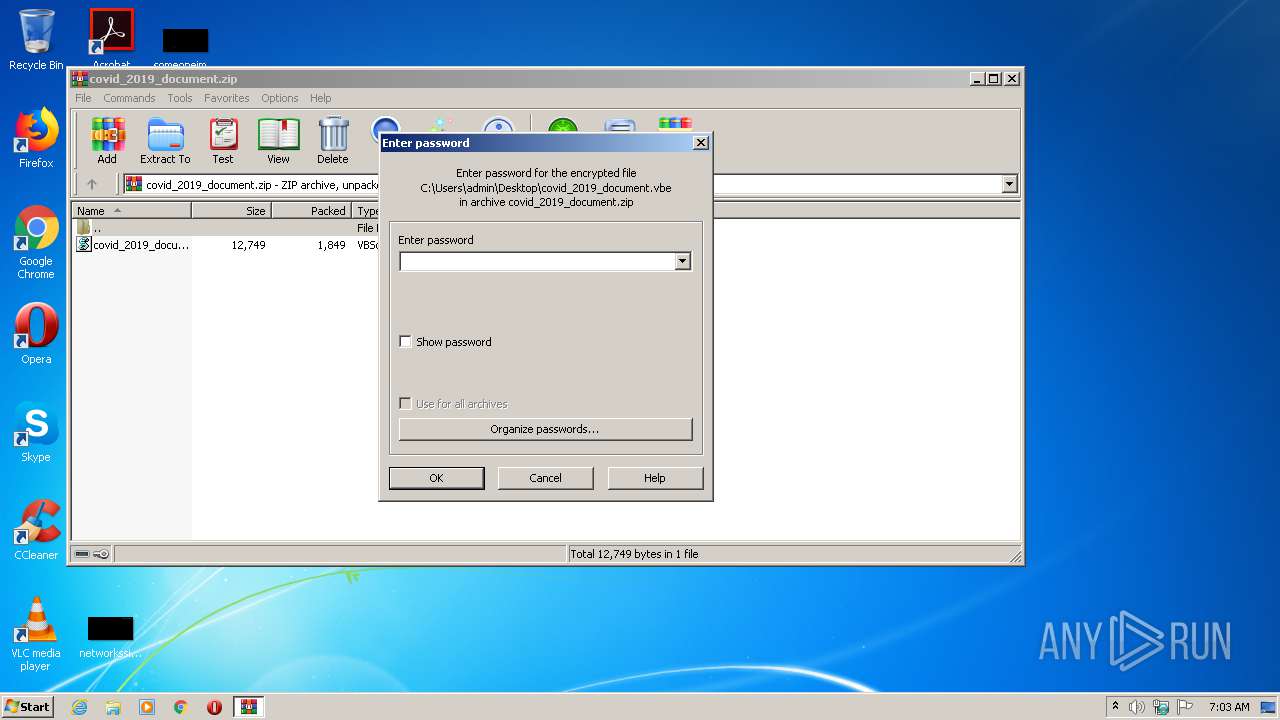
| File name: | covid_2019_document.zip |
| Full analysis: | https://app.any.run/tasks/b8e79cdc-256f-4efd-b9d0-93f60a1c9c50 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 06:02:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
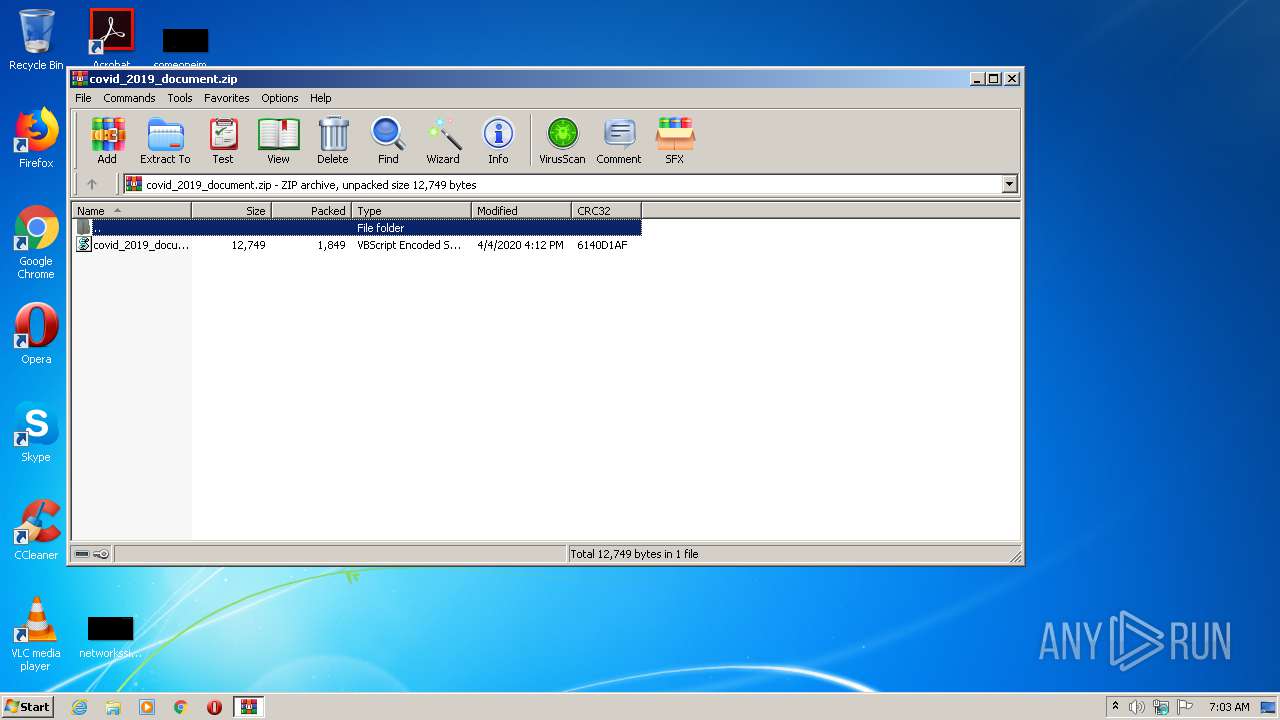
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 40E468FB0D344317BC3E73278DF00F32 |
| SHA1: | EB1E3E5CC528C1E00E361DB4532FC13627A31359 |
| SHA256: | 1F89D17F3C28987691F1A55475D2C189C1FFD63A76D0494AB9E97EFADB1EC749 |
| SSDEEP: | 48:90eR0YyHyFXsWEs5lmpxCM/U/XBy43pltDnso/R0Q5ywRg:KeR0kFXjExxCM/WXByYPlZ/2eBRg |
MALICIOUS
Changes settings of System certificates
- WScript.exe (PID: 2460)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 2592)
- wscript.exe (PID: 584)
SUSPICIOUS
Executes scripts
- WScript.exe (PID: 2460)
- wscript.exe (PID: 584)
- wscript.exe (PID: 2376)
Application launched itself
- WScript.exe (PID: 2460)
- wscript.exe (PID: 584)
- wscript.exe (PID: 2376)
Adds / modifies Windows certificates
- wscript.exe (PID: 584)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 2592)
- WScript.exe (PID: 2460)
INFO
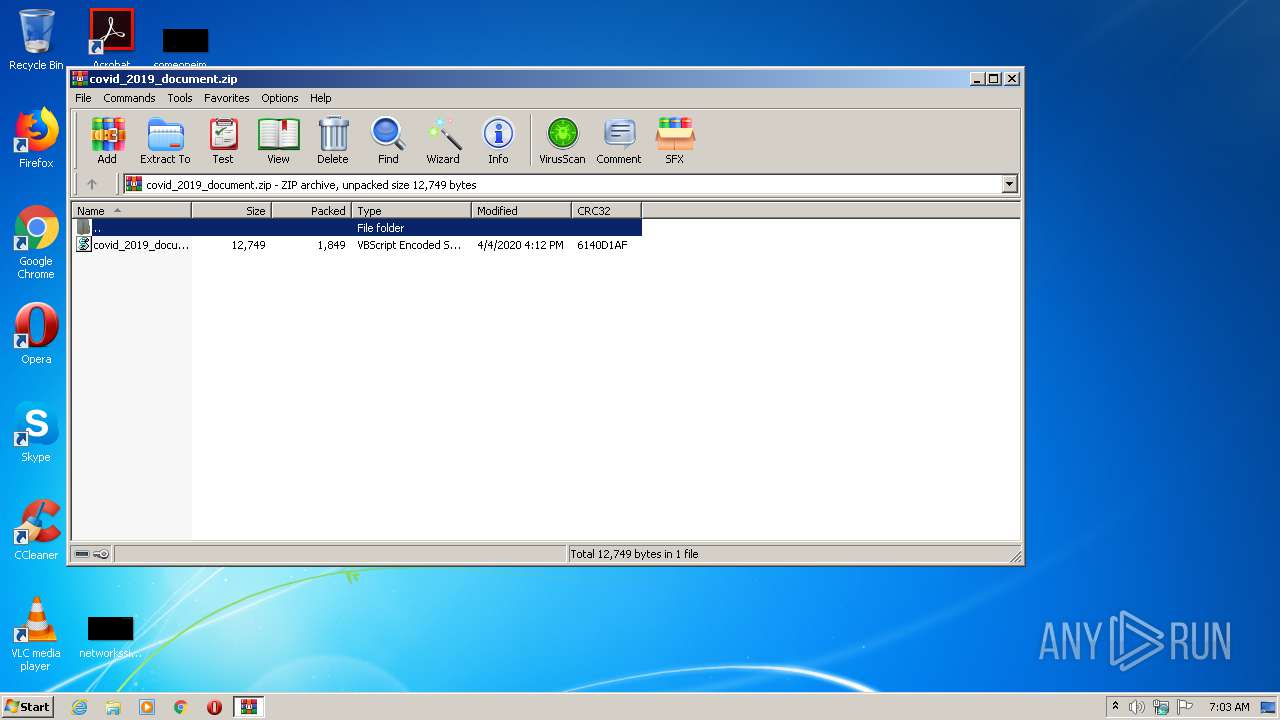
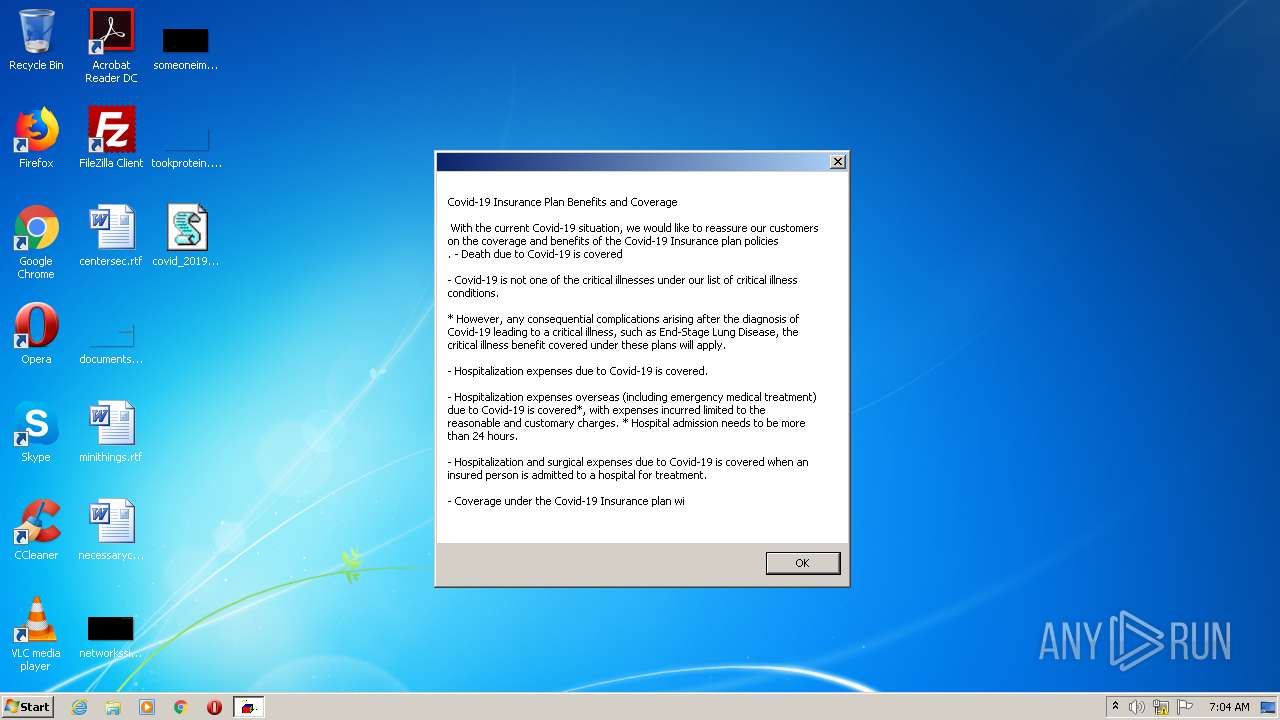
Drops Coronavirus (possible) decoy
- WinRAR.exe (PID: 2516)
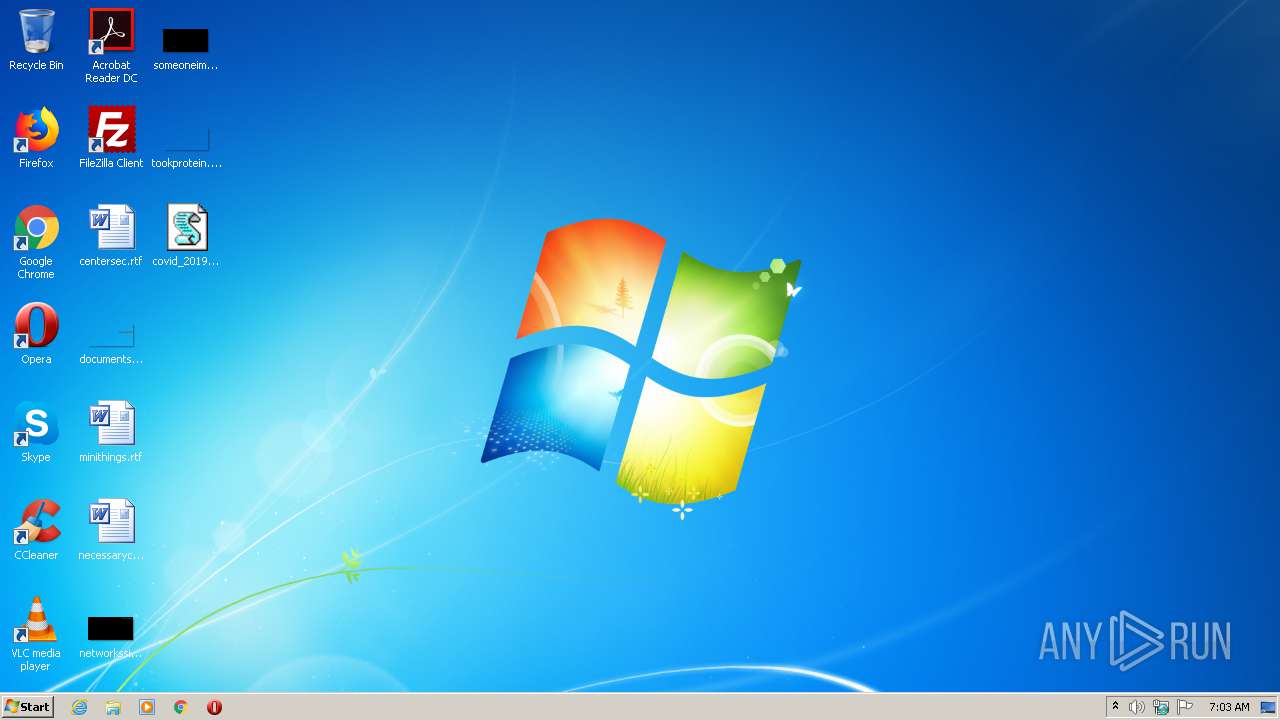
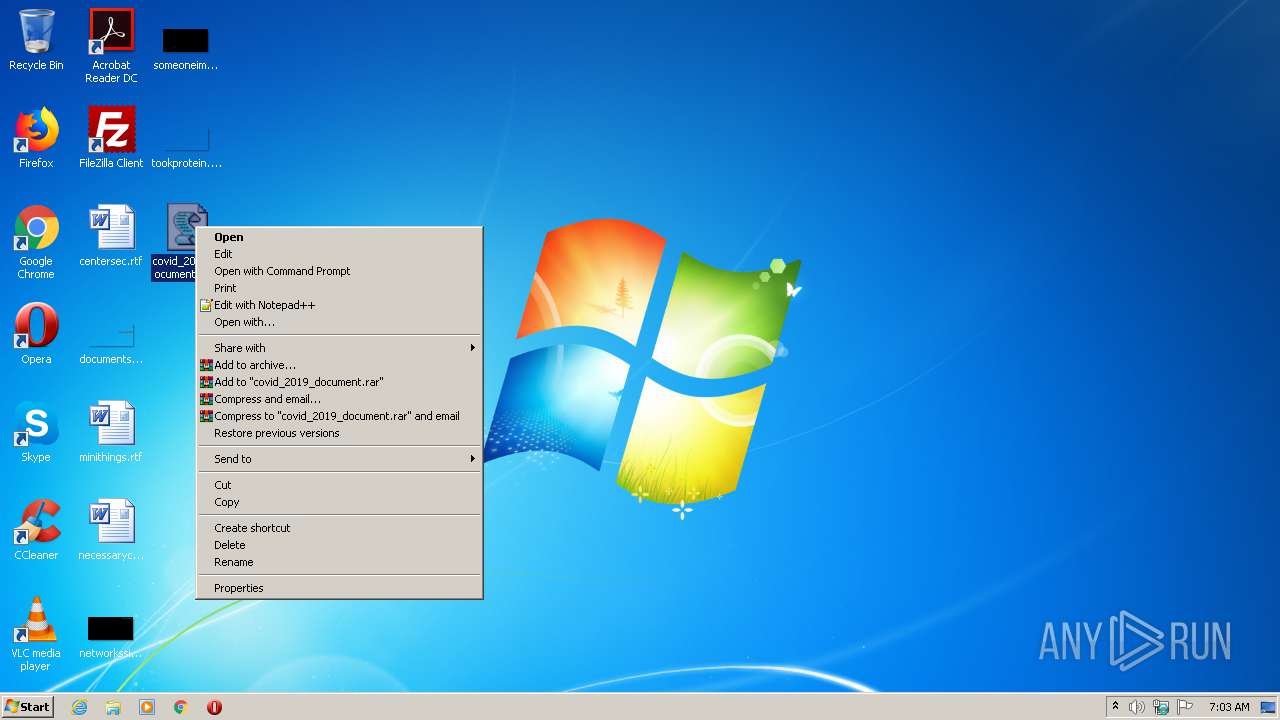
Manual execution by user
- WScript.exe (PID: 2460)
Reads settings of System Certificates
- wscript.exe (PID: 584)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 2592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:04:05 00:12:28 |
| ZipCRC: | 0x6140d1af |
| ZipCompressedSize: | 1849 |
| ZipUncompressedSize: | 12749 |
| ZipFileName: | covid_2019_document.vbe |
Total processes
38
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\covid_2019_document.vbe oc | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2376 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\covid_2019_document.vbe oc oc | C:\Windows\System32\wscript.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2460 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\covid_2019_document.vbe" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
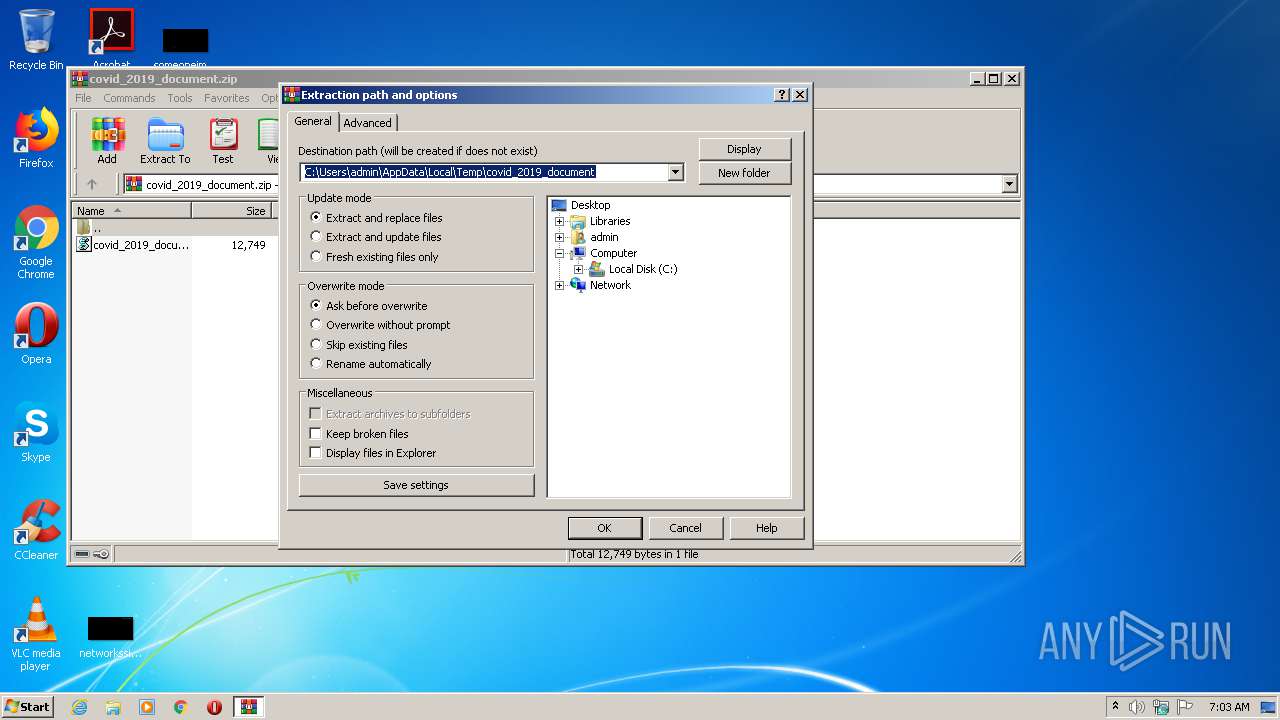
| 2516 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\covid_2019_document.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2592 | "C:\Windows\System32\wscript.exe" C:\Users\admin\Desktop\covid_2019_document.vbe oc oc oc | C:\Windows\System32\wscript.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
14 956
Read events
750
Write events
9 466
Delete events
4 740
Modification events
| (PID) Process: | (2516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2516) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2516) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\covid_2019_document.zip | |||
| (PID) Process: | (2516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2516) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2516) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4803 |
Value: VBScript Encoded Script File | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | WinRAR.exe | C:\Users\admin\Desktop\covid_2019_document.vbe | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2460 | WScript.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
584 | wscript.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
2376 | wscript.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
2592 | wscript.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
xxococococ.xyz |
| unknown |