| File name: | 执行查看.msi |
| Full analysis: | https://app.any.run/tasks/0b9d749c-67b1-4020-8b29-caf717c626f9 |
| Verdict: | Malicious activity |
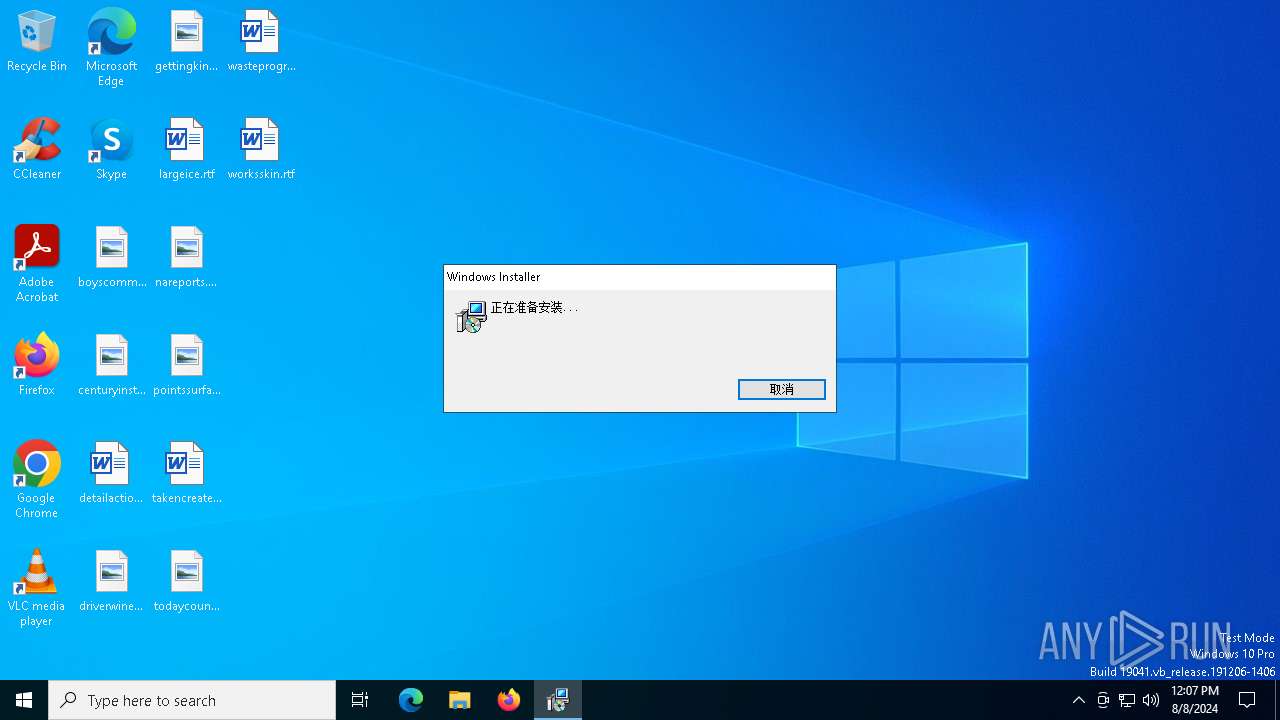
| Analysis date: | August 08, 2024, 12:07:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Title: Installation Database, Keywords: Installer, MSI, Database, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Dec 11 11:47:44 2009, Number of Pages: 200, Security: 0, Code page: 936, Revision Number: {816C418A-7A64-4F9B-977B-F070B2EFBD7D}, Number of Words: 2, Name of Creating Application: Advanced Installer 11.0 build 55831, Template: ;2052, Comments: Installer |
| MD5: | A778E5DAD14EBF83F19F73EB08CF8151 |
| SHA1: | 4FF8724B7DDC4ECA00B8802DBDE9582E9ABC72DD |
| SHA256: | 1FBF17C276222A2D710AEFFA08C811FB854E9304D658AA74126F32B05AF1E688 |
| SSDEEP: | 49152:fYwbkrMi3euZ3OzbsM5y/r6h4Wl2k3N857U0BDYyGzDXtkFeaY4M+QIj1n8h9//7:cMi3N3OX3yzw2k3N8lGzzKFC4M+QM1nA |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 6836)
- msiexec.exe (PID: 6932)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6932)
Executes as Windows Service
- VSSVC.exe (PID: 6988)
Reads security settings of Internet Explorer
- MSIABDF.tmp (PID: 7748)
Reads the date of Windows installation
- MSIABDF.tmp (PID: 7748)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6932)
Connects to unusual port
- shost.exe (PID: 7848)
INFO
Executable content was dropped or overwritten
- msiexec.exe (PID: 6932)
Checks supported languages
- msiexec.exe (PID: 6932)
- MSIABDF.tmp (PID: 7748)
- msiexec.exe (PID: 7696)
- shost.exe (PID: 7848)
Reads the computer name
- msiexec.exe (PID: 6932)
- MSIABDF.tmp (PID: 7748)
- msiexec.exe (PID: 7696)
- shost.exe (PID: 7848)
Starts application with an unusual extension
- msiexec.exe (PID: 6932)
Process checks computer location settings
- MSIABDF.tmp (PID: 7748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Title: | Installation Database |
|---|---|
| Keywords: | Installer, MSI, Database |
| LastPrinted: | 2009:12:11 11:47:44 |
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2009:12:11 11:47:44 |
| Pages: | 200 |
| Security: | None |
| CodePage: | Windows Simplified Chinese (PRC, Singapore) |
| RevisionNumber: | {816C418A-7A64-4F9B-977B-F070B2EFBD7D} |
| Words: | 2 |
| Subject: | ????Ӧ?ó??? |
| Author: | ???Ĺ?˾ |
| LastModifiedBy: | - |
| Software: | Advanced Installer 11.0 build 55831 |
| Template: | ;2052 |
| Comments: | ?? Installer ???ݿ??????˰?װ ????Ӧ?ó??? ?????????????ݡ? |
Total processes
141
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6836 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\执行查看.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6932 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6988 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7568 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7580 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7696 | C:\Windows\syswow64\MsiExec.exe -Embedding 5C737013C93333C06EACAD804AB30BC6 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7748 | "C:\WINDOWS\Installer\MSIABDF.tmp" /RunAsAdmin "C:\Program Files (x86)\shost.exe" | C:\Windows\Installer\MSIABDF.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7848 | "C:\Program Files (x86)\shost.exe" | C:\Program Files (x86)\shost.exe | MSIABDF.tmp | ||||||||||||
User: admin Company: setup.exe: <公司名> Integrity Level: HIGH Description: setup.exe: <文件说明> Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
5 861
Read events
5 643
Write events
199
Delete events
19
Modification events
| (PID) Process: | (6932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000BFBF1D838BE9DA01141B00003C1B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000BFBF1D838BE9DA01141B00003C1B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000011686C838BE9DA01141B00003C1B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000011686C838BE9DA01141B00003C1B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000ECCB6E838BE9DA01141B00003C1B0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000399373838BE9DA01141B00003C1B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000005744E1838BE9DA01141B00003C1B0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E9FCE5838BE9DA01141B0000F41B0000E8030000010000000000000000000000AB6A5FA6620A9844831377BEF61B484500000000000000000000000000000000 | |||
| (PID) Process: | (6988) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000002AE2F1838BE9DA014C1B00003C180000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
5
Suspicious files
15
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6932 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6932 | msiexec.exe | C:\Windows\Installer\MSIA92C.tmp | executable | |
MD5:9A4968FE67C177850163DEAFEC64D0A6 | SHA256:441D8C2EE1B434E21B7A8547F3C9E8B5B654ED7C790372D7870C8071D3A9B6AB | |||
| 6932 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{a65f6aab-0a62-4498-8313-77bef61b4845}_OnDiskSnapshotProp | binary | |
MD5:045C9556904532887FBE005FD25C6A42 | SHA256:BB7D0B201578412CC6E507002AFA76FC8424A6CADE23B5B9269053177ABA8BA2 | |||
| 6932 | msiexec.exe | C:\Config.Msi\ea640.rbs | binary | |
MD5:2D929E2269E0E5C343A2617E9E0C6311 | SHA256:A29DEFF3BBEF9C22D41BE1E2E0DDAE4845F6866FA9F3023EDB5352EB5383C270 | |||
| 6932 | msiexec.exe | C:\Windows\Installer\SourceHash{AD4E1403-2261-400A-A0E6-9651346CE519} | binary | |
MD5:37B2BA73B12699E3C0BA14186AF02547 | SHA256:C980A17C27E3B88B4214E289D1FC1CD6D4E6EAF4D6EC3B11EA7120A72F64CA3F | |||
| 6932 | msiexec.exe | C:\Windows\Temp\~DFE790DF2695EE9A03.TMP | binary | |
MD5:54597C0665289BC88B4AC62FDB0B32AD | SHA256:3CDCB36648E14D9957F4F3E55E7CEDDBE4241450A115B200CA76040B6A0924F3 | |||
| 6932 | msiexec.exe | C:\Windows\Installer\MSIABDF.tmp | executable | |
MD5:0979CEA9804FBCD758F60649F29D01EA | SHA256:E5DF917742012911D358DCDE17A38FF4999020557FEE4F1BBFFD1DB04994E1CF | |||
| 6932 | msiexec.exe | C:\Windows\Temp\~DFCDBFBAF88D1A9DB8.TMP | binary | |
MD5:5706933078968B94B1651666DA8B1E93 | SHA256:088BA9E97DB4D095469B67DCC8BEFC6AA098CFFF3D4587B5E8EDBA5BC0340BEE | |||
| 6932 | msiexec.exe | C:\Windows\Temp\~DF44E569113DB32925.TMP | binary | |
MD5:54597C0665289BC88B4AC62FDB0B32AD | SHA256:3CDCB36648E14D9957F4F3E55E7CEDDBE4241450A115B200CA76040B6A0924F3 | |||
| 6932 | msiexec.exe | C:\Windows\Temp\~DF2B43679B9C09146A.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
52
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6292 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6320 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1420 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 92.123.104.59:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 92.123.104.59:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
go.microsoft.com |
| whitelisted |