| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/834a1e23-de79-4ea7-abd3-5c3095be2bca |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2024, 16:42:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2D707EE1D13704DDE2546D66C4622C54 |
| SHA1: | 3F7FC43BFD22C0A1F4565869BC61D21A1BEB2235 |
| SHA256: | 1FB68E812BEB3966A8E534C6F0314A24A859A3B3ADE3FDD928827DDDA97B1D0B |
| SSDEEP: | 98304:Amy/4bk8c/7F2g1s7CWphAnW3JHzTT9oa4cr3qYAKhBMQLWCkhgawSDZHTFMa5M5:ws+jhncK+e2oI2o |
MALICIOUS
No malicious indicators.SUSPICIOUS
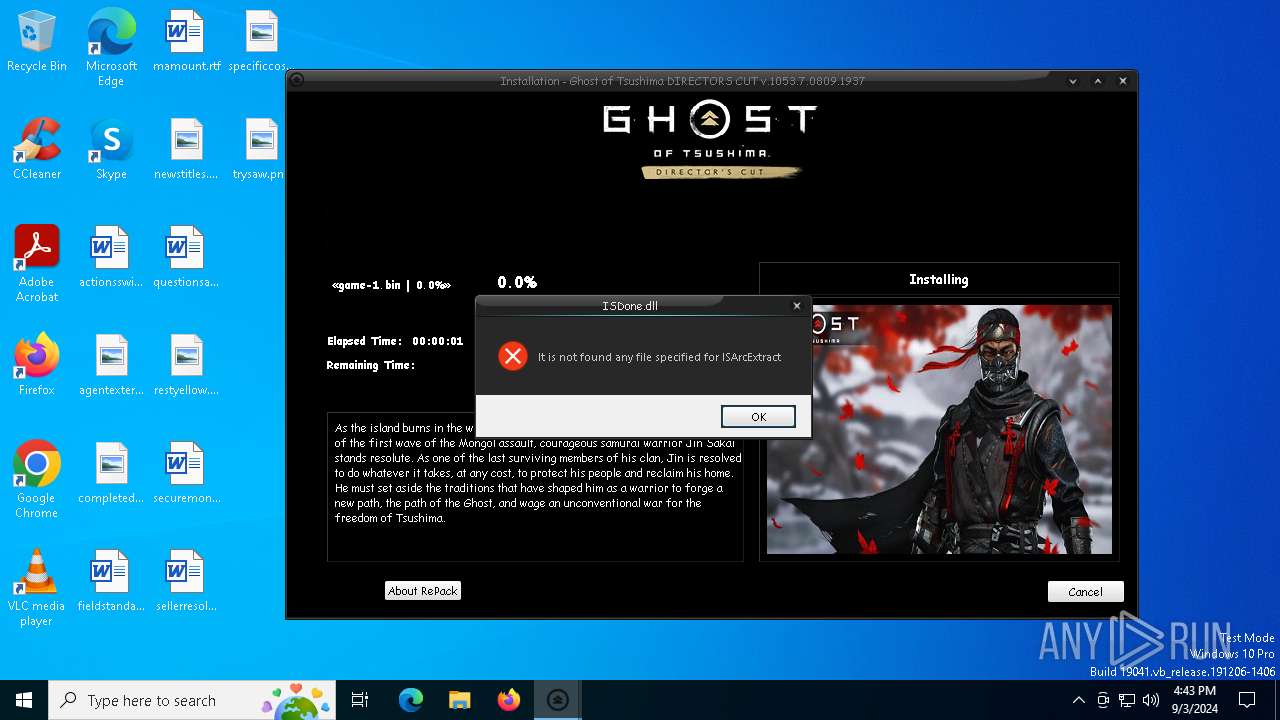
Process drops legitimate windows executable
- Setup.tmp (PID: 1156)
- _iu14D2N.tmp (PID: 2096)
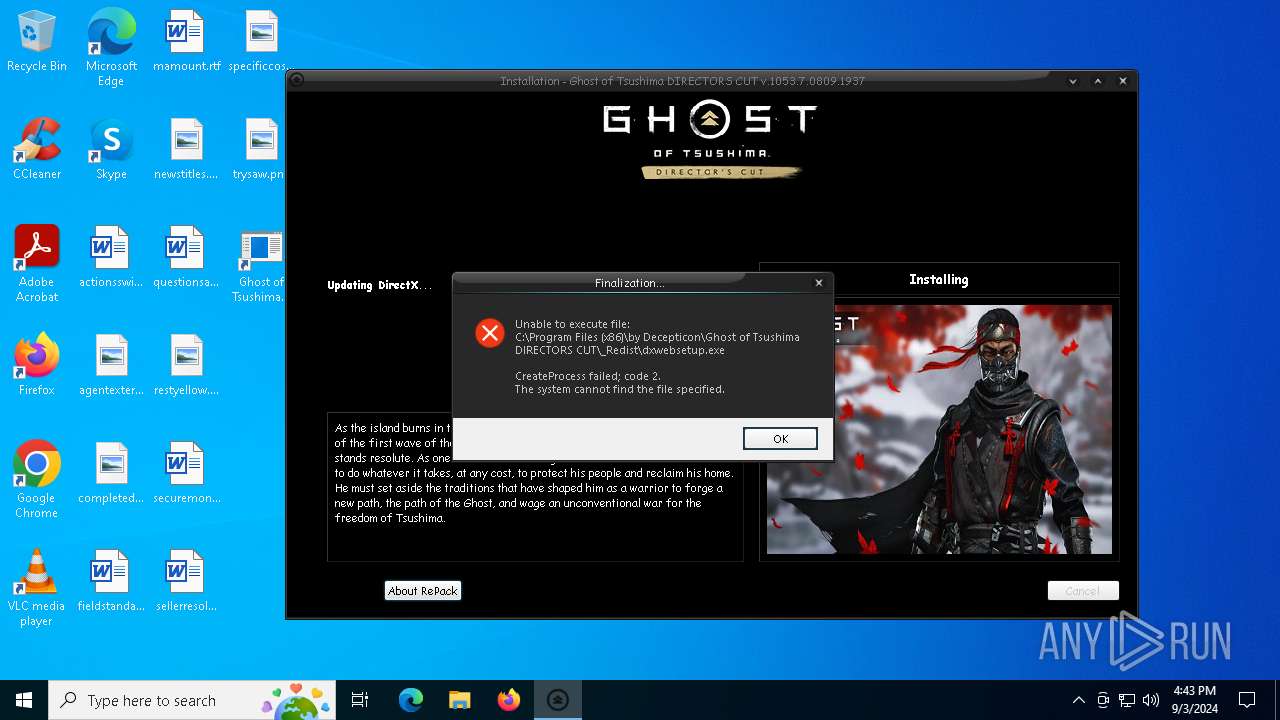
Executing commands from a ".bat" file
- Setup.tmp (PID: 1156)
Reads the Windows owner or organization settings
- Setup.tmp (PID: 1156)
- _iu14D2N.tmp (PID: 2096)
Executable content was dropped or overwritten
- unins000.exe (PID: 5220)
- Setup.exe (PID: 5184)
- Setup.tmp (PID: 1156)
- _iu14D2N.tmp (PID: 2096)
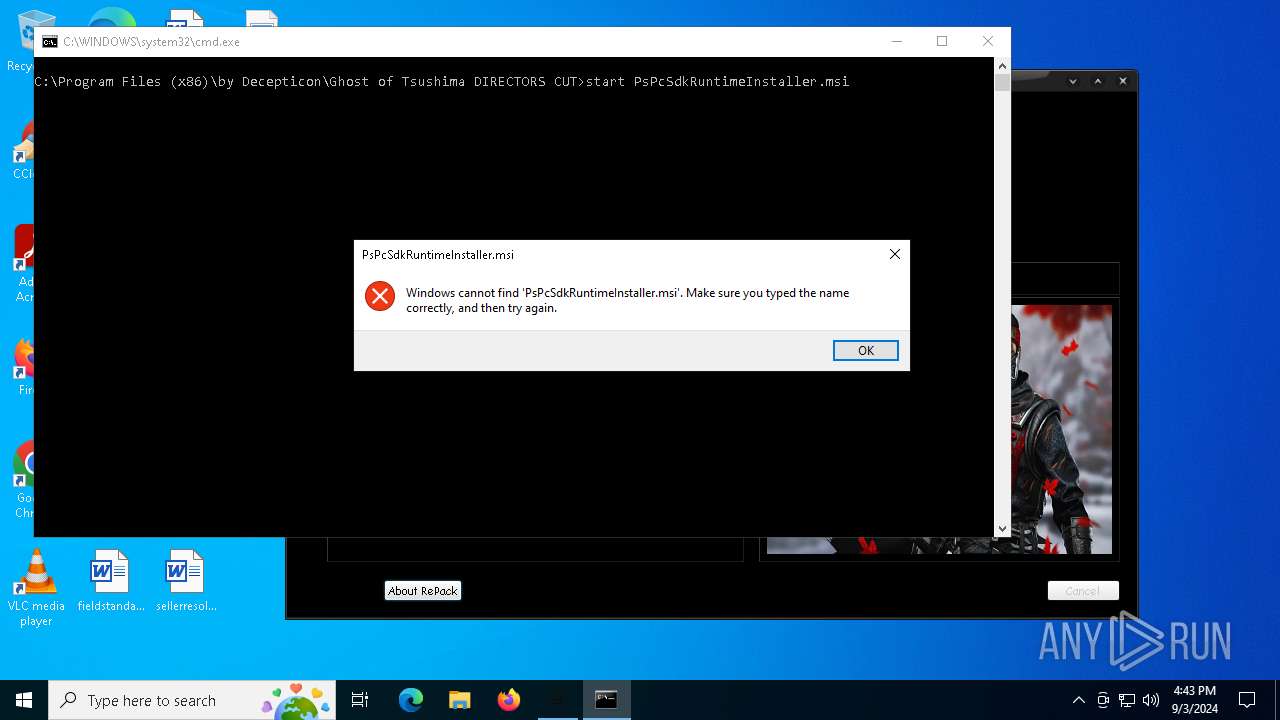
Starts CMD.EXE for commands execution
- Setup.tmp (PID: 1156)
Uses TASKKILL.EXE to kill process
- Setup.tmp (PID: 1156)
There is functionality for taking screenshot (YARA)
- Setup.tmp (PID: 1156)
Starts application with an unusual extension
- unins000.exe (PID: 5220)
Reads the date of Windows installation
- _iu14D2N.tmp (PID: 2096)
Starts itself from another location
- unins000.exe (PID: 5220)
INFO
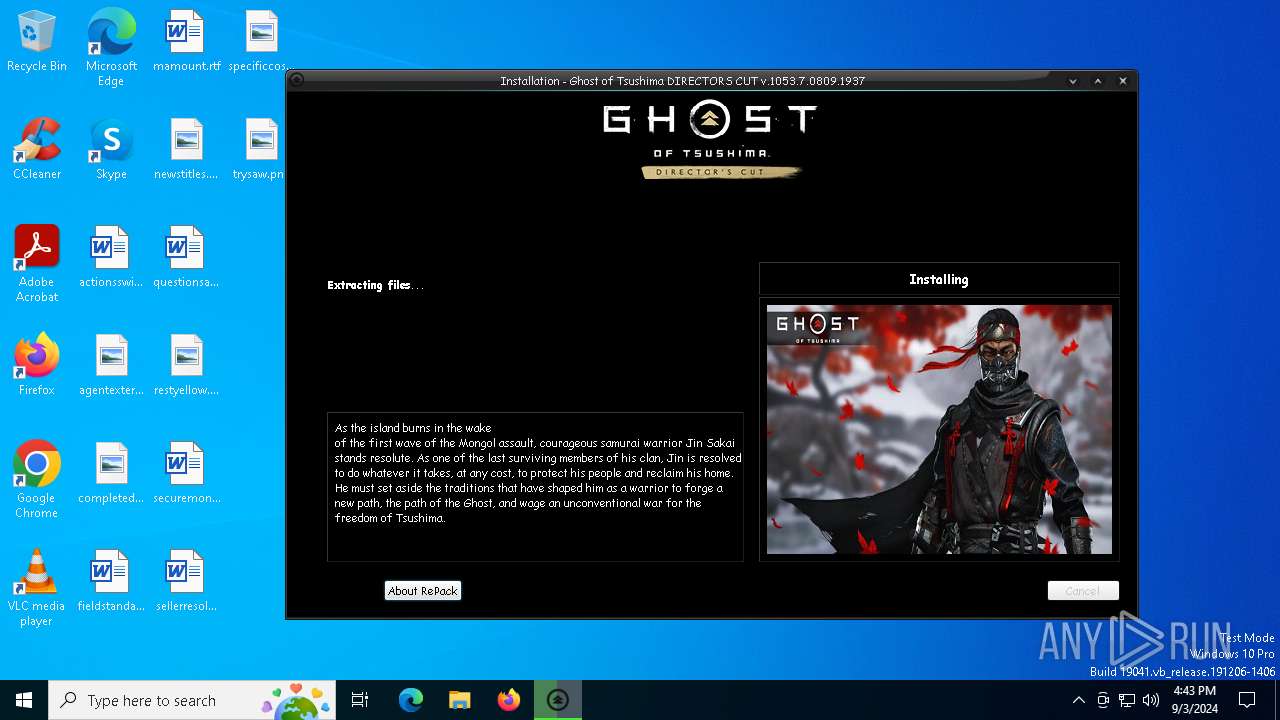
Creates files in the program directory
- Setup.tmp (PID: 1156)
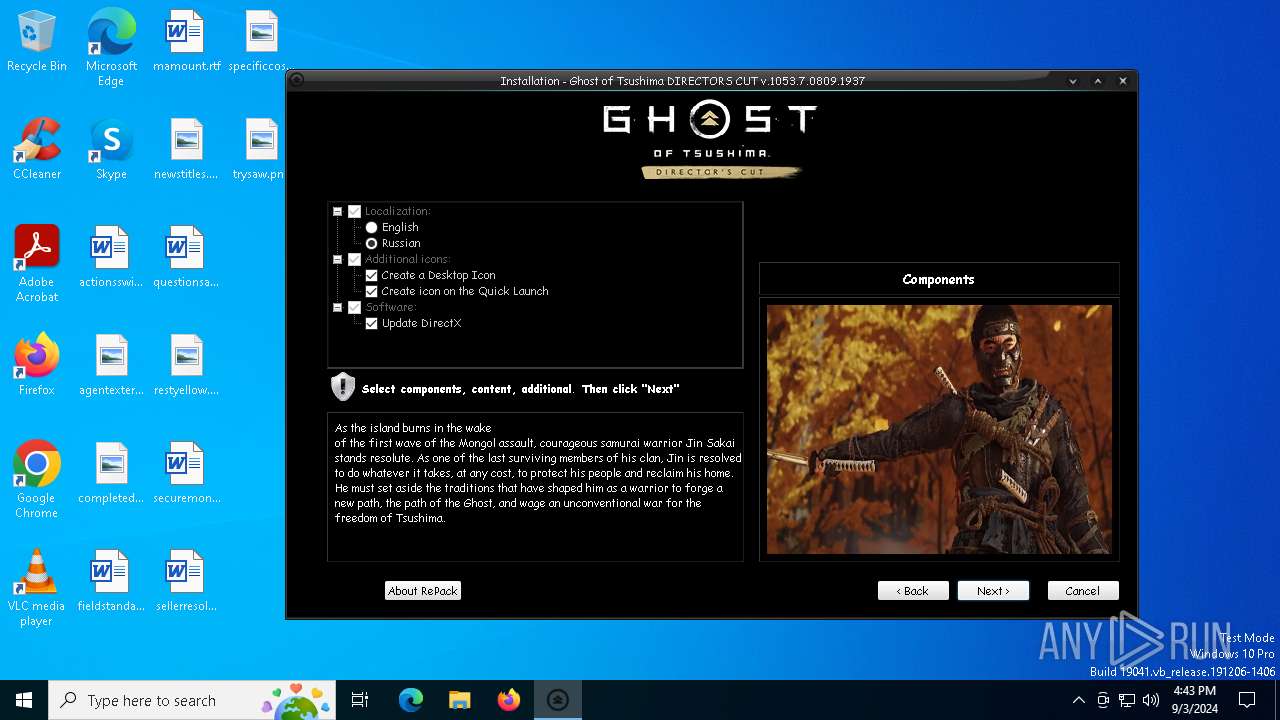
Checks supported languages
- Setup.exe (PID: 5184)
- unins000.exe (PID: 5220)
- Setup.tmp (PID: 1156)
- _iu14D2N.tmp (PID: 2096)
Reads the computer name
- Setup.tmp (PID: 1156)
- unins000.exe (PID: 5220)
- _iu14D2N.tmp (PID: 2096)
Create files in a temporary directory
- unins000.exe (PID: 5220)
- Setup.exe (PID: 5184)
- Setup.tmp (PID: 1156)
- _iu14D2N.tmp (PID: 2096)
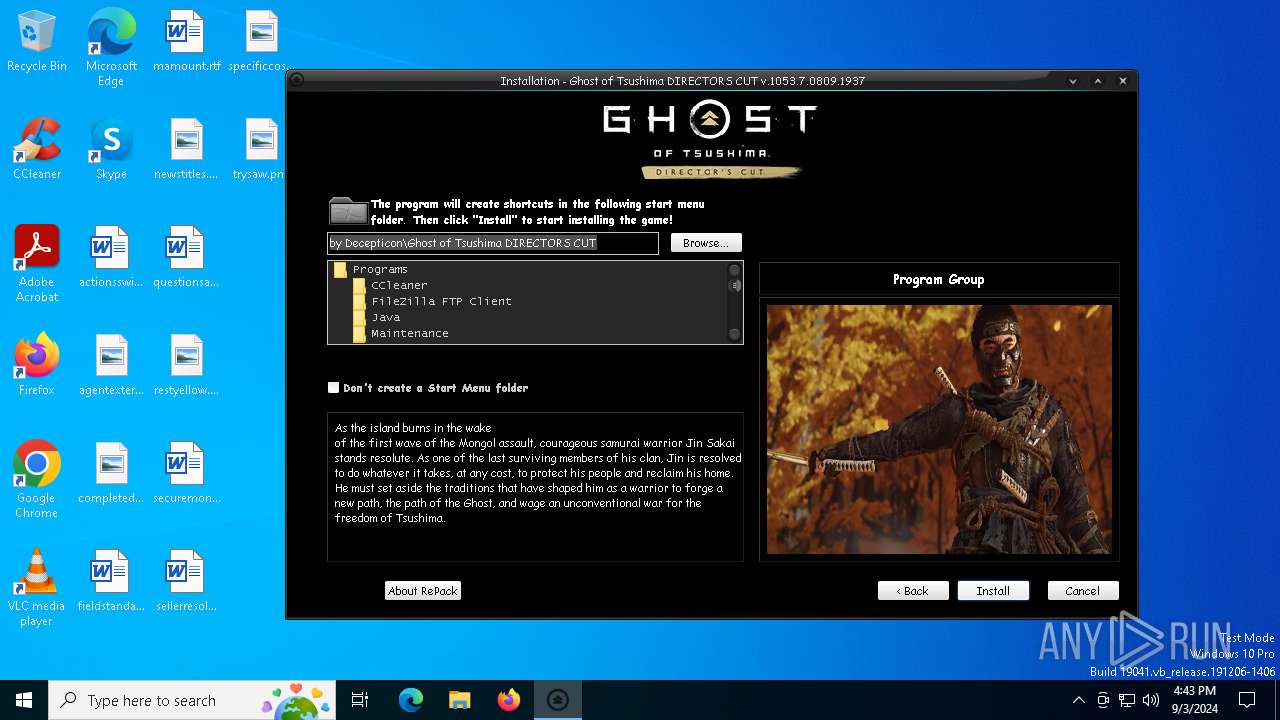
Creates a software uninstall entry
- Setup.tmp (PID: 1156)
UPX packer has been detected
- Setup.tmp (PID: 1156)
Process checks computer location settings
- _iu14D2N.tmp (PID: 2096)
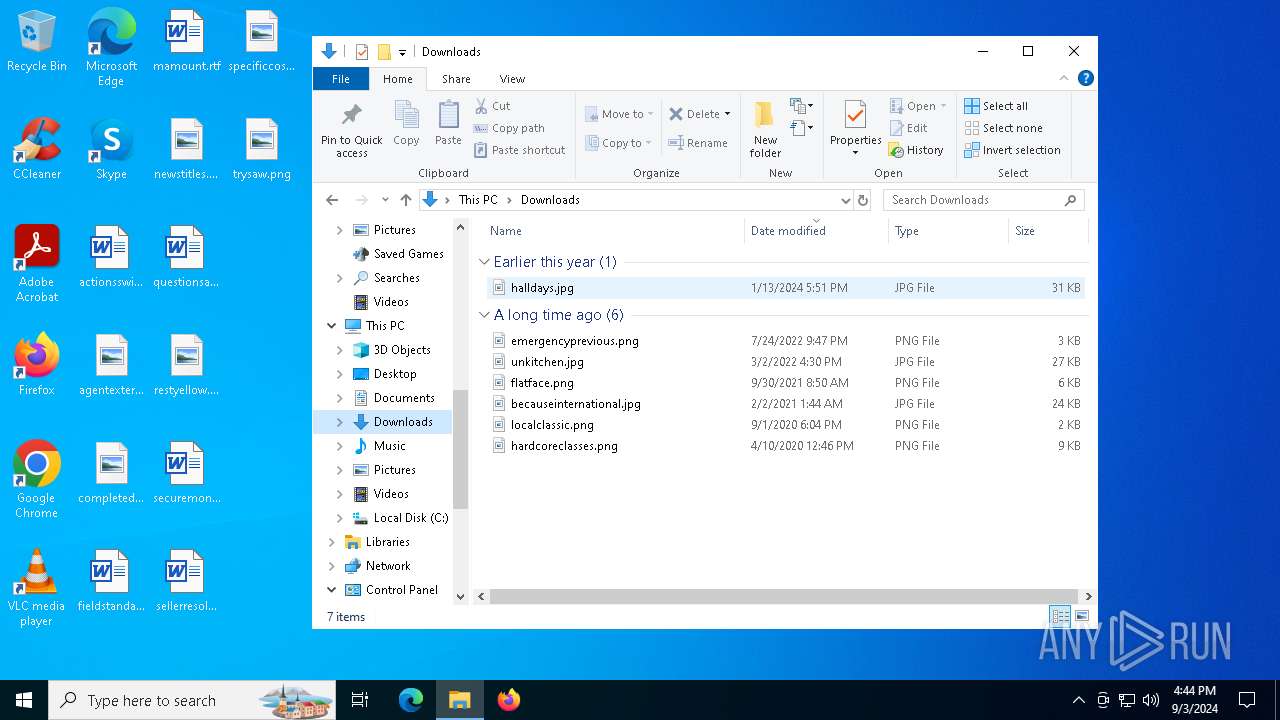
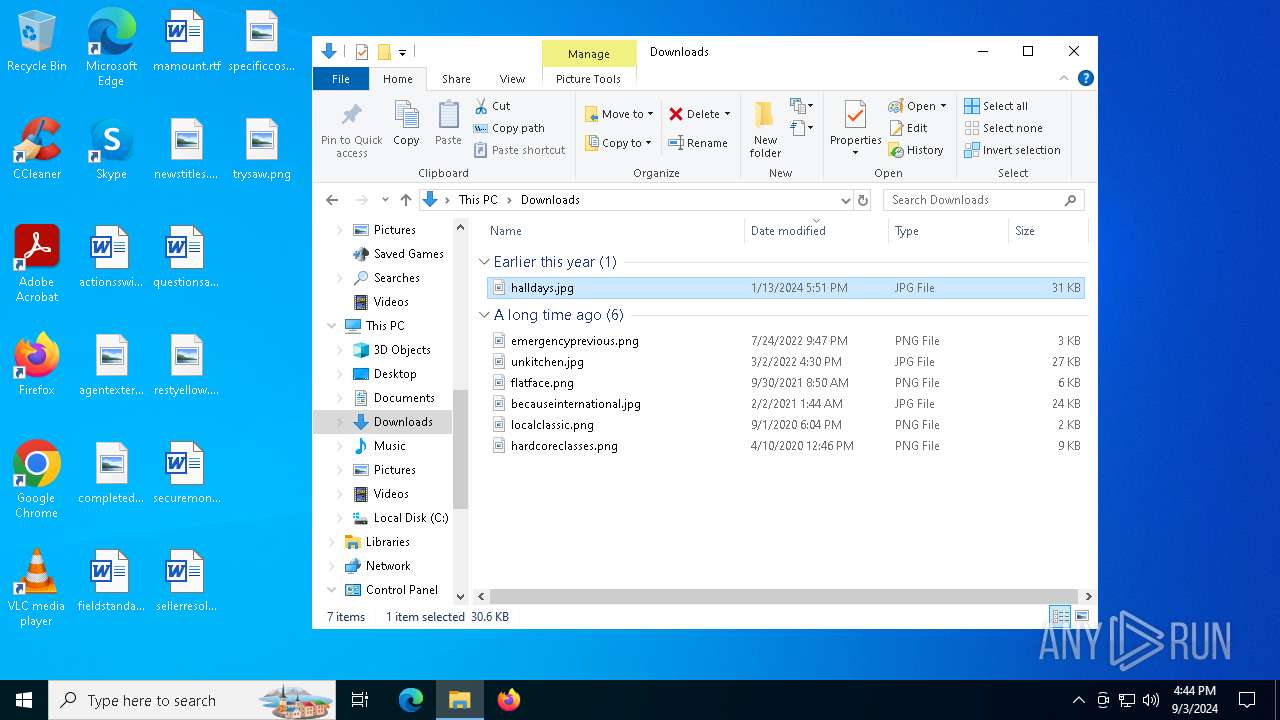
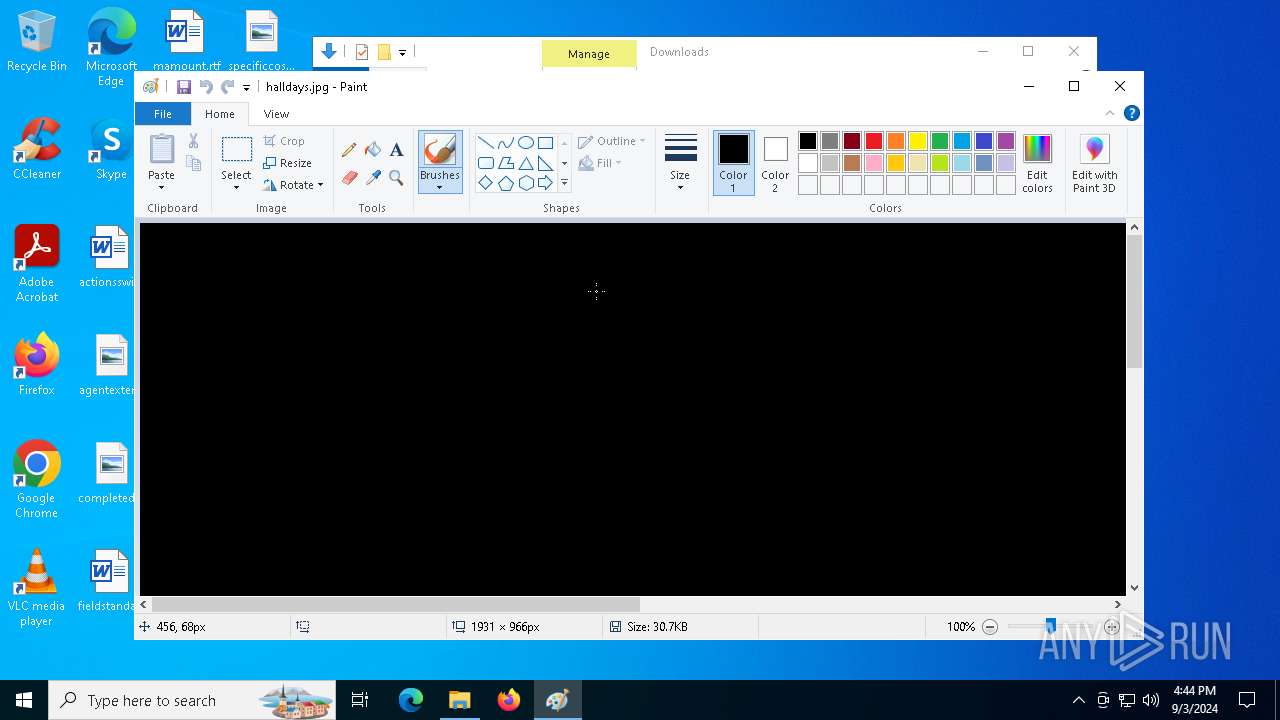
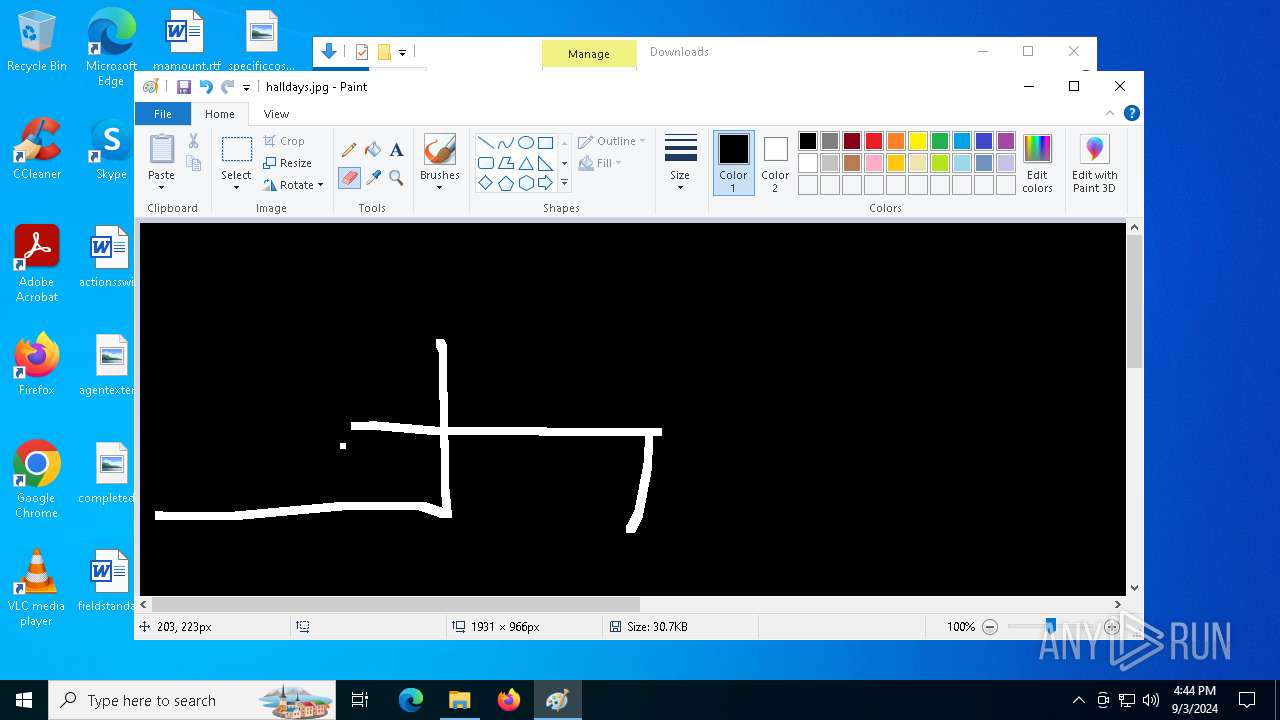
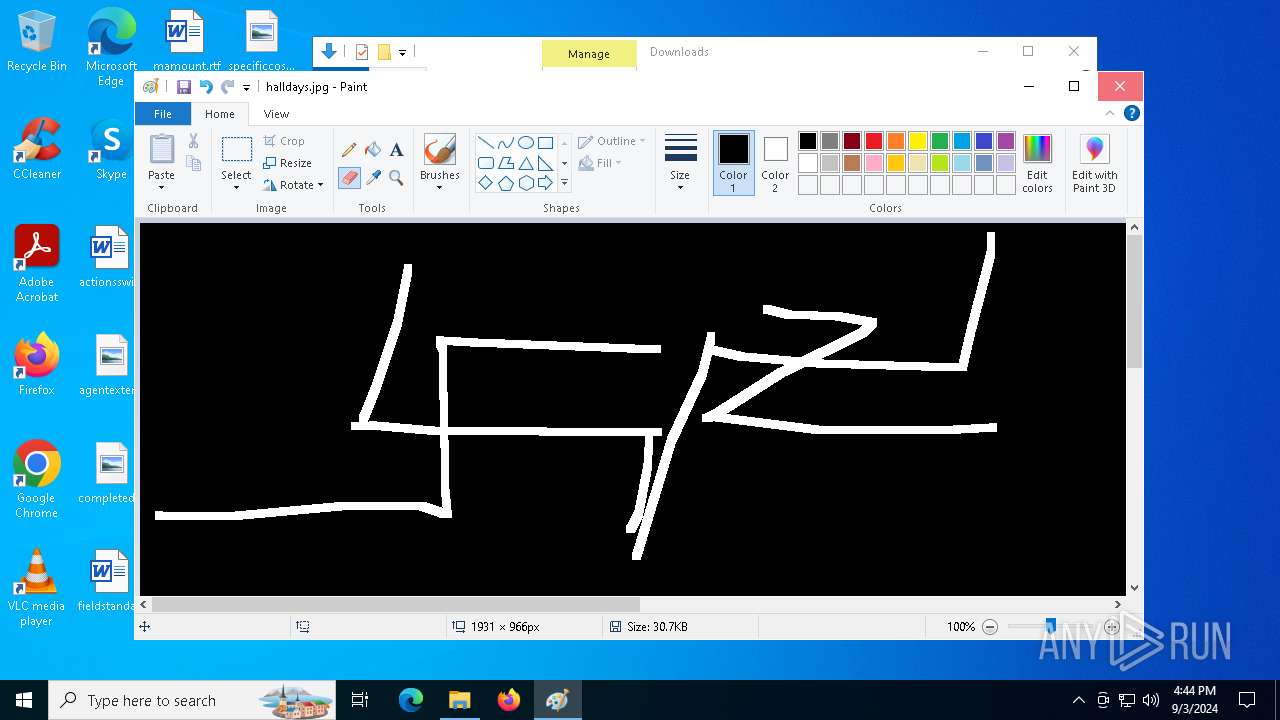
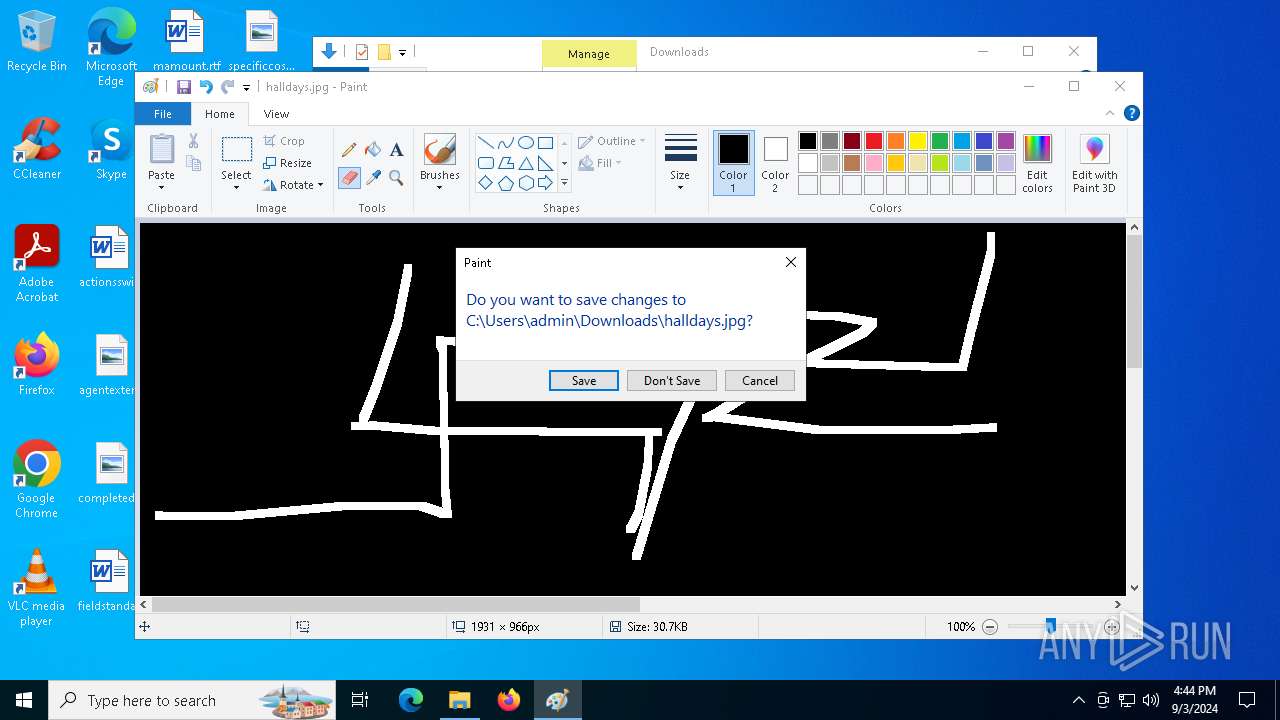
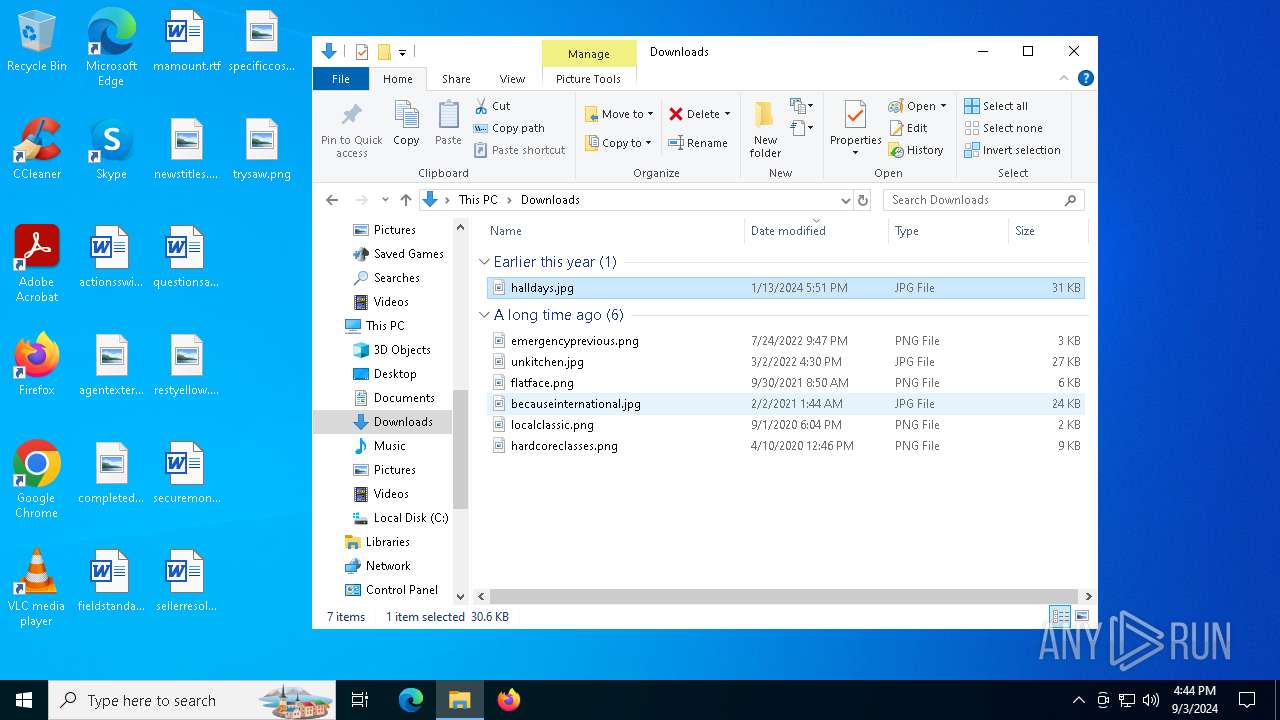
Manual execution by a user
- mspaint.exe (PID: 2724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (56.3) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (13.9) |
| .exe | | | Win32 EXE Yoda's Crypter (13.6) |
| .exe | | | Win32 Executable Delphi generic (7.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 45568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c14 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
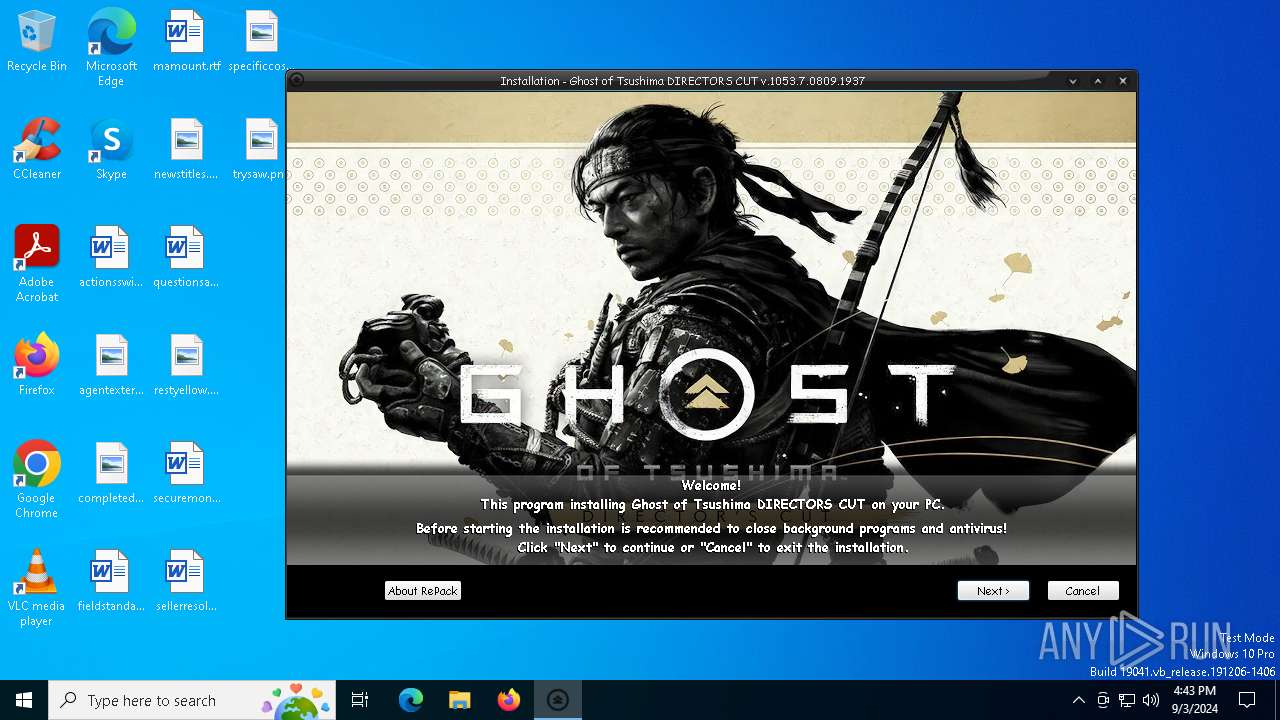
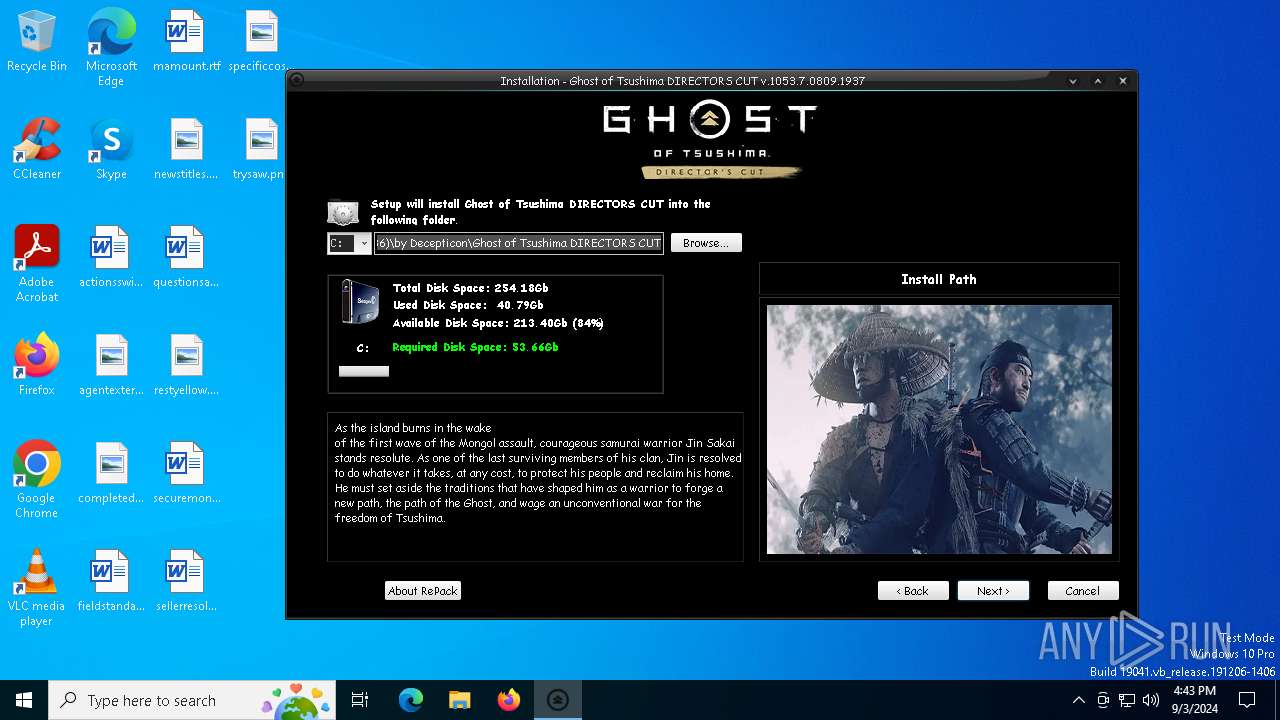
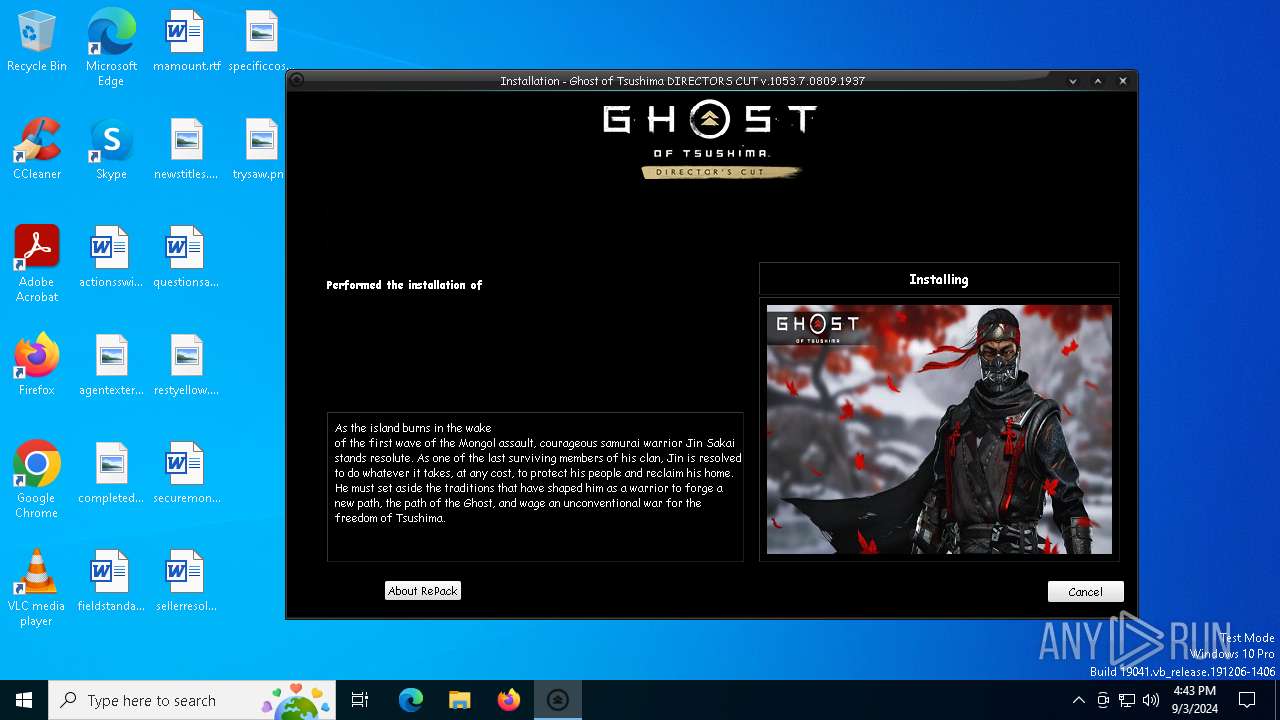
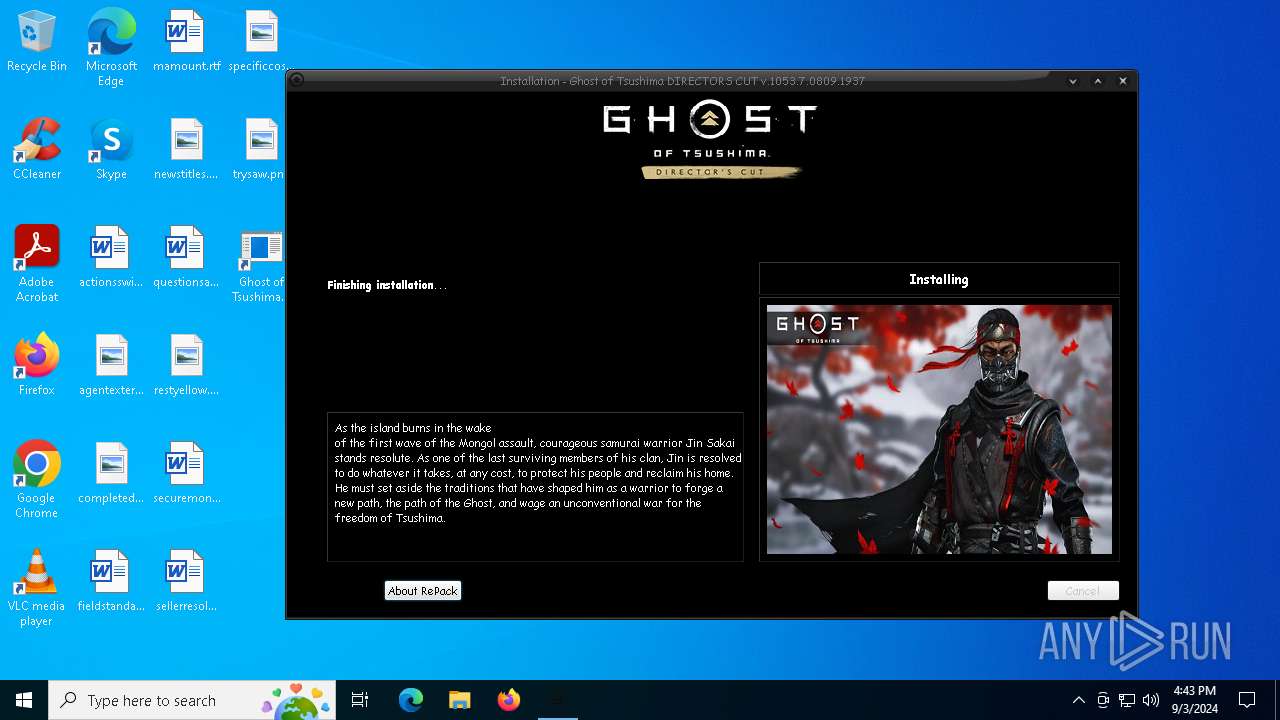
| CompanyName: | Decepticon |
| FileDescription: | Ghost of Tsushima DIRECTORS CUT Setup |
| FileVersion: | |
| LegalCopyright: | Decepticon |
| ProductName: | Ghost of Tsushima DIRECTORS CUT |
| ProductVersion: | v.1053.7.0809.1937 |
Total processes
145
Monitored processes
19
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | "C:\WINDOWS\system32\taskkill.exe" /F /IM bitcomet.exe | C:\Windows\SysWOW64\taskkill.exe | — | Setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | "C:\Users\admin\AppData\Local\Temp\is-MJJ6I.tmp\Setup.tmp" /SL5="$D01E4,3503117,84480,C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\is-MJJ6I.tmp\Setup.tmp | Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1744 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1940 | "C:\WINDOWS\system32\taskkill.exe" /F /IM utorrent.exe | C:\Windows\SysWOW64\taskkill.exe | — | Setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Program Files (x86)\by Decepticon\Ghost of Tsushima DIRECTORS CUT\Uninstall\unins000.exe" /FIRSTPHASEWND=$7039C /VERYSILENT | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
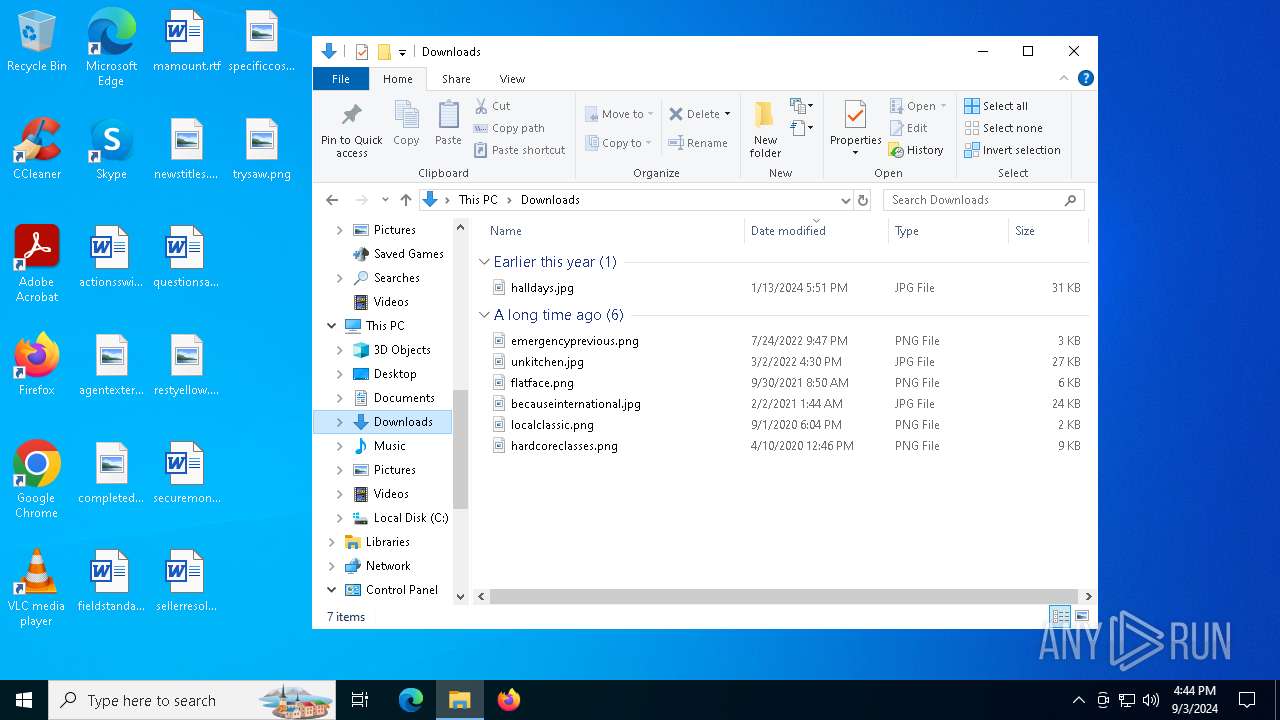
| 2724 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Downloads\halldays.jpg" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3384 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3980 | "C:\WINDOWS\system32\cmd.exe" /C ""C:\Program Files (x86)\by Decepticon\Ghost of Tsushima DIRECTORS CUT\Run.bat"" | C:\Windows\SysWOW64\cmd.exe | — | Setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4760 | "C:\WINDOWS\system32\taskkill.exe" /F /IM bittorrent.exe | C:\Windows\SysWOW64\taskkill.exe | — | Setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 940
Read events
7 886
Write events
50
Delete events
4
Modification events
| (PID) Process: | (1156) Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Program Files (x86)\by Decepticon\Ghost of Tsushima DIRECTORS CUT\GhostOfTsushima.exe |
Value: HIGHDPIAWARE RUNASADMIN | |||
| (PID) Process: | (1156) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Ghost of Tsushima DIRECTORS CUT_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.4.3.ee1 (a) | |||
| (PID) Process: | (1156) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Ghost of Tsushima DIRECTORS CUT_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\by Decepticon\Ghost of Tsushima DIRECTORS CUT | |||
| (PID) Process: | (1156) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Ghost of Tsushima DIRECTORS CUT_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\by Decepticon\Ghost of Tsushima DIRECTORS CUT\ | |||
| (PID) Process: | (1156) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Ghost of Tsushima DIRECTORS CUT_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: by Decepticon\Ghost of Tsushima DIRECTORS CUT | |||
| (PID) Process: | (1156) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Ghost of Tsushima DIRECTORS CUT_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (1156) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Ghost of Tsushima DIRECTORS CUT_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
| (PID) Process: | (1156) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Ghost of Tsushima DIRECTORS CUT_is1 |
| Operation: | write | Name: | DisplayName |
Value: Ghost of Tsushima DIRECTORS CUT | |||
| (PID) Process: | (1156) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Ghost of Tsushima DIRECTORS CUT_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\by Decepticon\Ghost of Tsushima DIRECTORS CUT\Uninstall\unins000.exe" | |||
| (PID) Process: | (1156) Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Ghost of Tsushima DIRECTORS CUT_is1 |
| Operation: | write | Name: | UninstallDataFile |
Value: C:\Program Files (x86)\by Decepticon\Ghost of Tsushima DIRECTORS CUT\Uninstall\unins000.dat | |||
Executable files
31
Suspicious files
5
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1156 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IRPJ.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 1156 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IRPJ.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 1156 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IRPJ.tmp\Hdd.bmp | image | |
MD5:54D727BA9B269A0D80F0DF61825A3013 | SHA256:B9933BA8FAA7C79227857DDDCCC1814BA867B57C1461937D183FE4308C832094 | |||
| 1156 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IRPJ.tmp\ISDone.dll | executable | |
MD5:49F8639B771AA32E1F26FC68EF176208 | SHA256:8A00A8394719E0CD02E81EB7F38E7AABAB30036A308D8987DE6192CAB1E31755 | |||
| 1156 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IRPJ.tmp\steam.cjstyles | executable | |
MD5:27696C3663181F06EC44FF2D709E36B9 | SHA256:FD6BCAF84E5D5917AAEE4205772E7D30F5A575DF4CE7E158224F782F6DA5F83A | |||
| 1156 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IRPJ.tmp\WizardForm.SelectGroupBitmapImage.bmp | image | |
MD5:011C11E5BDC6282F0844CBCB44861918 | SHA256:D0BD462D04DD5A4053505FF99C63D8571FDC0E95DBF92840C8408E940E4C20D0 | |||
| 1156 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IRPJ.tmp\isgsg.dll | executable | |
MD5:09974EAFF6DEFADDE38B1328754DBE09 | SHA256:9EEEF28D82FC4DB7D1269DFBC0EA282768CE5E2E4E4BDC867D80D6847468DCA7 | |||
| 1156 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IRPJ.tmp\WizardForm.WizardBitmapImage2.bmp | image | |
MD5:0D735F0439A51860E57288F61A837D24 | SHA256:AA99B04FAC61B532E15A720A3E2B16FDC3A9340DA504BE91FC8B9F5DCC5B0D23 | |||
| 1156 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IRPJ.tmp\logo.png | image | |
MD5:7319987699F2803BE0916D8D7E8A5680 | SHA256:0FA9710752130E5CCEBCF37FC24620C986788C6D2B9478011CBF82E515F46A68 | |||
| 1156 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IRPJ.tmp\Image_3.bmp | image | |
MD5:E95E255AF51F86AA932D6CC8A2BFF207 | SHA256:F92DB3739D022E9AE7084EFA377BF116BDE780CB51EC66BE264B50E88C8136F0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
43
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4392 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4392 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
448 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6232 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1776 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1776 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6232 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |