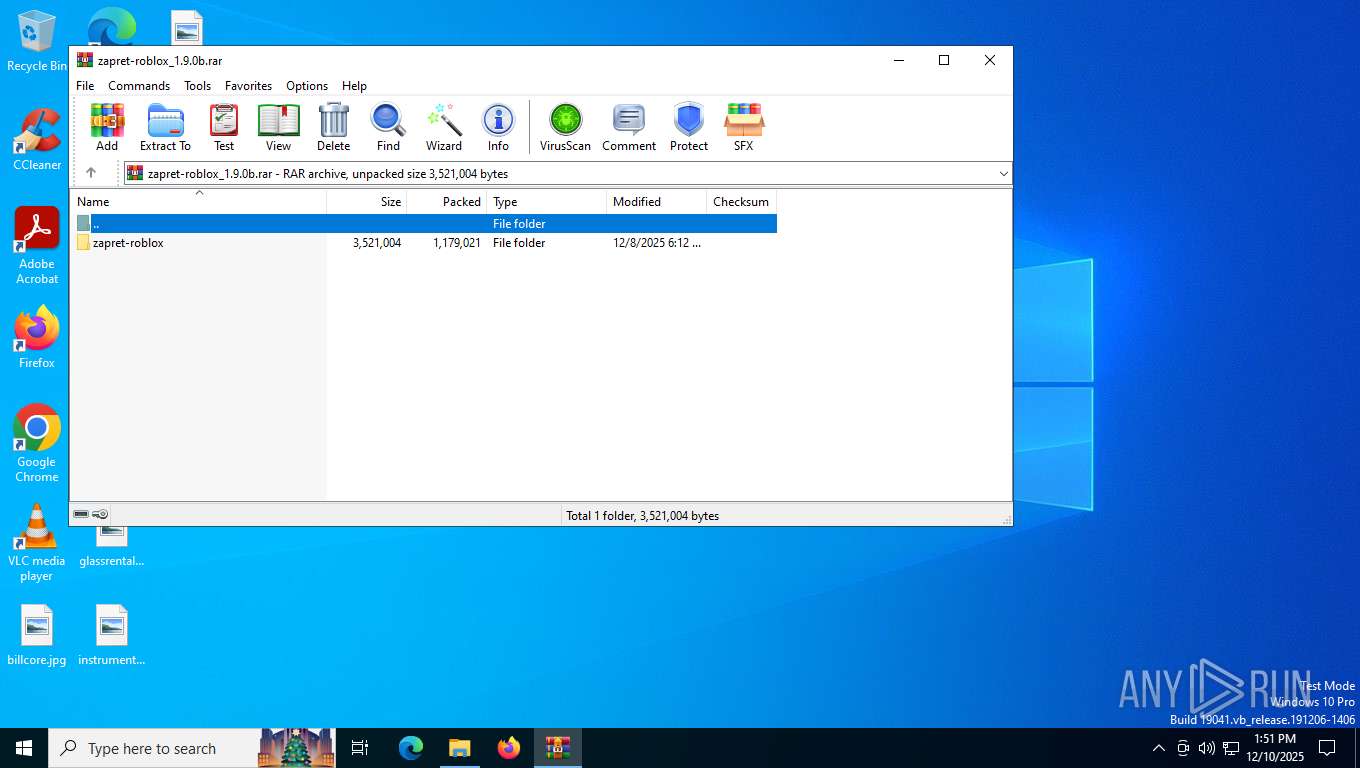
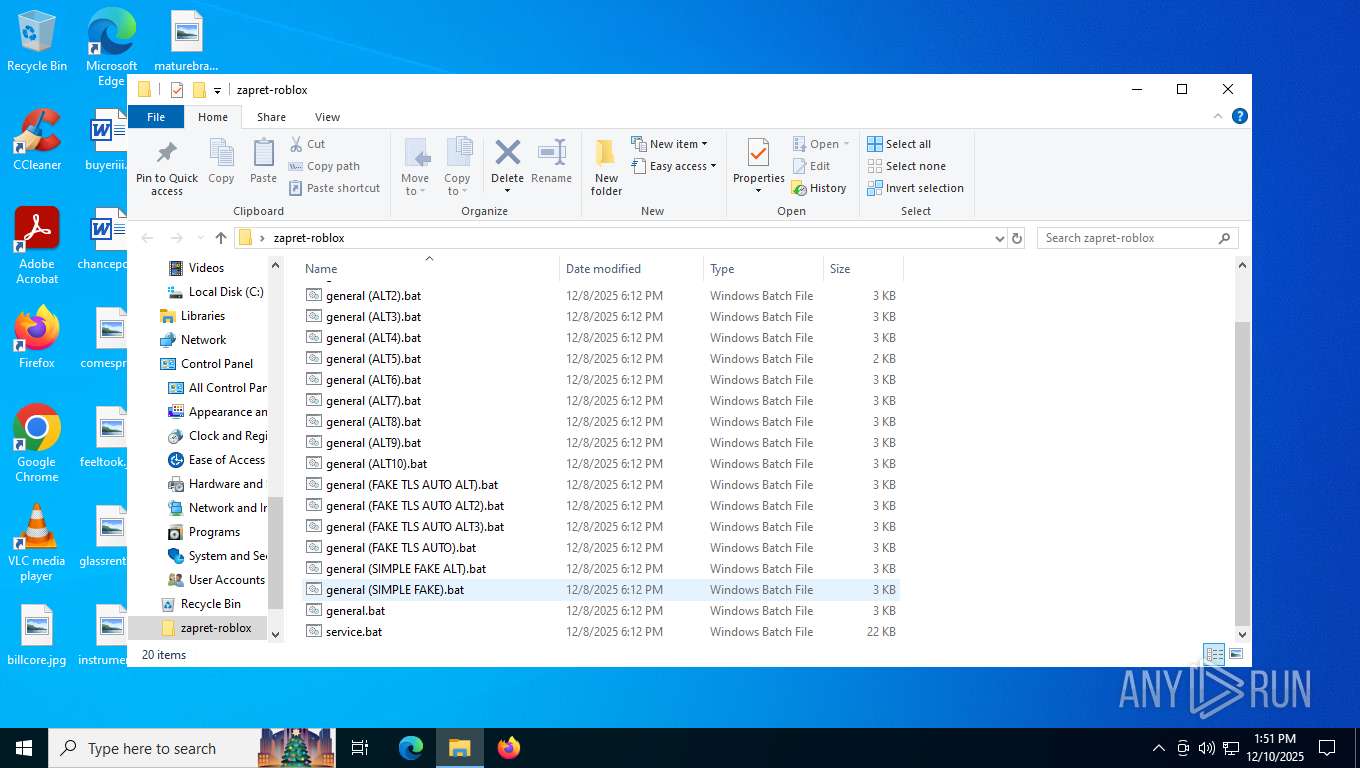
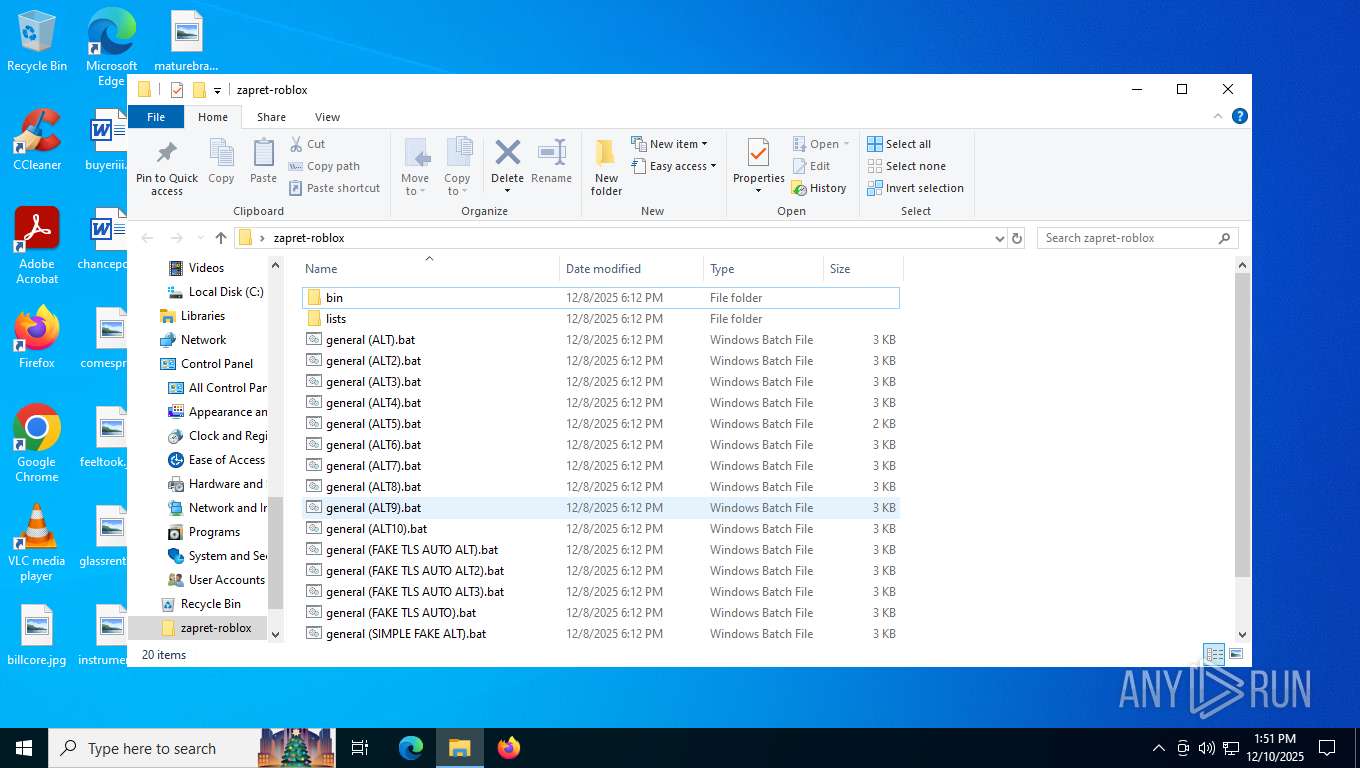
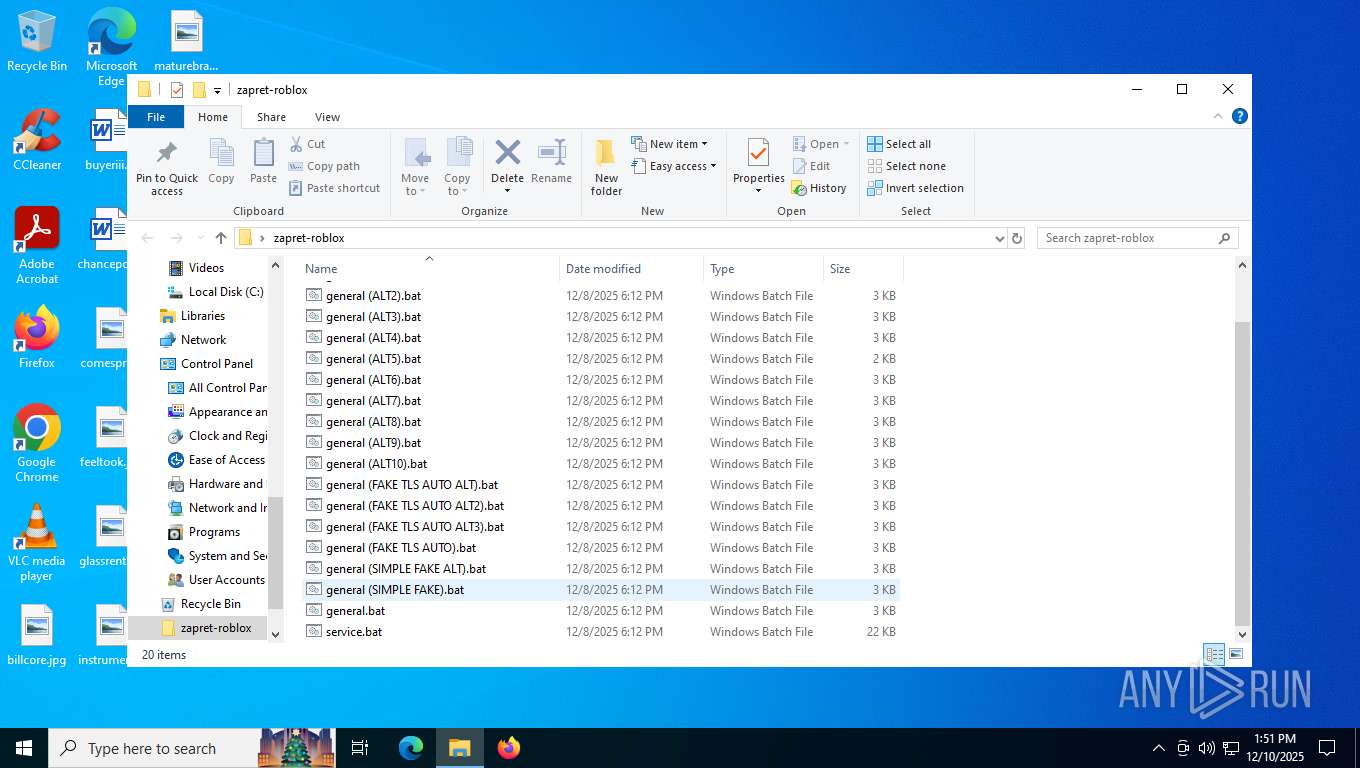
| File name: | zapret-roblox_1.9.0b.rar |
| Full analysis: | https://app.any.run/tasks/0818c59b-4704-4782-be93-45c7f1dfabaa |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2025, 13:51:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 1243A6143E8996A7BB58A67D9256CC7C |
| SHA1: | DFADCB33931CBB779766F05787C5A0BD321320D8 |
| SHA256: | 1F7229BE0BF5A29F6990A8EF1D6B14D4203F76FB7D0A278500298F578B3C3053 |
| SSDEEP: | 49152:sb4FMyNCQMf5udb/DNj7Ze9rm45sDC69wDe1fwTCFvppsBS9VWIwQtkcTSHWdvpo:sb4utV58b/Jj789rv5D6uDefjFvppr9a |
MALICIOUS
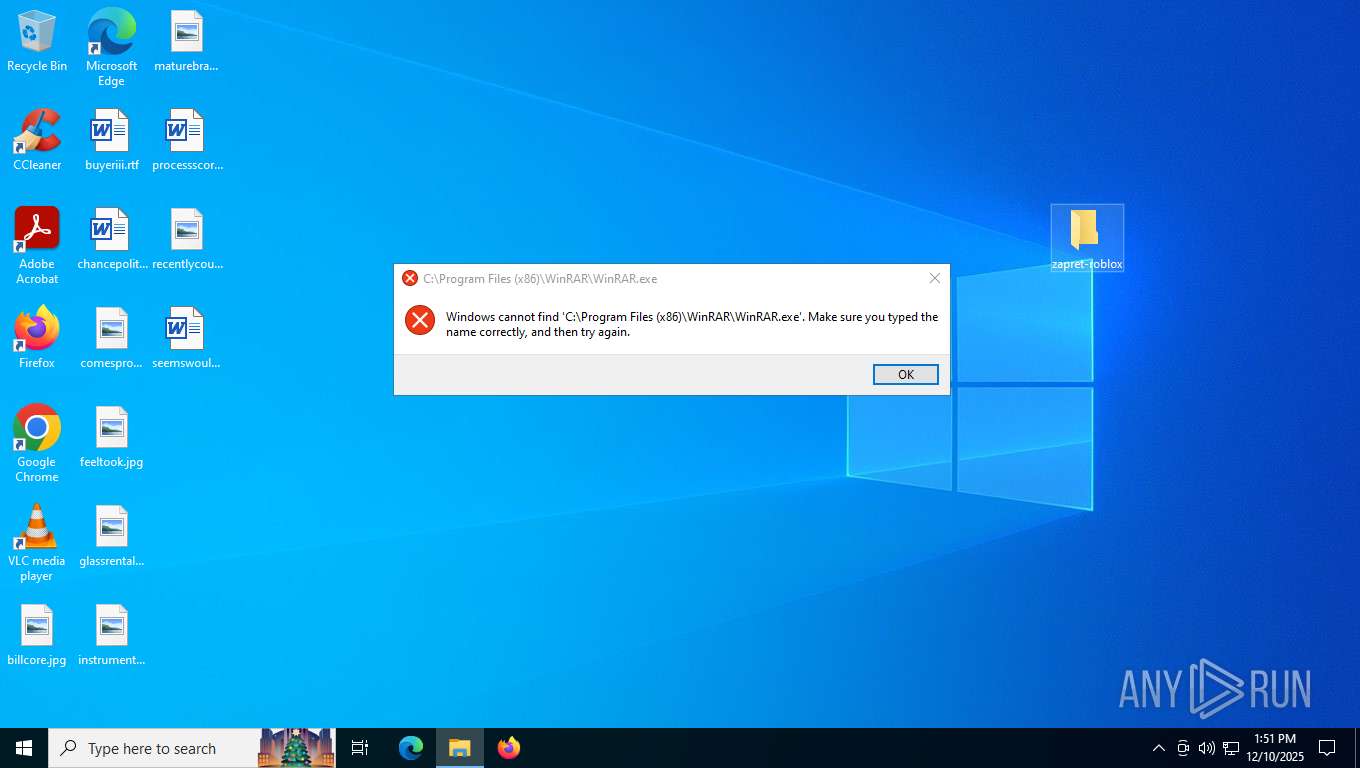
Malicious driver has been detected
- WinRAR.exe (PID: 7556)
Detects Cygwin installation
- WinRAR.exe (PID: 7556)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 7556)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2360)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 4768)
- cmd.exe (PID: 7724)
Windows service management via SC.EXE
- sc.exe (PID: 4508)
- sc.exe (PID: 7960)
Starts SC.EXE for service management
- cmd.exe (PID: 2360)
- cmd.exe (PID: 7724)
Starts application with an unusual extension
- cmd.exe (PID: 7388)
- cmd.exe (PID: 412)
- cmd.exe (PID: 4768)
- cmd.exe (PID: 7976)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 7388)
- cmd.exe (PID: 4768)
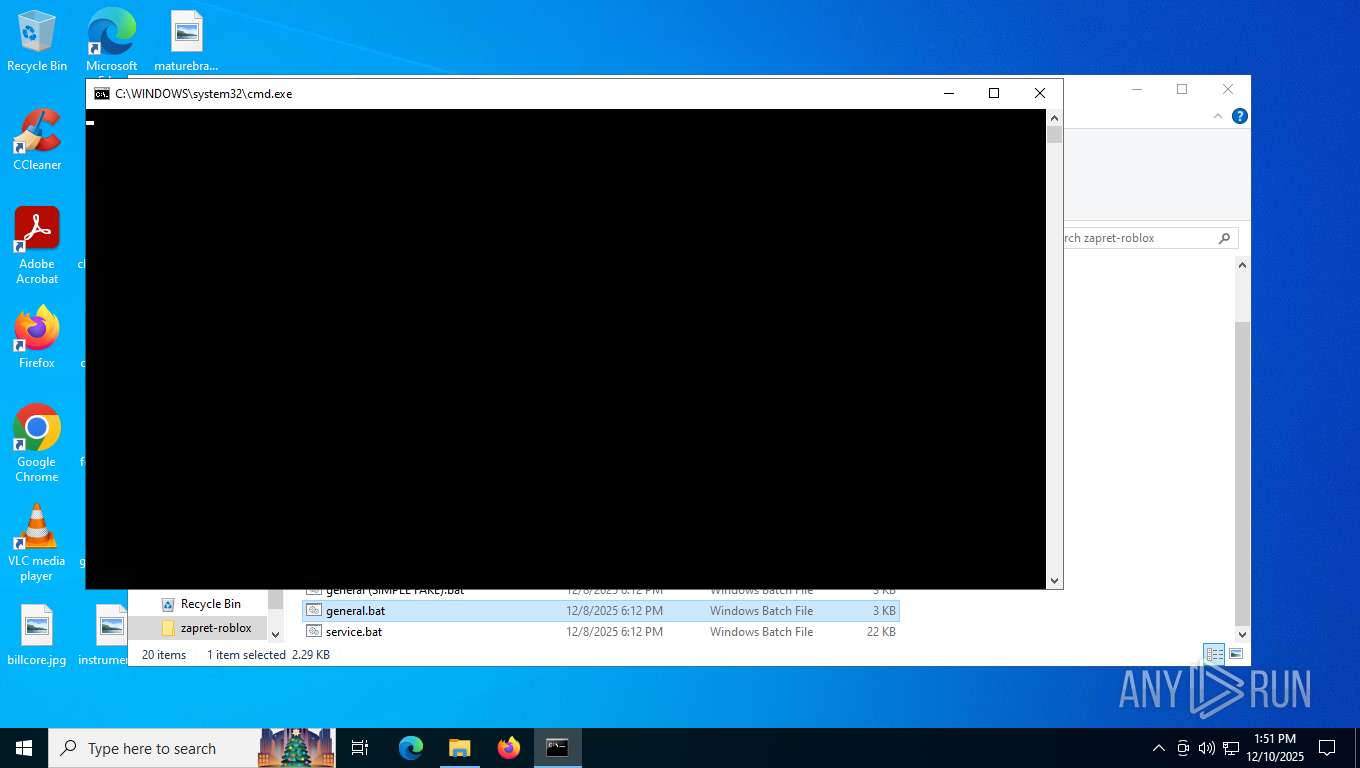
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7388)
- cmd.exe (PID: 412)
- cmd.exe (PID: 4768)
- cmd.exe (PID: 7976)
Application launched itself
- cmd.exe (PID: 7388)
- cmd.exe (PID: 412)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 4768)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3168)
- cmd.exe (PID: 7896)
Hides command output
- cmd.exe (PID: 3168)
- cmd.exe (PID: 7896)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7556)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7556)
Manual execution by a user
- cmd.exe (PID: 7388)
- cmd.exe (PID: 4768)
- winws.exe (PID: 2288)
- winws.exe (PID: 680)
Disables trace logs
- netsh.exe (PID: 7328)
- netsh.exe (PID: 2428)
- powershell.exe (PID: 6296)
- netsh.exe (PID: 5016)
- netsh.exe (PID: 8064)
- powershell.exe (PID: 7876)
Checks supported languages
- chcp.com (PID: 5984)
- chcp.com (PID: 5156)
- chcp.com (PID: 1368)
- chcp.com (PID: 7720)
- winws.exe (PID: 3568)
- chcp.com (PID: 8036)
- chcp.com (PID: 7888)
- winws.exe (PID: 2628)
- winws.exe (PID: 680)
Changes the display of characters in the console
- cmd.exe (PID: 7388)
- cmd.exe (PID: 412)
- cmd.exe (PID: 4768)
- cmd.exe (PID: 7976)
Checks proxy server information
- powershell.exe (PID: 6296)
- powershell.exe (PID: 7876)
Reads the computer name
- winws.exe (PID: 3568)
- winws.exe (PID: 2628)
- winws.exe (PID: 680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 972491 |
| UncompressedSize: | 2954293 |
| OperatingSystem: | Win32 |
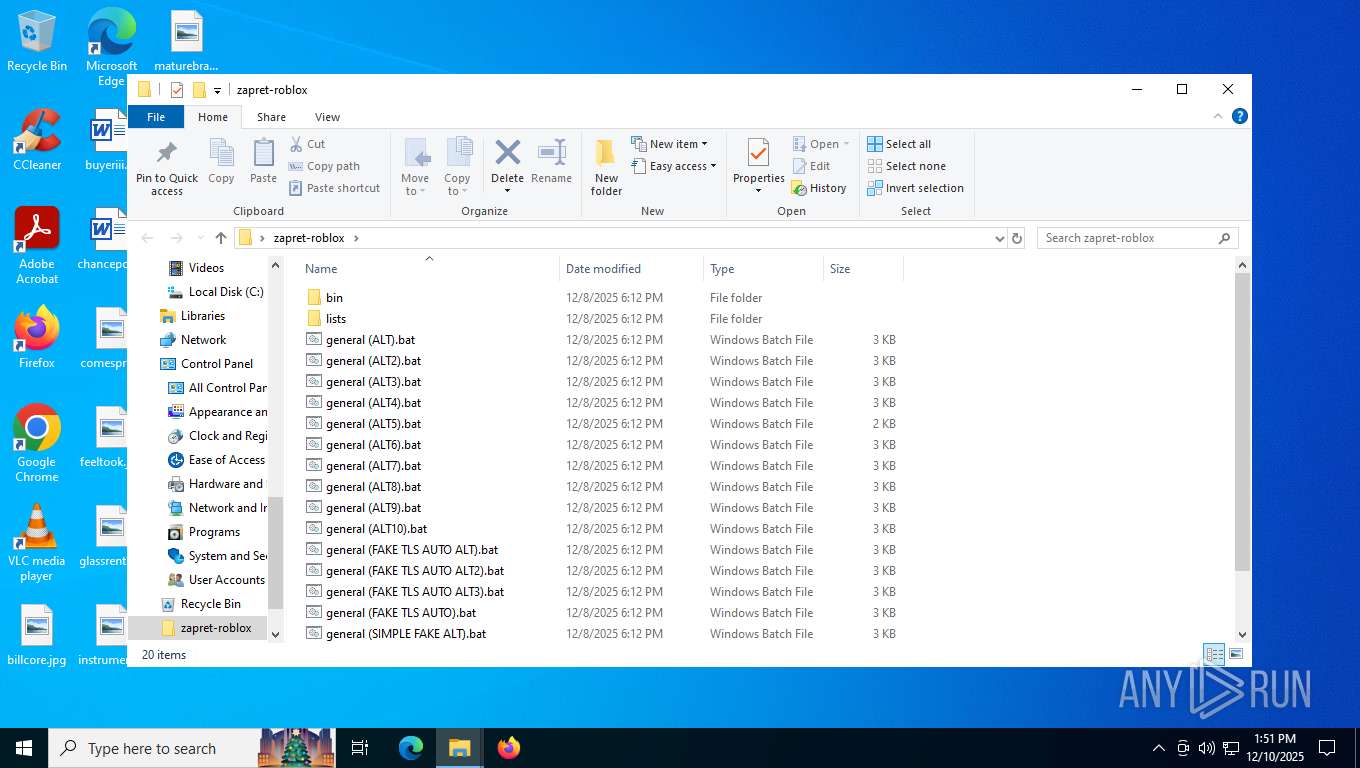
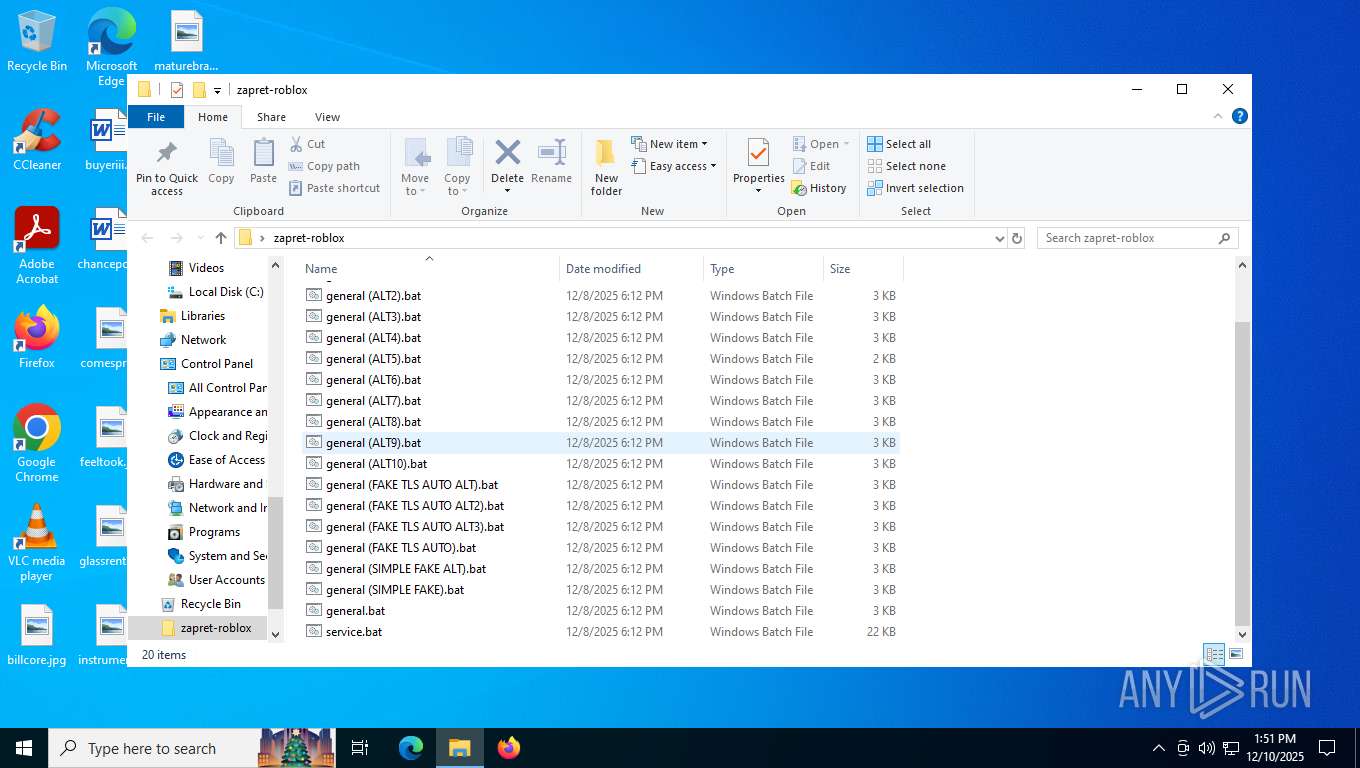
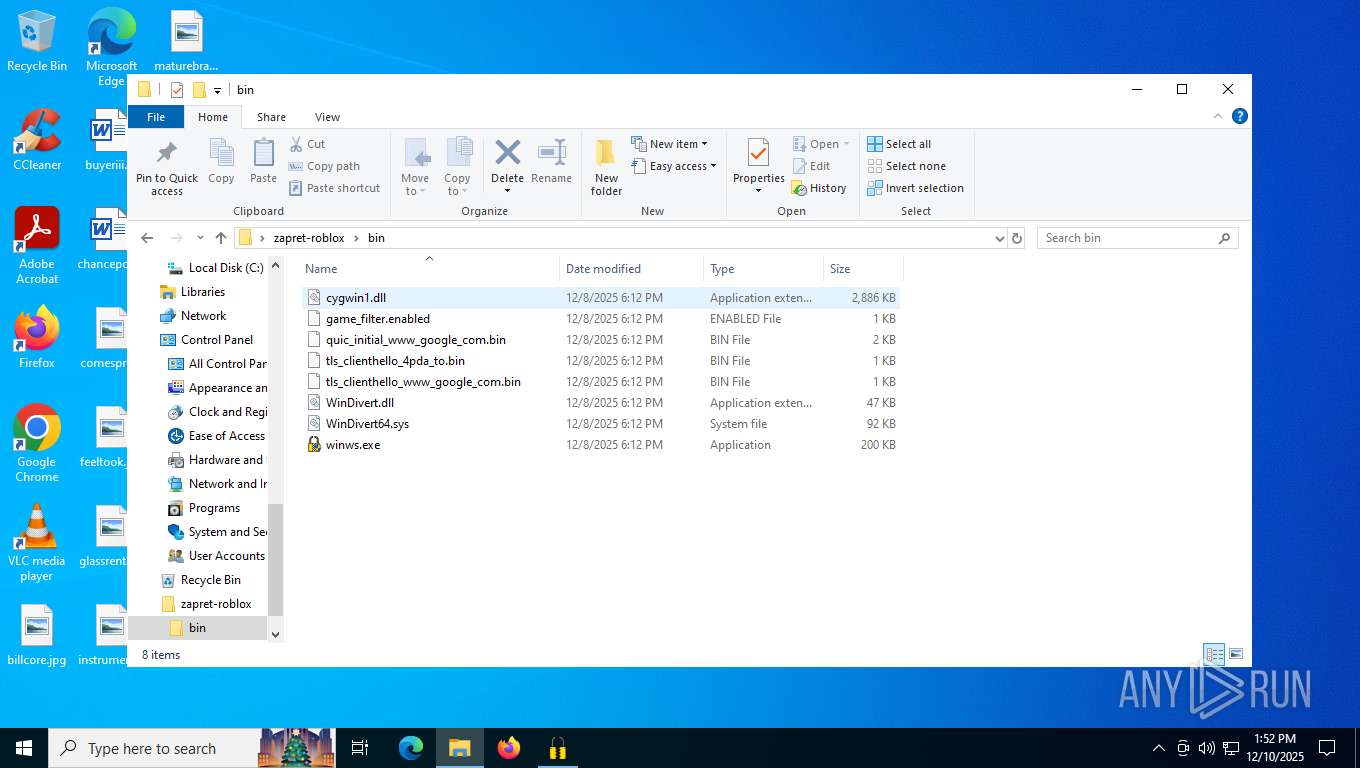
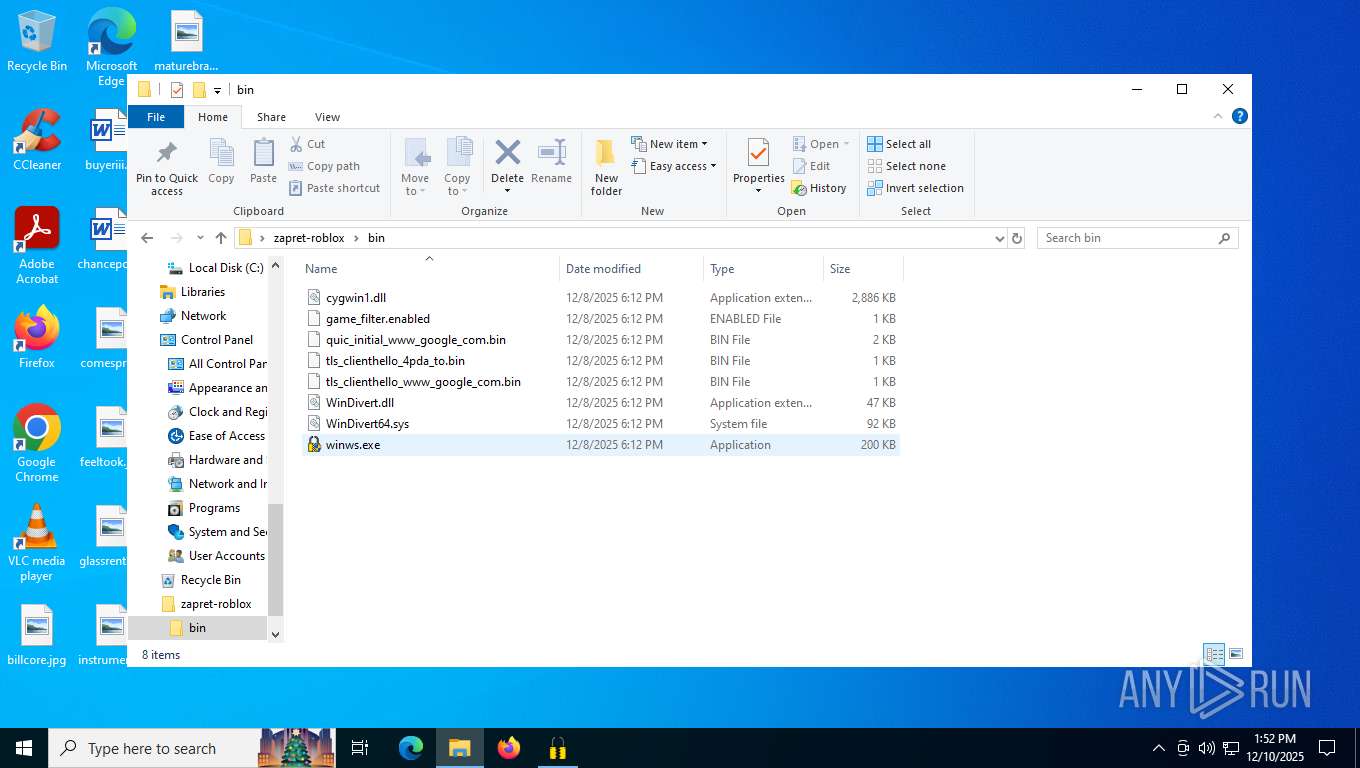
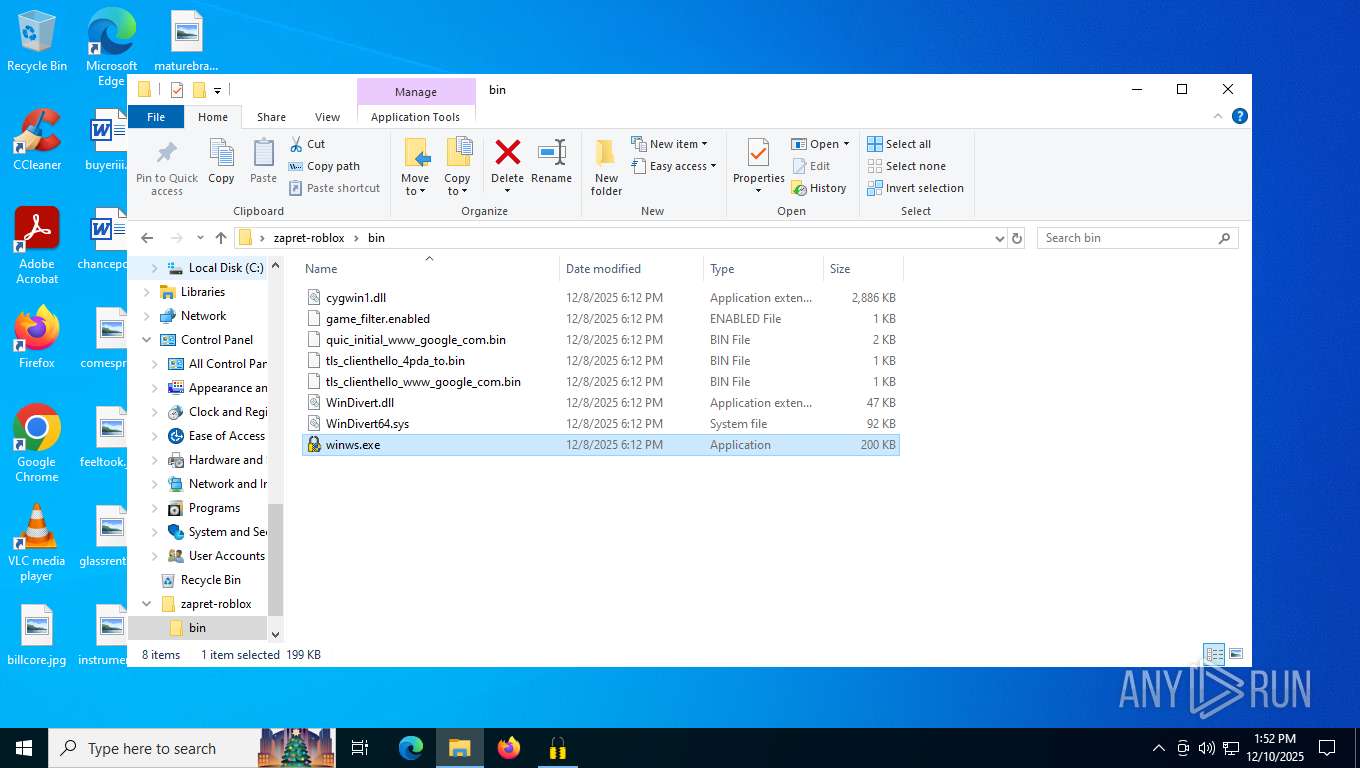
| ArchivedFileName: | zapret-roblox/bin/cygwin1.dll |
Total processes
184
Monitored processes
42
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
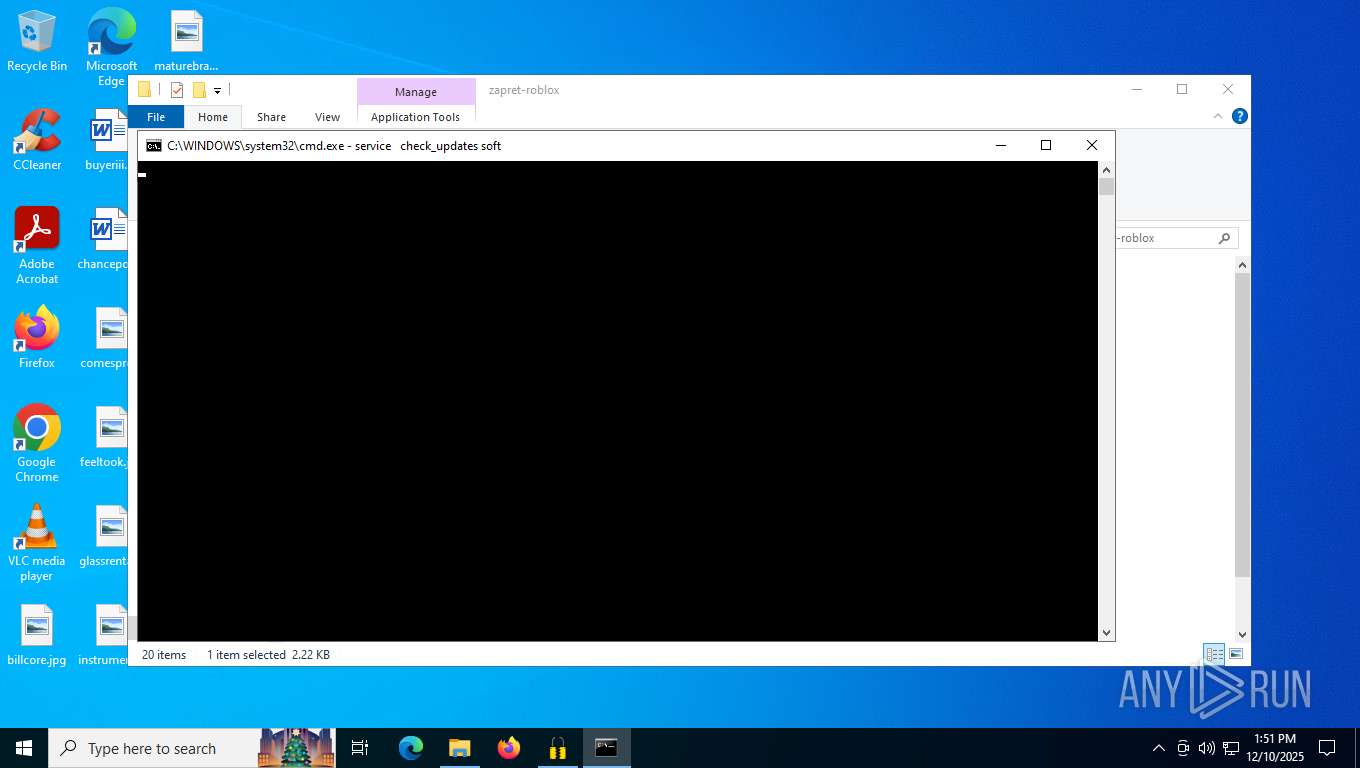
| 412 | C:\WINDOWS\system32\cmd.exe /K service check_updates soft | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Users\admin\Desktop\zapret-roblox\bin\winws.exe" | C:\Users\admin\Desktop\zapret-roblox\bin\winws.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1176 | findstr /i "enabled" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1368 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2016 | "C:\Users\admin\Desktop\zapret-roblox\bin\winws.exe" --wf-tcp=80,443,2053,2083,2087,2096,8443,1024-65535 --wf-udp=443,19294-19344,50000-50100,1024-65535 --filter-udp=443 --hostlist="C:\Users\admin\Desktop\zapret-roblox\lists\list-general.txt" --hostlist-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret-roblox\bin\quic_initial_www_google_com.bin" --new --filter-udp=19294-19344,50000-50100 --filter-l7=discord,stun --dpi-desync=fake --dpi-desync-repeats=6 --new --filter-tcp=2053,2083,2087,2096,8443 --hostlist-domains=discord.media --dpi-desync=multisplit --dpi-desync-split-seqovl=568 --dpi-desync-split-pos=1 --dpi-desync-split-seqovl-pattern="C:\Users\admin\Desktop\zapret-roblox\bin\tls_clienthello_4pda_to.bin" --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\zapret-roblox\lists\list-google.txt" --ip-id=zero --dpi-desync=multisplit --dpi-desync-split-seqovl=681 --dpi-desync-split-pos=1 --dpi-desync-split-seqovl-pattern="C:\Users\admin\Desktop\zapret-roblox\bin\tls_clienthello_www_google_com.bin" --new --filter-tcp=80,443 --hostlist="C:\Users\admin\Desktop\zapret-roblox\lists\list-general.txt" --hostlist-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-exclude.txt" --dpi-desync=multisplit --dpi-desync-split-seqovl=568 --dpi-desync-split-pos=1 --dpi-desync-split-seqovl-pattern="C:\Users\admin\Desktop\zapret-roblox\bin\tls_clienthello_4pda_to.bin" --new --filter-udp=443 --ipset="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-all.txt" --hostlist-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret-roblox\bin\quic_initial_www_google_com.bin" --new --filter-tcp=80,443,1024-65535 --ipset="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-all.txt" --hostlist-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-exclude.txt" --dpi-desync=multisplit --dpi-desync-split-seqovl=568 --dpi-desync-split-pos=1 --dpi-desync-split-seqovl-pattern="C:\Users\admin\Desktop\zapret-roblox\bin\tls_clienthello_4pda_to.bin" --new --filter-udp=1024-65535 --ipset="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-all.txt" --ipset-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-autottl=2 --dpi-desync-repeats=12 --dpi-desync-any-protocol=1 --dpi-desync-fake-unknown-udp="C:\Users\admin\Desktop\zapret-roblox\bin\quic_initial_www_google_com.bin" --dpi-desync-cutoff=n2 | C:\Users\admin\Desktop\zapret-roblox\bin\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2288 | findstr /i "STATE" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\Desktop\zapret-roblox\bin\winws.exe" | C:\Users\admin\Desktop\zapret-roblox\bin\winws.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2360 | C:\WINDOWS\system32\cmd.exe /c sc query "zapret" | findstr /i "STATE" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | netsh interface tcp set global timestamps=enabled | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2628 | "C:\Users\admin\Desktop\zapret-roblox\bin\winws.exe" --wf-tcp=80,443,2053,2083,2087,2096,8443,1024-65535 --wf-udp=443,19294-19344,50000-50100,1024-65535 --filter-udp=443 --hostlist="C:\Users\admin\Desktop\zapret-roblox\lists\list-general.txt" --hostlist-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret-roblox\bin\quic_initial_www_google_com.bin" --new --filter-udp=19294-19344,50000-50100 --filter-l7=discord,stun --dpi-desync=fake --dpi-desync-repeats=6 --new --filter-tcp=2053,2083,2087,2096,8443 --hostlist-domains=discord.media --dpi-desync=fake --dpi-desync-fake-tls-mod=none --dpi-desync-repeats=6 --dpi-desync-fooling=badseq --dpi-desync-badseq-increment=2 --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\zapret-roblox\lists\list-google.txt" --ip-id=zero --dpi-desync=fake --dpi-desync-fake-tls-mod=none --dpi-desync-repeats=6 --dpi-desync-fooling=badseq --dpi-desync-badseq-increment=2 --new --filter-tcp=80,443 --hostlist="C:\Users\admin\Desktop\zapret-roblox\lists\list-general.txt" --hostlist-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-fake-tls-mod=none --dpi-desync-repeats=6 --dpi-desync-fooling=badseq --dpi-desync-badseq-increment=2 --new --filter-udp=443 --ipset="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-all.txt" --hostlist-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-repeats=6 --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret-roblox\bin\quic_initial_www_google_com.bin" --new --filter-tcp=80,443,1024-65535 --ipset="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-all.txt" --hostlist-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\list-exclude.txt" --ipset-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-fake-tls-mod=none --dpi-desync-repeats=6 --dpi-desync-fooling=badseq --dpi-desync-badseq-increment=2 --new --filter-udp=1024-65535 --ipset="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-all.txt" --ipset-exclude="C:\Users\admin\Desktop\zapret-roblox\lists\ipset-exclude.txt" --dpi-desync=fake --dpi-desync-autottl=2 --dpi-desync-repeats=12 --dpi-desync-any-protocol=1 --dpi-desync-fake-unknown-udp="C:\Users\admin\Desktop\zapret-roblox\bin\quic_initial_www_google_com.bin" --dpi-desync-cutoff=n2 | C:\Users\admin\Desktop\zapret-roblox\bin\winws.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
Total events
13 299
Read events
13 276
Write events
23
Delete events
0
Modification events
| (PID) Process: | (7556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zapret-roblox_1.9.0b.rar | |||
| (PID) Process: | (7556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7556) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
4
Suspicious files
4
Text files
29
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
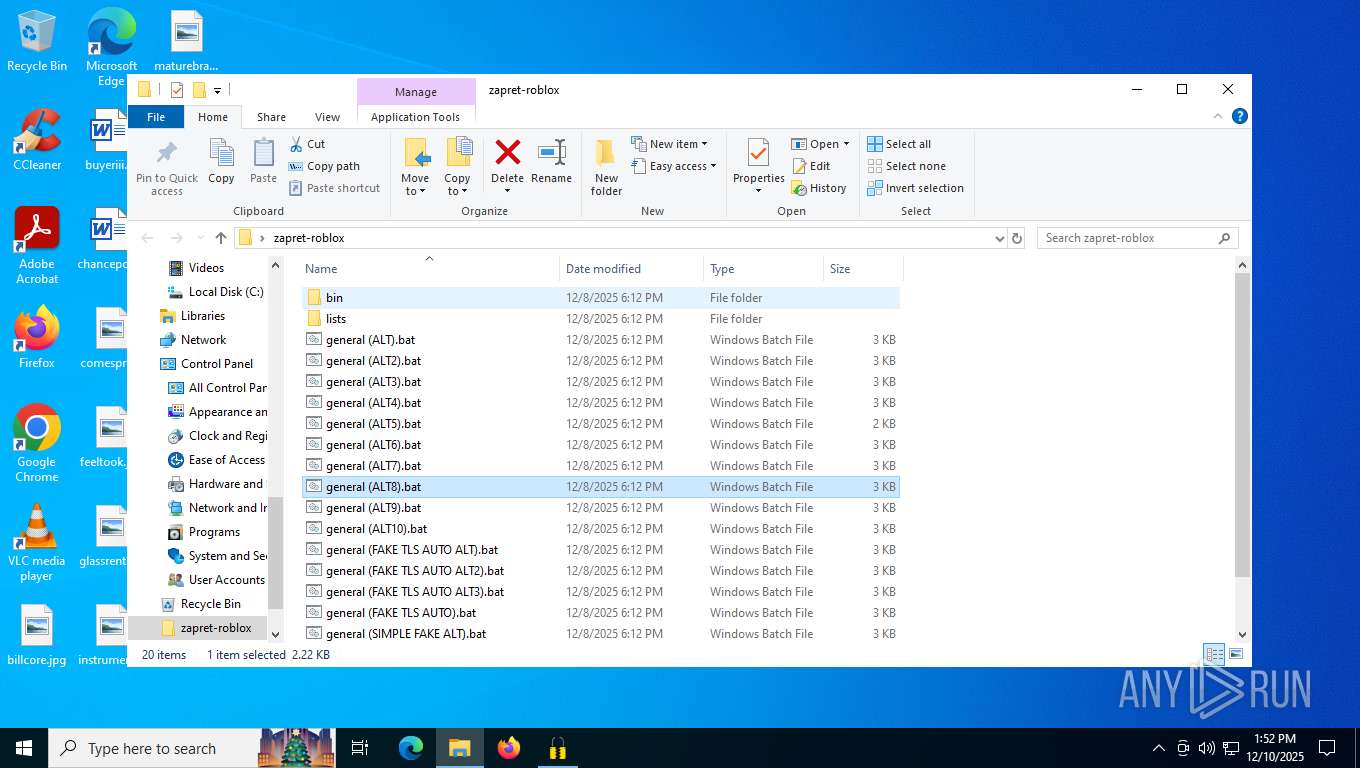
| 7556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7556.33367\zapret-roblox\bin\tls_clienthello_www_google_com.bin | binary | |
MD5:41E47557F16690DF1781F67C8712714E | SHA256:F966351AE376963DFFBCB5B94256872649B9CDAAB8C5175025936FA50E07DC19 | |||
| 7556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7556.33367\zapret-roblox\bin\cygwin1.dll | executable | |
MD5:A1C82ED072DC079DD7851F82D9AA7678 | SHA256:103104A52E5293CE418944725DF19E2BF81AD9269B9A120D71D39028E821499B | |||
| 7556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7556.33367\zapret-roblox\bin\quic_initial_www_google_com.bin | binary | |
MD5:312526D39958D89B1F8AB67789AB985F | SHA256:F4589C57749F956BB30538197A521D7005F8B0A8723B4707E72405E51DDAC50A | |||
| 7556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7556.33367\zapret-roblox\bin\game_filter.enabled | text | |
MD5:9E57D6BDA4BEC067FF636FE400AF6EA5 | SHA256:02FA0E83883800772EC3462347E9A9F623FA3E13BE7D4DE7E0B2CB7E425AB212 | |||
| 7556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7556.33367\zapret-roblox\bin\tls_clienthello_4pda_to.bin | binary | |
MD5:E6D649DE132C3C10CB62531EF74F5B73 | SHA256:EEFEAF09DDE8D69B1F176212541F63C68B314A33A335ECED99A8A29F17254DA8 | |||
| 7556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7556.33367\zapret-roblox\bin\WinDivert64.sys | executable | |
MD5:89ED5BE7EA83C01D0DE33D3519944AA5 | SHA256:8DA085332782708D8767BCACE5327A6EC7283C17CFB85E40B03CD2323A90DDC2 | |||
| 7556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7556.33367\zapret-roblox\bin\WinDivert.dll | executable | |
MD5:B2014D33EE645112D5DC16FE9D9FCBFF | SHA256:C1E060EE19444A259B2162F8AF0F3FE8C4428A1C6F694DCE20DE194AC8D7D9A2 | |||
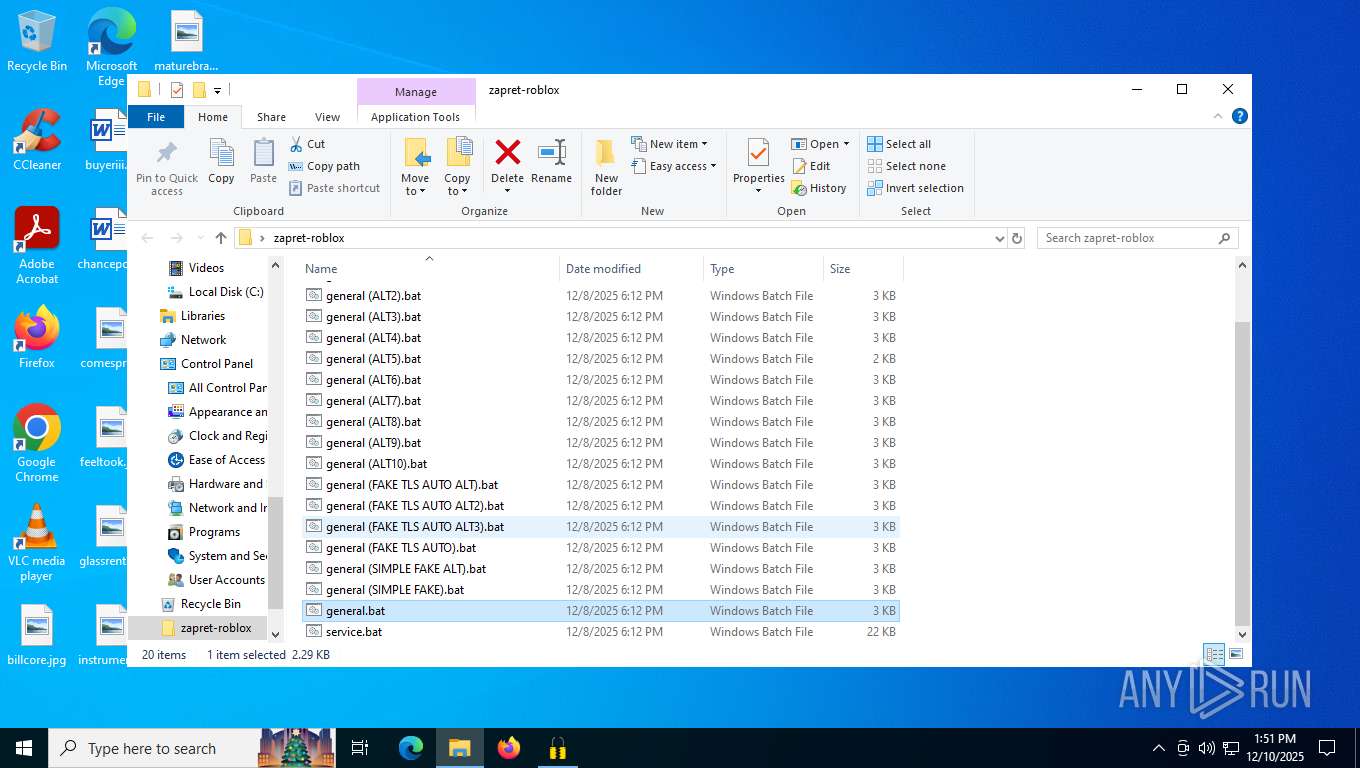
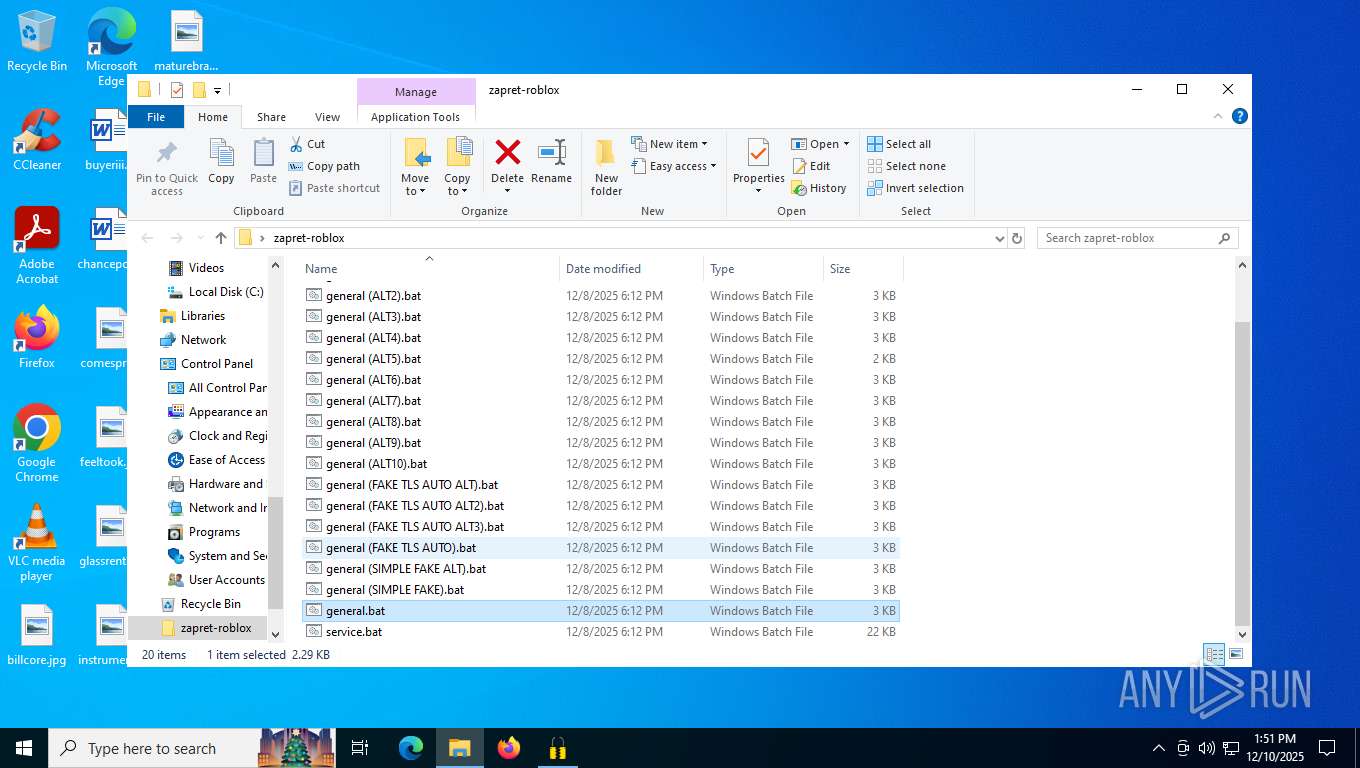
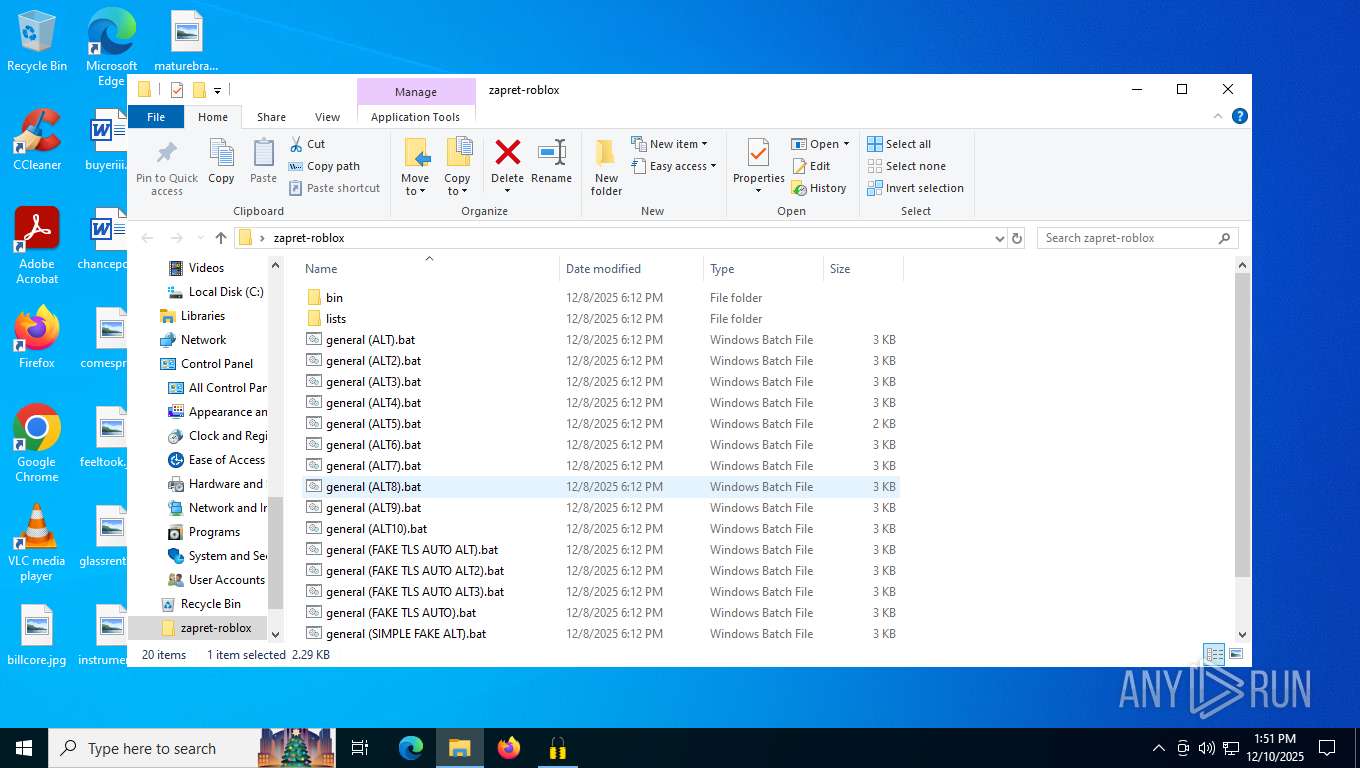
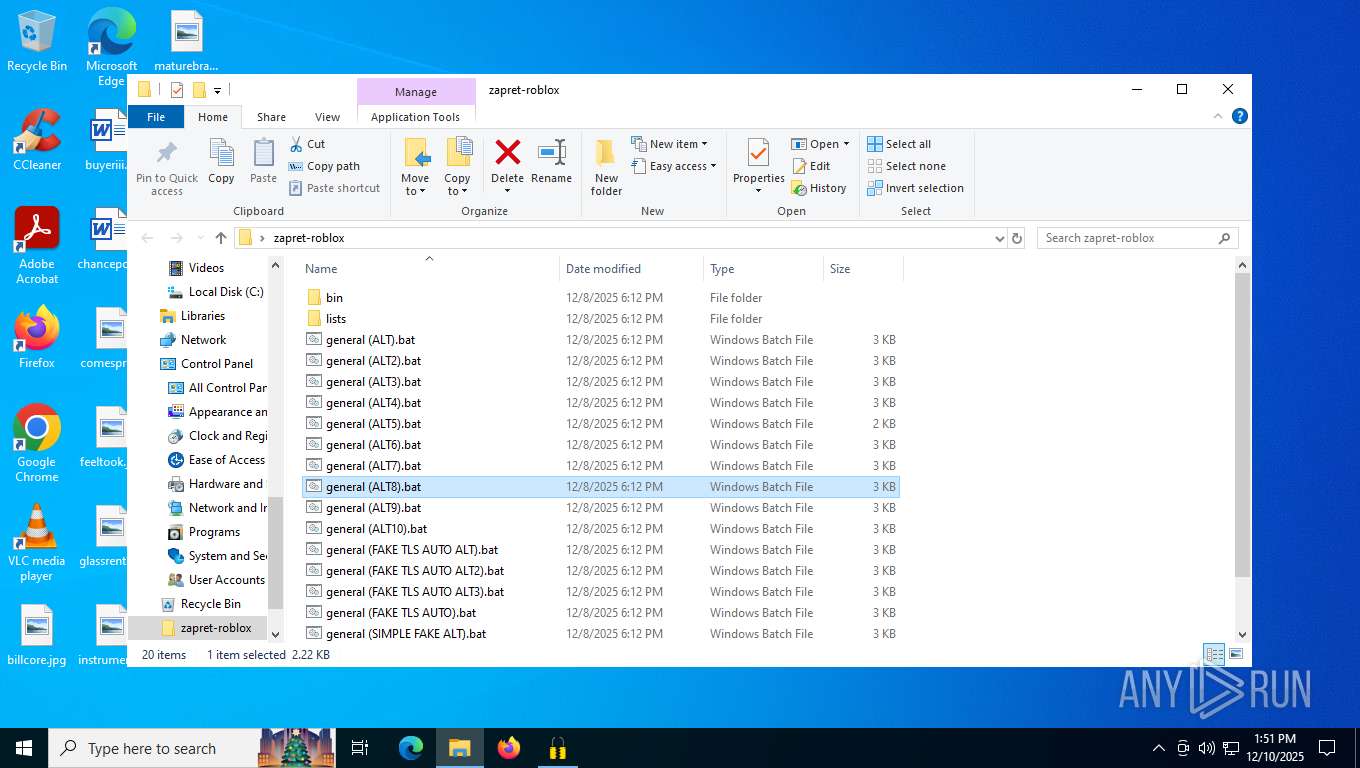
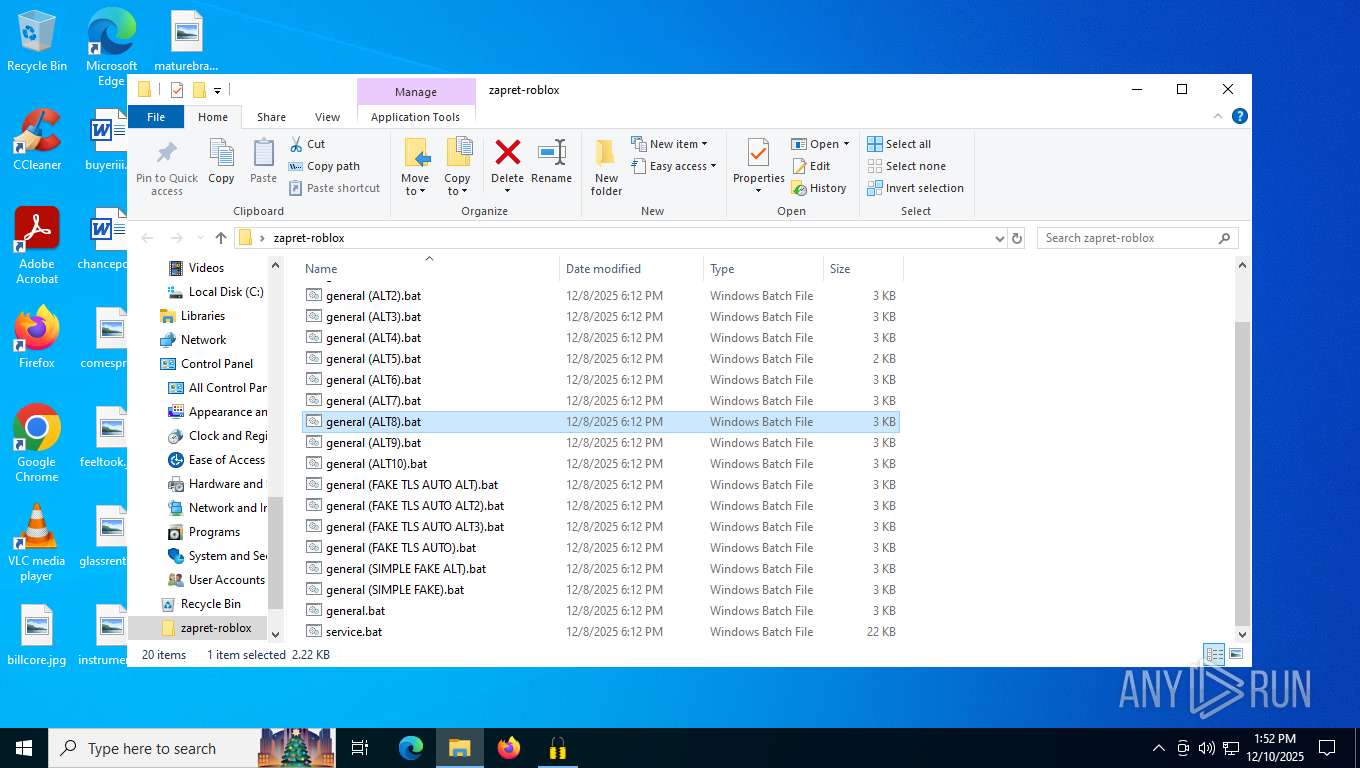
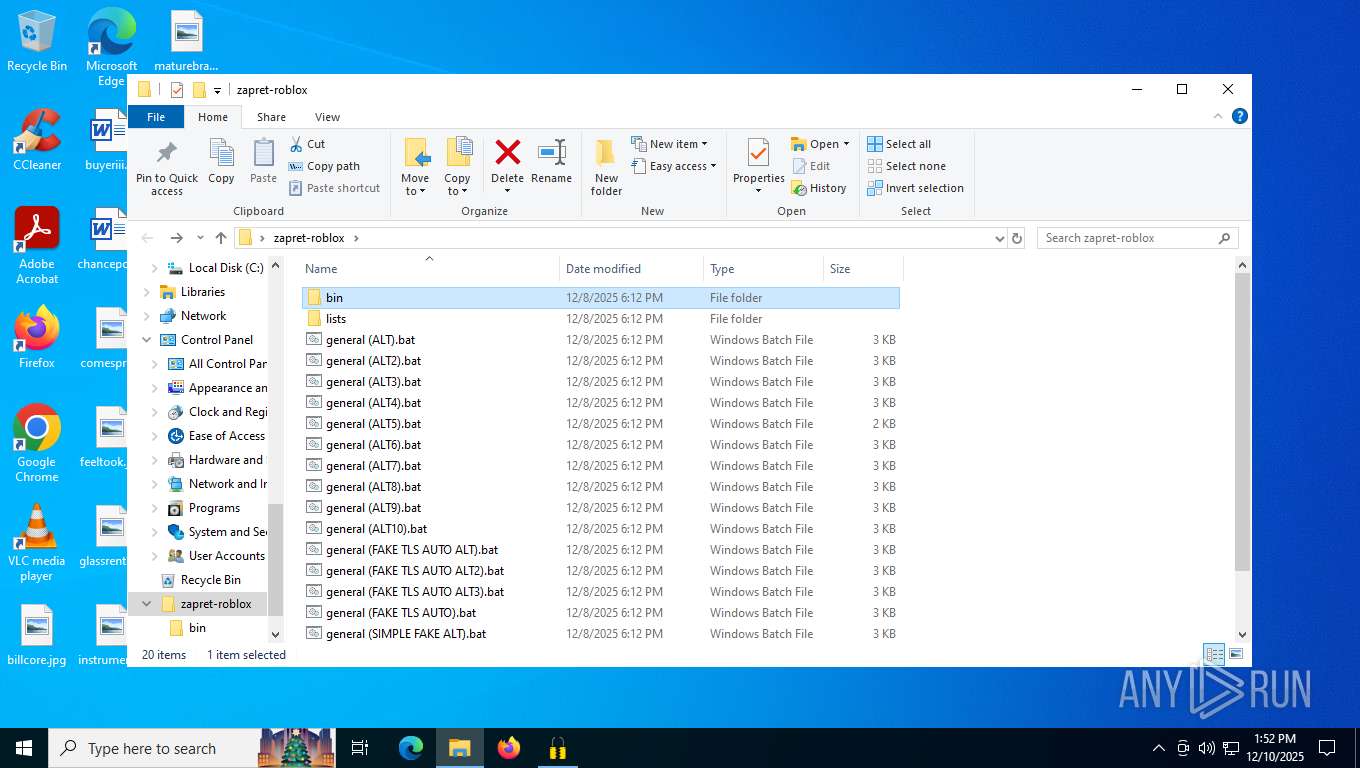
| 7556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7556.33367\zapret-roblox\general (ALT8).bat | text | |
MD5:9DF643A46B4CB69CC926035B7C012F4C | SHA256:83321EF1B714267AE8AEE99F4E4B0EC3A0FA3AA53E1C94A7A169918B99767566 | |||
| 7556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7556.33367\zapret-roblox\general (ALT5).bat | text | |
MD5:77D16DBC97714C2287BA1BDAC96B2A9A | SHA256:99EEA6F7DE9EA0DE0924823C1DB1FB99A25B78FDACCD862E751706C4D01FBF44 | |||
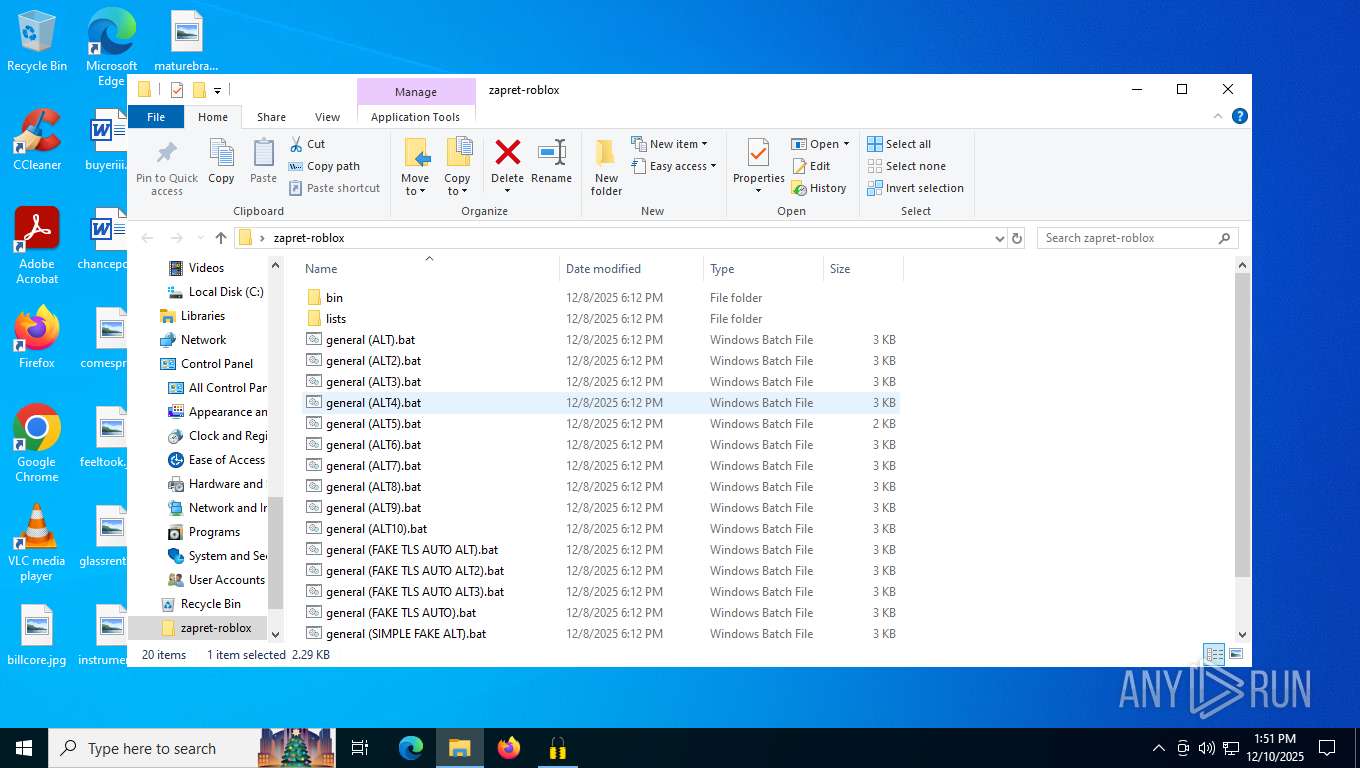
| 7556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7556.33367\zapret-roblox\general (ALT4).bat | text | |
MD5:AEEE5054DB95EF77E520B3455FE47FA9 | SHA256:46409E3C9239057702E03EB6896277B8904CA529D842D72A938A34B0C2B18CBC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
27
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4140 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
224 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
7772 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | US | binary | 419 b | whitelisted |
7772 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | US | binary | 408 b | whitelisted |
7772 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
7772 | SIHClient.exe | GET | 200 | 23.216.77.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | NL | binary | 824 b | whitelisted |
7772 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
7772 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | US | binary | 401 b | whitelisted |
7772 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 402 b | whitelisted |
7772 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | US | binary | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
224 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1136 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.49:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4140 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4140 | svchost.exe | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
224 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
224 | svchost.exe | 23.216.77.33:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |