| File name: | platform_experience_helper.exe |
| Full analysis: | https://app.any.run/tasks/e58b6941-2202-495e-ab8f-1a98d2a6606b |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | February 25, 2026, 21:33:24 |
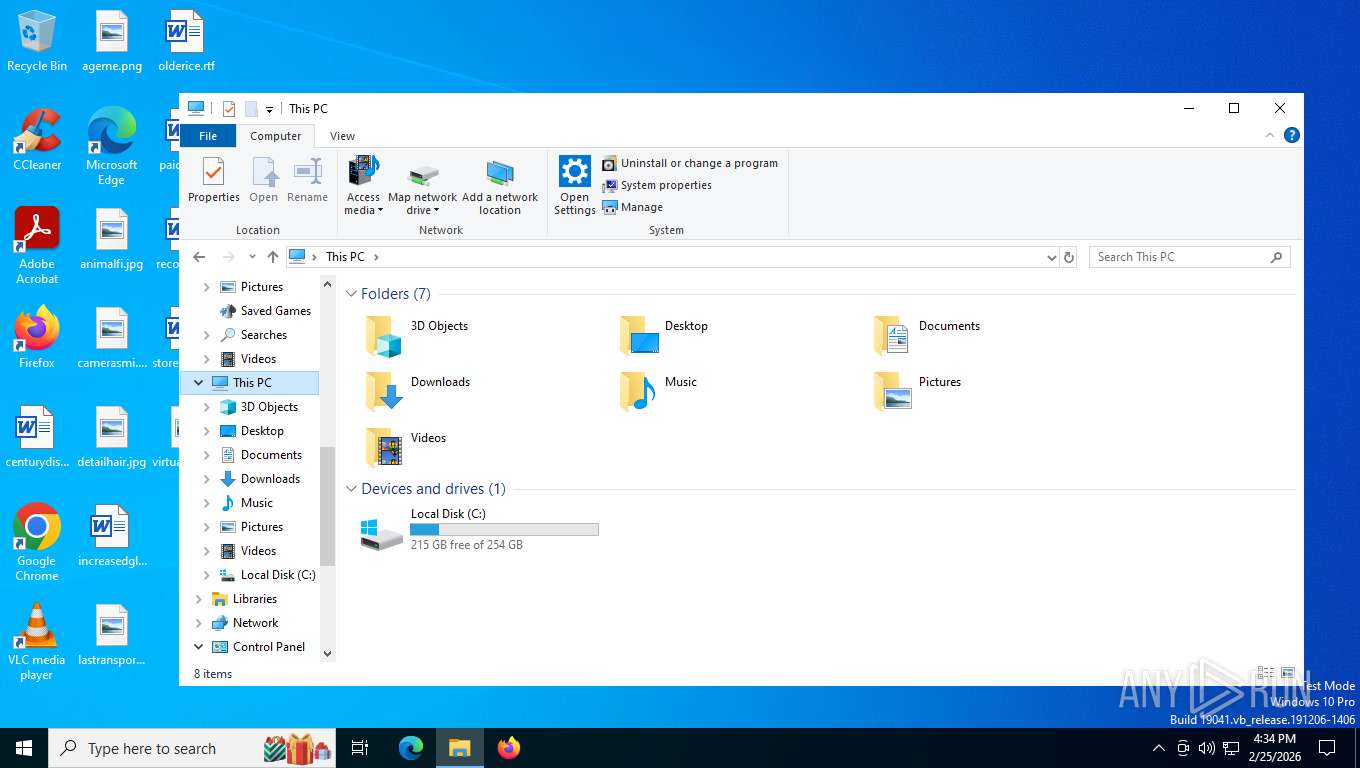
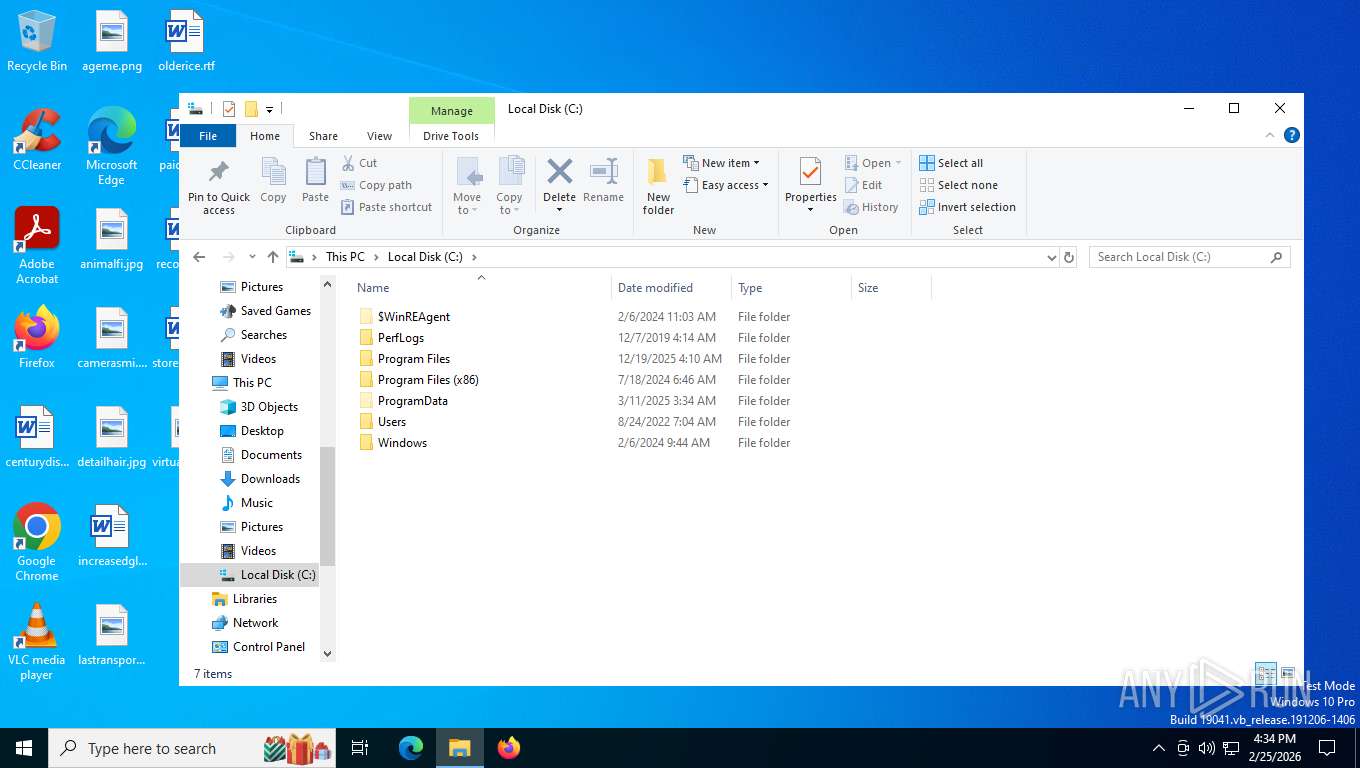
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 12 sections |
| MD5: | BF37F1AF6DD56ACFC41DBDF2714659DF |
| SHA1: | 88D5600EB9BE3803EF4FD3D0F2CE7E90FBB2E34D |
| SHA256: | 1F4D4F0BDC6CEC35286D010B69387C0A1A887BA92F0375FC12AE256D6CAE19E1 |
| SSDEEP: | 98304:K1tWt2HCmiq9McQaciFxnQkAhBw3NrCRXgdDLcVGMFxXFr/90+:haciBCPlT |
MALICIOUS
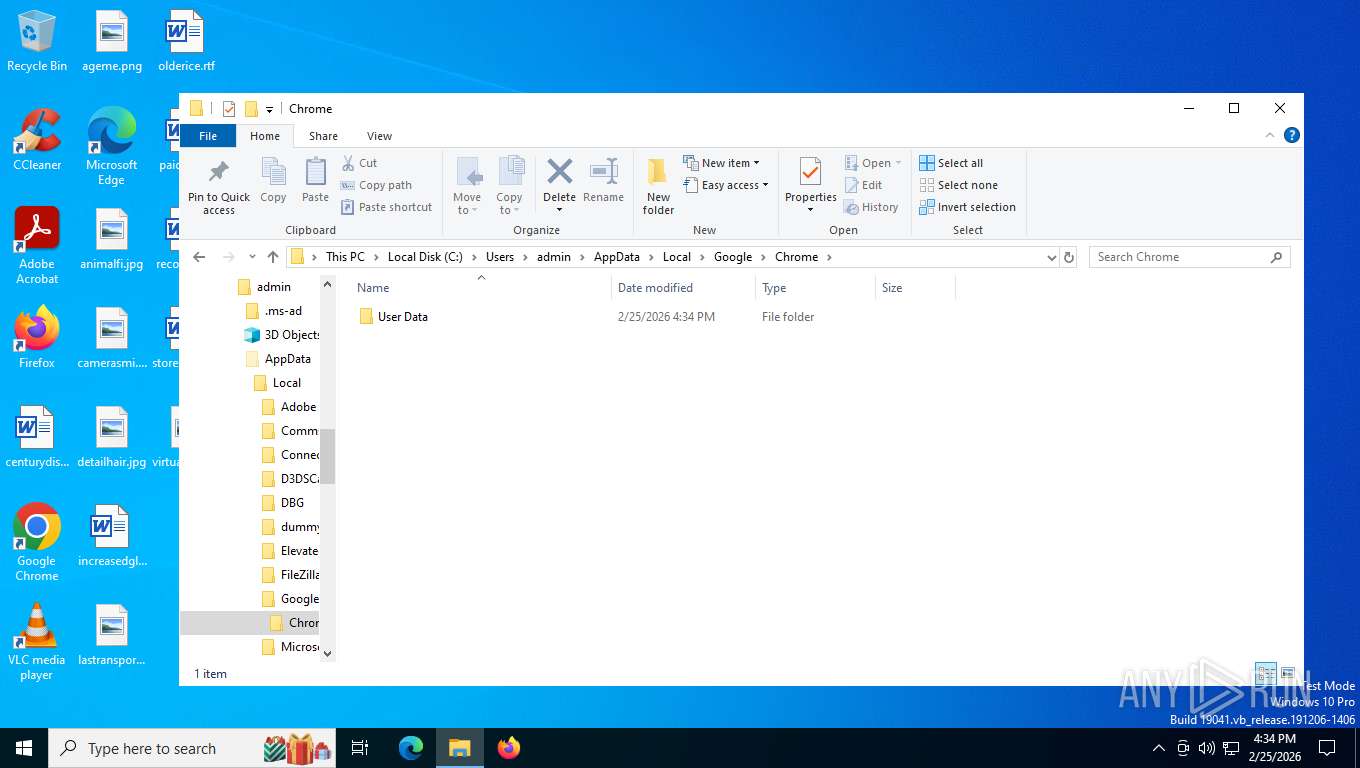
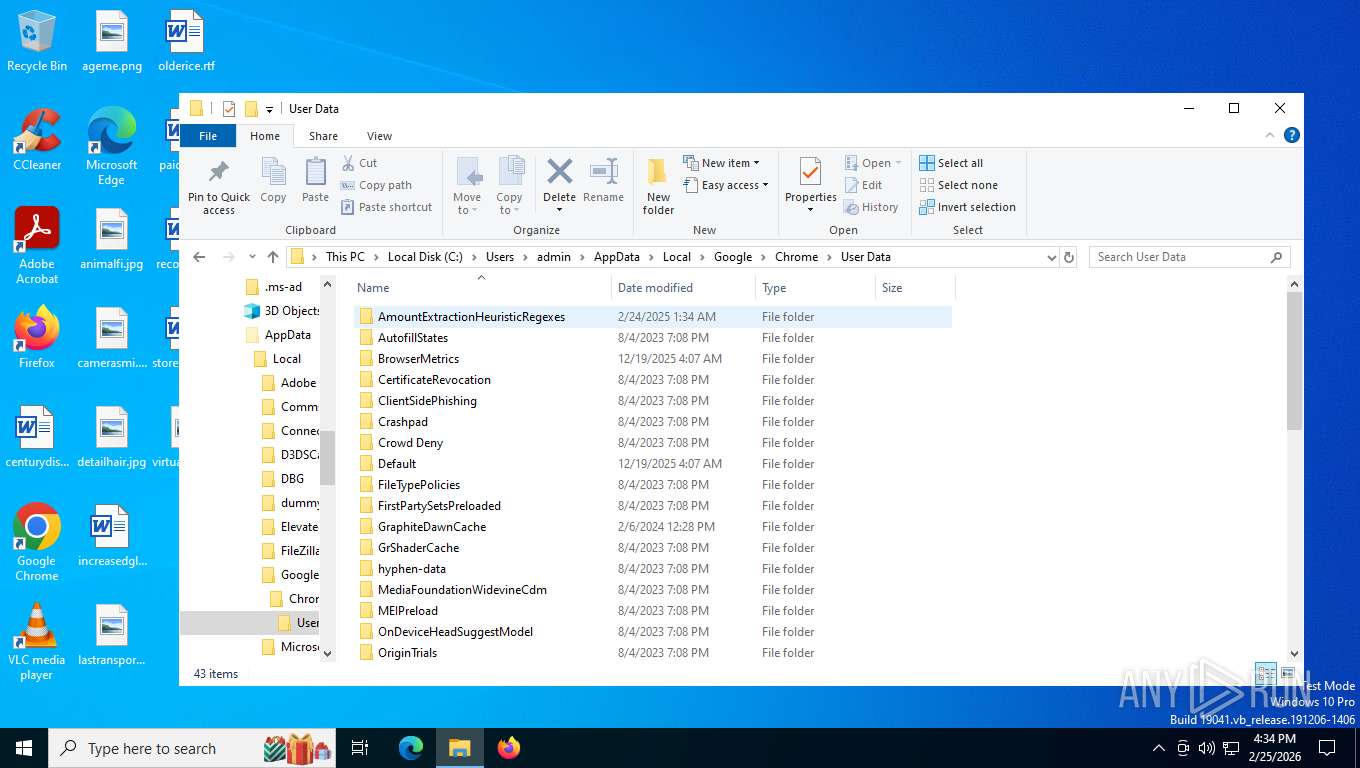
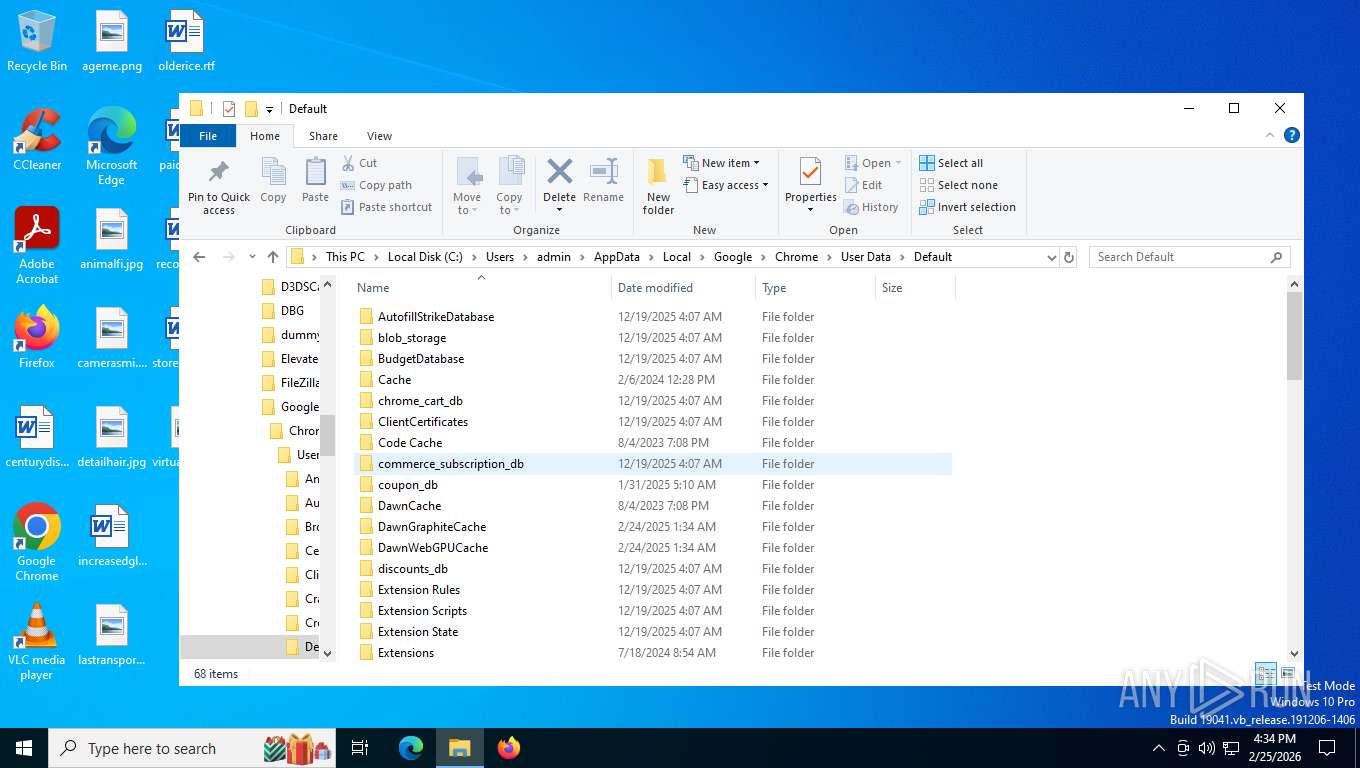
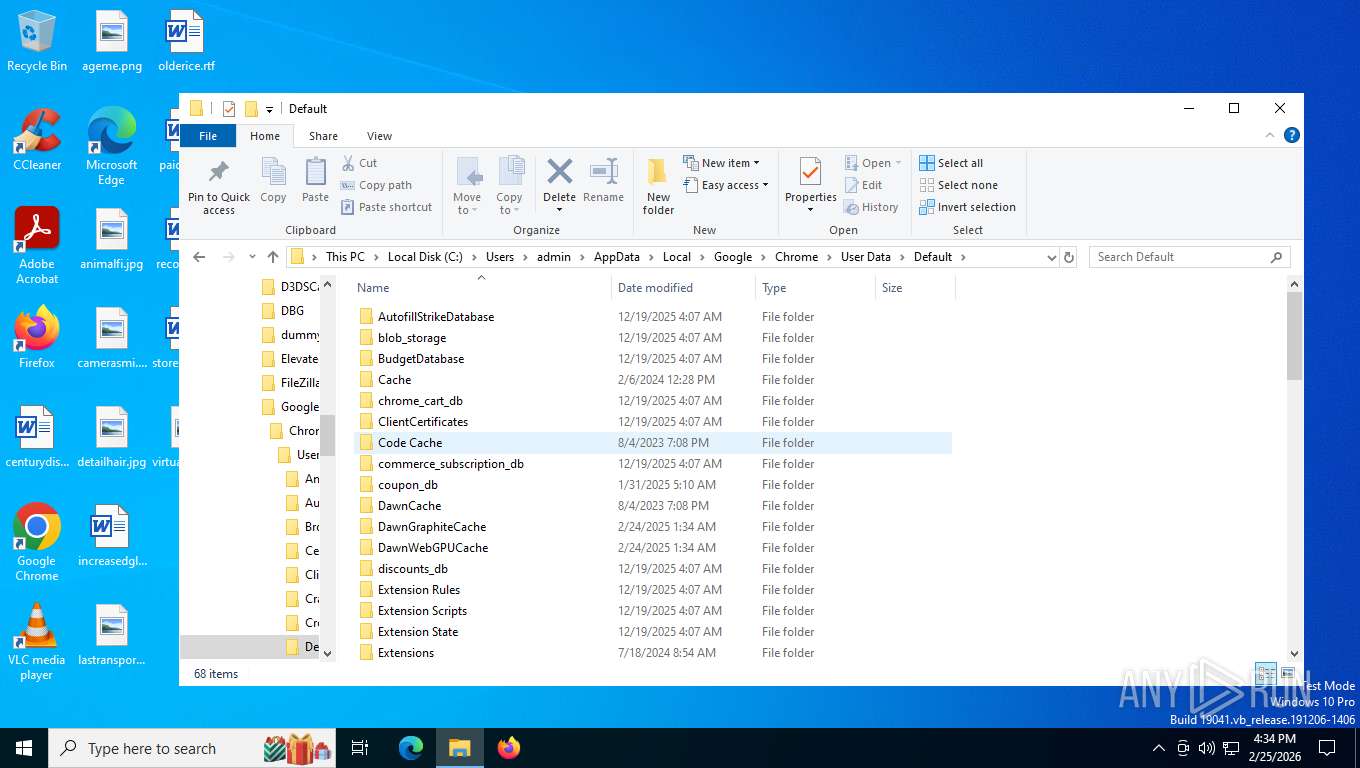
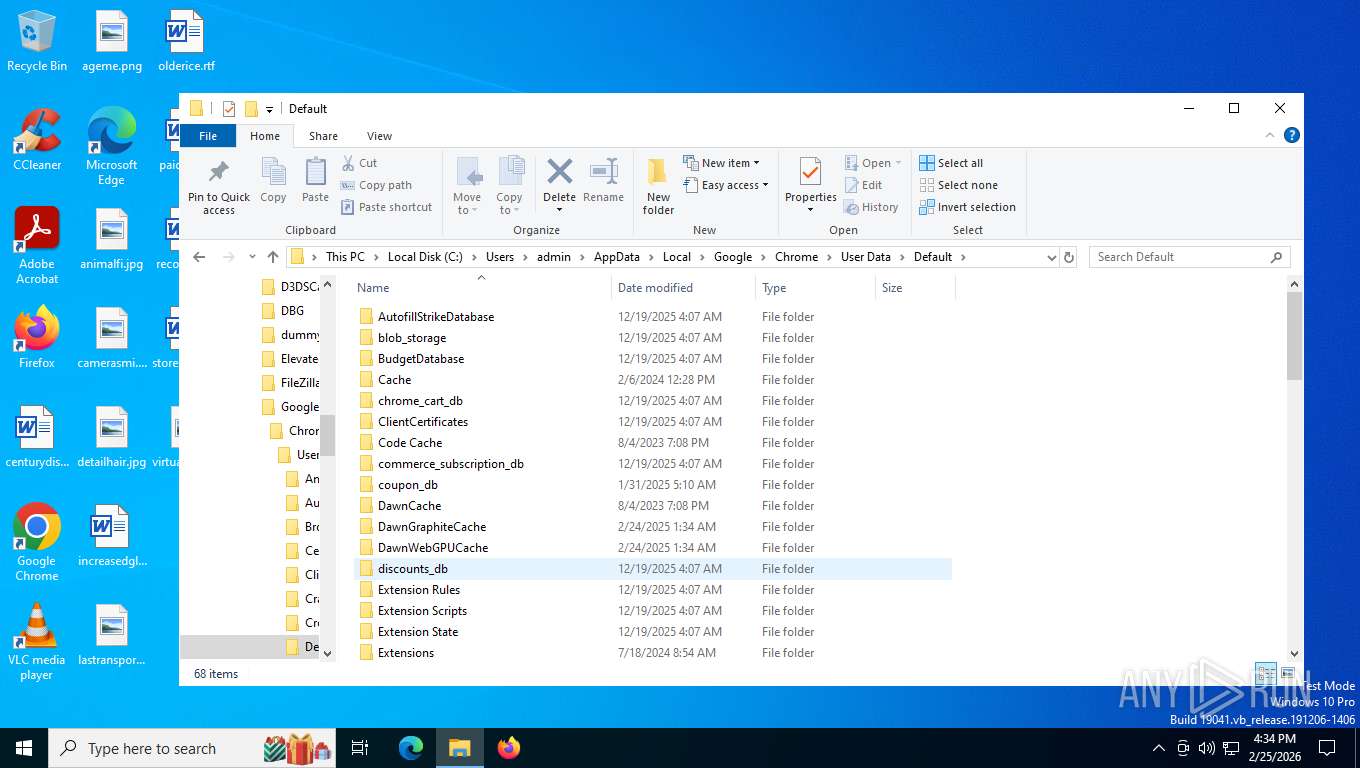
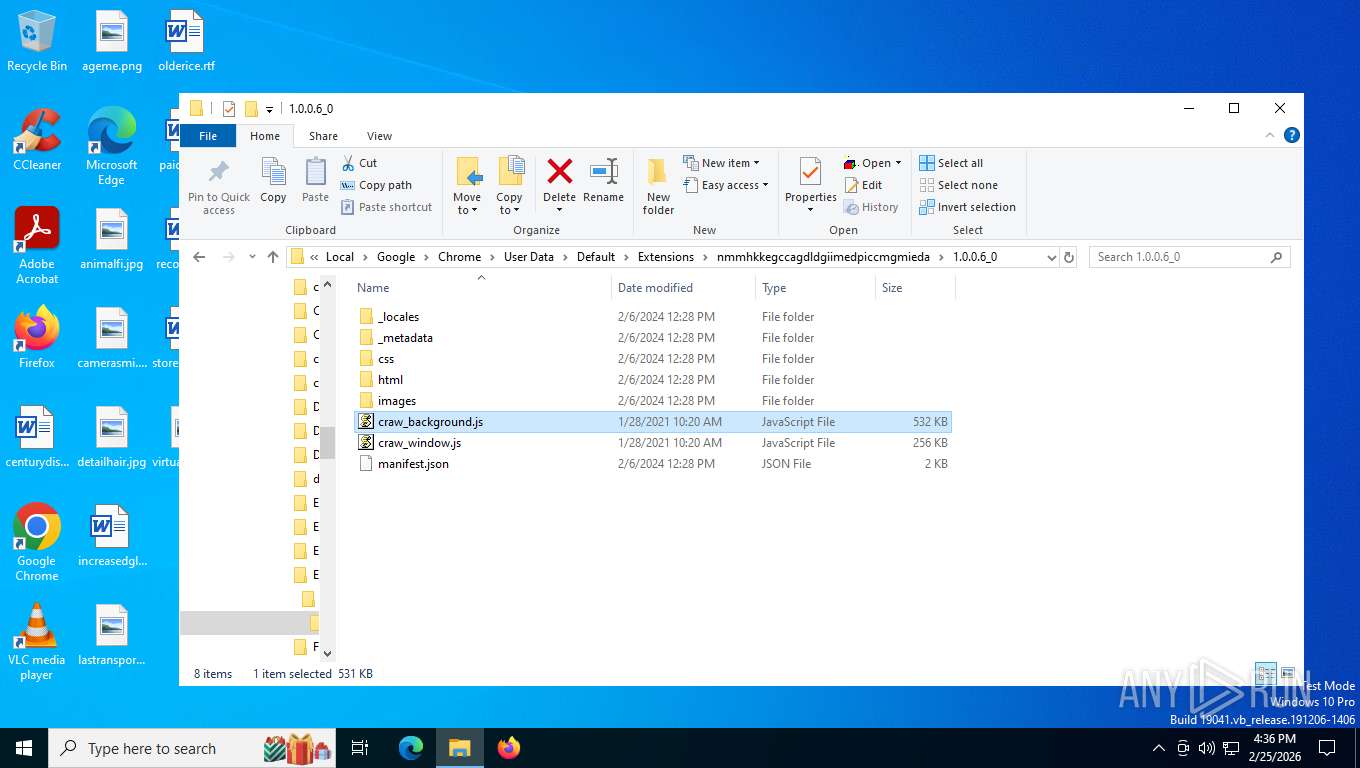
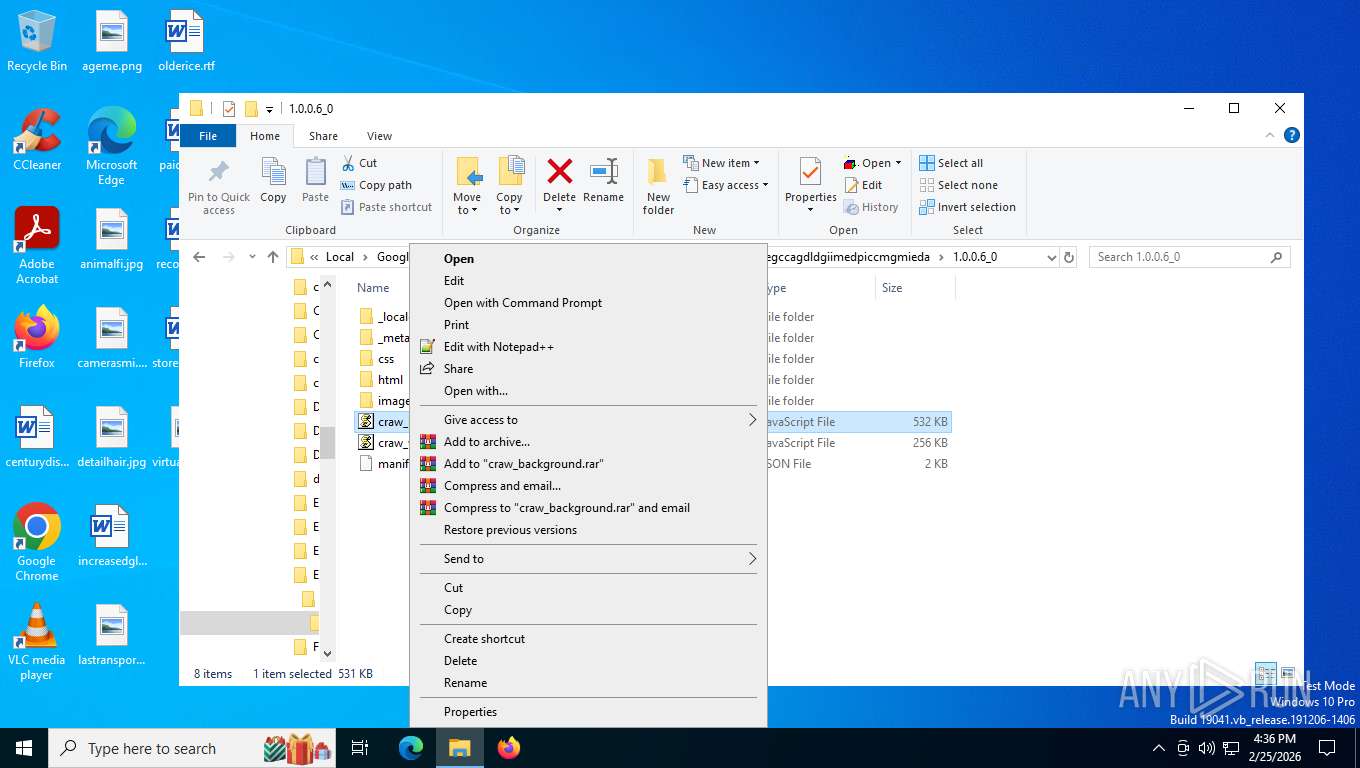
Steals credentials from Web Browsers
- wscript.exe (PID: 6920)
Actions looks like stealing of personal data
- wscript.exe (PID: 6920)
SUSPICIOUS
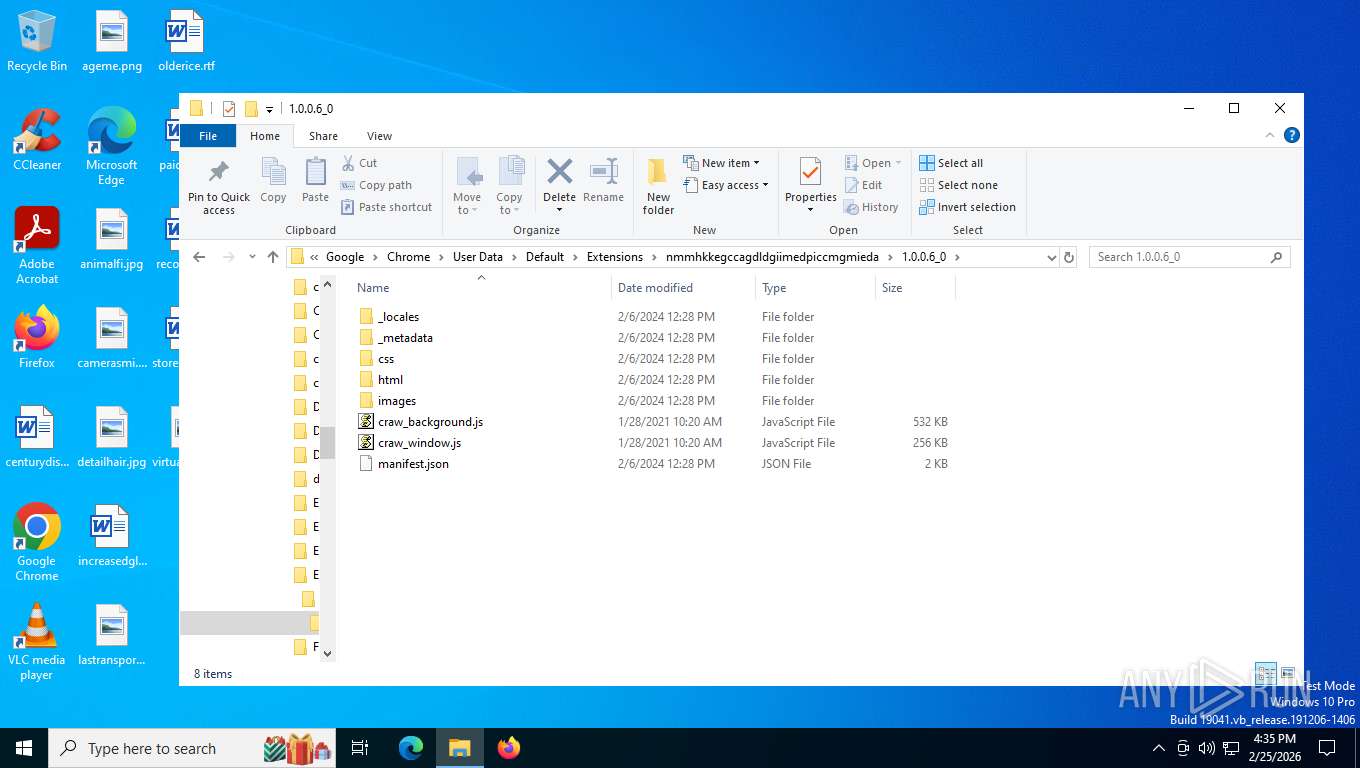
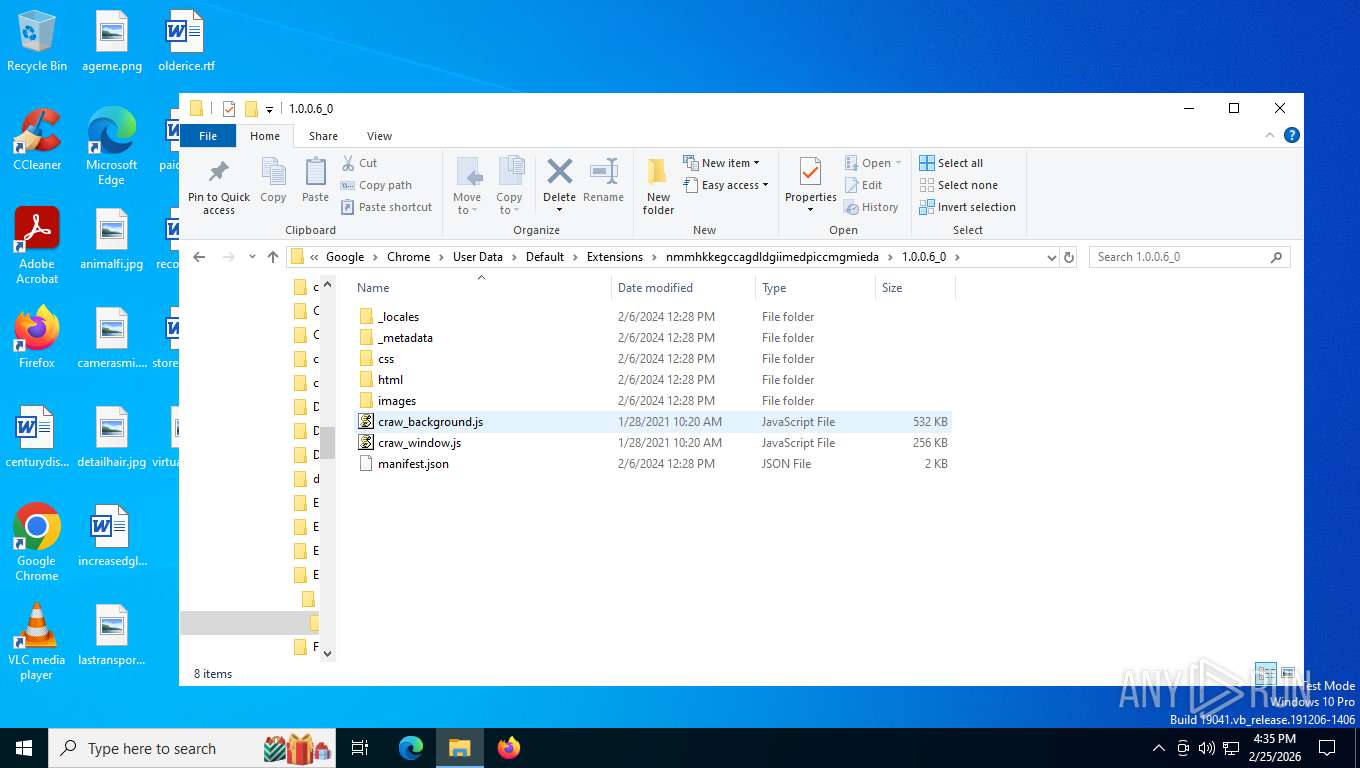
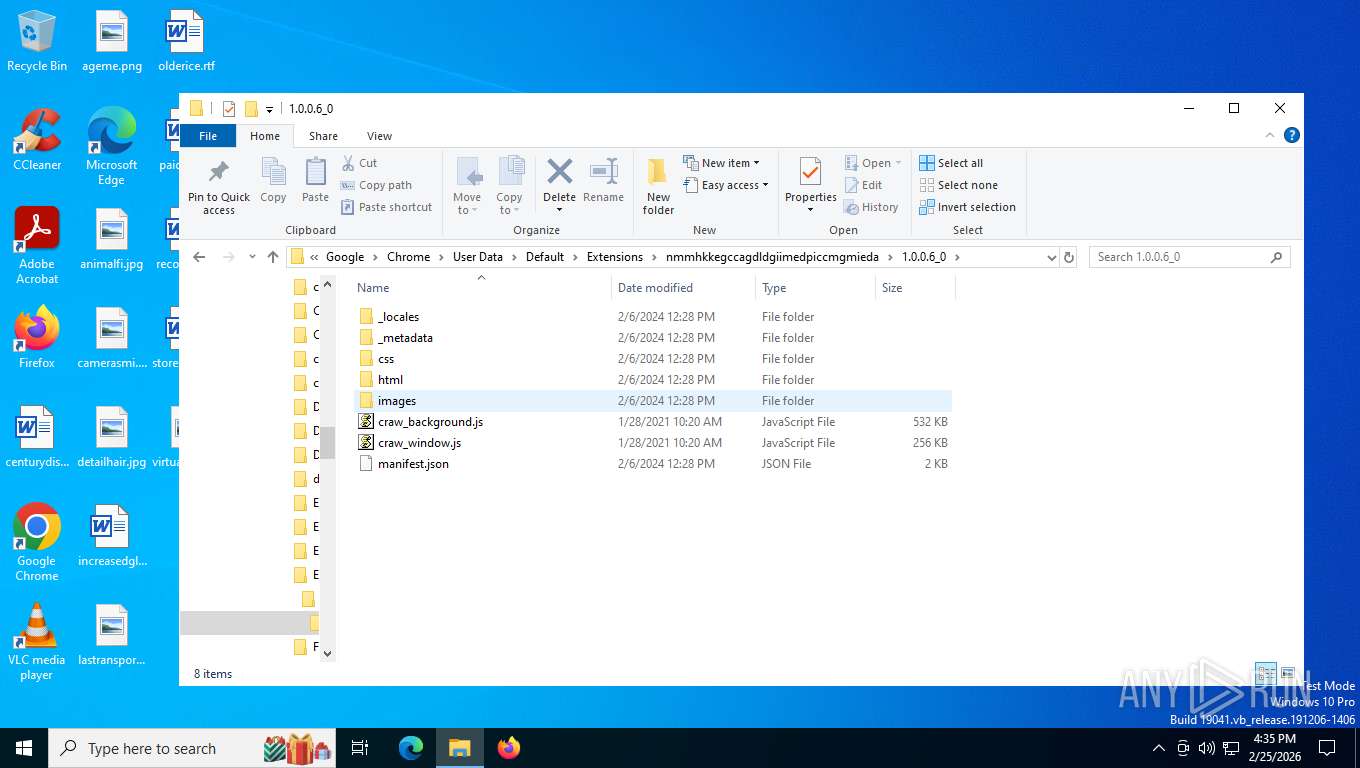
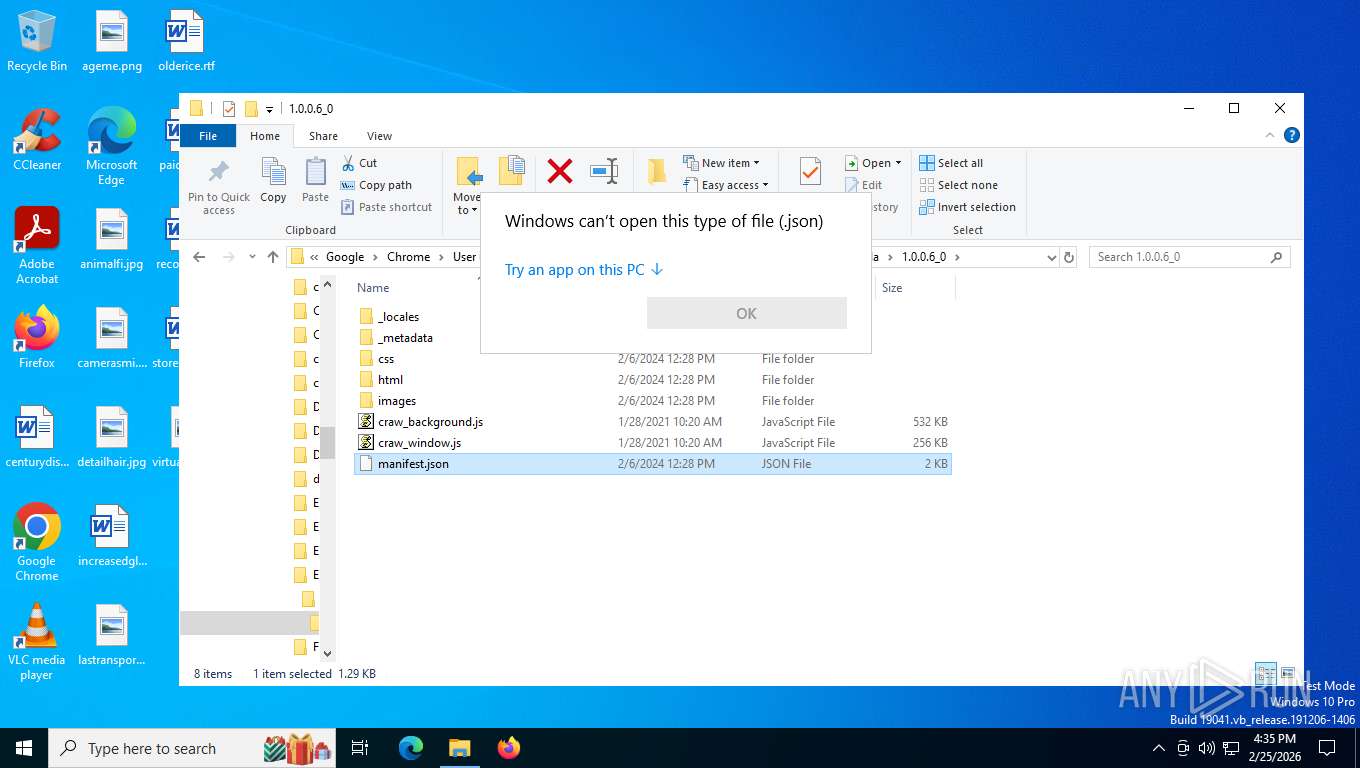
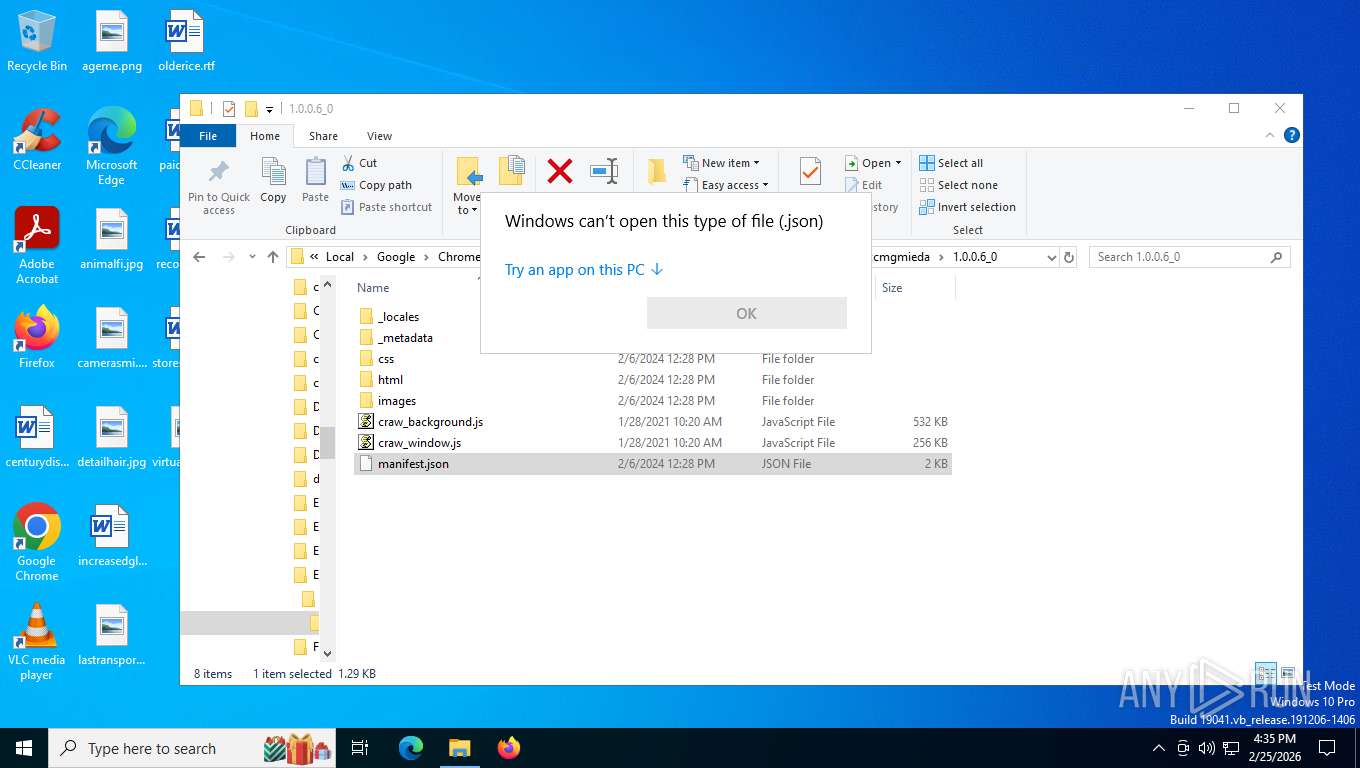
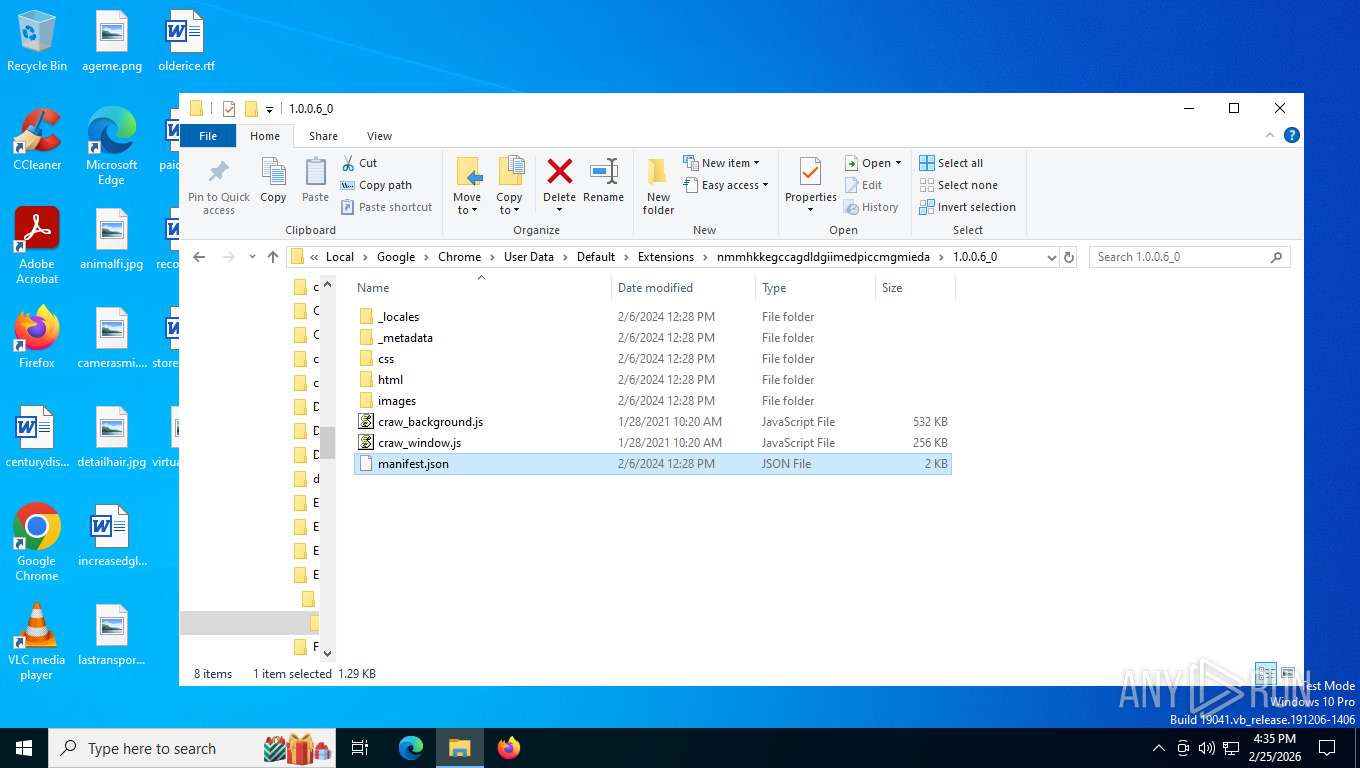
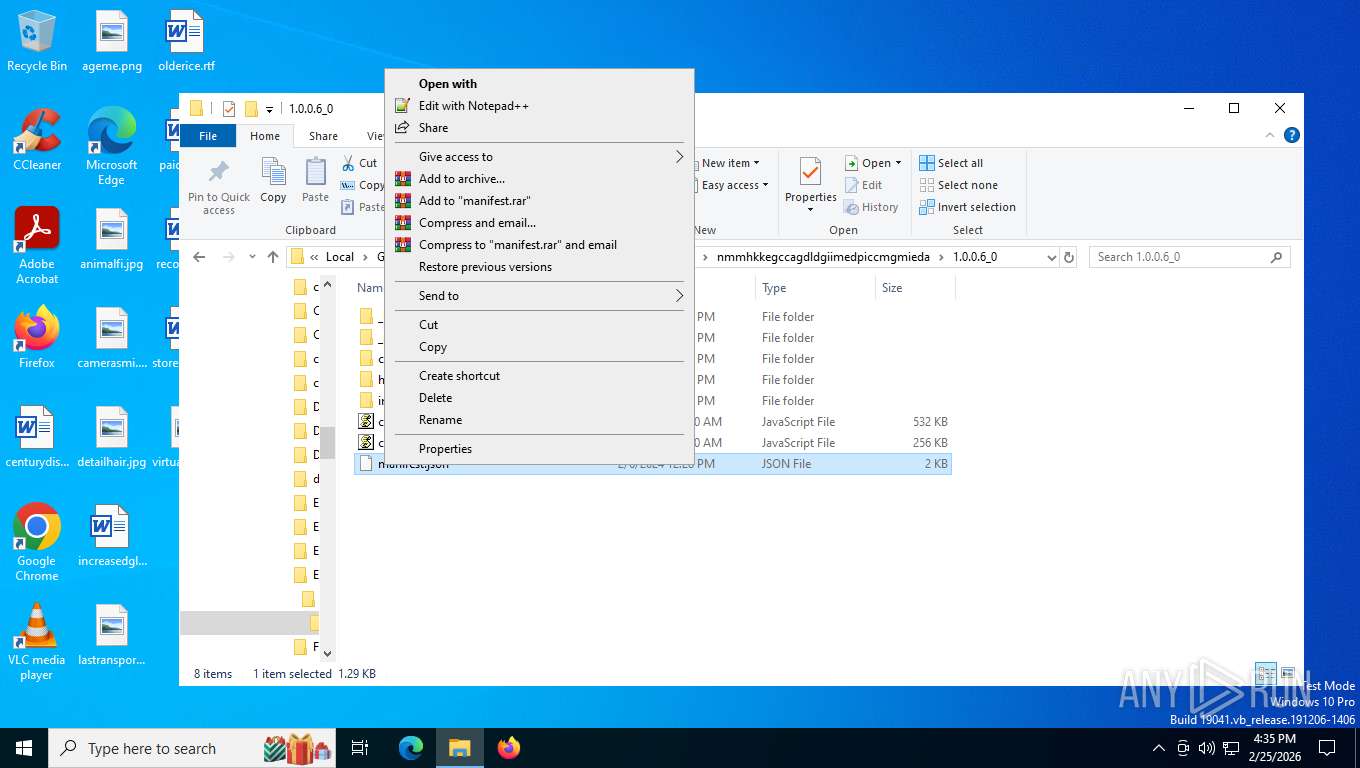
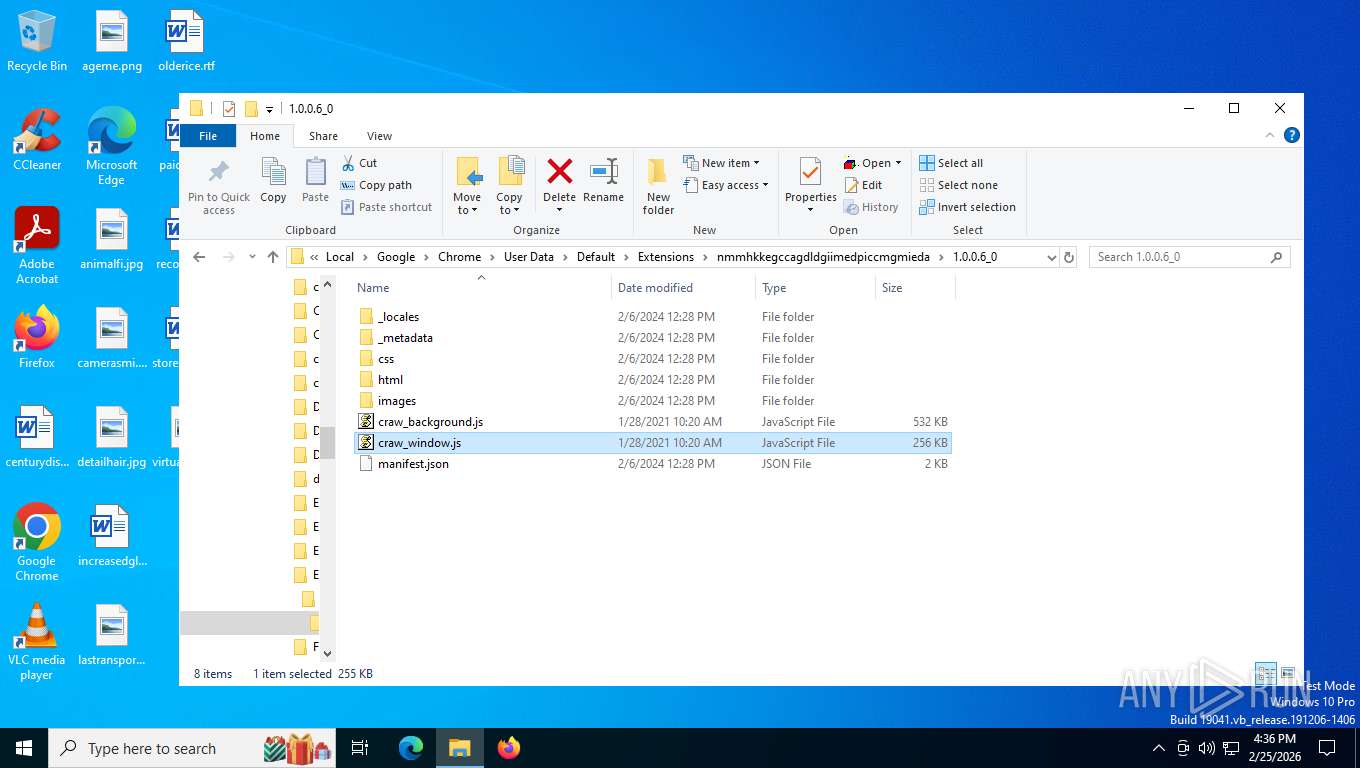
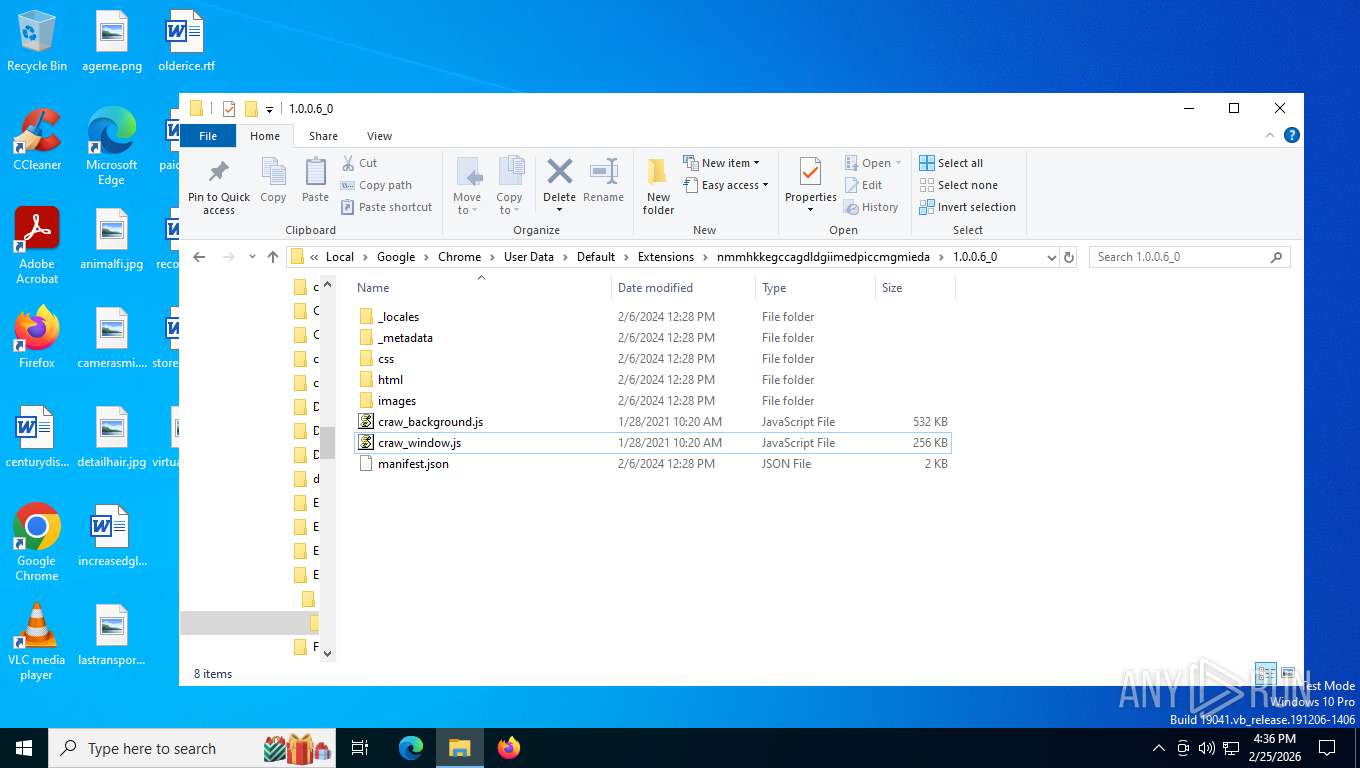
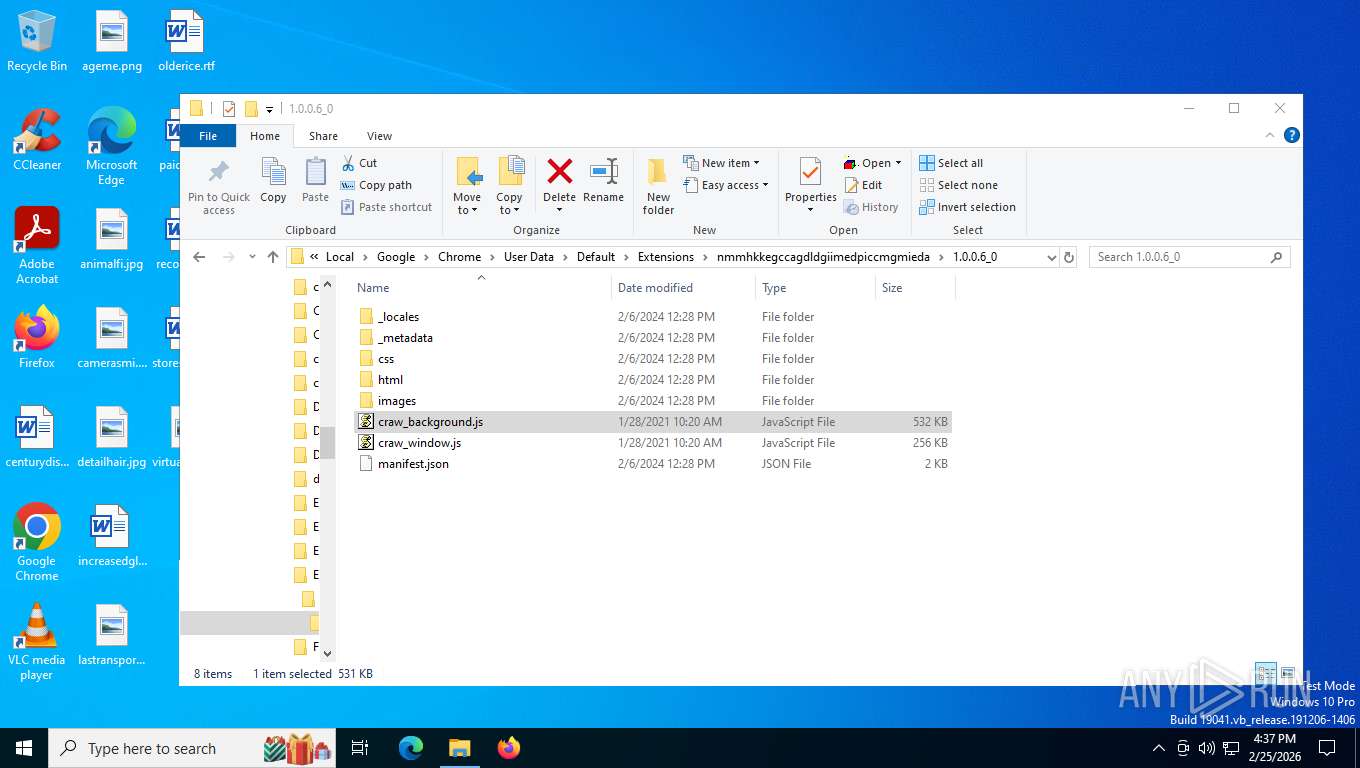
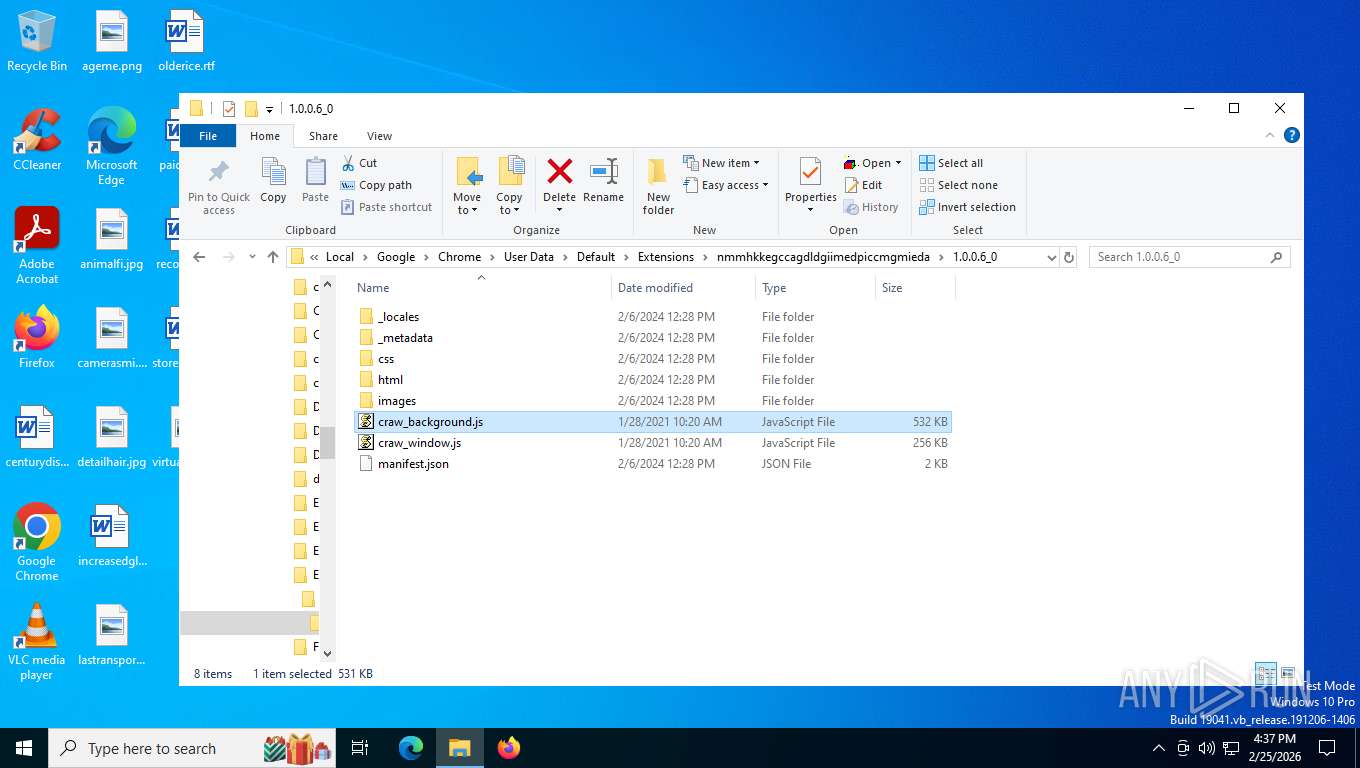
Browser headless start
- chrome.exe (PID: 9176)
- chrome.exe (PID: 5184)
- chrome.exe (PID: 7408)
- chrome.exe (PID: 5040)
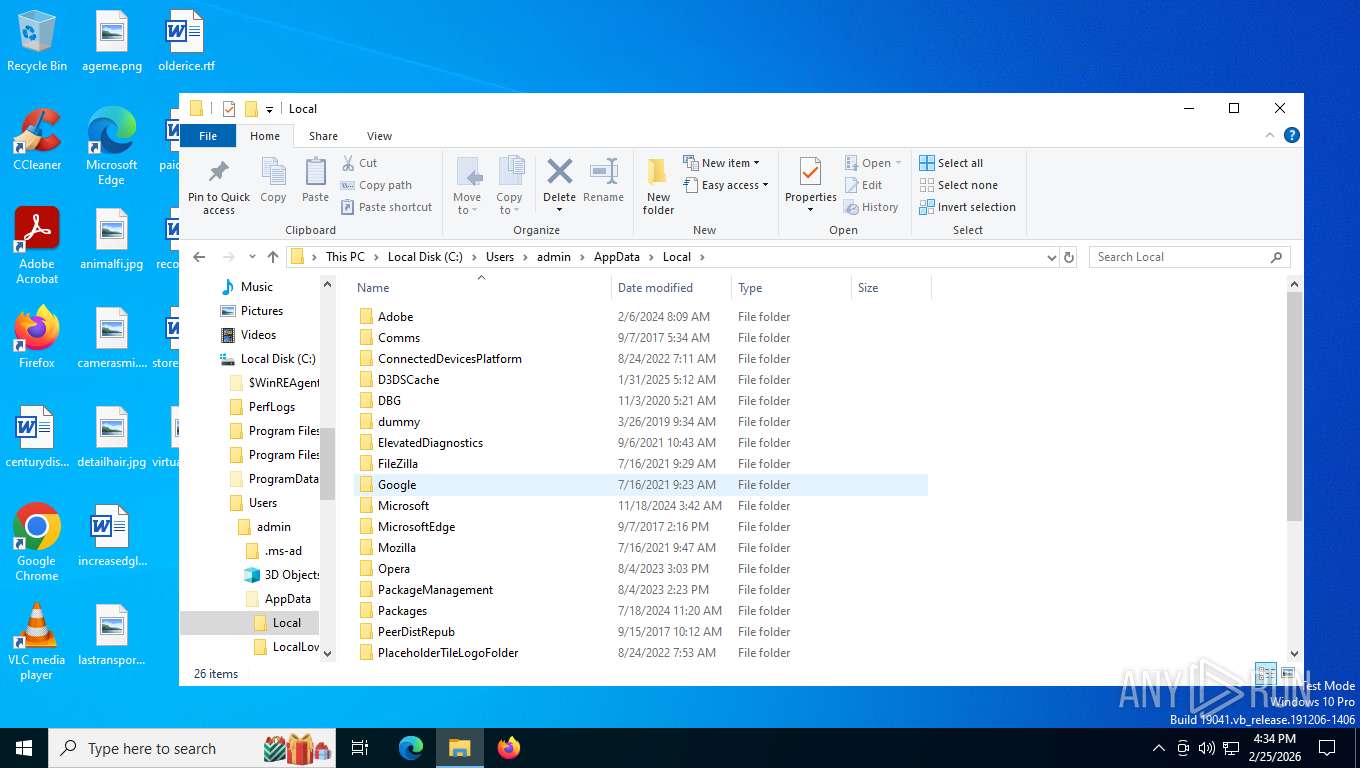
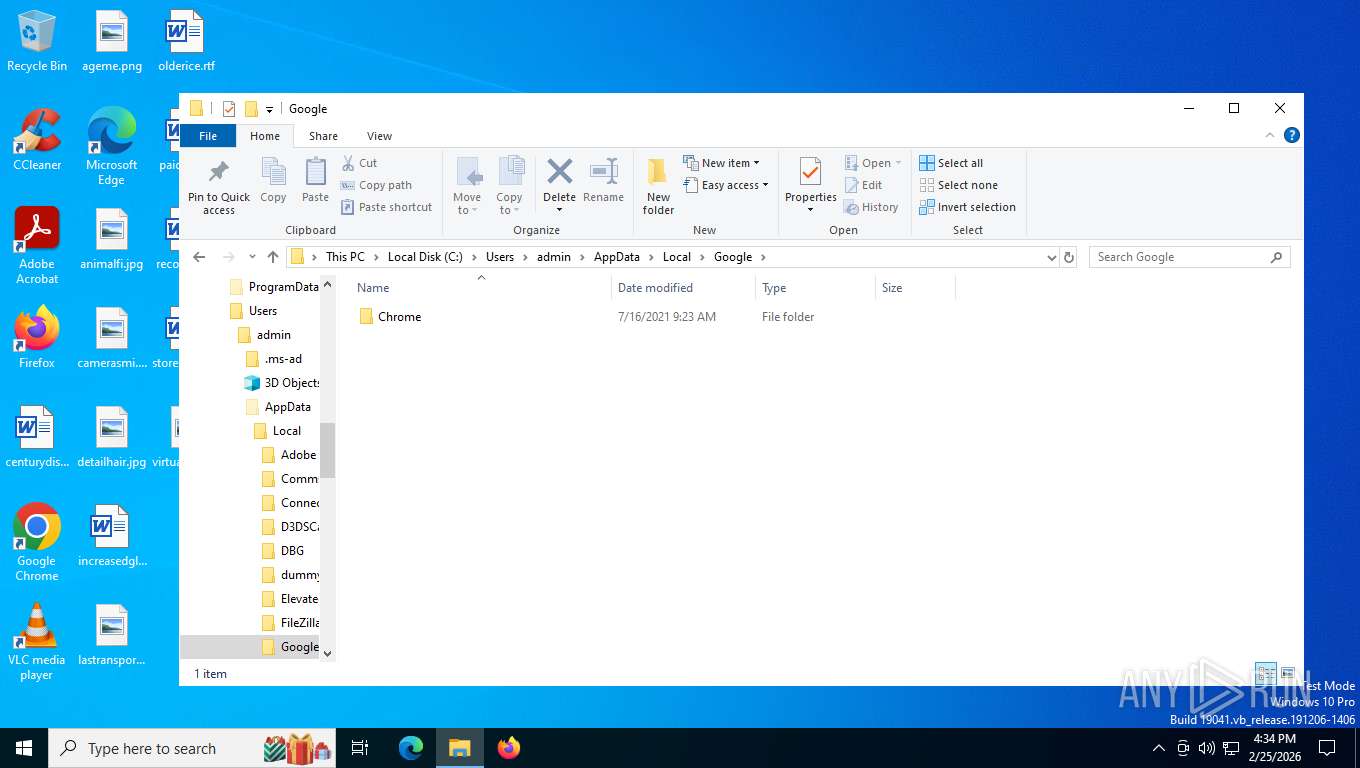
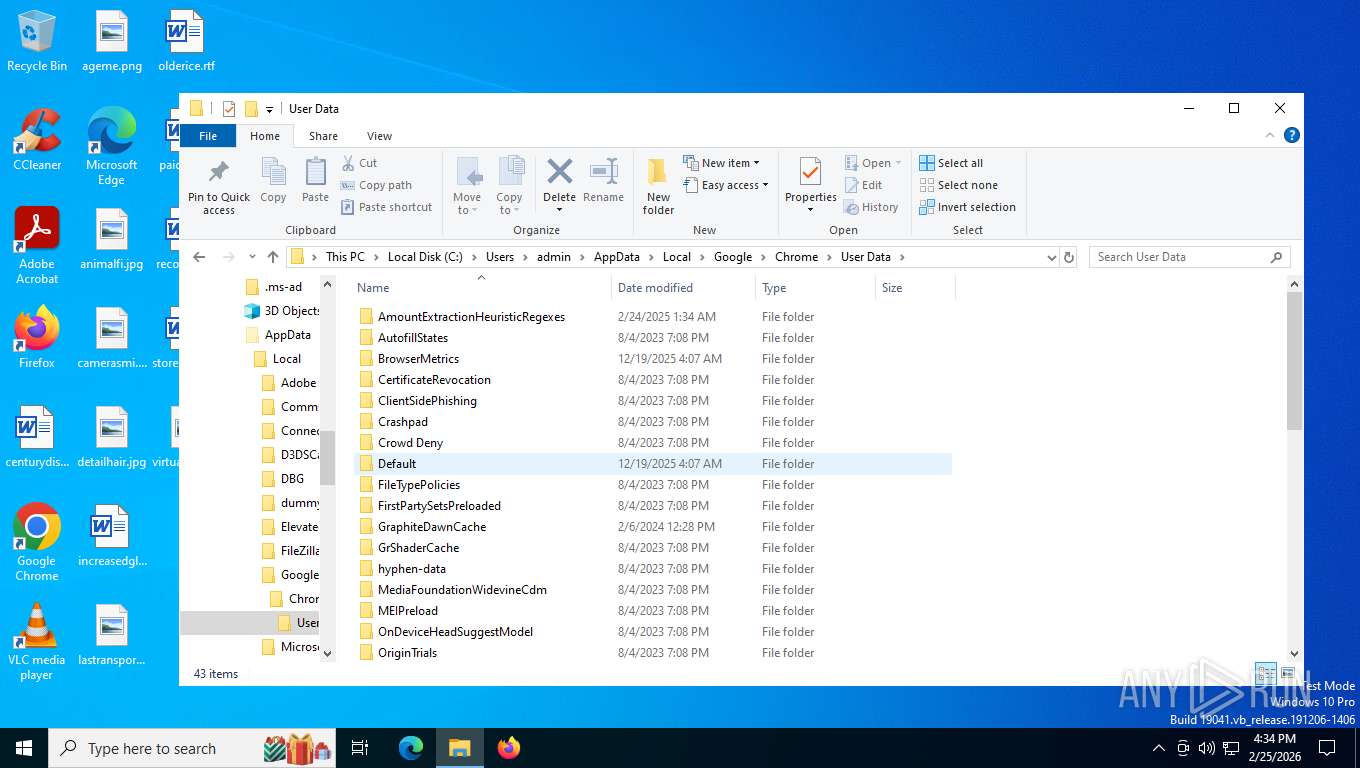
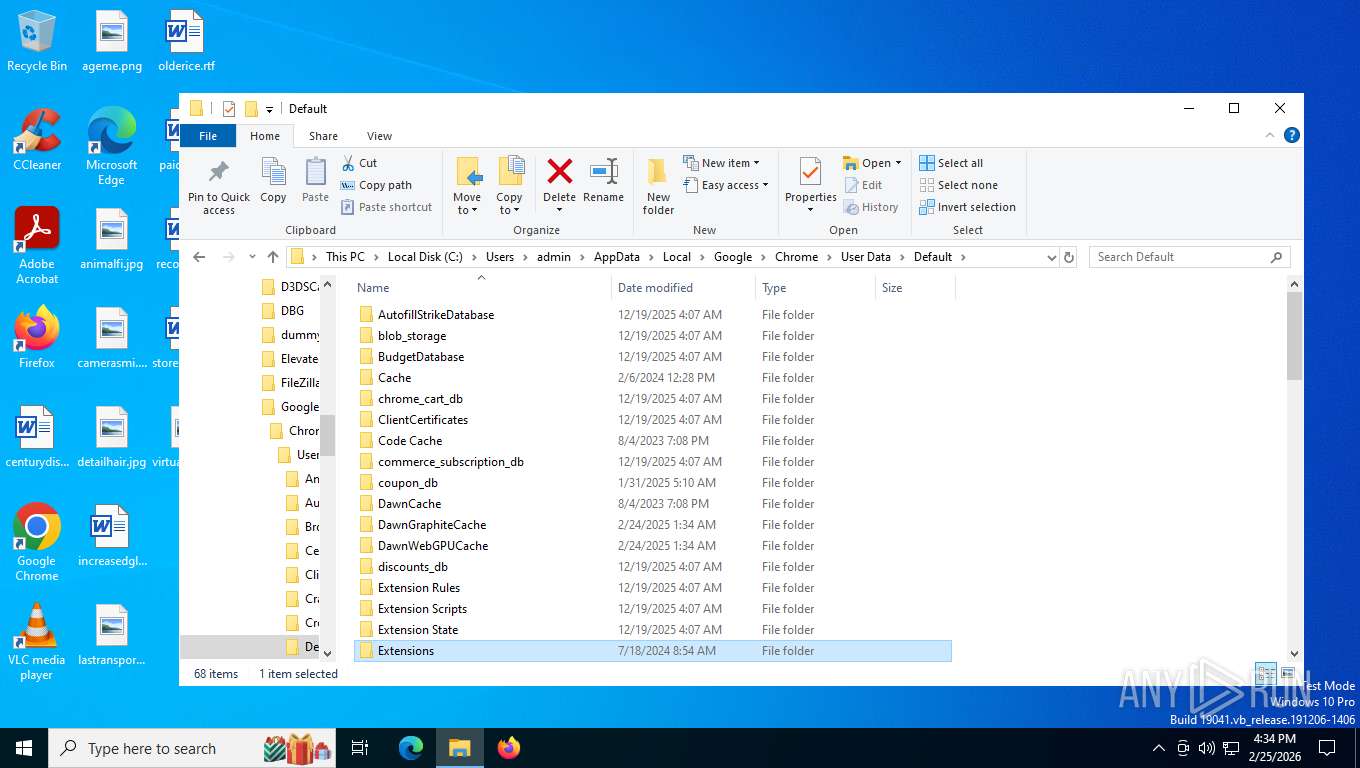
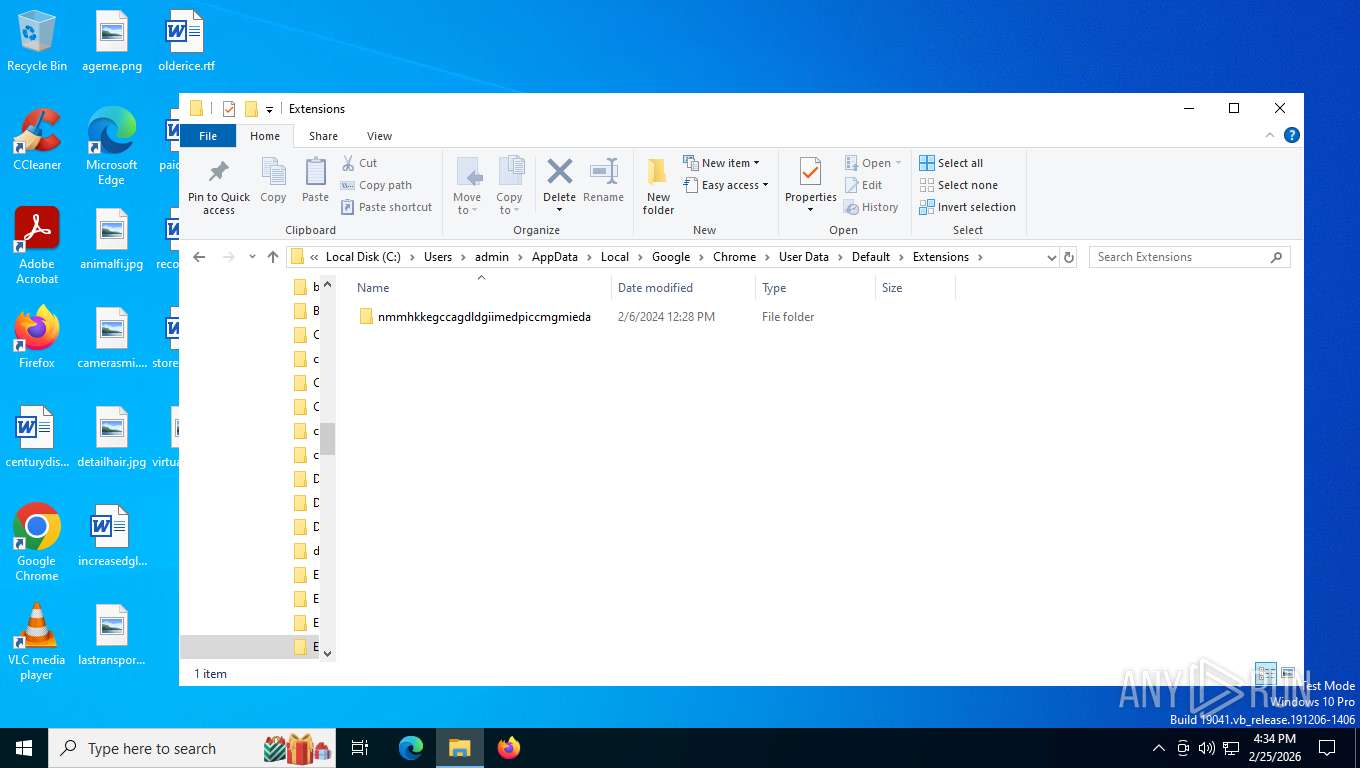
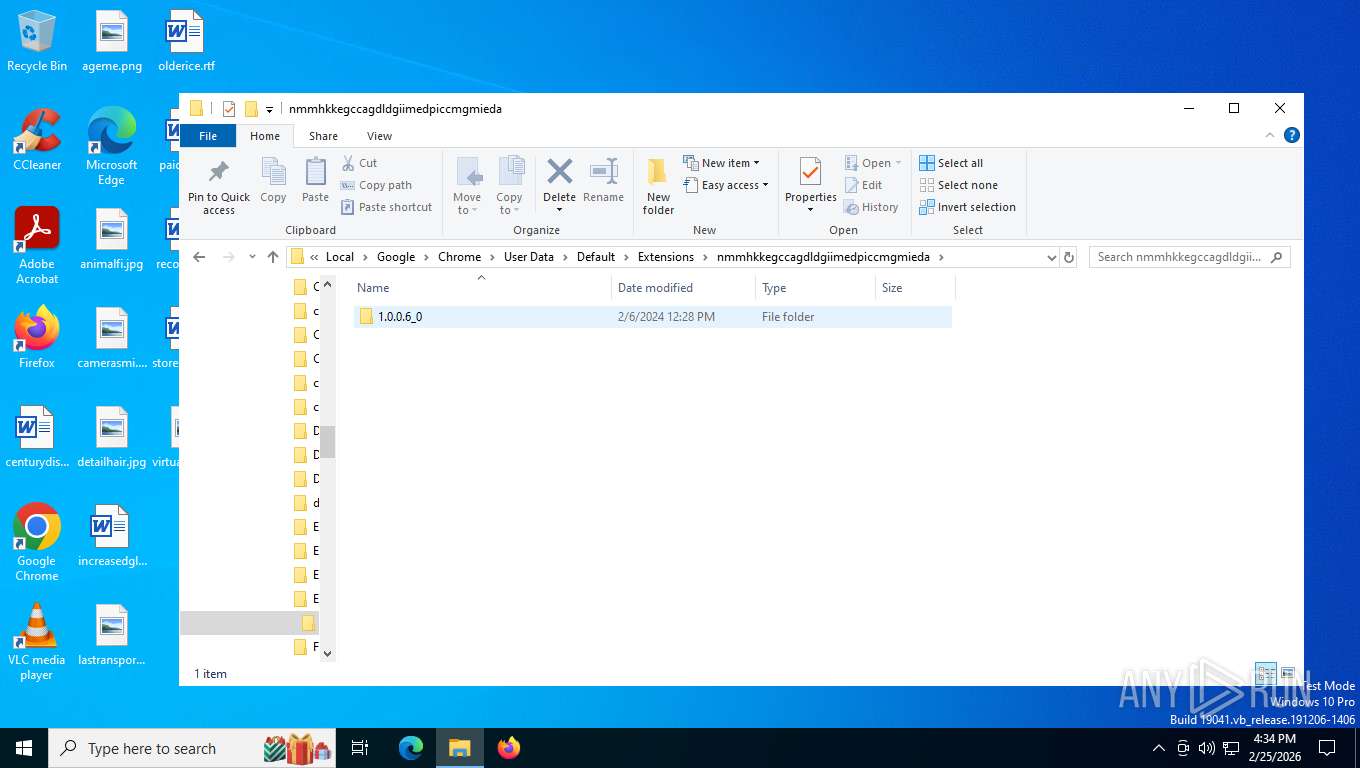
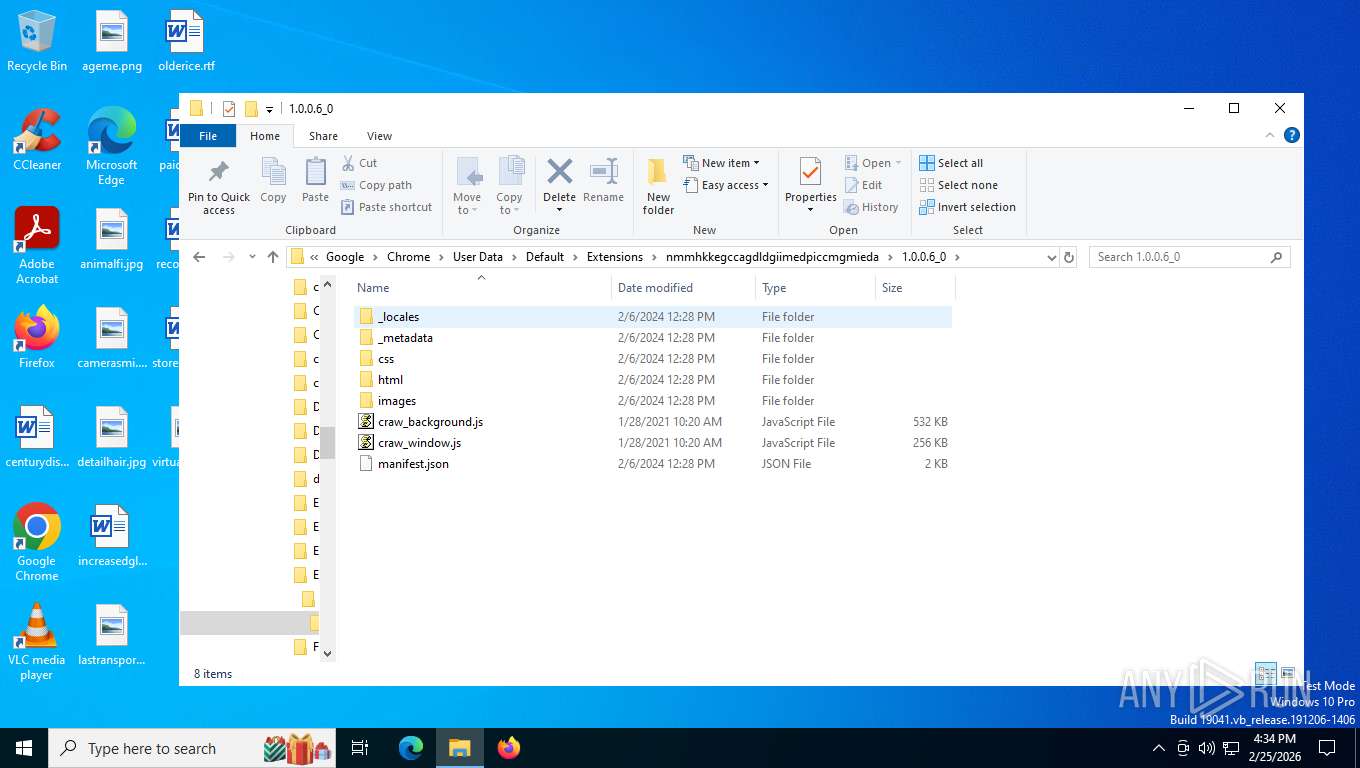
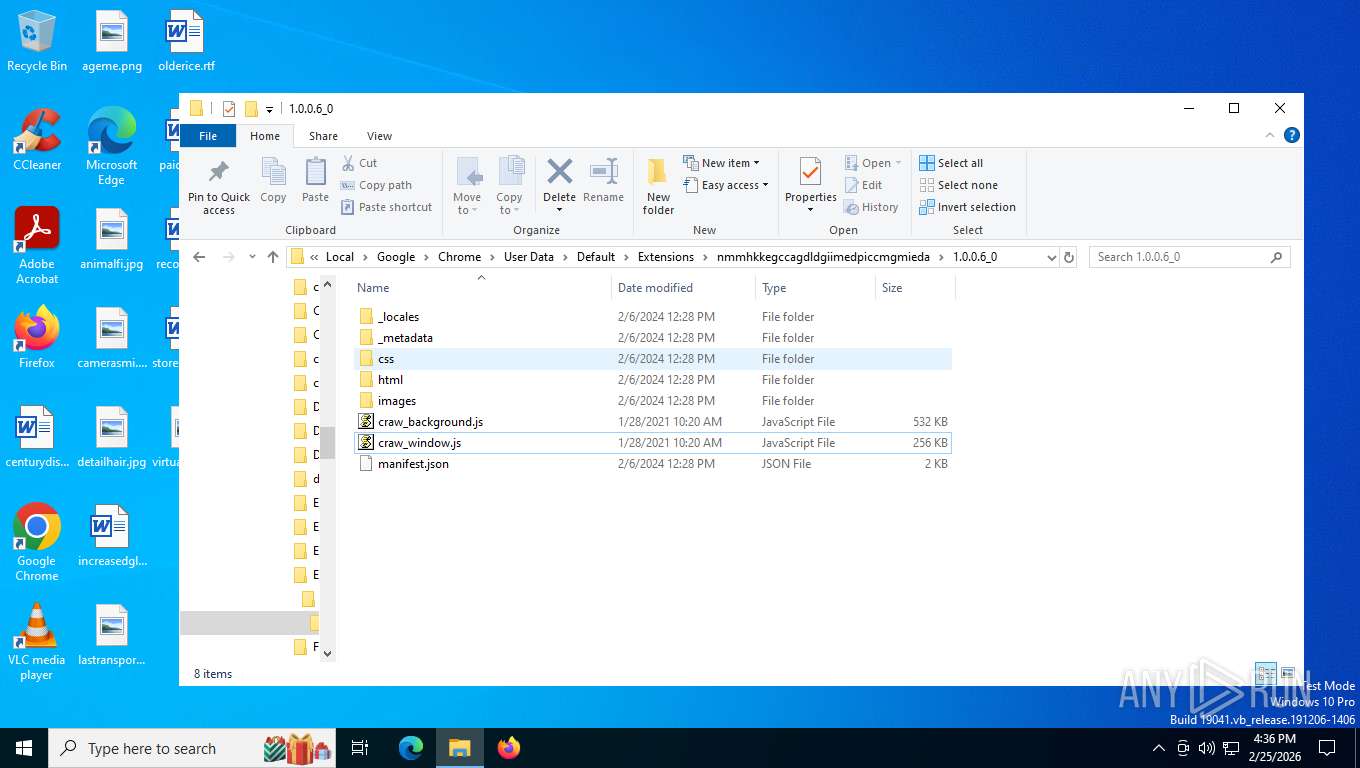
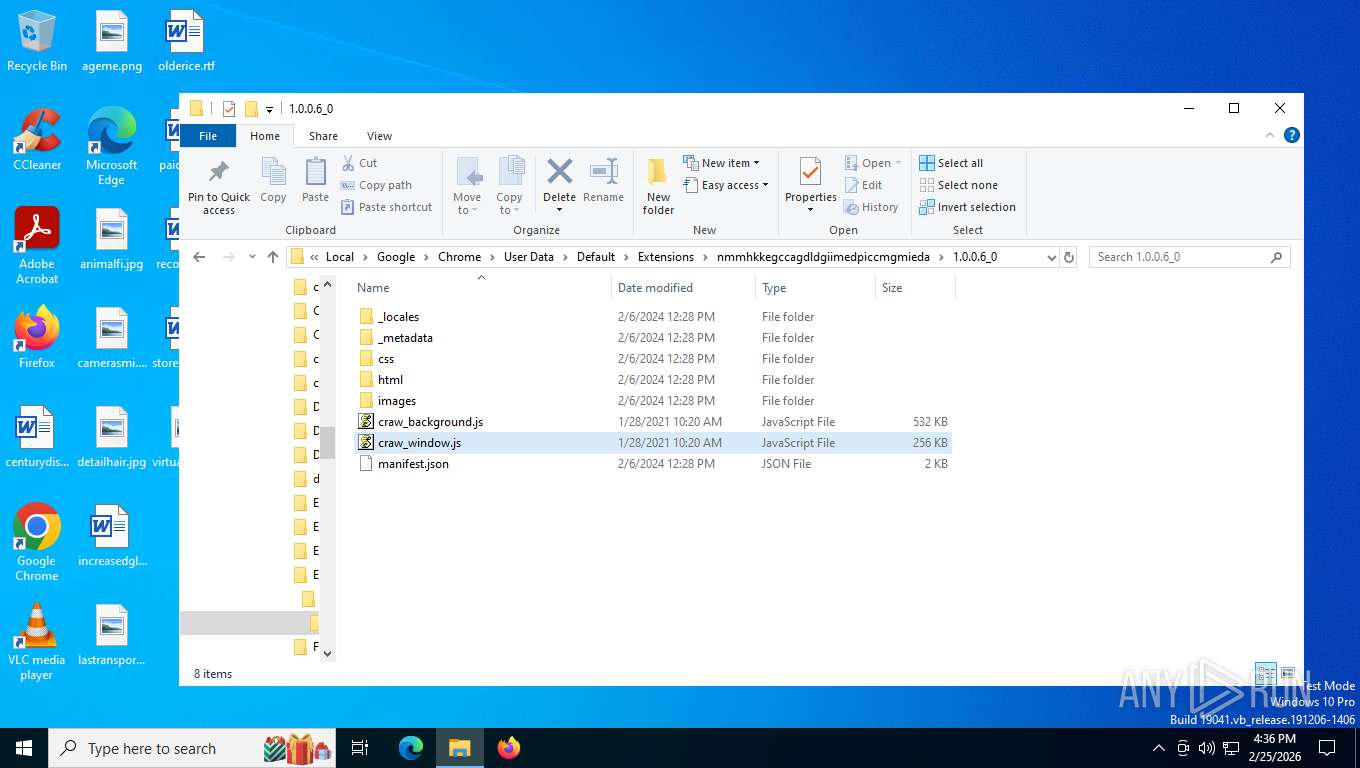
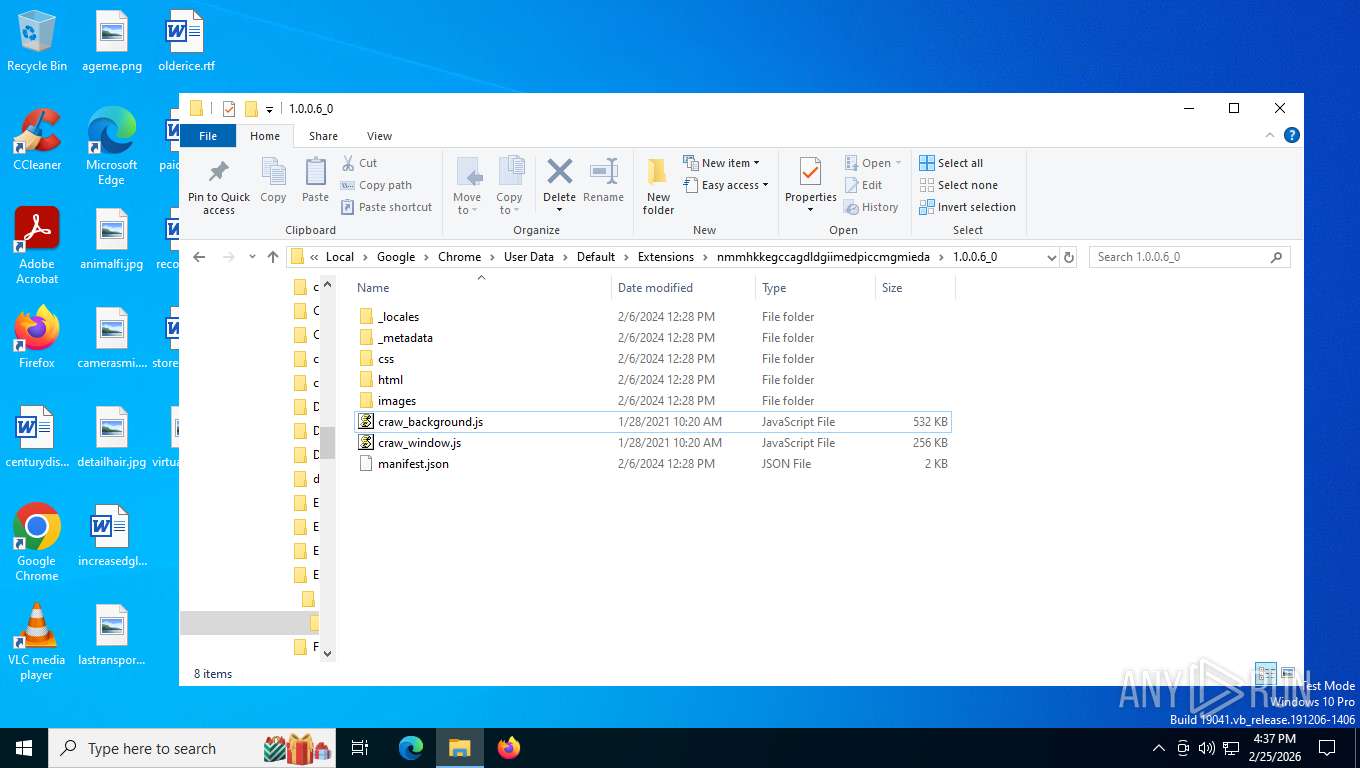
Browser launch with unusual user-data-dir
- chrome.exe (PID: 5184)
- platform_experience_helper.exe (PID: 6156)
- chrome.exe (PID: 7408)
The process executes via Task Scheduler
- platform_experience_helper.exe (PID: 5412)
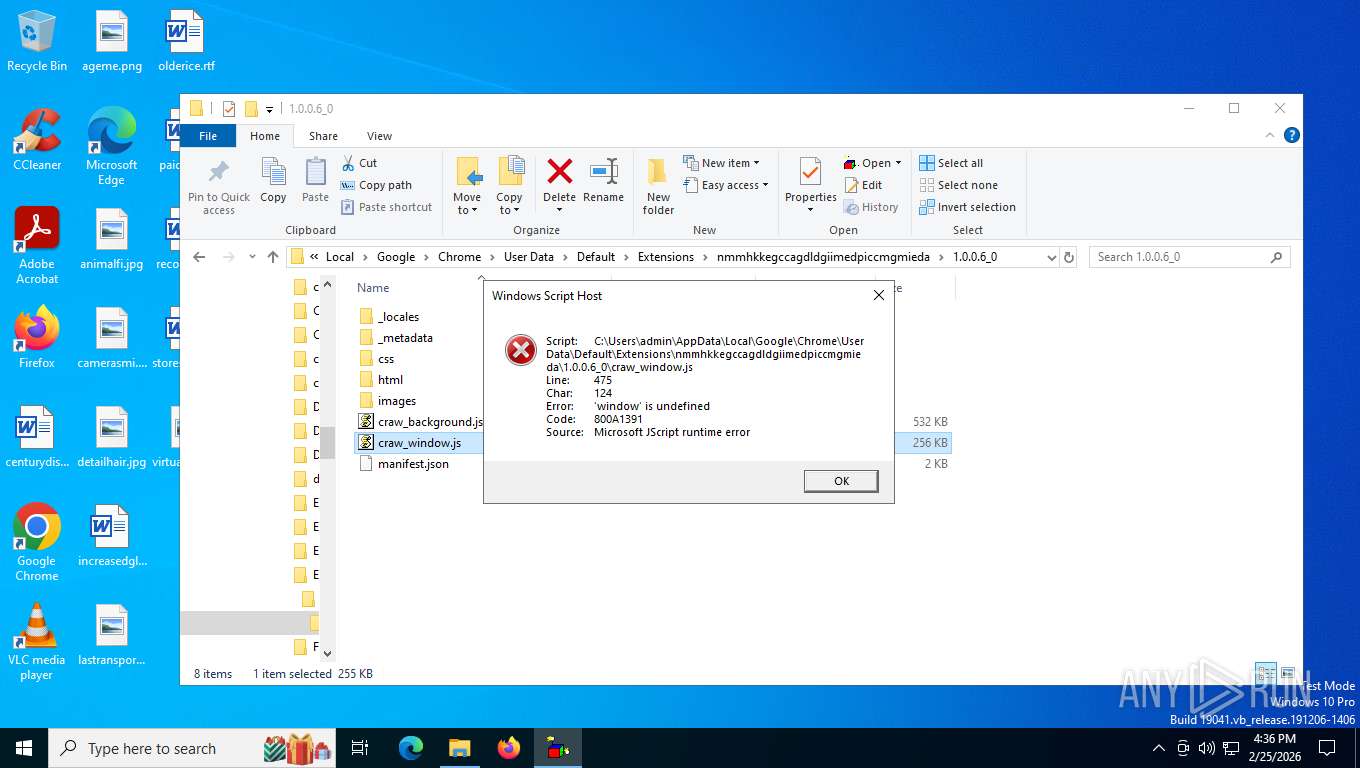
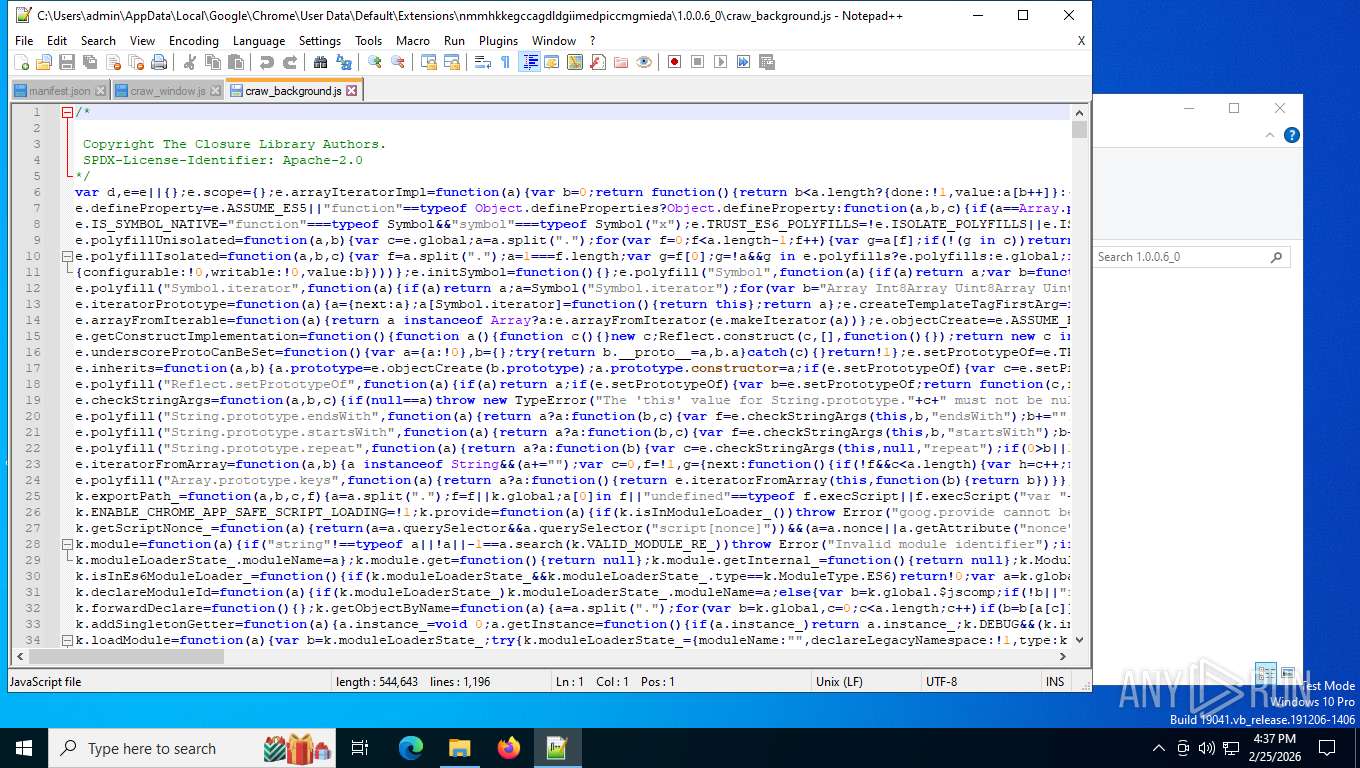
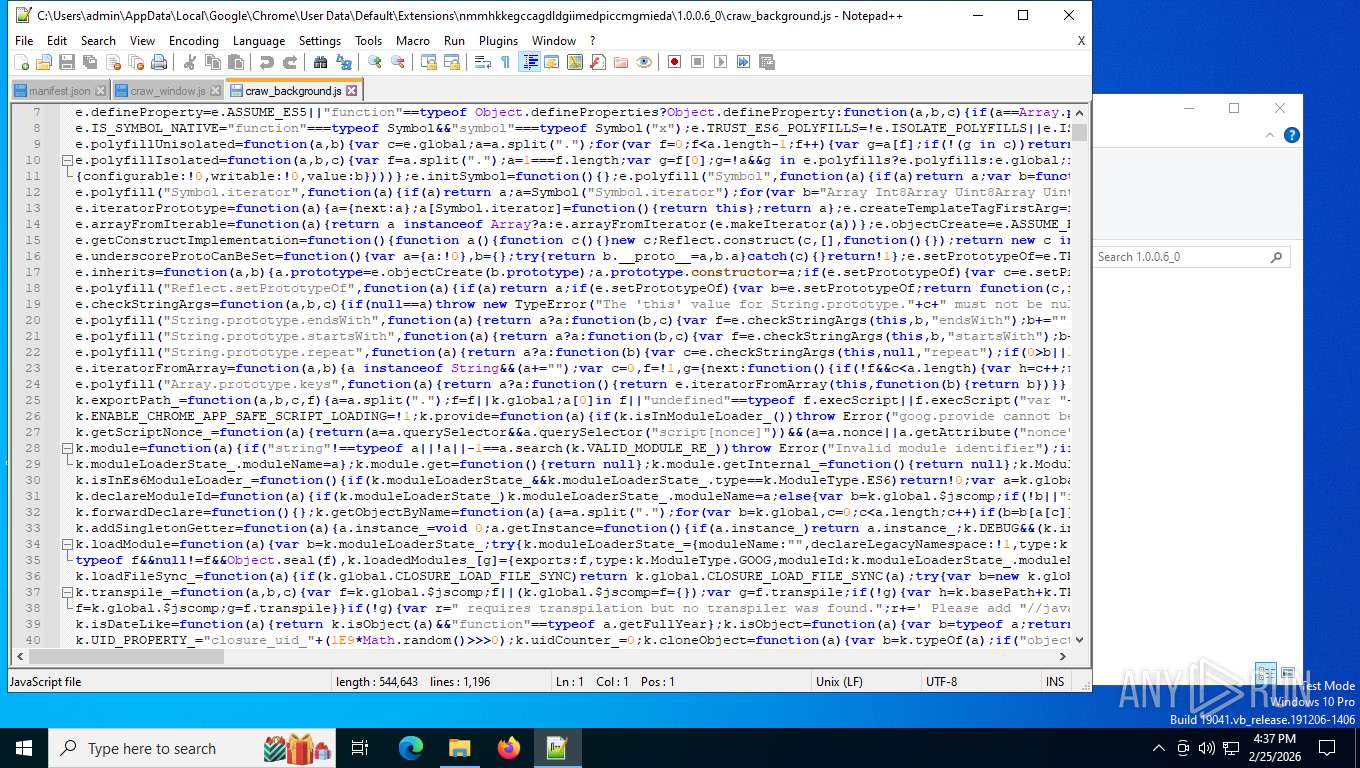
The process executes JS scripts
- wscript.exe (PID: 6920)
Possible stealing from browsers
- wscript.exe (PID: 6920)
INFO
The sample compiled with english language support
- platform_experience_helper.exe (PID: 6156)
Reads the computer name
- platform_experience_helper.exe (PID: 6156)
- platform_experience_helper.exe (PID: 5412)
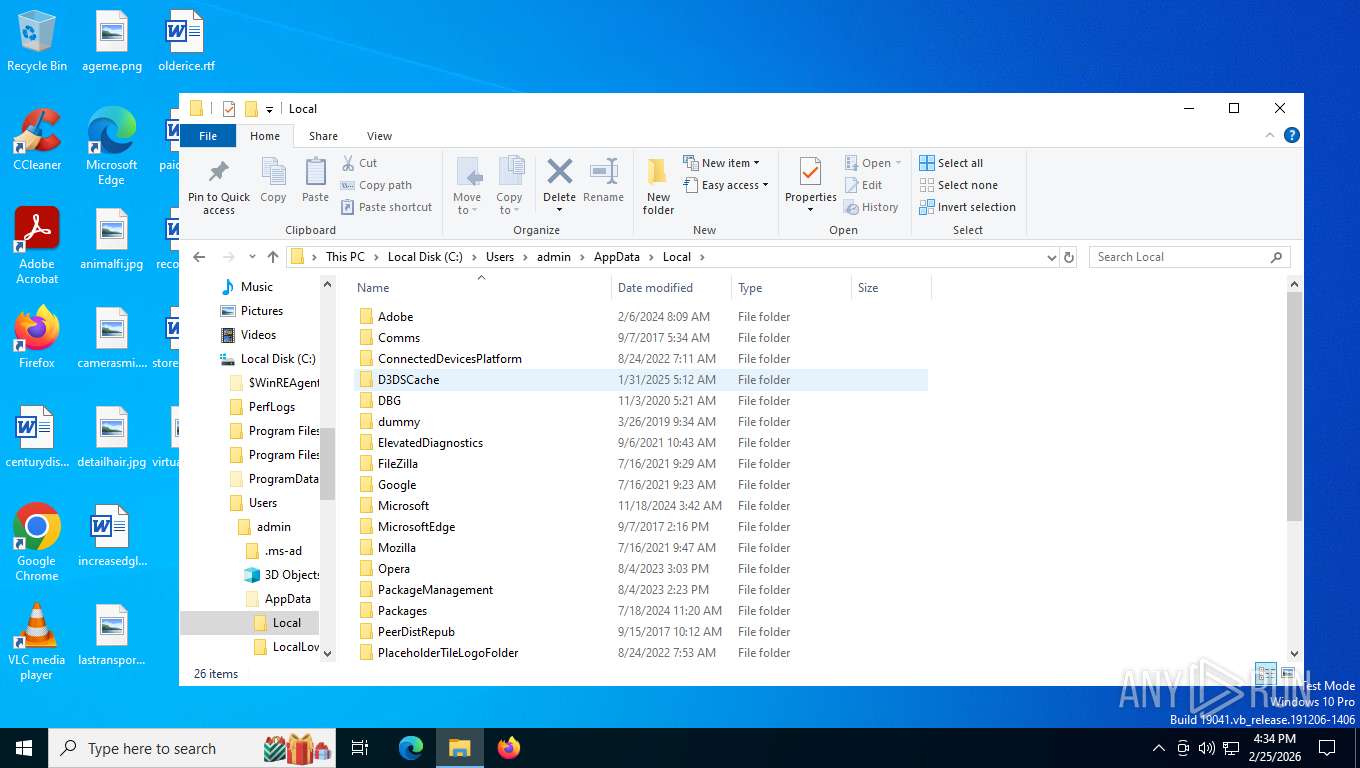
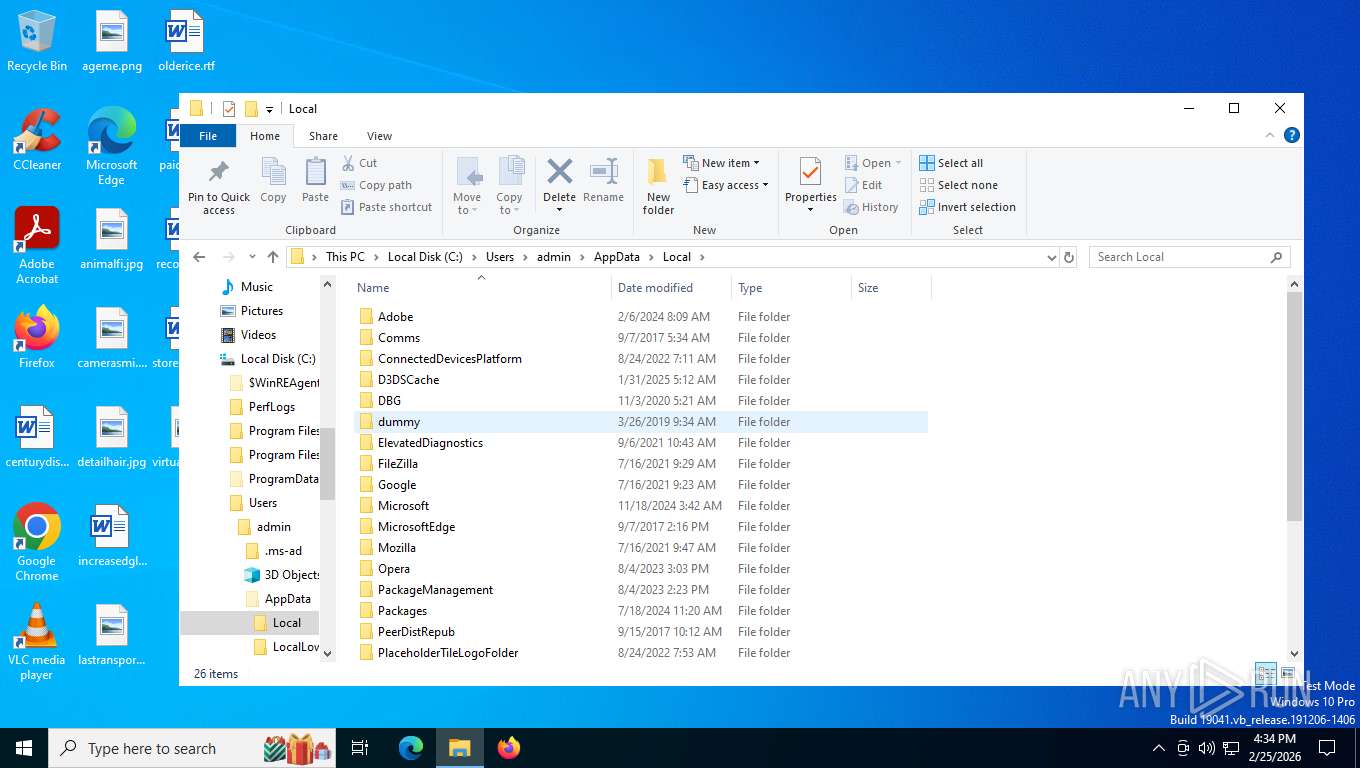
Create files in a temporary directory
- platform_experience_helper.exe (PID: 6156)
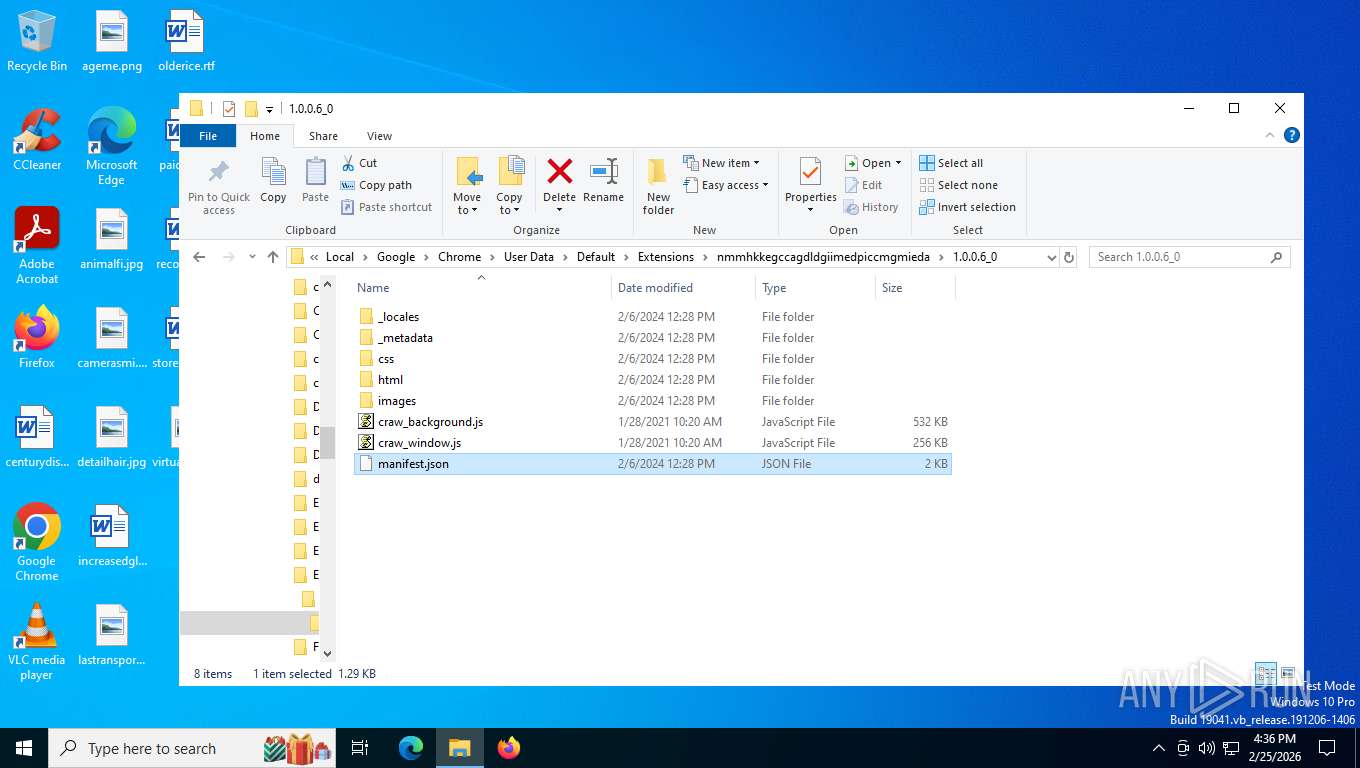
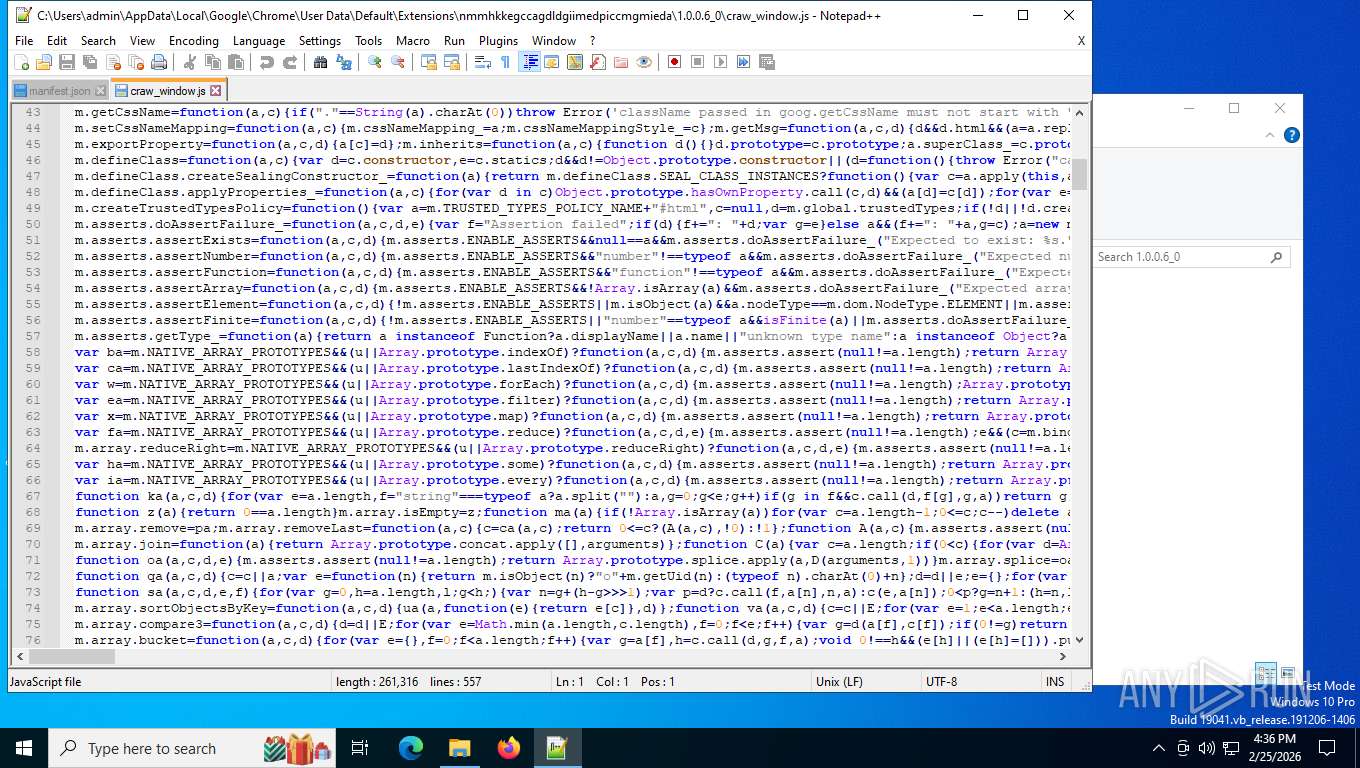
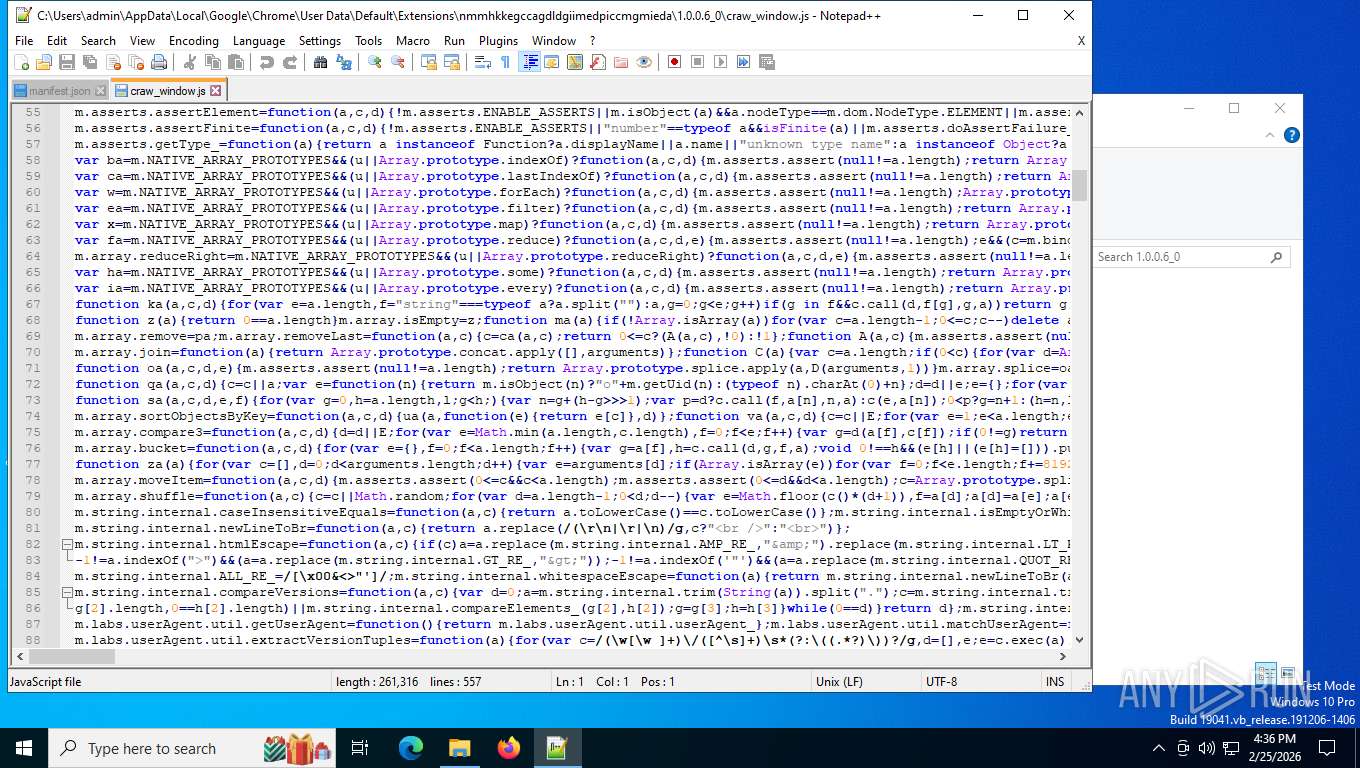
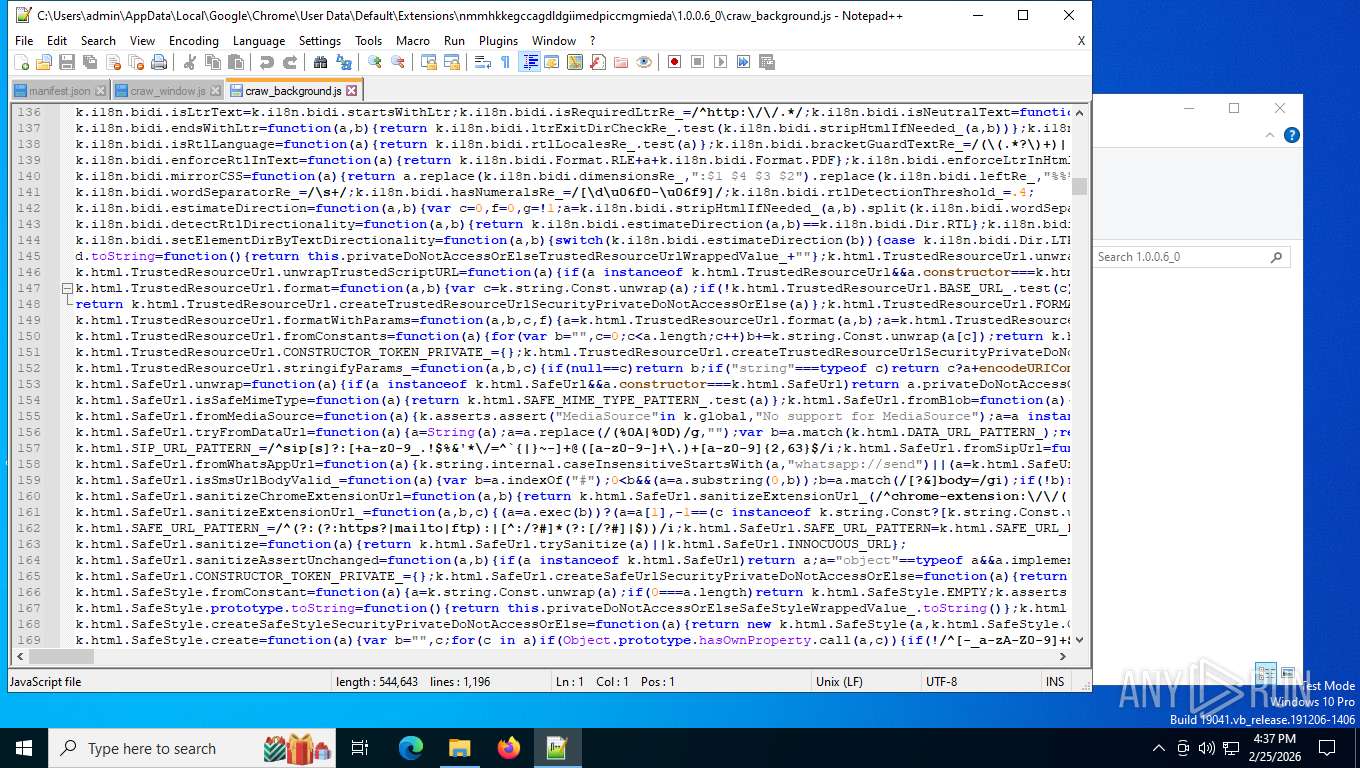
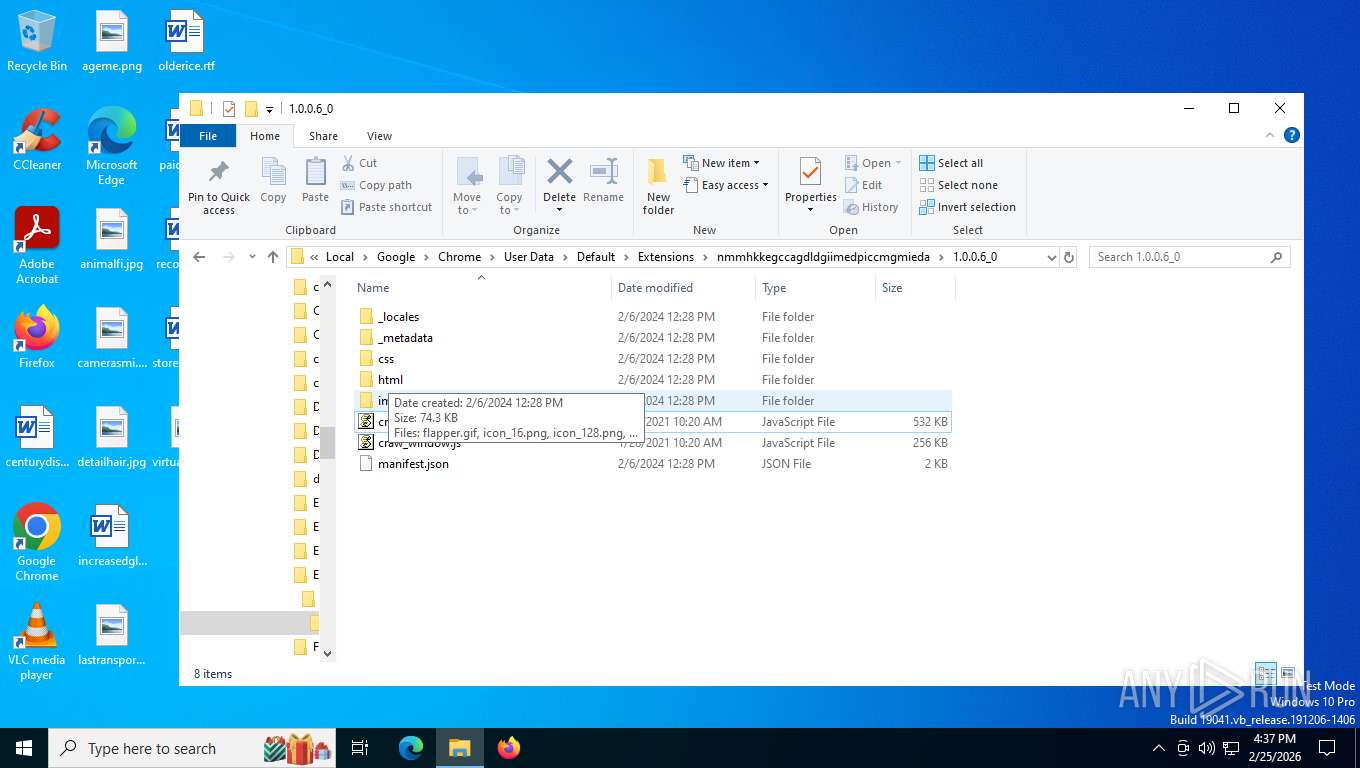
Drops script file
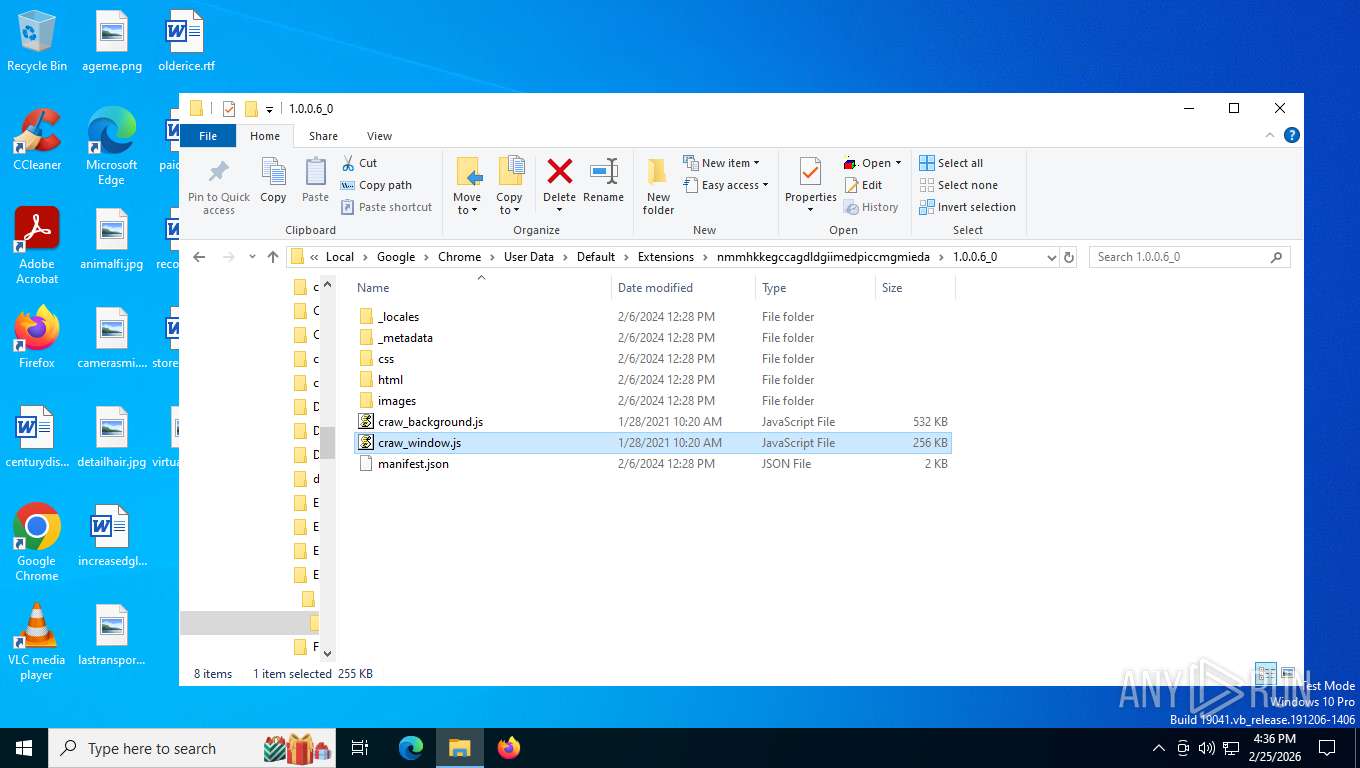
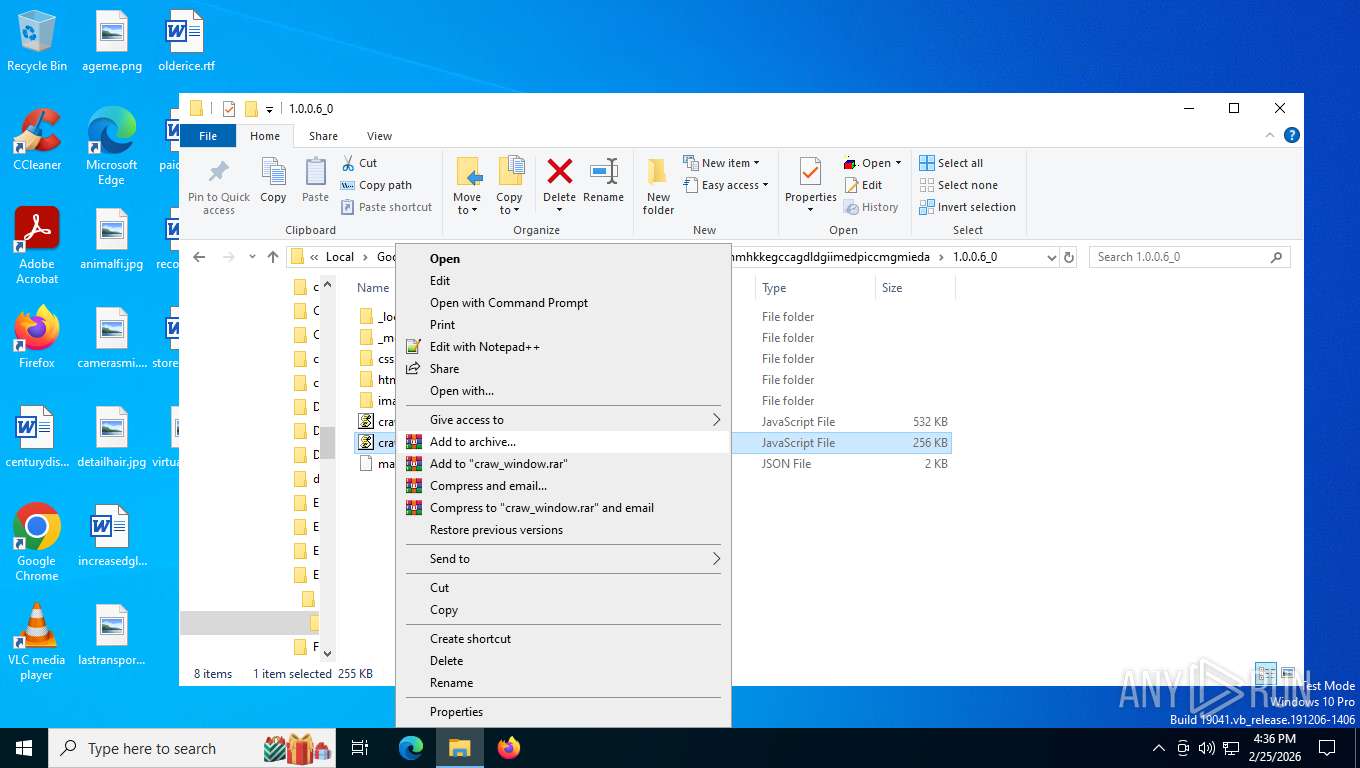
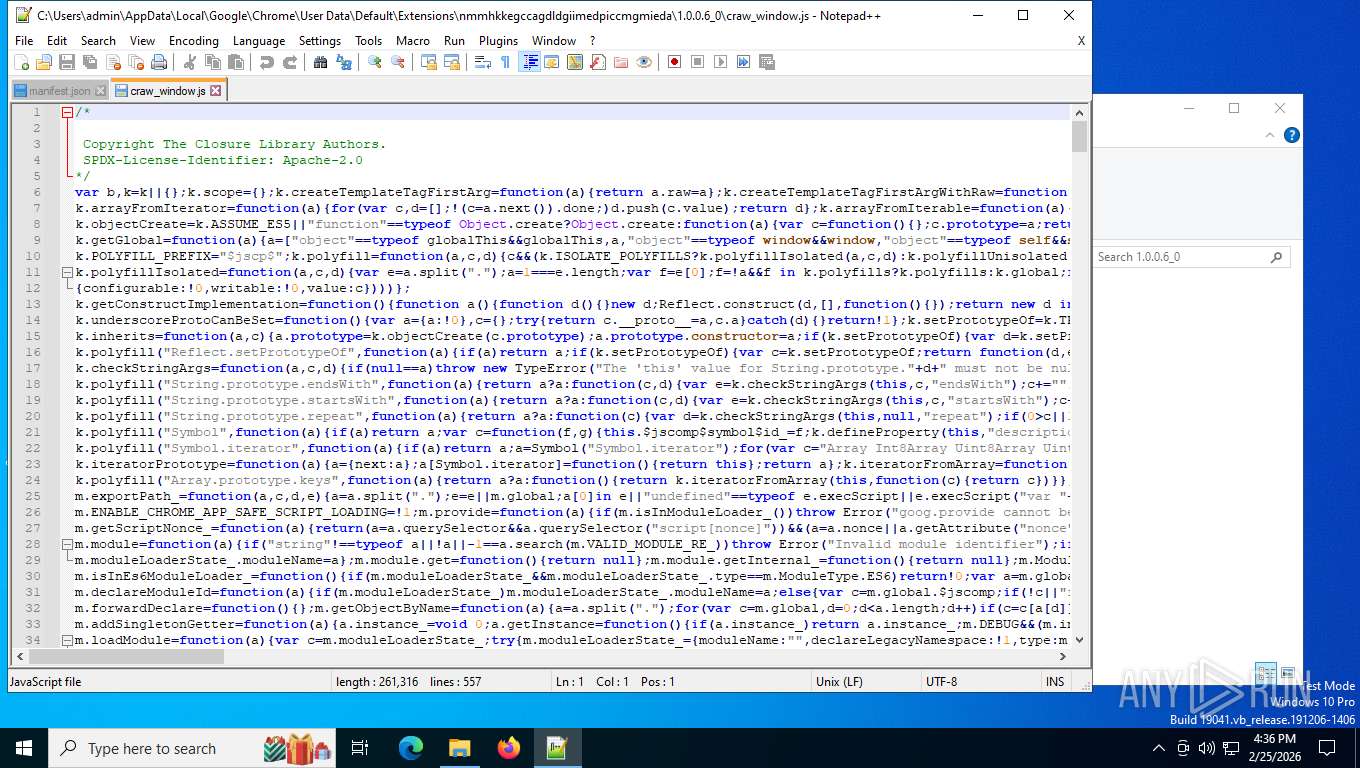
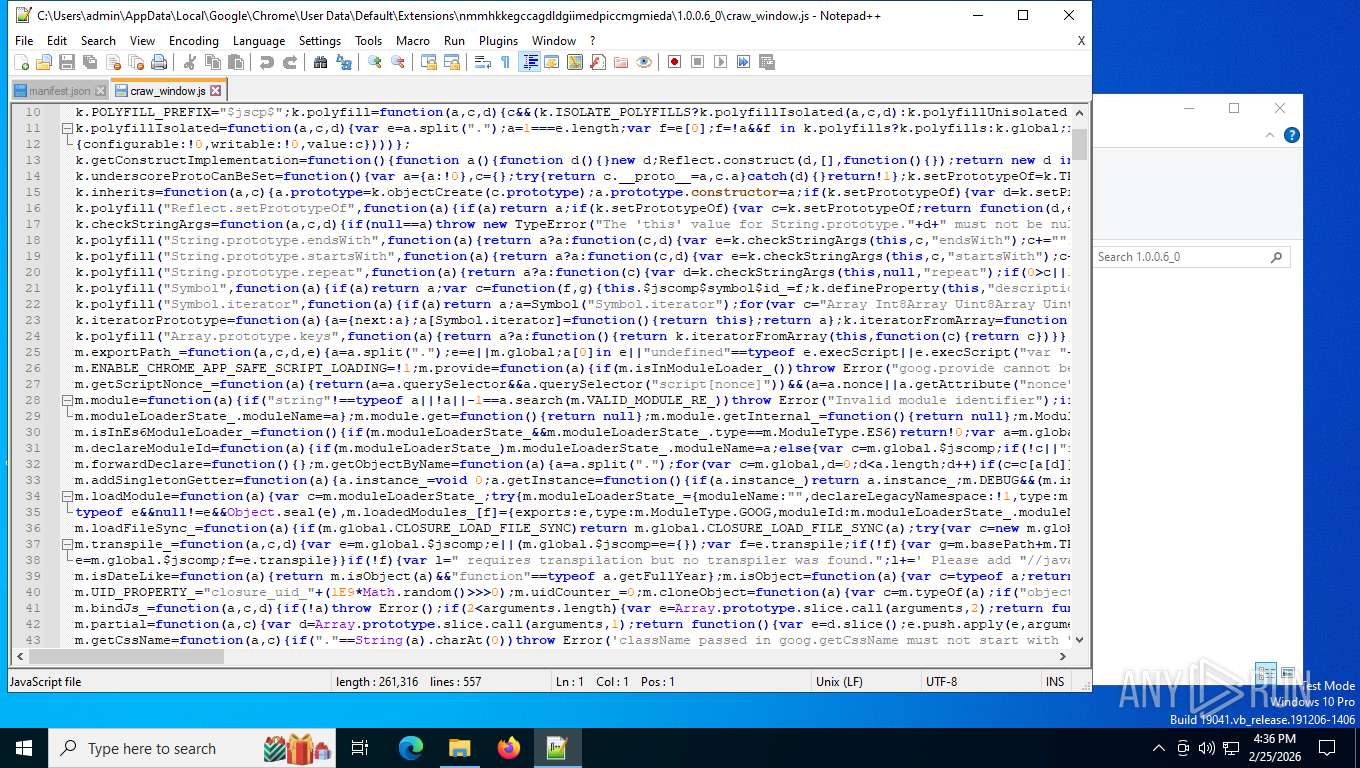
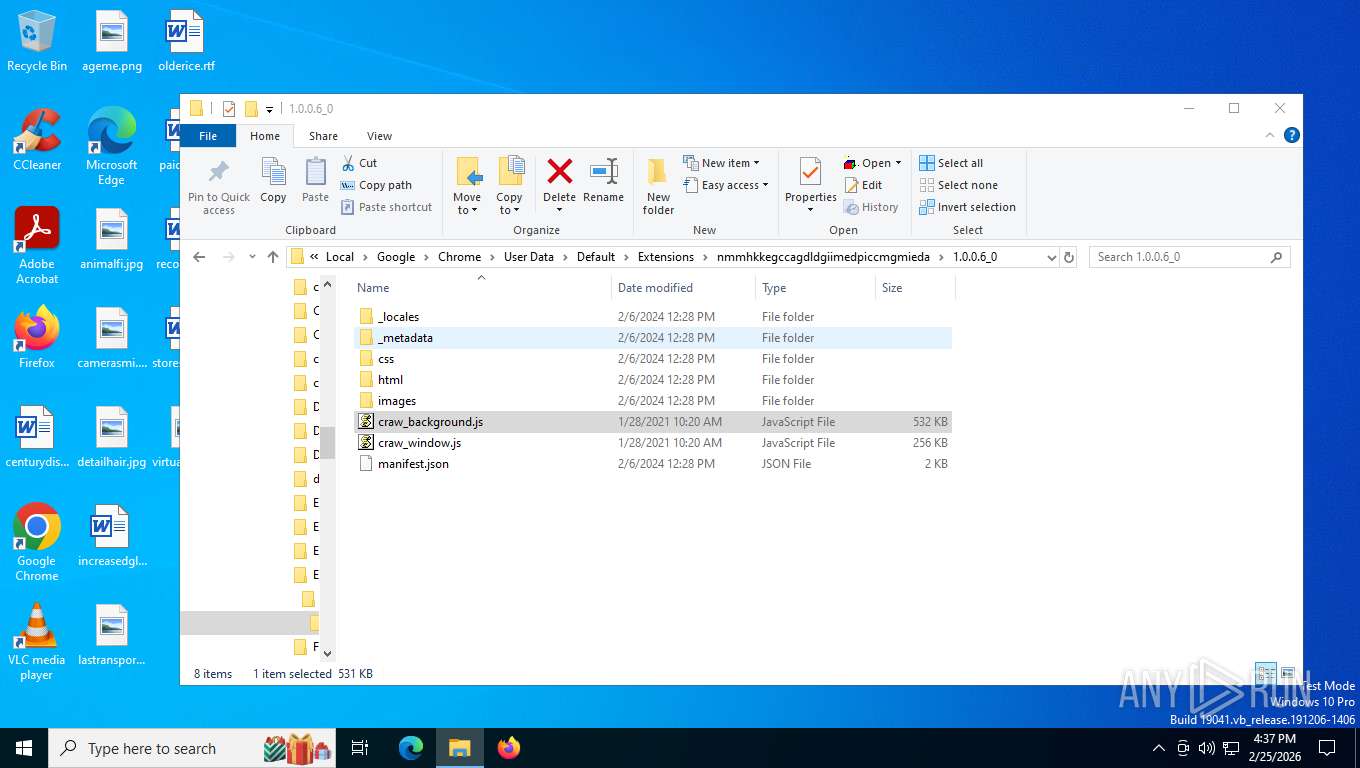
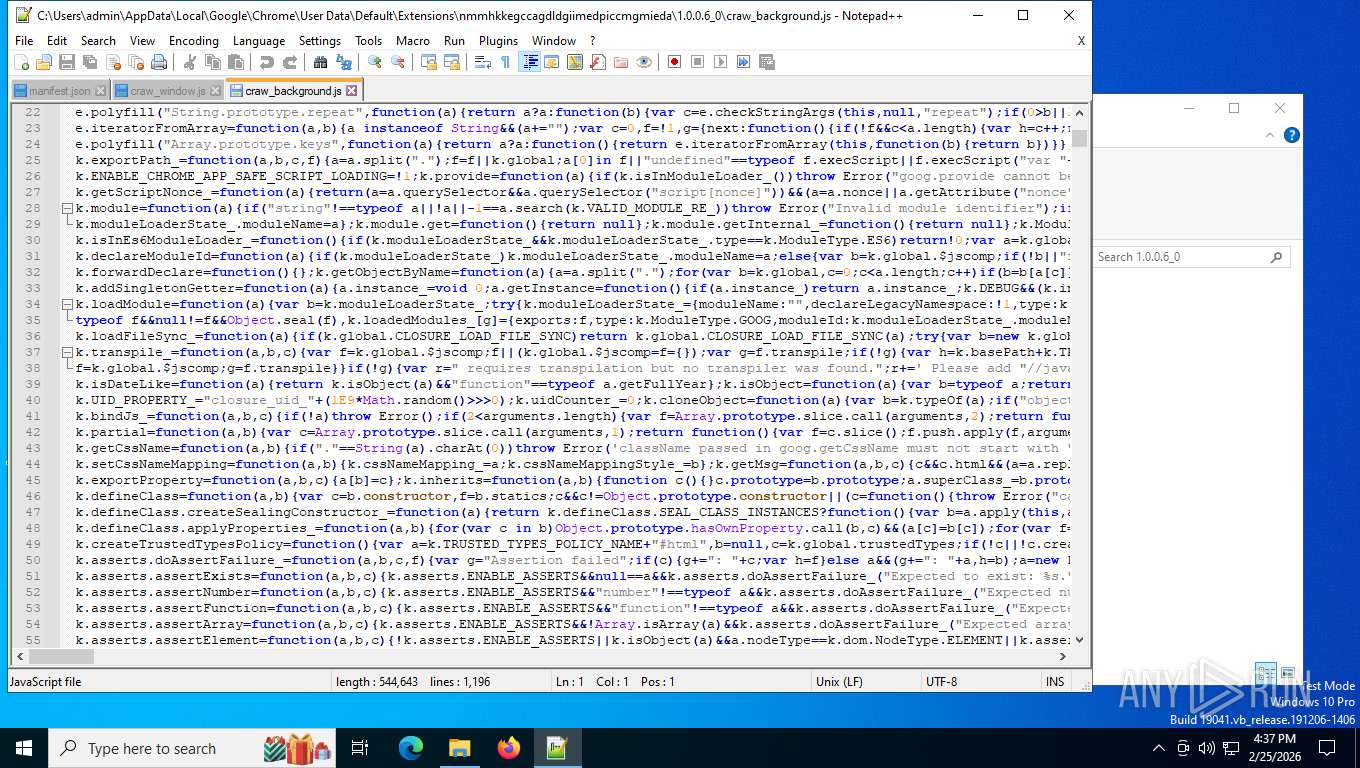
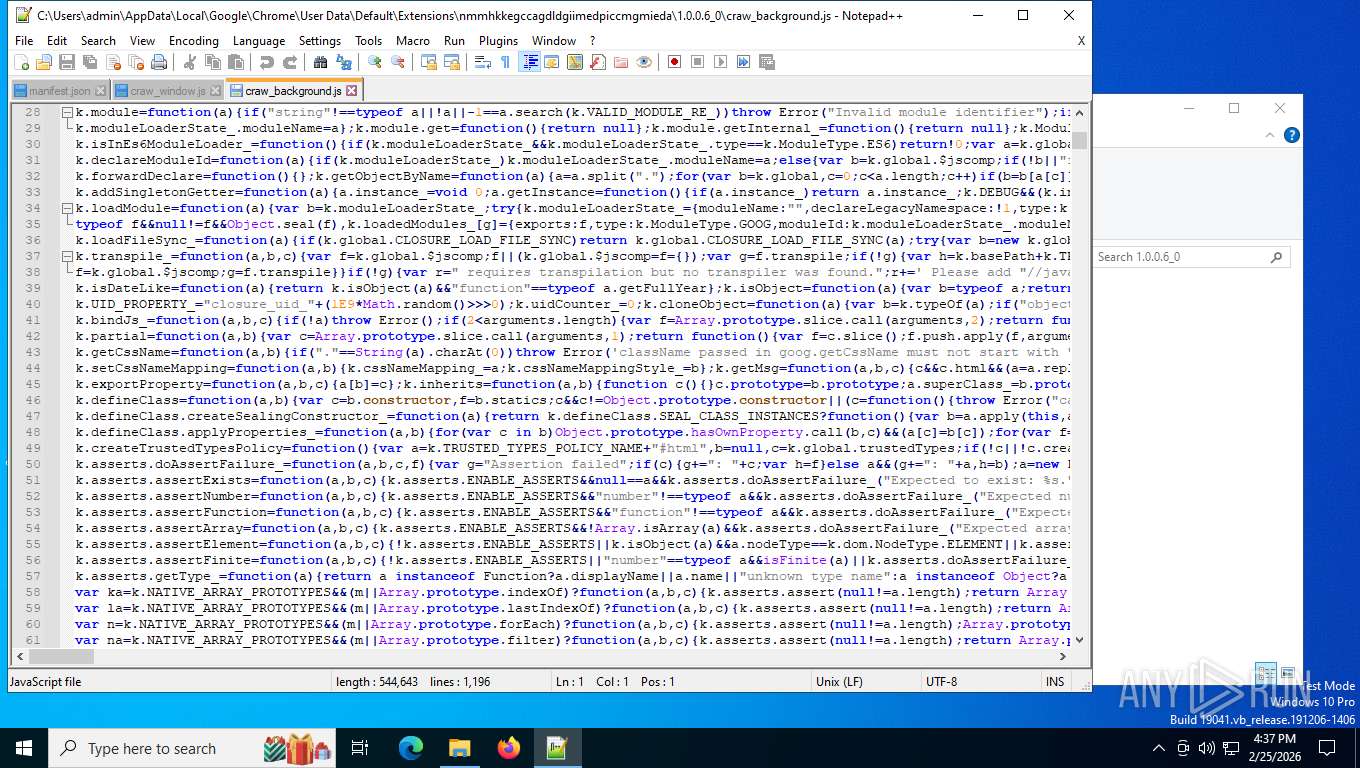
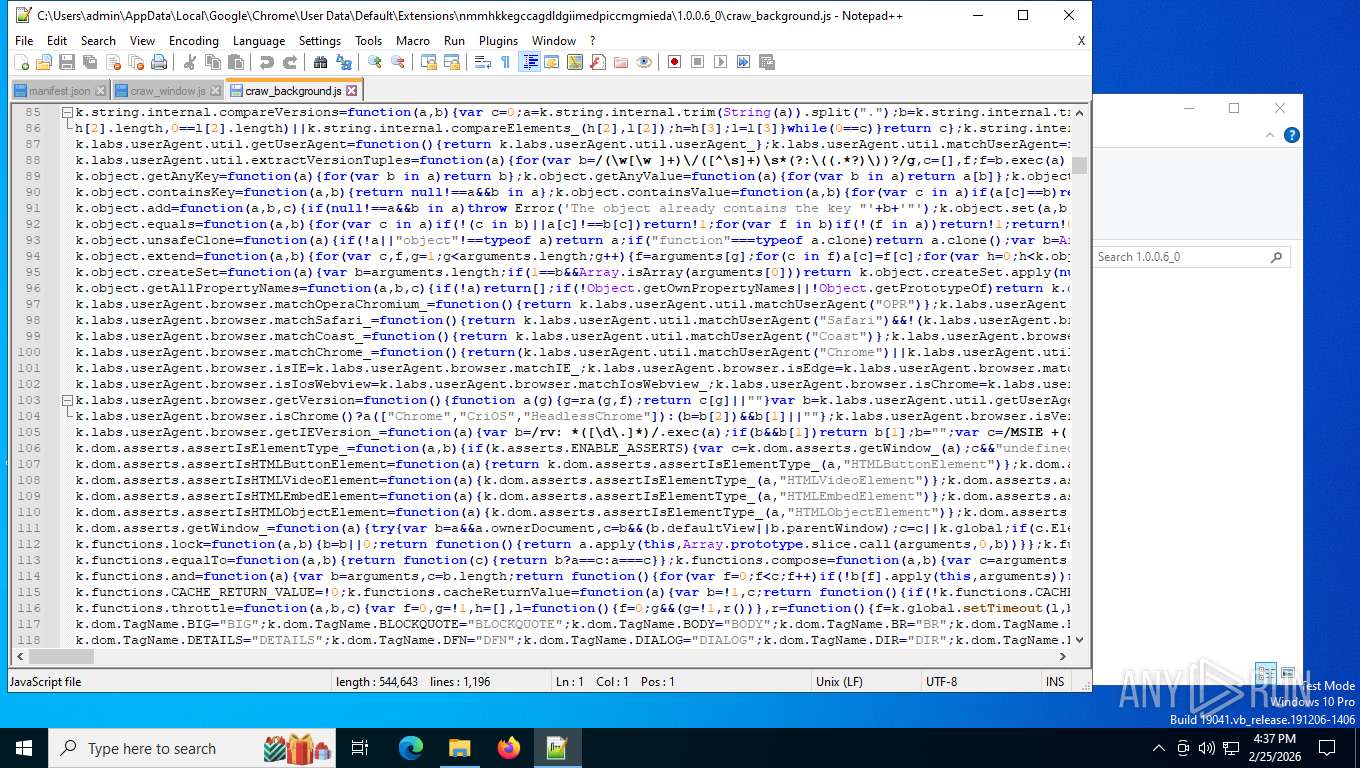
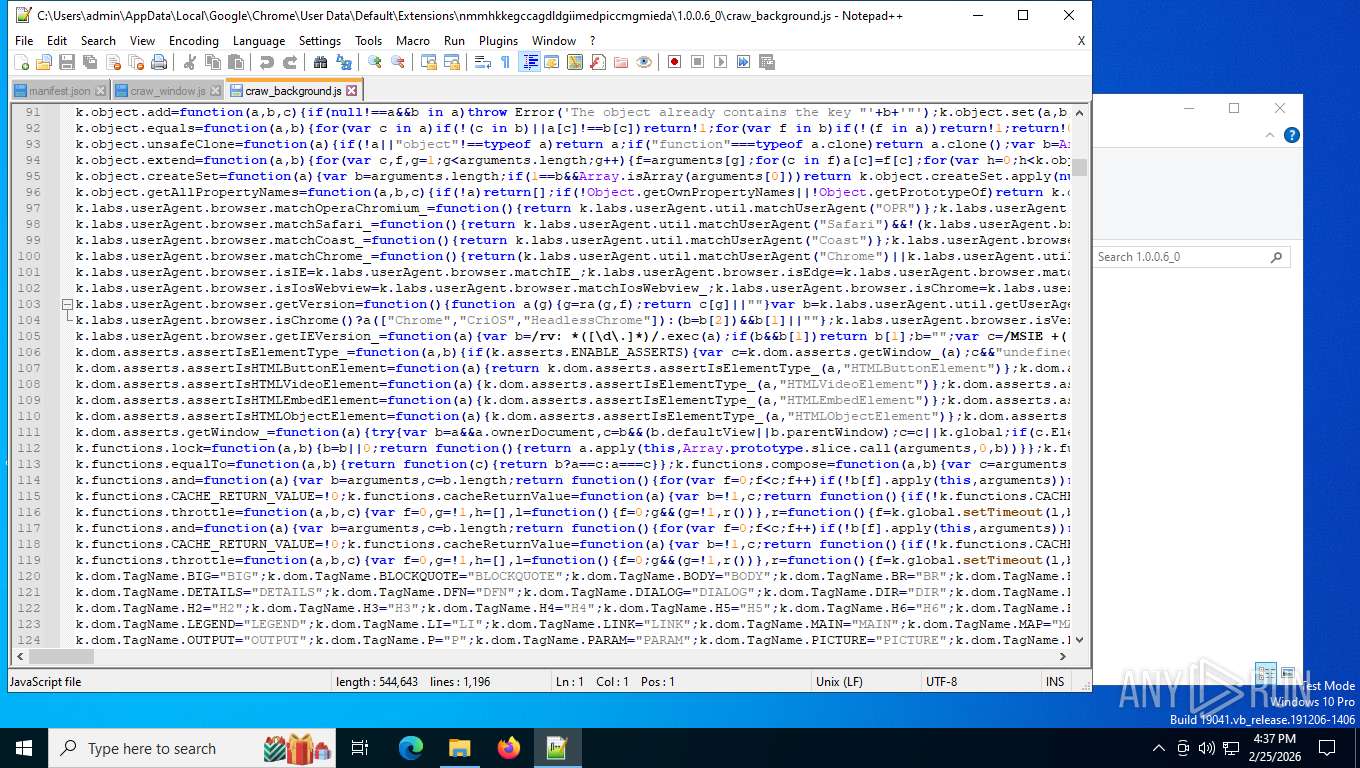
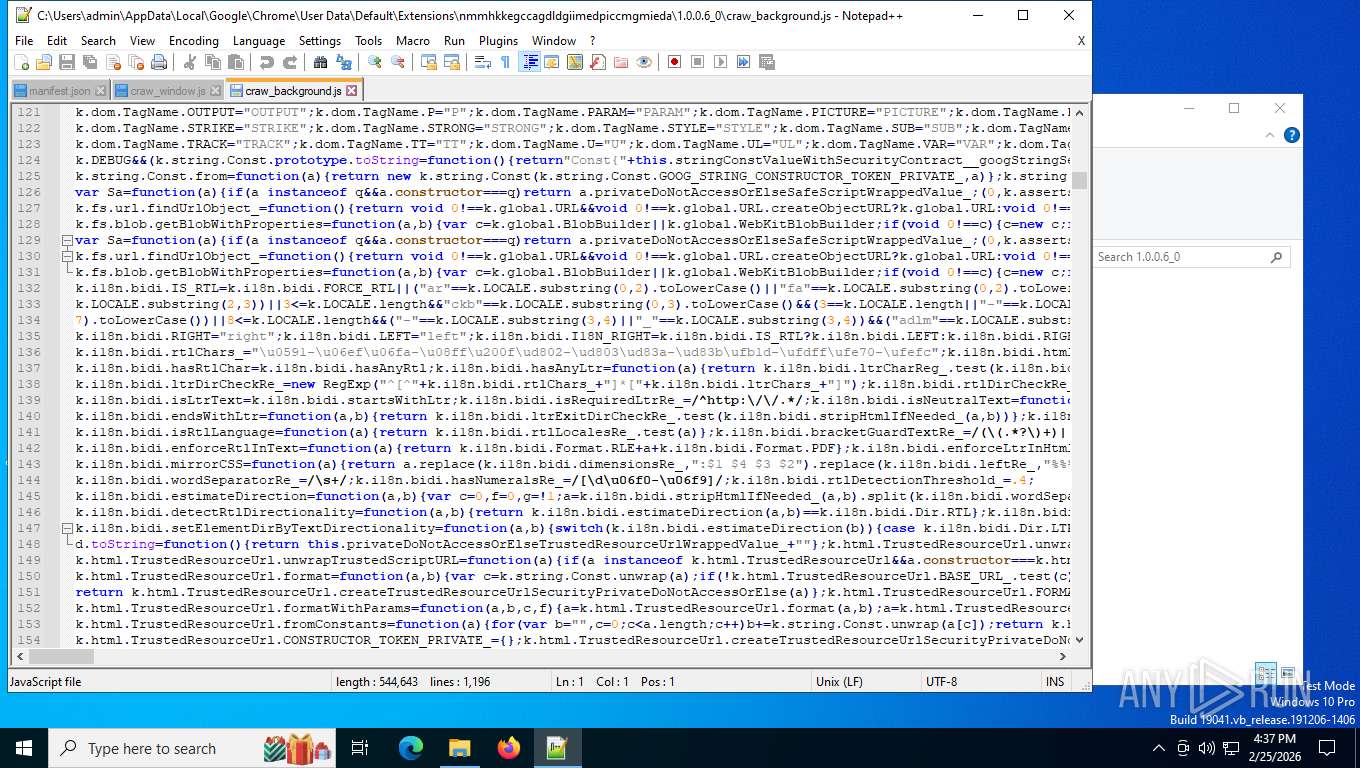
- chrome.exe (PID: 8568)
- chrome.exe (PID: 6232)
- platform_experience_helper.exe (PID: 6156)
- wscript.exe (PID: 6920)
- notepad++.exe (PID: 4060)
- notepad++.exe (PID: 7576)
Checks supported languages
- platform_experience_helper.exe (PID: 6156)
- platform_experience_helper.exe (PID: 5412)
Application launched itself
- chrome.exe (PID: 7408)
- chrome.exe (PID: 5184)
Process checks computer location settings
- platform_experience_helper.exe (PID: 6156)
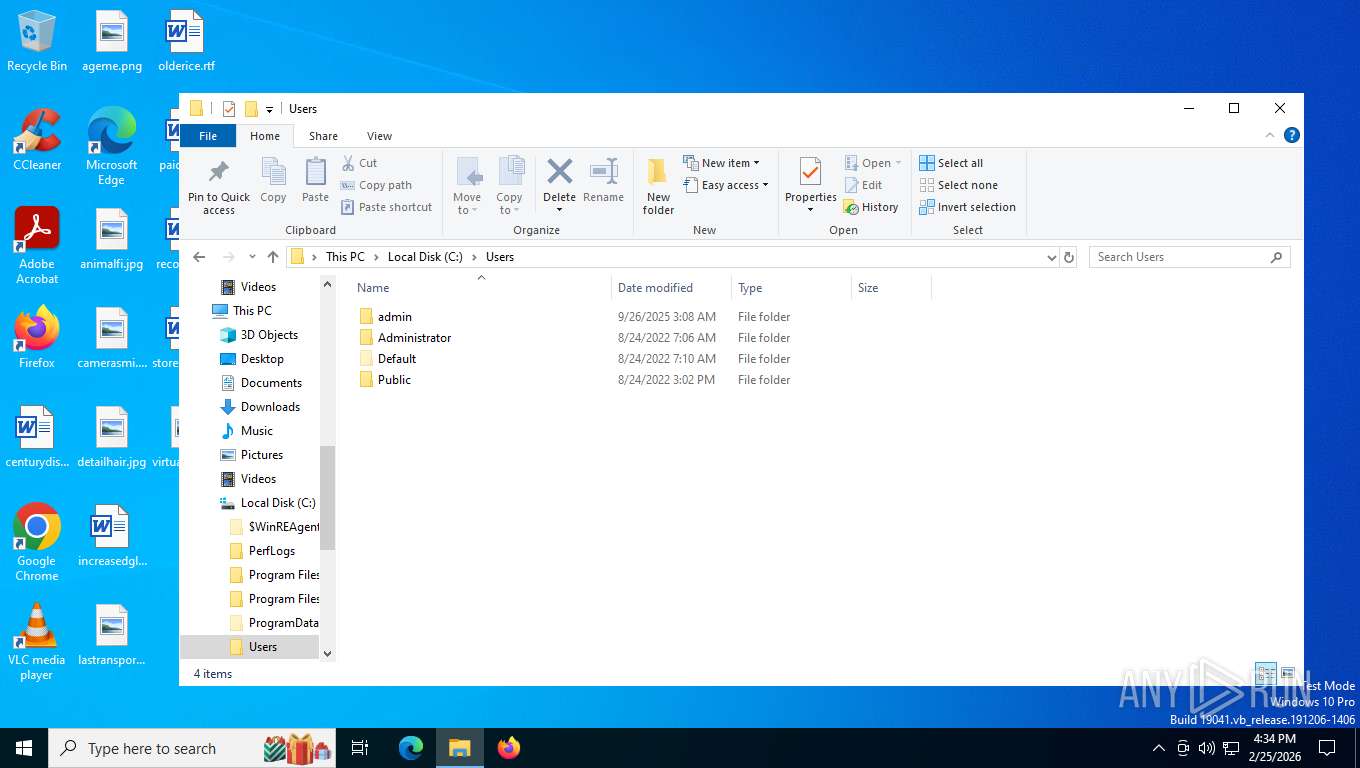
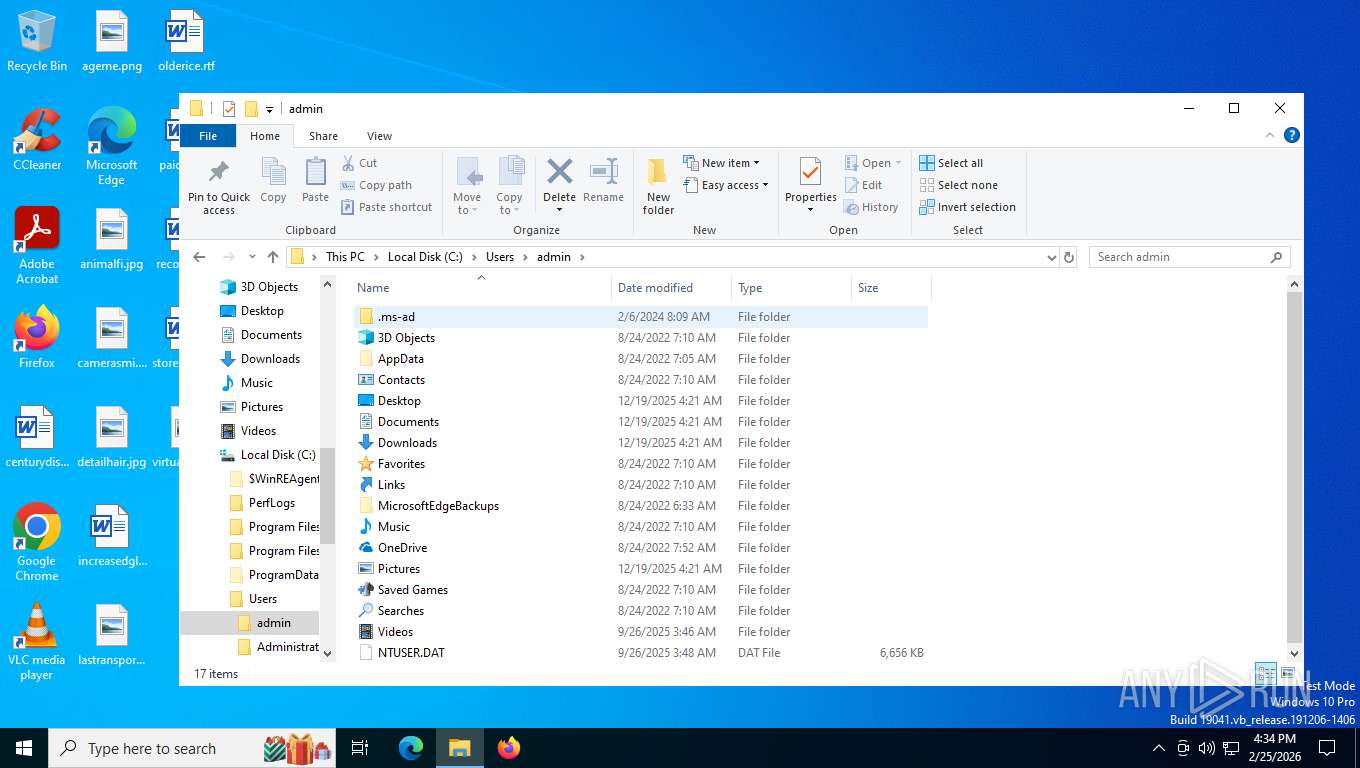
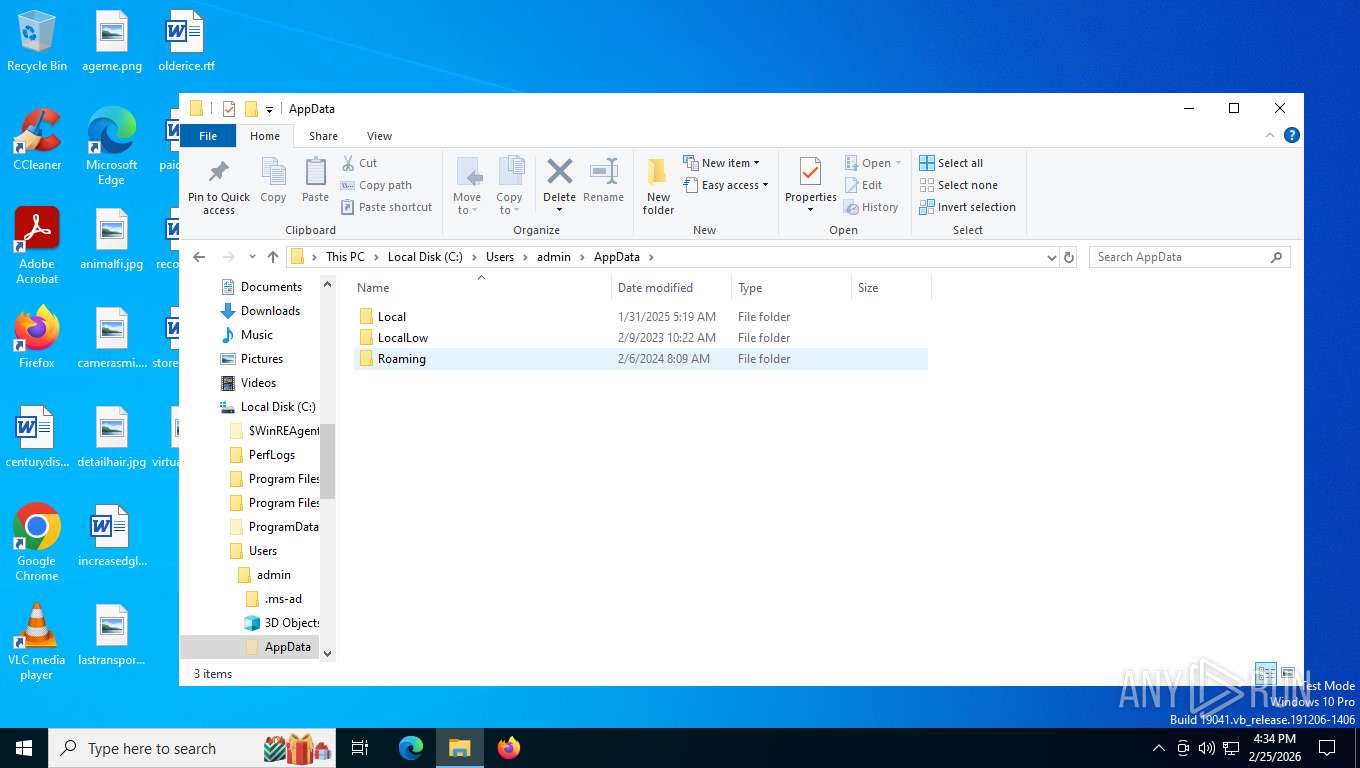
Creates files or folders in the user directory
- platform_experience_helper.exe (PID: 6156)
- platform_experience_helper.exe (PID: 5412)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4804)
Manual execution by a user
- notepad++.exe (PID: 7372)
- wscript.exe (PID: 6920)
- notepad++.exe (PID: 4060)
- notepad++.exe (PID: 7576)
Checks proxy server information
- slui.exe (PID: 1520)
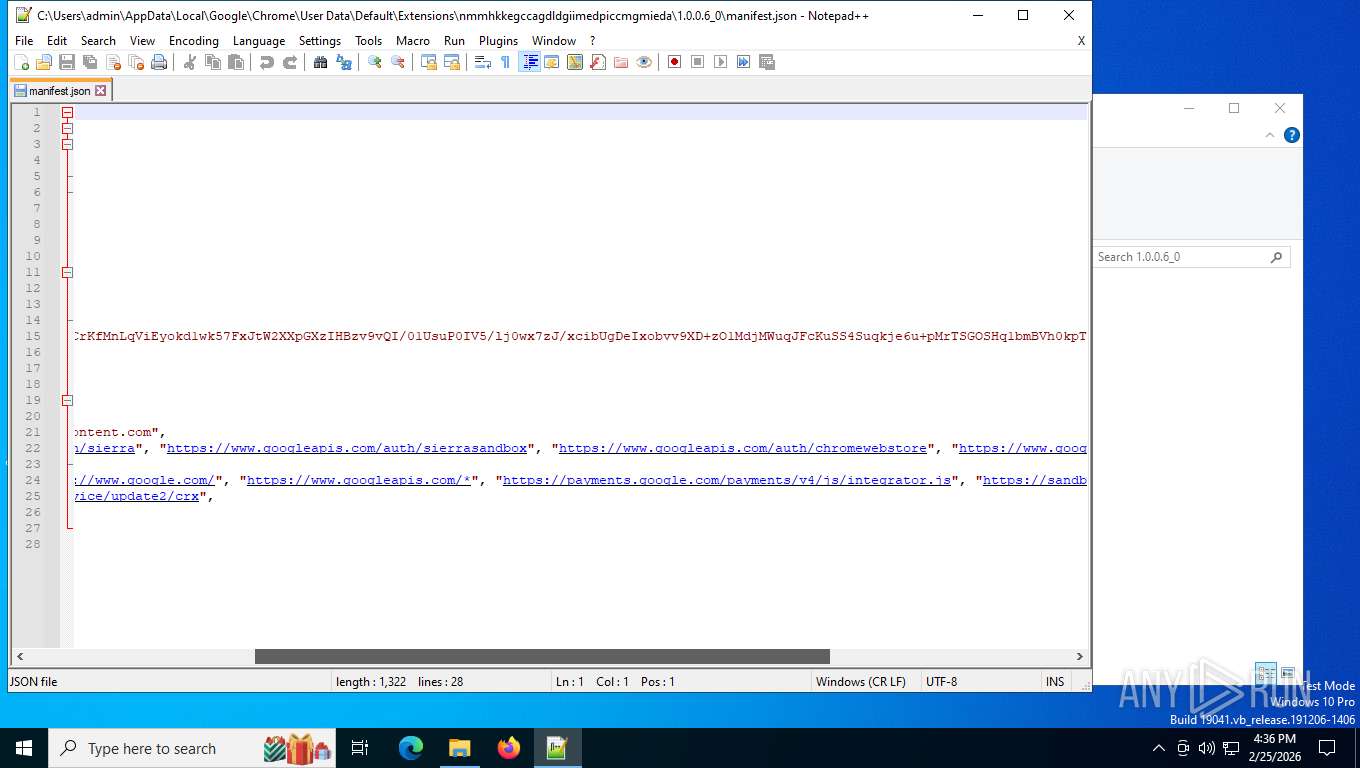
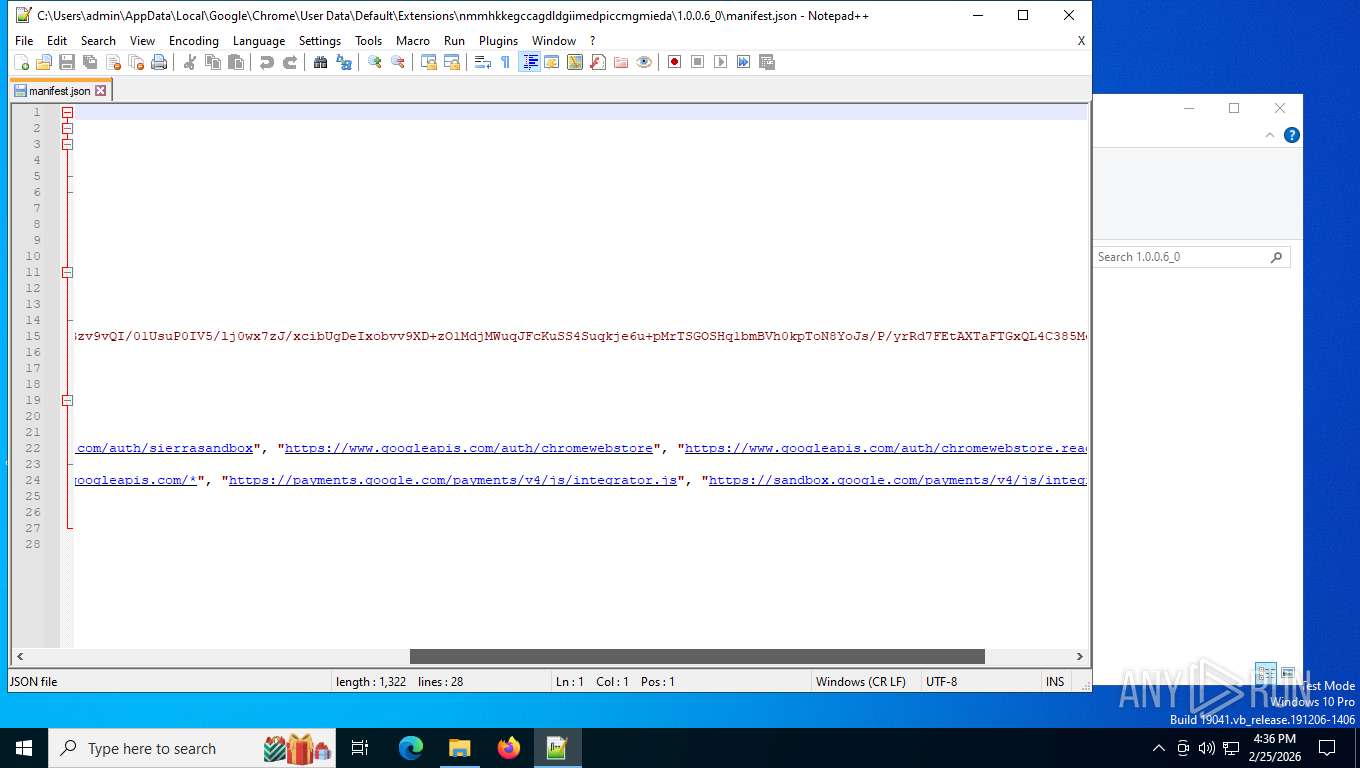
JScript runtime error (SCRIPT)
- wscript.exe (PID: 6920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2026:01:30 04:11:19+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 3288064 |
| InitializedDataSize: | 874496 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2eaed0 |
| OSVersion: | 10 |
| ImageVersion: | - |
| SubsystemVersion: | 10 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 146.0.7659.1 |
| ProductVersionNumber: | 146.0.7659.1 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Google LLC |
| FileDescription: | Google Chrome |
| FileVersion: | 146.0.7659.1 |
| InternalName: | platform_experience_helper |
| LegalCopyright: | Copyright 2026 Google LLC. All rights reserved. |
| OriginalFileName: | platform_experience_helper.exe |
| ProductName: | Google Chrome |
| ProductVersion: | 146.0.7659.1 |
| CompanyShortName: | |
| ProductShortName: | Chrome |
| LastChange: | f9ef68d4ad1d944673acc51a771e31f29f060f50-refs/branch-heads/7659@{#2} |
| OfficialBuild: | 1 |
Total processes
224
Monitored processes
71
Malicious processes
1
Suspicious processes
3
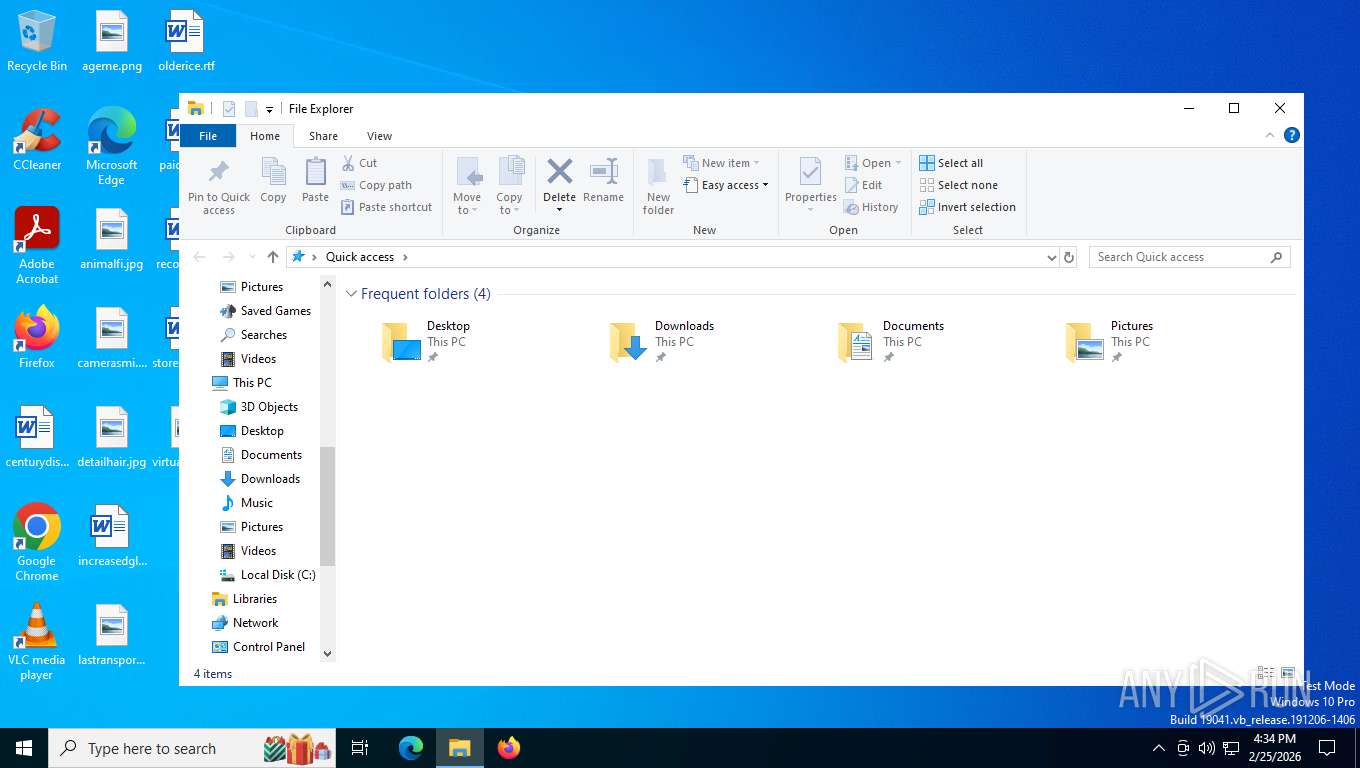
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037" --field-trial-handle=6548,i,5204158047146632346,13527973450765751597,262144 --enable-features=LoadLowEngagementPEHFeaturesToPrefs --disable-features=PaintHolding --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6784 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037" --field-trial-handle=5024,i,5204158047146632346,13527973450765751597,262144 --enable-features=LoadLowEngagementPEHFeaturesToPrefs --disable-features=PaintHolding --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6828 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037" --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --field-trial-handle=4032,i,5204158047146632346,13527973450765751597,262144 --enable-features=LoadLowEngagementPEHFeaturesToPrefs --disable-features=PaintHolding --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1520 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037" --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3220,i,5204158047146632346,13527973450765751597,262144 --enable-features=LoadLowEngagementPEHFeaturesToPrefs --disable-features=PaintHolding --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037" --field-trial-handle=5392,i,5204158047146632346,13527973450765751597,262144 --enable-features=LoadLowEngagementPEHFeaturesToPrefs --disable-features=PaintHolding --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5400 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037" --field-trial-handle=6280,i,5204158047146632346,13527973450765751597,262144 --enable-features=LoadLowEngagementPEHFeaturesToPrefs --disable-features=PaintHolding --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6736 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037" --field-trial-handle=4748,i,5204158047146632346,13527973450765751597,262144 --enable-features=LoadLowEngagementPEHFeaturesToPrefs --disable-features=PaintHolding --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3828 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037" --field-trial-handle=6388,i,5204158047146632346,13527973450765751597,262144 --enable-features=LoadLowEngagementPEHFeaturesToPrefs --disable-features=PaintHolding --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6528 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=146.0.7659.1 --initial-client-data=0x25c,0x260,0x264,0x238,0x268,0x7ff7cd1b0da8,0x7ff7cd1b0db4,0x7ff7cd1b0d78 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | platform_experience_helper.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
4 955
Read events
4 952
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6156) platform_experience_helper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{2c7ed102-d237-41b3-9a78-7ec8ca5a4692} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6156) platform_experience_helper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PlatformExperienceHelper |
| Operation: | write | Name: | DaysUntilNextNotification |
Value: 4 | |||
| (PID) Process: | (6920) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 050C210000000000 | |||
Executable files
0
Suspicious files
198
Text files
382
Unknown types
42
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5184 | chrome.exe | C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037\Crashpad\settings.dat | binary | |
MD5:98895F4B716AC8977CC4749744607746 | SHA256:E3B2593CE41B02F8814A6739952A277D859291E15488307C9F7F9C2355C9DA88 | |||
| 5184 | chrome.exe | C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037\Variations | text | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 5184 | chrome.exe | C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037\ShaderCache\data_1 | binary | |
MD5:259E7ED5FB3C6C90533B963DA5B2FC1B | SHA256:35BB2F189C643DCF52ECF037603D104035ECDC490BF059B7736E58EF7D821A09 | |||
| 5184 | chrome.exe | C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037\ShaderCache\index | binary | |
MD5:5916BD66017785C0DD72E01B4A0D46C4 | SHA256:3EC8C4BAA4F625734A8594DFE1D1A53E3472E32CB1E32730B82EC8C6CEE5CD2E | |||
| 5184 | chrome.exe | C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037\Default\History-journal | — | |
MD5:— | SHA256:— | |||
| 5184 | chrome.exe | C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037\ShaderCache\data_0 | binary | |
MD5:CF89D16BB9107C631DAABF0C0EE58EFB | SHA256:D6A5FE39CD672781B256E0E3102F7022635F1D4BB7CFCC90A80FFFE4D0F3877E | |||
| 5184 | chrome.exe | C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037\ShaderCache\data_2 | binary | |
MD5:0962291D6D367570BEE5454721C17E11 | SHA256:EC1702806F4CC7C42A82FC2B38E89835FDE7C64BB32060E0823C9077CA92EFB7 | |||
| 5184 | chrome.exe | C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037\ShaderCache\data_3 | binary | |
MD5:41876349CB12D6DB992F1309F22DF3F0 | SHA256:E09F42C398D688DCE168570291F1F92D079987DEDA3099A34ADB9E8C0522B30C | |||
| 5184 | chrome.exe | C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037\segmentation_platform\ukm_db-journal | binary | |
MD5:40537974E5D9642574C35DE69760878F | SHA256:C9CB3E820F0ABCCC62256D7BF72F4A6E921D9C0C31B688E79C9BCB8F0F207F38 | |||
| 5184 | chrome.exe | C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037\Default\README | text | |
MD5:883D62ACD72005F3AD7A14500D482033 | SHA256:C43668EEC4A8D88A5B3A06A84F8846853FE33E54293C2DB56899A5A5DFB4D944 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
75
TCP/UDP connections
74
DNS requests
73
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 313 b | whitelisted |
6796 | chrome.exe | OPTIONS | 200 | 216.58.206.42:443 | https://ogads-pa.clients6.google.com/$rpc/google.internal.onegoogle.asyncdata.v1.AsyncDataService/GetAsyncData | US | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
6796 | chrome.exe | GET | 200 | 142.251.143.110:80 | http://clients2.google.com/time/1/current?cup2key=8:mzyeee7c81k91K8ymlot_JYDPzz_a7VorGx_JE7gD-U&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
6796 | chrome.exe | OPTIONS | 200 | 142.251.127.100:443 | https://play.google.com/log?format=json&hasfast=true | US | — | — | whitelisted |
6796 | chrome.exe | GET | 302 | 172.217.168.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 627 b | whitelisted |
6796 | chrome.exe | GET | 200 | 216.58.206.42:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | binary | 41 b | whitelisted |
6796 | chrome.exe | GET | 200 | 142.251.141.67:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | US | binary | 87.7 Kb | whitelisted |
6796 | chrome.exe | GET | 200 | 142.251.143.110:443 | https://clients2.google.com/service/update2/crx?os=win&arch=x64&os_arch=x86_64&nacl_arch=x86-64&prod=chromecrx&prodchannel=&prodversion=133.0.6943.127&lang=en-US&acceptformat=crx3,puff&x=id%3Dghbmnnjooekpmoecnnnilnnbdlolhkhi%26v%3D0.0.0.0%26installedby%3Dinternal%26uc%26brand%3DGCEB%26ping%3Dr%253D-1%2526e%253D1&x=id%3Dnmmhkkegccagdldgiimedpiccmgmieda%26v%3D0.0.0.0%26installedby%3Dother%26uc%26brand%3DGCEB%26ping%3Dr%253D-1%2526e%253D1 | US | xml | 1.31 Kb | whitelisted |
6796 | chrome.exe | GET | 200 | 142.250.201.164:443 | https://www.google.com/async/ddljson?async=ntp:2 | US | text | 19 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
9080 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7428 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.222:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5568 | SearchApp.exe | 2.16.241.205:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
9080 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037 directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\scoped_dir6156_1414977037 directory exists )
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|