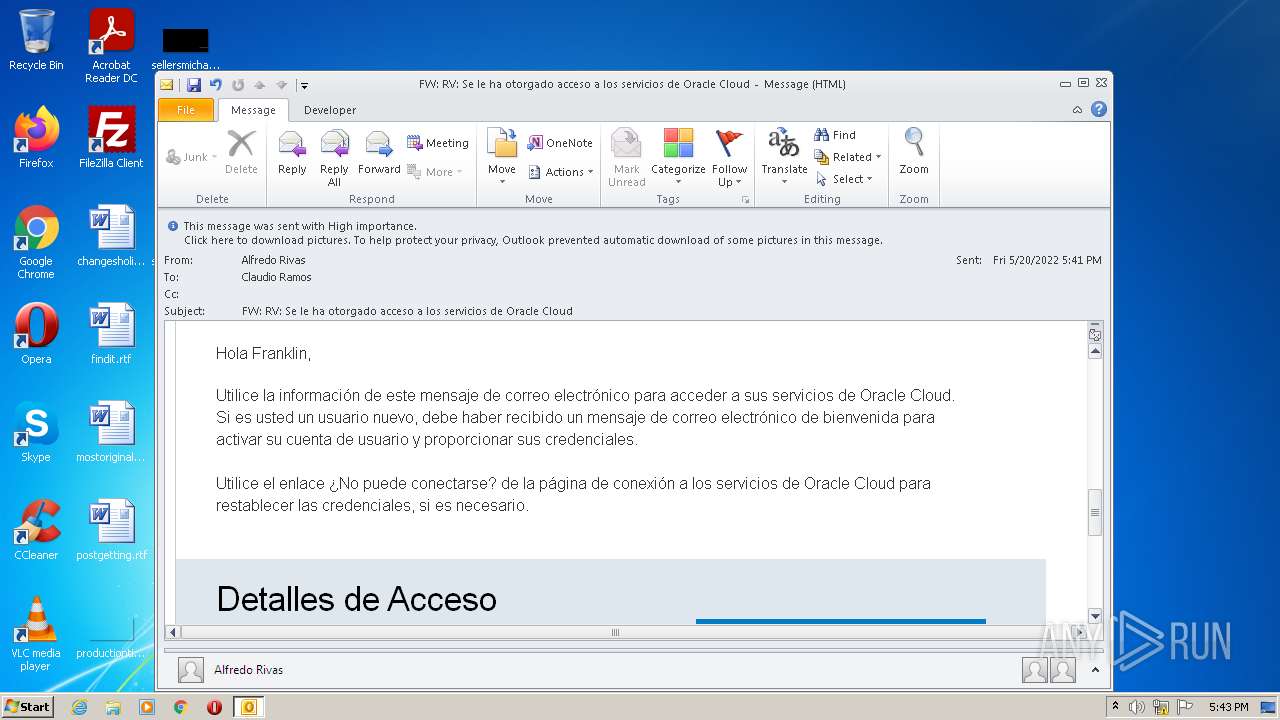
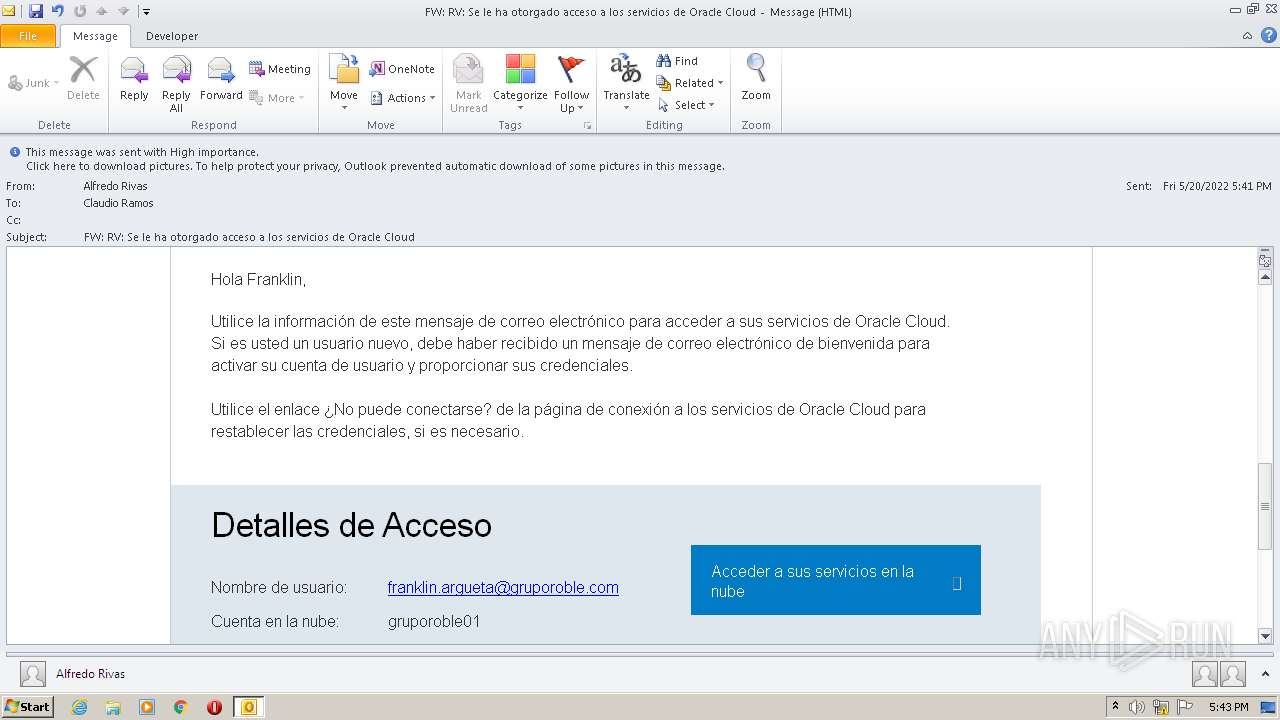
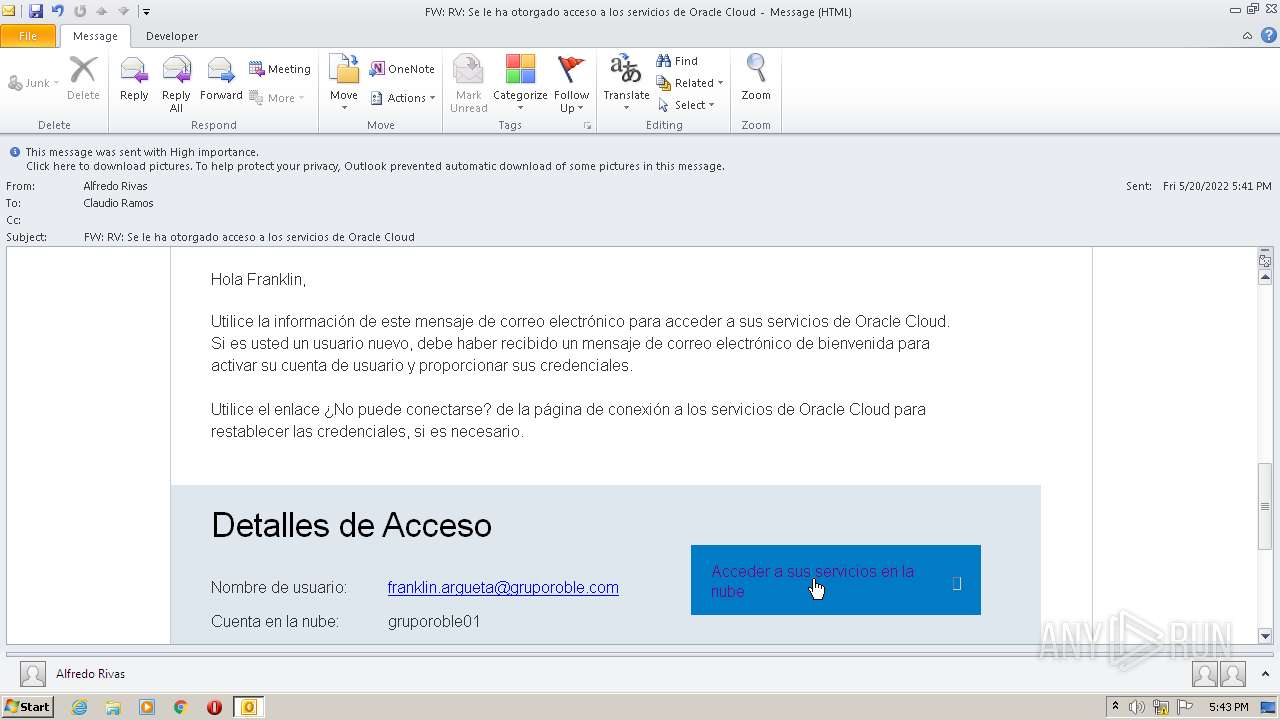
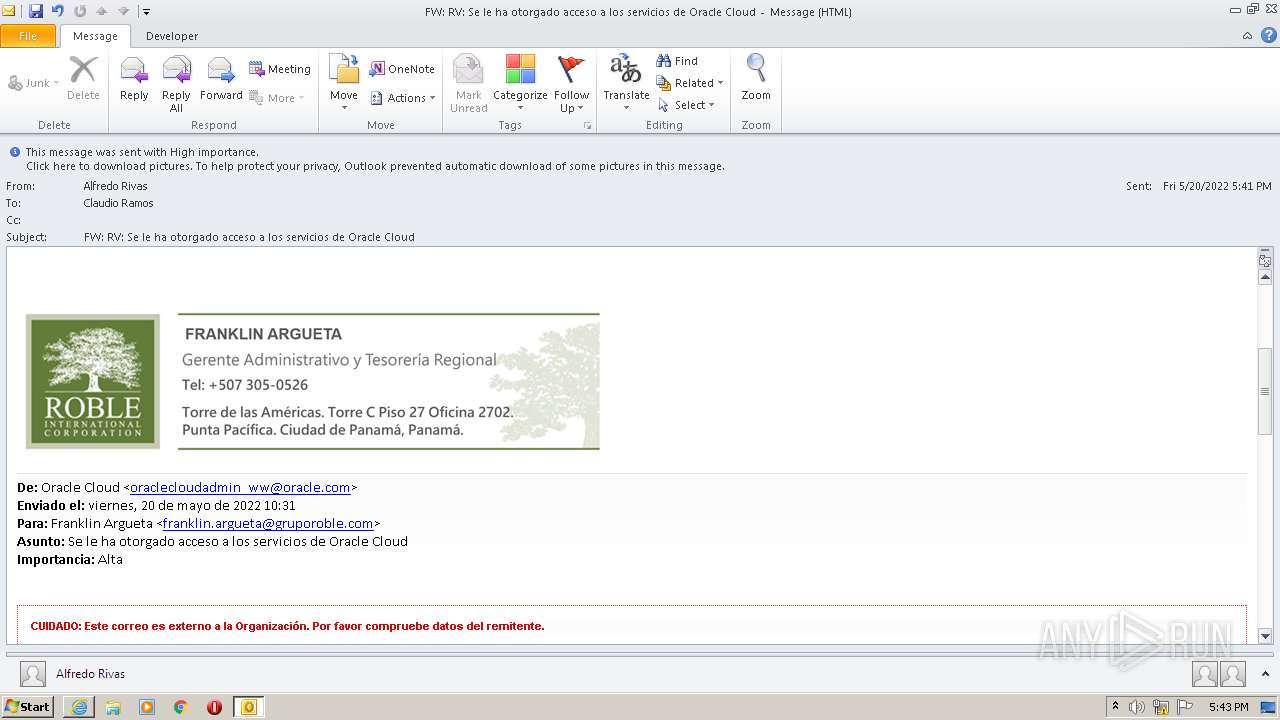
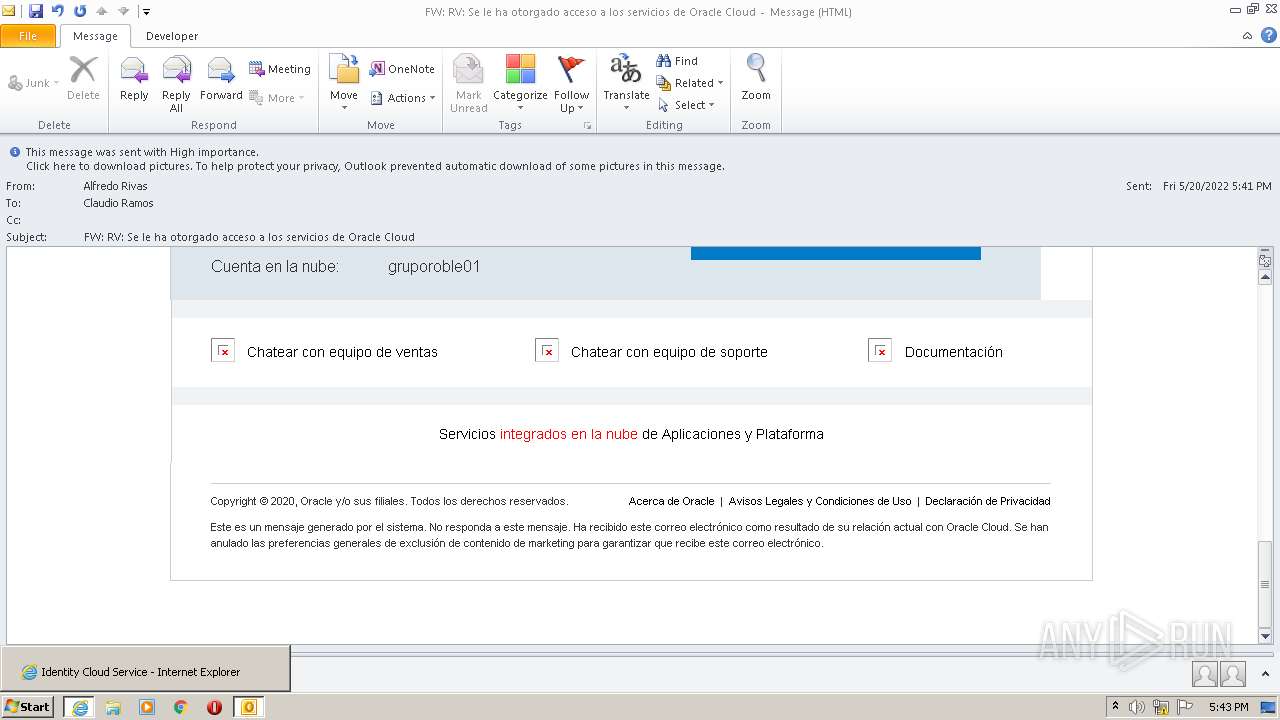
| File name: | FW RV Se le ha otorgado acceso a los servicios de Oracle Cloud.msg |
| Full analysis: | https://app.any.run/tasks/9a41471e-5cff-475f-8aa5-991b94334dc3 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 16:42:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 1BD48FF4B7714D31E4C9209372A6EFEA |
| SHA1: | B9DFE98871F096D23C9446358CEFFBD0957932CB |
| SHA256: | 1FE571AC9F966AB07DD850EC2E69880FF10280A0DCCE2F9E3F181E4C43C751D2 |
| SSDEEP: | 3072:oYSykxYkxRAkZfy+4iImVqKlRRuCTS2tT2pMavC70npyXiy:oYSykxYkximNbqidTScMC4npK |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 116)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1340)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 116)
INFO
Checks supported languages
- OUTLOOK.EXE (PID: 116)
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 1340)
Reads the computer name
- iexplore.exe (PID: 1340)
- OUTLOOK.EXE (PID: 116)
- iexplore.exe (PID: 3356)
Checks Windows Trust Settings
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 1340)
Changes internet zones settings
- iexplore.exe (PID: 3356)
Application launched itself
- iexplore.exe (PID: 3356)
Reads internet explorer settings
- iexplore.exe (PID: 1340)
Reads settings of System Certificates
- iexplore.exe (PID: 1340)
- iexplore.exe (PID: 3356)
Creates files in the user directory
- iexplore.exe (PID: 1340)
- OUTLOOK.EXE (PID: 116)
Searches for installed software
- OUTLOOK.EXE (PID: 116)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\FW RV Se le ha otorgado acceso a los servicios de Oracle Cloud.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
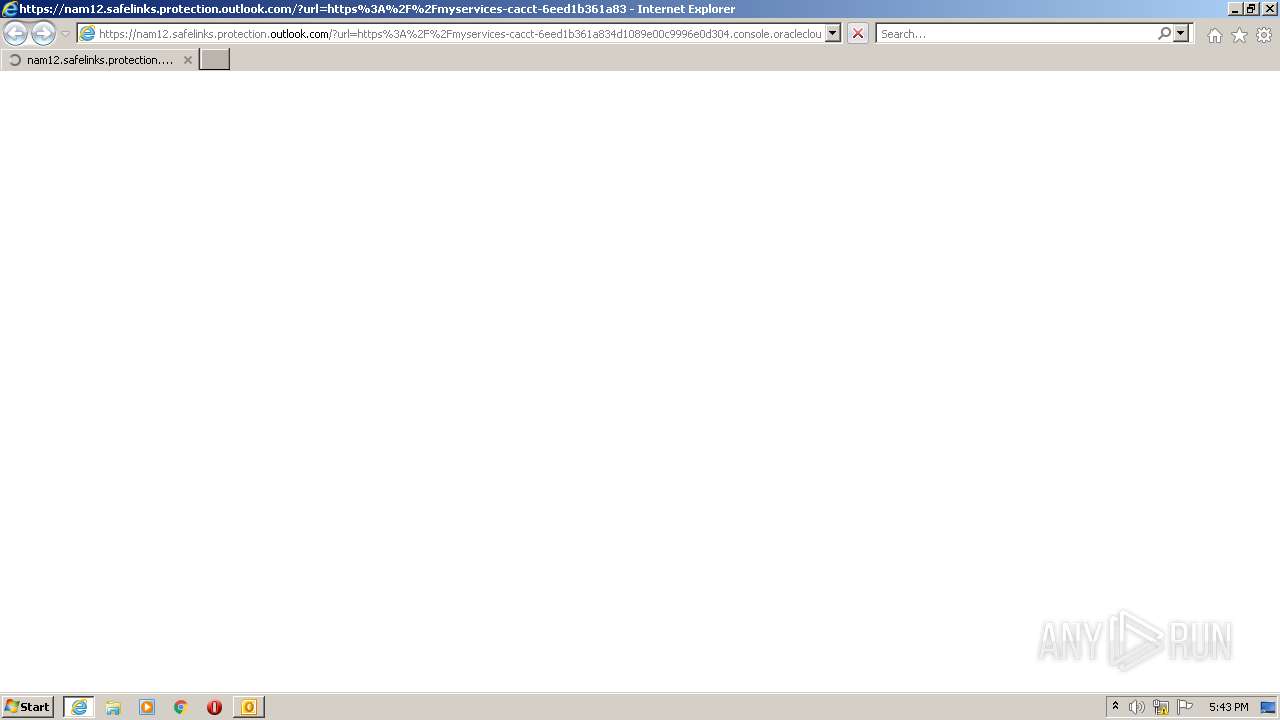
| 1340 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3356 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
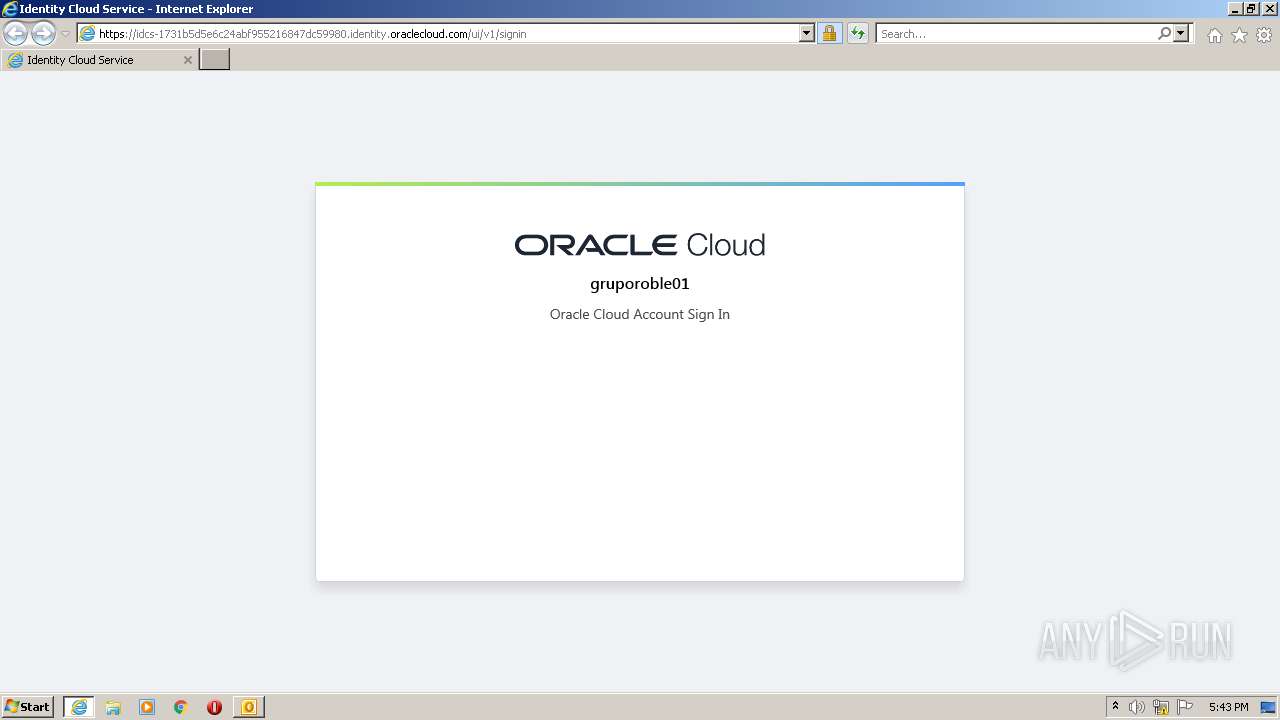
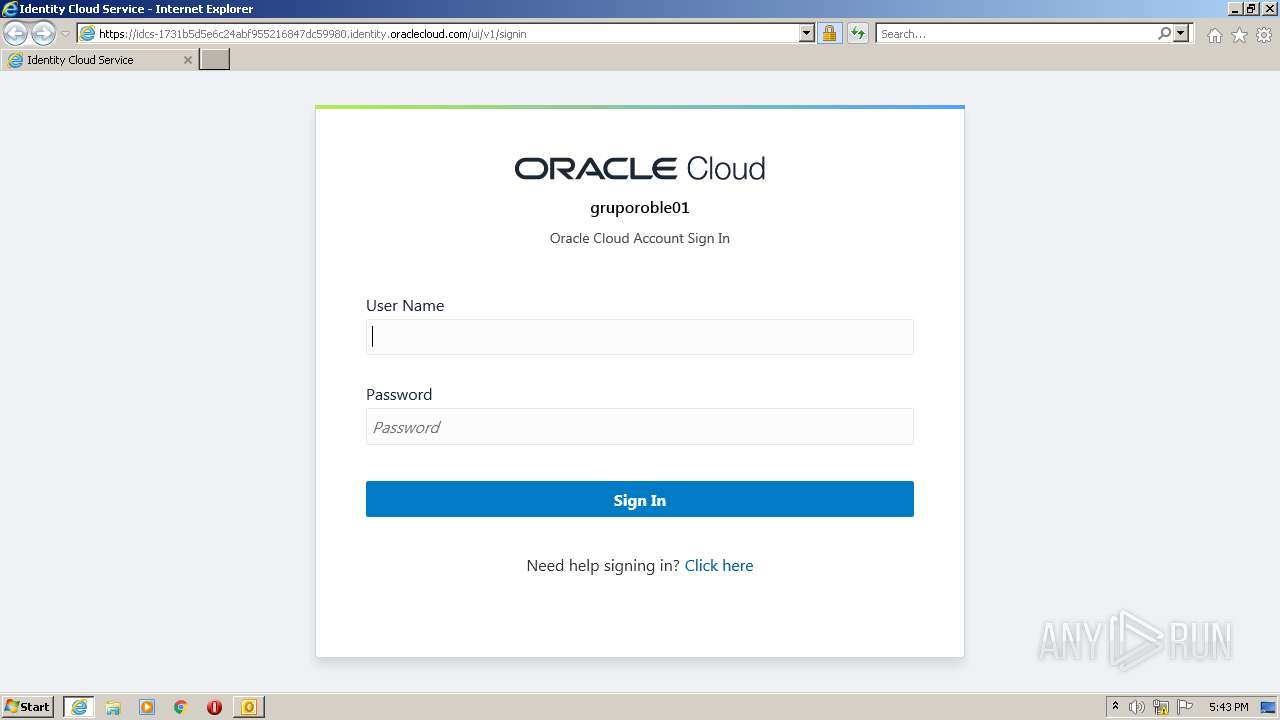
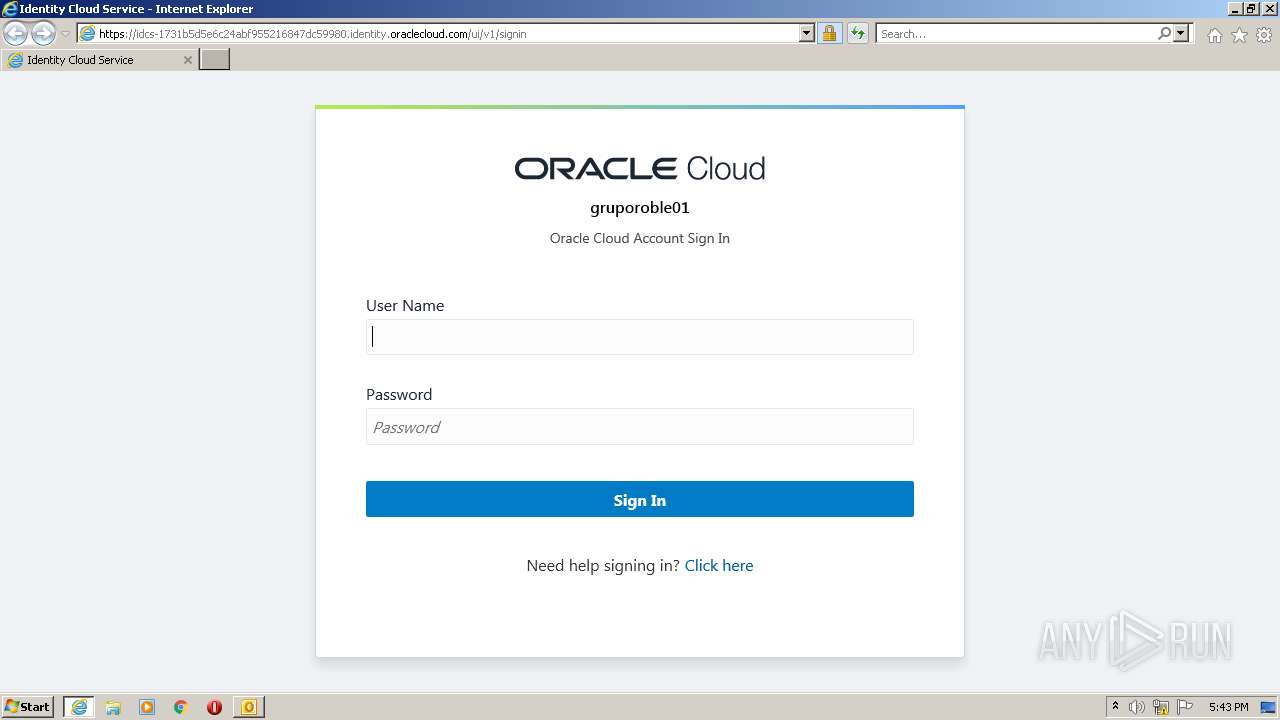
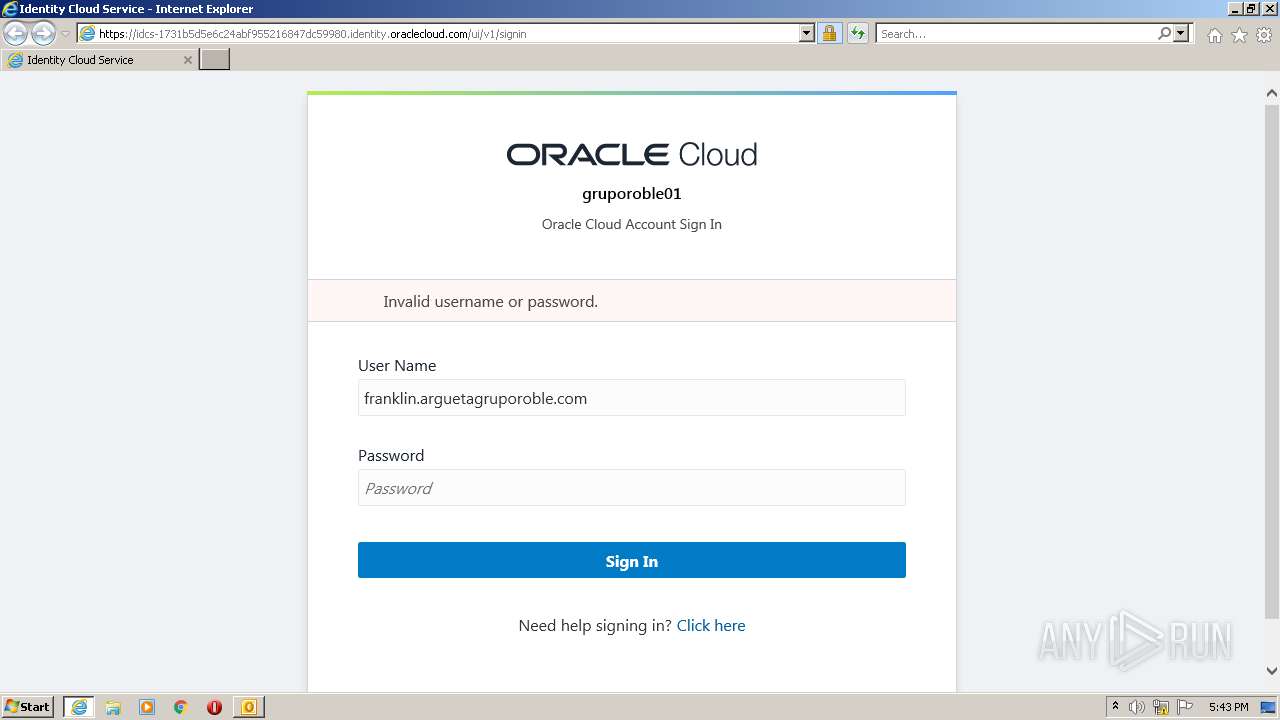
| 3356 | "C:\Program Files\Internet Explorer\iexplore.exe" https://nam12.safelinks.protection.outlook.com/?url=https%3A%2F%2Fmyservices-cacct-6eed1b361a834d1089e00c9996e0d304.console.oraclecloud.com%2Fmycloud%2Fcloudportal%2FgettingStarted&data=05%7C01%7Cclaudio.ramos%40gruporoble.com%7C80d5a354f88742dcedd708da3a7f909d%7Ccb388aaebefa48faa09d2e43af392906%7C0%7C0%7C637886616824932167%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C3000%7C%7C%7C&sdata=Wd6PEkaQqYUX02gHqURYTtONCgvzxloBZW4T%2Fv6obJ0%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
17 441
Read events
16 734
Write events
687
Delete events
20
Modification events
| (PID) Process: | (116) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (116) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (116) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (116) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (116) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (116) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (116) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (116) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (116) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (116) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
11
Text files
48
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 116 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR4C3D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 116 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 116 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 116 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 116 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\27576C3A.dat | image | |
MD5:— | SHA256:— | |||
| 116 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9359DFDD.dat | image | |
MD5:— | SHA256:— | |||
| 1340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 116 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{51CA776D-D471-478F-986F-D3E7585EFC95}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 1340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2F23D0F5E4D72862517E1CB26A329742_F6FACC49395CFA949BCE851E73323C49 | binary | |
MD5:— | SHA256:— | |||
| 116 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_D803A1EFD7F62247B8C4AD6A7CC3E70E.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
43
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAIecmfGeVA8KKXFtswdUeU%3D | US | der | 471 b | whitelisted |
1340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEA9C%2F8%2B%2Bz8JG5F%2F5nyKl%2B%2FU%3D | US | der | 471 b | whitelisted |
1340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
1340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
1340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAP7kGKR3NlYtF7LQ7y8XnM%3D | US | der | 313 b | whitelisted |
1340 | iexplore.exe | GET | 200 | 8.252.192.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b488852043d327e1 | US | compressed | 4.70 Kb | whitelisted |
1340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAGewca9P1l7sgwzOOVR2Hc%3D | US | der | 471 b | whitelisted |
3356 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3356 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
116 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1340 | iexplore.exe | 8.248.131.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3356 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1340 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3356 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1340 | iexplore.exe | 129.191.5.179:443 | myservices-cacct-6eed1b361a834d1089e00c9996e0d304.console.oraclecloud.com | Oracle Corporation | US | unknown |
1340 | iexplore.exe | 147.154.119.52:443 | idcs-1731b5d5e6c24abf955216847dc59980.identity.oraclecloud.com | — | US | unknown |
3356 | iexplore.exe | 147.154.119.52:443 | idcs-1731b5d5e6c24abf955216847dc59980.identity.oraclecloud.com | — | US | unknown |
1340 | iexplore.exe | 13.32.121.98:443 | consent.truste.com | Amazon.com, Inc. | US | unknown |
3356 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
nam12.safelinks.protection.outlook.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
myservices-cacct-6eed1b361a834d1089e00c9996e0d304.console.oraclecloud.com |
| unknown |
idcs-1731b5d5e6c24abf955216847dc59980.identity.oraclecloud.com |
| unknown |
consent.truste.com |
| whitelisted |
oracle.112.2o7.net |
| whitelisted |