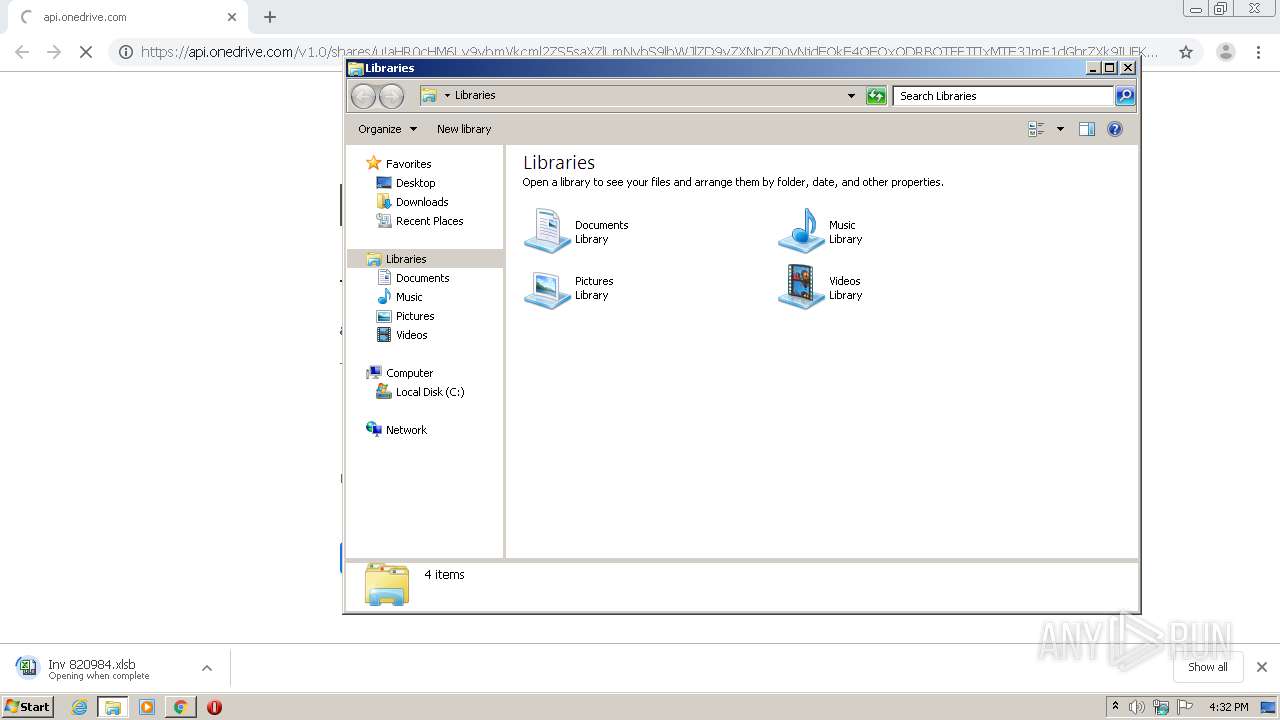
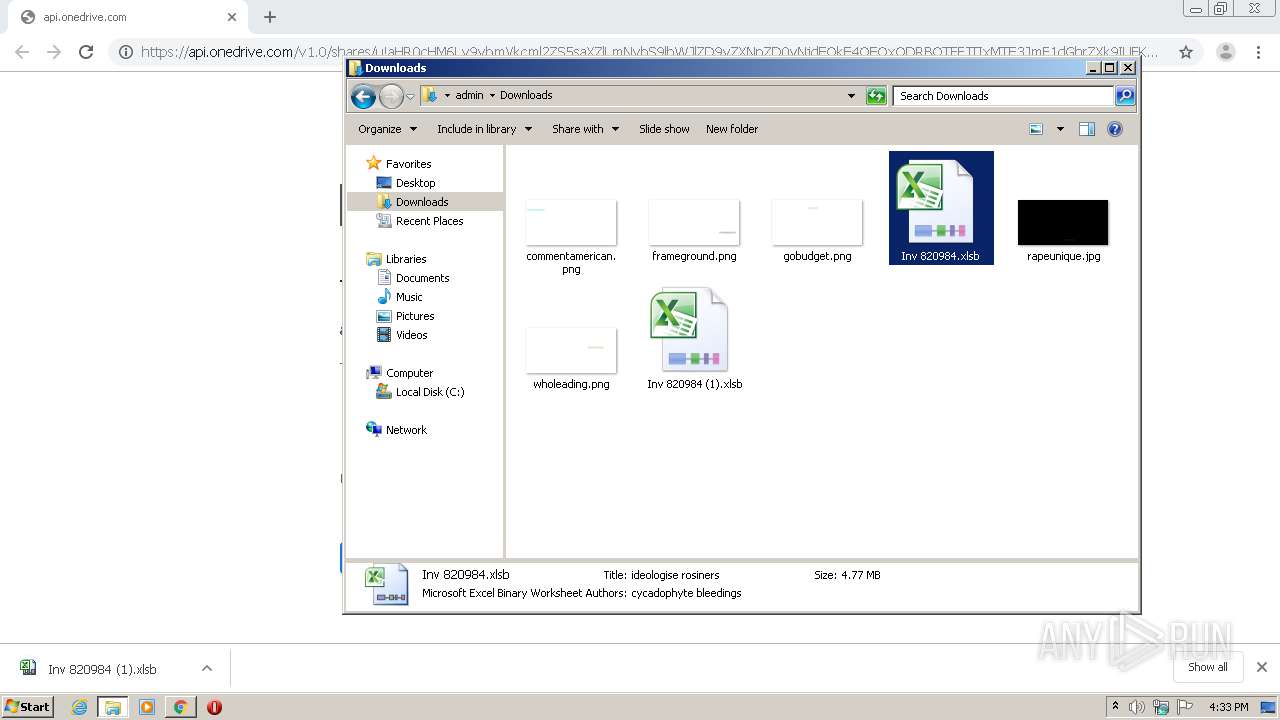
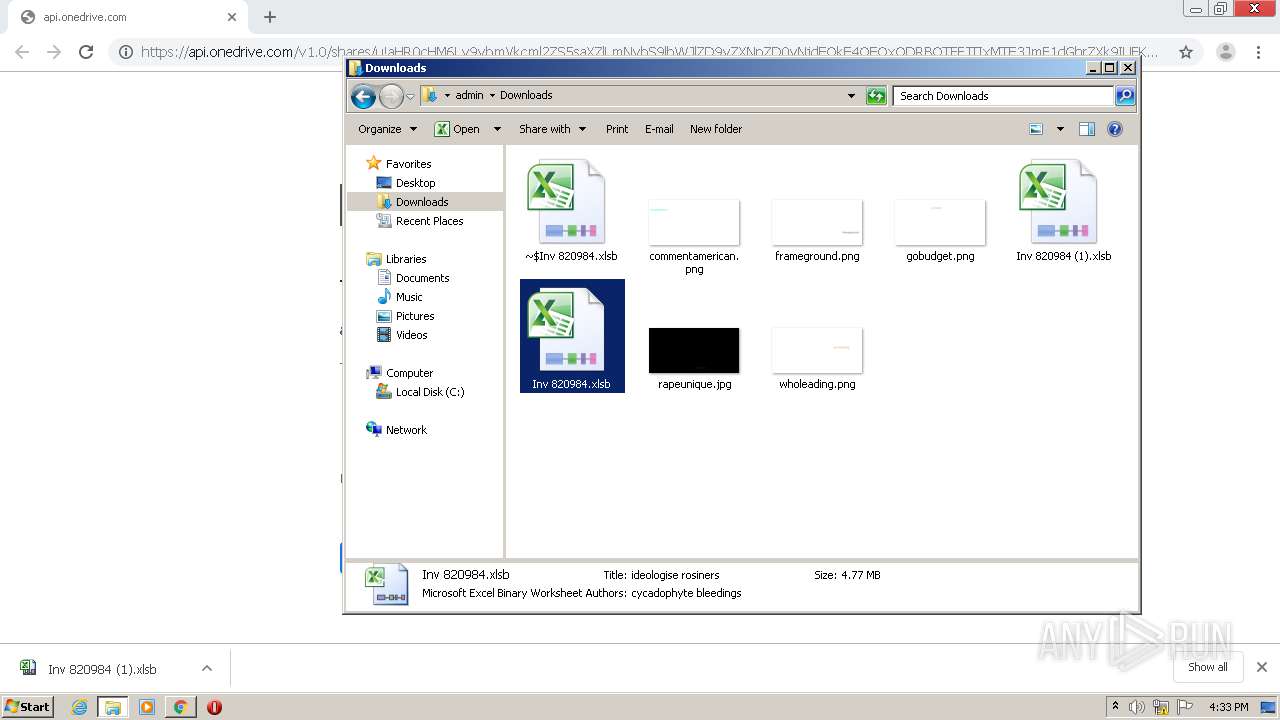
| URL: | https://api.onedrive.com/v1.0/shares/u!aHR0cHM6Ly9vbmVkcml2ZS5saXZlLmNvbS9lbWJlZD9yZXNpZD0yNjdEQkE4OEQxODRBOTFFJTIxMTE3JmF1dGhrZXk9IUFKd1NkMFZPUUdVcktFUSZlbT0y/root/content |
| Full analysis: | https://app.any.run/tasks/eb7a1ca2-e6c6-426f-b3f8-b60c22a699d1 |
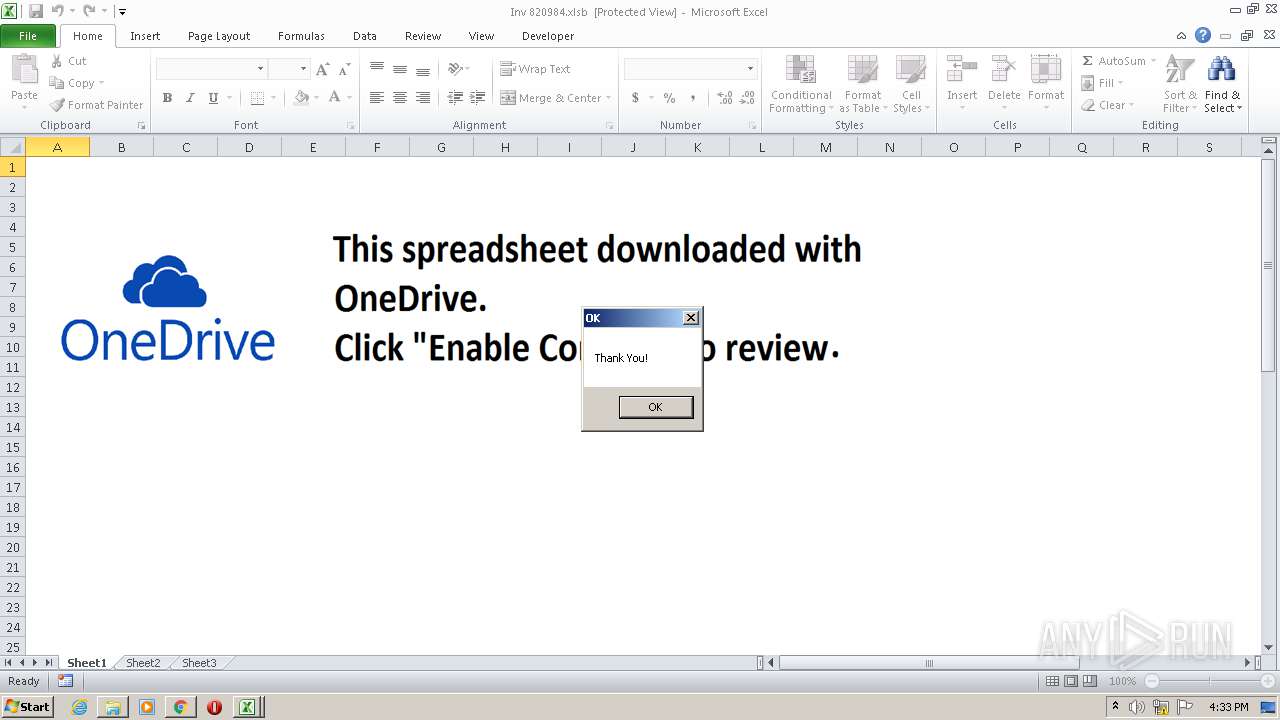
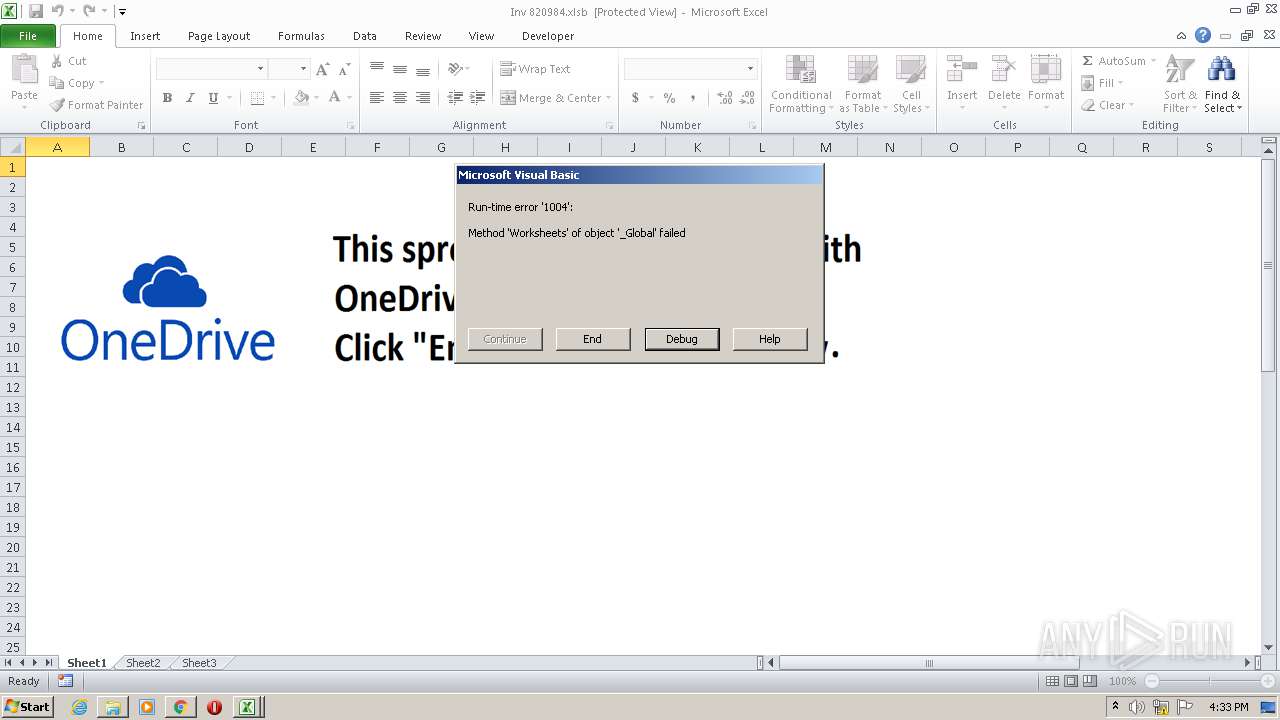
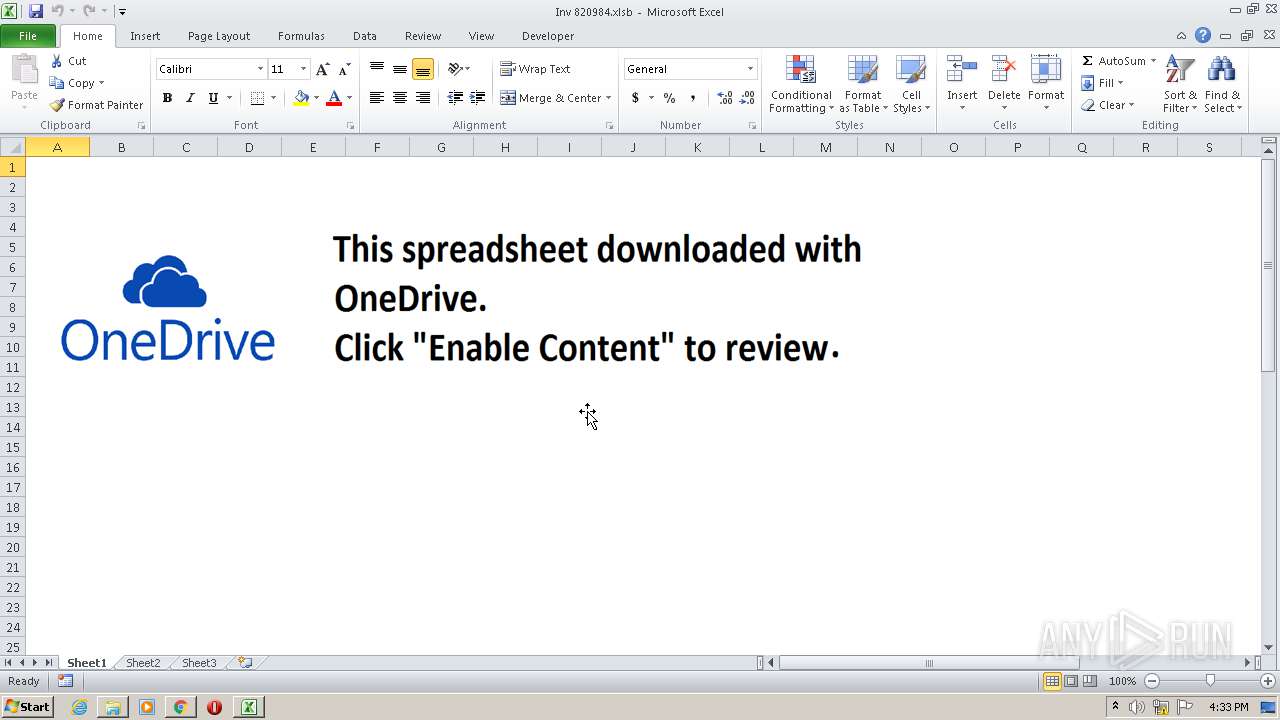
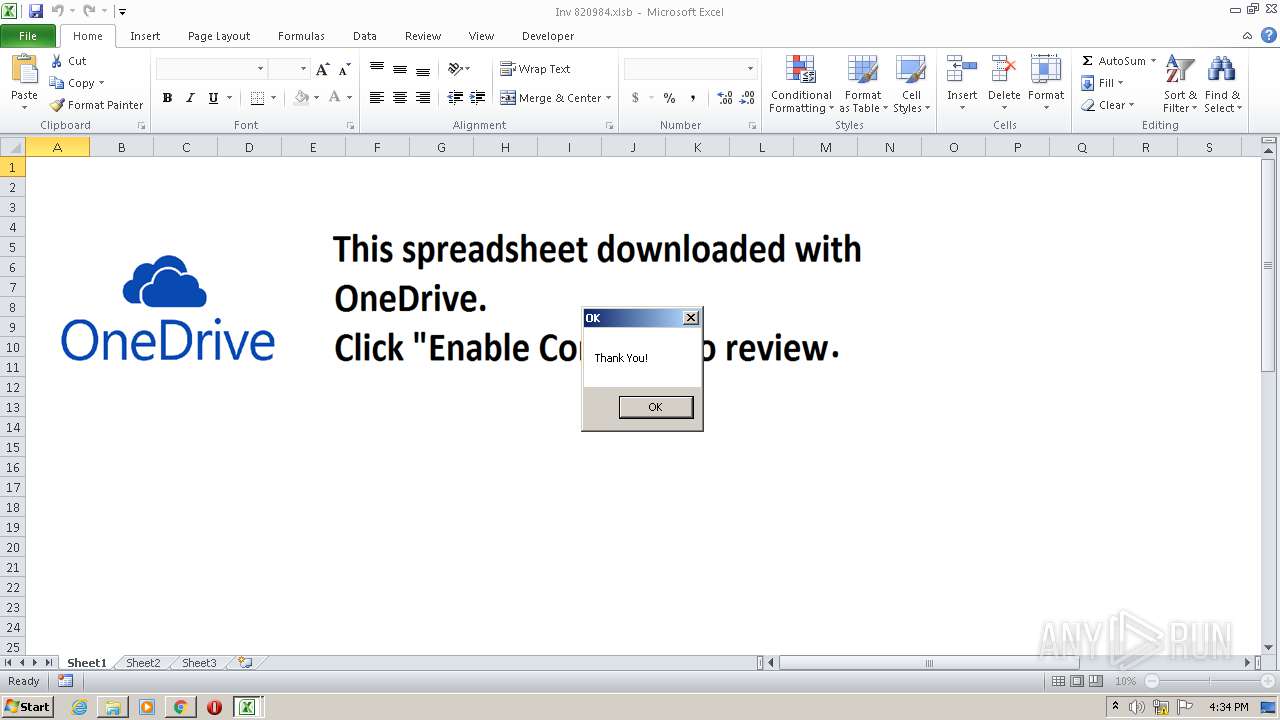
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2021, 15:32:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 39490BEDB43112D3C7BB12C60D151D4A |
| SHA1: | 102F4B728A252DC08CE29F577AAAD8F6FBE12D54 |
| SHA256: | 1FA3777128A365D8563C43EC3CB33FE746445693B6B21626AE4DDF01E8B7A3FB |
| SSDEEP: | 3:N8DLrXndjULVKIWwE3VPPLLXvDdWf+nc47cmg+a3nVqxT2UO1swSBnwFZFDxTGP0:2XruLVK8ENLXvDwfiYX+a3Vq0SBwFZF/ |
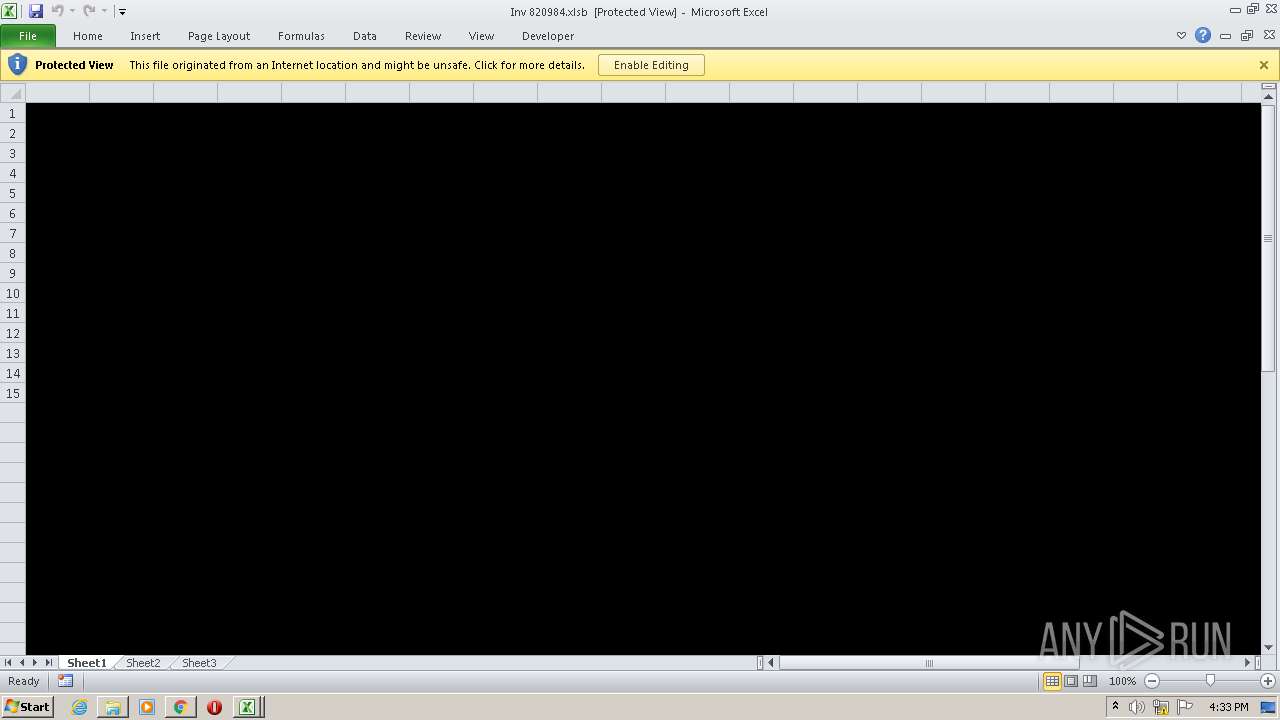
MALICIOUS
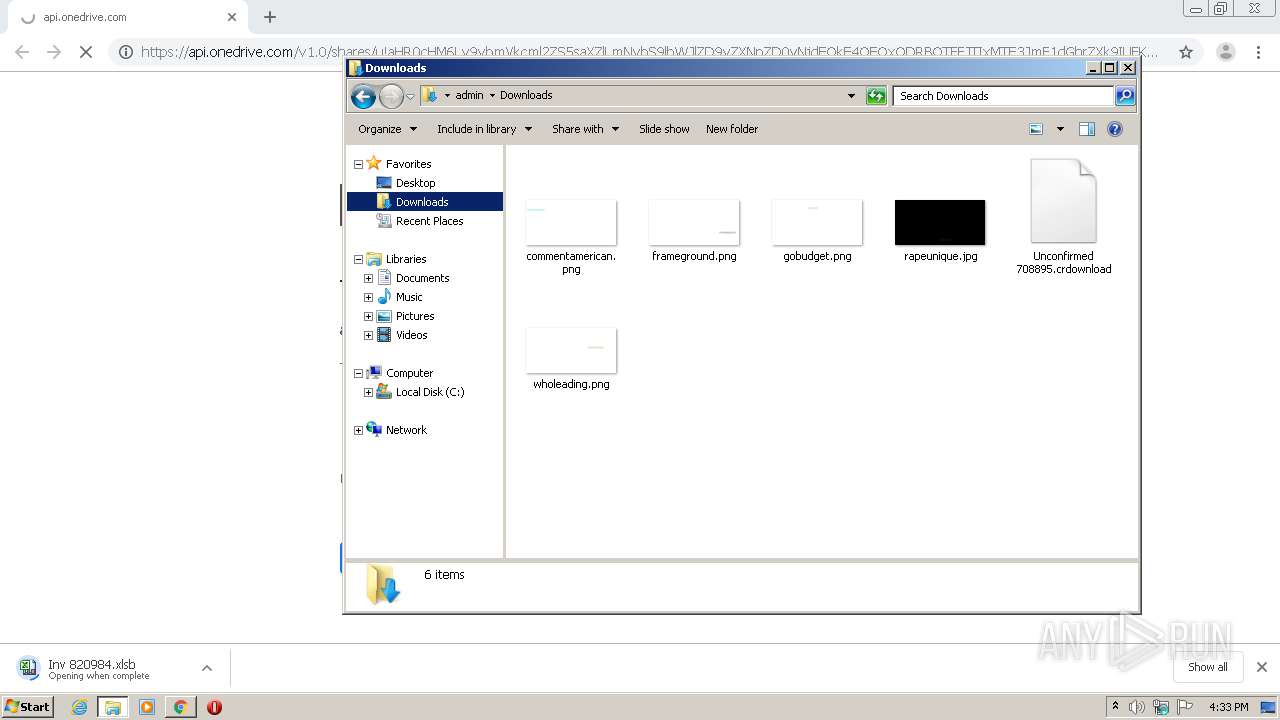
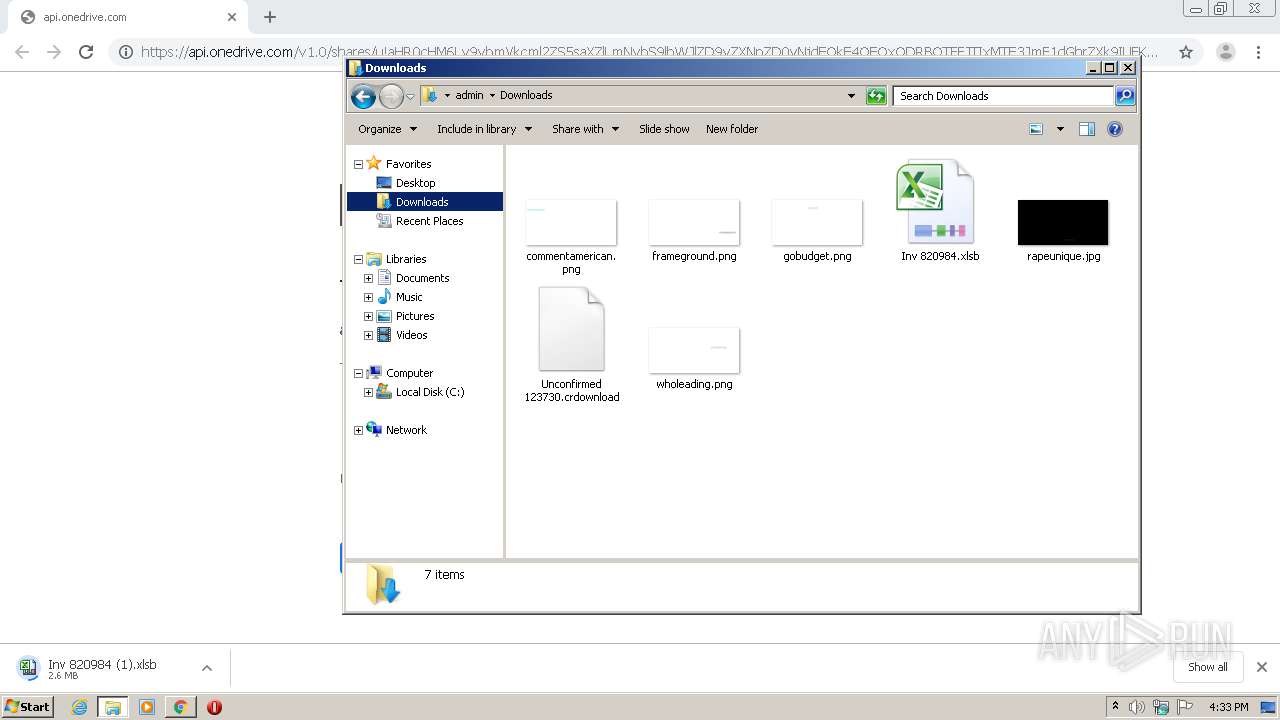
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 1796)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1796)
SUSPICIOUS
Starts Microsoft Office Application
- chrome.exe (PID: 2372)
- EXCEL.EXE (PID: 2792)
Application launched itself
- EXCEL.EXE (PID: 2792)
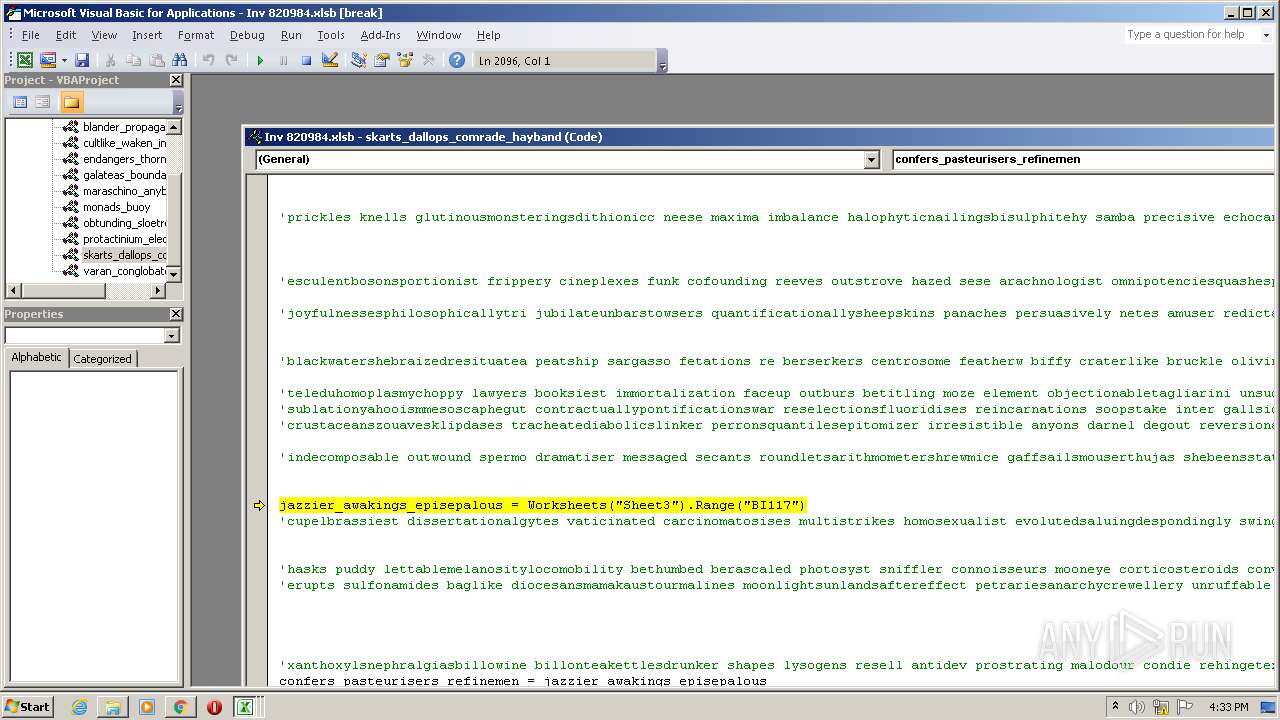
Uses WMIC.EXE to create a new process
- EXCEL.EXE (PID: 1796)
Drops a file with a compile date too recent
- EXCEL.EXE (PID: 1796)
INFO
Application launched itself
- chrome.exe (PID: 2372)
Changes default file association
- chrome.exe (PID: 2372)
Reads the hosts file
- chrome.exe (PID: 2372)
- chrome.exe (PID: 1500)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1964)
- EXCEL.EXE (PID: 2792)
- EXCEL.EXE (PID: 2576)
- EXCEL.EXE (PID: 1796)
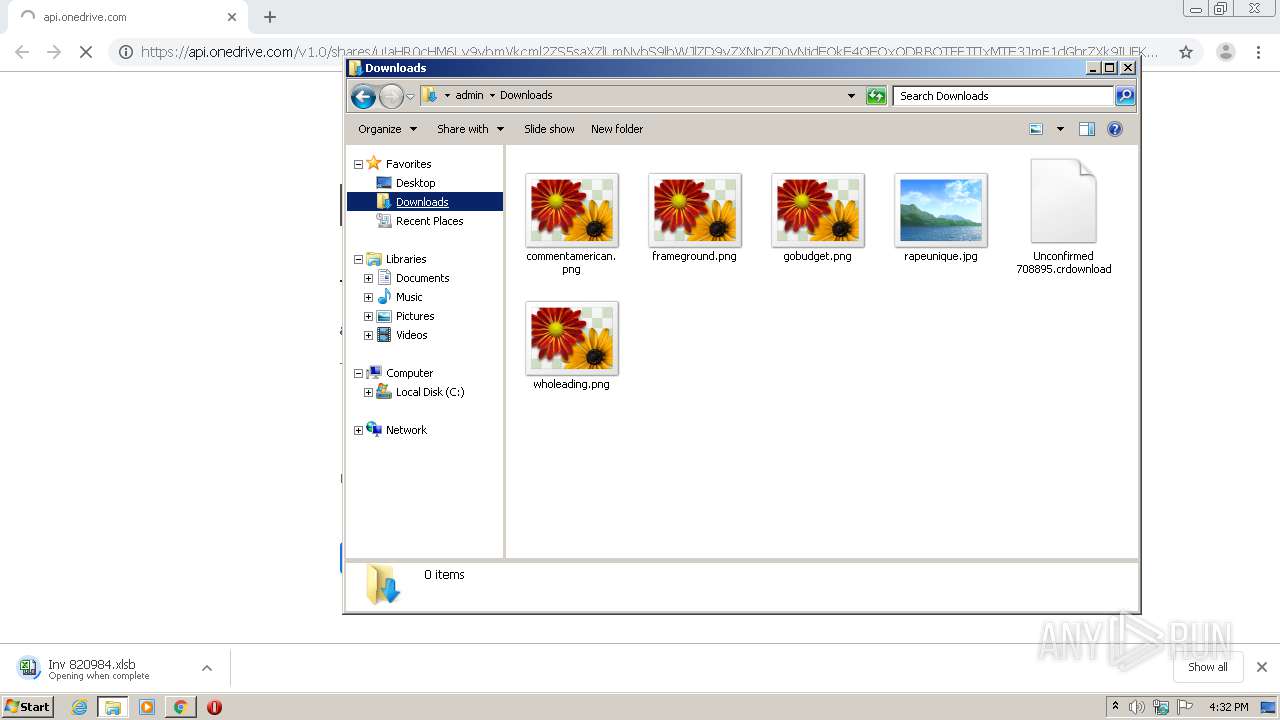
Manual execution by user
- EXCEL.EXE (PID: 1796)
- explorer.exe (PID: 3848)
Creates files in the user directory
- EXCEL.EXE (PID: 1796)
- EXCEL.EXE (PID: 2792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,9200135226228005457,16816078397030934515,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1216288328057342564 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2432 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1452 | "C:\Windows\System32\wbem\WMIC.exe" process call create 'rundll32.exe "C:\Users\admin\AppData\Roaming\39583.dll" FeClientInitialize' | C:\Windows\System32\wbem\WMIC.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,9200135226228005457,16816078397030934515,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5544940793995000915 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,9200135226228005457,16816078397030934515,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3599641265245522385 --mojo-platform-channel-handle=3304 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,9200135226228005457,16816078397030934515,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=251920775139741434 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://api.onedrive.com/v1.0/shares/u!aHR0cHM6Ly9vbmVkcml2ZS5saXZlLmNvbS9lbWJlZD9yZXNpZD0yNjdEQkE4OEQxODRBOTFFJTIxMTE3JmF1dGhrZXk9IUFKd1NkMFZPUUdVcktFUSZlbT0y/root/content" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,9200135226228005457,16816078397030934515,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14275383630291475965 --mojo-platform-channel-handle=2024 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 338
Read events
3 012
Write events
261
Delete events
65
Modification events
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2372-13265739139434875 |
Value: 259 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2372) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
24
Text files
87
Unknown types
6
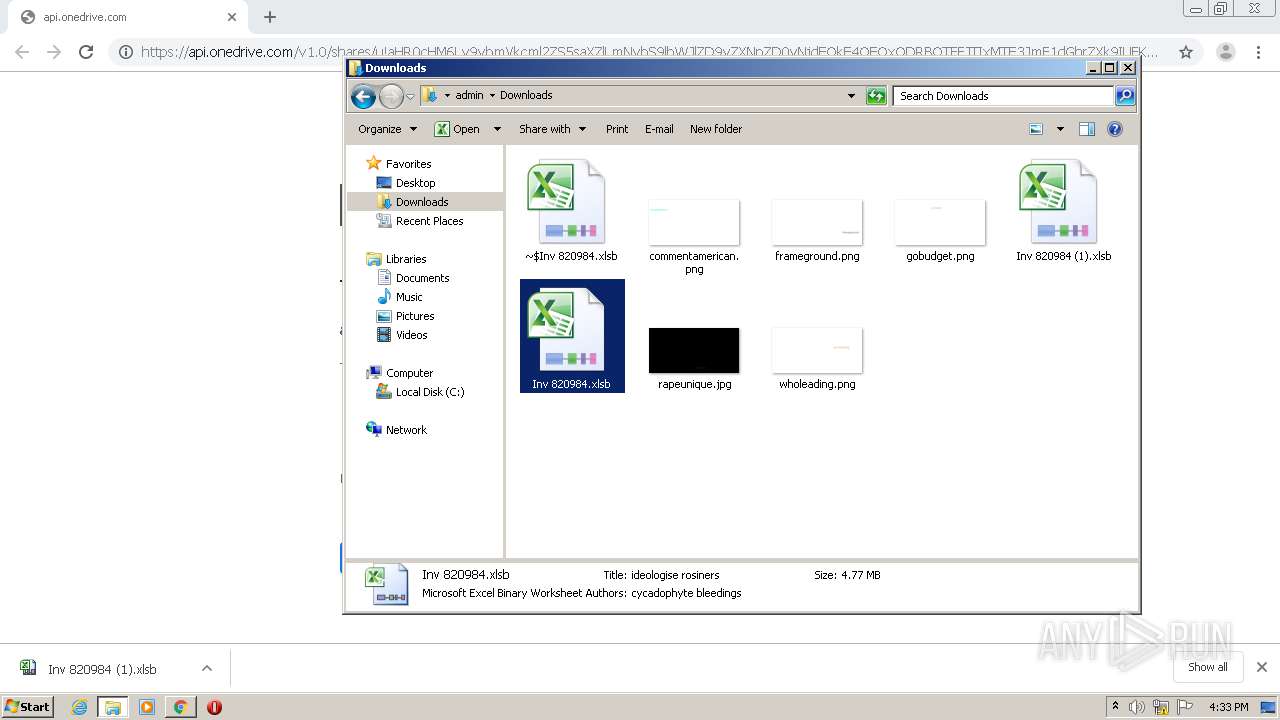
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60A28C84-944.pma | — | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\567ea060-7f47-44b6-9605-820ea8cbd91c.tmp | — | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF131c17.TMP | text | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF131f62.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
24
DNS requests
11
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1796 | EXCEL.EXE | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEQDwHUvue3yjezwFZqwFlyRY | US | der | 728 b | whitelisted |
1796 | EXCEL.EXE | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1500 | chrome.exe | 13.107.42.12:443 | api.onedrive.com | Microsoft Corporation | US | suspicious |
1500 | chrome.exe | 142.250.184.237:443 | accounts.google.com | Google Inc. | US | suspicious |
1500 | chrome.exe | 142.250.186.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1500 | chrome.exe | 142.250.186.142:443 | clients4.google.com | Google Inc. | US | whitelisted |
1500 | chrome.exe | 13.107.43.12:443 | johqdg.am.files.1drv.com | Microsoft Corporation | US | suspicious |
1500 | chrome.exe | 172.217.18.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1796 | EXCEL.EXE | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1500 | chrome.exe | 142.250.185.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1796 | EXCEL.EXE | 162.144.12.168:443 | impress-hrd.mysoftheaven.com | Unified Layer | US | suspicious |
1796 | EXCEL.EXE | 173.236.44.34:443 | proyectomoodle.labora.com.pe | SingleHop, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.onedrive.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
clients4.google.com |
| whitelisted |
johqdg.am.files.1drv.com |
| suspicious |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
impress-hrd.mysoftheaven.com |
| suspicious |
proyectomoodle.labora.com.pe |
| unknown |
ocsp.comodoca.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1796 | EXCEL.EXE | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1796 | EXCEL.EXE | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1796 | EXCEL.EXE | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1796 | EXCEL.EXE | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1796 | EXCEL.EXE | Potentially Bad Traffic | ET INFO TLS Handshake Failure |