| File name: | Net-Worm.zip |
| Full analysis: | https://app.any.run/tasks/bae25f78-3b9a-4a77-9afa-679d93881f60 |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2024, 13:18:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
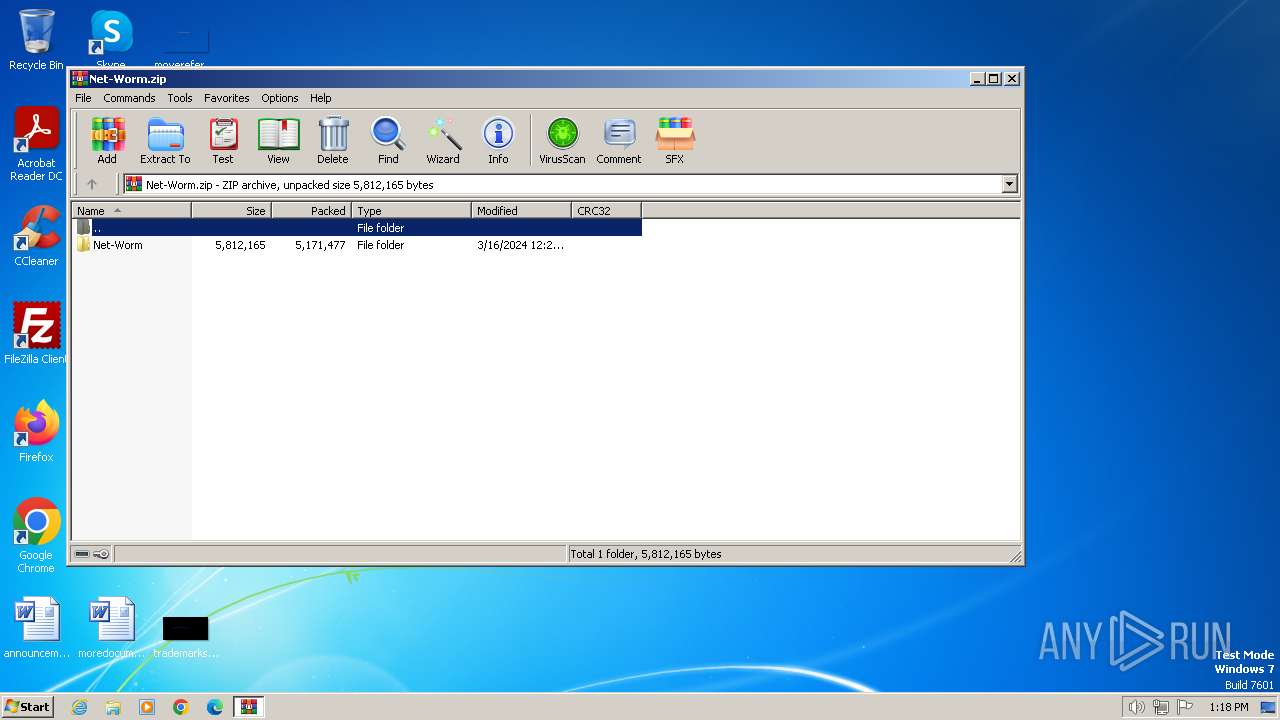
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 346FFDD056F329E084C09E3FA5A5D3D9 |
| SHA1: | 6225A8B13D67BC8617B0C48BC9EB4B050875C982 |
| SHA256: | 1F39E3EBF80E66923D7AE2A49C2CDF9DF50FEC5D187CB253C4485E83BD1AD170 |
| SSDEEP: | 98304:x1Fmmecd/fuc8nJUxB3wyEuo0vZ9RNkxFg3m8IUbfkhR98mw9csB69sxLGR9O973:dwPy8dfIn |
MALICIOUS
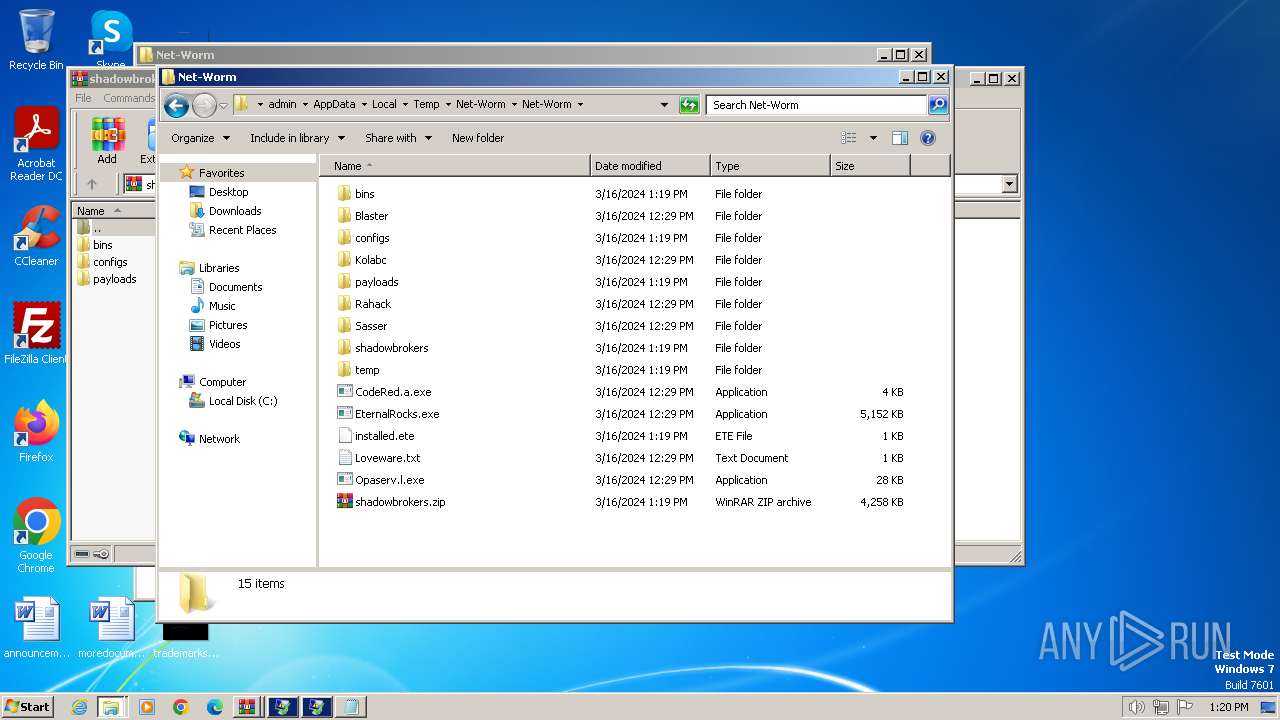
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3992)
- EternalRocks.exe (PID: 848)
Starts NET.EXE for service management
- net.exe (PID: 2152)
- Opaserv.l.exe (PID: 1740)
- net.exe (PID: 2072)
- net.exe (PID: 748)
- net.exe (PID: 1560)
- net.exe (PID: 2184)
Changes the autorun value in the registry
- Opaserv.l.exe (PID: 1740)
SUSPICIOUS
Creates file in the systems drive root
- ntvdm.exe (PID: 1348)
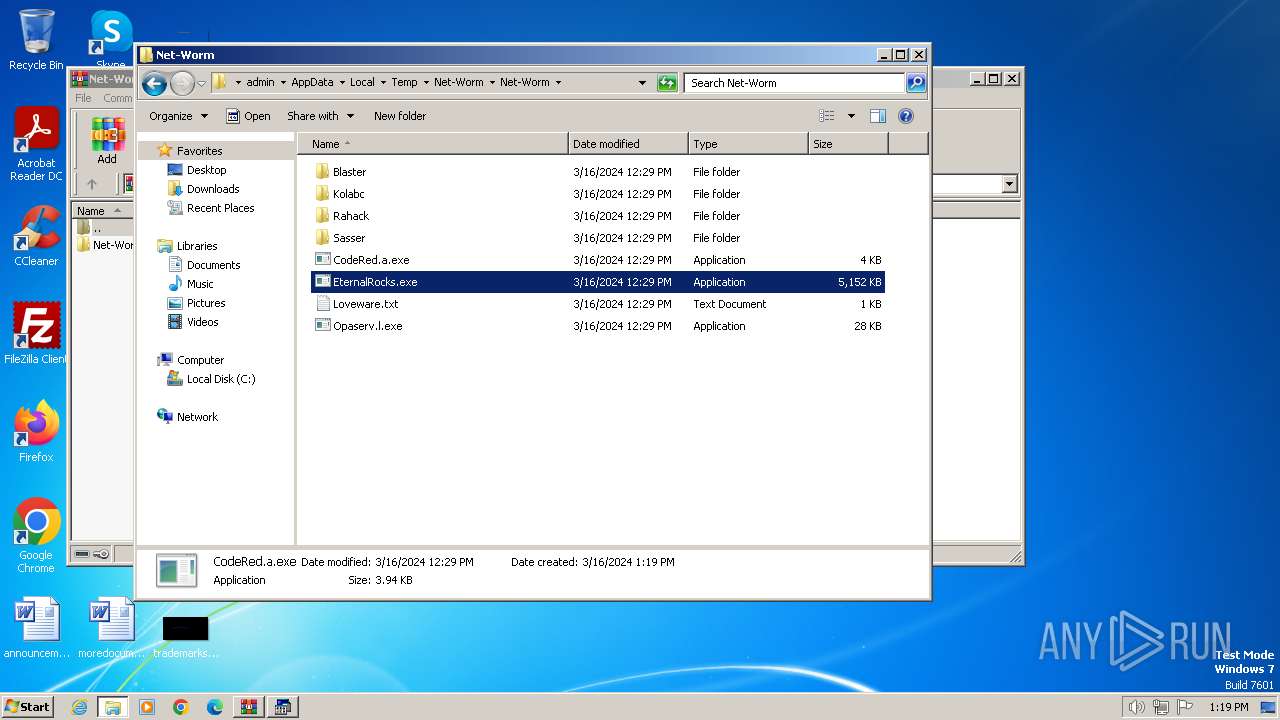
Executable content was dropped or overwritten
- EternalRocks.exe (PID: 848)
The process creates files with name similar to system file names
- EternalRocks.exe (PID: 848)
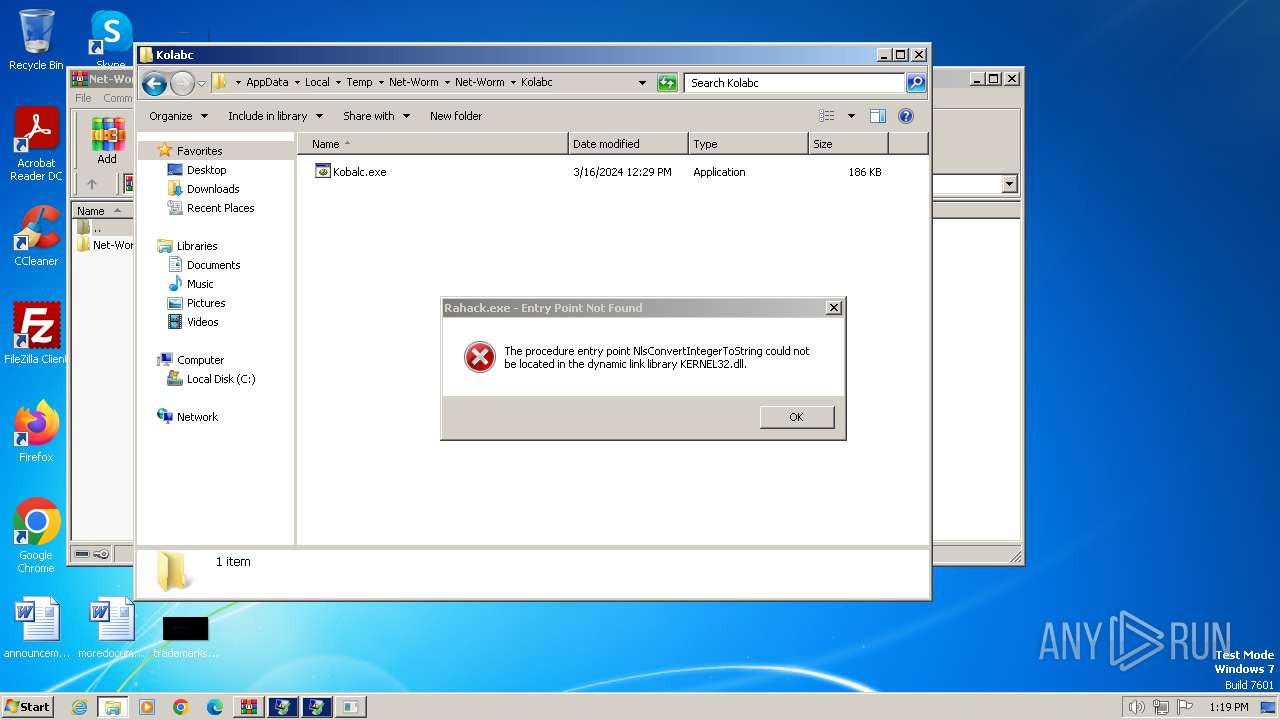
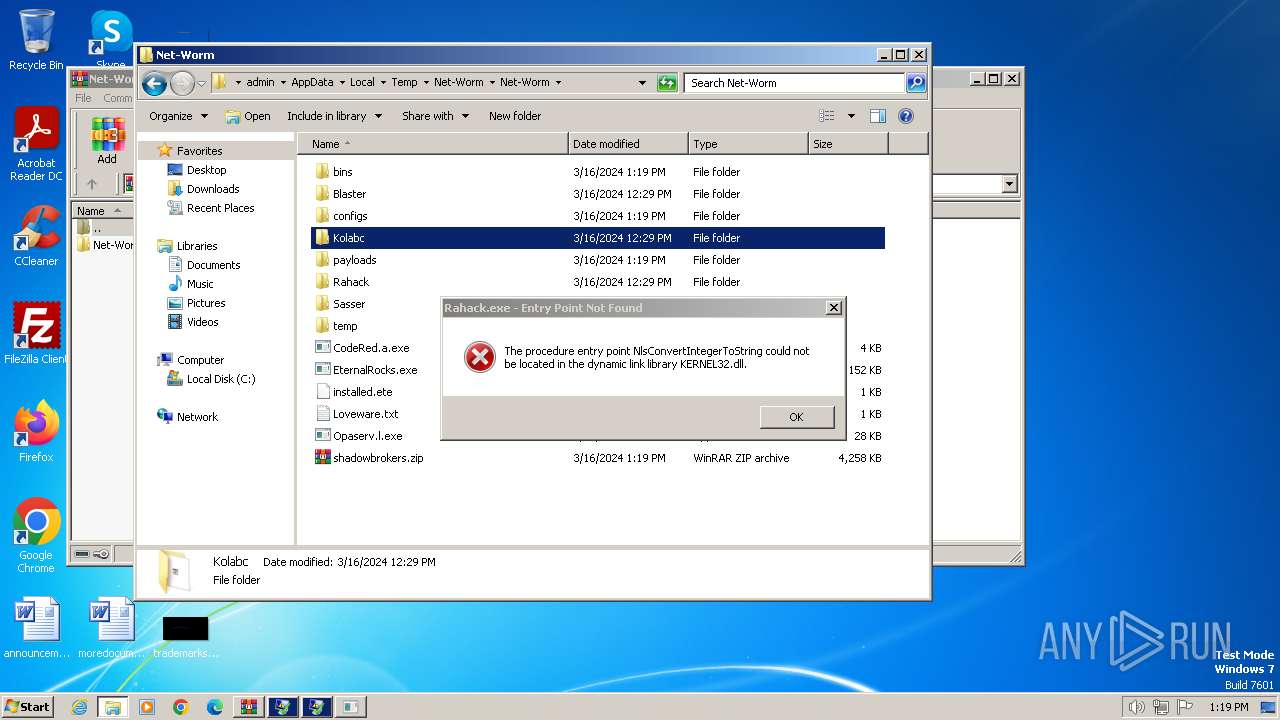
Uses NETSH.EXE to change the status of the firewall
- Kobalc.exe (PID: 3236)
Uses NETSH.EXE to add a firewall rule or allowed programs
- Kobalc.exe (PID: 3236)
INFO
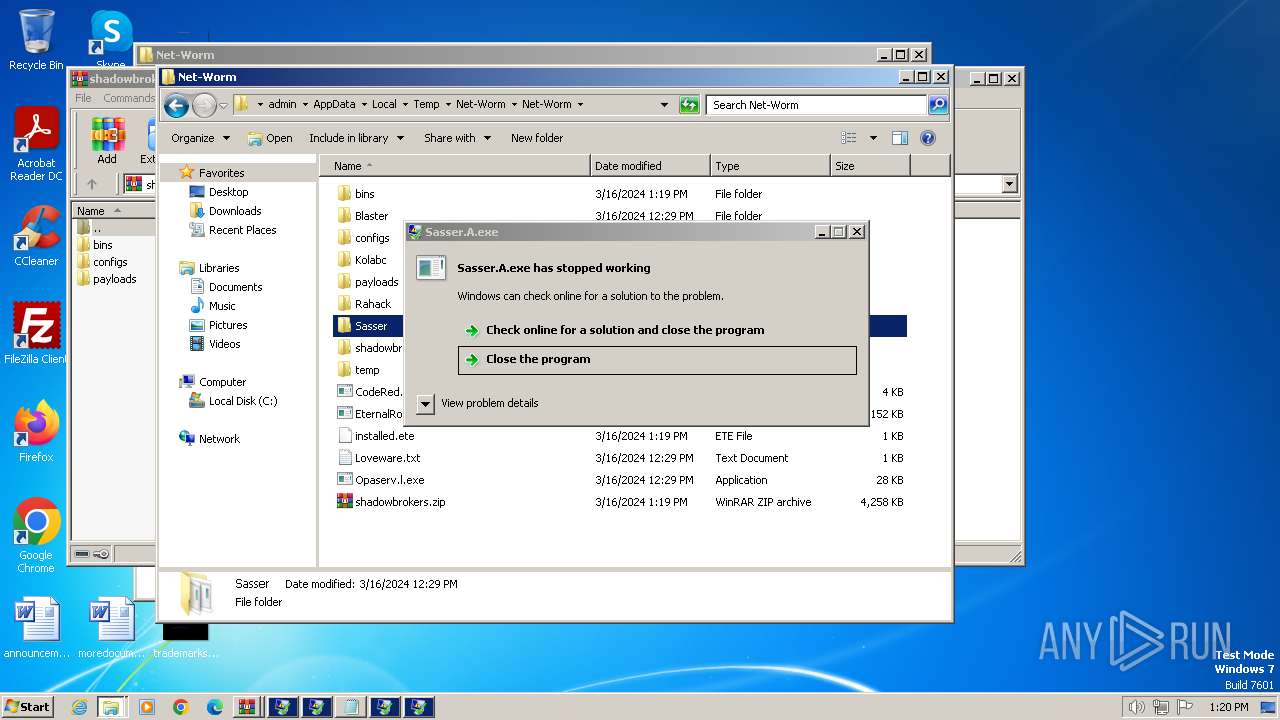
Manual execution by a user
- Opaserv.l.exe (PID: 1740)
- ntvdm.exe (PID: 1348)
- EternalRocks.exe (PID: 848)
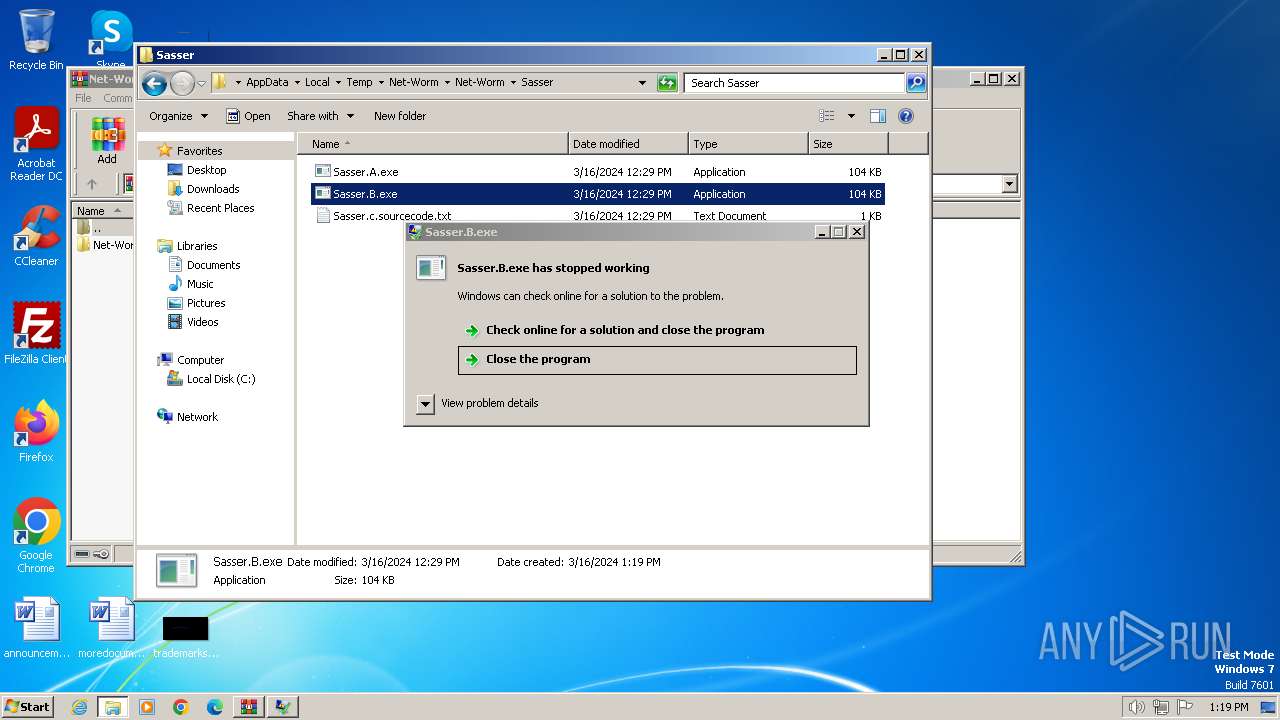
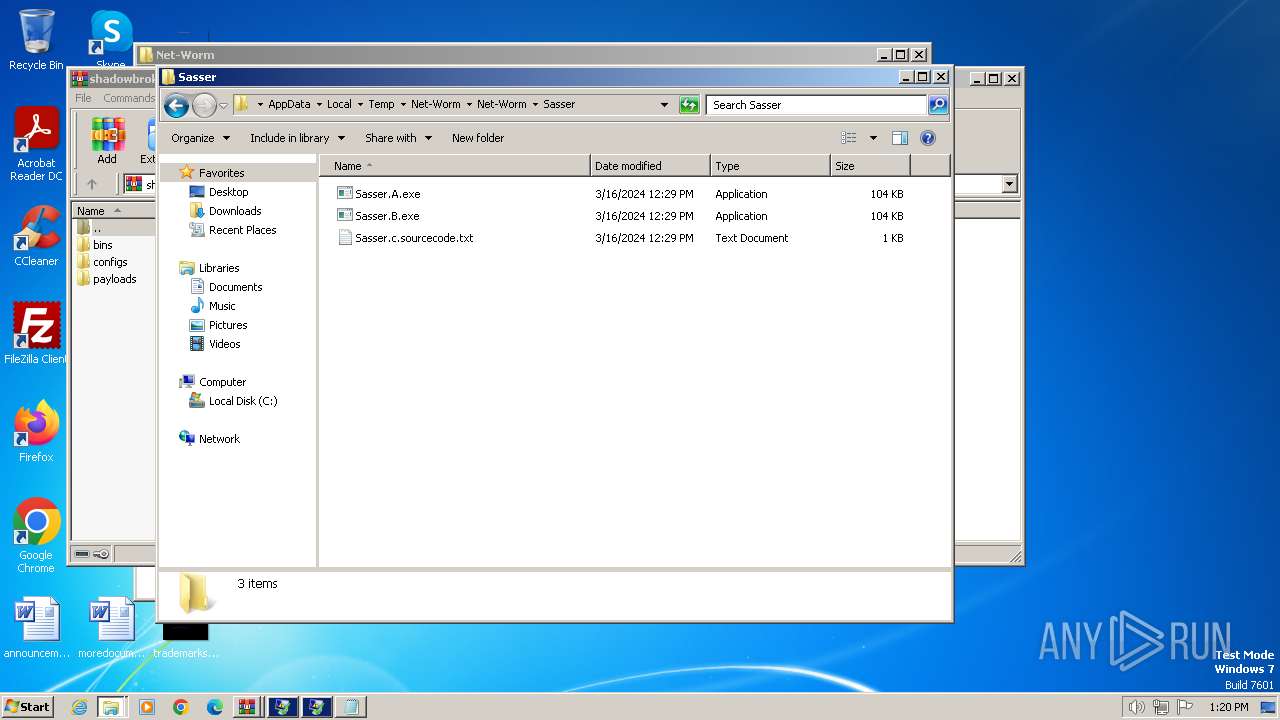
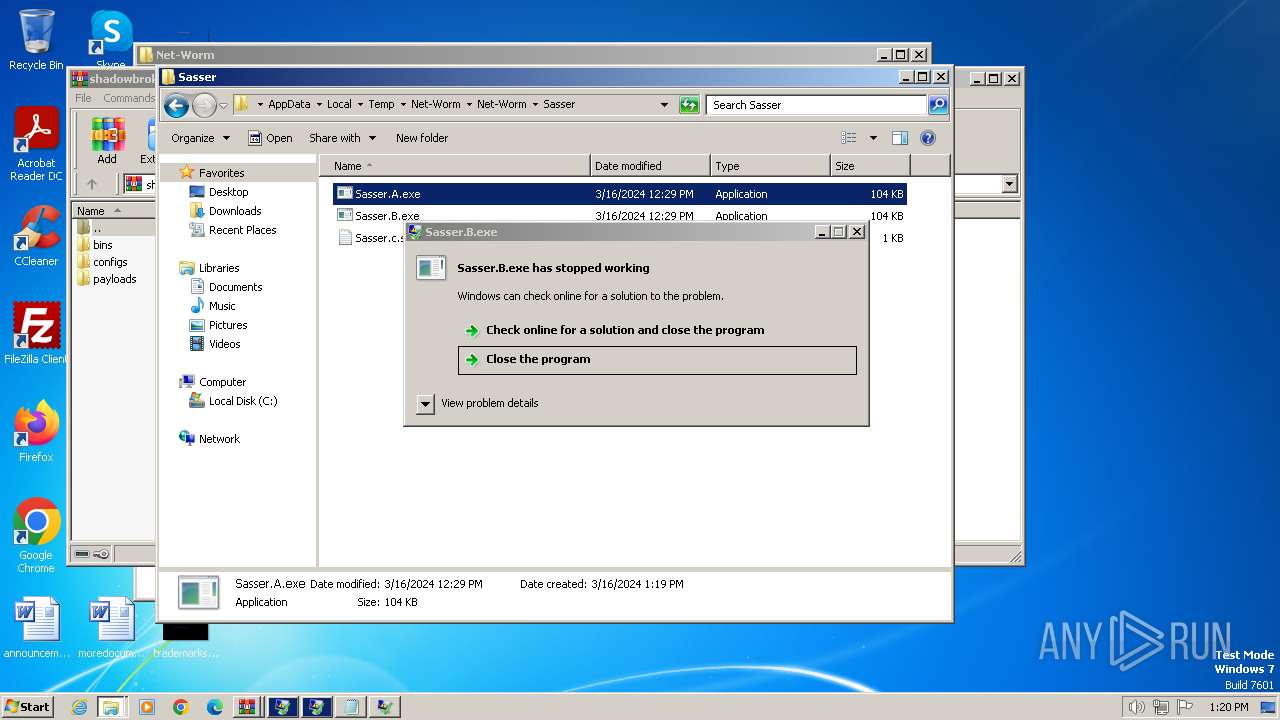
- Sasser.B.exe (PID: 3496)
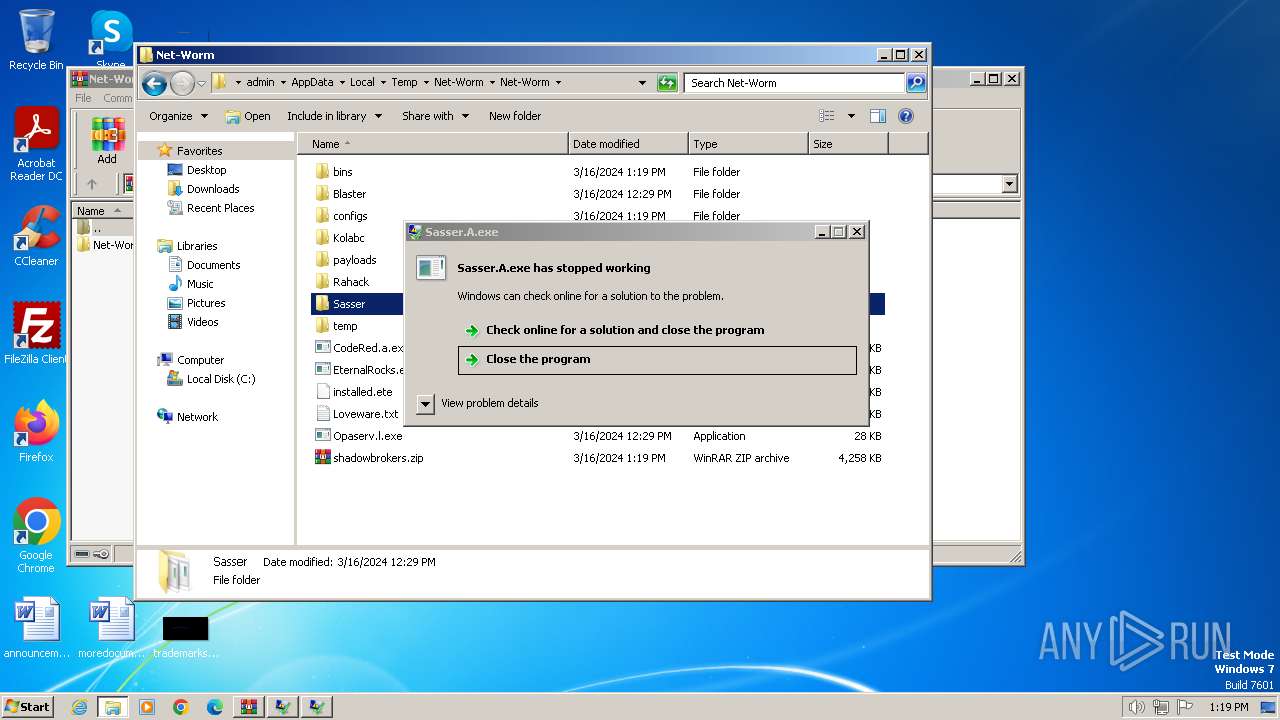
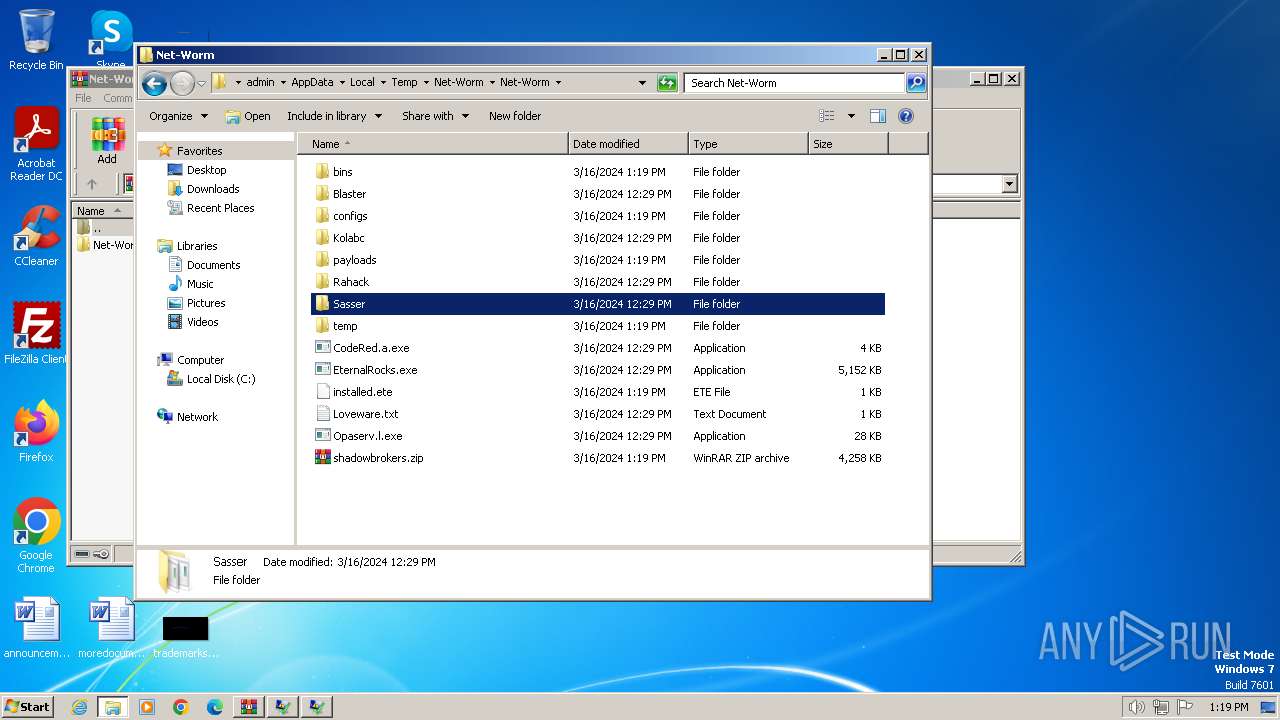
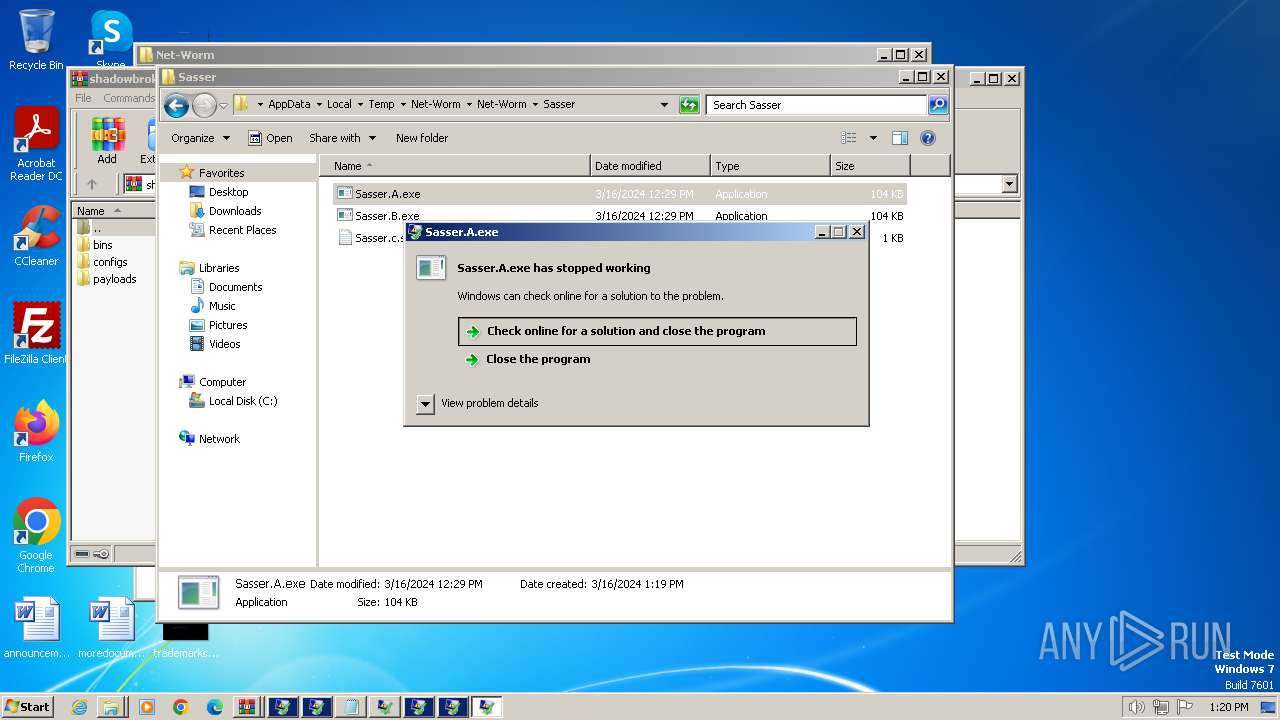
- Sasser.A.exe (PID: 3444)
- Kobalc.exe (PID: 3236)
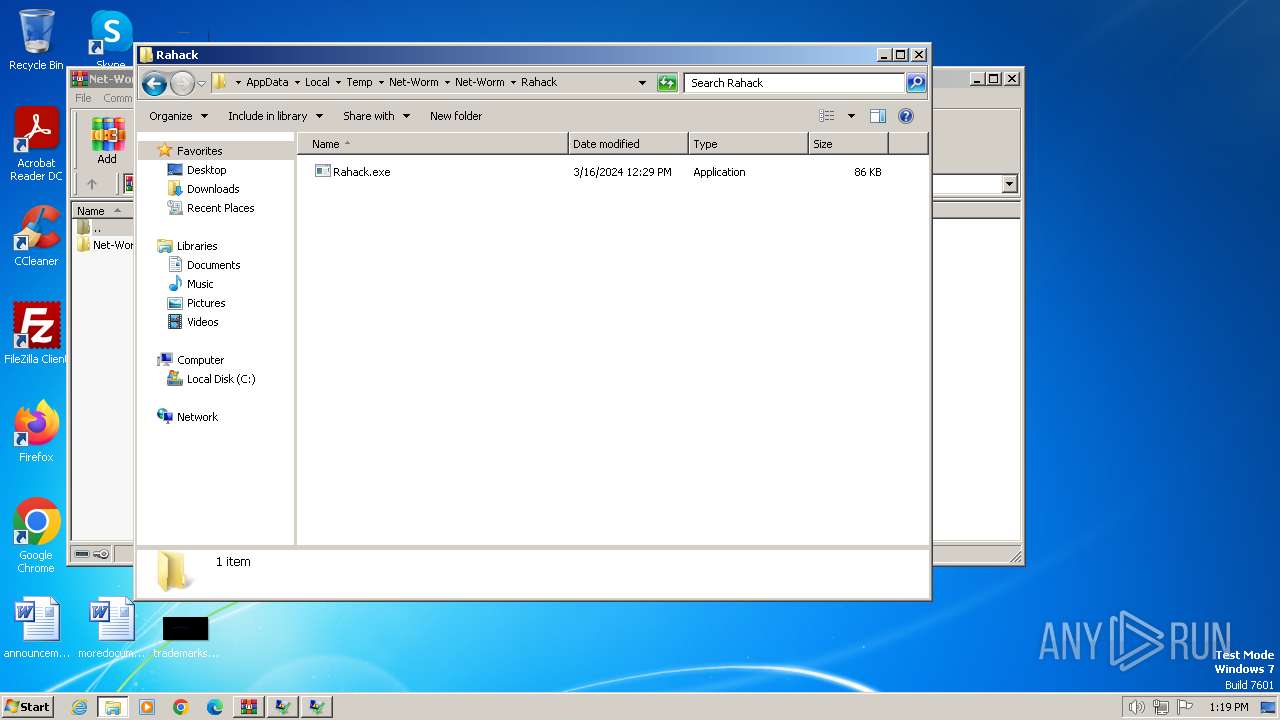
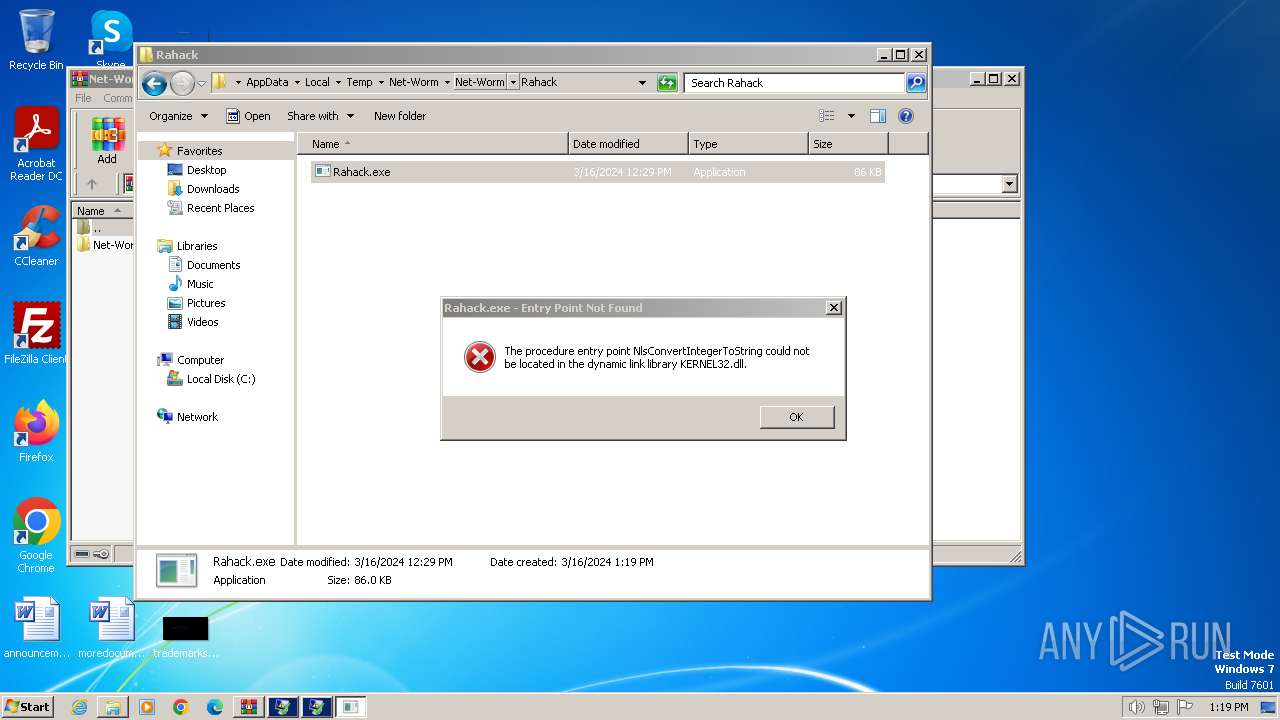
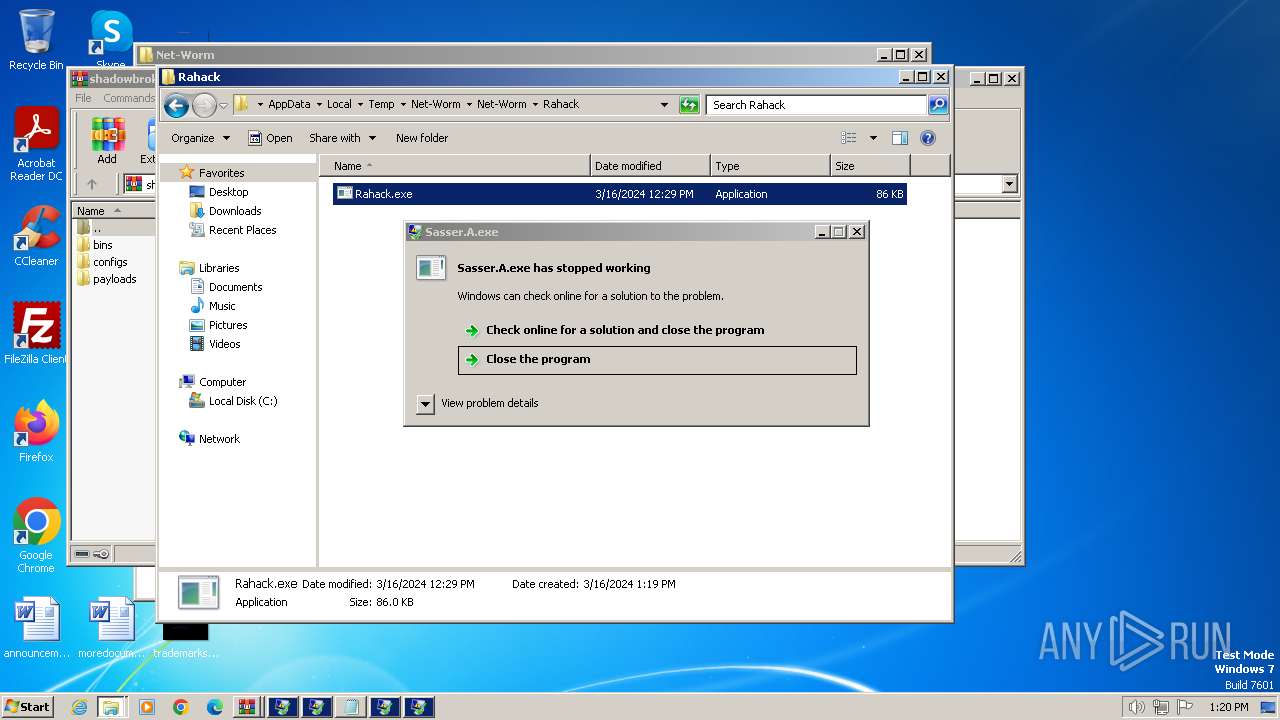
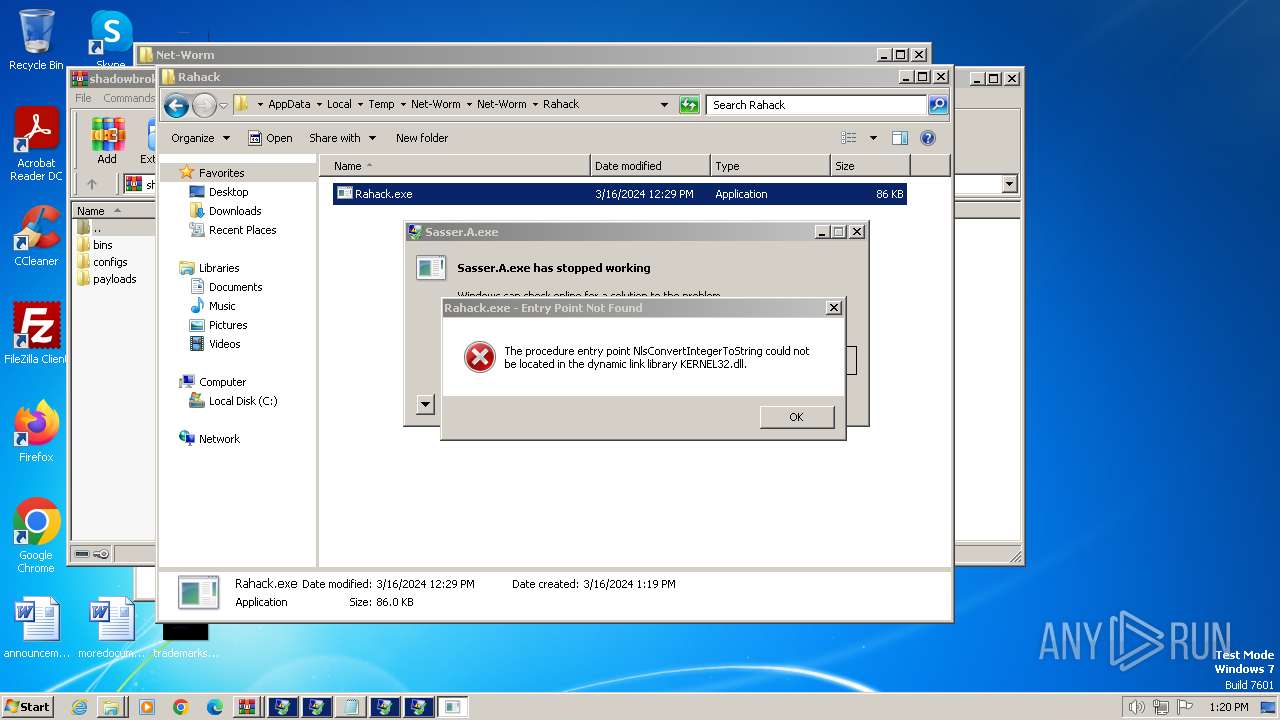
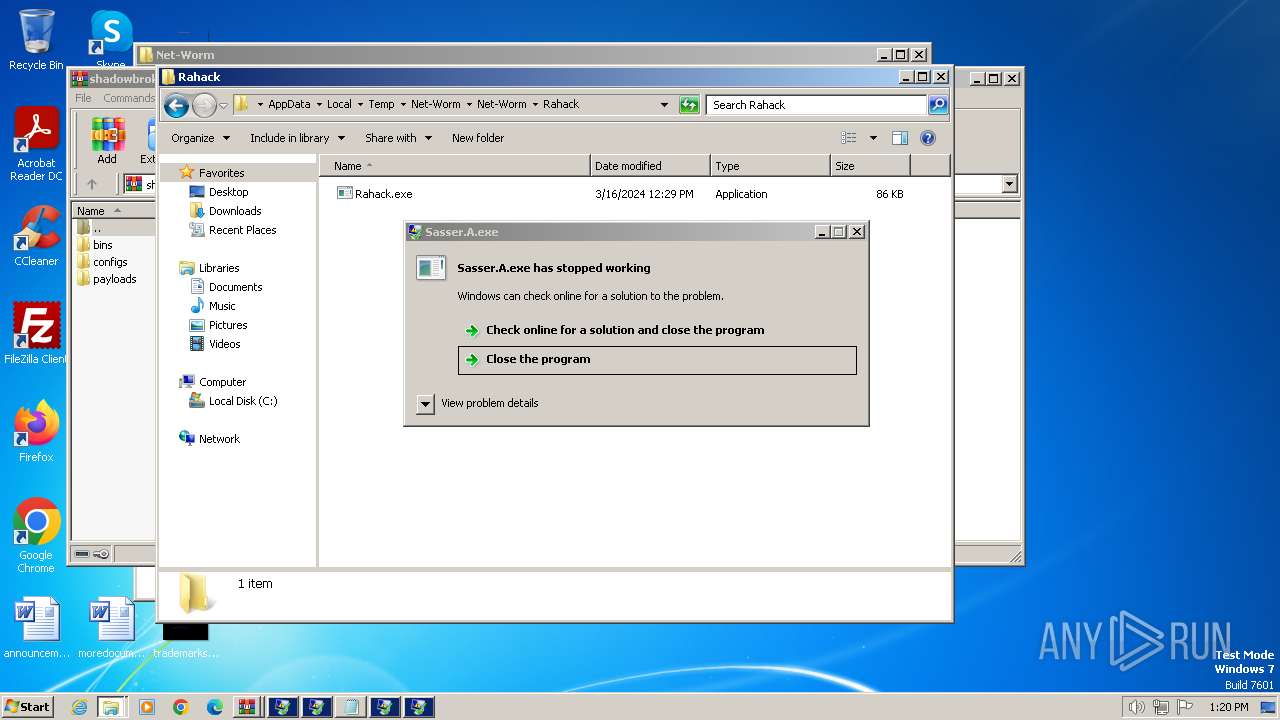
- Rahack.exe (PID: 948)
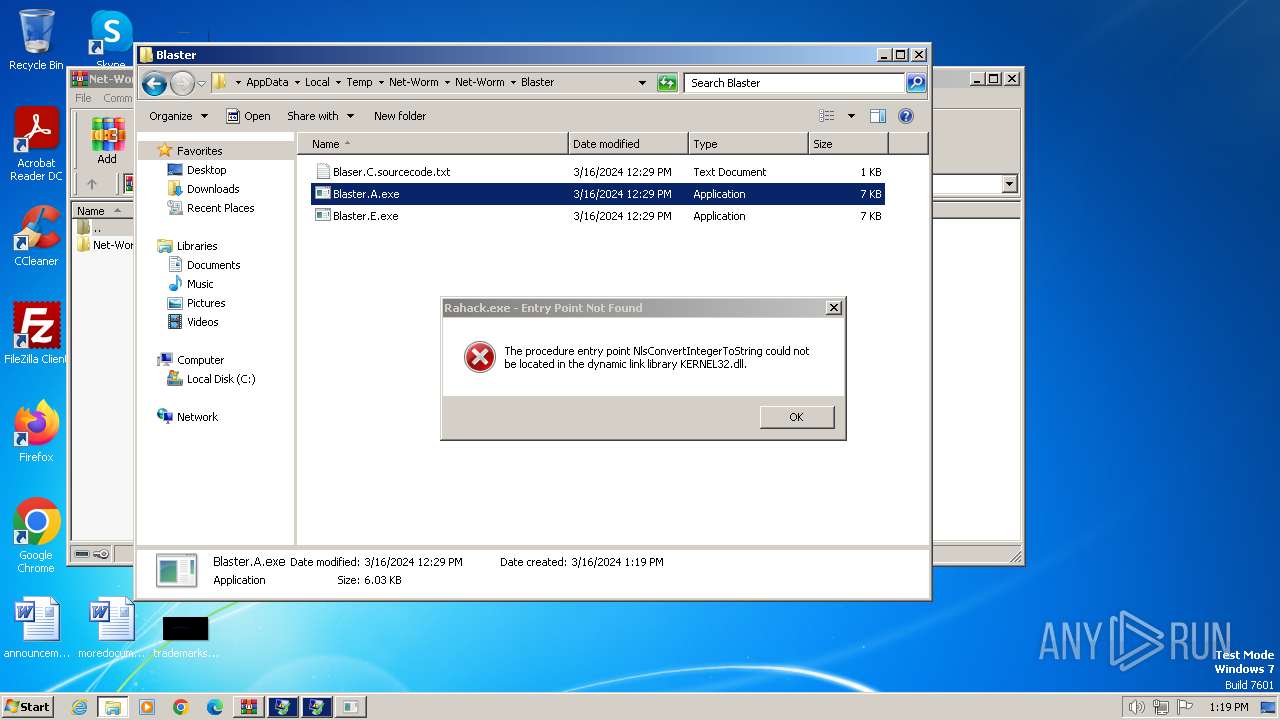
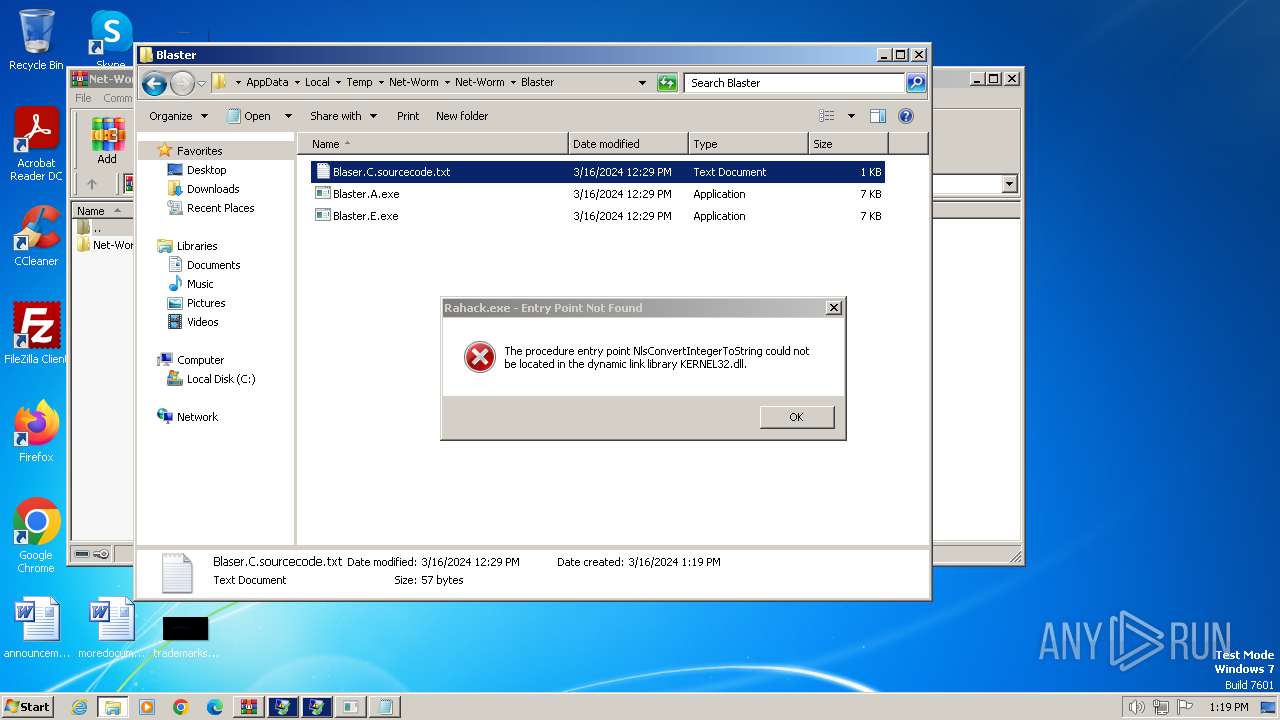
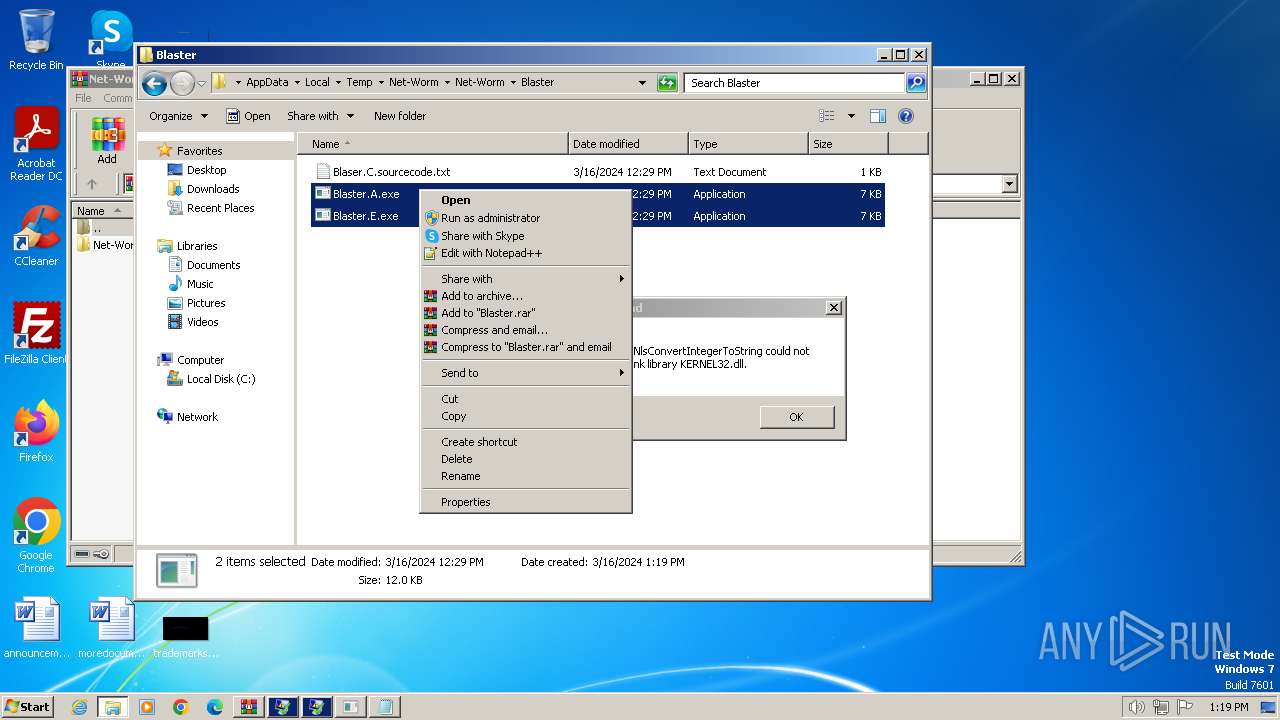
- Blaster.A.exe (PID: 2768)
- Blaster.E.exe (PID: 1288)
- notepad.exe (PID: 3604)
- Sasser.A.exe (PID: 3480)
- Sasser.B.exe (PID: 2028)
- Rahack.exe (PID: 2864)
- Sasser.A.exe (PID: 2808)
- Sasser.A.exe (PID: 3708)
- Blaster.A.exe (PID: 4016)
- Blaster.E.exe (PID: 2948)
- WinRAR.exe (PID: 3296)
Executable content was dropped or overwritten
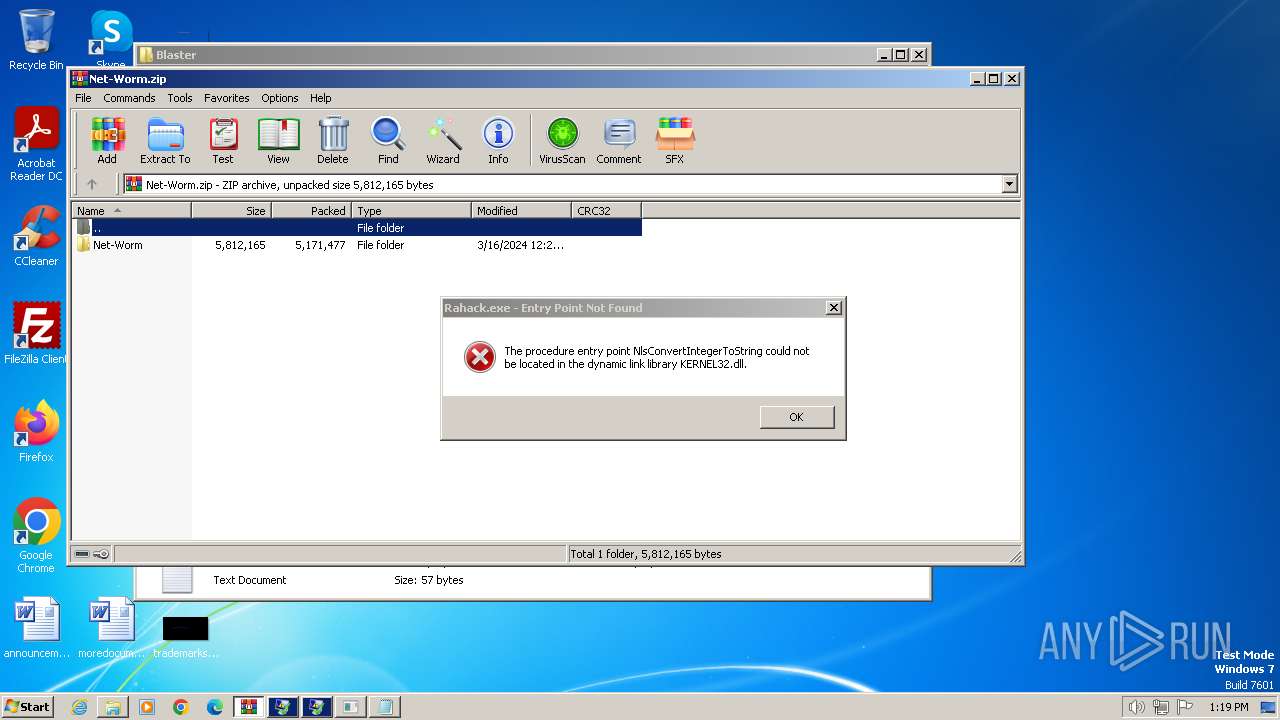
- WinRAR.exe (PID: 3992)
- WinRAR.exe (PID: 3296)
Checks supported languages
- EternalRocks.exe (PID: 848)
- Opaserv.l.exe (PID: 1740)
- Sasser.B.exe (PID: 3496)
- Sasser.A.exe (PID: 3444)
Reads the computer name
- Opaserv.l.exe (PID: 1740)
- EternalRocks.exe (PID: 848)
Reads the machine GUID from the registry
- EternalRocks.exe (PID: 848)
Reads Environment values
- EternalRocks.exe (PID: 848)
Create files in a temporary directory
- EternalRocks.exe (PID: 848)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:03:16 12:29:42 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
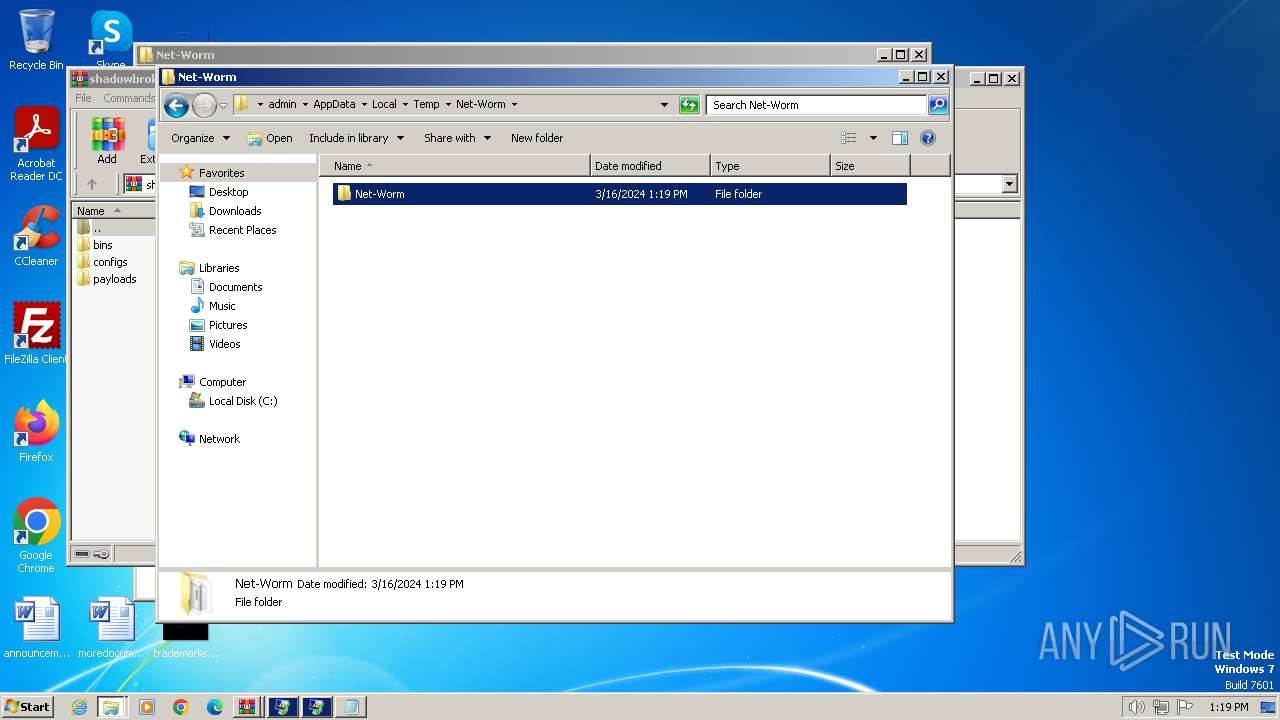
| ZipFileName: | Net-Worm/ |
Total processes
93
Monitored processes
34
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | NET STOP MCSHIELD | C:\Windows\System32\net.exe | — | Opaserv.l.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
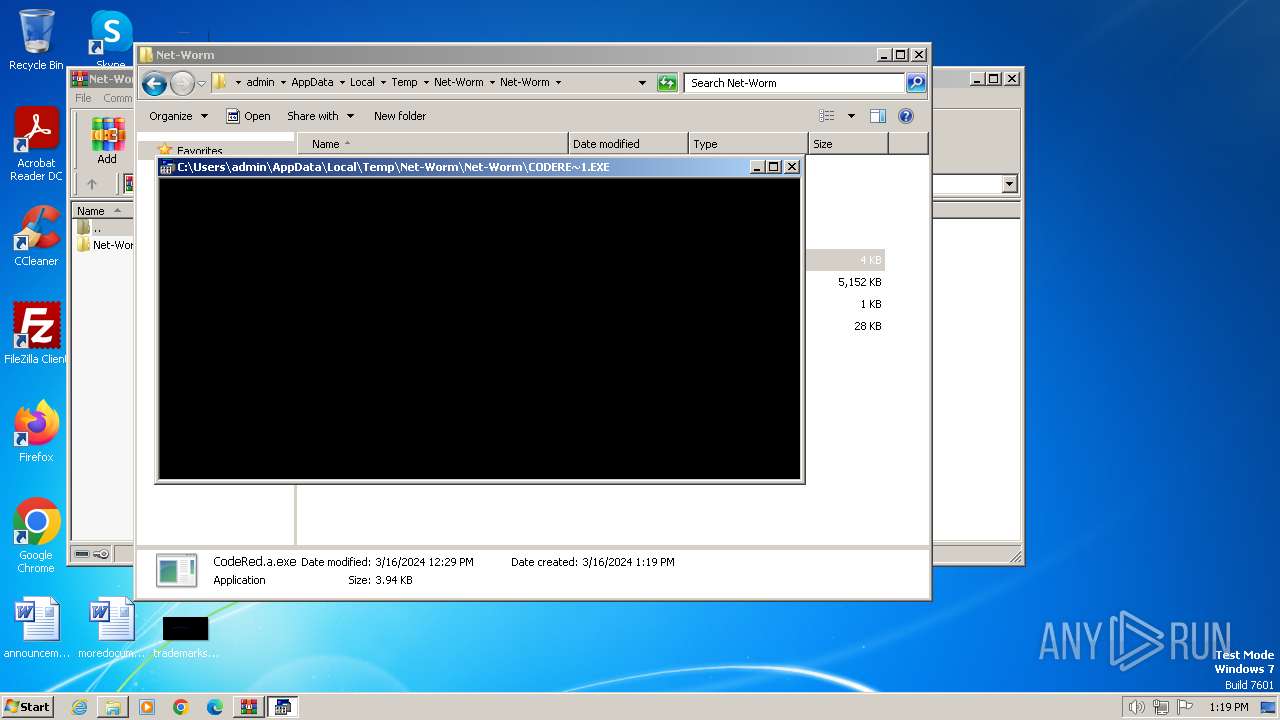
| 848 | "C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\EternalRocks.exe" | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\EternalRocks.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: EternalRocks Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
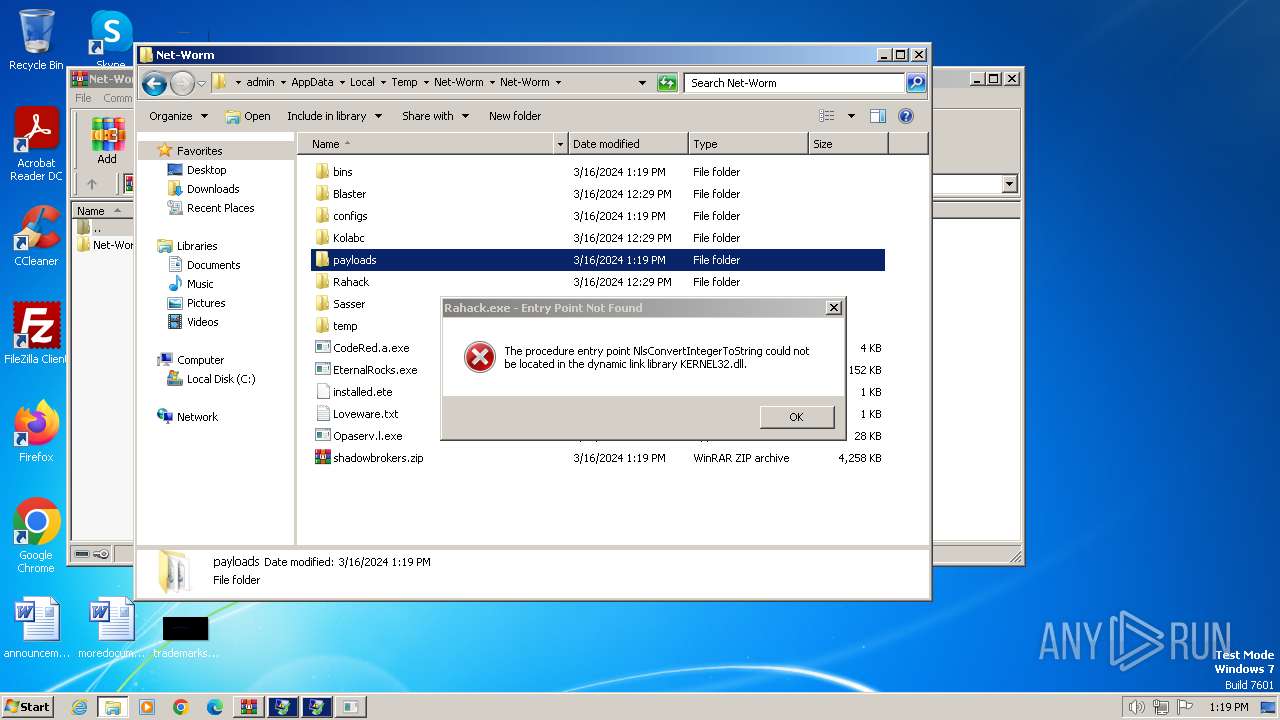
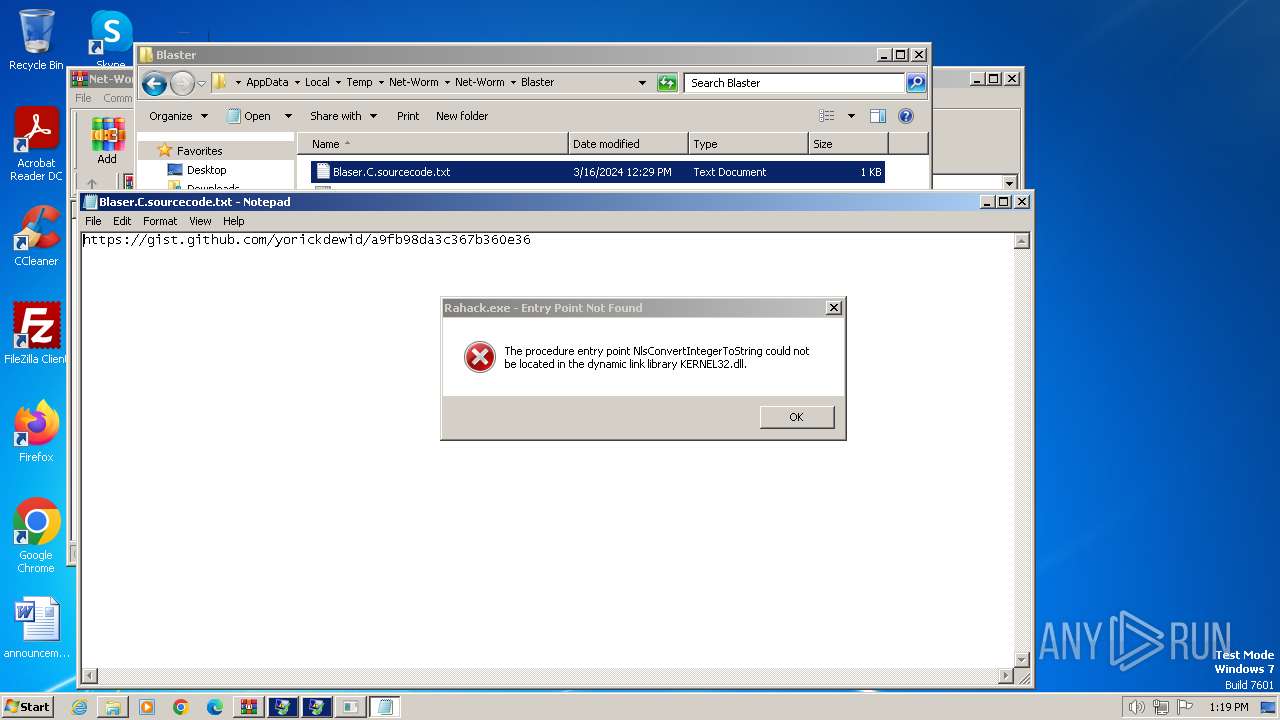
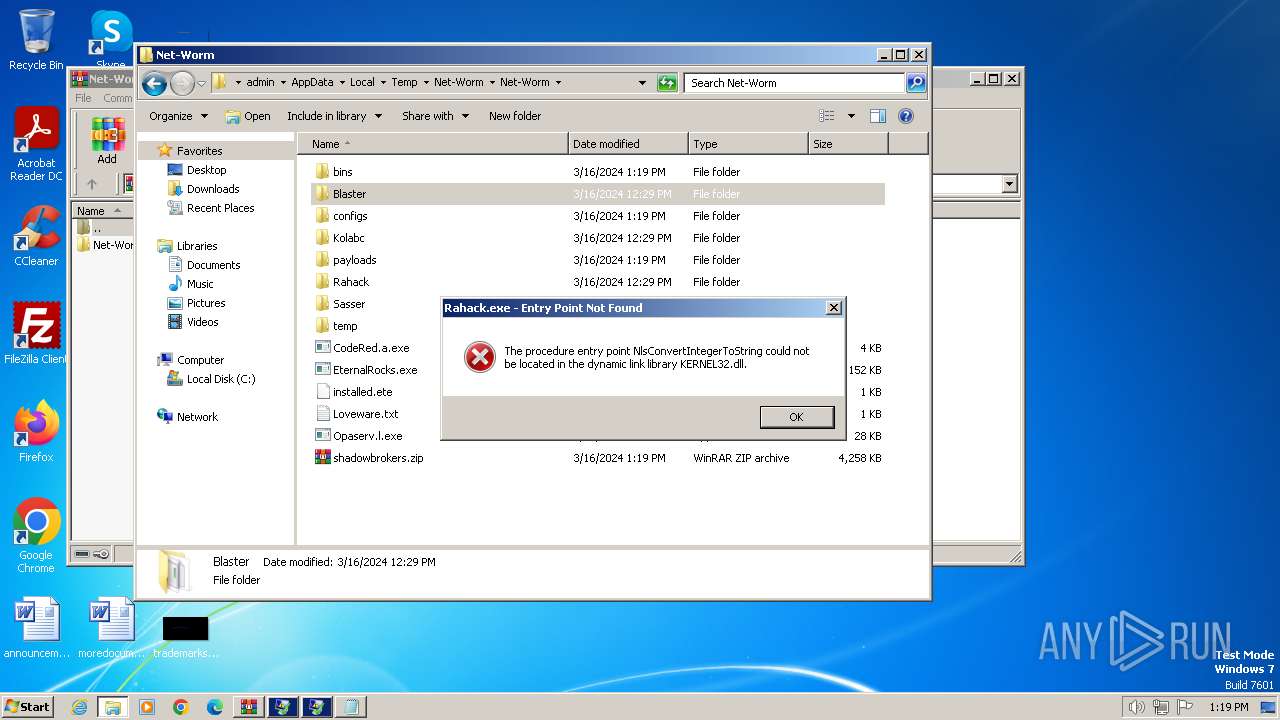
| 948 | "C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Rahack\Rahack.exe" | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Rahack\Rahack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225785 Modules
| |||||||||||||||
| 1288 | "C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Blaster\Blaster.E.exe" | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Blaster\Blaster.E.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 | |||||||||||||||
| 1348 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\System32\ntvdm.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | C:\Windows\system32\net1 STOP MCSHIELD | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1496 | "C:\Windows\System32\netsh.exe" firewall set portopening TCP 1013 BS | C:\Windows\System32\netsh.exe | — | Kobalc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 1560 | NET STOP SWEEPSRV.SYS | C:\Windows\System32\net.exe | — | Opaserv.l.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1576 | C:\Windows\system32\net1 STOP PERSFW | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1740 | "C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Opaserv.l.exe" | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Opaserv.l.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 306
Read events
4 285
Write events
21
Delete events
0
Modification events
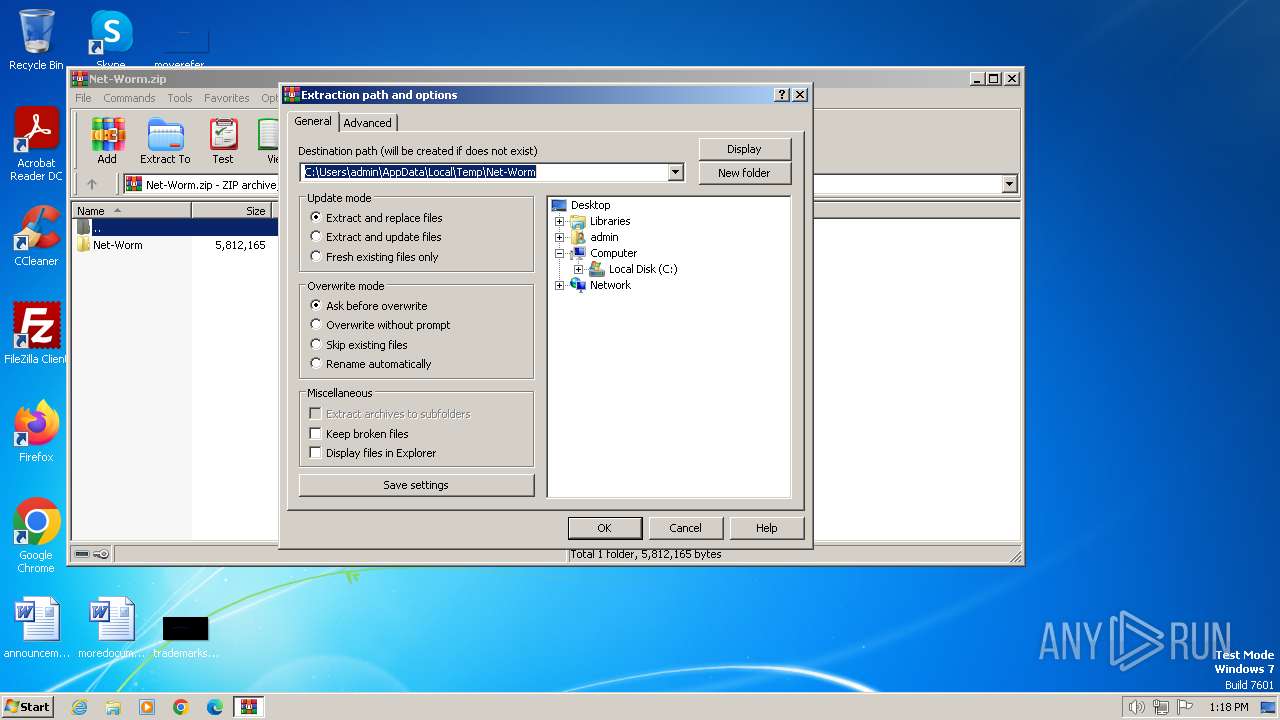
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Net-Worm.zip | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
118
Suspicious files
4
Text files
34
Unknown types
2
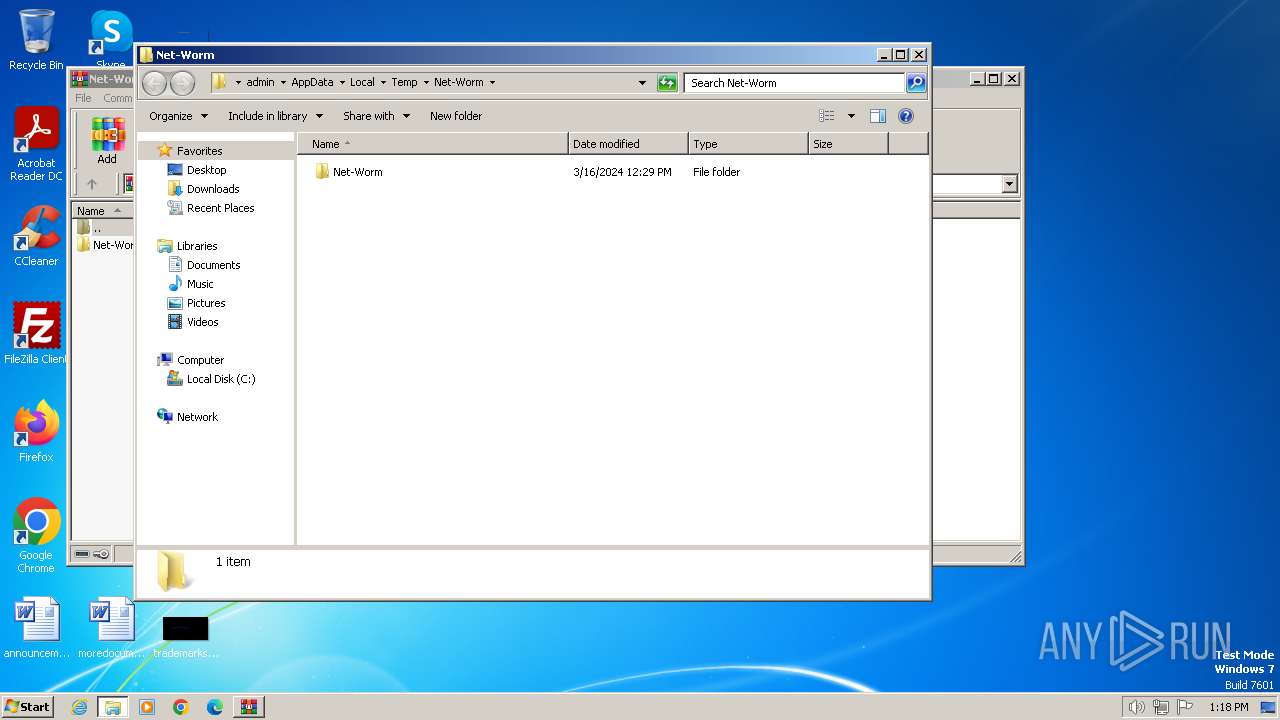
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
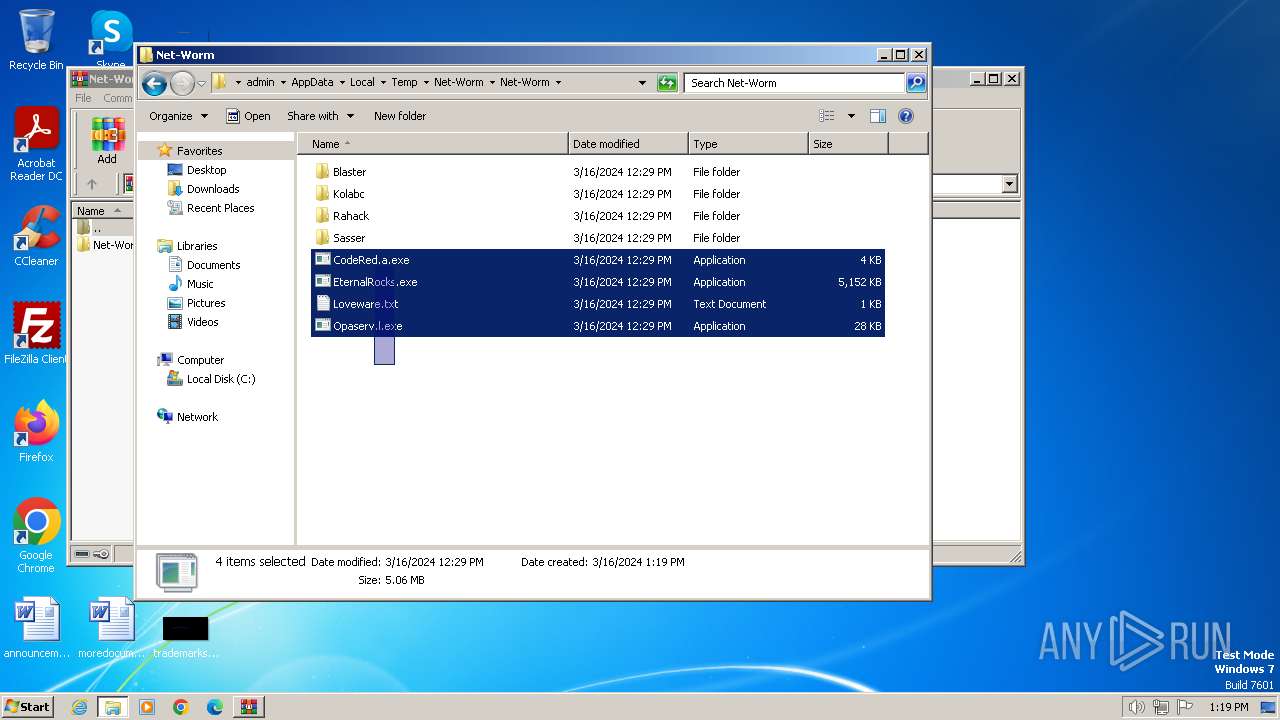
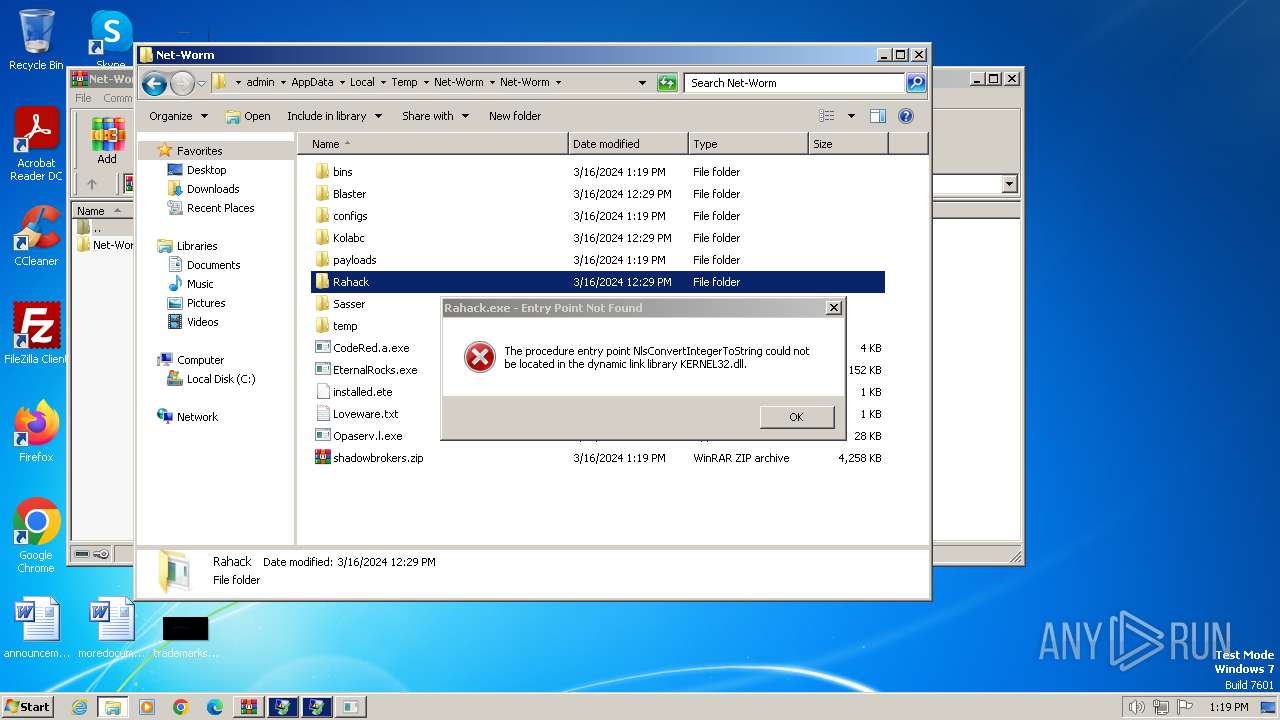
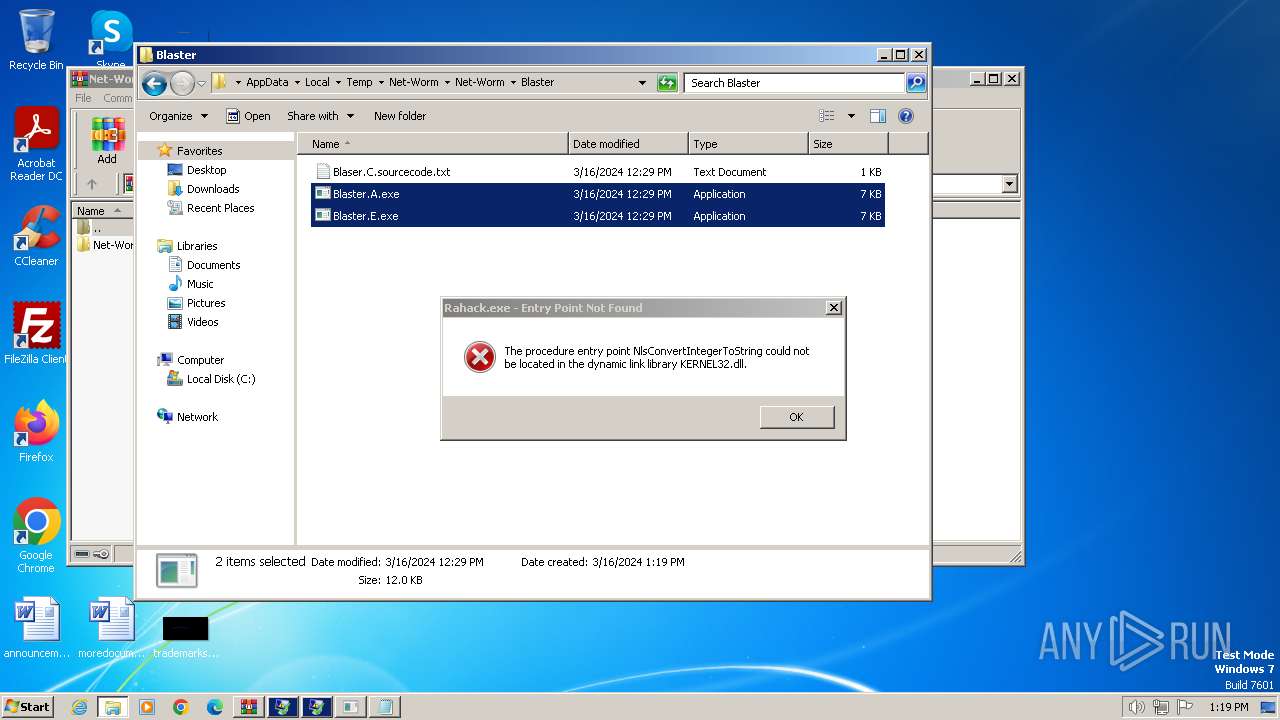
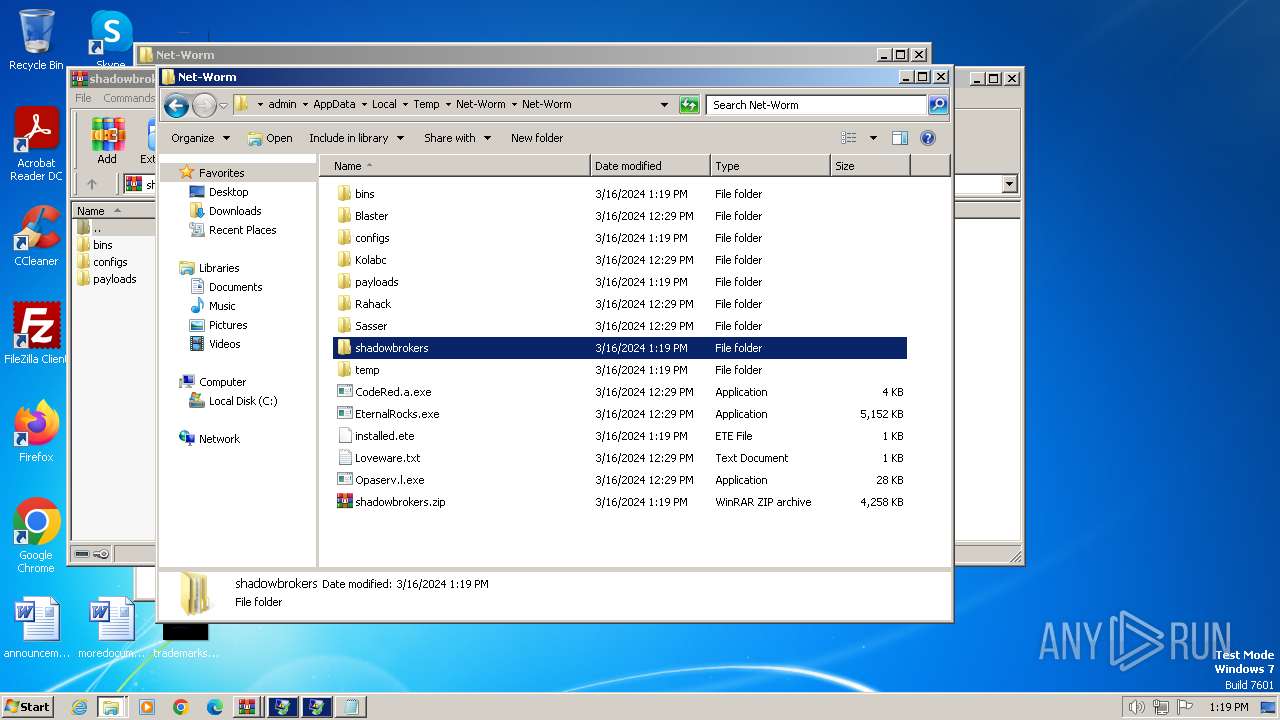
| 3992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Blaster\Blaster.E.exe | executable | |
MD5:8676210E6246948201AA014DB471DE90 | SHA256:2E481059B9BC9686C676D69A80202EED5022C9A53ECD8CAC215E70C601DD7FDC | |||
| 3992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Blaster\Blaster.A.exe | executable | |
MD5:5AE700C1DFFB00CEF492844A4DB6CD69 | SHA256:258F82166D20C68497A66D82349FC81899FDE8FE8C1CC66E59F739A9EA2C95A9 | |||
| 3992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Blaster\Blaser.C.sourcecode.txt | text | |
MD5:D1D3280B12EFBE2EEA097D8EC9162B9B | SHA256:604619EFB204C92DB0A983EF0C120080610EBBC2C1EA6637230F78024EFC46C8 | |||
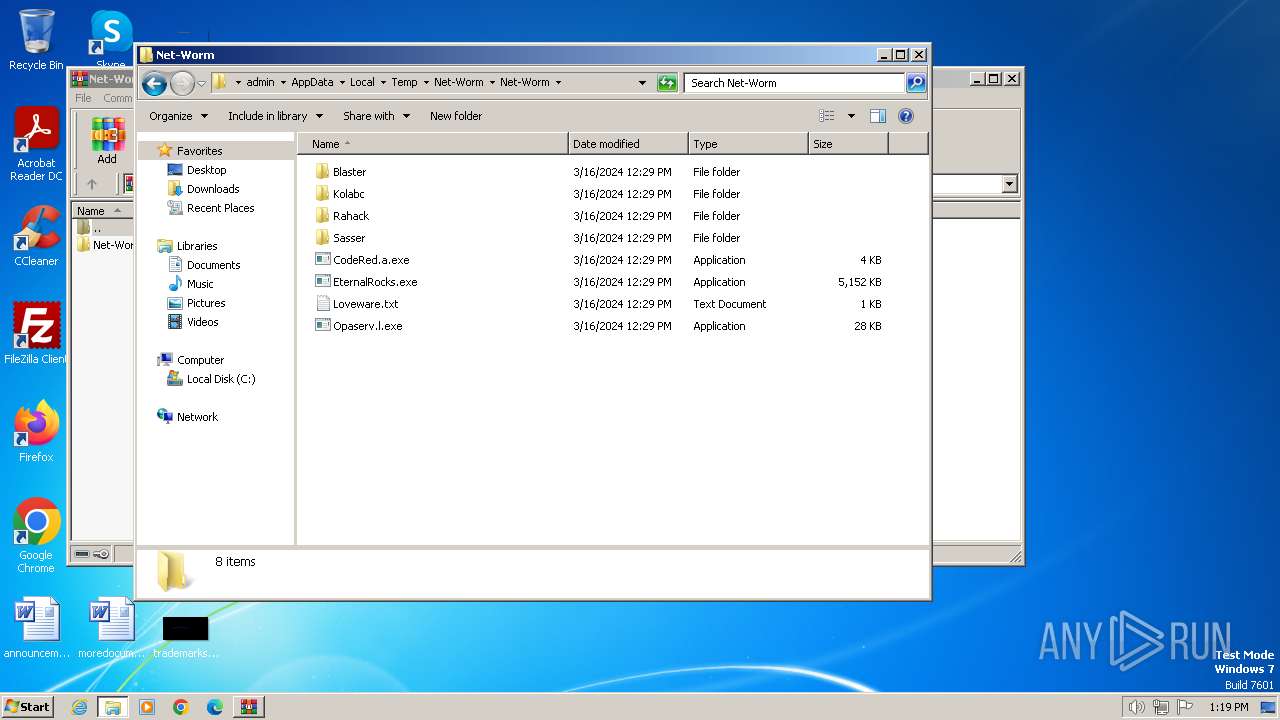
| 3992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\CodeRed.a.exe | bs | |
MD5:6F5767EC5A9CC6F7D195DDE3C3939120 | SHA256:59FE169797953F2046B283235FE80158EBF02BA586EABFEA306402FBA8473DAE | |||
| 3992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Opaserv.l.exe | executable | |
MD5:71C981D4F5316C3AD1DEEFE48FDDB94A | SHA256:DE709DACAC623C637448DC91F6DFD441A49C89372AF2C53E2027E4AF5310B95D | |||
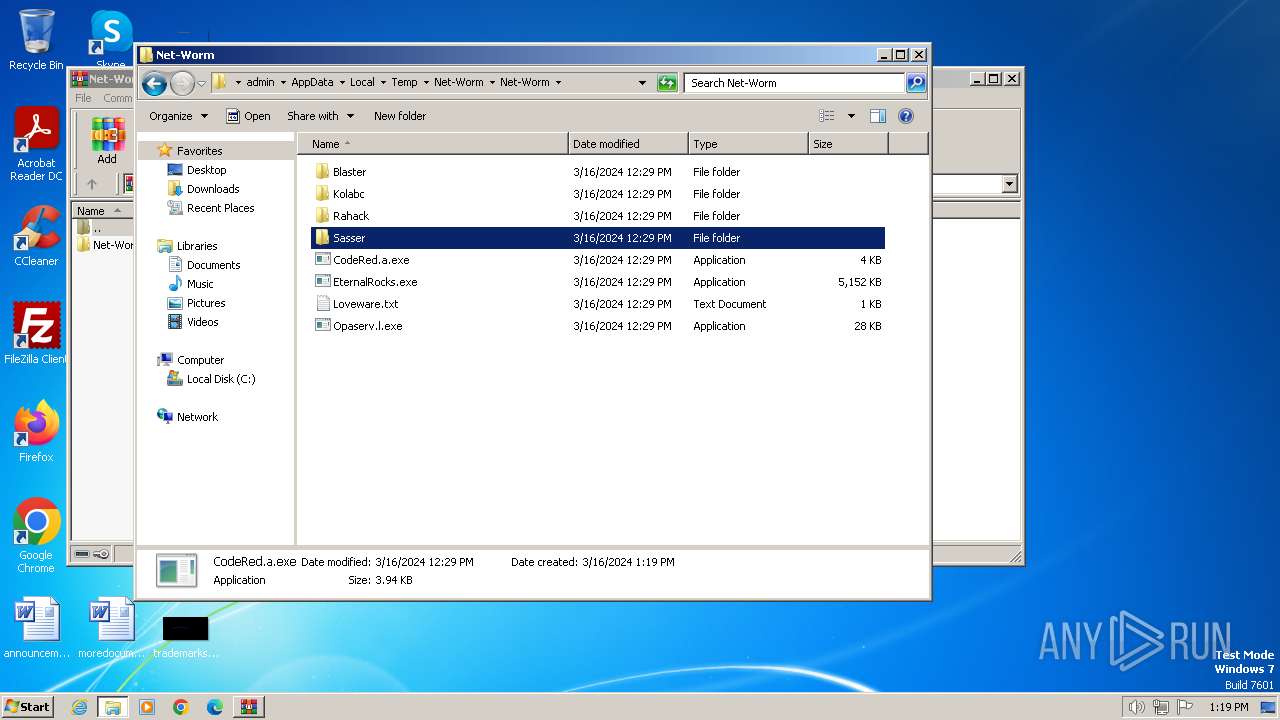
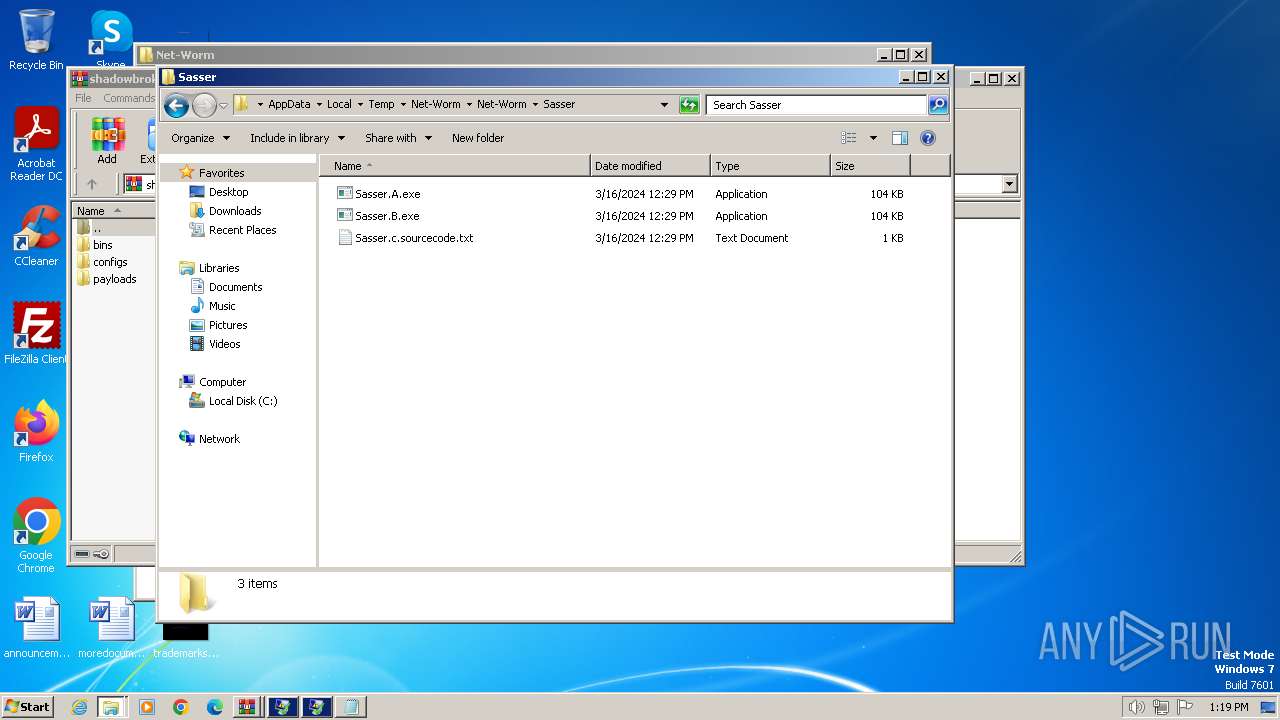
| 3992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Sasser\Sasser.c.sourcecode.txt | text | |
MD5:28FAD72D643985282FB85CA9B7892DFB | SHA256:FEBBF809124ED9D5771CA2DA4F2D8FD23643970BECC3D6B062E14CC97FAEE4B7 | |||
| 3992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Sasser\Sasser.B.exe | executable | |
MD5:FA3348956253F9F733B28B4CF1D45942 | SHA256:00808F00EC970E3ED518ED40BA77F64BE2B9761B02FBAEA2047C5AC82D8B8F99 | |||
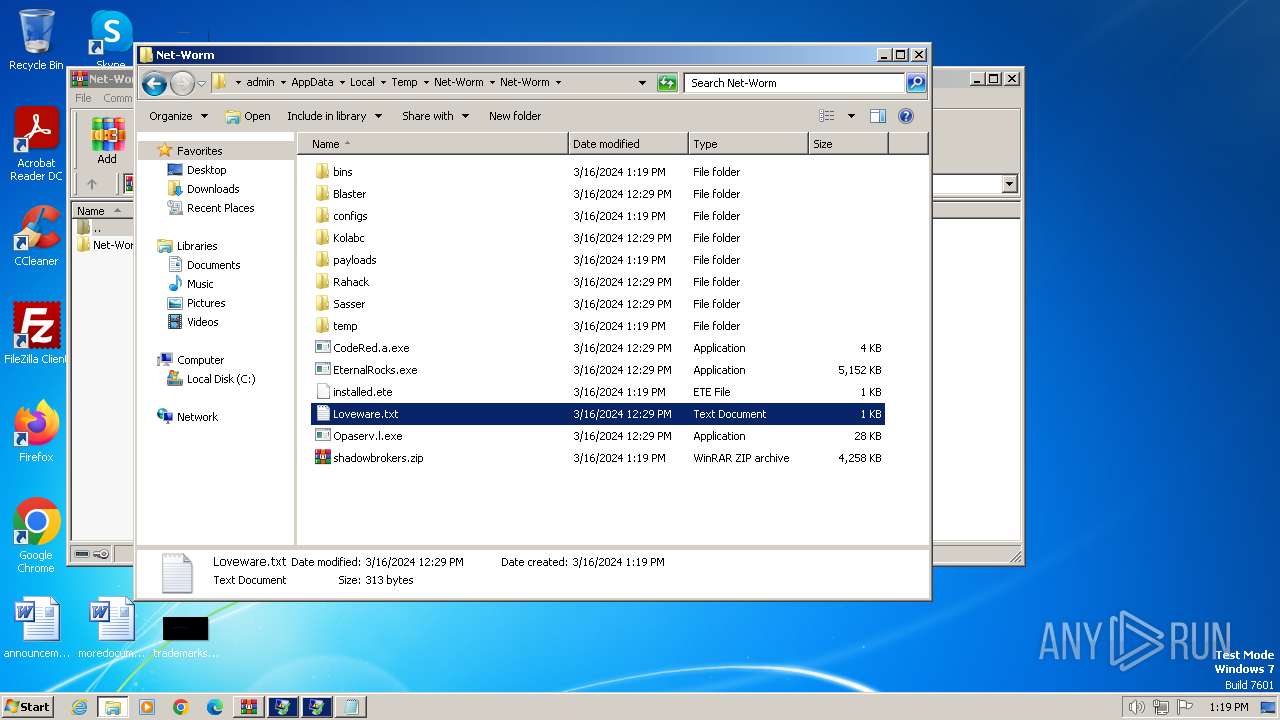
| 3992 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\Loveware.txt | text | |
MD5:9F59E4D545E1A16EC4AD1B11291C5346 | SHA256:CD41EB3B411ABD314E90D980F4E05D7D2DB60FB8A9616F84754B4E1EEB10F290 | |||
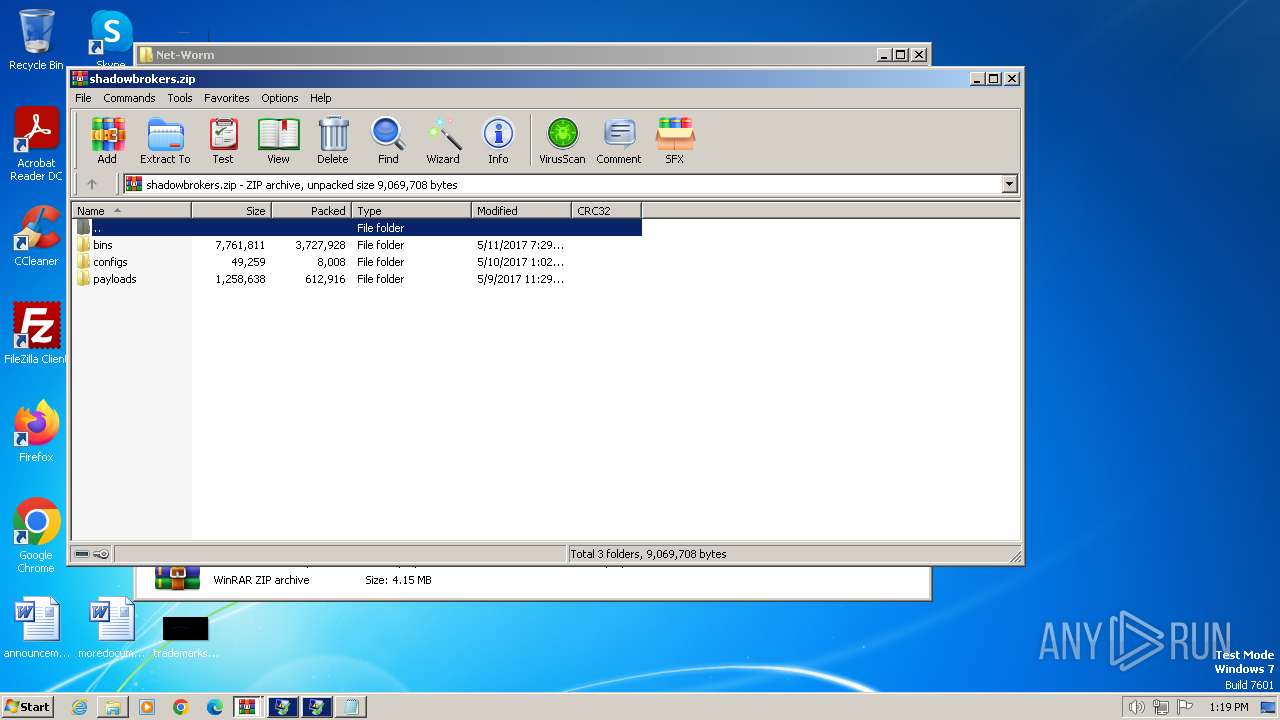
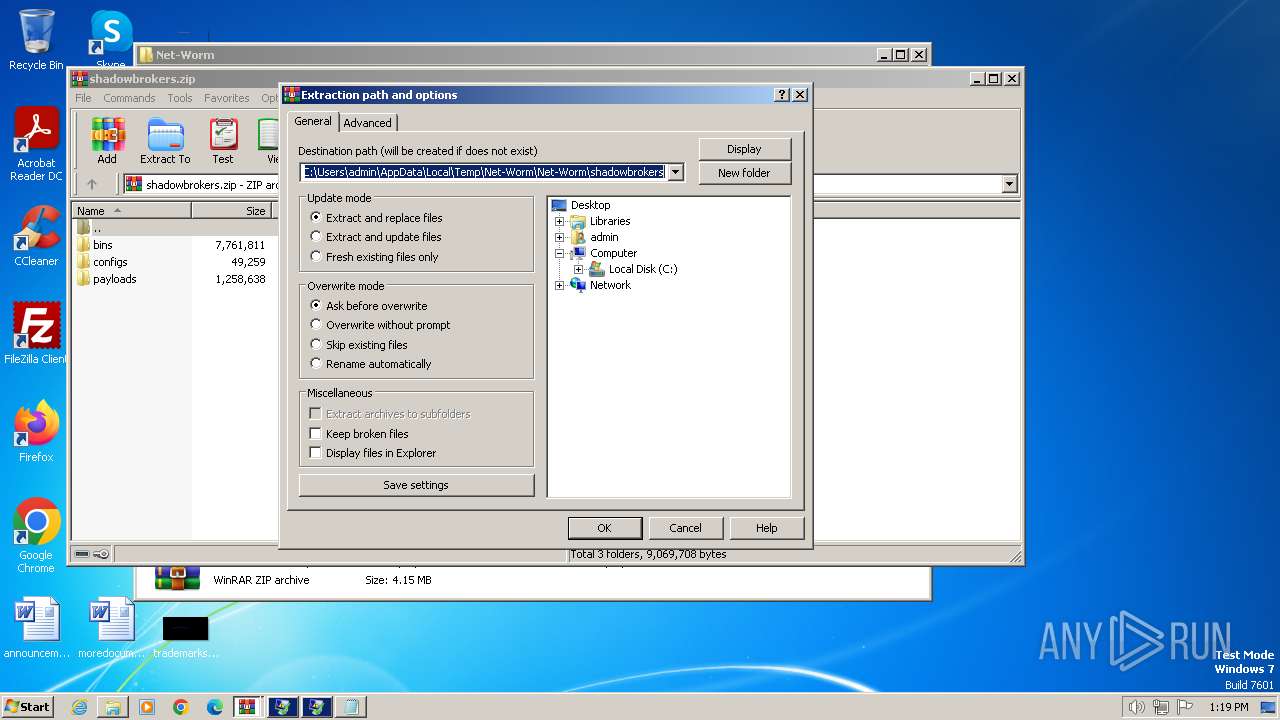
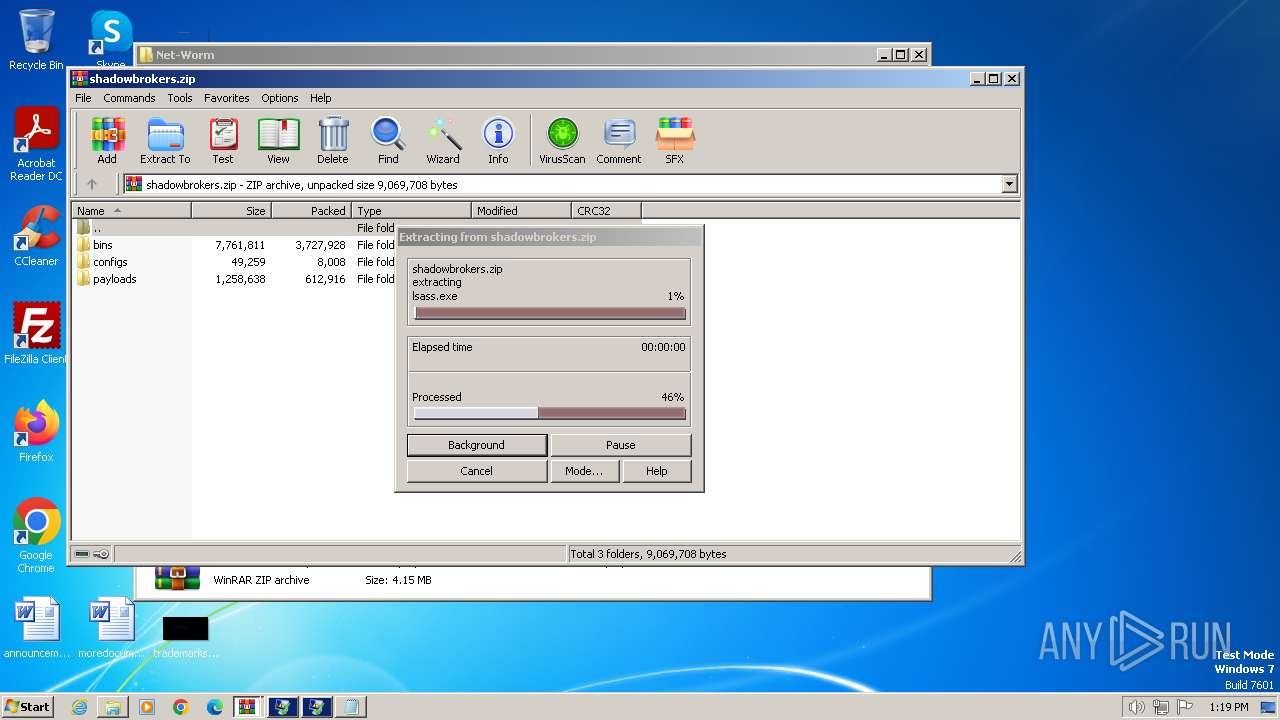
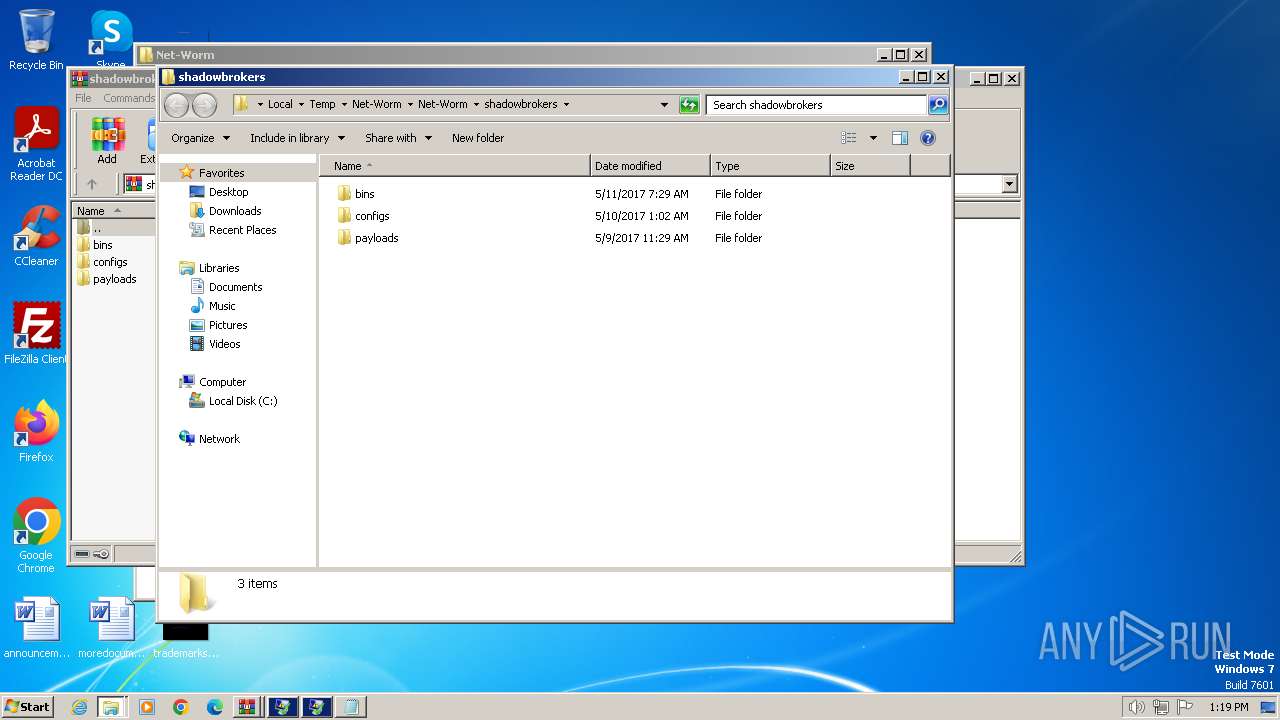
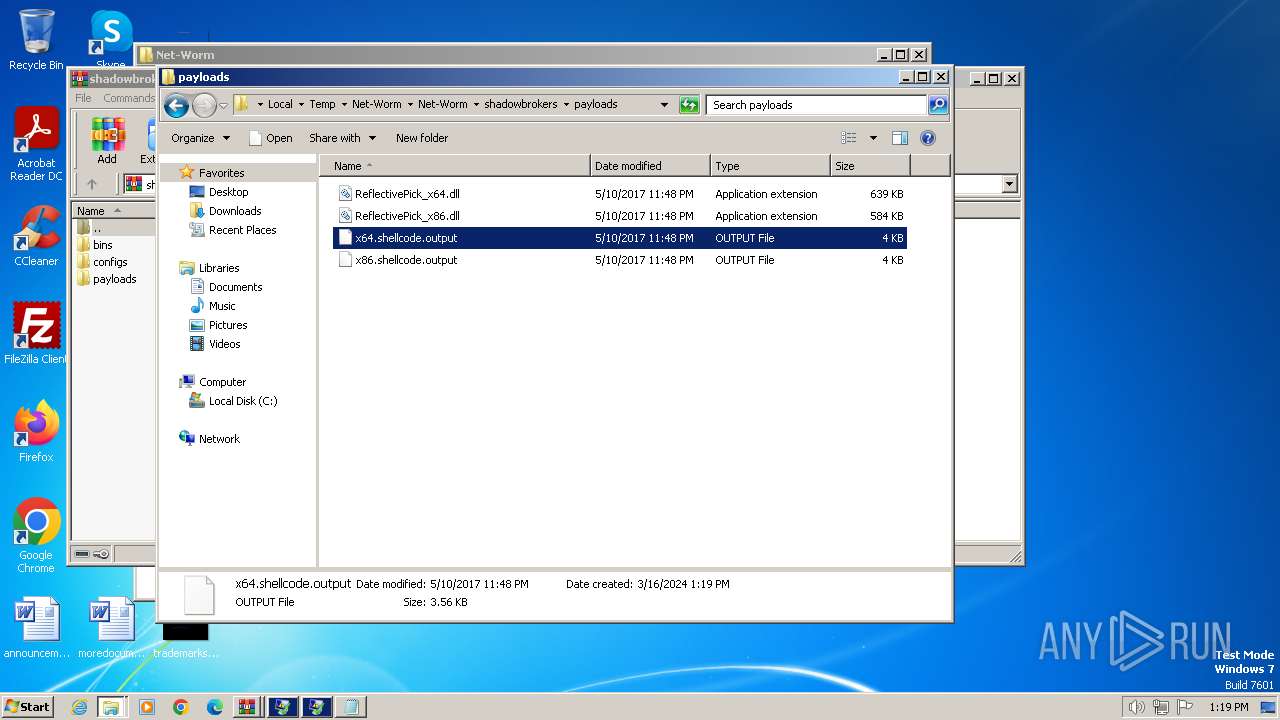
| 848 | EternalRocks.exe | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\shadowbrokers.zip | compressed | |
MD5:6FDBEE99DC99A63AC6A5809450D55AD5 | SHA256:70EC0E2B6F9FF88B54618A5F7FBD55B383CF62F8E7C3795C25E2F613BFDDF45D | |||
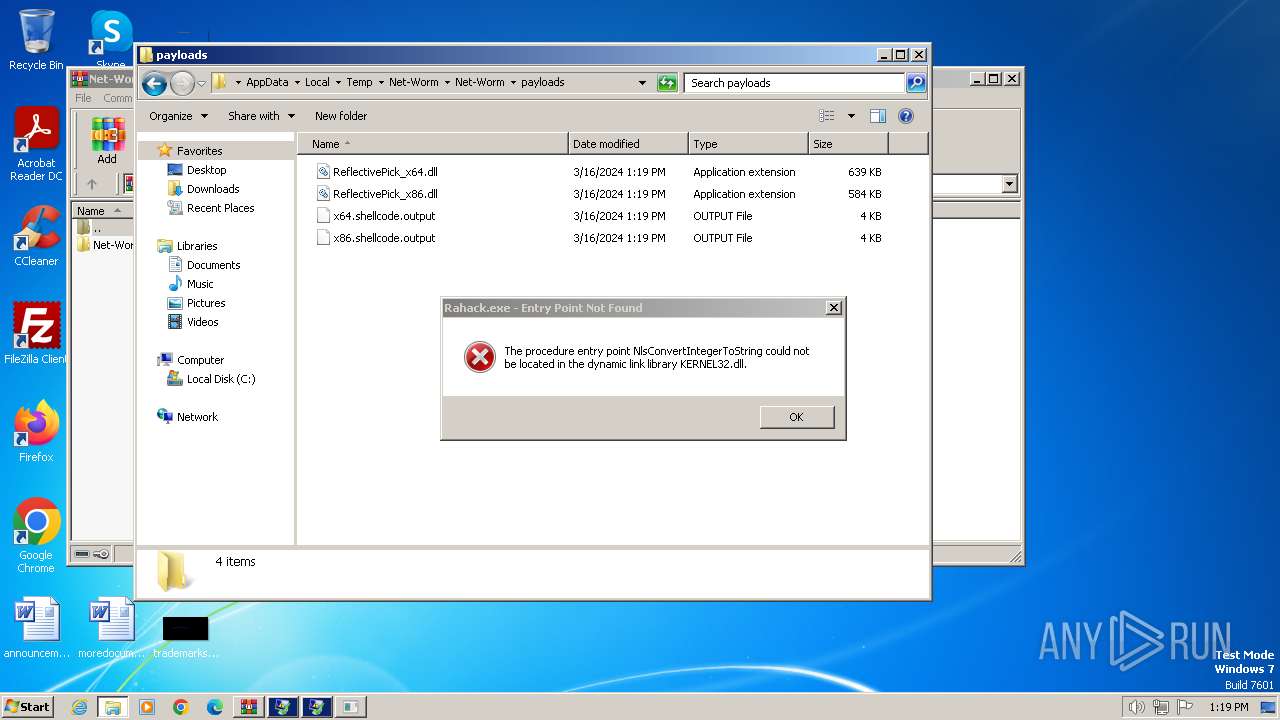
| 848 | EternalRocks.exe | C:\Users\admin\AppData\Local\Temp\Net-Worm\Net-Worm\bins\cnli-1.dll | executable | |
MD5:A539D27F33EF16E52430D3D2E92E9D5C | SHA256:DB0831E19A4E3A736EA7498DADC2D6702342F75FD8F7FBAE1894EE2E9738C2B4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
105
DNS requests
12
Threats
10
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
— | — | 192.168.87.1:135 | — | — | — | unknown |
— | — | 192.168.87.2:135 | — | — | — | unknown |
— | — | 192.168.87.3:135 | — | — | — | unknown |
— | — | 192.168.87.4:135 | — | — | — | unknown |
— | — | 192.168.87.5:135 | — | — | — | unknown |
— | — | 192.168.87.6:135 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
windowsupdate.com |
| unknown |
kimble.org |
| unknown |
hodkskis1981.weedns.com |
| unknown |
xoxoxmyman.weedns.com |
| unknown |
watson.microsoft.com |
| whitelisted |
1.0x0103x0x0m.co.cc |
| unknown |
1.itsy-bitsy.co.cc |
| unknown |
dashman.dnip.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .co.cc Domain |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .co.cc Domain |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .co.cc Domain |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .co.cc Domain |
— | — | Misc activity | ET INFO IRC Nick change on non-standard port |
— | — | Misc activity | ET INFO IRC Nick change on non-standard port |