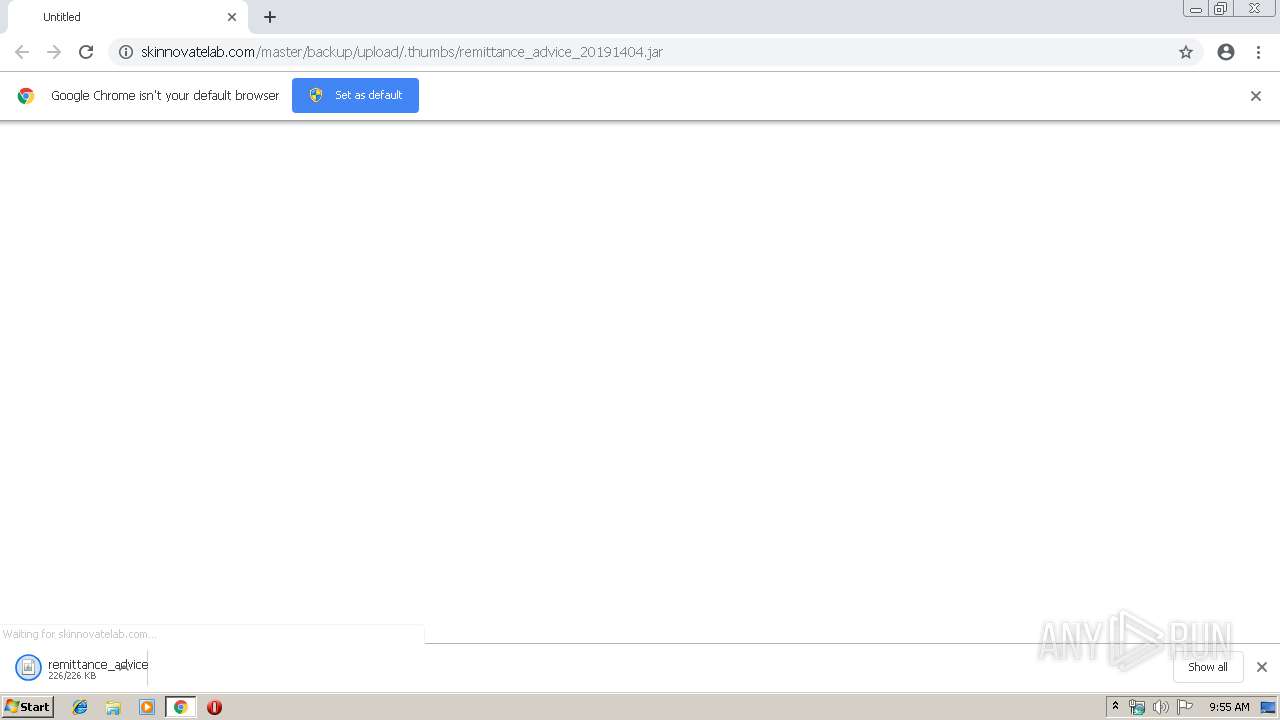
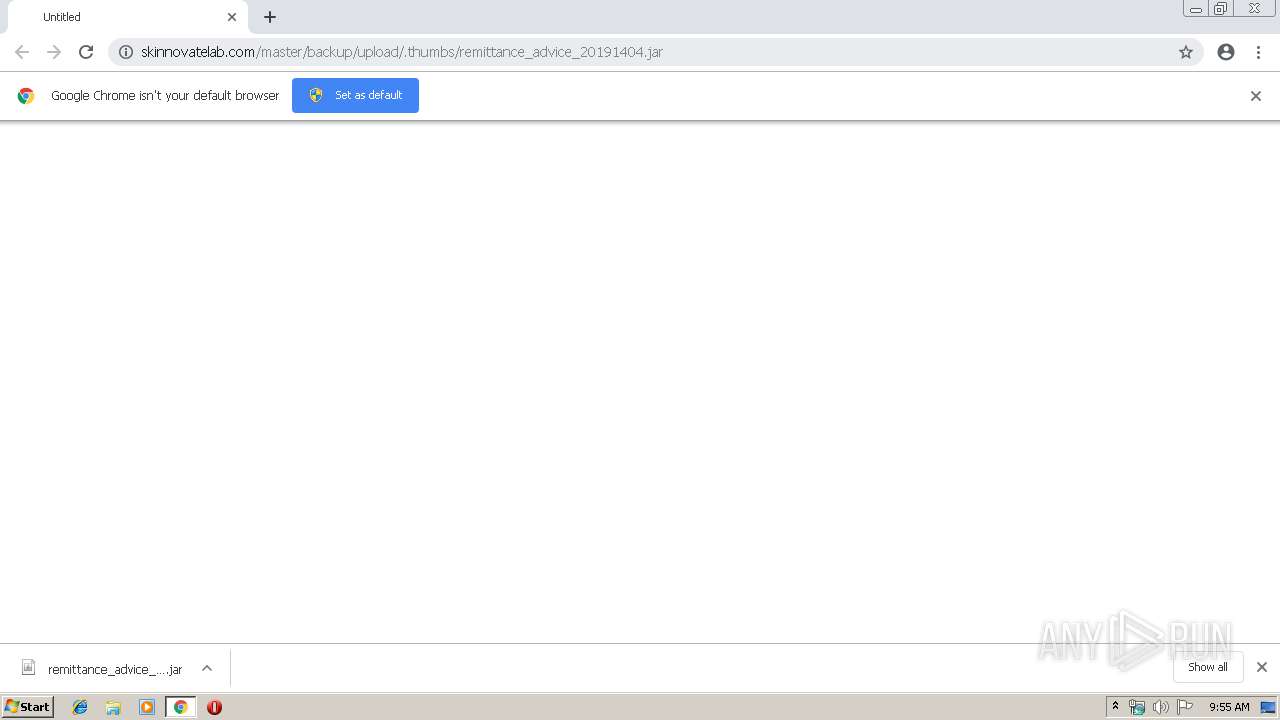
| URL: | http://skinnovatelab.com/master/backup/upload/.thumbs/remittance_advice_20191404.jar |
| Full analysis: | https://app.any.run/tasks/d94b5413-4749-41d9-9f5c-60b77661a001 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 08:55:20 |
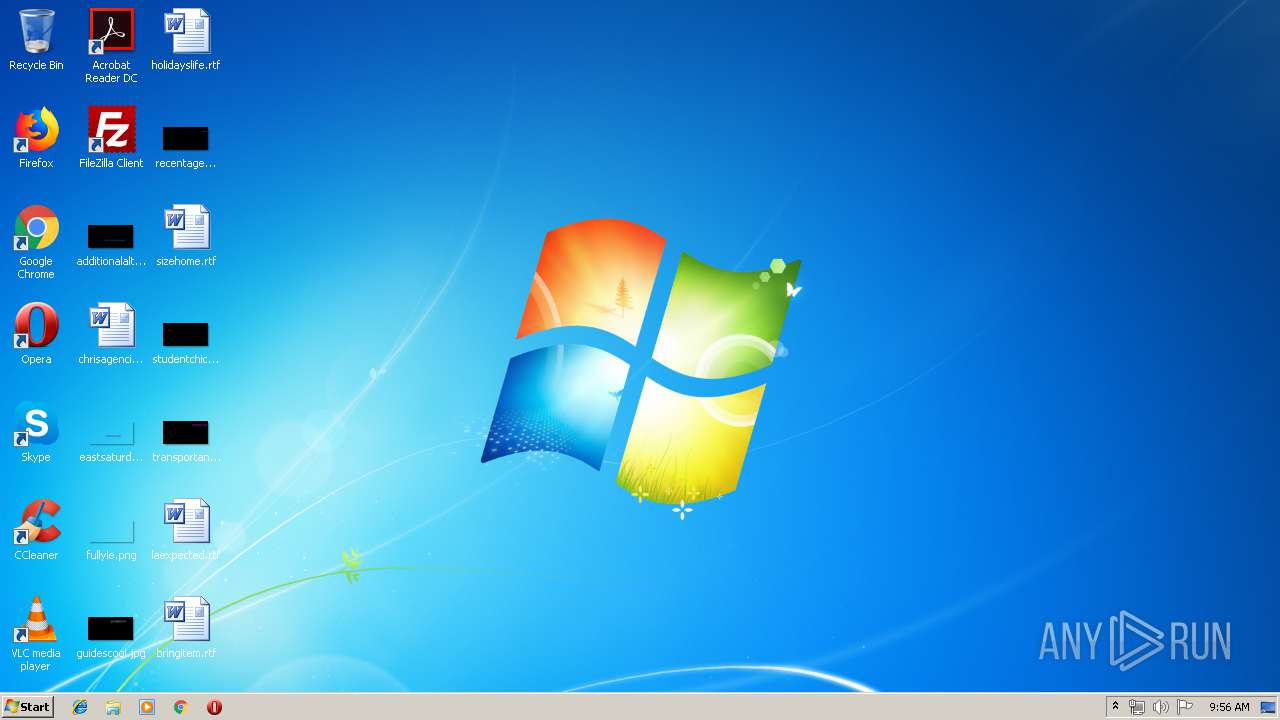
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F4AC02483369C805061106CFCA5BE1D4 |
| SHA1: | 822FC0230B174AA1E5633BA172A22D06F7961959 |
| SHA256: | 1F3CA70419AB289DCC9EACFDFB72B1EAF2F947E9F11A9110B13011AEE5E4D3FD |
| SSDEEP: | 3:N1KNOfTNKHZ3IXEmjKEaRzFuRELX6CXn:CcfhKHtIXECazkRETvXn |
MALICIOUS
Application was dropped or rewritten from another process
- 7z_12430026021176677189099378900047.exe (PID: 2292)
- python.exe (PID: 1772)
Loads dropped or rewritten executable
- python.exe (PID: 1772)
SUSPICIOUS
Executes JAVA applets
- chrome.exe (PID: 2820)
Executable content was dropped or overwritten
- javaw.exe (PID: 2496)
- 7z_12430026021176677189099378900047.exe (PID: 2292)
Creates files in the user directory
- javaw.exe (PID: 2496)
Loads Python modules
- python.exe (PID: 1772)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2820)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3940)
Dropped object may contain Bitcoin addresses
- 7z_12430026021176677189099378900047.exe (PID: 2292)
Application launched itself
- chrome.exe (PID: 2820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
18
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6720039834152031947 --mojo-platform-channel-handle=3600 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --service-pipe-token=15988800002122817165 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15988800002122817165 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1772 | C:\Users\admin\AppData\Local\Temp\qealler\python\python.exe C:\Users\admin\AppData\Local\Temp\qealler\qazaqne\main.py all | C:\Users\admin\AppData\Local\Temp\qealler\python\python.exe | — | javaw.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2292 | C:\Users\admin\AppData\Local\Temp\7z_12430026021176677189099378900047.exe x C:\Users\admin\AppData\Local\Temp\_12430026018336578936149433897642.tmp -oC:\Users\admin\AppData\Local\Temp -p"bbb6fec5ebef0d936db0b031b7ab19b6" -mmt -aoa -y | C:\Users\admin\AppData\Local\Temp\7z_12430026021176677189099378900047.exe | javaw.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 17.00 beta Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8231840146062366530 --mojo-platform-channel-handle=2684 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --service-pipe-token=14350677977991495945 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14350677977991495945 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,17215634630916836933,4176483723390307175,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6193387253512047670 --mojo-platform-channel-handle=3780 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\remittance_advice_20191404.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | chrome.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2824 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://skinnovatelab.com/master/backup/upload/.thumbs/remittance_advice_20191404.jar | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
524
Read events
446
Write events
74
Delete events
4
Modification events
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2820-13199792136096000 |
Value: 259 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
34
Suspicious files
36
Text files
152
Unknown types
375
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF12f9f8.TMP | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\31a47a3e-53a4-4a33-984a-68a8faa9c7f1.tmp | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
22
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
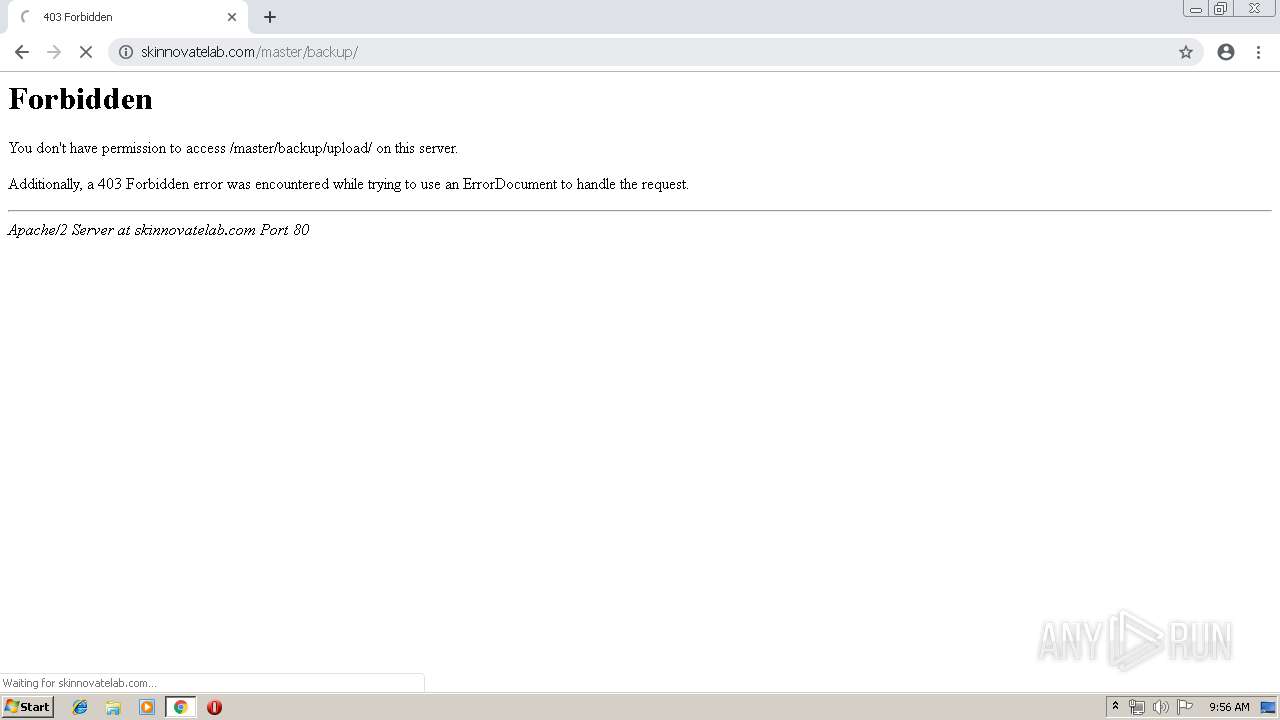
3940 | chrome.exe | GET | — | 27.254.66.193:80 | http://skinnovatelab.com/master/backup/upload/ | TH | — | — | unknown |
3940 | chrome.exe | GET | — | 27.254.66.193:80 | http://skinnovatelab.com/favicon.ico | TH | — | — | unknown |
2496 | javaw.exe | GET | 200 | 188.166.150.227:8104 | http://188.166.150.227:8104/lib/7z | GB | java | 576 Kb | suspicious |
3940 | chrome.exe | GET | 200 | 27.254.66.193:80 | http://skinnovatelab.com/master/backup/upload/.thumbs/remittance_advice_20191404.jar | TH | java | 201 Kb | unknown |
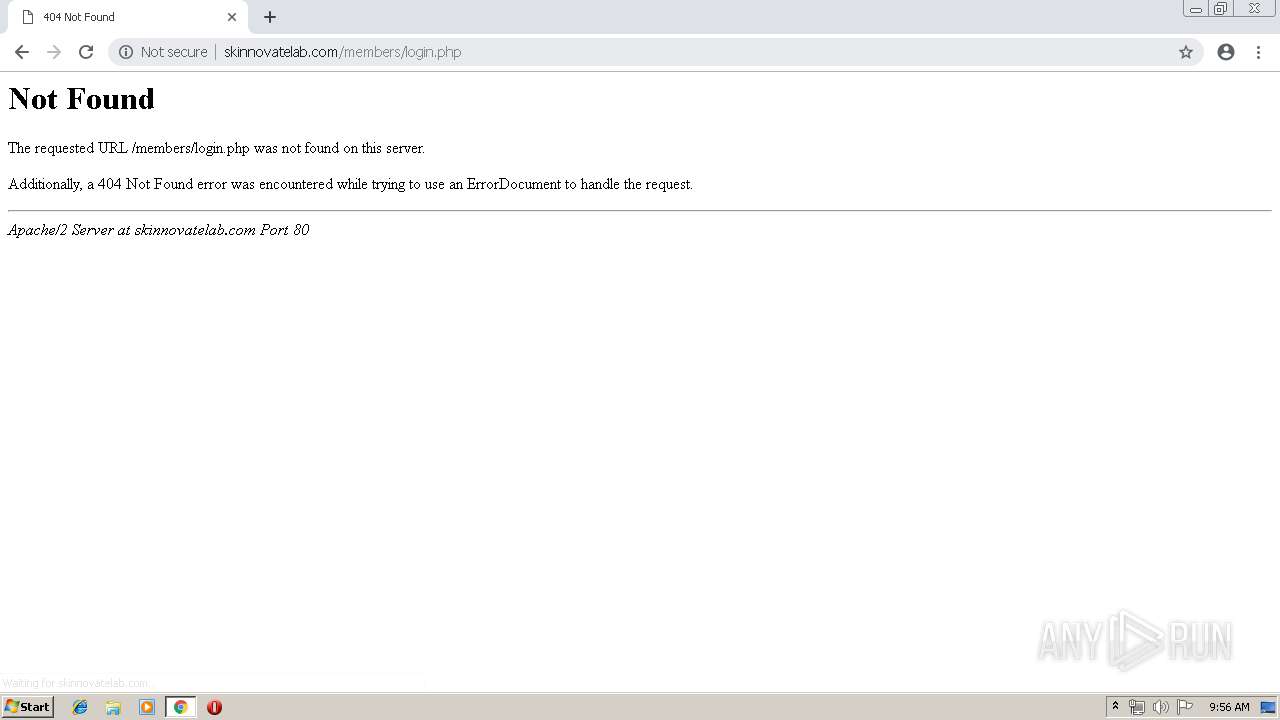
3940 | chrome.exe | GET | 404 | 27.254.66.193:80 | http://skinnovatelab.com/members/login.php | TH | html | 403 b | unknown |
2496 | javaw.exe | POST | 200 | 188.166.150.227:8084 | http://188.166.150.227:8084/qealler-reloaded/ping | GB | text | 108 b | suspicious |
3940 | chrome.exe | GET | 200 | 194.9.24.113:80 | http://r6---sn-5uh5o-f5fd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.217.54&mm=28&mn=sn-5uh5o-f5fd&ms=nvh&mt=1555318054&mv=u&pl=21&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
3940 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 507 b | whitelisted |
3940 | chrome.exe | GET | 301 | 27.254.66.193:80 | http://skinnovatelab.com/master/backup/upload | TH | html | 323 b | unknown |
2496 | javaw.exe | GET | 200 | 188.166.150.227:8929 | http://188.166.150.227:8929/lib/qealler | GB | compressed | 1.84 Mb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3940 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3940 | chrome.exe | 27.254.66.193:80 | skinnovatelab.com | CS LOXINFO Public Company Limited. | TH | unknown |
3940 | chrome.exe | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3940 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2496 | javaw.exe | 188.166.150.227:8104 | — | Digital Ocean, Inc. | GB | suspicious |
2496 | javaw.exe | 188.166.150.227:8929 | — | Digital Ocean, Inc. | GB | suspicious |
3940 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
3940 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3940 | chrome.exe | 194.9.24.113:80 | r6---sn-5uh5o-f5fd.gvt1.com | ATM S.A. | PL | whitelisted |
2496 | javaw.exe | 188.166.150.227:8084 | — | Digital Ocean, Inc. | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
skinnovatelab.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r6---sn-5uh5o-f5fd.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2496 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
2496 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Qealler.Java.Rat HTTP header |