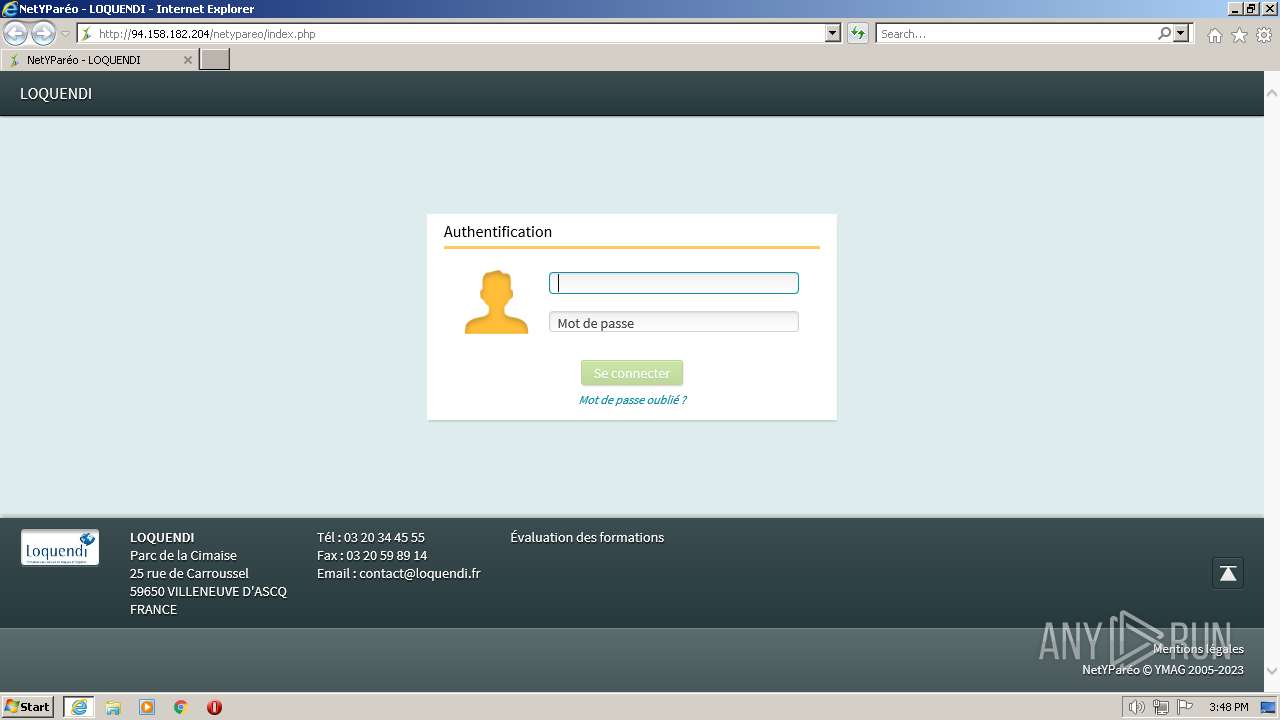
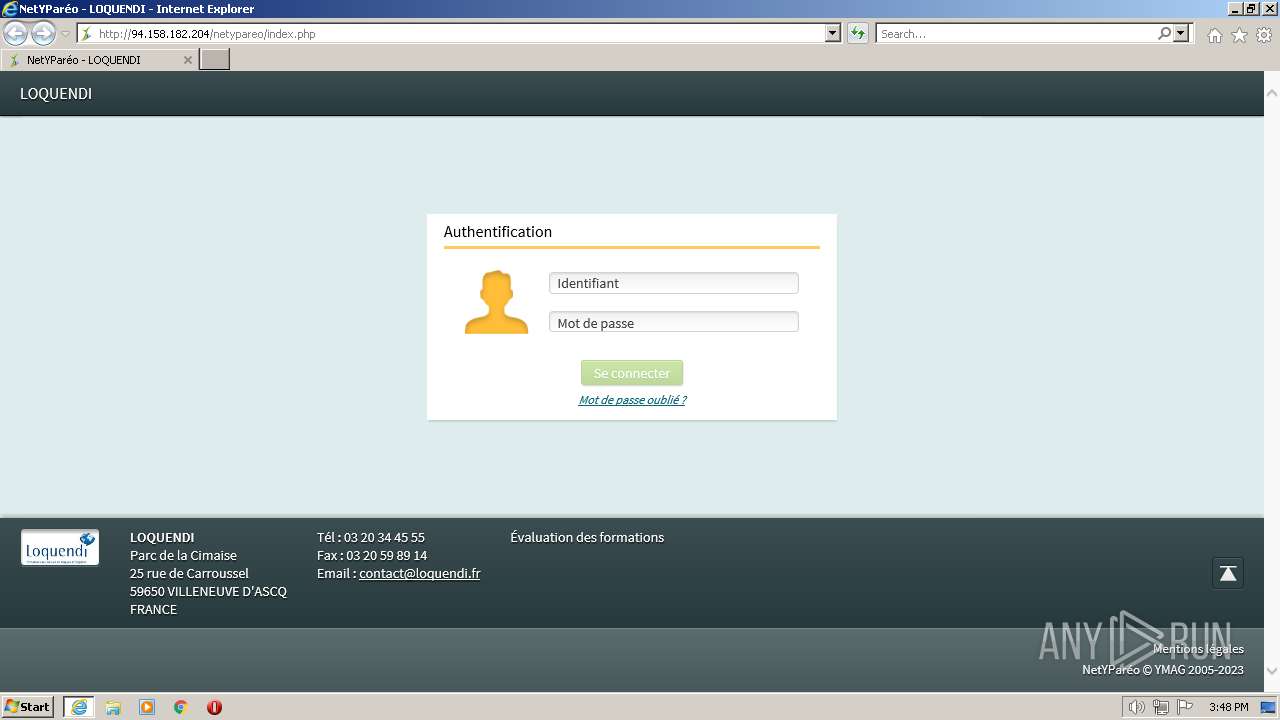
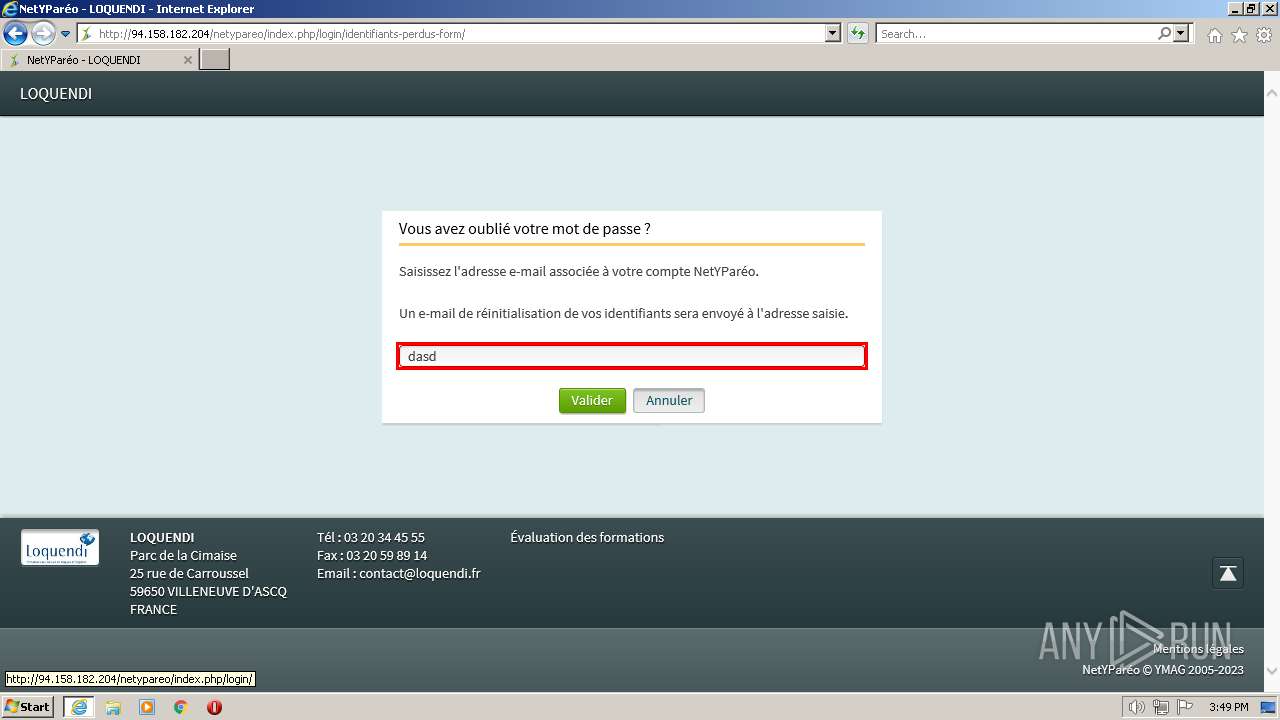
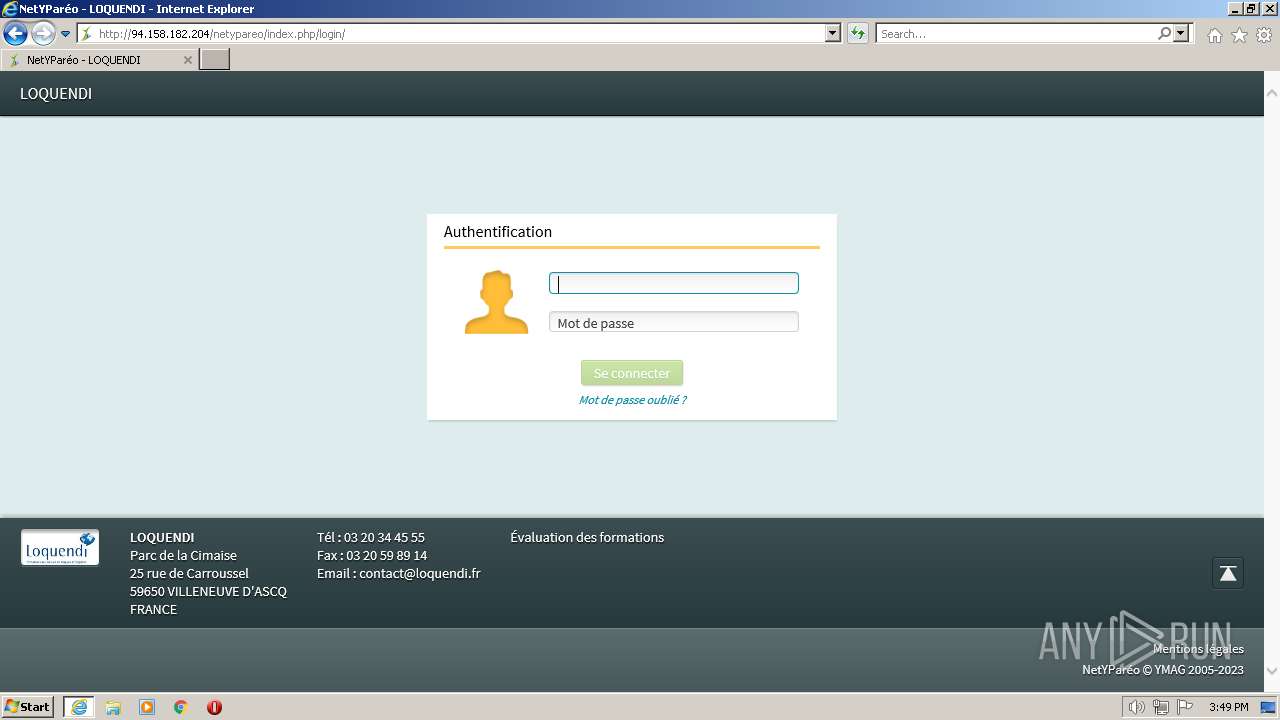
| URL: | http://94.158.182.204/netypareo/index.php |
| Full analysis: | https://app.any.run/tasks/758c5790-effe-44e1-8fd6-fe6e4628e820 |
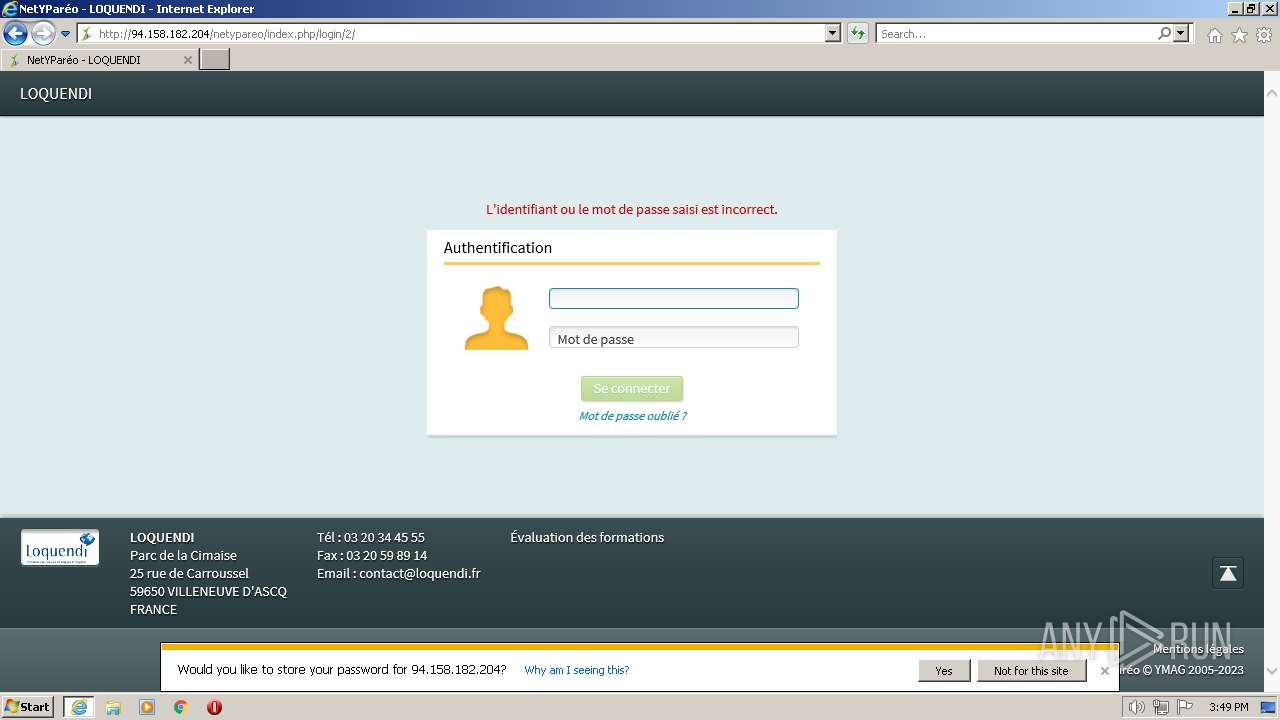
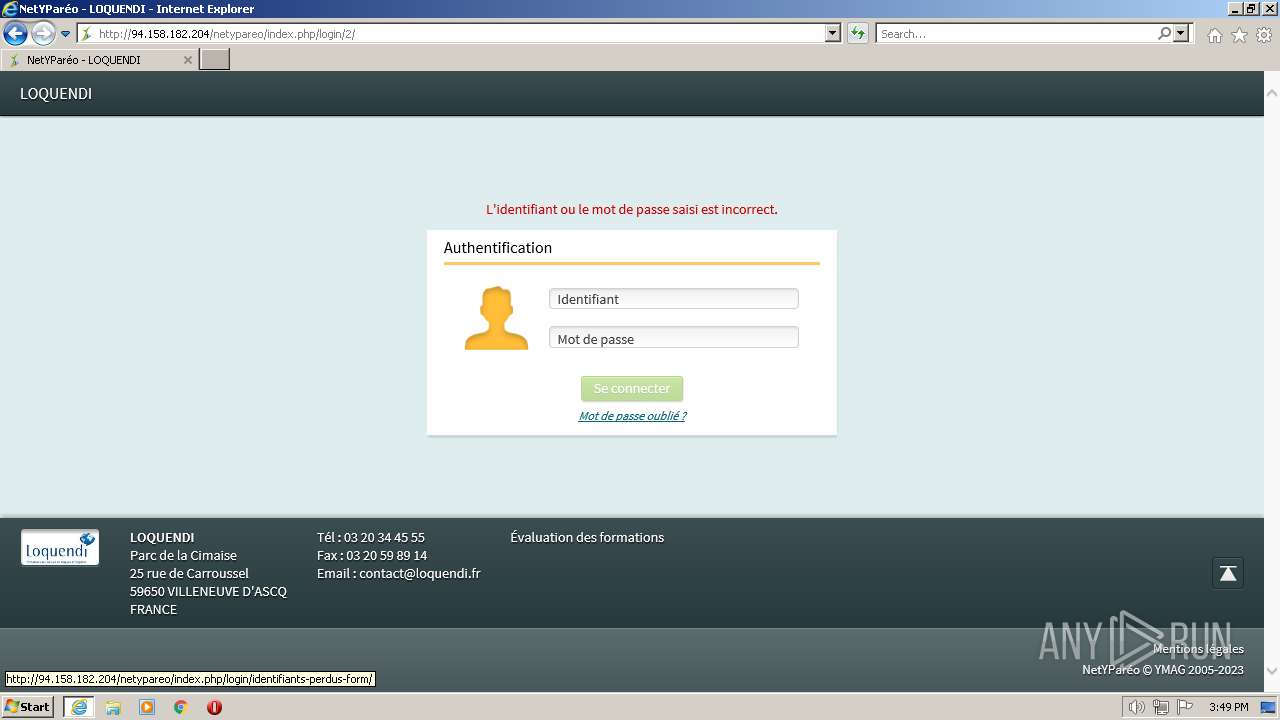
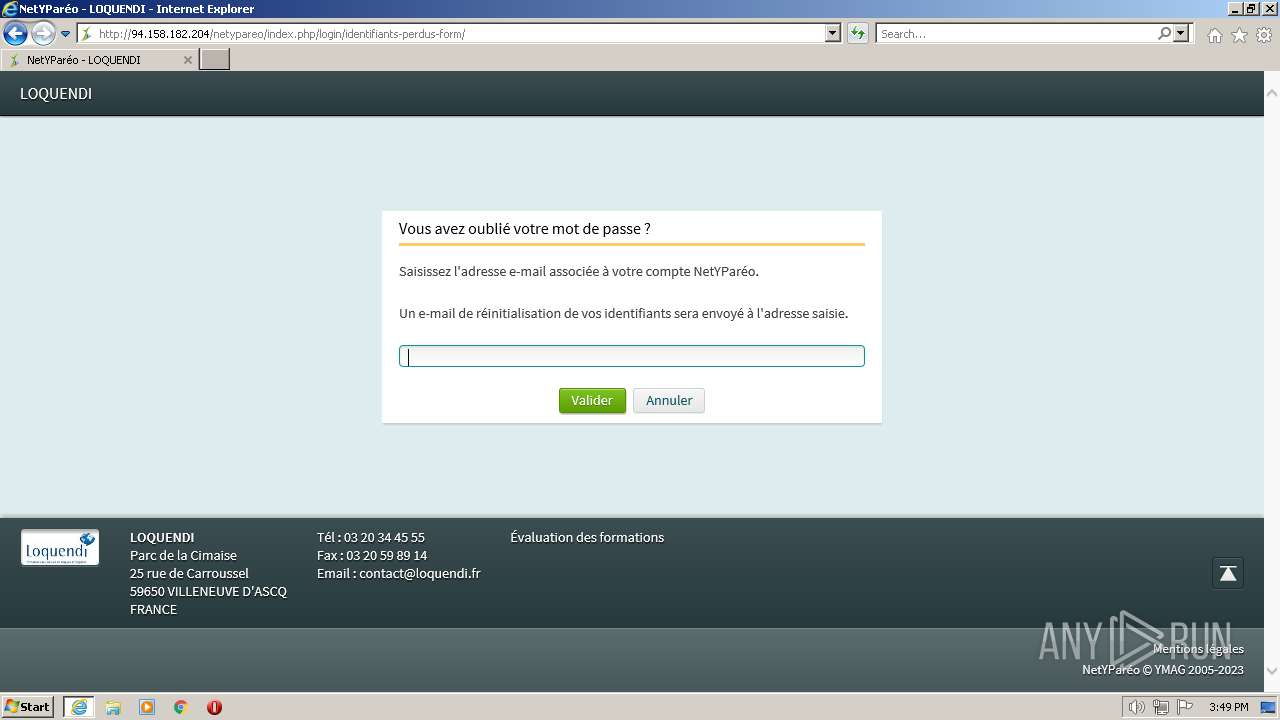
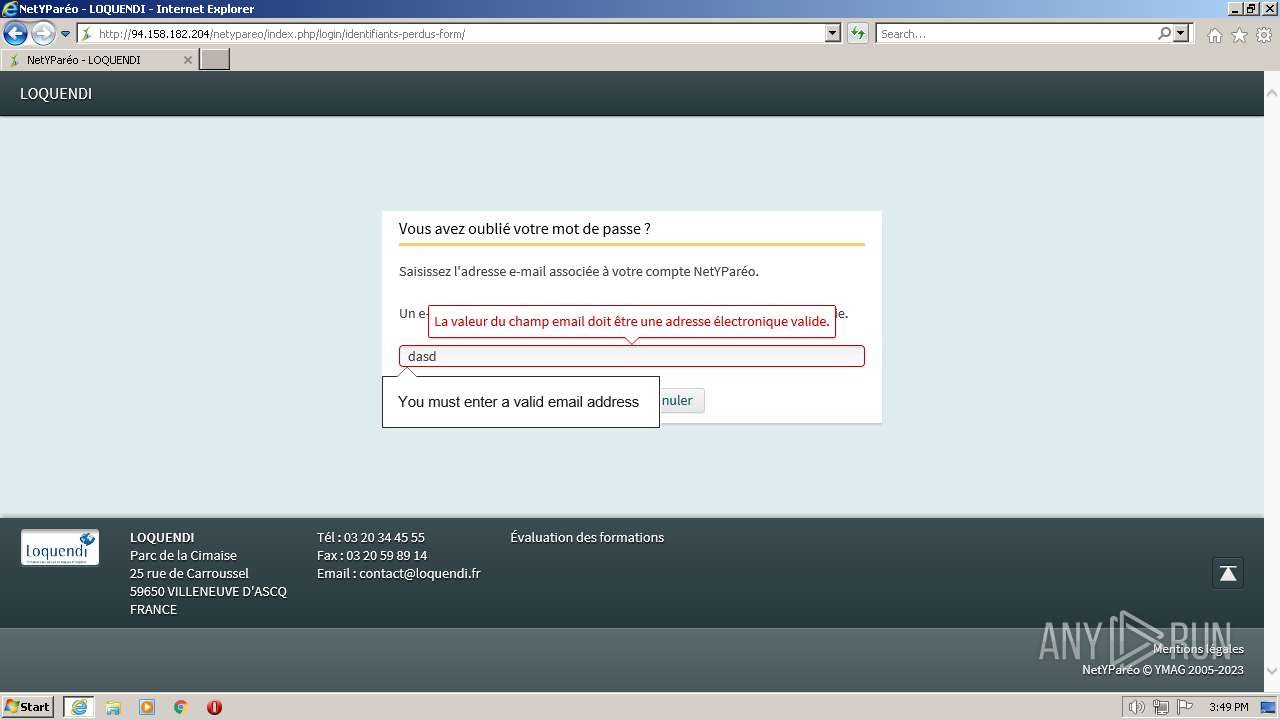
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2023, 15:48:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1FD33FAEC0751659425975BC61247755 |
| SHA1: | 56DFA3D5B11587D71637D2B9E2B324E468D786C3 |
| SHA256: | 1F7E338190BDBB72C11FC5AF57354EA477579DAD9EE21CB9DDDD528077A159C0 |
| SSDEEP: | 3:N1KxLT6L8/KUHn:CNeL8/FHn |
MALICIOUS
No malicious indicators.SUSPICIOUS
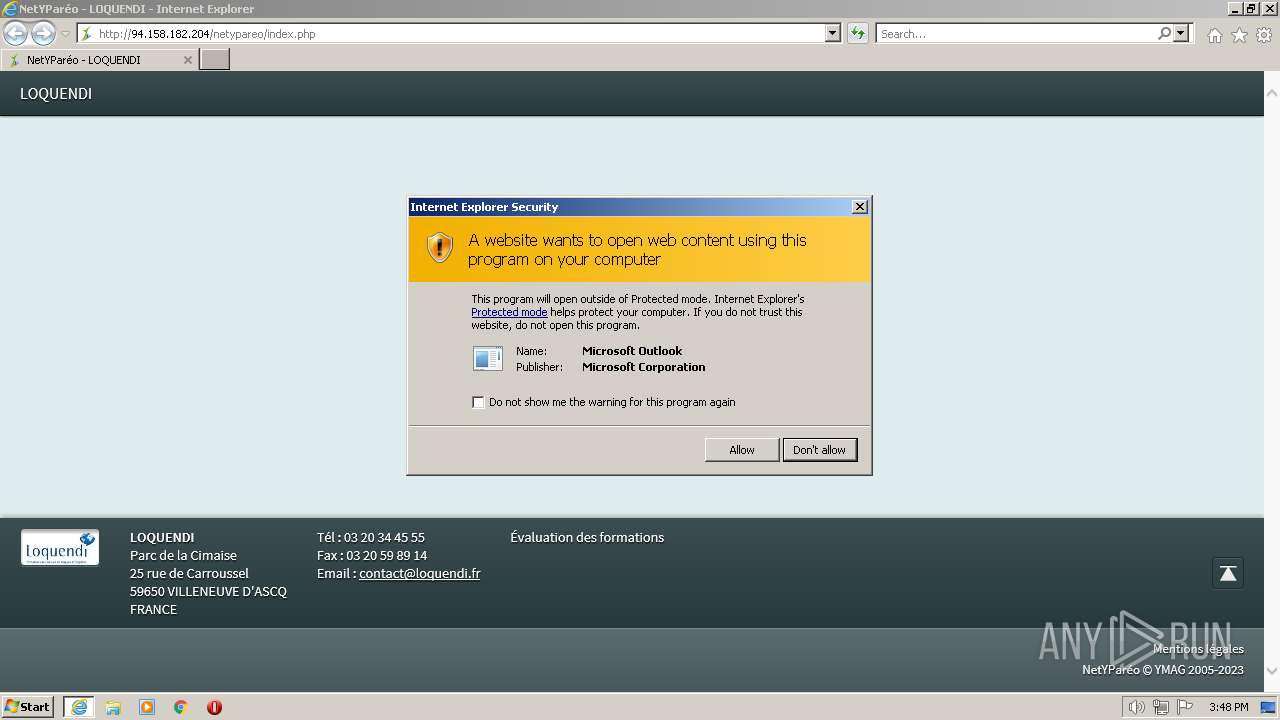
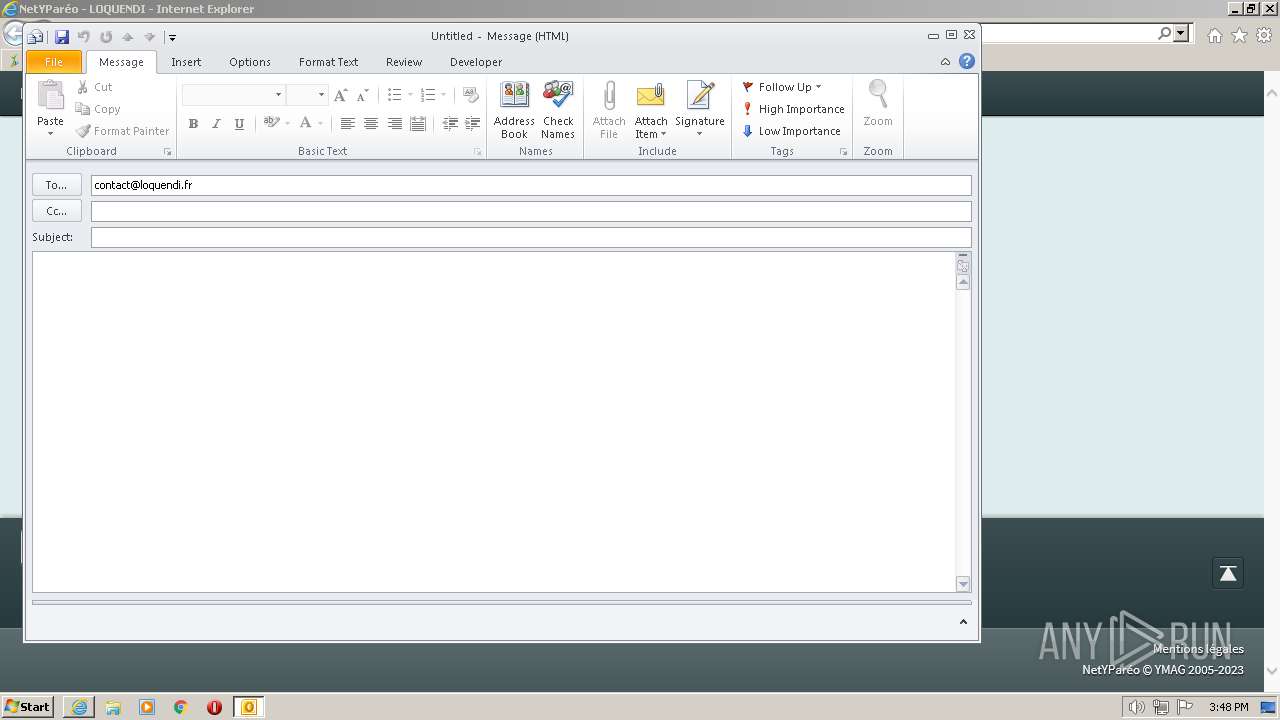
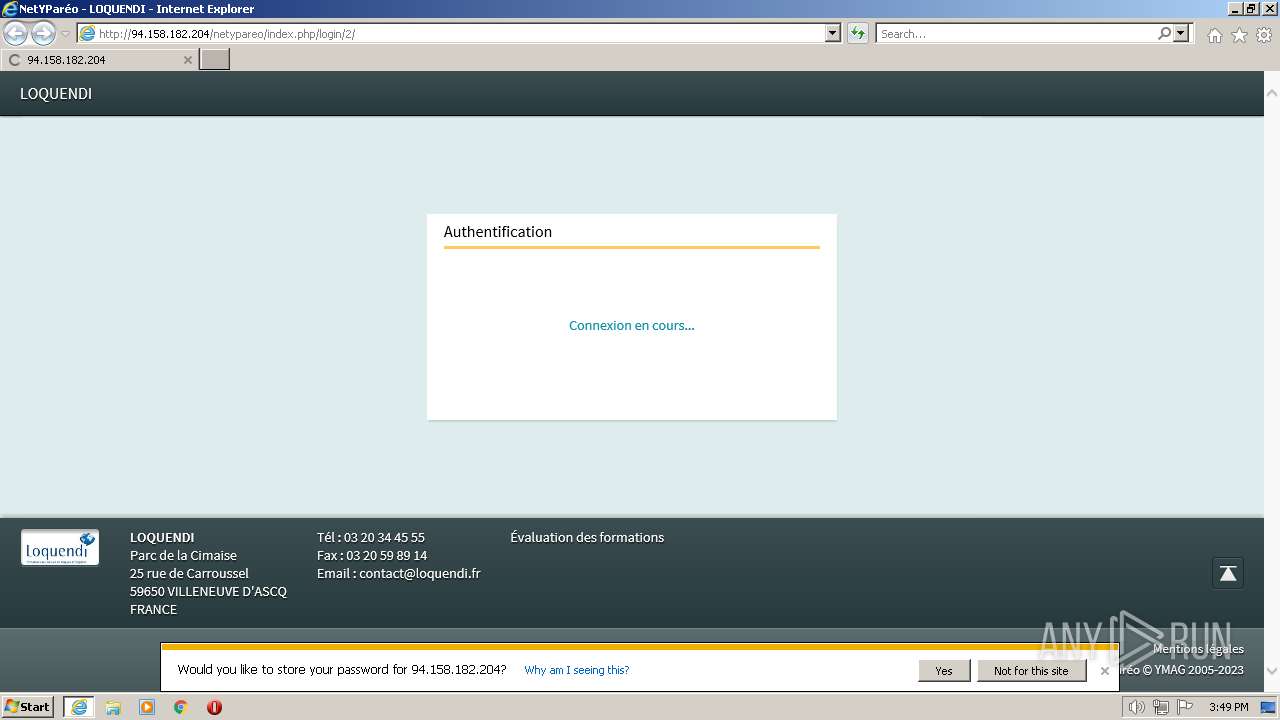
Send credential is detected
- iexplore.exe (PID: 3936)
INFO
Create files in a temporary directory
- iexplore.exe (PID: 2676)
Manual execution by a user
- wmpnscfg.exe (PID: 3096)
The process checks LSA protection
- wmpnscfg.exe (PID: 3096)
Checks supported languages
- wmpnscfg.exe (PID: 3096)
Reads the computer name
- wmpnscfg.exe (PID: 3096)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3096)
Application launched itself
- iexplore.exe (PID: 2676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2676 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://94.158.182.204/netypareo/index.php" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3096 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
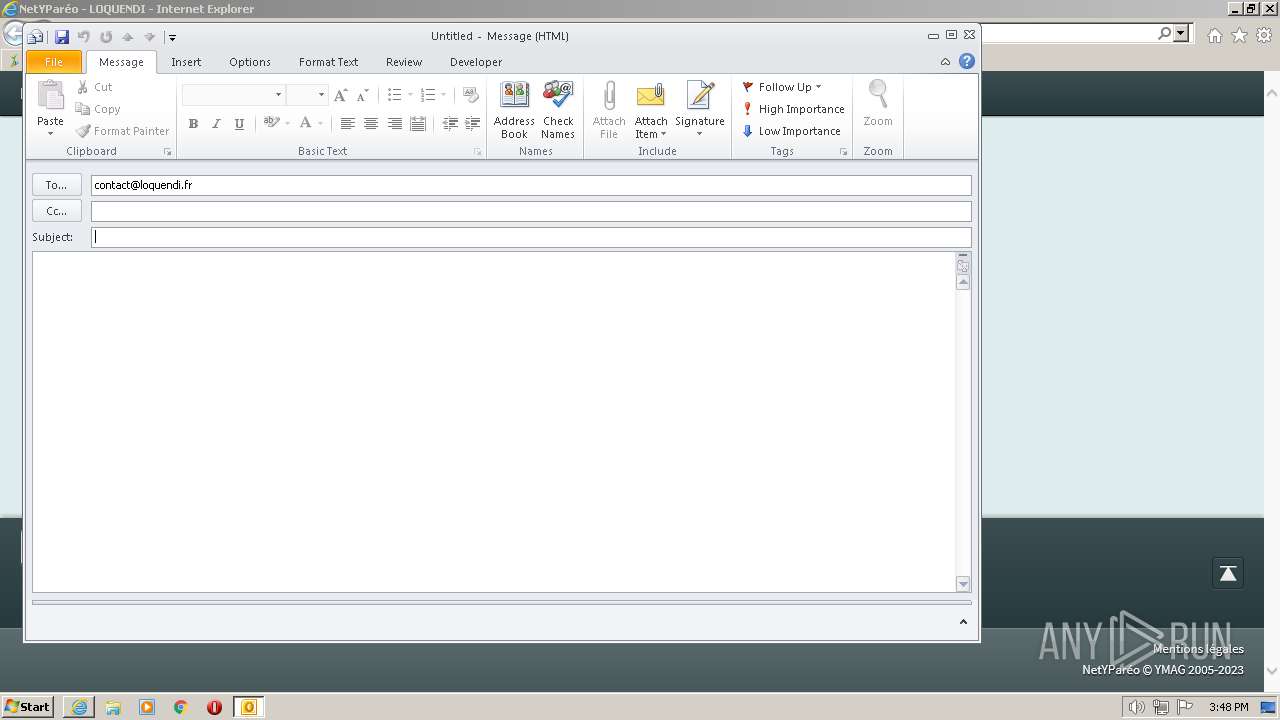
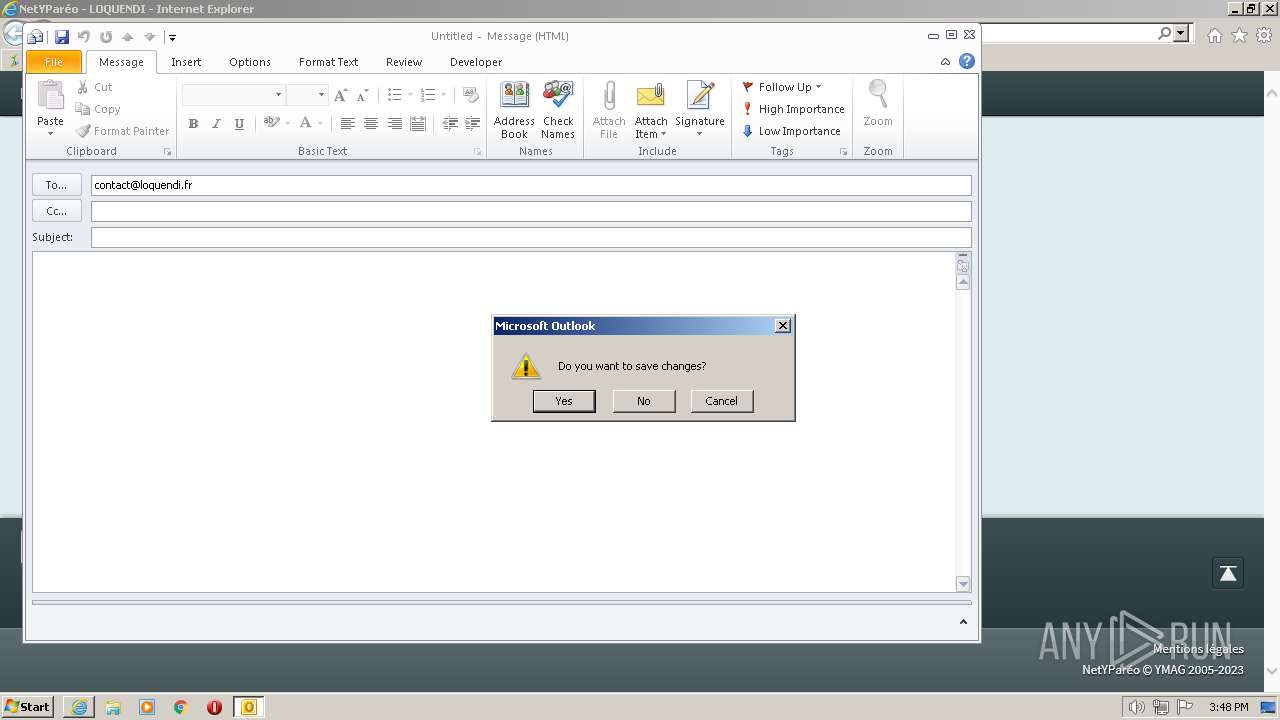
| 3368 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:contact@loquendi.fr" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3636 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:contact@loquendi.fr" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3936 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2676 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
28 784
Read events
27 356
Write events
1 378
Delete events
50
Modification events
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31017063 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31017063 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
20
Text files
60
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\index[1].htm | html | |
MD5:— | SHA256:— | |||
| 3368 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR2DFD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\imagestore\f7ruq93\imagestore.dat | binary | |
MD5:— | SHA256:— | |||
| 3368 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3936 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\styles[1].css | text | |
MD5:98120F4A25E014B67730ABEA5A7E95E6 | SHA256:313362BE073EAB113150C3BC856594988539BD377812716F77266E4FE2EED163 | |||
| 3936 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\DOTBATAV\94.158.182[1].xml | text | |
MD5:C1DDEA3EF6BBEF3E7060A1A9AD89E4C5 | SHA256:B71E4D17274636B97179BA2D97C742735B6510EB54F22893D3A2DAFF2CEB28DB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
20
DNS requests
12
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3936 | iexplore.exe | GET | — | 94.158.182.204:80 | http://94.158.182.204/netypareo/css/styles.css?v=3.14.2 | FR | — | — | suspicious |
3368 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3936 | iexplore.exe | GET | 200 | 94.158.182.204:80 | http://94.158.182.204/netypareo/index.php | FR | html | 2.80 Kb | suspicious |
3936 | iexplore.exe | GET | 200 | 94.158.182.204:80 | http://94.158.182.204/netypareo/css/custom.css?v=3.14.2 | FR | compressed | 67.9 Kb | suspicious |
3936 | iexplore.exe | GET | 200 | 94.158.182.204:80 | http://94.158.182.204/netypareo/css/view/connexion.css?v=3.14.2 | FR | text | 518 b | suspicious |
3936 | iexplore.exe | GET | 200 | 94.158.182.204:80 | http://94.158.182.204/netypareo/css/fonts/SourceSansPro-Light.eot? | FR | eot | 67.9 Kb | suspicious |
3936 | iexplore.exe | GET | 200 | 94.158.182.204:80 | http://94.158.182.204/netypareo/images/sprites/build/picto-white_1633428425729.png | FR | image | 17.7 Kb | suspicious |
3936 | iexplore.exe | GET | 200 | 94.158.182.204:80 | http://94.158.182.204/netypareo/css/fonts/SourceSansPro-Regular.eot? | FR | eot | 68.0 Kb | suspicious |
3936 | iexplore.exe | GET | 200 | 94.158.182.204:80 | http://94.158.182.204/netypareo/images/icon-nobody/nobody.png | FR | image | 2.92 Kb | suspicious |
3936 | iexplore.exe | GET | 200 | 94.158.182.204:80 | http://94.158.182.204/netypareo/js/vendor/modernizr.min.js?v=3.14.2 | FR | text | 2.47 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3936 | iexplore.exe | 94.158.182.204:80 | — | Avenir Telematique SAS | FR | suspicious |
2676 | iexplore.exe | 94.158.182.204:80 | — | Avenir Telematique SAS | FR | suspicious |
2676 | iexplore.exe | 2.16.187.98:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
2676 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
2676 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3368 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2676 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.messenger.msn.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
4 ETPRO signatures available at the full report