| File name: | RED2.exe |
| Full analysis: | https://app.any.run/tasks/4fdf7b00-571a-41b9-bf88-93204f76983e |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2024, 18:18:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 75F6CD0423C6ADB5640828FF7FBDAE19 |
| SHA1: | E5A151B1C735436F25E82BF5292D672A236C6180 |
| SHA256: | 1F778ACC4D56B96437A084B9D8FB2DBEC6CB8AFB67E9D29FFA3653591ABFAA48 |
| SSDEEP: | 3072:eDNOGY/pu8//rIWRrizmUxkZ2zB61wQ8b77/pu8//rIWRr:SOGY/pu8/jBRrl2lYM/pu8/jBRr |
MALICIOUS
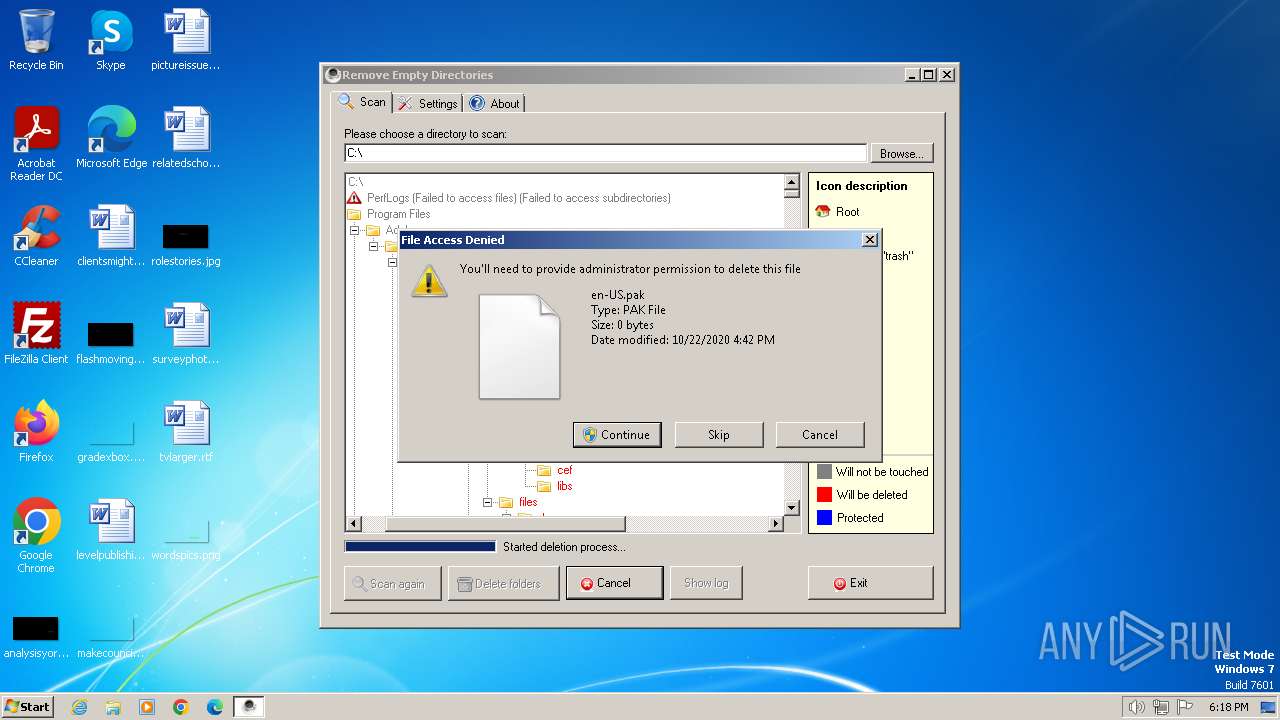
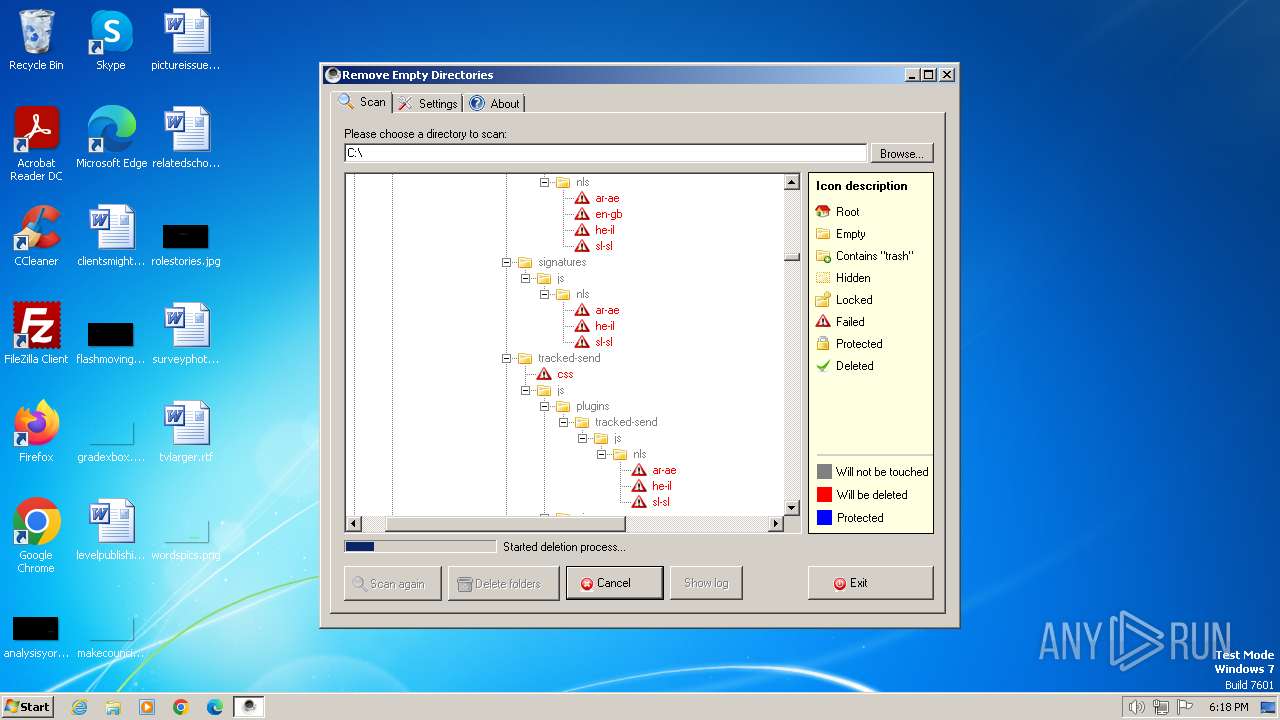
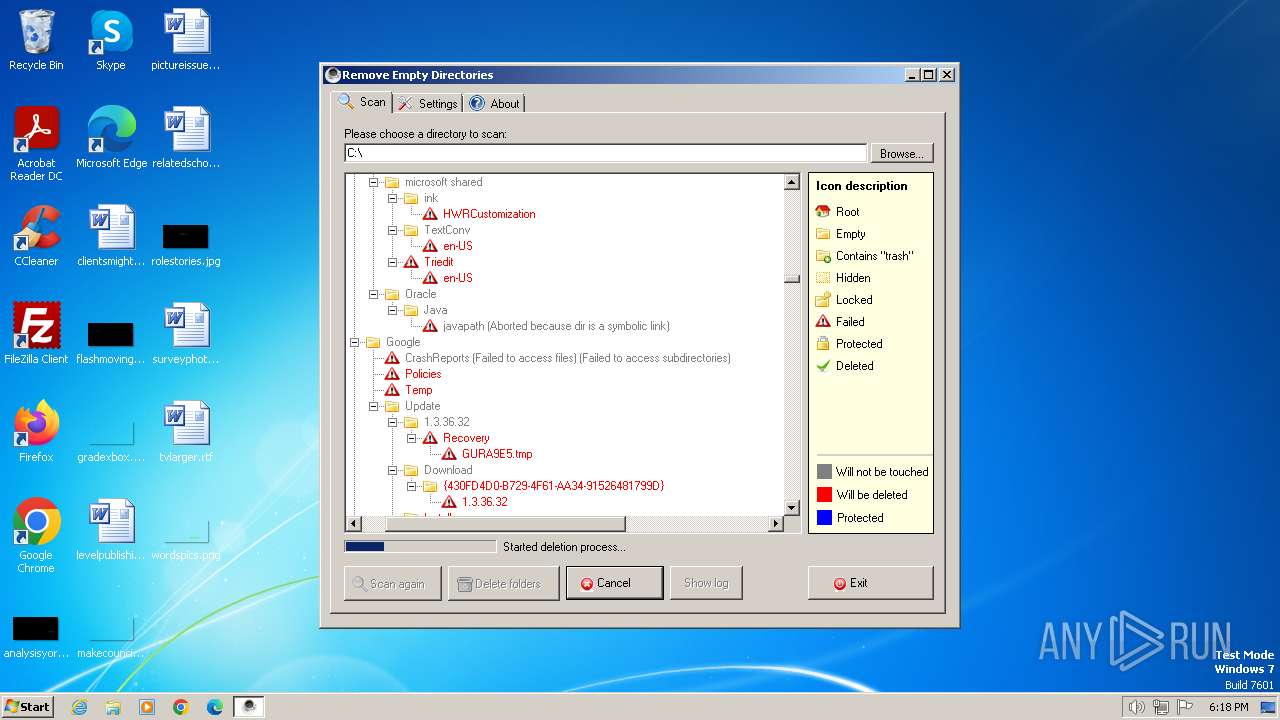
Drops the executable file immediately after the start
- RED2.exe (PID: 2040)
Actions looks like stealing of personal data
- RED2.exe (PID: 2040)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- RED2.exe (PID: 2040)
Checks transactions between databases Windows and Oracle
- RED2.exe (PID: 2040)
Reads the computer name
- RED2.exe (PID: 2040)
Reads the machine GUID from the registry
- RED2.exe (PID: 2040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:02:06 20:07:42+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 133120 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2267e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
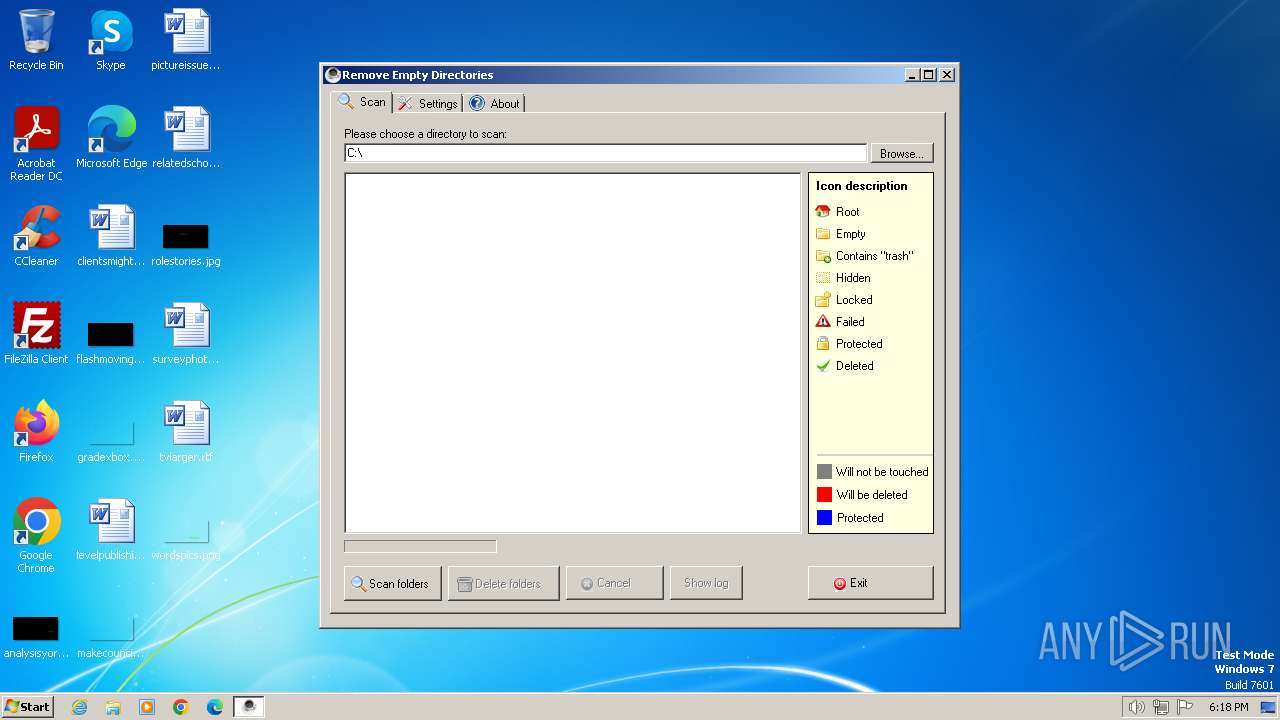
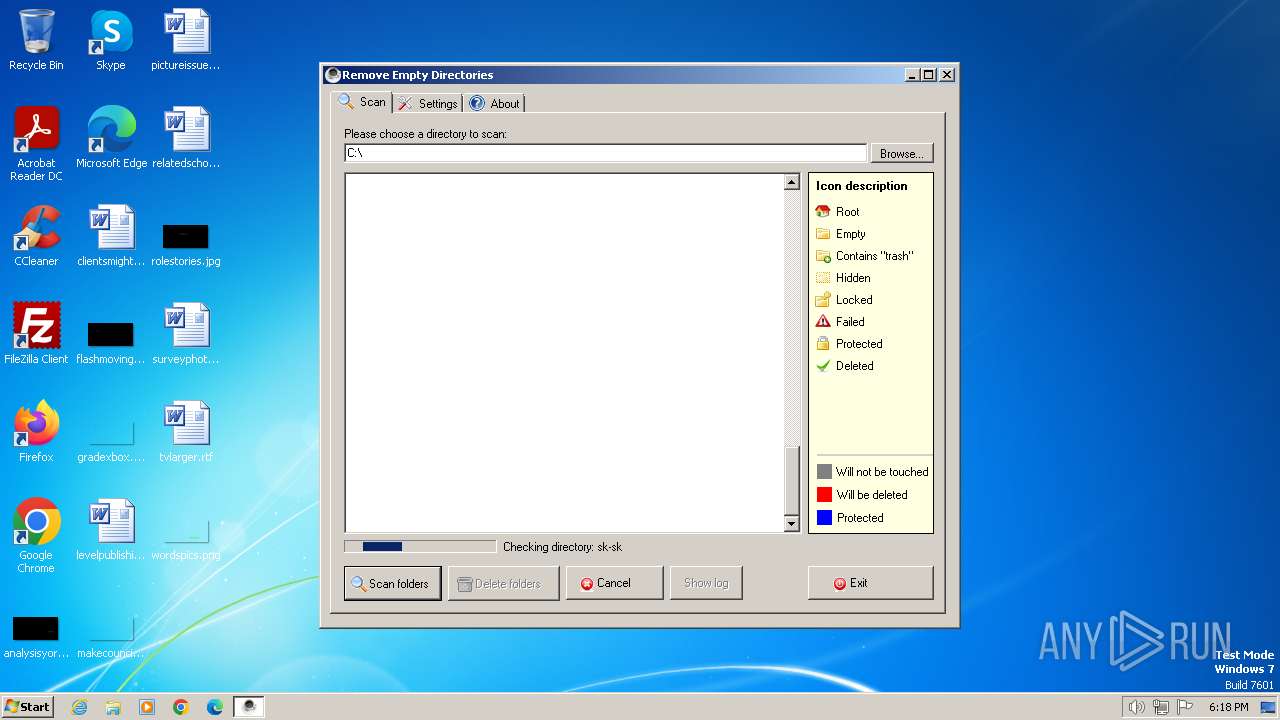
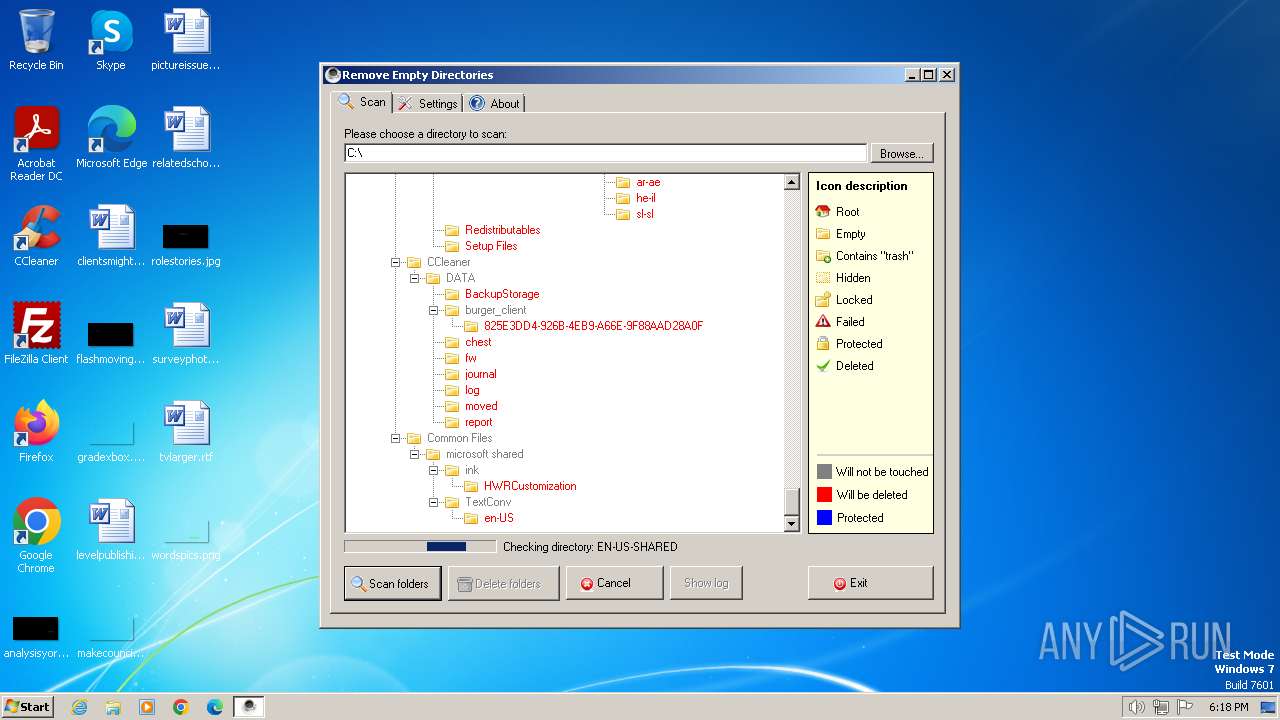
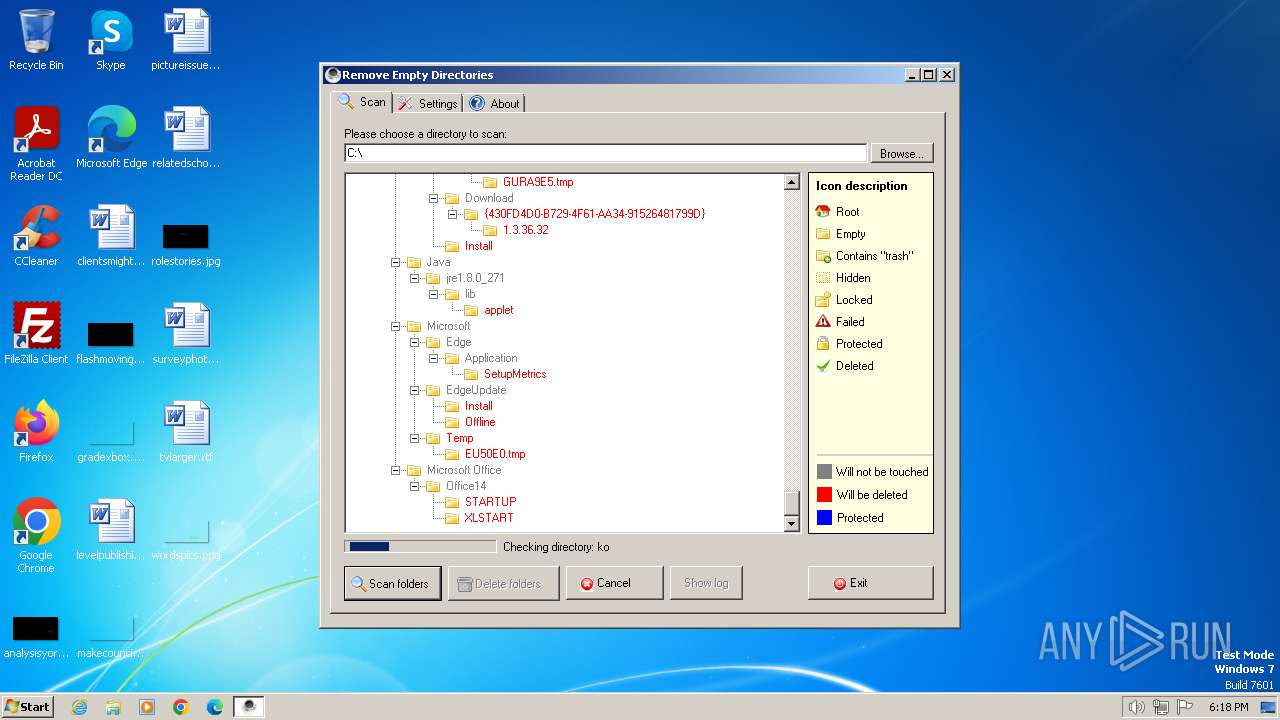
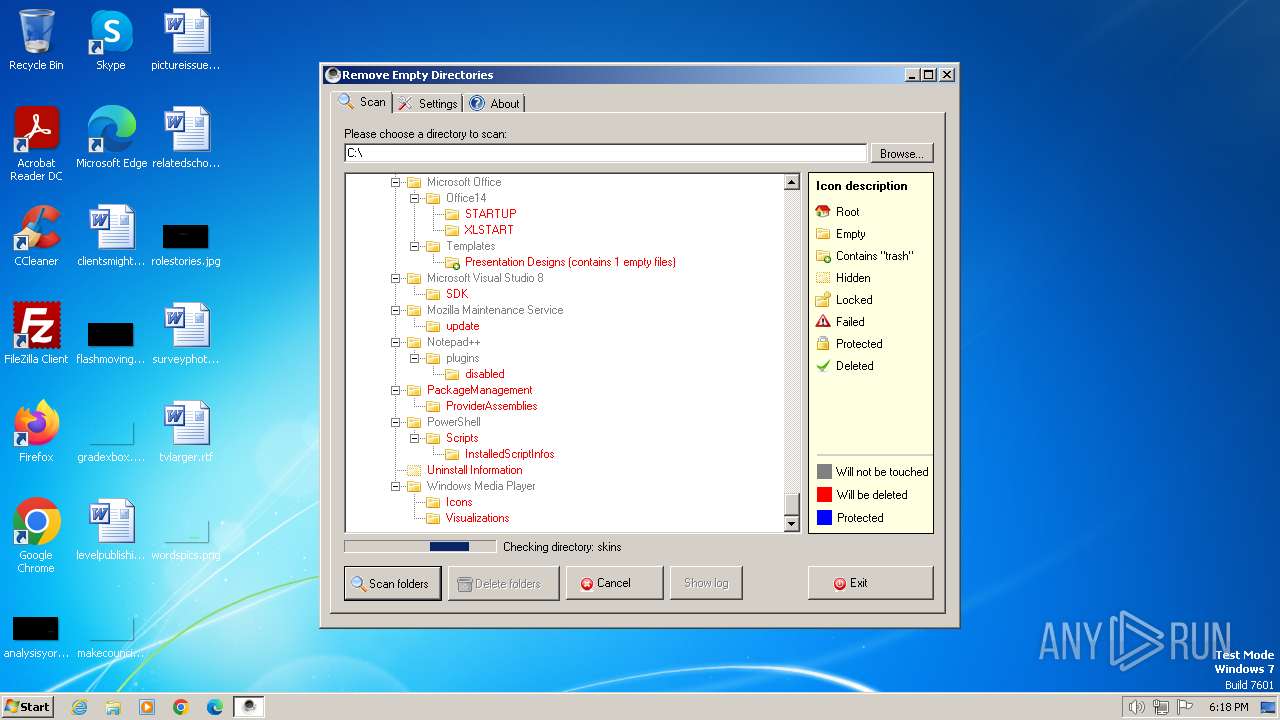
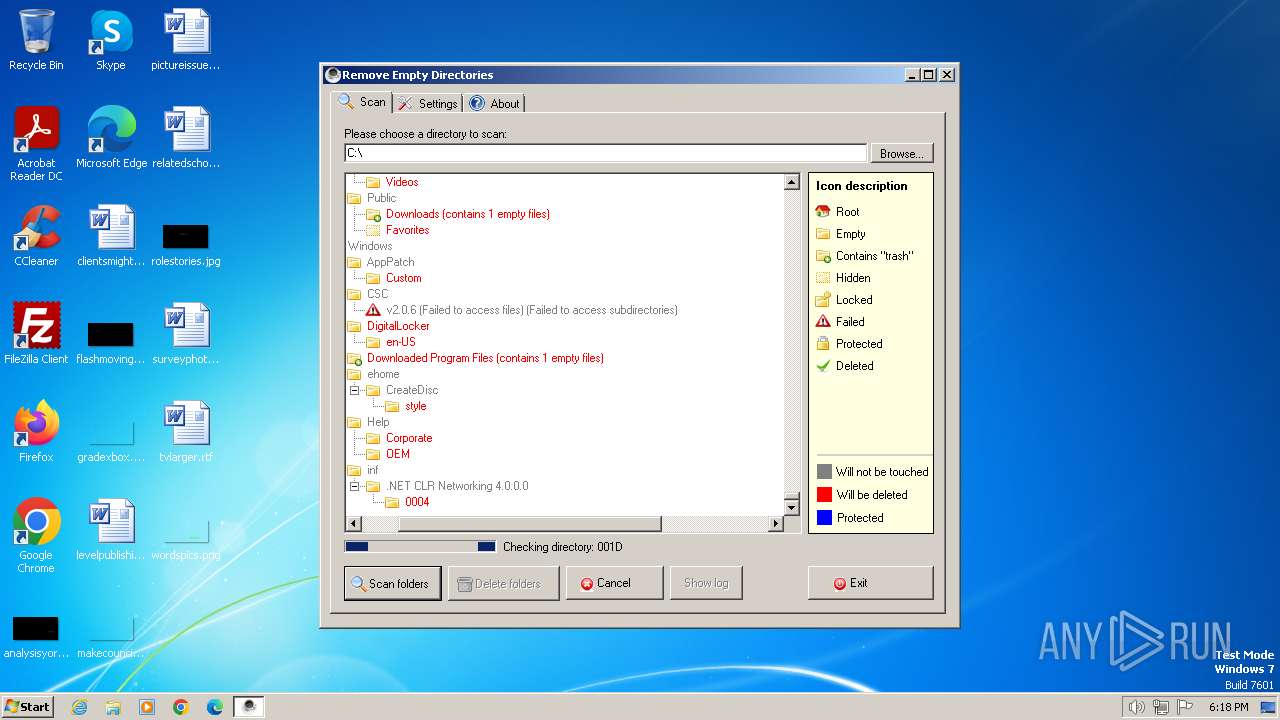
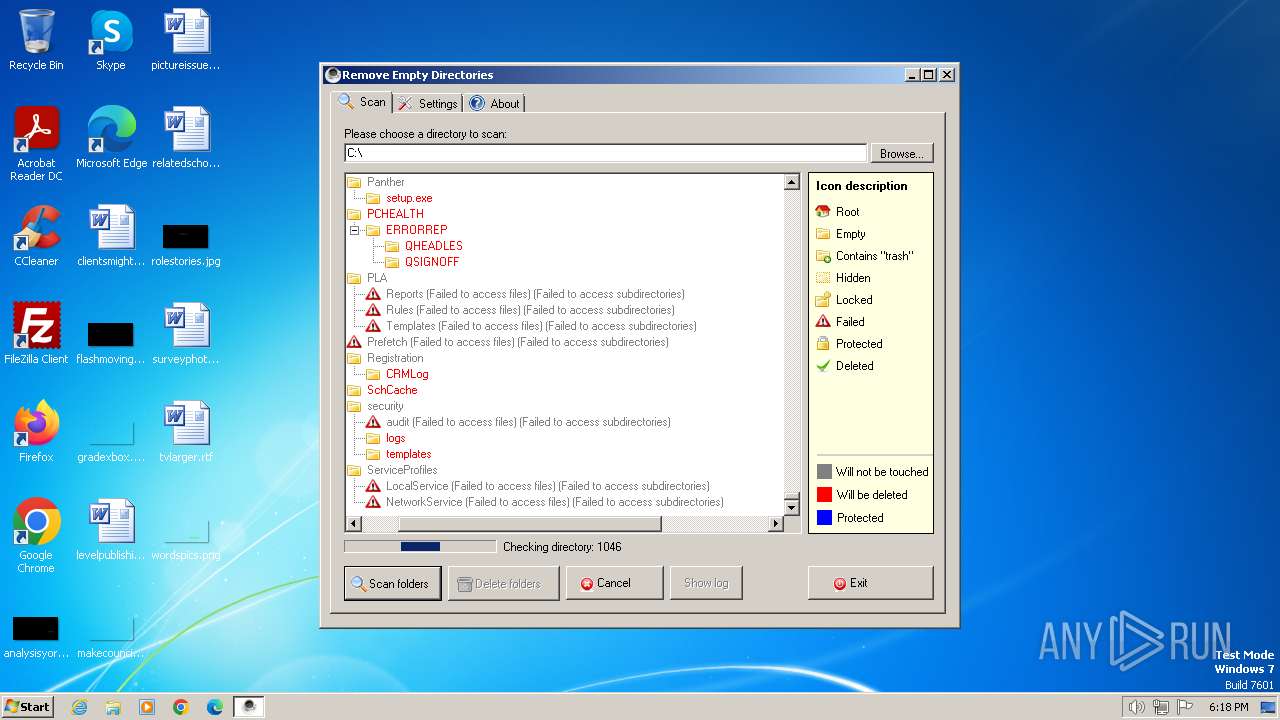
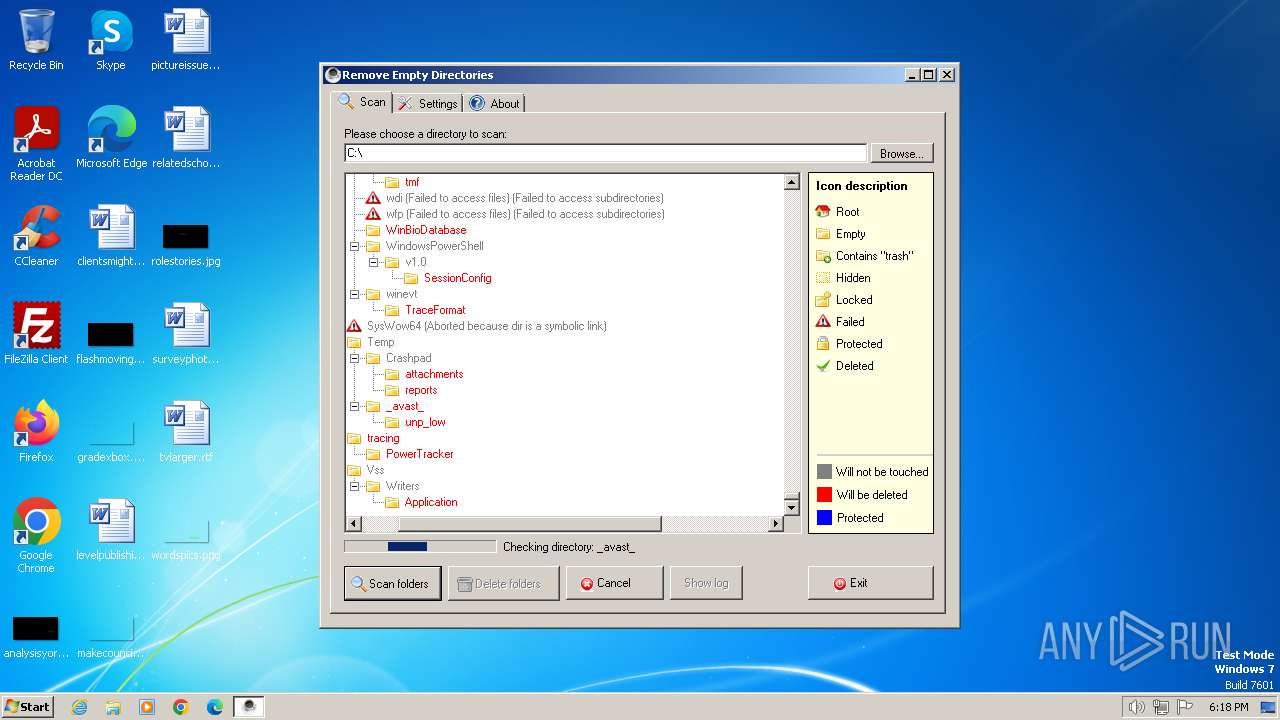
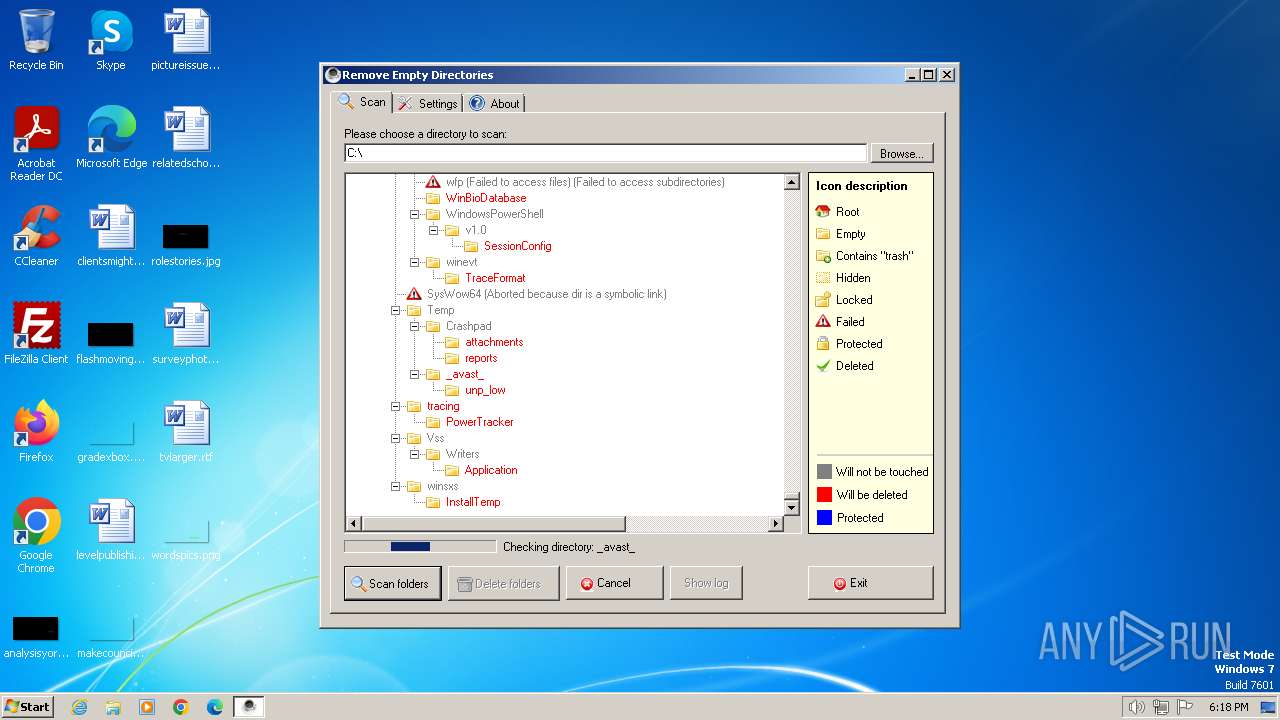
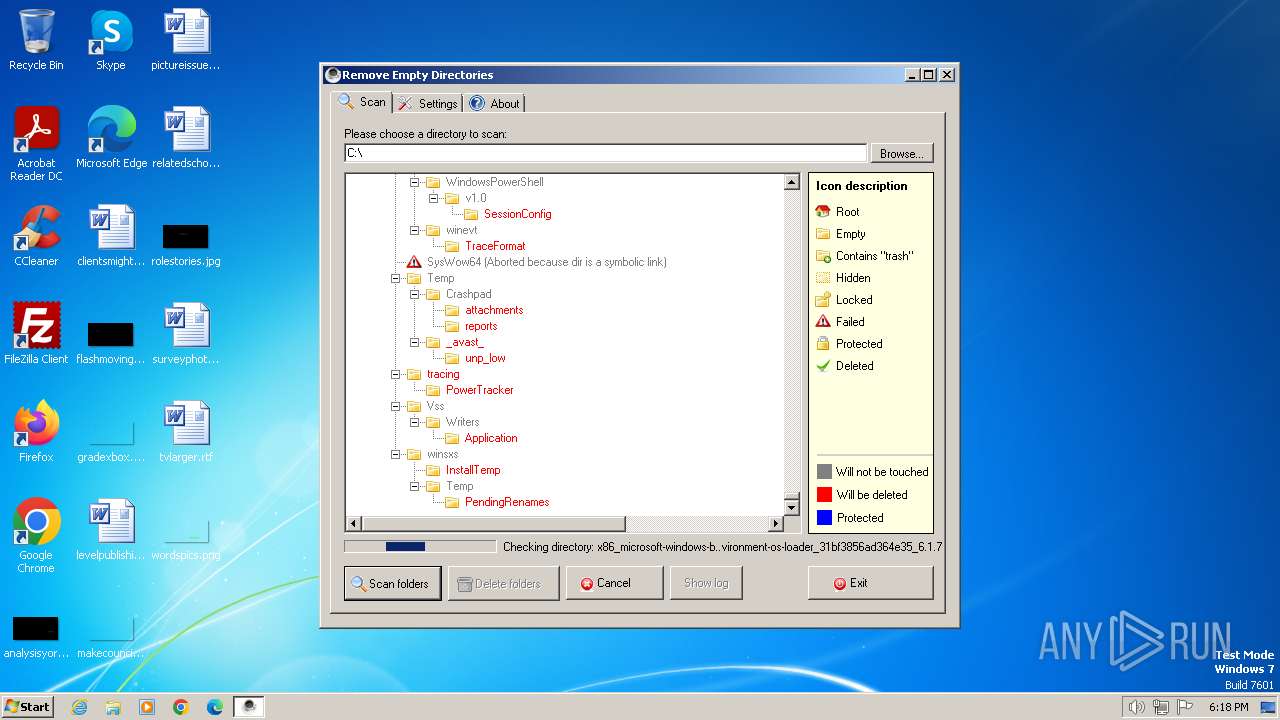
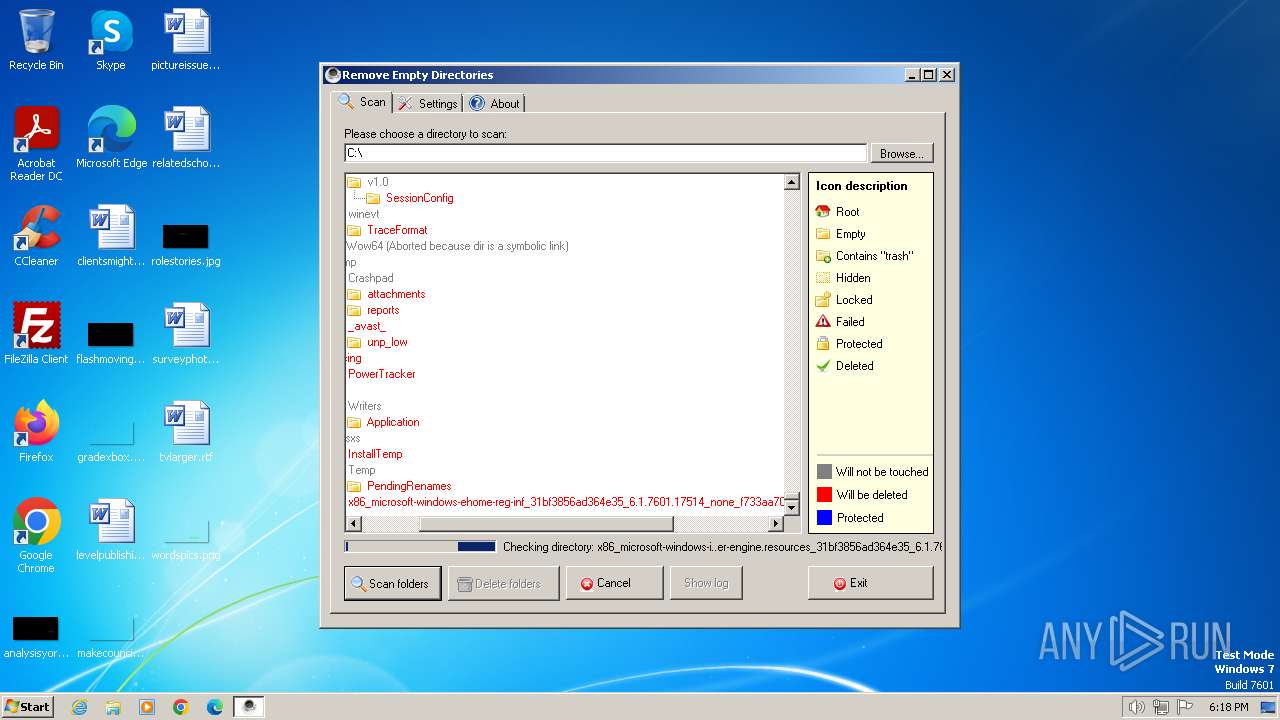
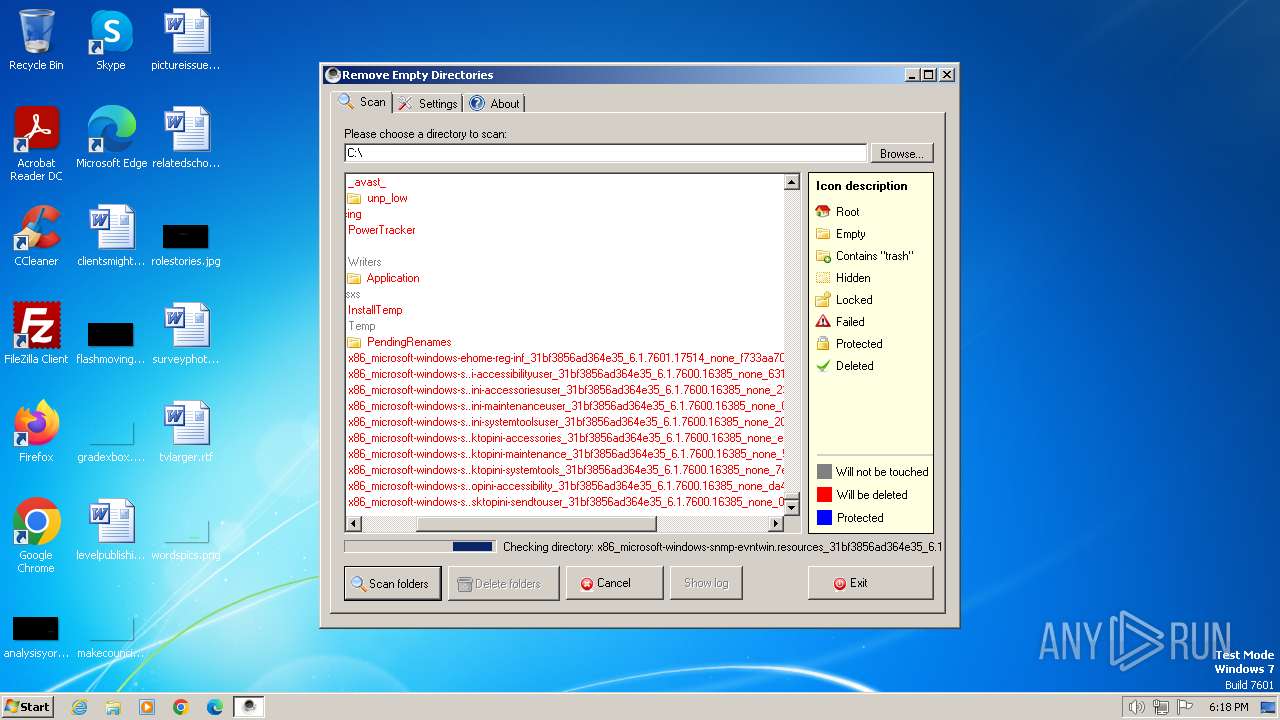
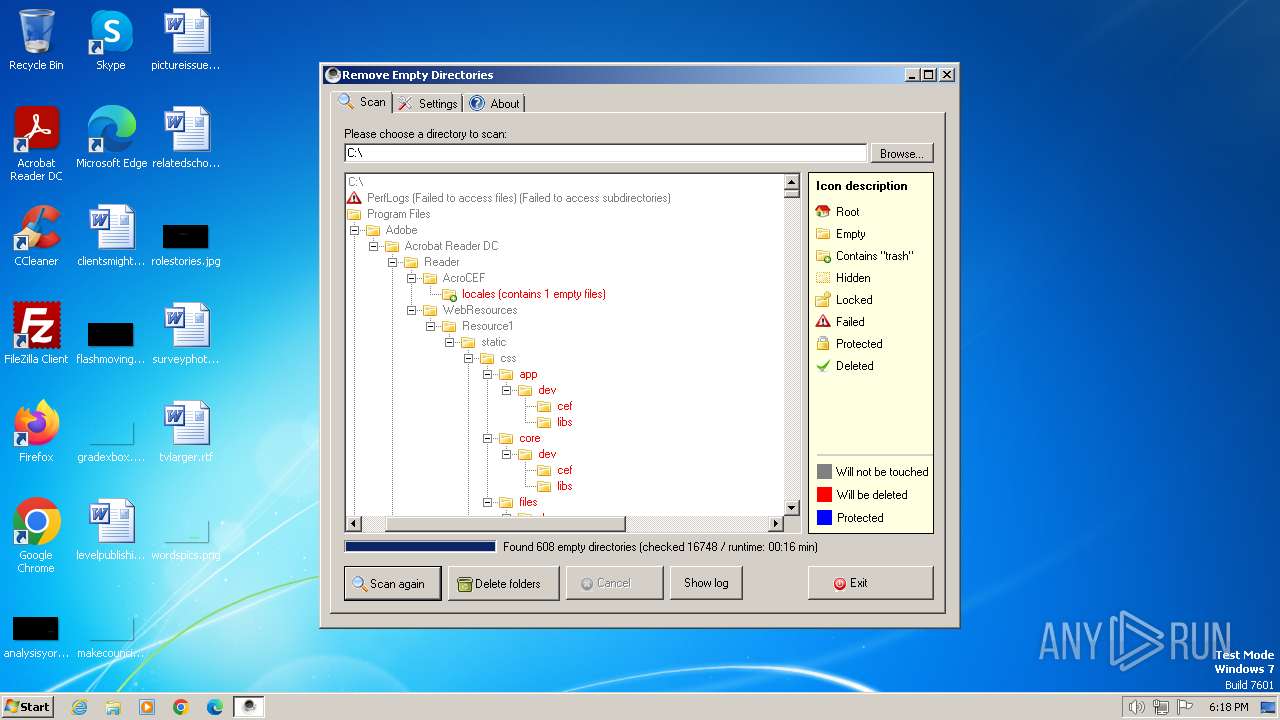
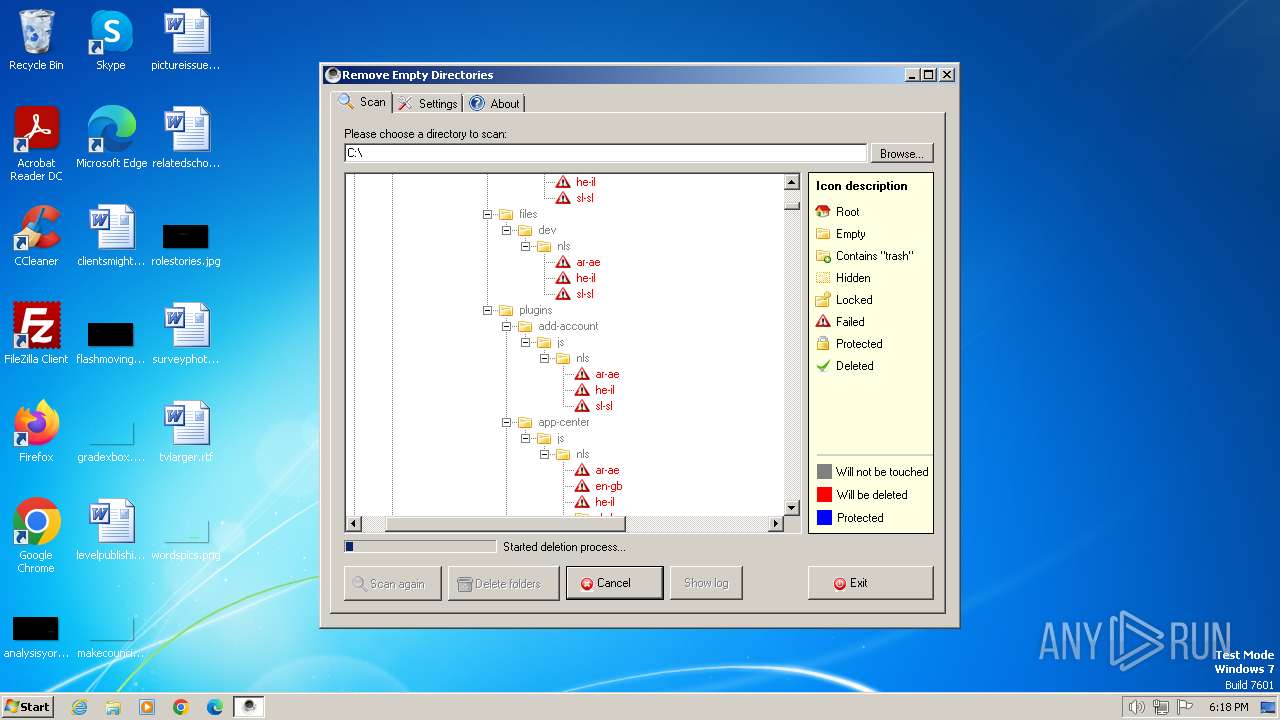
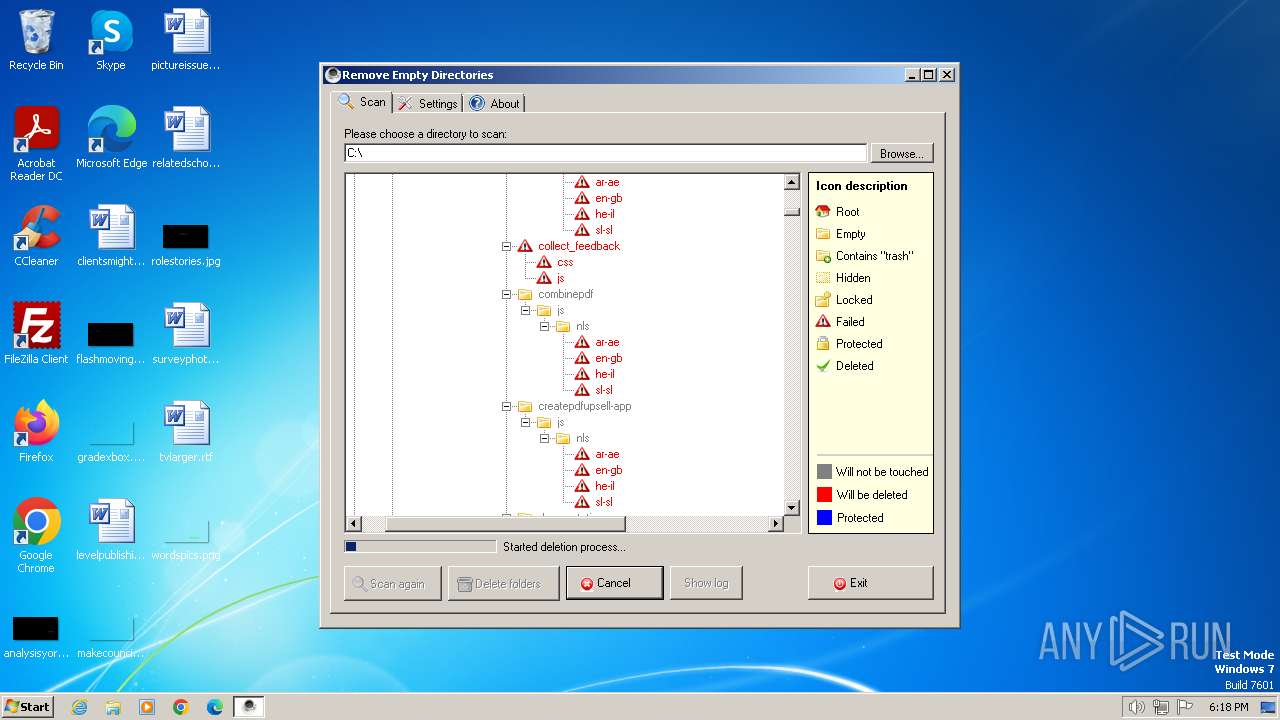
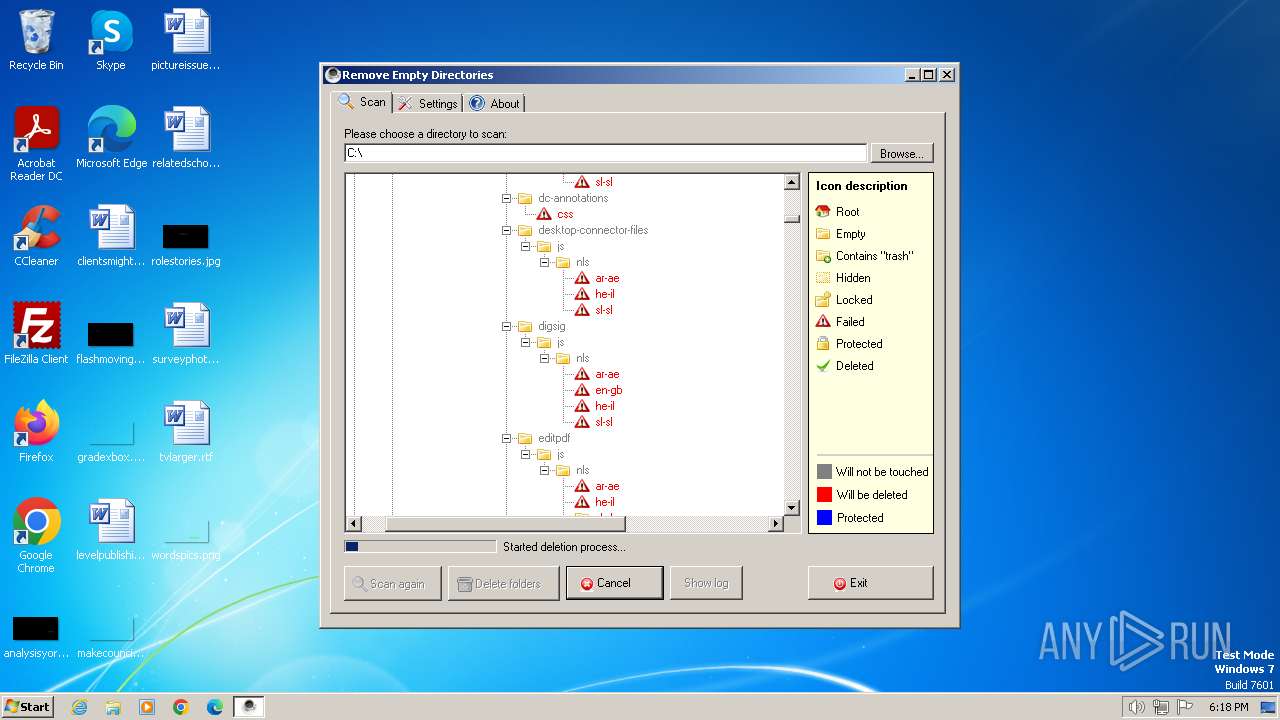
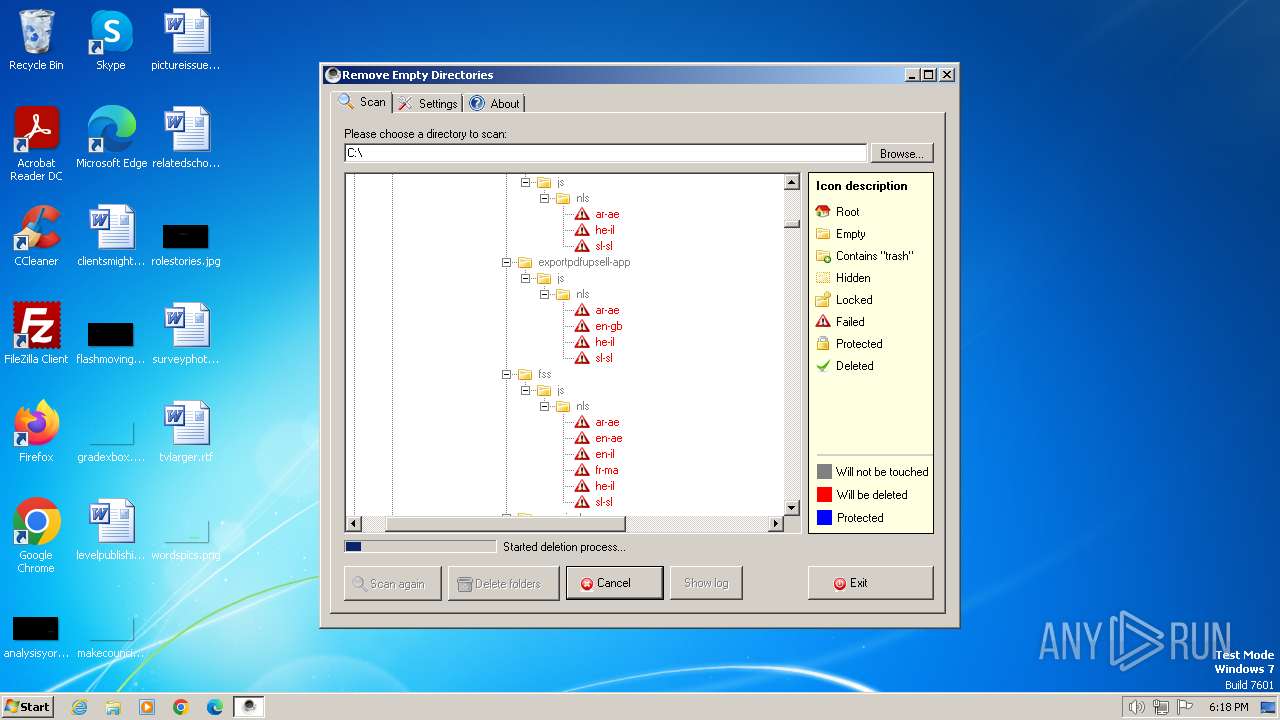
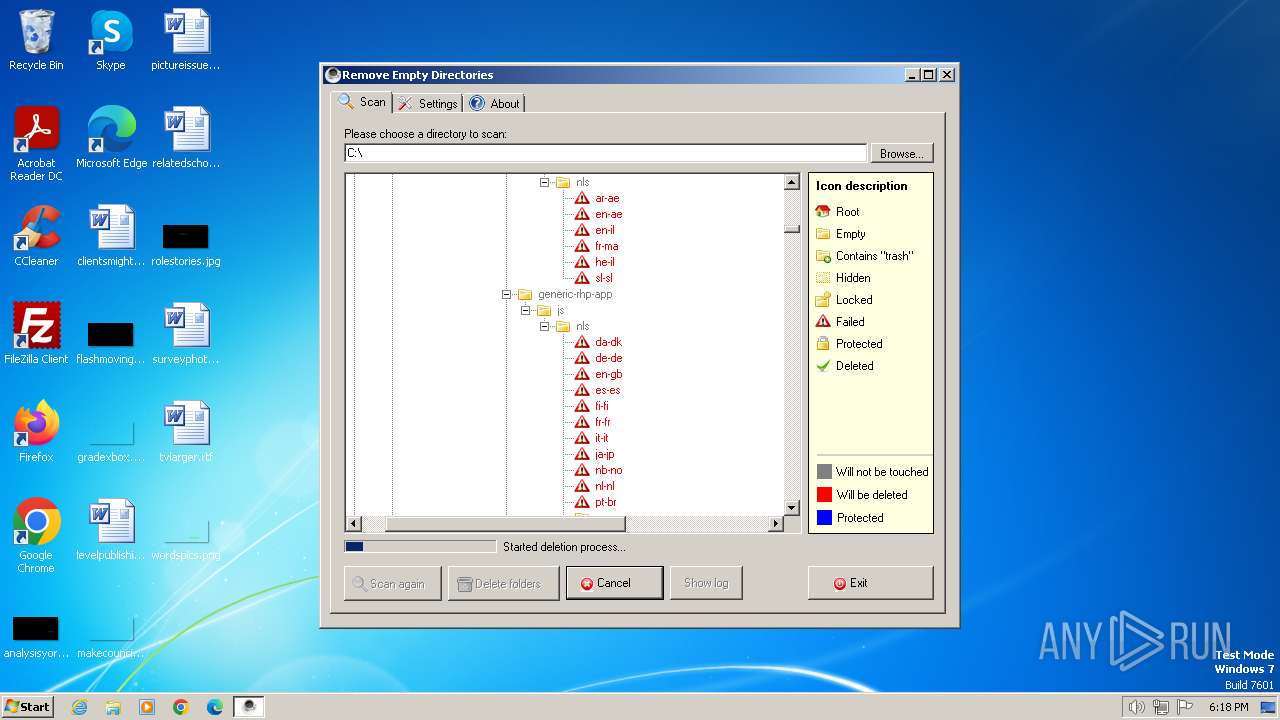
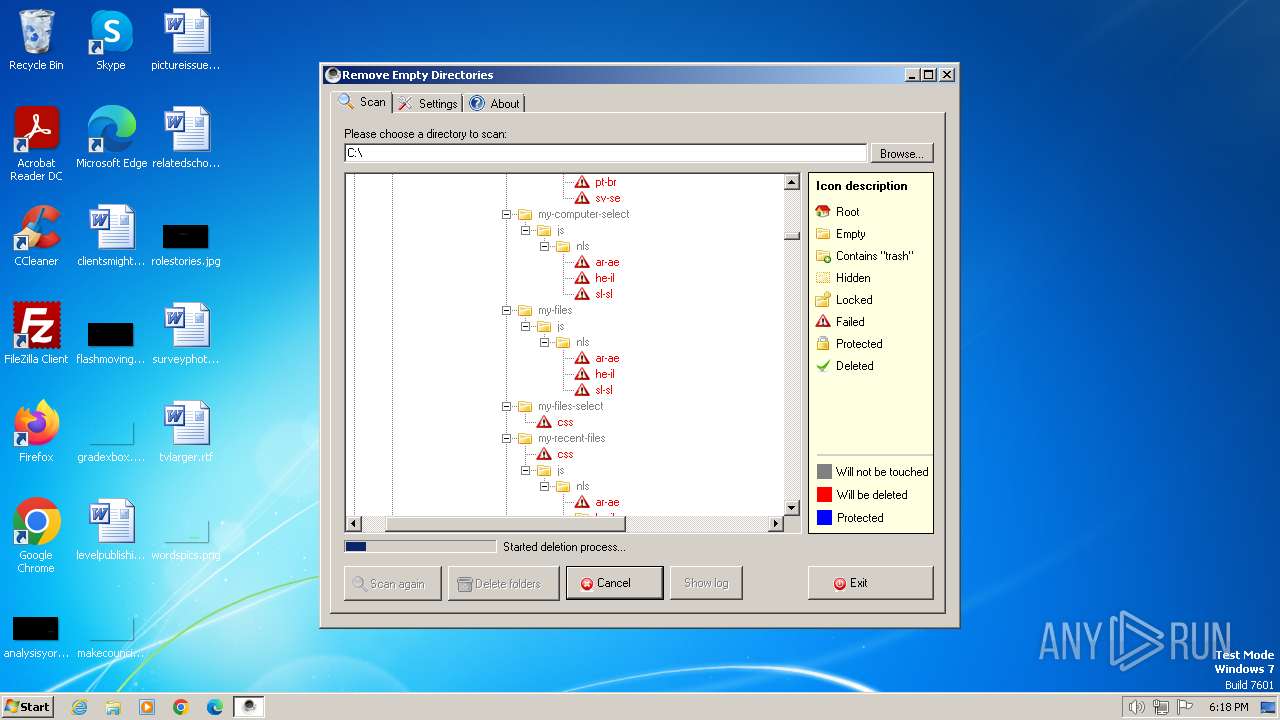
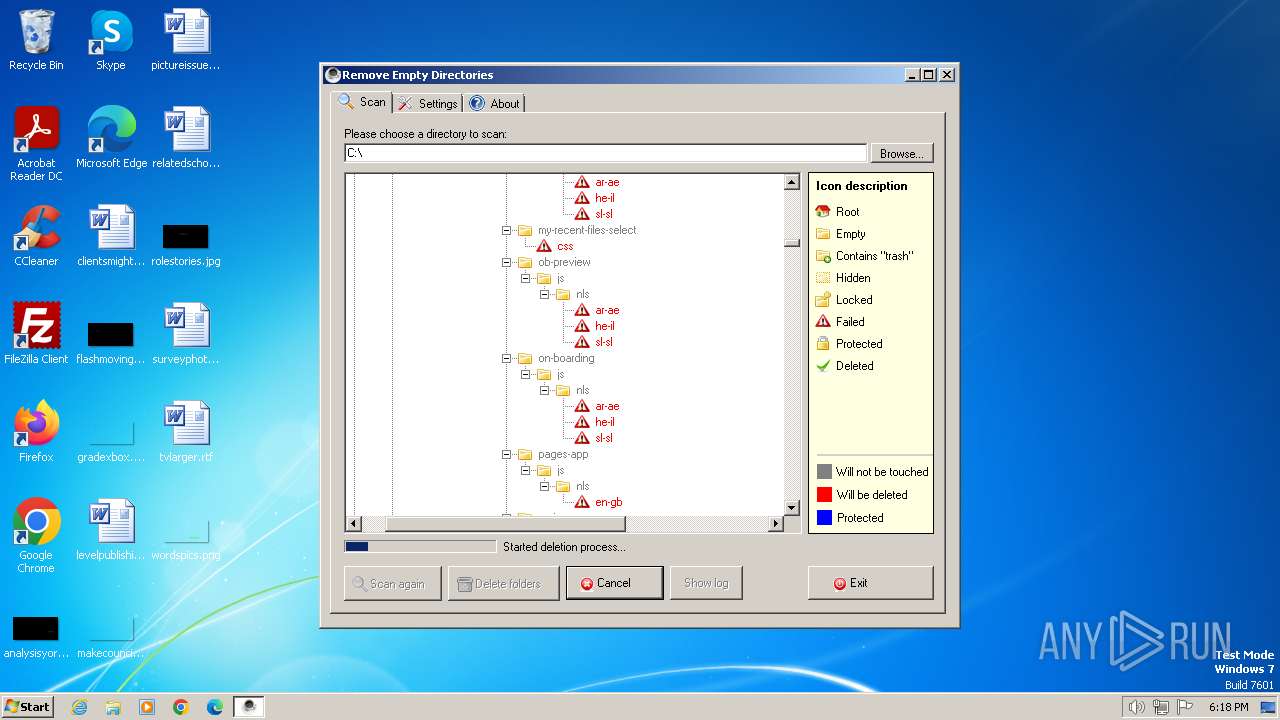
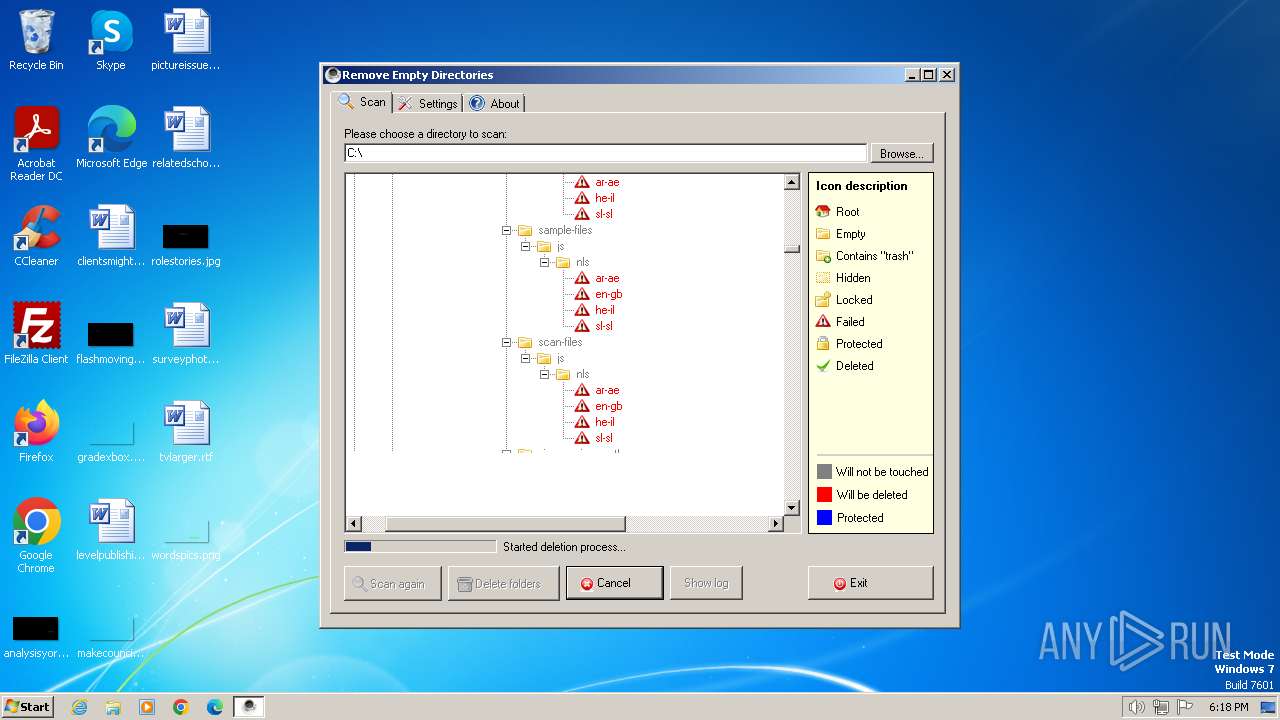
| Comments: | RED searches and deletes empty directories recursively below a given start folder. |
| CompanyName: | Remove Empty Directories |
| FileDescription: | Remove Empty Directories |
| FileVersion: | 2.2.0.0 |
| InternalName: | RED2.exe |
| LegalCopyright: | Copyright (c) Jonas John 2005-2011 |
| LegalTrademarks: | Remove Empty Directories |
| OriginalFileName: | RED2.exe |
| ProductName: | Remove Empty Directories |
| ProductVersion: | 2.2.0.0 |
| AssemblyVersion: | 2.2.0.0 |
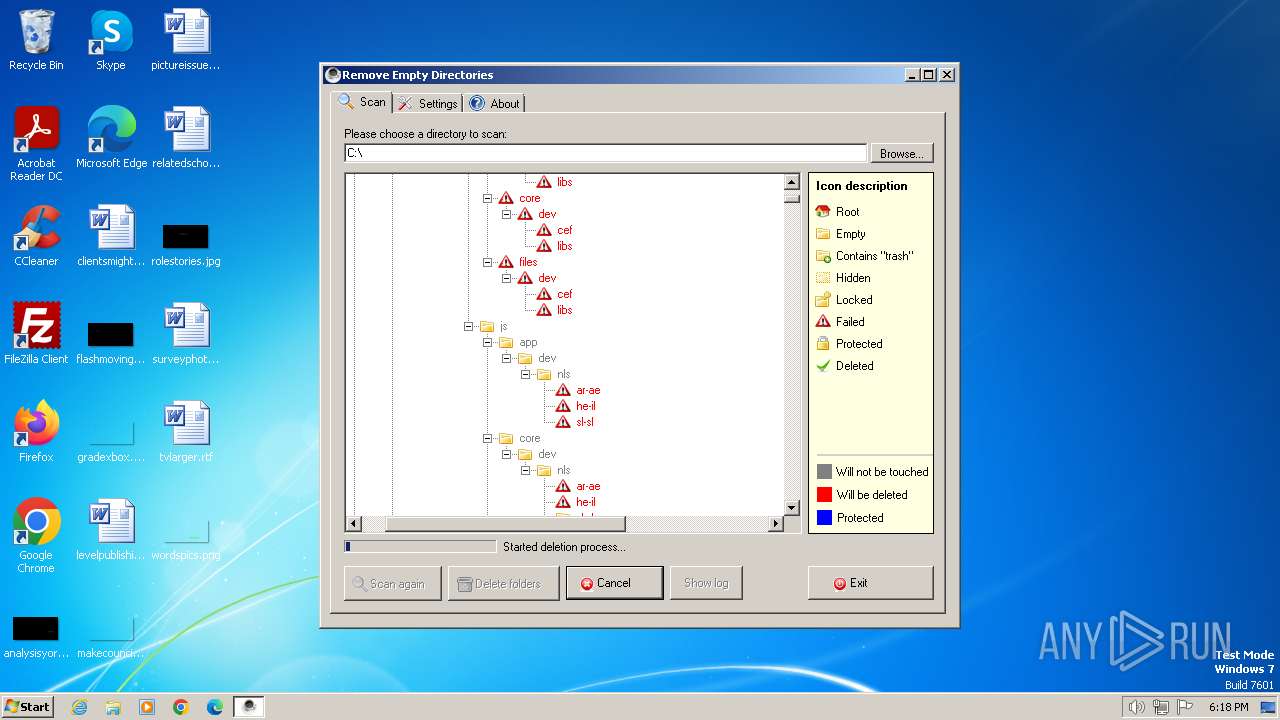
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1592 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 2040 | "C:\Users\admin\AppData\Local\Temp\RED2.exe" | C:\Users\admin\AppData\Local\Temp\RED2.exe | explorer.exe | ||||||||||||
User: admin Company: Remove Empty Directories Integrity Level: MEDIUM Description: Remove Empty Directories Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
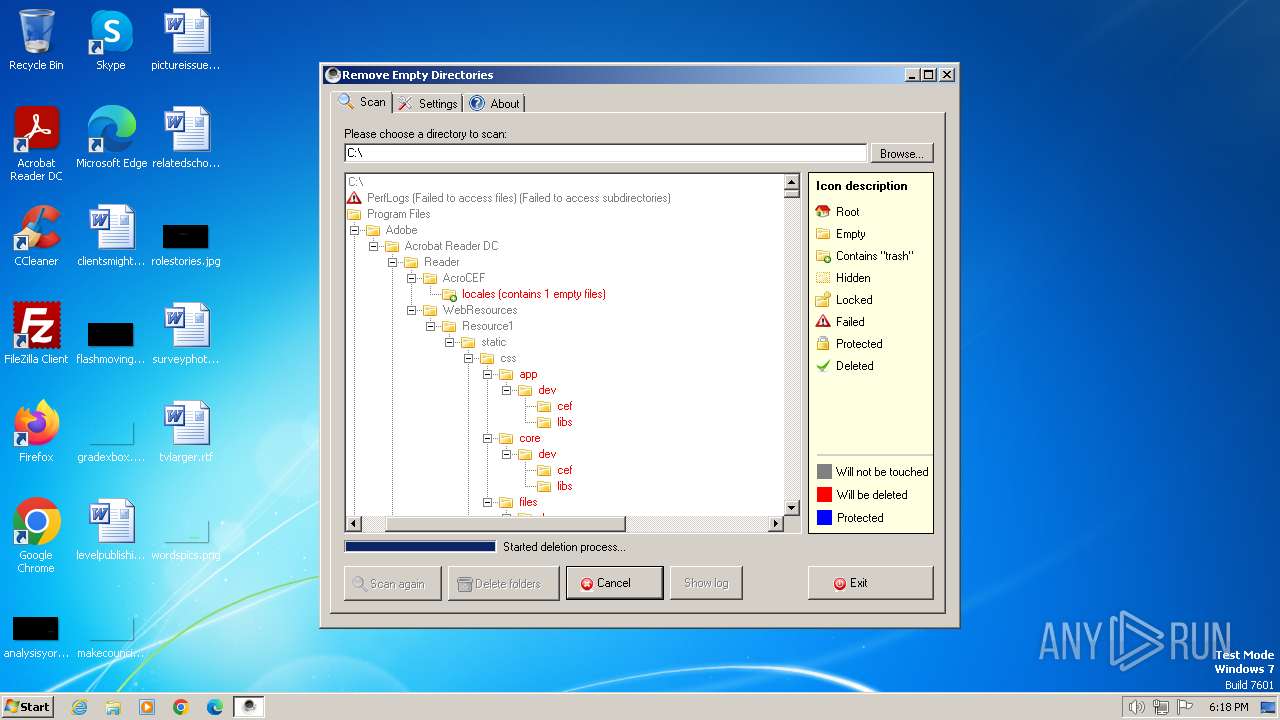
Total events
1 071
Read events
1 070
Write events
0
Delete events
1
Modification events
| (PID) Process: | (2040) RED2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{e1a82db4-a9f0-11e7-b142-806e6f6e6963} |
| Operation: | delete value | Name: | NeedToPurge |
Value: 1 | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 268 | dllhost.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\$RA7CCGX.pak | — | |
MD5:— | SHA256:— | |||
| 1592 | dllhost.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\$RRX1SJZ.gif | — | |
MD5:— | SHA256:— | |||
| 2040 | RED2.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\$RT8HLE2 | — | |
MD5:— | SHA256:— | |||
| 2040 | RED2.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\$REUHJ39 | — | |
MD5:— | SHA256:— | |||
| 2040 | RED2.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\$R8TC3OR.old | — | |
MD5:— | SHA256:— | |||
| 268 | dllhost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$IA7CCGX.pak | binary | |
MD5:A050B1D4FADD5D493FA3E5228FD6BB00 | SHA256:AD1B001F144C05773179AAFA52A56321A87B78D9924F8C42E464D154418E18C7 | |||
| 2040 | RED2.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$I4L67NT.20064 | cdxl | |
MD5:5C9AD31D2794DC01A30474B796B2677C | SHA256:6BC15471C240C5F09D08EBA84FC4824F1F697B858C7476809616DA4F07AEF4B0 | |||
| 1592 | dllhost.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$IRX1SJZ.gif | cdxl | |
MD5:D4F07AB8DE9AA1827E5882BBC2EF8210 | SHA256:C5C9AFADE9A669434508F54EC72F0253FD8F3EEF04BA148A31EDDC99F2641954 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |