| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/cceaddbd-639c-4a46-9ca0-96b65371776d |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 10:08:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E4B02474909D19B9CEA5405861421CBD |
| SHA1: | 4A2AB944A84BA96C9AE3B9C7644166613B0ADD5E |
| SHA256: | 1FB31C96E9EBE00BE83AFDCA89FD578BA40F5A83930E855DB6C4686DD7EFD5A8 |
| SSDEEP: | 98304:EGsjOpph/Ufci65u5hDK/R624Q3RprHQaFB/wmdSCs20GcTvYBszDqjGdD2k3BKt:EGSrK/RHrVzwmUCs2nGQqzD8i2mBzed |
MALICIOUS
No malicious indicators.SUSPICIOUS
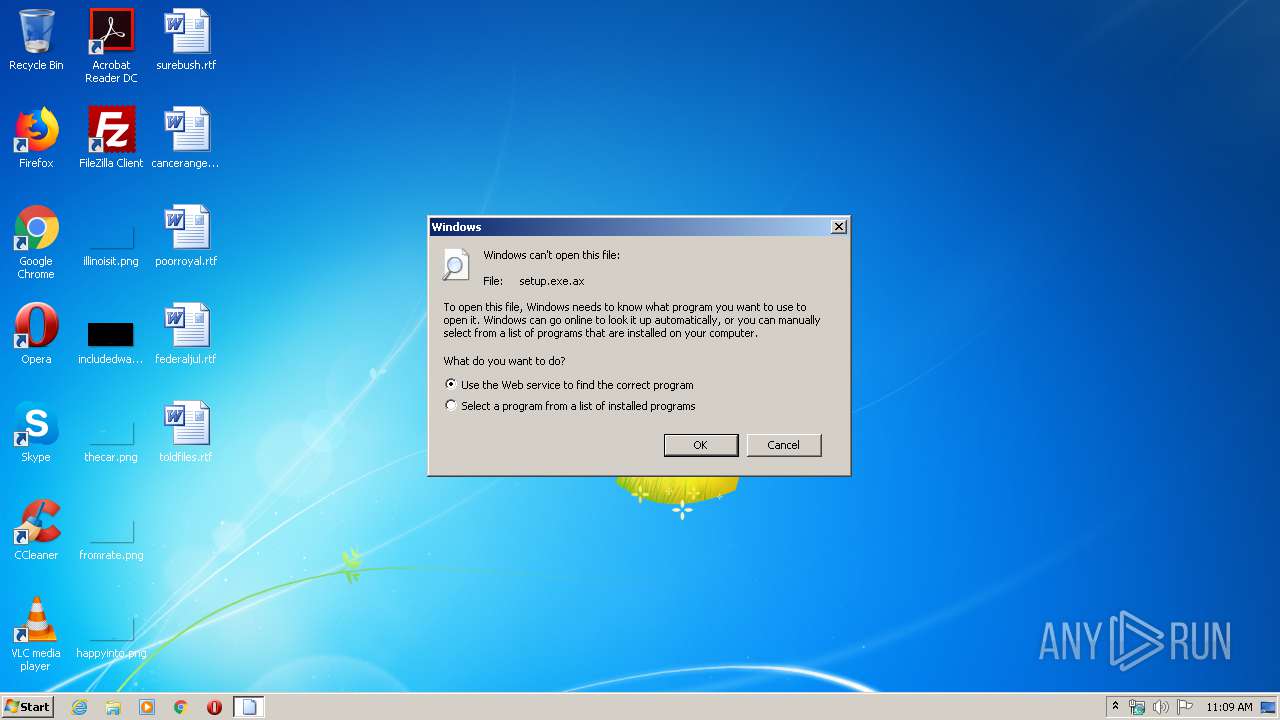
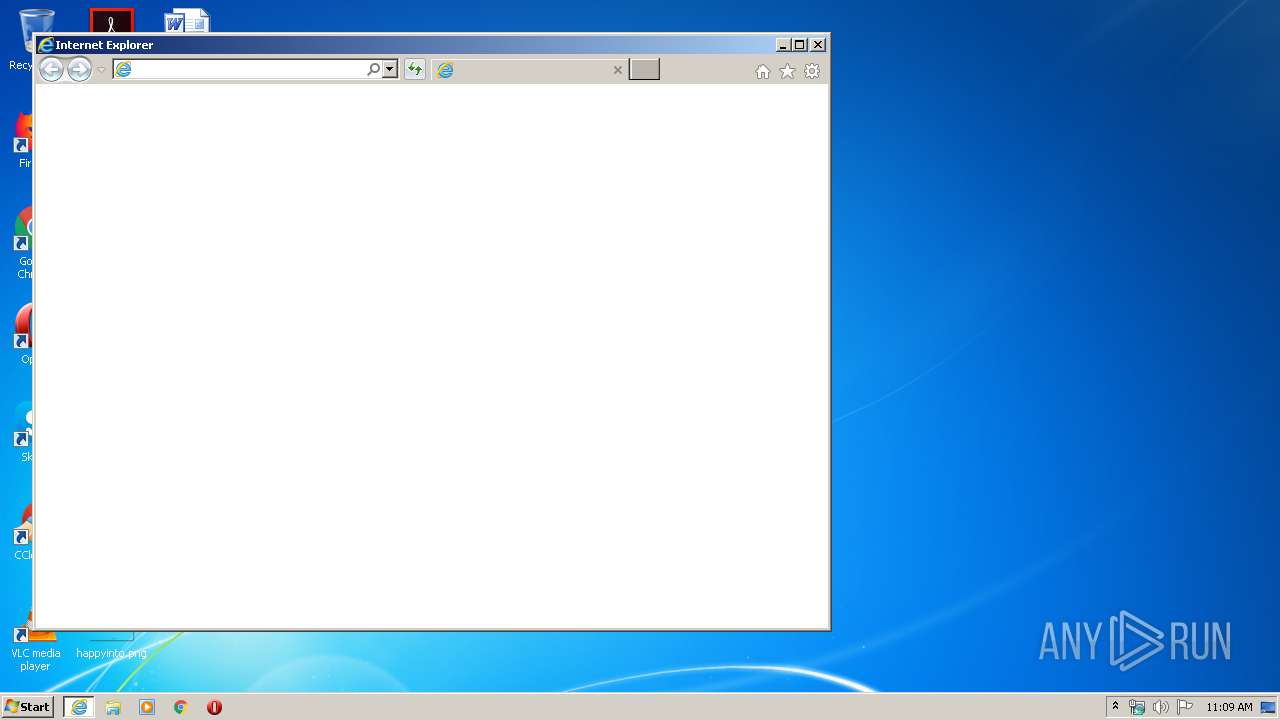
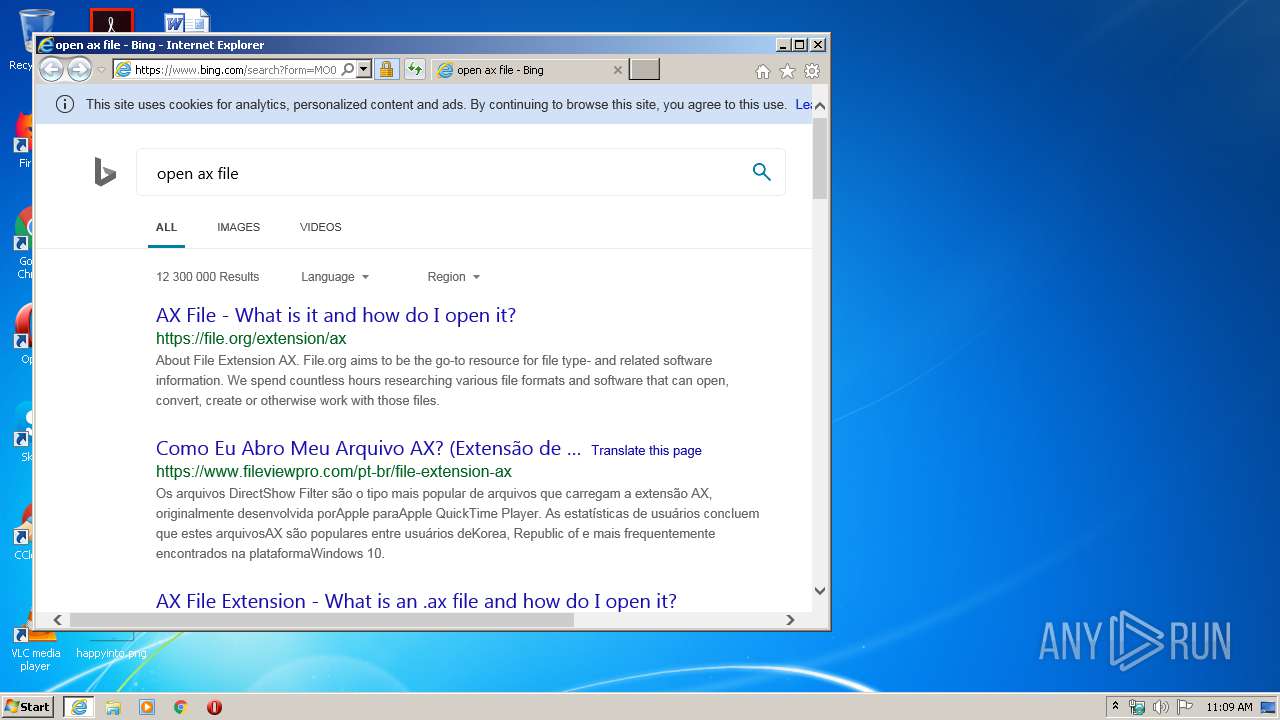
Starts Internet Explorer
- rundll32.exe (PID: 3724)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2084)
Reads Internet Cache Settings
- iexplore.exe (PID: 2084)
- iexplore.exe (PID: 2068)
Reads internet explorer settings
- iexplore.exe (PID: 2068)
Creates files in the user directory
- iexplore.exe (PID: 2068)
Reads settings of System Certificates
- iexplore.exe (PID: 2084)
- iexplore.exe (PID: 2068)
Changes settings of System certificates
- iexplore.exe (PID: 2084)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
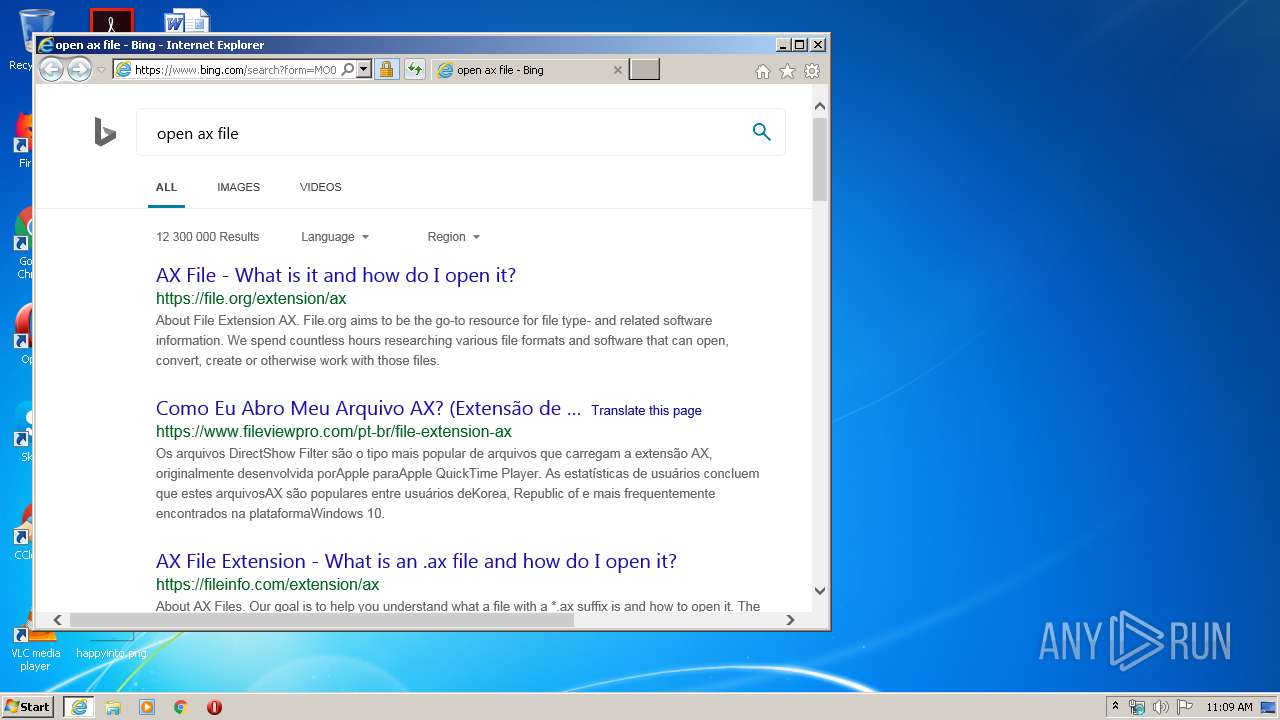
| .ax | | | DirectShow filter (36.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (v2.x) (10.7) |
| .exe | | | InstallShield setup (7.8) |
| .exe | | | Win32 EXE PECompact compressed (generic) (7.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:04:19 02:08:20+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 294912 |
| InitializedDataSize: | 73728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x22094 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 14.0.0.162 |
| ProductVersionNumber: | 14.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Macrovision Corporation |
| FileDescription: | Setup.exe |
| FileVersion: | 14.0.162 |
| InternalName: | Setup |
| OriginalFileName: | Setup.exe |
| LegalCopyright: | Copyright (C) 2007 Macrovision Corporation |
| ProductName: | InstallShield |
| ProductVersion: | 14 |
| InternalBuildNumber: | 62562 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Apr-2007 00:08:20 |
| Detected languages: |
|
| CompanyName: | Macrovision Corporation |
| FileDescription: | Setup.exe |
| FileVersion: | 14.0.162 |
| InternalName: | Setup |
| OriginalFilename: | Setup.exe |
| LegalCopyright: | Copyright (C) 2007 Macrovision Corporation |
| ProductName: | InstallShield |
| ProductVersion: | 14.0 |
| Internal Build Number: | 62562 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 19-Apr-2007 00:08:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00047A42 | 0x00048000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58216 |
.rdata | 0x00049000 | 0x00009A70 | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.5637 |
.data | 0x00053000 | 0x0000742C | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.27497 |
.rsrc | 0x0005B000 | 0x00001B58 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.13215 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.03019 | 895 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.39652 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.9625 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 6.67739 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
100 | 2.64576 | 62 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
108 | 2.34615 | 66 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
LZ32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2068 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2084 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=ax | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3724 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\setup.exe.ax | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 678
Read events
535
Write events
779
Delete events
364
Modification events
| (PID) Process: | (2084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2471421120 | |||
| (PID) Process: | (2084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803780 | |||
| (PID) Process: | (2084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2084) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
15
Text files
70
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEEBD.tmp | — | |
MD5:— | SHA256:— | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEEBE.tmp | — | |
MD5:— | SHA256:— | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\TKP7DMNH.txt | — | |
MD5:— | SHA256:— | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\4V3RLV70.txt | — | |
MD5:— | SHA256:— | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8RNFF1Z0.txt | — | |
MD5:— | SHA256:— | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PXKWO8KA.txt | — | |
MD5:— | SHA256:— | |||
| 2084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3D3R9VHS.txt | text | |
MD5:— | SHA256:— | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\th[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\8QcjeZc73qKUmEdB-gREOYYIC8o[1].png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
28
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2068 | iexplore.exe | GET | 301 | 23.55.161.159:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=ax | US | — | — | whitelisted |
2068 | iexplore.exe | GET | 302 | 23.77.210.216:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=ax | NL | — | — | whitelisted |
2068 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2068 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAi4elAbvpzaLRZNPjlRv1U%3D | US | der | 1.47 Kb | whitelisted |
2068 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAi4elAbvpzaLRZNPjlRv1U%3D | US | der | 1.47 Kb | whitelisted |
2068 | iexplore.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPC1vZt9qvn7bzY3Iidtbhla4mKQQUWIif1tycSCK3FD7%2FhIjo5oX%2F%2Bn0CE3sAAvTsRon4%2BRVzrdwAAAAC9Ow%3D | US | der | 1.79 Kb | whitelisted |
2068 | iexplore.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPC1vZt9qvn7bzY3Iidtbhla4mKQQUWIif1tycSCK3FD7%2FhIjo5oX%2F%2Bn0CE3sAAvTsRon4%2BRVzrdwAAAAC9Ow%3D | US | der | 1.79 Kb | whitelisted |
2084 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2068 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2068 | iexplore.exe | 23.77.210.216:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
2068 | iexplore.exe | 23.55.161.159:80 | shell.windows.com | Akamai International B.V. | US | unknown |
2068 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2068 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2084 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2084 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2068 | iexplore.exe | 20.190.129.130:443 | login.microsoftonline.com | Microsoft Corporation | US | malicious |
2068 | iexplore.exe | 40.90.23.247:443 | login.live.com | Microsoft Corporation | US | unknown |
2068 | iexplore.exe | 104.18.25.243:80 | ocsp.msocsp.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
tse1.mm.bing.net |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
www2.bing.com |
| whitelisted |