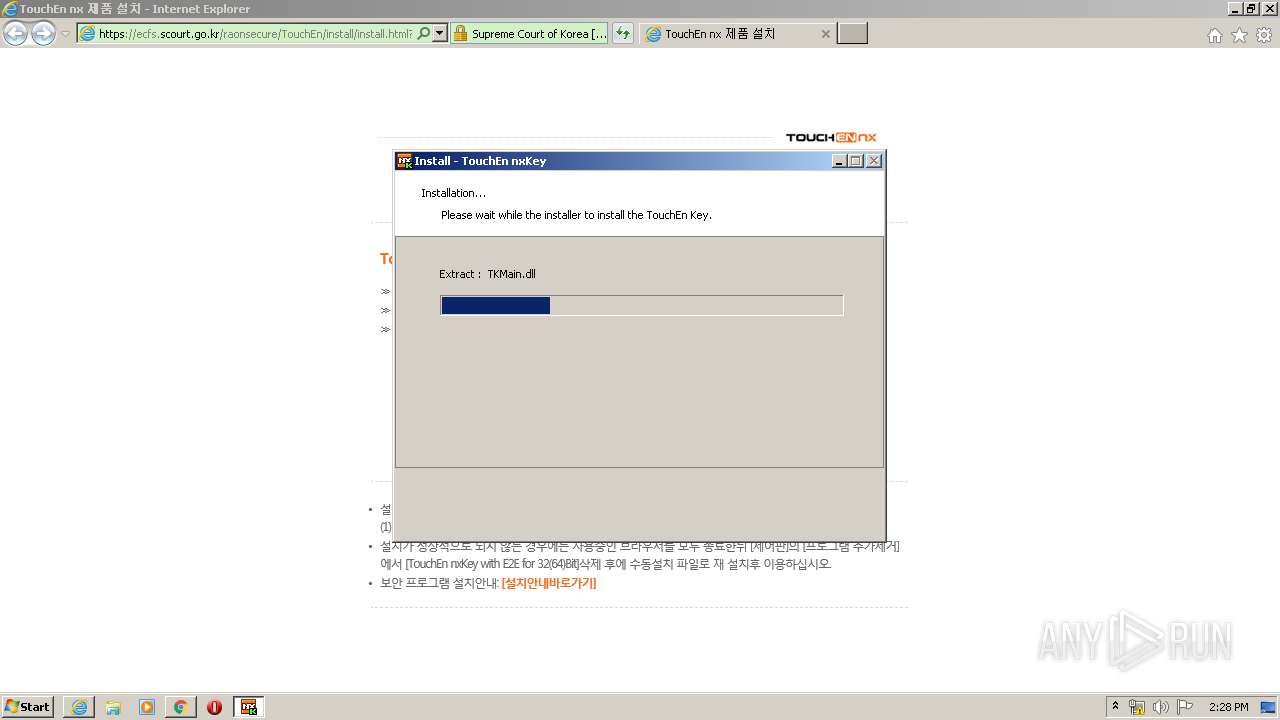
| 1672 | C:\Windows\system32\CKSetup32.exe /install appm | C:\Windows\system32\CKSetup32.exe | TouchEn_nxKey_Installer_32bit.exe | ||||||||||||
User: admin Company: RaonSecure Co., Ltd. Integrity Level: HIGH Description: TouchEn key Installer Exit code: 0 Version: 3, 1, 1, 29 Modules
| |||||||||||||||
| 1728 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\TouchEn_nxKey_Installer_32bit.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\TouchEn_nxKey_Installer_32bit.exe | iexplore.exe | ||||||||||||
User: admin Company: RaonSecure Co., Ltd. Integrity Level: HIGH Description: TouchEn nxKey Keyboard Protector Installer Exit code: 0 Version: 1, 0, 0, 47 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2645801533404314906,11539777688616125608,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18391925008139583127 --mojo-platform-channel-handle=1636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2645801533404314906,11539777688616125608,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15320924768680652558 --mojo-platform-channel-handle=3004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2645801533404314906,11539777688616125608,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11339581875581459277 --mojo-platform-channel-handle=4220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2645801533404314906,11539777688616125608,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8942545415769334386 --mojo-platform-channel-handle=4424 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
17 425
Read events
6 573
Write events
7 684
Delete events
3 168
Modification events
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3162552744 | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30790136 | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
47
Suspicious files
91
Text files
514
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab88DF.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar88E0.tmp | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5080DC7A65DB6A5960ECD874088F3328_6B3C86056F9AA33BFBA8EF35E4D23D14 | binary | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F6D2120A74D8E120A79AE4737511E774_E4CF8C1C151331B9828793B3483EF448 | der | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\8QU1CQCK.htm | html | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5457A8CE4B2A7499F8299A013B6E1C7C_CE50F893881D43DC0C815E4D80FAF2B4 | der | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5457A8CE4B2A7499F8299A013B6E1C7C_CE50F893881D43DC0C815E4D80FAF2B4 | binary | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5080DC7A65DB6A5960ECD874088F3328_6B3C86056F9AA33BFBA8EF35E4D23D14 | der | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\xecureweb_ecf_o[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
123
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2988 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEAanQ4DU6%2F7UNbWj9%2BFqvdg%3D | US | der | 727 b | whitelisted |
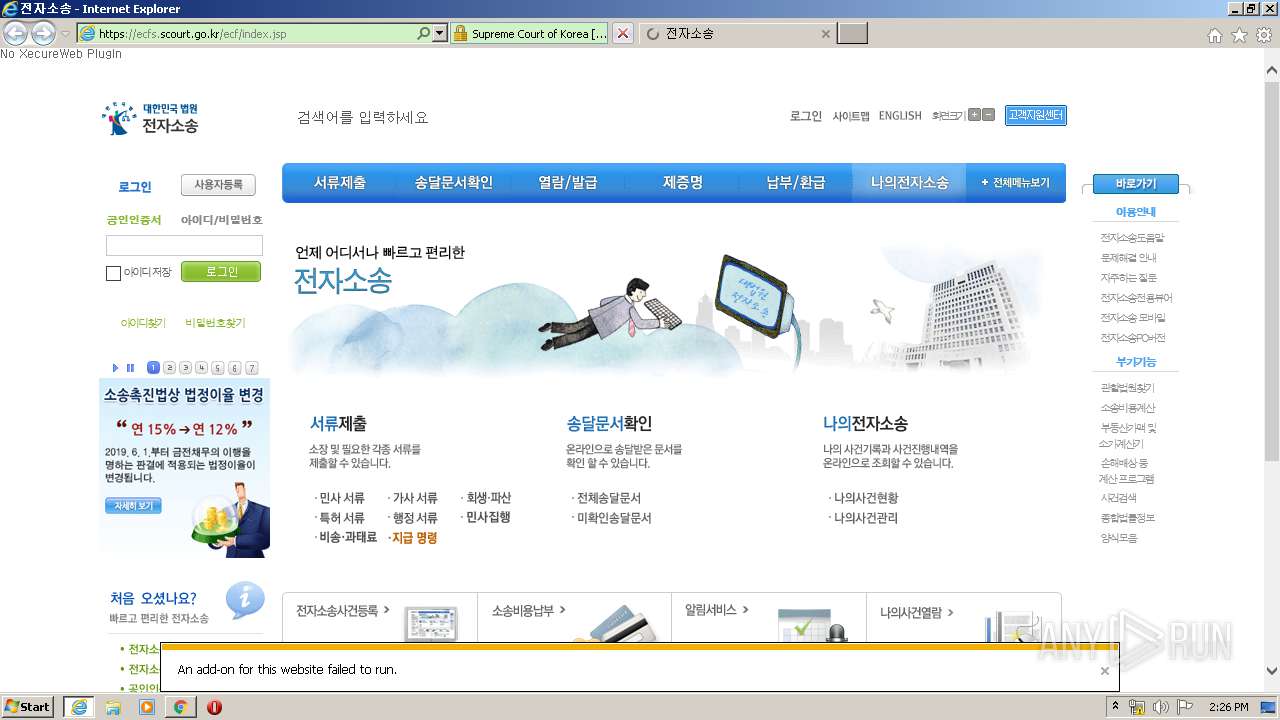
2988 | iexplore.exe | GET | 302 | 203.240.75.213:80 | http://ecfs.scourt.go.kr/ecf/index.jsp | KR | html | 306 b | whitelisted |
2988 | iexplore.exe | GET | 200 | 203.240.75.213:80 | http://ecfs.scourt.go.kr/ | KR | html | 306 b | whitelisted |
2988 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
2360 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
2988 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBT0MXB3rveIElndnl0j8v4md2bQRgQUOdr%2FyigUiqh0Ewi55A6p0vp%2BnWkCEQCV9Iy342%2FREvMzMRwkMyiR | US | der | 472 b | whitelisted |
2988 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | US | der | 1.48 Kb | whitelisted |
2360 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2872 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2988 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | US | der | 1.49 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2988 | iexplore.exe | 203.240.75.213:80 | ecfs.scourt.go.kr | Supreme Court of Korea | KR | unknown |
2988 | iexplore.exe | 203.240.75.213:443 | ecfs.scourt.go.kr | Supreme Court of Korea | KR | unknown |
2988 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
2872 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2360 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
2360 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2360 | chrome.exe | 172.217.18.110:443 | clients4.google.com | Google Inc. | US | whitelisted |
2360 | chrome.exe | 216.58.207.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2360 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2360 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ecfs.scourt.go.kr |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients4.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
TouchEn_nxKey_Installer_32bit.exe | 20141130 fn : C:\Users\admin\AppData\Local\Temp\~RAPack1195500\_Chunk.zip, C:\Users\admin\AppData\Local\Temp\~RAPack1195500 308
|
TouchEn_nxKey_Installer_32bit.exe | 20141211 1.szResVersion : 3,1,1,29
|
TouchEn_nxKey_Installer_32bit.exe | 20141130 fn : C:\Windows\system32\CKSetup32.exe, C:\Windows\system32(size=2716536) 549
|
TouchEn_nxKey_Installer_32bit.exe | 20141130 1191_.\TouchEn_nxKey_Installer.cpp
|
TouchEn_nxKey_Installer_32bit.exe | C:\Windows\system32\CKSetup32.exe /install appm
|
CKSetup32.exe | [TK] KillProcessByImageName = CKAgentNXE.exe
|
CKSetup32.exe | [TK] KillProcessByImageName return = 0
|
CKSetup32.exe | [TK] KillProcessByImageName = CKAgent.exe
|
CKSetup32.exe | [TK] KillProcessByImageName return = 0
|
CKSetup32.exe | [TK] [CKSETUP 20130627 DOSPathFileName] C:\Windows\system32\winlogon.exe
|