| File name: | Maltoolkit.exe |
| Full analysis: | https://app.any.run/tasks/5ea5baed-4dd9-4165-a2c5-016bf744d0a5 |
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2024, 15:26:37 |
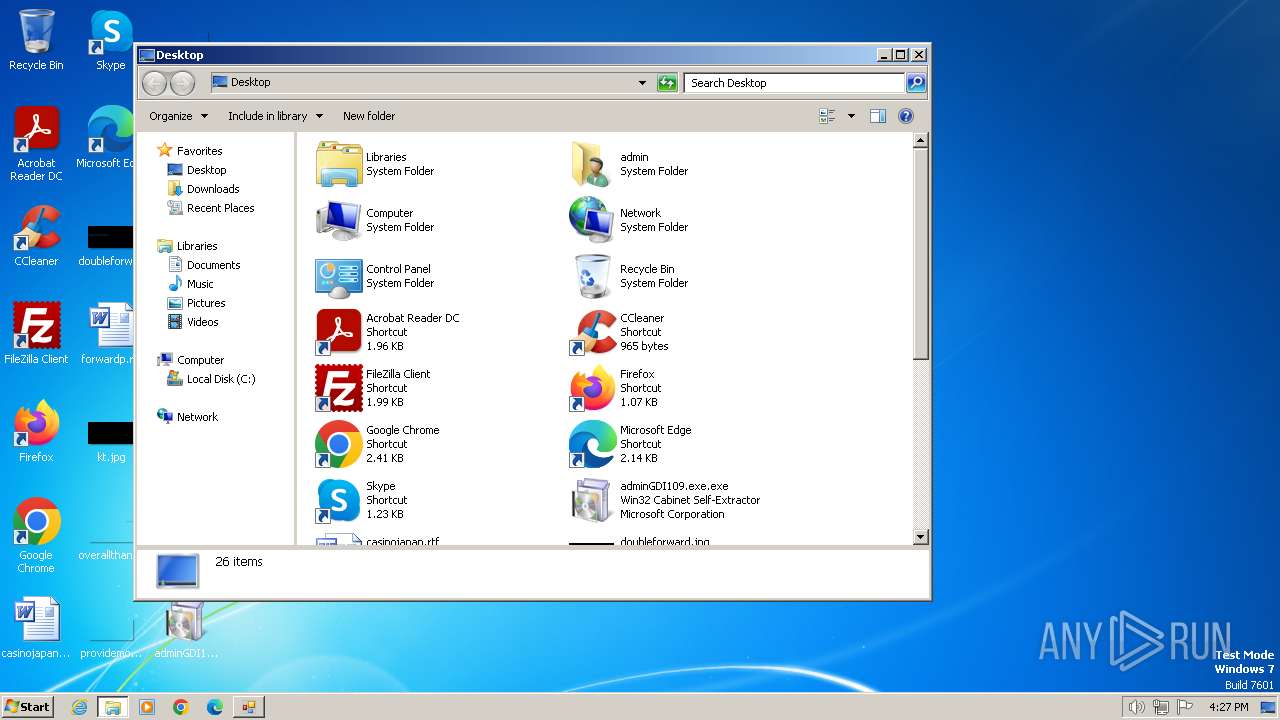
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D4163D85BA71A09B181DEA459744698C |
| SHA1: | 002EFBDAF3B87A486CD1B577B219A36995A66489 |
| SHA256: | 1FD51D6DD83F903B81C2FE5EE5811A32F4EEDDAE97B02C89659E6F0E7DA16B1E |
| SSDEEP: | 12288:FkJiiL9fPbGXY3ZuTmlOIq76xb35zdtKTKKpKKMi:Fk0iL97ngEMWx35i |
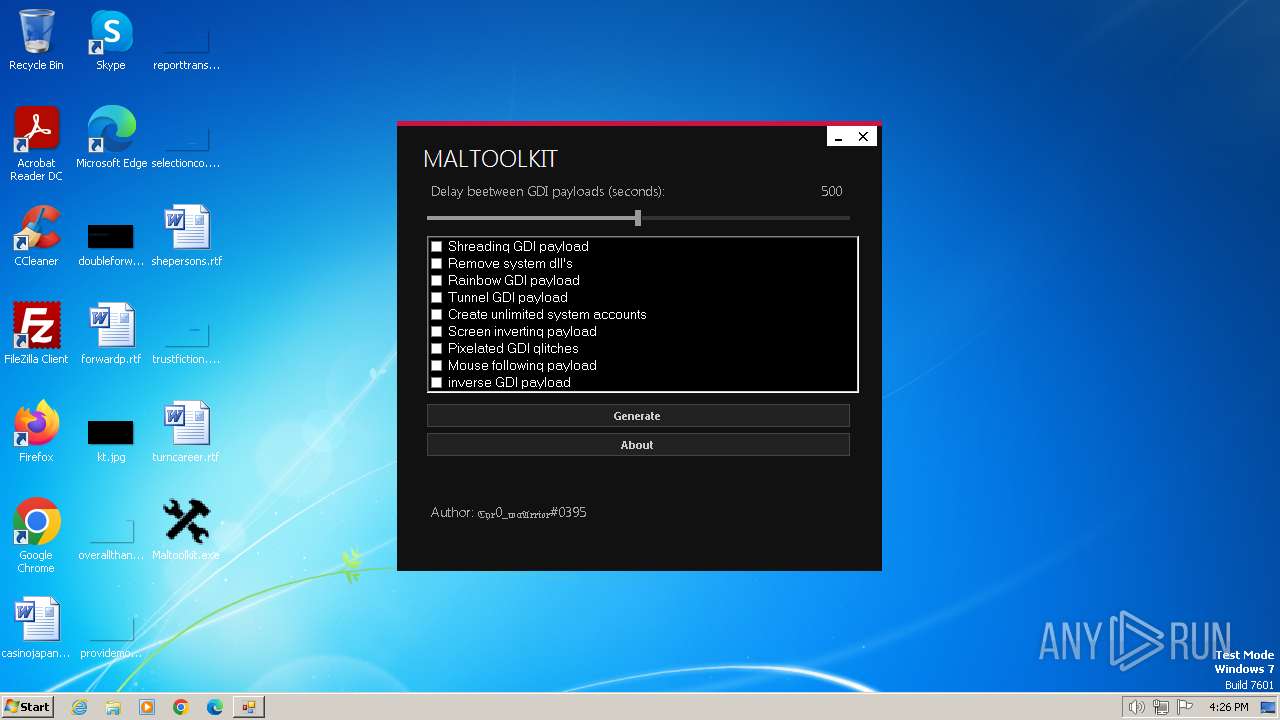
MALICIOUS
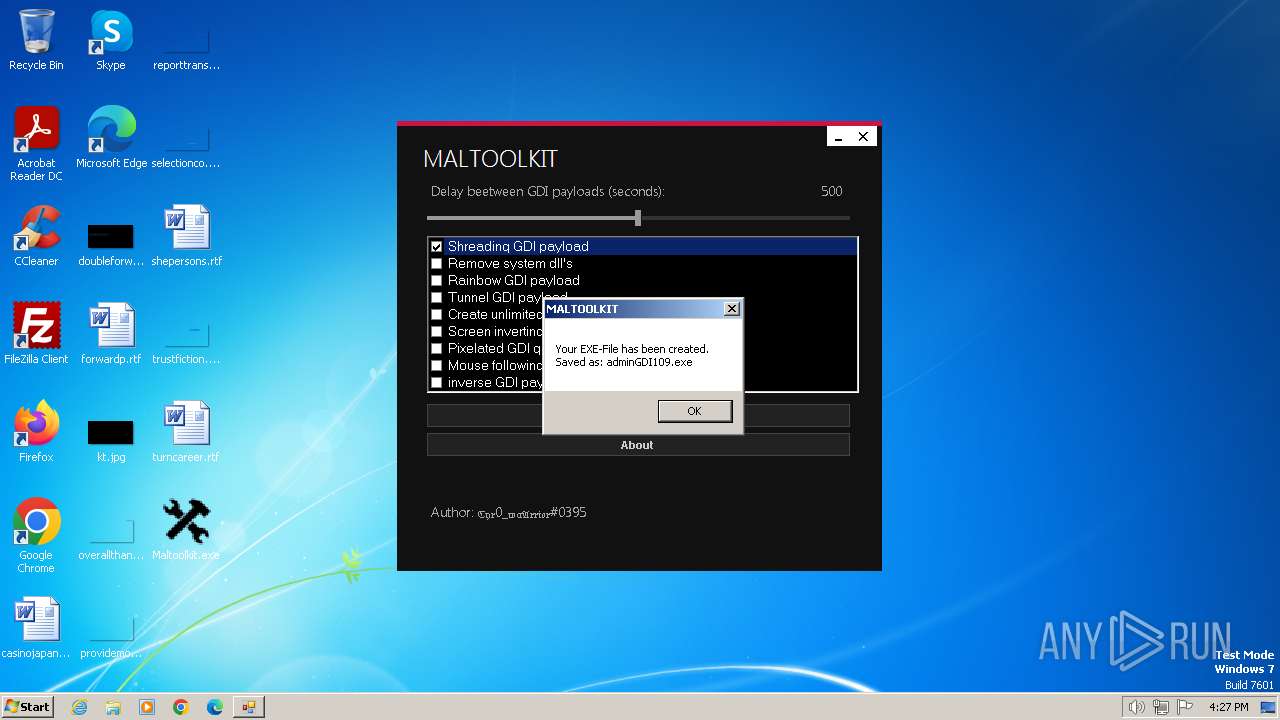
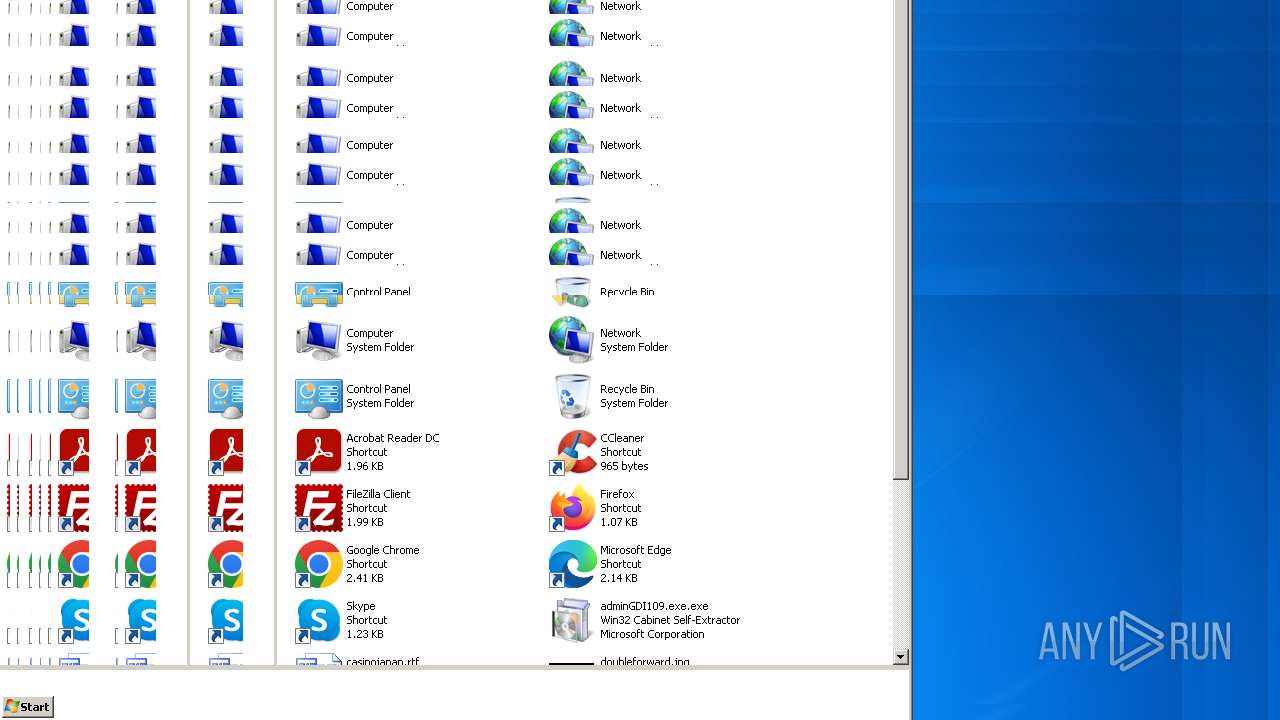
Drops the executable file immediately after the start
- Maltoolkit.exe (PID: 3392)
- adminGDI109.exe.exe (PID: 1980)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Maltoolkit.exe (PID: 3392)
- adminGDI109.exe.exe (PID: 1980)
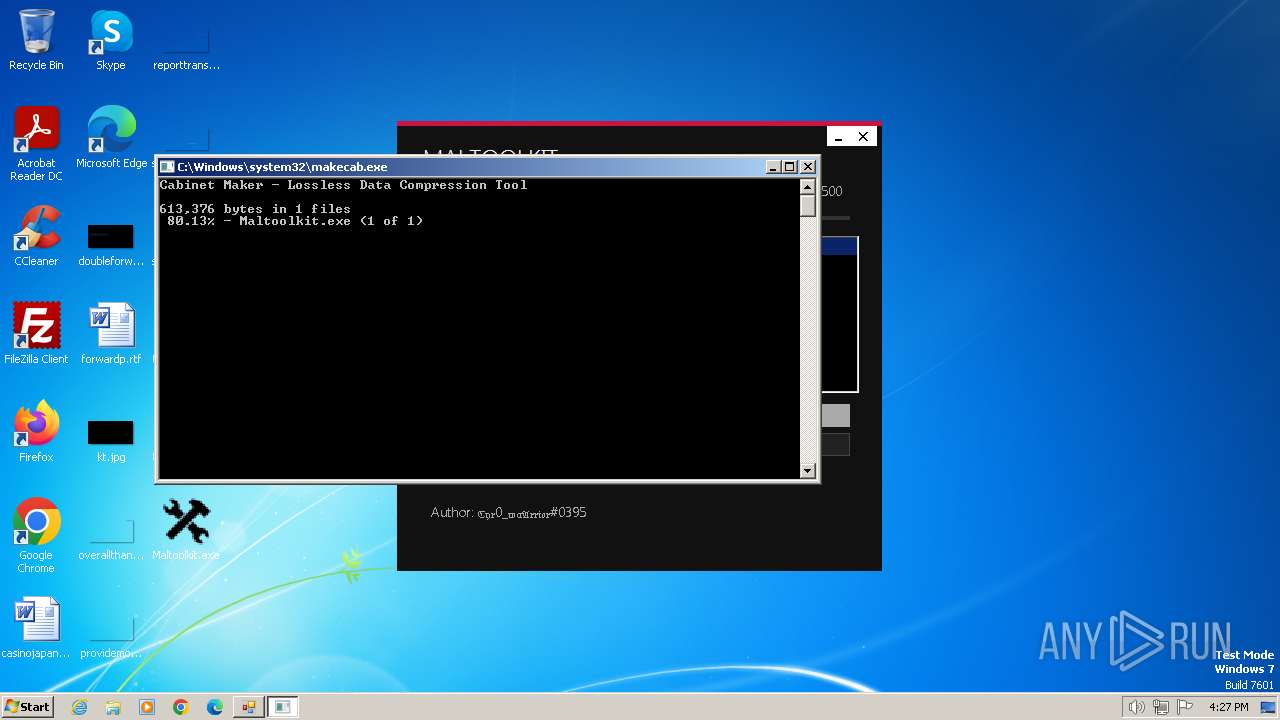
Process drops legitimate windows executable
- iexpress.exe (PID: 3204)
Executable content was dropped or overwritten
- iexpress.exe (PID: 3204)
- adminGDI109.exe.exe (PID: 1980)
Starts a Microsoft application from unusual location
- adminGDI109.exe.exe (PID: 1980)
The executable file from the user directory is run by the CMD process
- Maltoolkit.exe (PID: 3292)
INFO
Create files in a temporary directory
- Maltoolkit.exe (PID: 3392)
- makecab.exe (PID: 3192)
- adminGDI109.exe.exe (PID: 1980)
Reads the computer name
- Maltoolkit.exe (PID: 3392)
- Maltoolkit.exe (PID: 3292)
Reads the machine GUID from the registry
- Maltoolkit.exe (PID: 3392)
- Maltoolkit.exe (PID: 3292)
Checks supported languages
- Maltoolkit.exe (PID: 3392)
- adminGDI109.exe.exe (PID: 1980)
- Maltoolkit.exe (PID: 3292)
Drops the executable file immediately after the start
- iexpress.exe (PID: 3204)
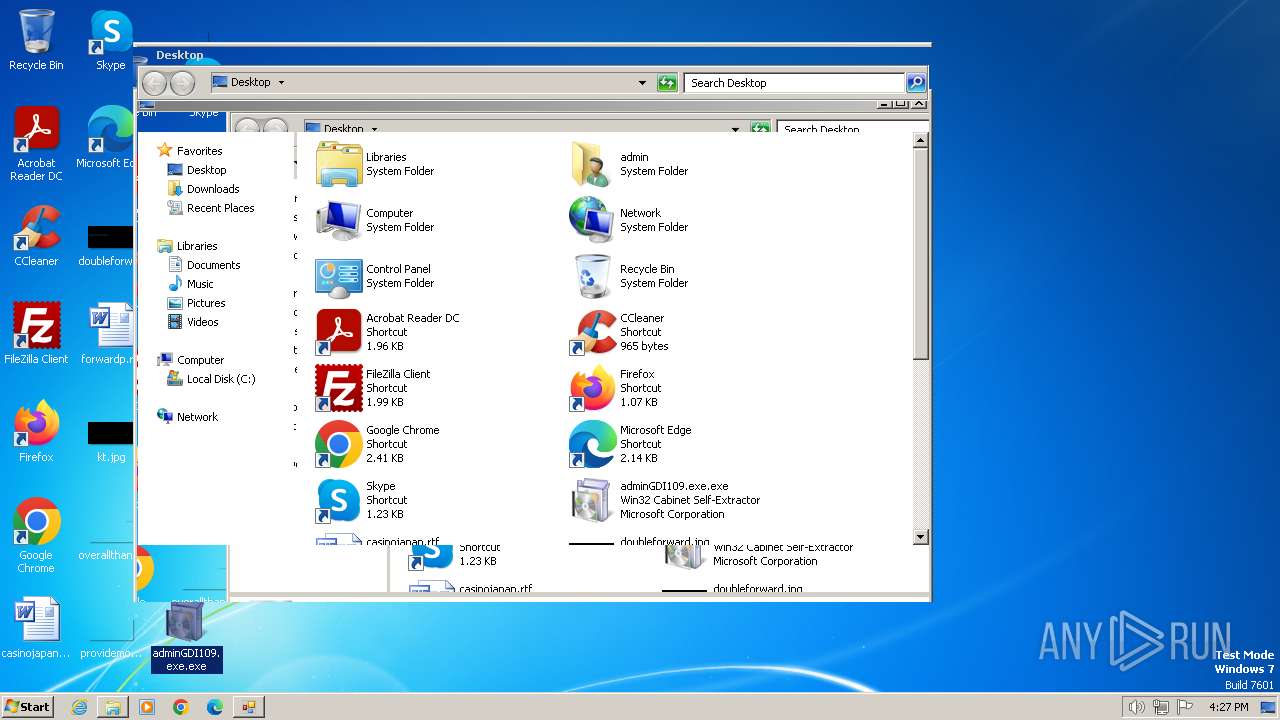
Manual execution by a user
- adminGDI109.exe.exe (PID: 1980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2046:11:16 21:21:40+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 606208 |
| InitializedDataSize: | 6656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x95f1e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Made by malwareman https://www.youtube.com/channel/UCk8Gj-r2kQdCkleLtKWz7rQ |
| CompanyName: | MALWAREMAN |
| FileDescription: | Maltoolkit |
| FileVersion: | 1.0.0.0 |
| InternalName: | Maltoolkit.exe |
| LegalCopyright: | Copyright © MALWAREMAN |
| LegalTrademarks: | - |
| OriginalFileName: | Maltoolkit.exe |
| ProductName: | Maltoolkit |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
48
Monitored processes
7
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 940 | cmd /c Maltoolkit.exe --shreadinggdipayload500 | C:\Windows\System32\cmd.exe | — | adminGDI109.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
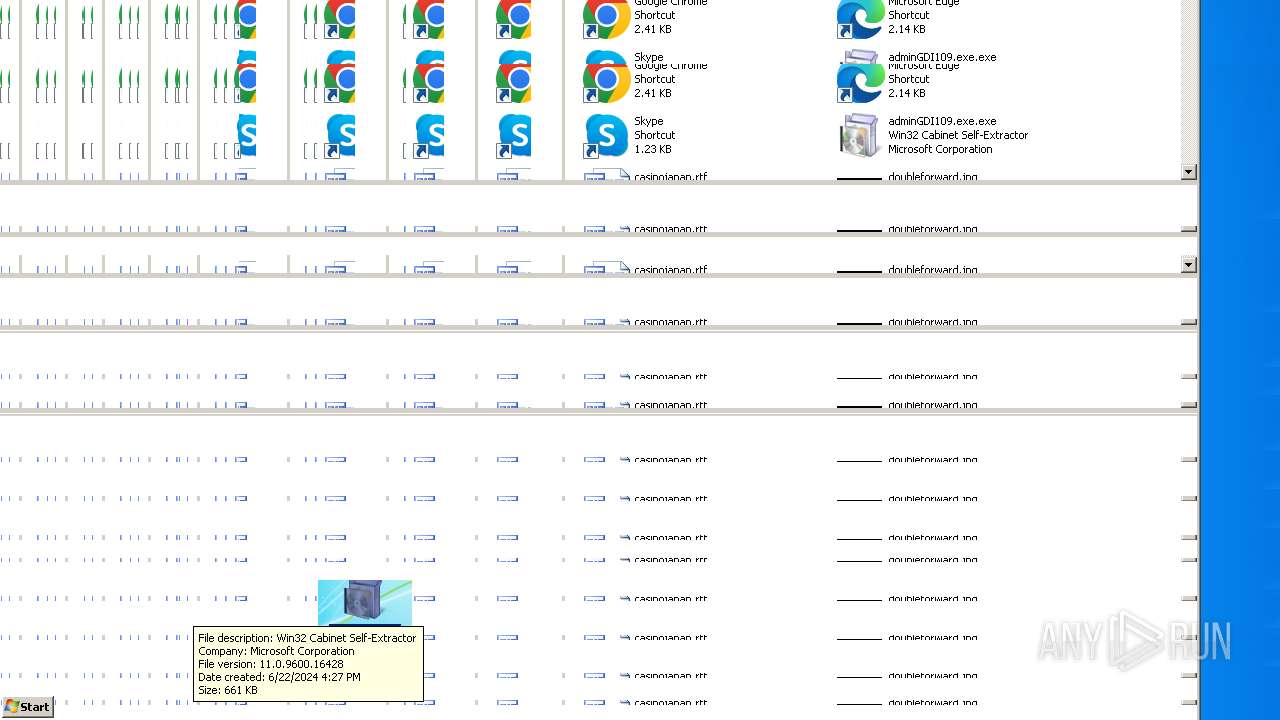
| 1980 | "C:\Users\admin\Desktop\adminGDI109.exe.exe" | C:\Users\admin\Desktop\adminGDI109.exe.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2248 | "cmd.exe" | C:\Windows\System32\cmd.exe | — | Maltoolkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3192 | C:\Windows\system32\makecab.exe /f "C:\Users\admin\Desktop\\~adminGDI109.exe.DDF" | C:\Windows\System32\makecab.exe | — | iexpress.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3204 | iexpress /N C:\Users\admin\AppData\Local\Temp\\optionfile.SED | C:\Windows\System32\iexpress.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Wizard Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3292 | Maltoolkit.exe --shreadinggdipayload500 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Maltoolkit.exe | — | cmd.exe | |||||||||||
User: admin Company: MALWAREMAN Integrity Level: MEDIUM Description: Maltoolkit Version: 1.0.0.0 Modules
| |||||||||||||||
| 3392 | "C:\Users\admin\Desktop\Maltoolkit.exe" | C:\Users\admin\Desktop\Maltoolkit.exe | — | explorer.exe | |||||||||||
User: admin Company: MALWAREMAN Integrity Level: MEDIUM Description: Maltoolkit Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 530
Read events
1 530
Write events
0
Delete events
0
Modification events
Executable files
4
Suspicious files
9
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3192 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_3192_6 | binary | |
MD5:62BC16959DE846F742984EF063A5914F | SHA256:35D9841E093186A38D807637514EA6C4654C8CF2CB124F99C31666C7A9A25FBD | |||
| 3392 | Maltoolkit.exe | C:\Windows\Temp\data.tmp | text | |
MD5:88FC38525095CC0D4C8D0BBA5C6E999B | SHA256:F90A610DF04BE7E55A4A864712357DC630AFE7D6ED1B1C4FAE51C03F431378EB | |||
| 3392 | Maltoolkit.exe | C:\Users\admin\AppData\Local\Temp\optionfile.SED | binary | |
MD5:D3C6034A82D6EB06E8120C57526A94EC | SHA256:E4DC624A9655A3C0AEC2CB4F90DE97E35B3DA224C0F9E47B6C8A5682305EBAD1 | |||
| 3204 | iexpress.exe | C:\Users\admin\Desktop\RCX2E7A.tmp | executable | |
MD5:27F92FD9D27BEF0E17996F507BF3D735 | SHA256:7DF6B8A6A57E0CF4EBA02F55412EBCE5B6B331BB825B3480DC21D31370DABDF4 | |||
| 3204 | iexpress.exe | C:\Users\admin\Desktop\~adminGDI109.exe.DDF | binary | |
MD5:60E21D6315E1F4A0F3D6C7BBCF0F56BC | SHA256:01D71111C332F00860A1ACE8A26C0962356DD585C27F20AED705D09A115CEF04 | |||
| 3204 | iexpress.exe | C:\Users\admin\Desktop\adminGDI109.exe.exe | executable | |
MD5:6A92CEC8532056791C6832B2725D170D | SHA256:3D0E2C0CCFEEA27D4B7414B9DA0DE4707C2087134D3FF8AFE6FF59522A98E137 | |||
| 1980 | adminGDI109.exe.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Maltoolkit.exe | executable | |
MD5:D4163D85BA71A09B181DEA459744698C | SHA256:1FD51D6DD83F903B81C2FE5EE5811A32F4EEDDAE97B02C89659E6F0E7DA16B1E | |||
| 3192 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_3192_5 | binary | |
MD5:29B1745E465A8BC3D4B8984B7FE0E36D | SHA256:891414EC318A8B972064CDD311E23036A7592326CBA452C91DB14F1E74F60618 | |||
| 3192 | makecab.exe | C:\Users\admin\Desktop\~adminGDI109.exe.RPT | text | |
MD5:87DD9EDC1259A69D3215E14BE7A0230F | SHA256:7C287796A33495D5CC4EFA36DCF9AC873DF7CD8AB4BCE001C0FDB5DC60C16491 | |||
| 3192 | makecab.exe | C:\Users\admin\AppData\Local\Temp\inf_3192_2 | text | |
MD5:CB492B7DF9B5C170D7C87527940EFF3B | SHA256:DBA5166AD9DB9BA648C1032EBBD34DCD0D085B50023B839EF5C68CA1DB93A563 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
11
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 23.50.131.222:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 23.50.131.222:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |