| File name: | dControl.exe |
| Full analysis: | https://app.any.run/tasks/024ee23c-e07f-4392-a10a-078eb9a06472 |
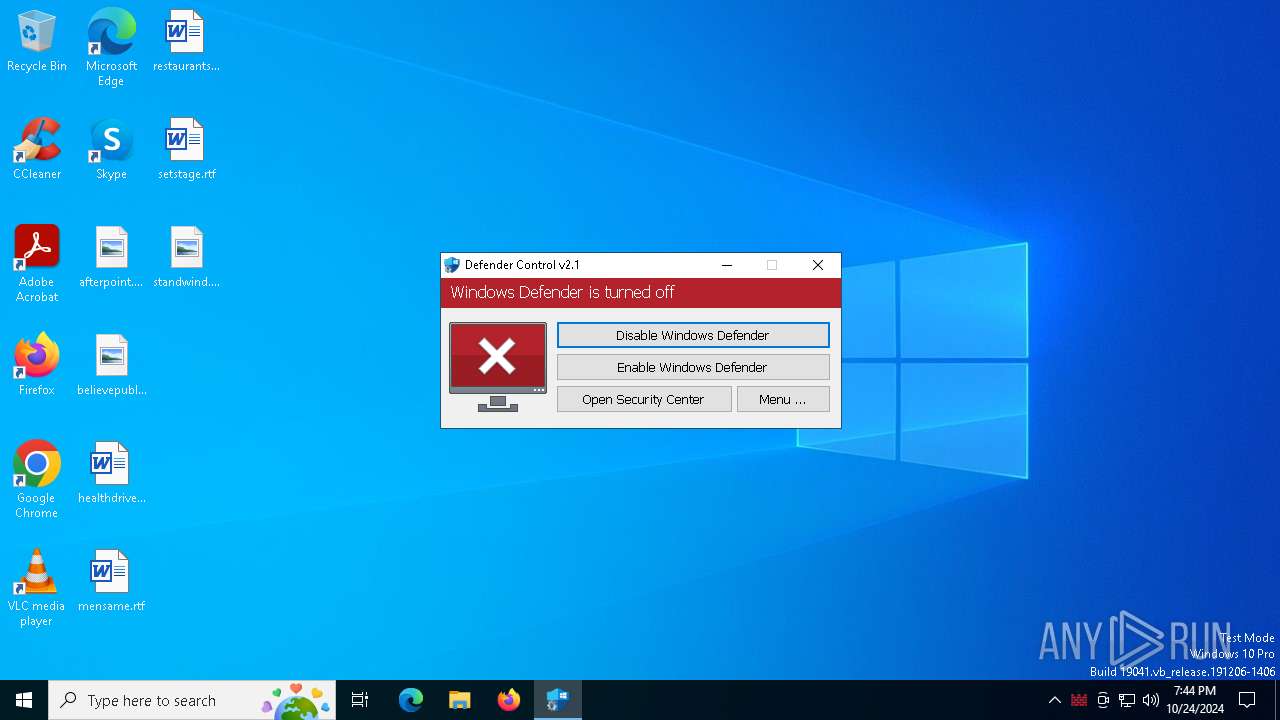
| Verdict: | Malicious activity |
| Analysis date: | October 24, 2024, 19:44:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 58008524A6473BDF86C1040A9A9E39C3 |
| SHA1: | CB704D2E8DF80FD3500A5B817966DC262D80DDB8 |
| SHA256: | 1EF6C1A4DFDC39B63BFE650CA81AB89510DE6C0D3D7C608AC5BE80033E559326 |
| SSDEEP: | 6144:Vzv+kSn74iCmfianQGDM3OXTWRDy9GYQDUmJFXIXHrsUBnBTF8JJCYrYNsQJzfgu:Vzcn7EanlQiWtYhmJFSwUBLcQZfgiD |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- dControl.exe (PID: 5400)
- dControl.exe (PID: 2184)
INFO
UPX packer has been detected
- dControl.exe (PID: 5516)
The process uses AutoIt
- dControl.exe (PID: 5516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (28.6) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (28) |
| .exe | | | Win32 EXE Yoda's Crypter (27.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.8) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:12:23 10:59:31+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 270336 |
| InitializedDataSize: | 61440 |
| UninitializedDataSize: | 503808 |
| EntryPoint: | 0xbd650 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.0.0 |
| ProductVersionNumber: | 2.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 2.1.0.0 |
| Comments: | dControl v2.1 |
| FileDescription: | dControl v2.1 |
| LegalCopyright: | Copyright © 2015-2022 www.sordum.org All Rights Reserved. |
| CompanyName: | www.sordum.org |
| ProductVersion: | 2.1.0.0 |
| OriginalFileName: | dControl.exe |
| Coder: | By BlueLife |
Total processes
140
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2184 | "C:\Users\admin\AppData\Local\Temp\dControl.exe" | C:\Users\admin\AppData\Local\Temp\dControl.exe | explorer.exe | ||||||||||||
User: admin Company: www.sordum.org Integrity Level: HIGH Description: dControl v2.1 Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 4312 | "C:\Users\admin\AppData\Local\Temp\dControl.exe" | C:\Users\admin\AppData\Local\Temp\dControl.exe | — | explorer.exe | |||||||||||
User: admin Company: www.sordum.org Integrity Level: MEDIUM Description: dControl v2.1 Exit code: 3221226540 Version: 2.1.0.0 Modules
| |||||||||||||||
| 5400 | C:\Users\admin\AppData\Local\Temp\dControl.exe | C:\Users\admin\AppData\Local\Temp\dControl.exe | dControl.exe | ||||||||||||
User: SYSTEM Company: www.sordum.org Integrity Level: SYSTEM Description: dControl v2.1 Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 5516 | "C:\Users\admin\AppData\Local\Temp\dControl.exe" /TI | C:\Users\admin\AppData\Local\Temp\dControl.exe | dControl.exe | ||||||||||||
User: SYSTEM Company: www.sordum.org Integrity Level: SYSTEM Description: dControl v2.1 Version: 2.1.0.0 Modules
| |||||||||||||||
Total events
334
Read events
334
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
9
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | dControl.exe | C:\Users\admin\AppData\Local\Temp\autB4E1.tmp | binary | |
MD5:9D5A0EF18CC4BB492930582064C5330F | SHA256:8F5BBCC572BC62FEB13A669F856D21886A61888FD6288AFD066272A27EA79BB3 | |||
| 2184 | dControl.exe | C:\Users\admin\AppData\Local\Temp\autB503.tmp | binary | |
MD5:ECFFD3E81C5F2E3C62BCDC122442B5F2 | SHA256:9874AB363B07DCC7E9CD6022A380A64102C1814343642295239A9F120CB941C5 | |||
| 5516 | dControl.exe | C:\Windows\Temp\5x5x1u6r.tmp | text | |
MD5:E00DCC76E4DCD90994587375125DE04B | SHA256:C8709F5A8B971D136E2273D66E65449791CA8EBA1F47DD767733EA52EE635447 | |||
| 2184 | dControl.exe | C:\Users\admin\AppData\Local\Temp\2g1j8k4y.tmp | text | |
MD5:E00DCC76E4DCD90994587375125DE04B | SHA256:C8709F5A8B971D136E2273D66E65449791CA8EBA1F47DD767733EA52EE635447 | |||
| 5516 | dControl.exe | C:\Windows\Temp\autB762.tmp | binary | |
MD5:9D5A0EF18CC4BB492930582064C5330F | SHA256:8F5BBCC572BC62FEB13A669F856D21886A61888FD6288AFD066272A27EA79BB3 | |||
| 5400 | dControl.exe | C:\Windows\Temp\autB688.tmp | binary | |
MD5:EFE44D9F6E4426A05E39F99AD407D3E7 | SHA256:5EA3B26C6B1B71EDAEF17CE365D50BE963AE9F4CB79B39EC723FE6E9E4054366 | |||
| 5400 | dControl.exe | C:\Windows\Temp\autB678.tmp | binary | |
MD5:9D5A0EF18CC4BB492930582064C5330F | SHA256:8F5BBCC572BC62FEB13A669F856D21886A61888FD6288AFD066272A27EA79BB3 | |||
| 2184 | dControl.exe | C:\Users\admin\AppData\Local\Temp\autB4F2.tmp | binary | |
MD5:EFE44D9F6E4426A05E39F99AD407D3E7 | SHA256:5EA3B26C6B1B71EDAEF17CE365D50BE963AE9F4CB79B39EC723FE6E9E4054366 | |||
| 5516 | dControl.exe | C:\Windows\Temp\autB773.tmp | binary | |
MD5:EFE44D9F6E4426A05E39F99AD407D3E7 | SHA256:5EA3B26C6B1B71EDAEF17CE365D50BE963AE9F4CB79B39EC723FE6E9E4054366 | |||
| 5516 | dControl.exe | C:\Windows\Temp\autB783.tmp | binary | |
MD5:ECFFD3E81C5F2E3C62BCDC122442B5F2 | SHA256:9874AB363B07DCC7E9CD6022A380A64102C1814343642295239A9F120CB941C5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
37
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3788 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6156 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6156 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4476 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3952 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 2.23.209.154:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |