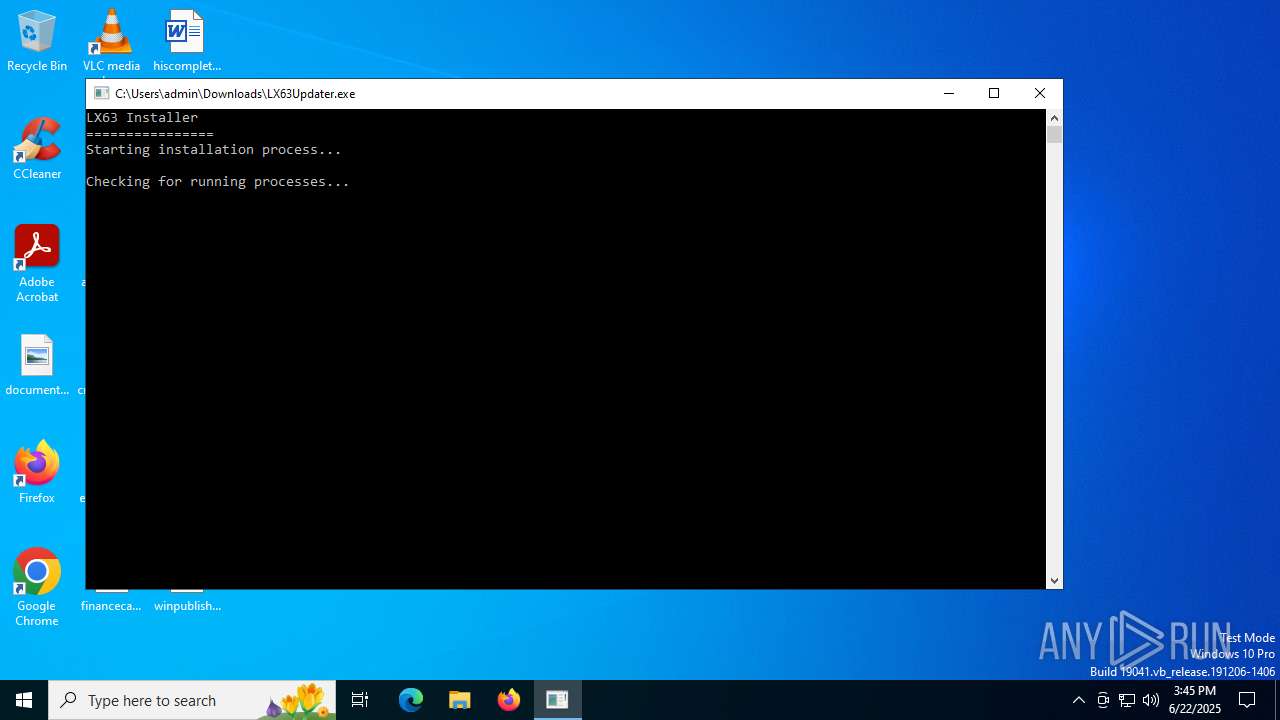
| File name: | LX63Updater.exe |
| Full analysis: | https://app.any.run/tasks/ff12b094-e3f5-42a4-a17e-3af0ce50691b |
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2025, 15:45:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 4651EEB55D975ABA81B111A99269653F |
| SHA1: | 7657CF3BBB14C5CF421C2B3BF2623AD2AEEE6E3F |
| SHA256: | 1F1BC42F90EEA13BB57A49EE7596B3FD6E371C9B871C7082E088D066287D2A01 |
| SSDEEP: | 768:Vec5hU/n08Ou0VGuNEP7lLVwyRcTuKjpG9H:VPR8OJVfKL16uKQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- LX63Updater.exe (PID: 1324)
- LX63.exe (PID: 6292)
- LX63.exe (PID: 7116)
- WinRAR.exe (PID: 1508)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 3780)
- net.exe (PID: 5476)
- cmd.exe (PID: 7108)
- net.exe (PID: 2976)
- net.exe (PID: 3740)
- cmd.exe (PID: 6776)
- net.exe (PID: 5476)
- cmd.exe (PID: 4236)
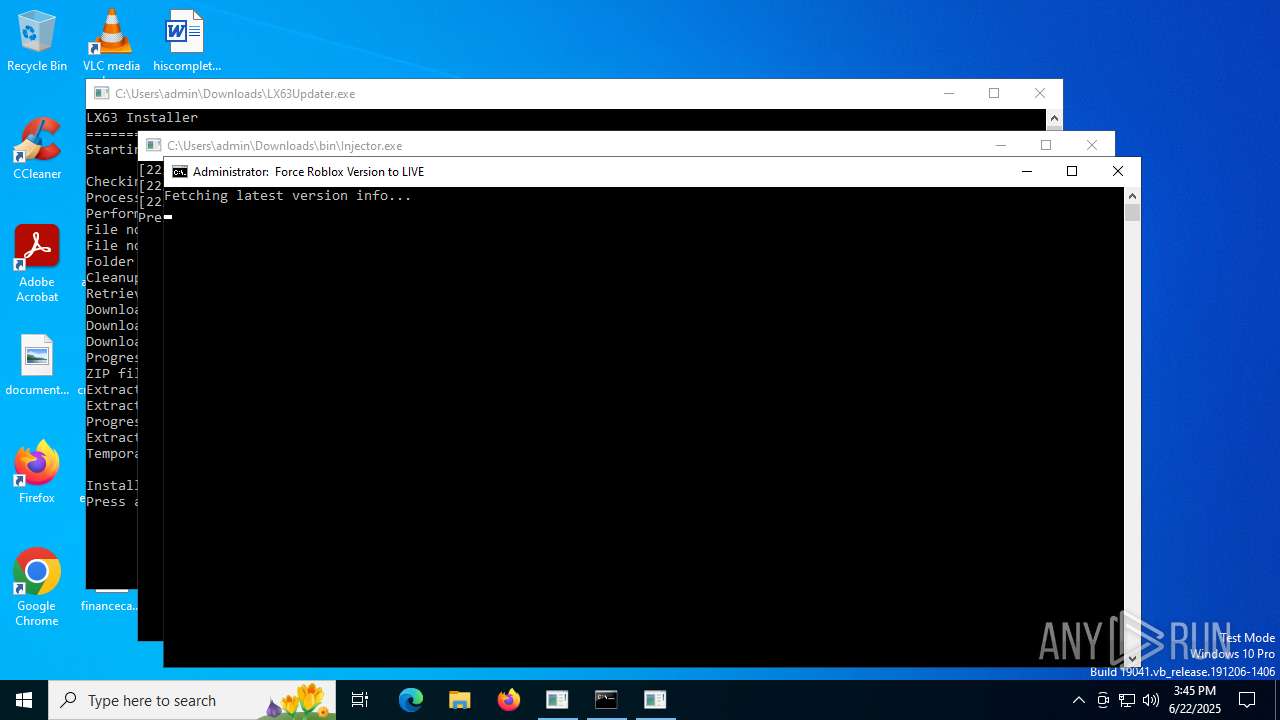
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3780)
- cmd.exe (PID: 4236)
- cmd.exe (PID: 5372)
- cmd.exe (PID: 6348)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 7948)
Starts process via Powershell
- powershell.exe (PID: 1560)
- powershell.exe (PID: 5780)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 1560)
- cmd.exe (PID: 7108)
- powershell.exe (PID: 5780)
- cmd.exe (PID: 6776)
Executing commands from a ".bat" file
- powershell.exe (PID: 1560)
- powershell.exe (PID: 5780)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6348)
- cmd.exe (PID: 5372)
- cmd.exe (PID: 7948)
- cmd.exe (PID: 8116)
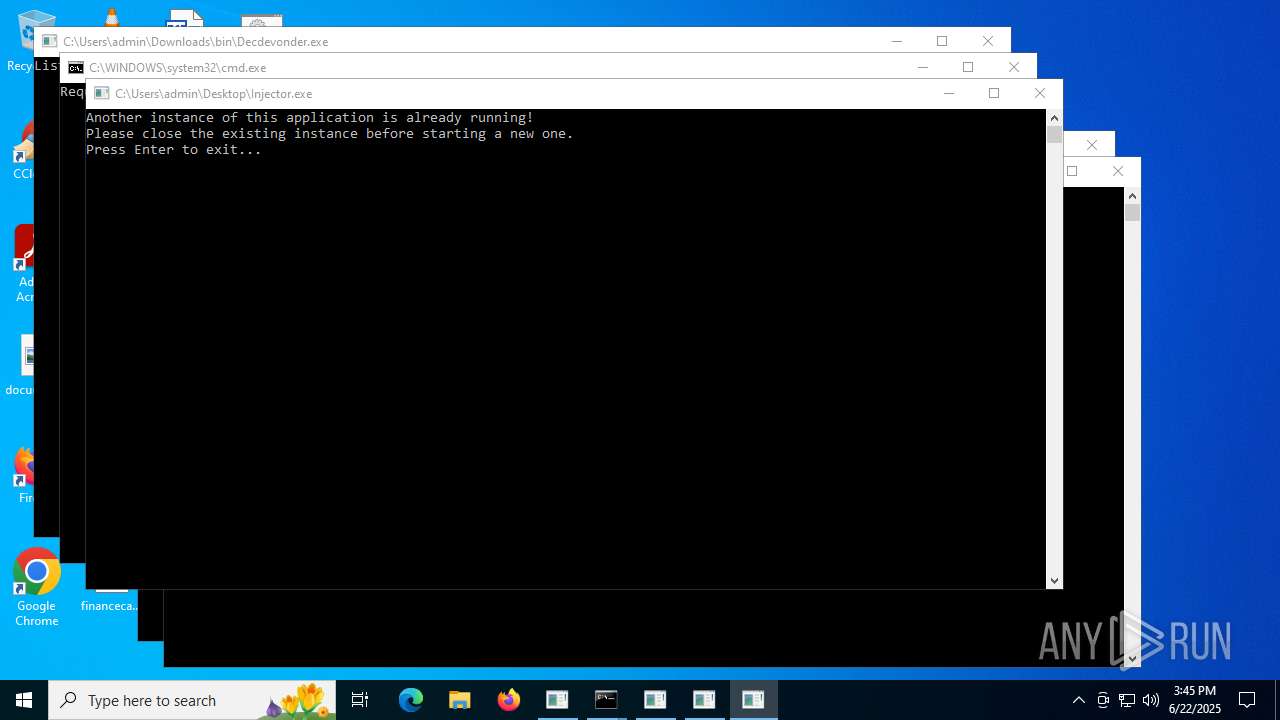
Application launched itself
- cmd.exe (PID: 7108)
- cmd.exe (PID: 6776)
Reads security settings of Internet Explorer
- LX63.exe (PID: 6292)
- LX63.exe (PID: 7116)
Hides command output
- cmd.exe (PID: 6676)
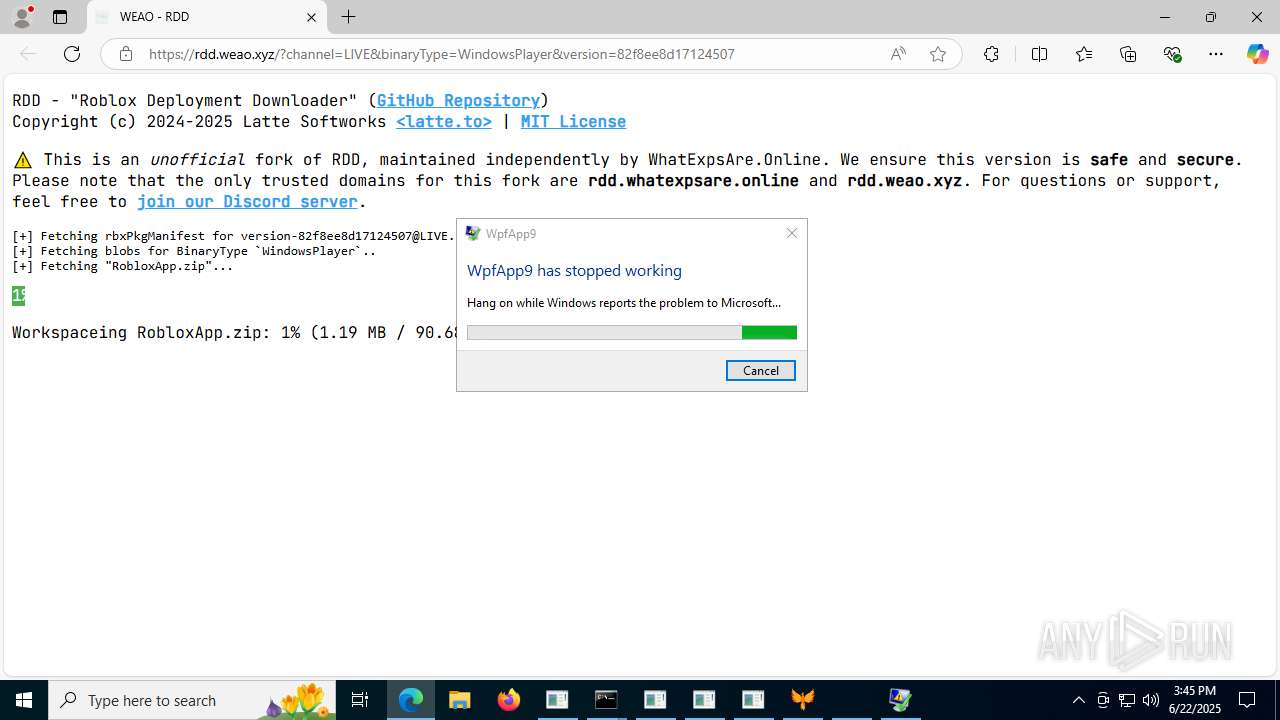
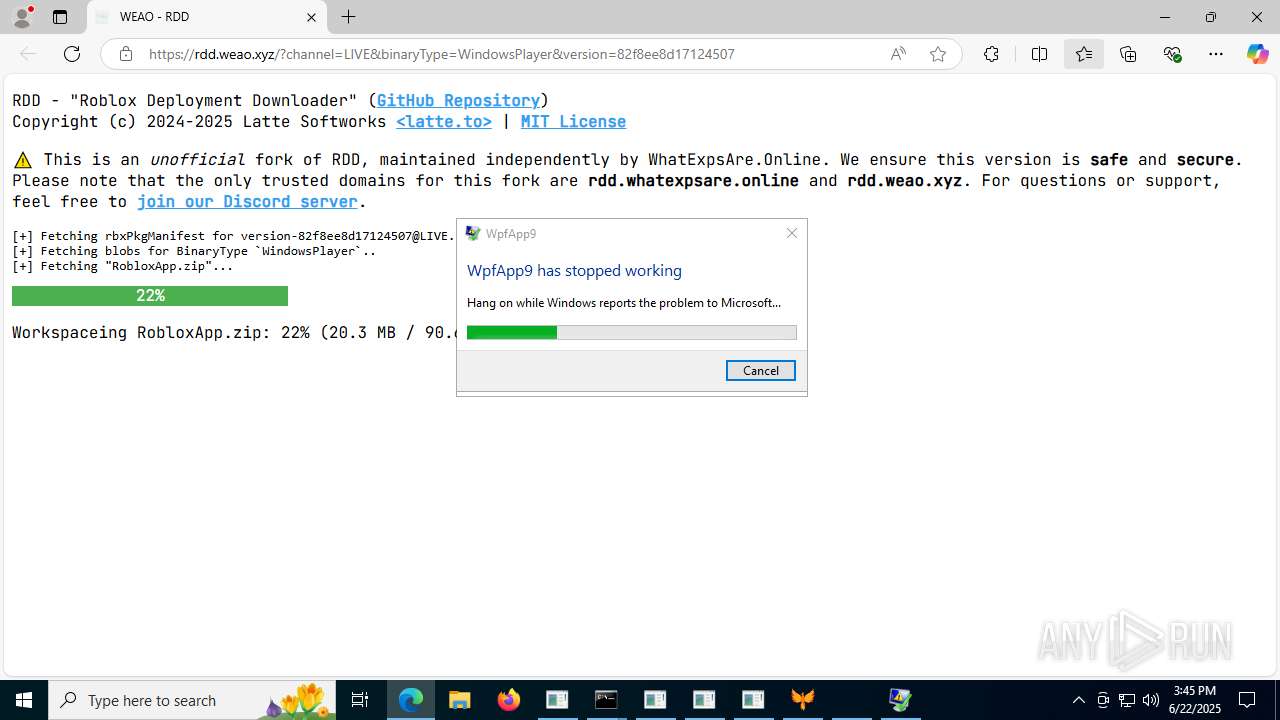
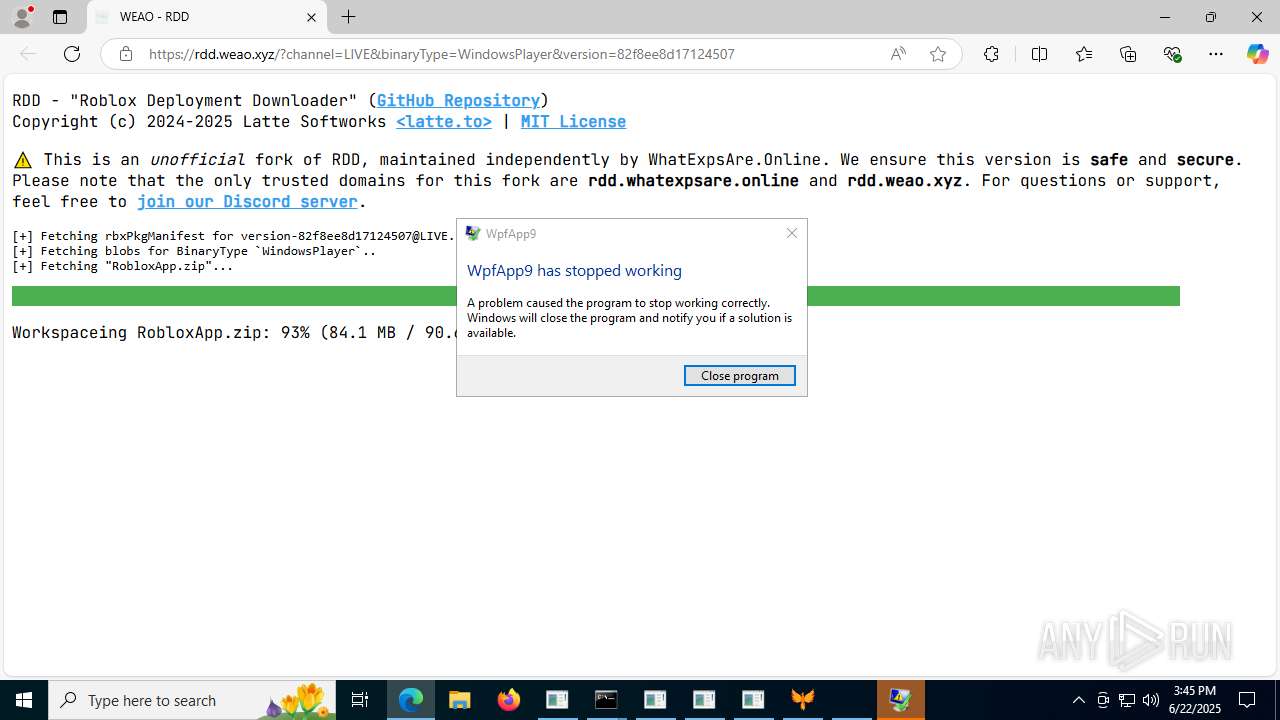
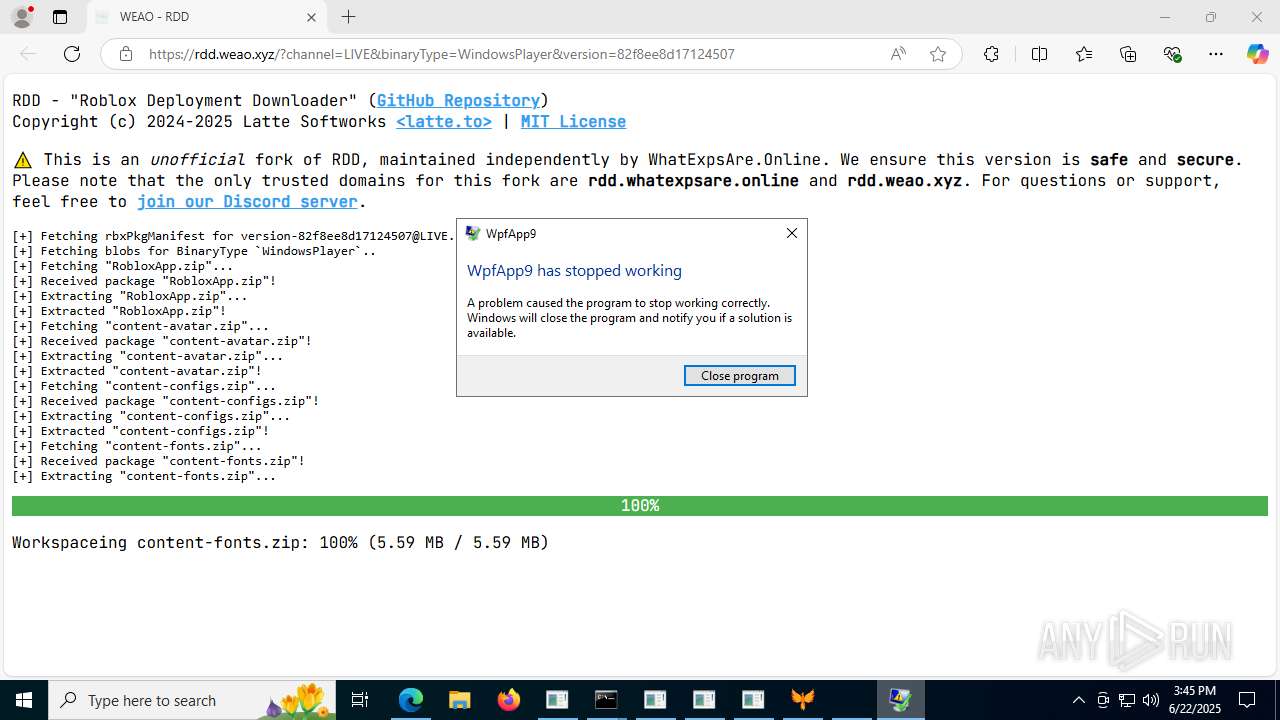
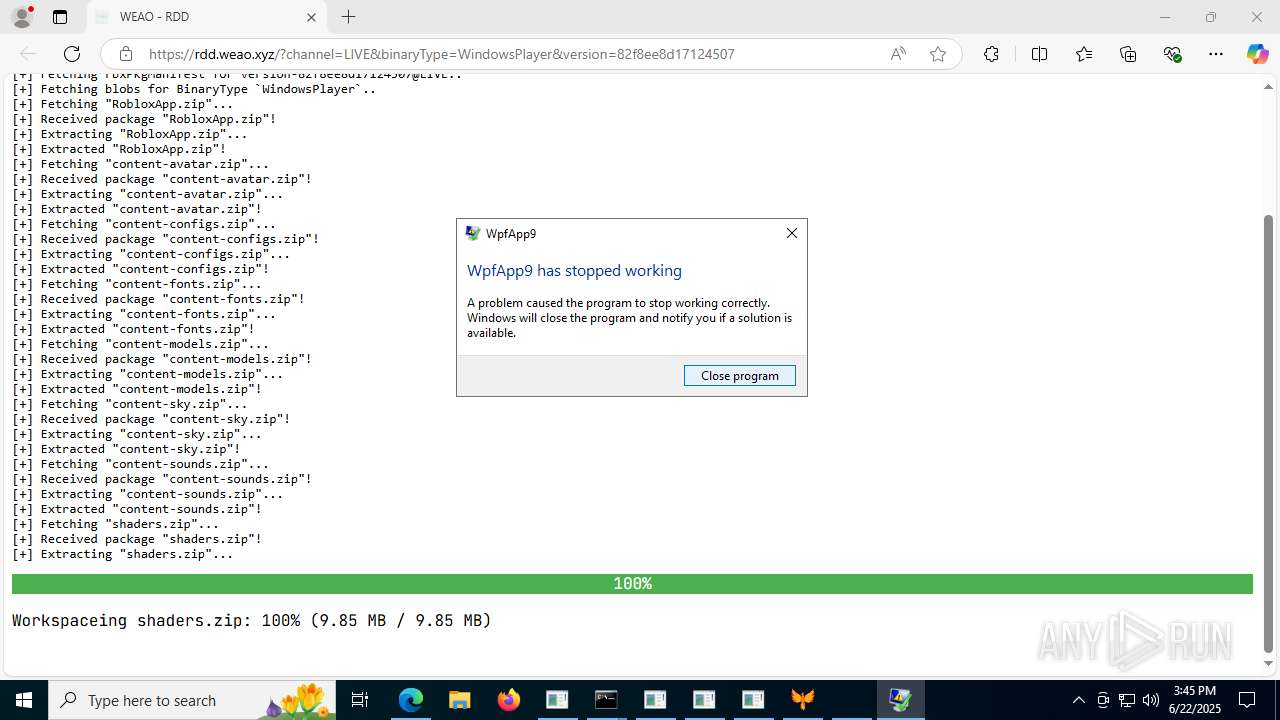
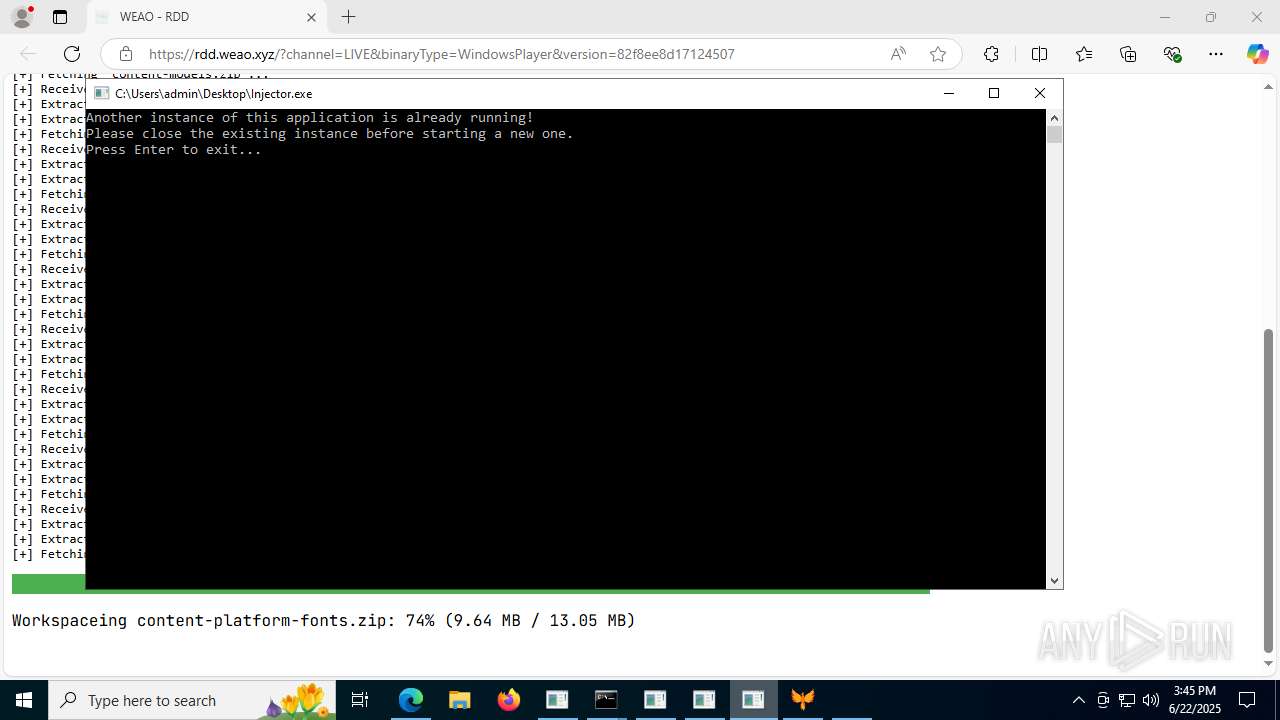
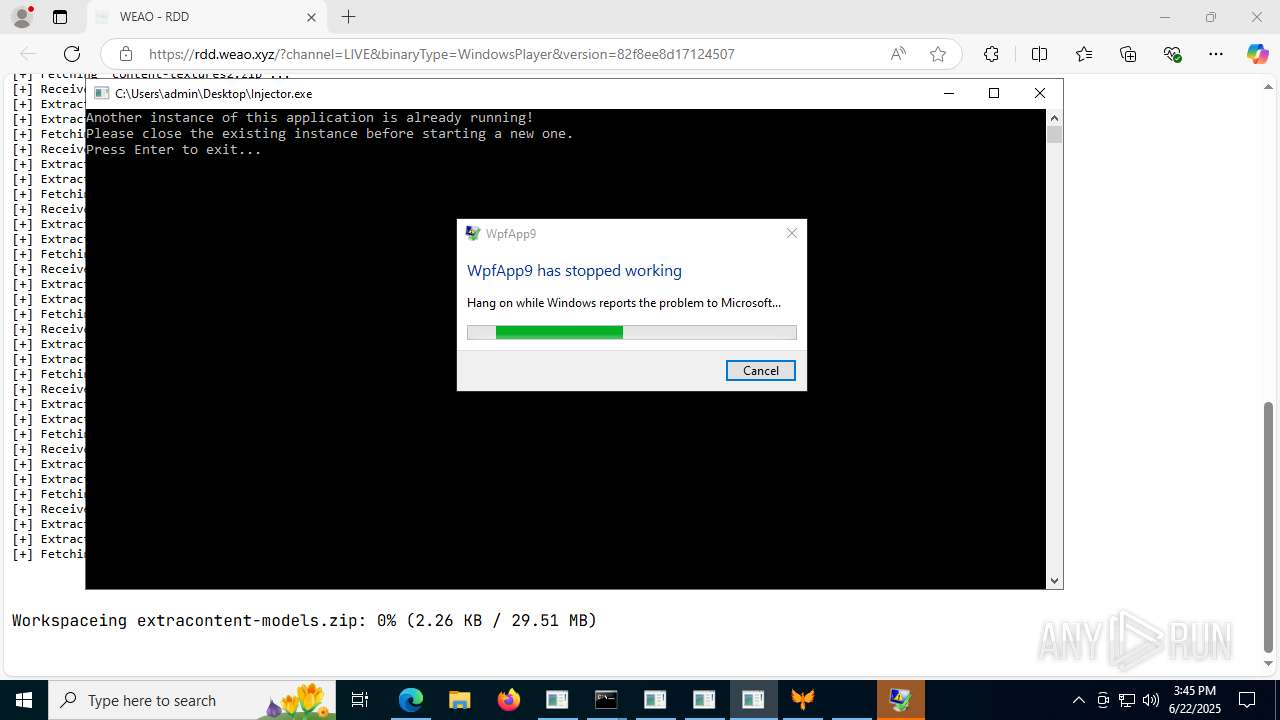
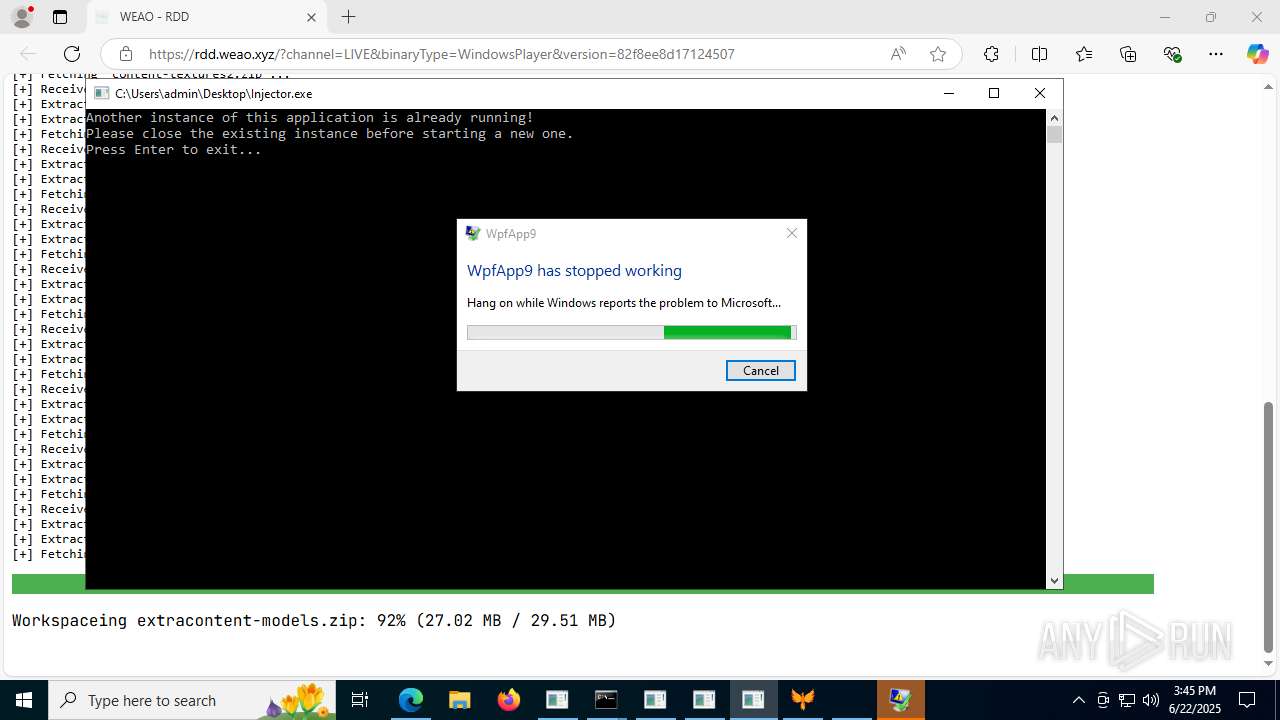
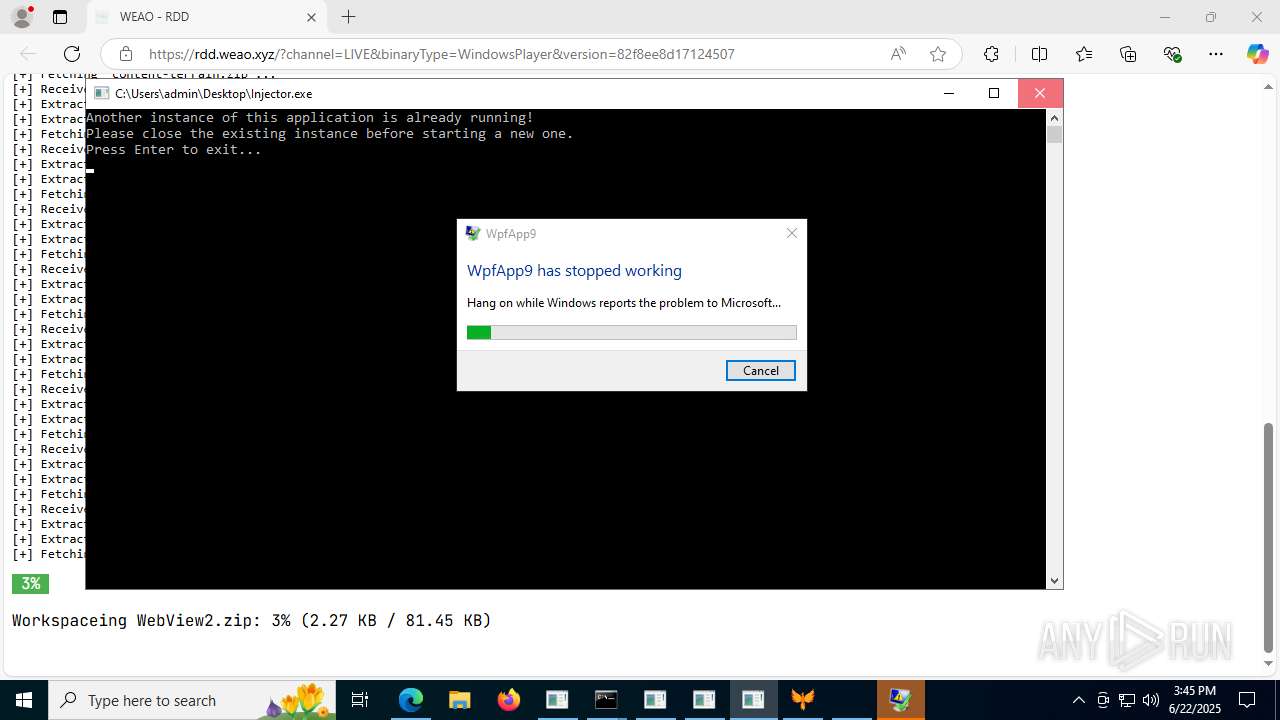
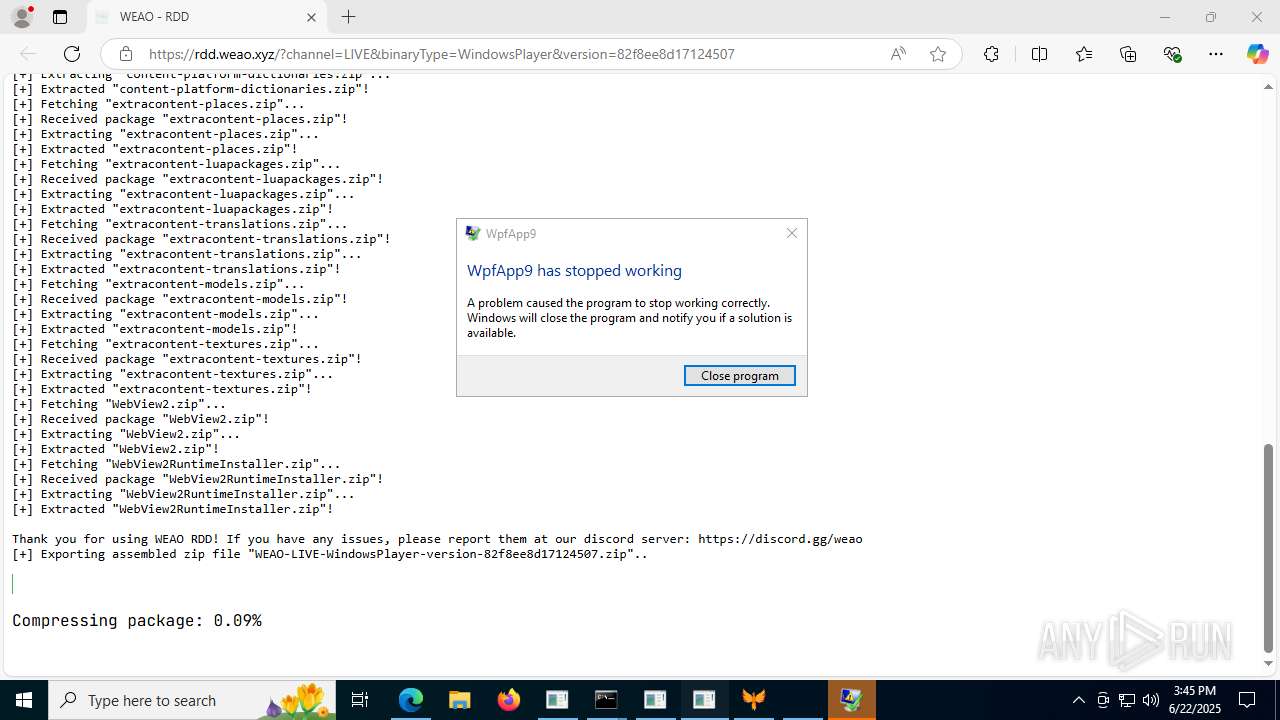
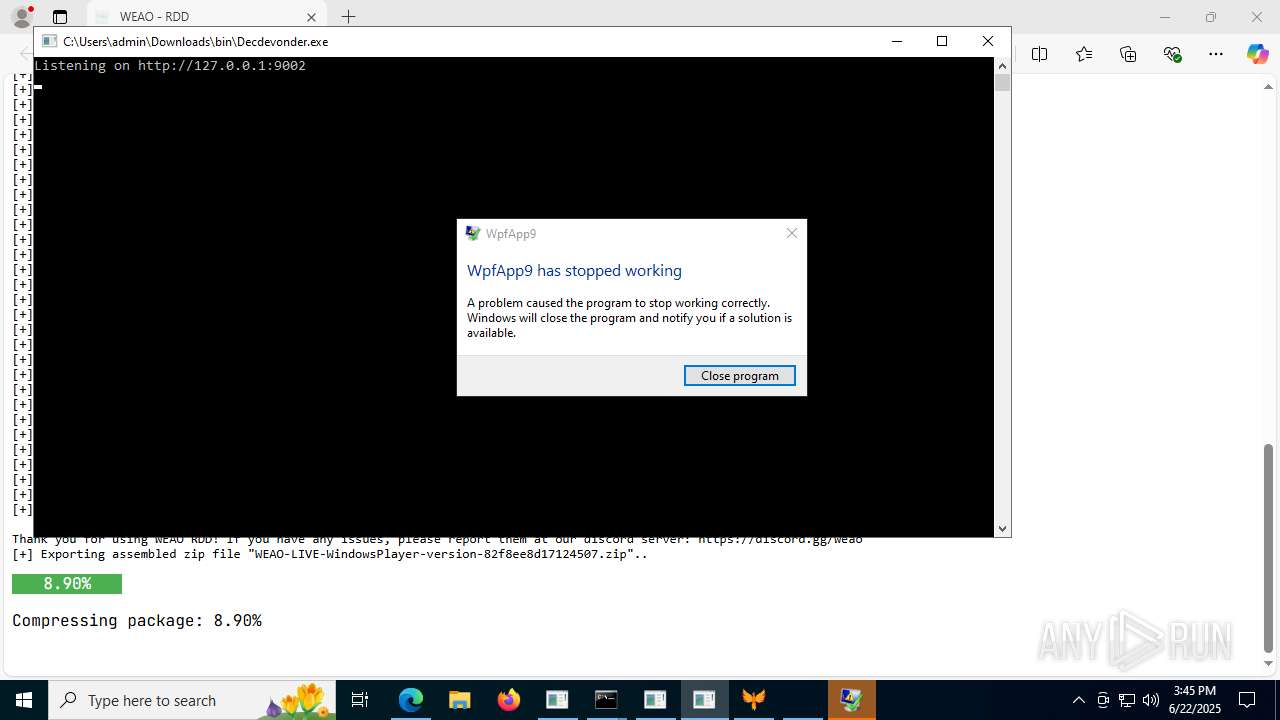
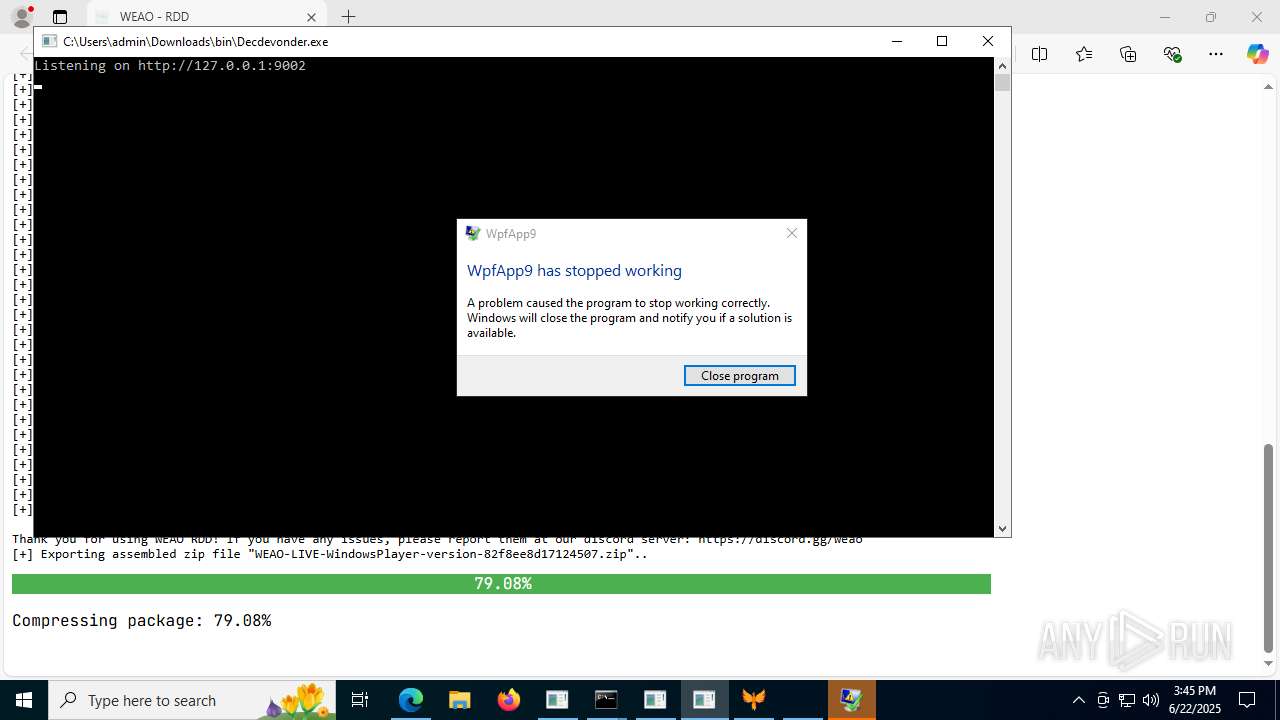
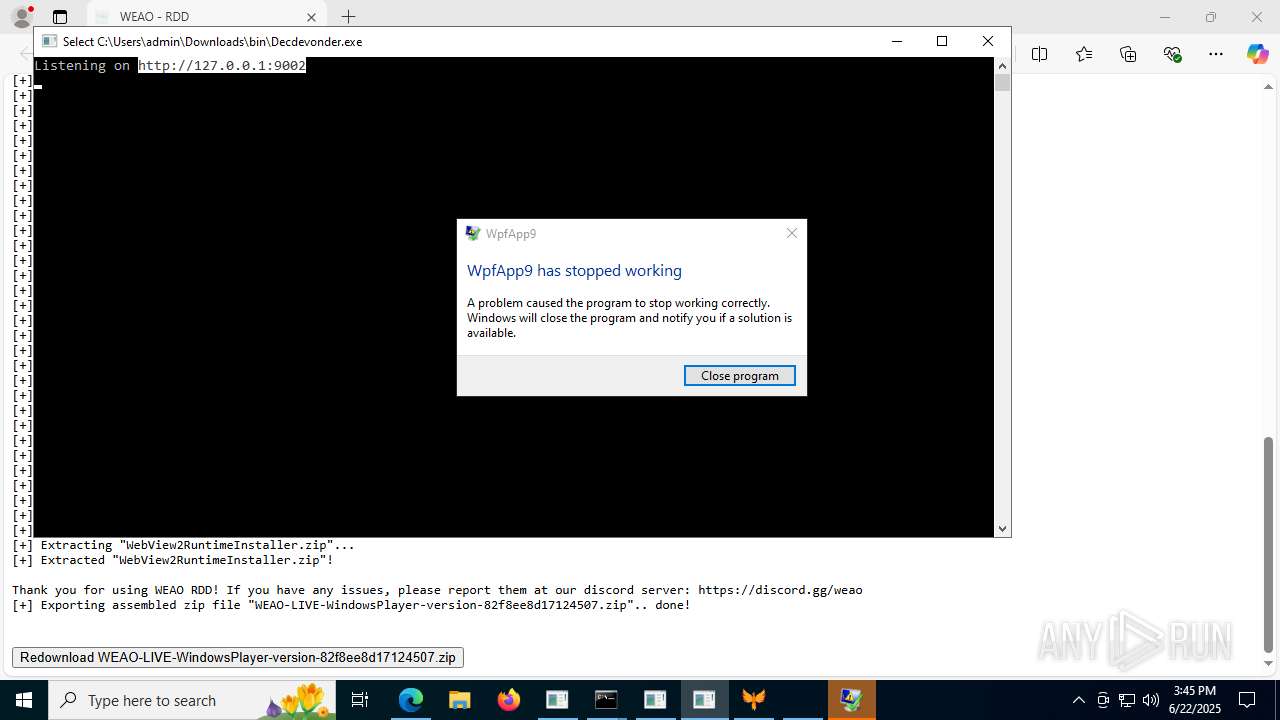
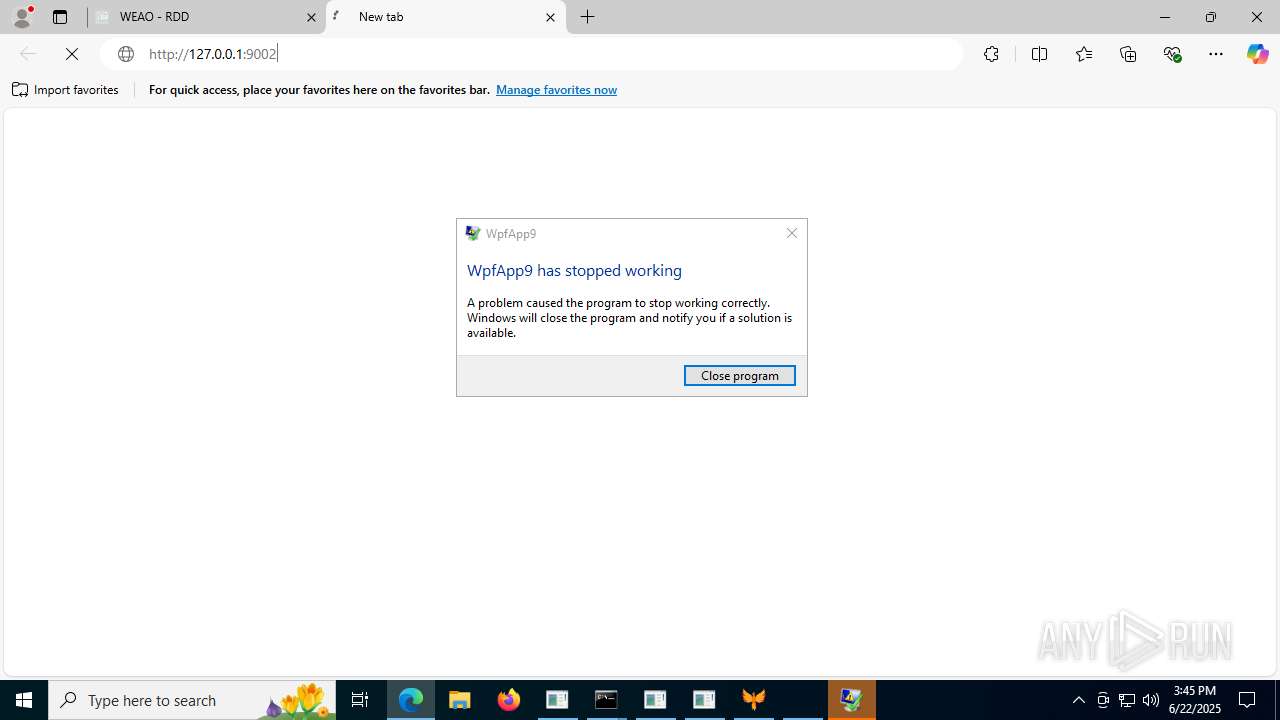
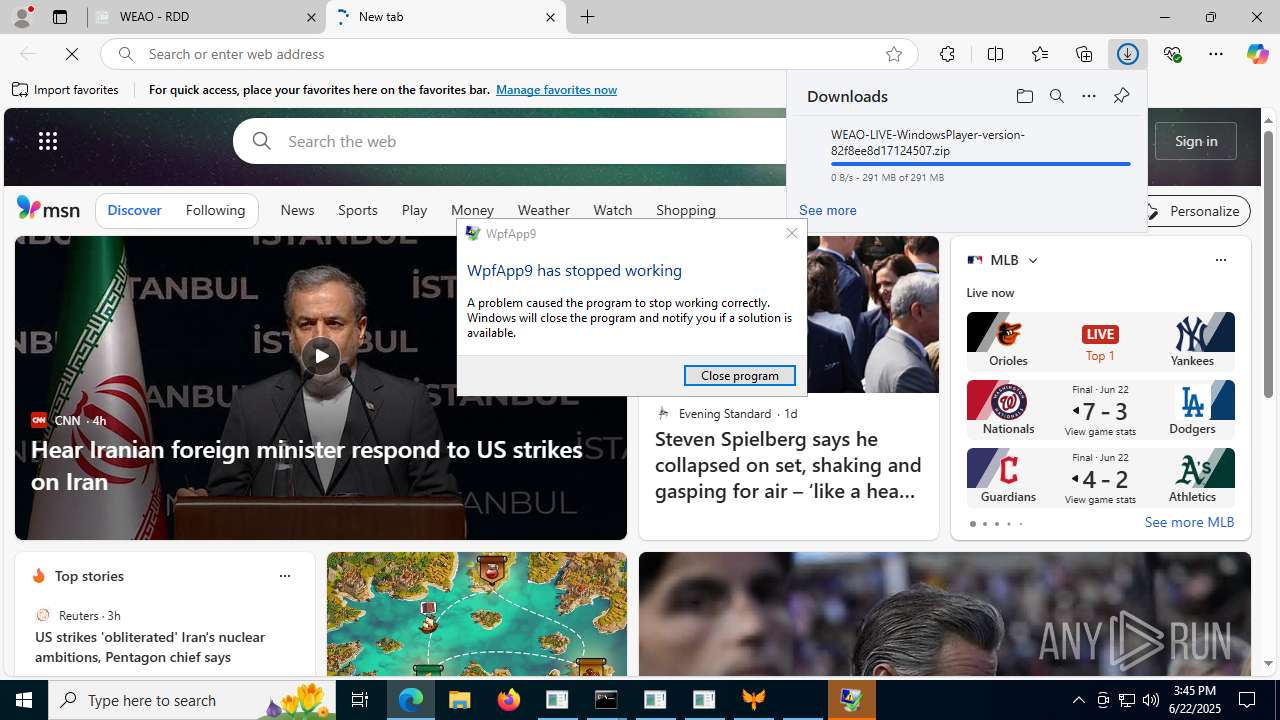
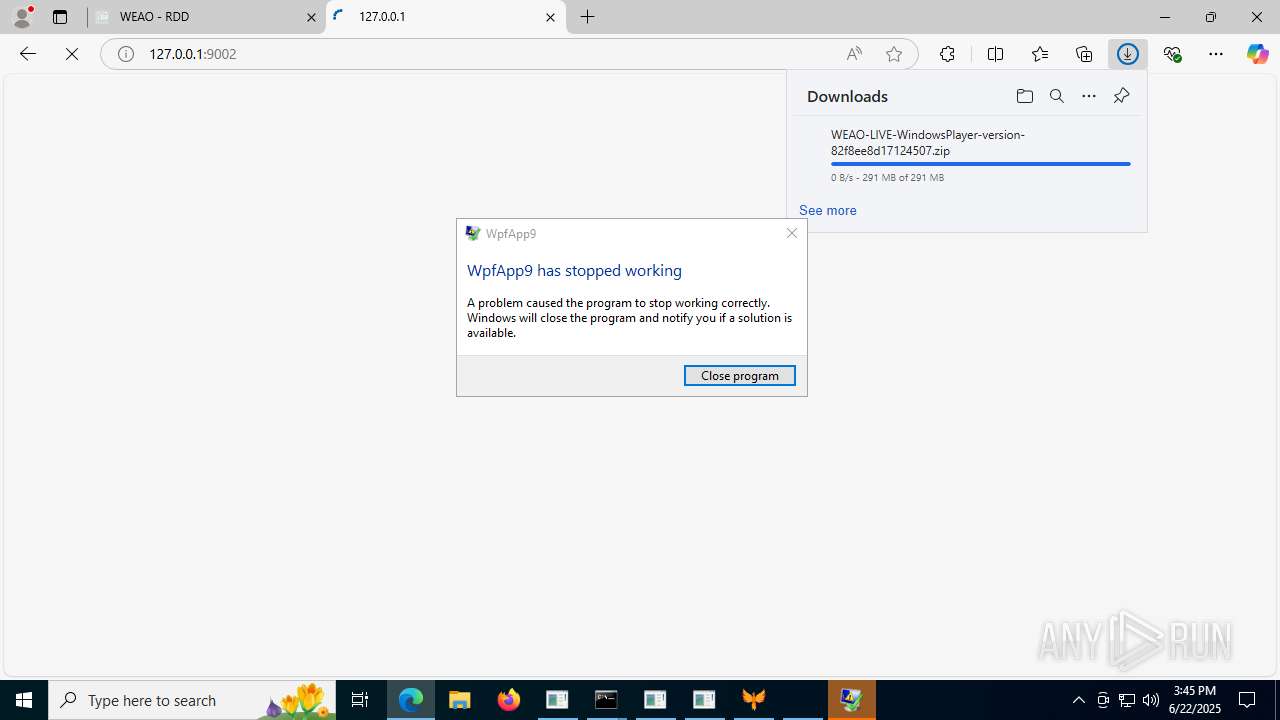
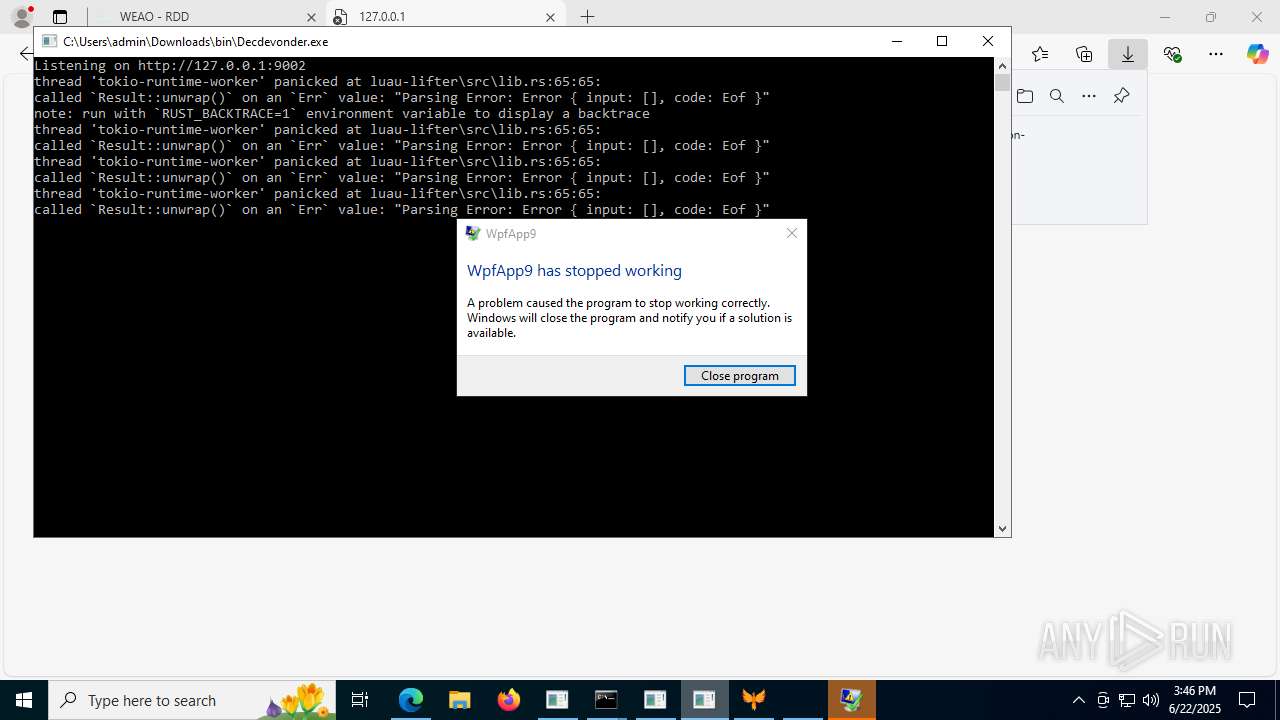
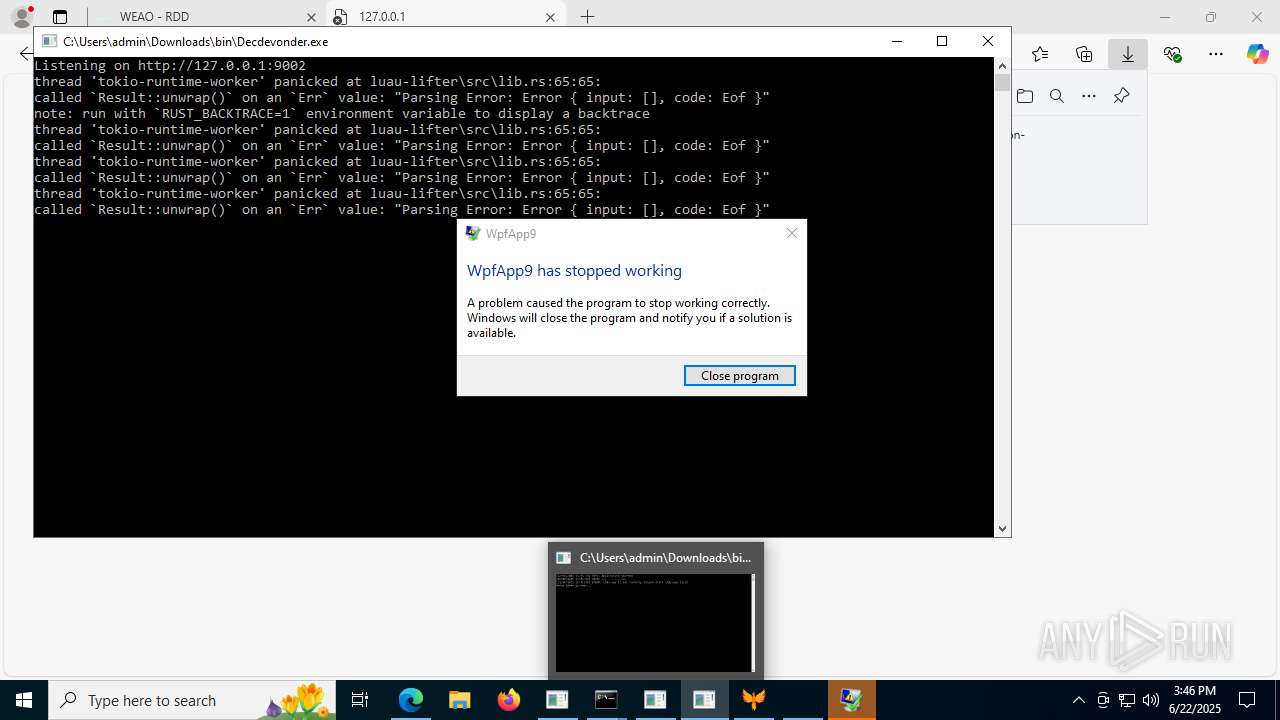
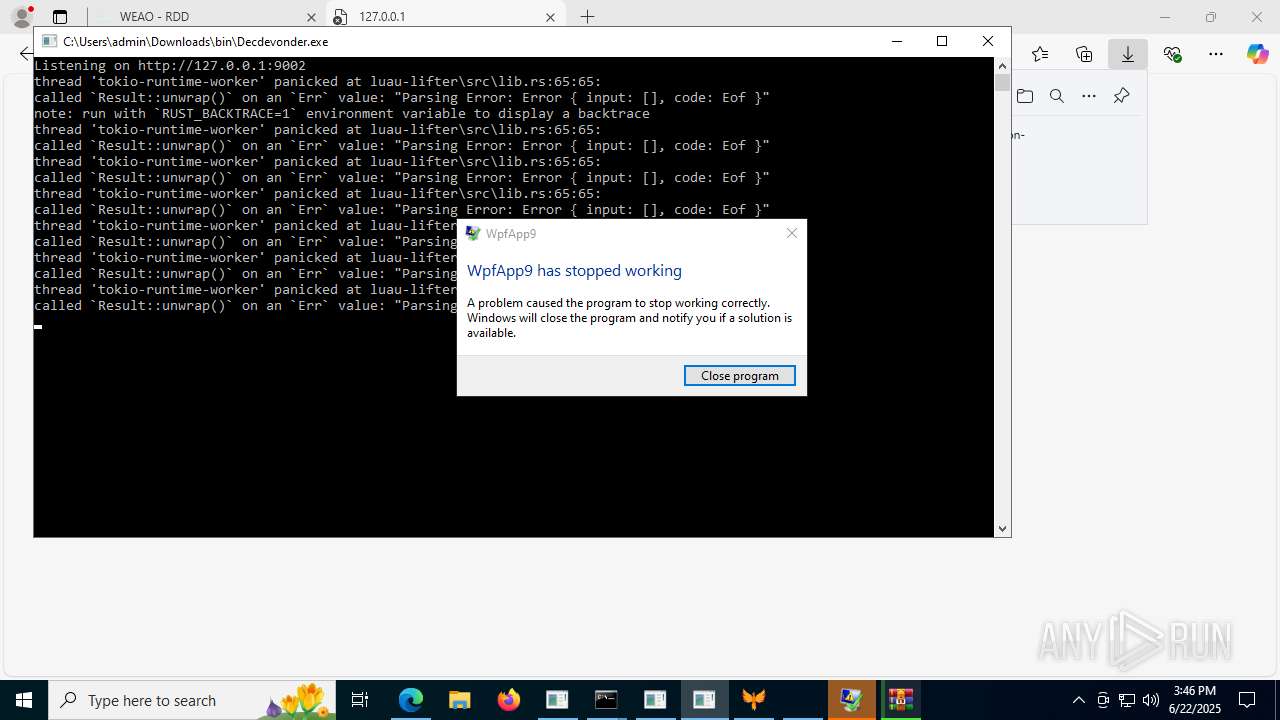
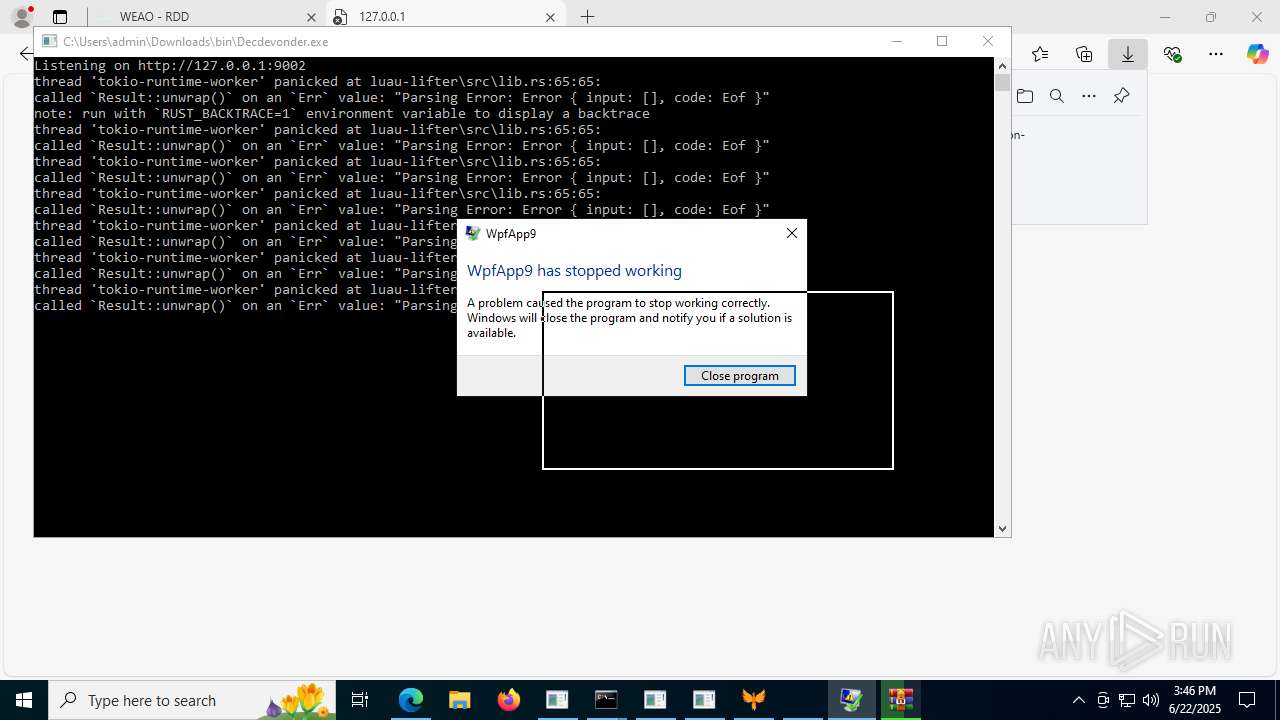
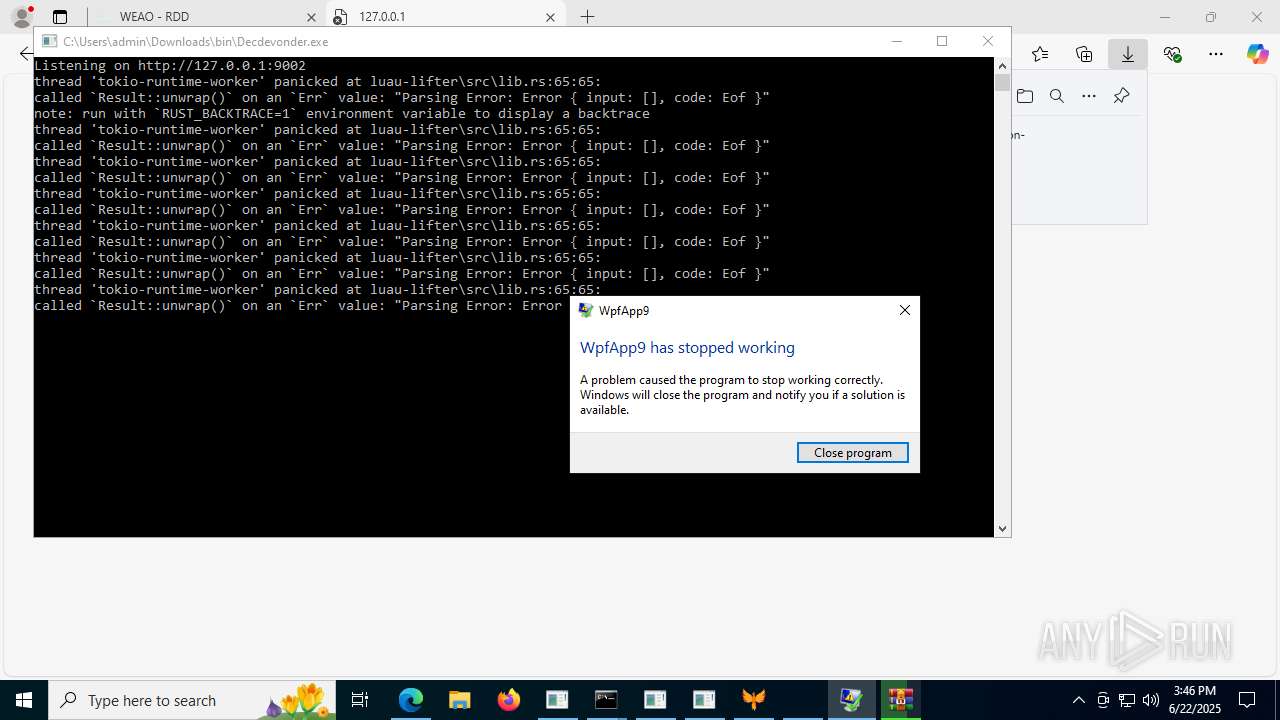
Executes application which crashes
- LX63.exe (PID: 7116)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6776)
Process drops legitimate windows executable
- msedge.exe (PID: 7488)
INFO
Checks supported languages
- LX63Updater.exe (PID: 1324)
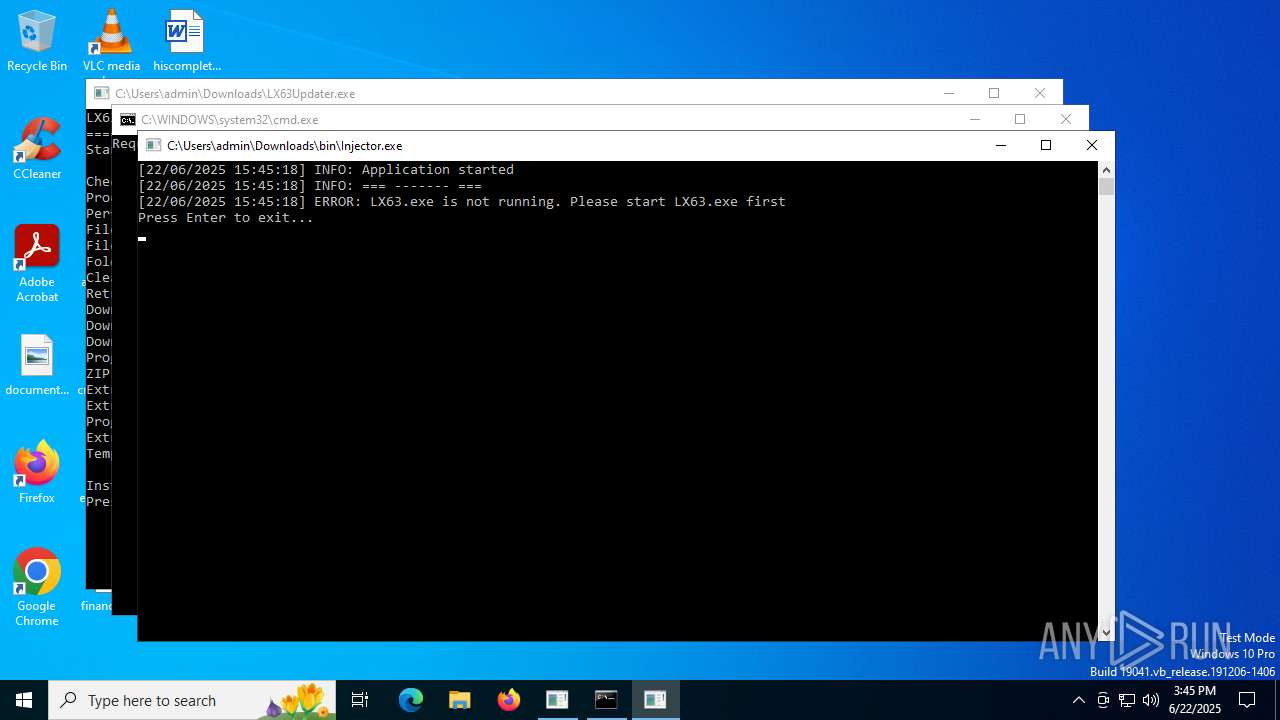
- Injector.exe (PID: 3624)
- LX63.exe (PID: 6292)
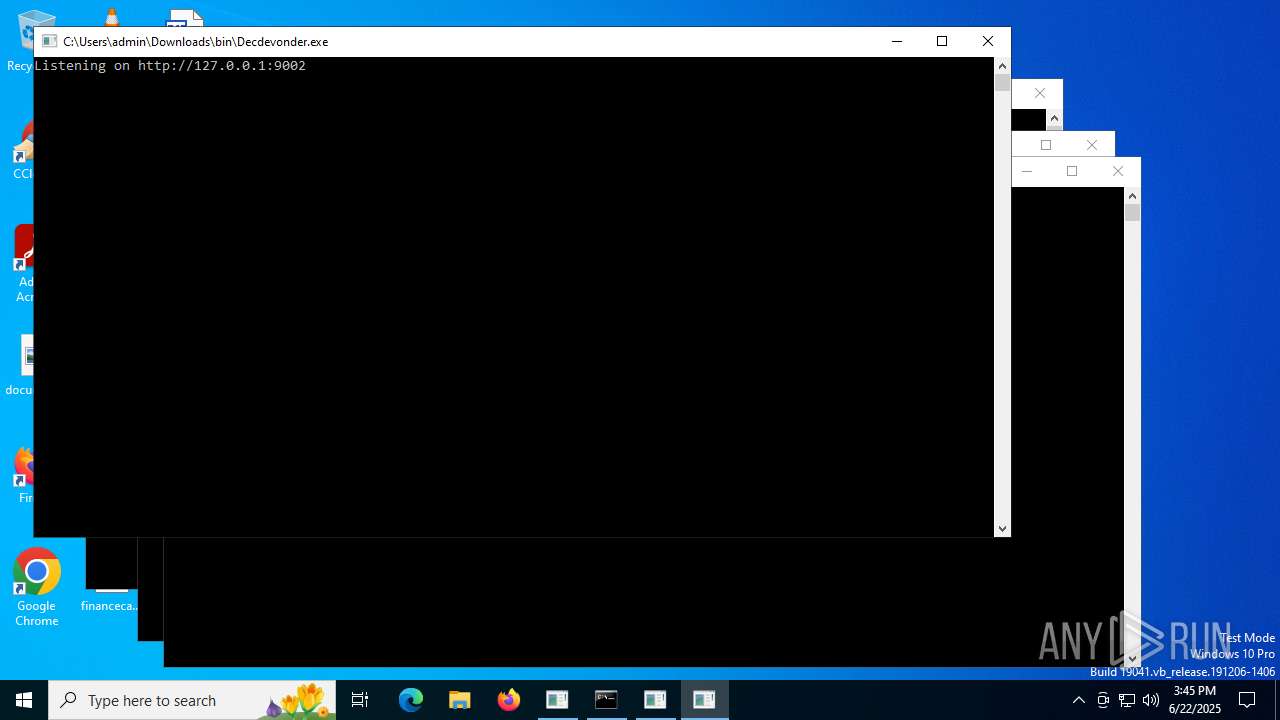
- Decdevonder.exe (PID: 3788)
- Injector.exe (PID: 3820)
- LX63.exe (PID: 7116)
- Decdevonder.exe (PID: 7000)
- identity_helper.exe (PID: 7232)
- WinRAR.exe (PID: 1508)
Reads the computer name
- LX63Updater.exe (PID: 1324)
- LX63.exe (PID: 6292)
- LX63.exe (PID: 7116)
- identity_helper.exe (PID: 7232)
- WinRAR.exe (PID: 1508)
Disables trace logs
- LX63Updater.exe (PID: 1324)
- powershell.exe (PID: 1028)
- LX63.exe (PID: 6292)
- powershell.exe (PID: 2232)
- LX63.exe (PID: 7116)
Reads the machine GUID from the registry
- LX63Updater.exe (PID: 1324)
- LX63.exe (PID: 6292)
- LX63.exe (PID: 7116)
Checks proxy server information
- LX63Updater.exe (PID: 1324)
- powershell.exe (PID: 1028)
- LX63.exe (PID: 6292)
- powershell.exe (PID: 2232)
- LX63.exe (PID: 7116)
- WerFault.exe (PID: 7888)
- WerFault.exe (PID: 3716)
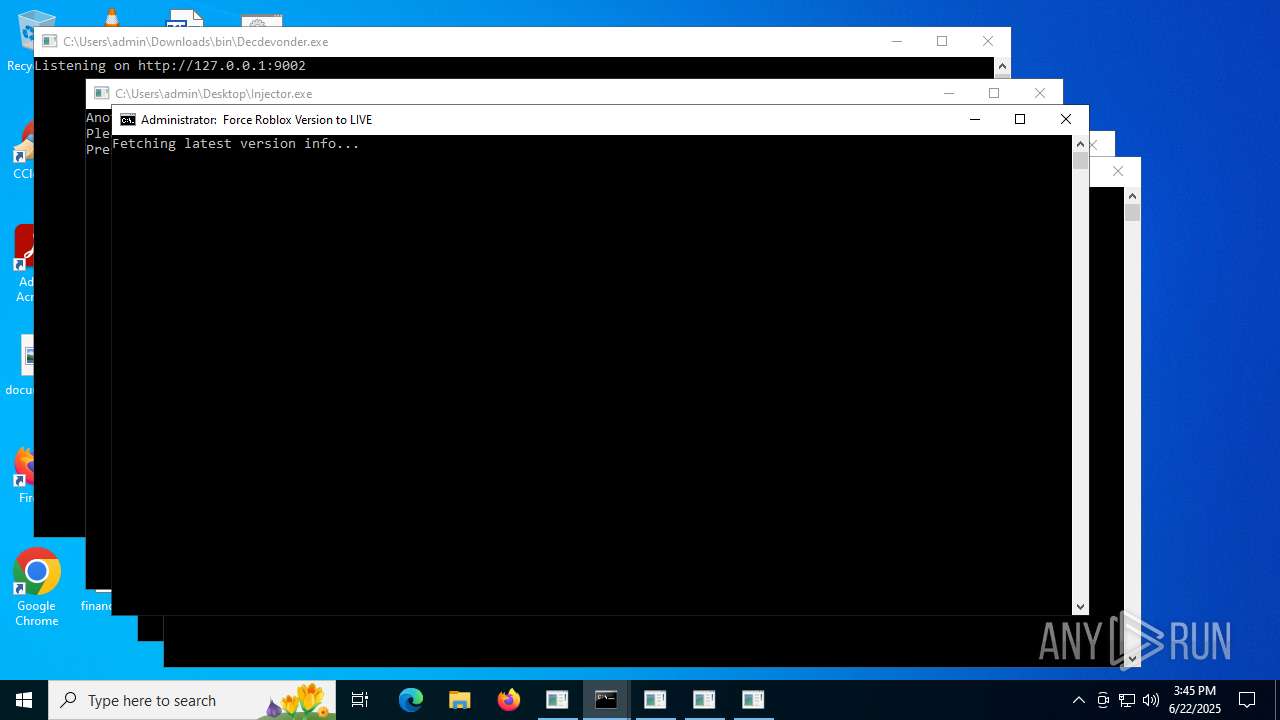
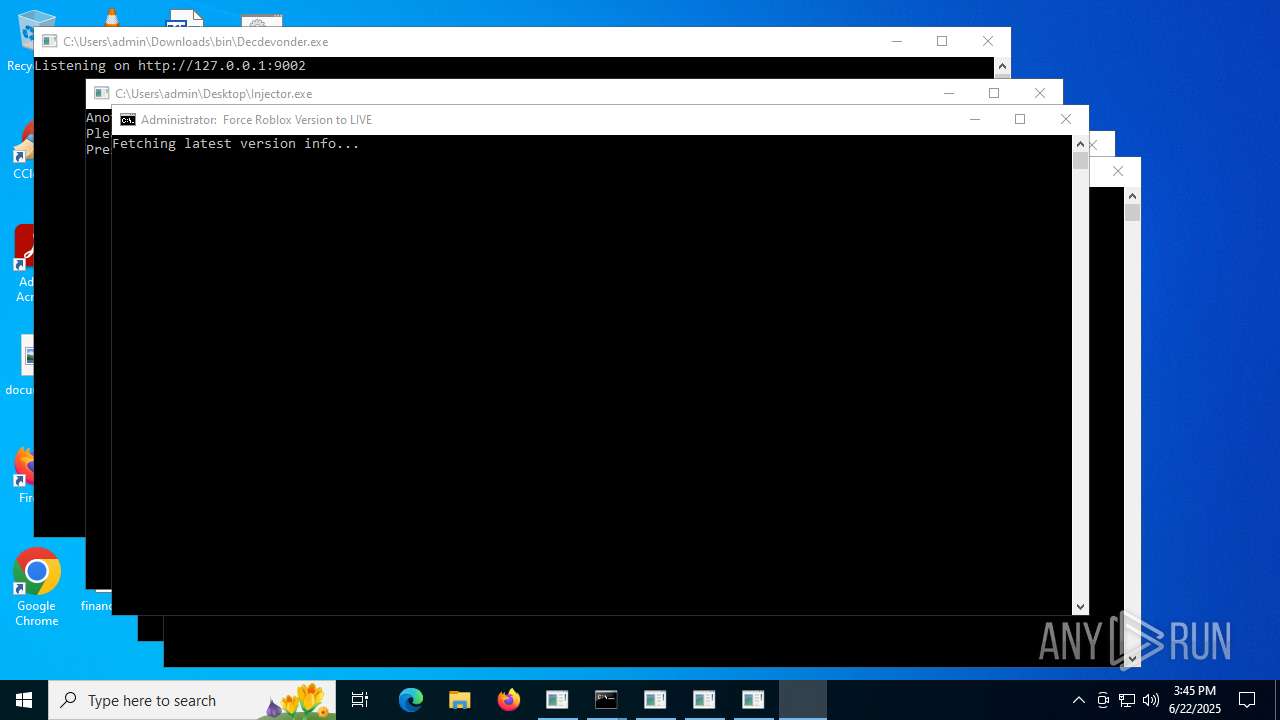
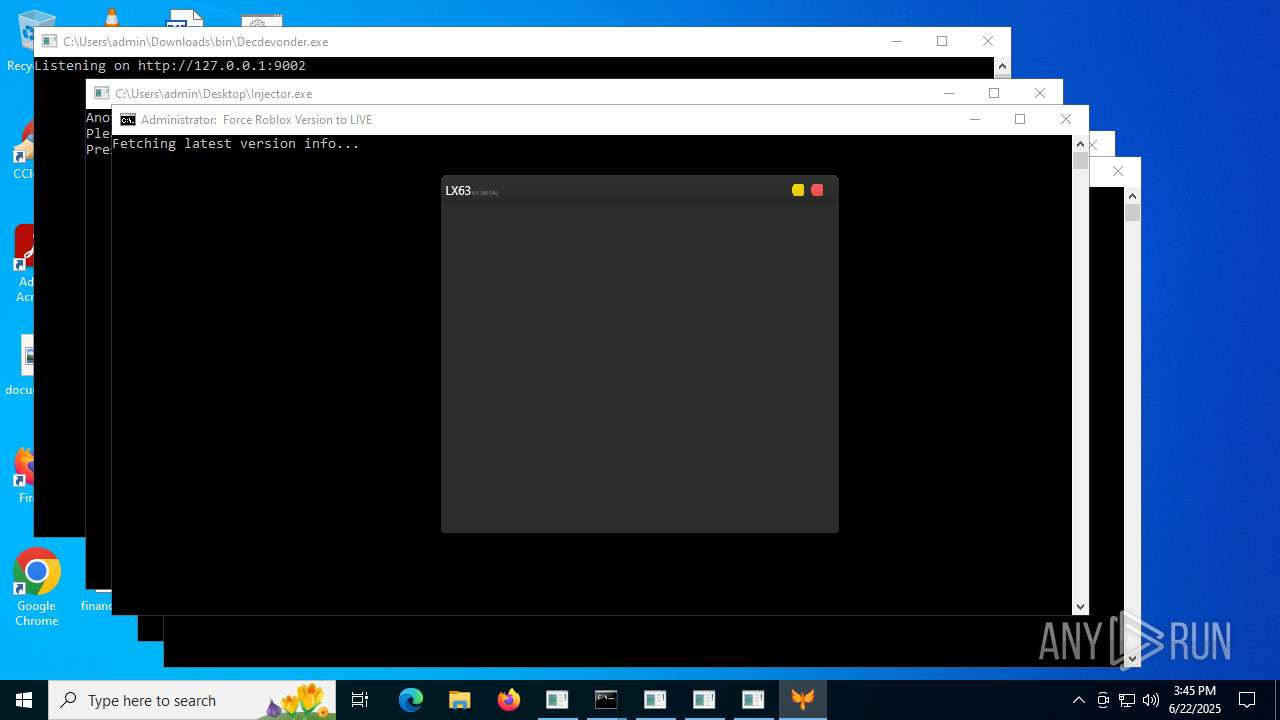
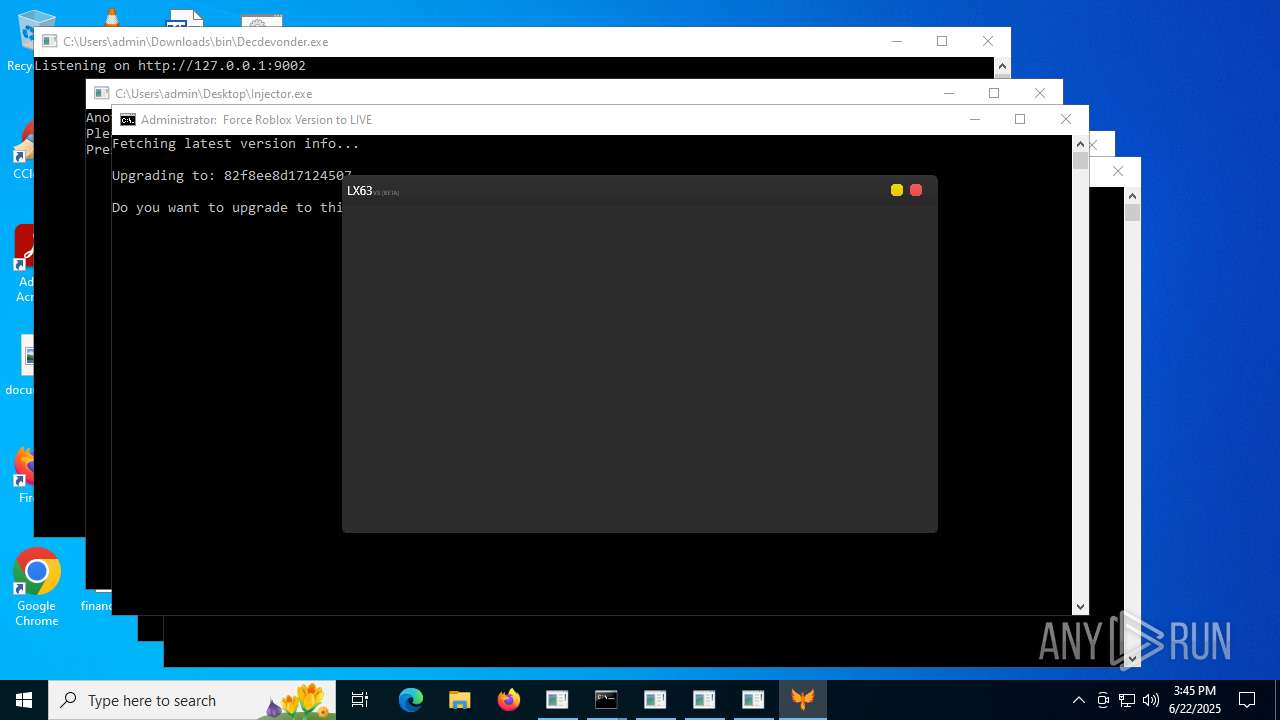
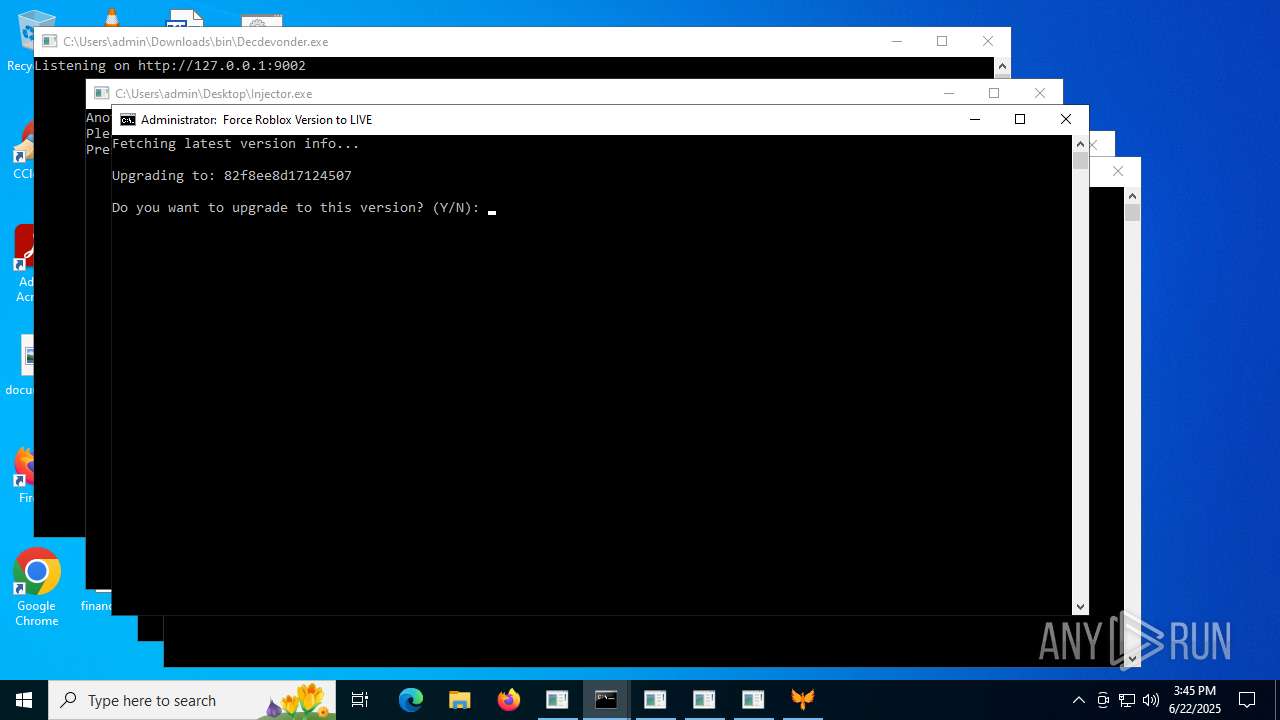
Manual execution by a user
- cmd.exe (PID: 3780)
- Injector.exe (PID: 3624)
- LX63.exe (PID: 6292)
- Decdevonder.exe (PID: 3788)
- cmd.exe (PID: 4236)
- Injector.exe (PID: 3820)
- LX63.exe (PID: 7116)
- msedge.exe (PID: 6460)
Create files in a temporary directory
- LX63Updater.exe (PID: 1324)
- LX63.exe (PID: 6292)
- LX63.exe (PID: 7116)
Reads the software policy settings
- LX63Updater.exe (PID: 1324)
- LX63.exe (PID: 6292)
- LX63.exe (PID: 7116)
- WerFault.exe (PID: 3716)
- WerFault.exe (PID: 7888)
Reads Environment values
- LX63.exe (PID: 6292)
- LX63.exe (PID: 7116)
- identity_helper.exe (PID: 7232)
Application launched itself
- msedge.exe (PID: 6460)
- msedge.exe (PID: 6304)
Creates files or folders in the user directory
- WerFault.exe (PID: 3716)
The sample compiled with english language support
- msedge.exe (PID: 7488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2068:01:27 10:14:48+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 24064 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7cbe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | LX63Installer |
| FileVersion: | 1.0.0.0 |
| InternalName: | LX63Installer.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | LX63Installer.exe |
| ProductName: | LX63Installer |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
238
Monitored processes
96
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5140,i,7090609023626071894,11136117765938630197,262144 --variations-seed-version --mojo-platform-channel-handle=5476 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Decdevonder.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x2f8,0x2fc,0x300,0x2f0,0x308,0x7ffc3fa9f208,0x7ffc3fa9f214,0x7ffc3fa9f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 892 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6776,i,7090609023626071894,11136117765938630197,262144 --variations-seed-version --mojo-platform-channel-handle=6712 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1028 | powershell -NoProfile -Command "$json = (Invoke-WebRequest -Uri 'https://clientsettings.roblox.com/v2/client-version/WindowsPlayer/channel/LIVE').Content | ConvertFrom-Json; $json.clientVersionUpload" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --always-read-main-dll --field-trial-handle=6424,i,7090609023626071894,11136117765938630197,262144 --variations-seed-version --mojo-platform-channel-handle=6588 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\Downloads\LX63Updater.exe" | C:\Users\admin\Downloads\LX63Updater.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: LX63Installer Version: 1.0.0.0 Modules
| |||||||||||||||
| 1328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --always-read-main-dll --field-trial-handle=7264,i,7090609023626071894,11136117765938630197,262144 --variations-seed-version --mojo-platform-channel-handle=7744 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
51 841
Read events
51 777
Write events
64
Delete events
0
Modification events
| (PID) Process: | (1324) LX63Updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\LX63Updater_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1324) LX63Updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\LX63Updater_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1324) LX63Updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\LX63Updater_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1324) LX63Updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\LX63Updater_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1324) LX63Updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\LX63Updater_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1324) LX63Updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\LX63Updater_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1324) LX63Updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\LX63Updater_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1324) LX63Updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\LX63Updater_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1324) LX63Updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\LX63Updater_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1324) LX63Updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\LX63Updater_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
24
Suspicious files
559
Text files
343
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1324 | LX63Updater.exe | C:\Users\admin\AppData\Local\Temp\tmp6522.tmp.zip | compressed | |
MD5:1FDEAB6DE33BD191D9739FC682810BD0 | SHA256:794AD1936ABA1D2A7F9CD81FF61235B49B4D965FE7DCEB043761625C2C5F7314 | |||
| 1324 | LX63Updater.exe | C:\Users\admin\Downloads\bin\LX63.dll | executable | |
MD5:D0E622CD19BC3CC1092788F5C5A962C4 | SHA256:4D622536BBEEE494B4DE7FC6A7CF4EB952BCDDDCCAC9B3467DFD33C12BA28DCF | |||
| 1324 | LX63Updater.exe | C:\Users\admin\Downloads\bin\Decdevonder.exe | executable | |
MD5:BF47609C2B066D057EBF81D4C280D603 | SHA256:36B045A24E0E854125D7CC2434F7971BEB5C19F045BFA8857433E232414397B9 | |||
| 1560 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:FBB13FCE6D72A208CF3A285DE9E76206 | SHA256:581F22244BDF4866A0D3A5F6D656B59CE6CCEFA0F28BC1F612E38C476F20919F | |||
| 1560 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_30qn0xmt.cva.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1324 | LX63Updater.exe | C:\Users\admin\Downloads\bin\Injector.exe | executable | |
MD5:C47B0659F84AB348BAC26A5005ED19E7 | SHA256:2F433BD0787B7C0B250C4EB09098A4251324D088CDACBB9140E62DF56A9A3B30 | |||
| 1324 | LX63Updater.exe | C:\Users\admin\Downloads\LX63.exe | executable | |
MD5:5F004EFD6B326DC525B5C5CAD6803F81 | SHA256:A052FD7DBA67842E3298DB30C288855304F2B23A7120A5AB7F2A874B8AB8ED21 | |||
| 1028 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rv4iw5ti.a2a.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3716 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC46A.tmp.WERInternalMetadata.xml | xml | |
MD5:0F8375652FB2D9B4138447DDC4F46394 | SHA256:7210635C94CAF4BE1B7C551DB1D3848BD20FCE0CEF1D9C84E05888849411816F | |||
| 1560 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yrzpc2h0.2lf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
97
DNS requests
87
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 184.24.77.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1200 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3676 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3676 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3716 | WerFault.exe | GET | 200 | 184.24.77.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3716 | WerFault.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7488 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:22cuUk-MeckIye65XtJhAYkWaDcouYTtADYZj0JguP4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2228 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1324 | LX63Updater.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
1324 | LX63Updater.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1200 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1200 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
github.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
clientsettings.roblox.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |