| File name: | Microsoft_Excel.msi |
| Full analysis: | https://app.any.run/tasks/8ecc866c-4be0-478d-9d89-064ab029ee8d |
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2025, 17:18:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Default, Author: ScreenConnect Software, Keywords: Default, Comments: Default, Template: Intel;1033, Revision Number: {63F222AA-0C09-8B28-5ABB-E7221BC1F823}, Create Time/Date: Wed Dec 18 21:40:44 2024, Last Saved Time/Date: Wed Dec 18 21:40:44 2024, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.0.1701), Security: 2 |
| MD5: | 11DD50D77AE2C24C8331D15F6ABE97D6 |
| SHA1: | D5B2B79DF6158F66DAEDF570E5762A2359296FD1 |
| SHA256: | 1FD040C91B03F71D5A120F3C6B696DA441D8424BA6F874991F5E7F1B014BEB65 |
| SSDEEP: | 196608:mlpHh8xBXNw0lpHhKlpHh9lpHh1lpHh3lpHhKklpHhKYylpHhKY:WB8xcIBaBVBtBLBlB6B |
MALICIOUS
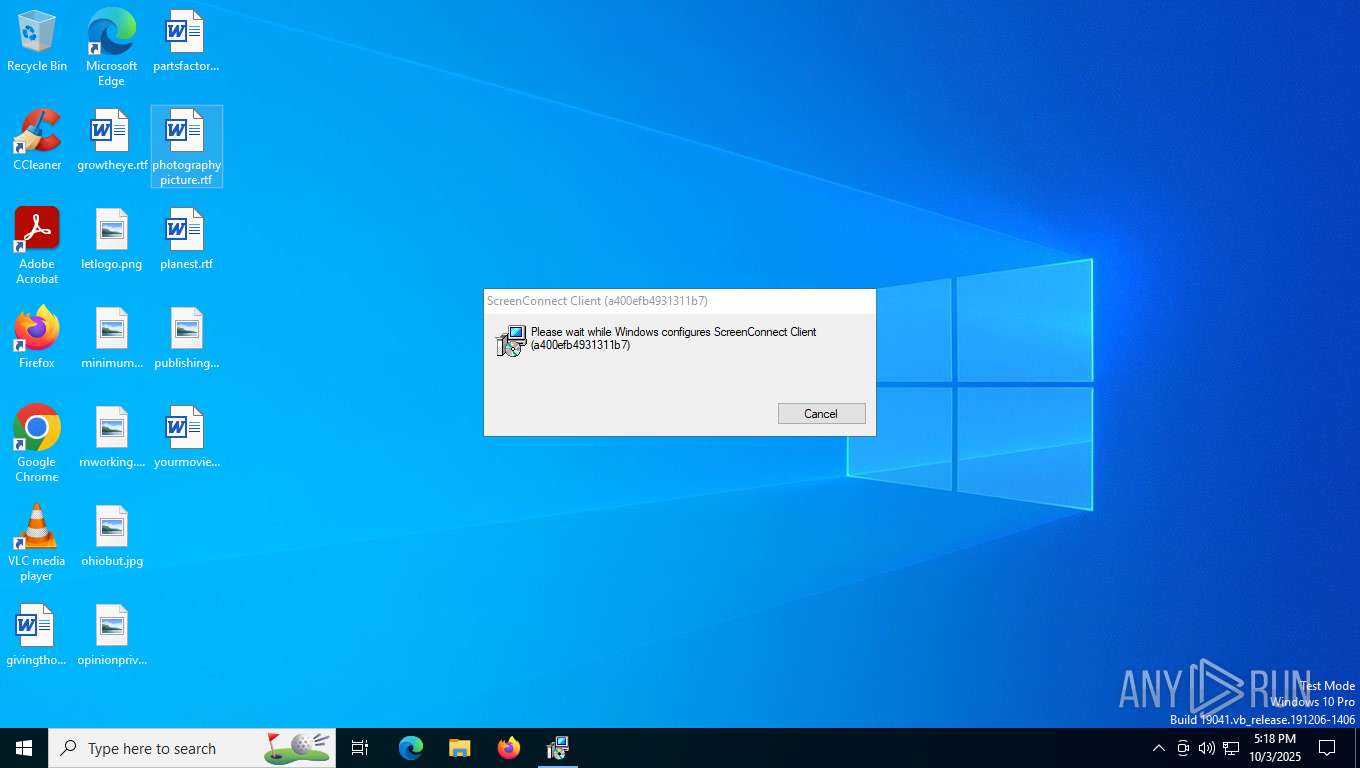
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 8476)
SUSPICIOUS
Executable content was dropped or overwritten
- rundll32.exe (PID: 7568)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3196)
The process creates files with name similar to system file names
- msiexec.exe (PID: 3196)
Screenconnect has been detected
- msiexec.exe (PID: 3196)
- ScreenConnect.ClientService.exe (PID: 8476)
- ScreenConnect.ClientService.exe (PID: 8476)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 8476)
Reads security settings of Internet Explorer
- ScreenConnect.ClientService.exe (PID: 8476)
- ScreenConnect.WindowsClient.exe (PID: 8536)
- ScreenConnect.WindowsClient.exe (PID: 8696)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 8476)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 3196)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 8476)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 8476)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 8476)
INFO
Checks proxy server information
- msiexec.exe (PID: 1924)
- BackgroundTransferHost.exe (PID: 8304)
- slui.exe (PID: 8388)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1924)
- BackgroundTransferHost.exe (PID: 9100)
- BackgroundTransferHost.exe (PID: 8304)
- BackgroundTransferHost.exe (PID: 4288)
- BackgroundTransferHost.exe (PID: 8912)
- BackgroundTransferHost.exe (PID: 9192)
An automatically generated document
- msiexec.exe (PID: 1924)
Reads the software policy settings
- msiexec.exe (PID: 1924)
- msiexec.exe (PID: 3196)
- BackgroundTransferHost.exe (PID: 8304)
Creates files or folders in the user directory
- msiexec.exe (PID: 1924)
- BackgroundTransferHost.exe (PID: 8304)
Checks supported languages
- msiexec.exe (PID: 5256)
- msiexec.exe (PID: 3196)
- msiexec.exe (PID: 8444)
- ScreenConnect.ClientService.exe (PID: 8476)
- msiexec.exe (PID: 8388)
- ScreenConnect.WindowsClient.exe (PID: 8696)
- ScreenConnect.WindowsClient.exe (PID: 8536)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1924)
- msiexec.exe (PID: 3196)
Reads the computer name
- msiexec.exe (PID: 3196)
- msiexec.exe (PID: 5256)
- msiexec.exe (PID: 8388)
- msiexec.exe (PID: 8444)
- ScreenConnect.ClientService.exe (PID: 8476)
- ScreenConnect.WindowsClient.exe (PID: 8696)
- ScreenConnect.WindowsClient.exe (PID: 8536)
CONNECTWISE has been detected
- msiexec.exe (PID: 1924)
- msiexec.exe (PID: 3196)
- ScreenConnect.ClientService.exe (PID: 8476)
- ScreenConnect.WindowsClient.exe (PID: 8696)
- ScreenConnect.WindowsClient.exe (PID: 8536)
Create files in a temporary directory
- rundll32.exe (PID: 7568)
Manages system restore points
- SrTasks.exe (PID: 8224)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3196)
- ScreenConnect.ClientService.exe (PID: 8476)
- ScreenConnect.WindowsClient.exe (PID: 8536)
- ScreenConnect.WindowsClient.exe (PID: 8696)
SCREENCONNECT has been detected
- msiexec.exe (PID: 3196)
- ScreenConnect.ClientService.exe (PID: 8476)
Creates a software uninstall entry
- msiexec.exe (PID: 3196)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 8696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Default |
| Author: | ScreenConnect Software |
| Keywords: | Default |
| Comments: | Default |
| Template: | Intel;1033 |
| RevisionNumber: | {63F222AA-0C09-8B28-5ABB-E7221BC1F823} |
| CreateDate: | 2024:12:18 21:40:44 |
| ModifyDate: | 2024:12:18 21:40:44 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.0.1701) |
| Security: | Read-only recommended |
Total processes
190
Monitored processes
18
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1924 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\Microsoft_Excel.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3196 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4288 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5256 | C:\Windows\syswow64\MsiExec.exe -Embedding 316A66C65C4DB6ABE02F15AD906BC4D8 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7568 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI186A.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1513718 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8224 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:14 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8304 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8388 | C:\Windows\syswow64\MsiExec.exe -Embedding E58EAA946776856ABAE3B1C2715AECC5 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 327
Read events
14 169
Write events
150
Delete events
8
Modification events
| (PID) Process: | (3196) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000E5A7EBCD8934DC017C0C0000B0020000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3196) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000E5A7EBCD8934DC017C0C0000B0020000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3196) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000E5A7EBCD8934DC017C0C0000B0020000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3196) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000836CF0CD8934DC017C0C0000B0020000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3196) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000B045E9CD8934DC017C0C0000B0020000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3196) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000B045E9CD8934DC017C0C0000B0020000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3196) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000006B0AEECD8934DC017C0C0000B0020000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3196) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 14 | |||
| (PID) Process: | (3196) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E7CEF2CD8934DC017C0C000098060000E80300000100000000000000000000003D04159BF5E13147840FC0680F7EE23C00000000000000000000000000000000 | |||
| (PID) Process: | (3196) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4800000000000000CBDAA0CE8934DC017C0C000098060000E80300000000000000000000000000003D04159BF5E13147840FC0680F7EE23C00000000000000000000000000000000 | |||
Executable files
19
Suspicious files
30
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3196 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3196 | msiexec.exe | C:\Windows\Installer\1743bf.msi | — | |
MD5:— | SHA256:— | |||
| 1924 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\FE17BEC2A573BC9AE36869D0274FFA19_6DA81F04C5F9EAD2CD0268808FCE61E1 | binary | |
MD5:AE55914DCC4D6E261E241FEE21982A86 | SHA256:6401890CBB268D4CB64F227FCC44B76A30BCB49085C04E8DBA3BB5733607AAE1 | |||
| 7568 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI186A.tmp-\Microsoft.Deployment.WindowsInstaller.Package.dll | executable | |
MD5:A921A2B83B98F02D003D9139FA6BA3D8 | SHA256:548C551F6EBC5D829158A1E9AD1948D301D7C921906C3D8D6B6D69925FC624A1 | |||
| 1924 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\248DDD9FCF61002E219645695E3FFC98_EB6660ADA54D907AB1364F711C276089 | binary | |
MD5:AB92718C82FAA98F03AF3AB3C121132F | SHA256:F0771DFAD7B37403C947588E9CE47AECFC86913F977DBD1BF3FD978334324207 | |||
| 7568 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI186A.tmp-\CustomAction.config | xml | |
MD5:6F52EBEA639FD7CEFCA18D9E5272463E | SHA256:7027B69AB6EBC9F3F7D2F6C800793FDE2A057B76010D8CFD831CF440371B2B23 | |||
| 7568 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI186A.tmp-\ScreenConnect.Core.dll | executable | |
MD5:665A8C1E8BA78F0953BC87F0521905CC | SHA256:3D016BEF20B3D2425939BFE32BEA6F8C08649399D8BE5A83EB461BC0E0C914EB | |||
| 3196 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:D9A290ABD64971859DC59F3E1DE648F6 | SHA256:0B8127714C4964C74A65F5096DA11335124A76D12B1D542D5026A9CE8E181CBC | |||
| 7568 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI186A.tmp-\Microsoft.Deployment.Compression.Cab.dll | executable | |
MD5:77BE59B3DDEF06F08CAA53F0911608A5 | SHA256:9D32032109FFC217B7DC49390BD01A067A49883843459356EBFB4D29BA696BF8 | |||
| 3196 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{9b15043d-e1f5-4731-840f-c0680f7ee23c}_OnDiskSnapshotProp | binary | |
MD5:D9A290ABD64971859DC59F3E1DE648F6 | SHA256:0B8127714C4964C74A65F5096DA11335124A76D12B1D542D5026A9CE8E181CBC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
38
DNS requests
22
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1924 | msiexec.exe | GET | 200 | 18.173.205.57:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQg3SSkKA74hABkhmlBtJTz8w3hlAQU%2BWC71OPVNPa49QaAJadz20ZpqJ4CEEJLalPOx2YUHCpjsaUcQQQ%3D | unknown | — | — | whitelisted |
4620 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8180 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7804 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4620 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8304 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8044 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1924 | msiexec.exe | GET | 200 | 18.173.205.57:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSoEwb5tith0jIBy9frSyNGB1lsAAQUNr1J%2FzEs669qQP6ZwBbtuvxI3V8CEHMBvXddPk3GU5sheiw8sTc%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3432 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6016 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5224 | SearchApp.exe | 92.123.104.58:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1924 | msiexec.exe | 18.173.205.57:80 | ocsps.ssl.com | — | US | whitelisted |
4620 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4620 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3464 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
8180 | backgroundTaskHost.exe | 92.123.104.58:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsps.ssl.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
listen.onyxaquarius.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2428 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2428 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (onyxaquarius .top) |
8476 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |