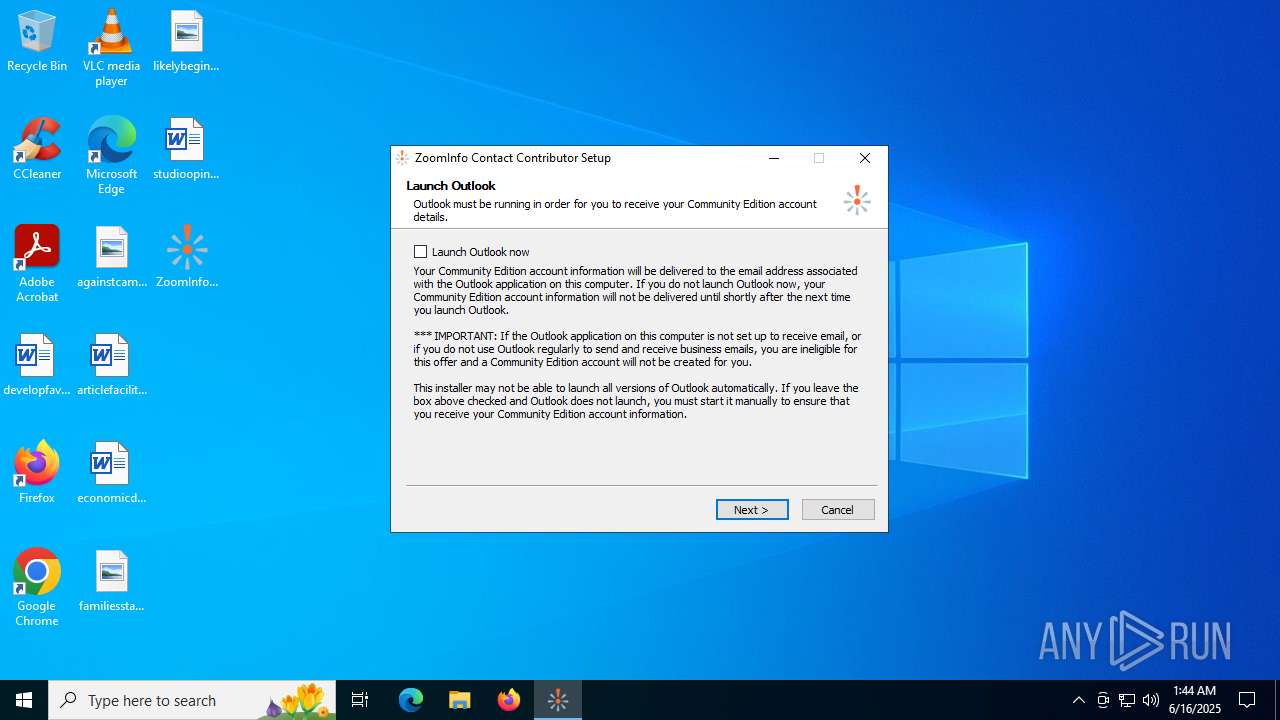
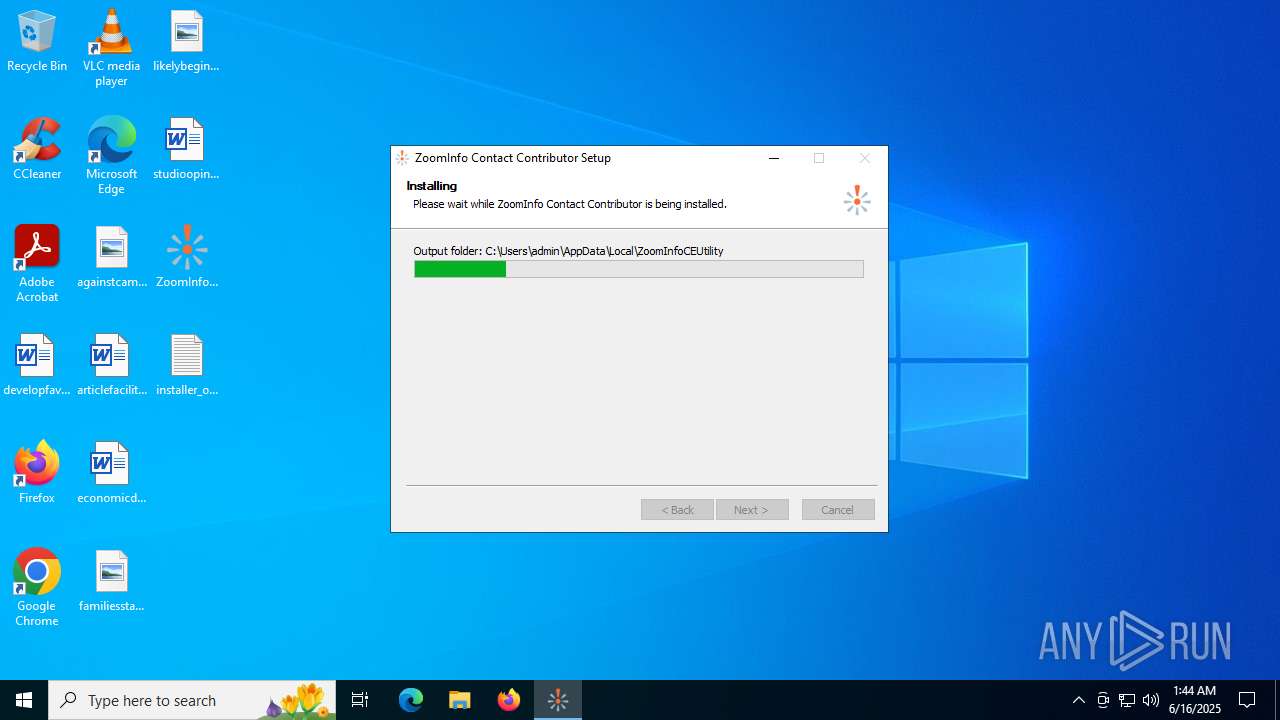
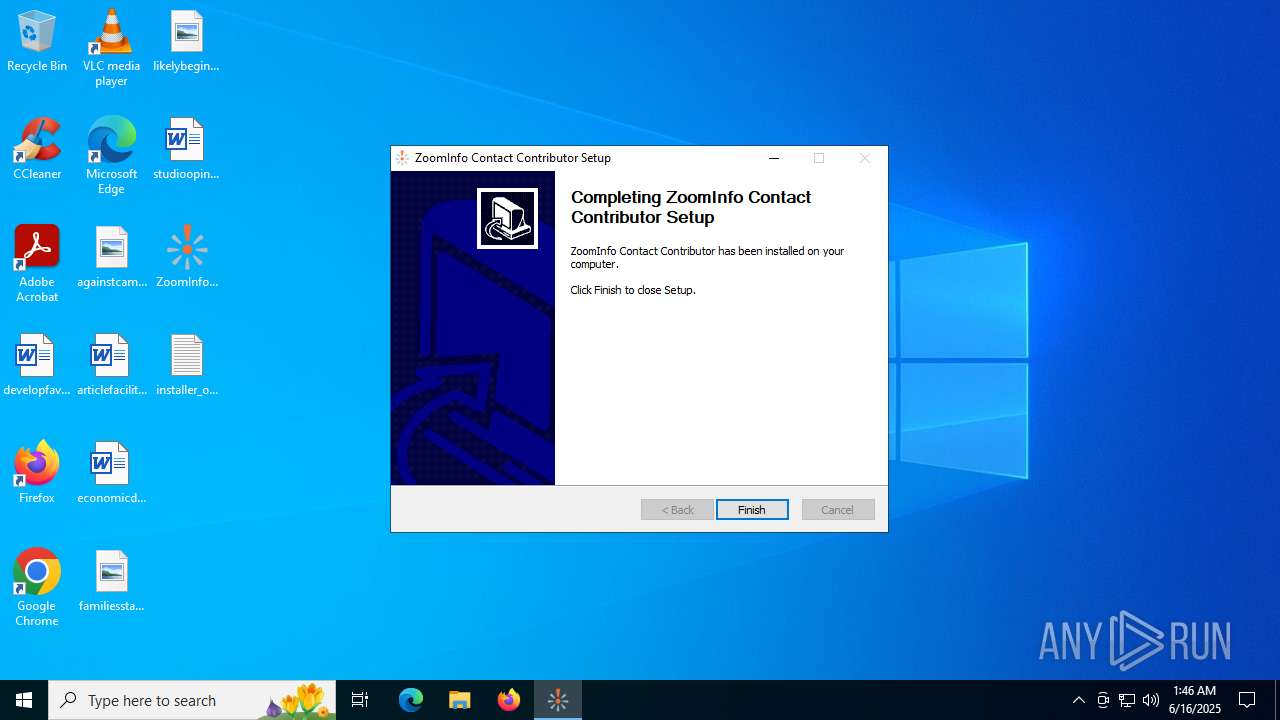
| File name: | ZoomInfoContactContributor.exe |
| Full analysis: | https://app.any.run/tasks/90c99cc8-a997-46cf-af03-867a686076a1 |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2025, 01:44:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 086F85821BF518ADF21F4013E675CB71 |
| SHA1: | 8394D652BFAAA76787290B3D19768D7A08BD52CD |
| SHA256: | 1EEFE50324A9E8DFD02FD2CB73554267E5FED2510A1EEAC54C10AE17B306D94A |
| SSDEEP: | 12288:Vk52OxotZC6Pl+Zva9999qqyZW+fP2/yEiTa:V8xbfPmyEiTa |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1668)
- powershell.exe (PID: 4036)
- powershell.exe (PID: 1036)
Bypass execution policy to execute commands
- powershell.exe (PID: 4036)
Changes powershell execution policy (Bypass)
- ZoomInfoContactContributor.exe (PID: 6640)
Changes the autorun value in the registry
- ZoomInfoContactContributor.exe (PID: 6640)
SUSPICIOUS
The process creates files with name similar to system file names
- ZoomInfoContactContributor.exe (PID: 6640)
Executable content was dropped or overwritten
- ZoomInfoContactContributor.exe (PID: 6640)
- powershell.exe (PID: 1036)
Malware-specific behavior (creating "System.dll" in Temp)
- ZoomInfoContactContributor.exe (PID: 6640)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 1668)
- powershell.exe (PID: 4036)
Starts POWERSHELL.EXE for commands execution
- ZoomInfoContactContributor.exe (PID: 6640)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1668)
- powershell.exe (PID: 4036)
Downloads file from URI via Powershell
- powershell.exe (PID: 1668)
- powershell.exe (PID: 4036)
There is functionality for taking screenshot (YARA)
- ZoomInfoContactContributor.exe (PID: 6640)
- coordinator.exe (PID: 3624)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 1036)
Process drops python dynamic module
- powershell.exe (PID: 1036)
Process drops legitimate windows executable
- powershell.exe (PID: 1036)
The process bypasses the loading of PowerShell profile settings
- ZoomInfoContactContributor.exe (PID: 6640)
The process hide an interactive prompt from the user
- ZoomInfoContactContributor.exe (PID: 6640)
Executing commands from a ".bat" file
- ZoomInfoContactContributor.exe (PID: 6640)
Creates a software uninstall entry
- ZoomInfoContactContributor.exe (PID: 6640)
Reads security settings of Internet Explorer
- ZoomInfoContactContributor.exe (PID: 6640)
Starts CMD.EXE for commands execution
- ZoomInfoContactContributor.exe (PID: 6640)
The executable file from the user directory is run by the CMD process
- coordinator.exe (PID: 3624)
The process drops C-runtime libraries
- powershell.exe (PID: 1036)
INFO
The sample compiled with english language support
- ZoomInfoContactContributor.exe (PID: 6640)
- powershell.exe (PID: 1036)
Checks supported languages
- ZoomInfoContactContributor.exe (PID: 6640)
- coordinator.exe (PID: 3624)
Create files in a temporary directory
- ZoomInfoContactContributor.exe (PID: 6640)
- coordinator.exe (PID: 3624)
Disables trace logs
- powershell.exe (PID: 1668)
- powershell.exe (PID: 4036)
Reads Microsoft Office registry keys
- ZoomInfoContactContributor.exe (PID: 6640)
Checks proxy server information
- powershell.exe (PID: 1668)
- powershell.exe (PID: 4036)
- slui.exe (PID: 6876)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1036)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1036)
Reads the computer name
- ZoomInfoContactContributor.exe (PID: 6640)
- coordinator.exe (PID: 3624)
Reads the software policy settings
- slui.exe (PID: 6876)
Creates files or folders in the user directory
- ZoomInfoContactContributor.exe (PID: 6640)
- coordinator.exe (PID: 3624)
Launching a file from a Registry key
- ZoomInfoContactContributor.exe (PID: 6640)
Reads the machine GUID from the registry
- coordinator.exe (PID: 3624)
Application launched itself
- msedge.exe (PID: 432)
- msedge.exe (PID: 2532)
- msedge.exe (PID: 7260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:30 16:55:23+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 184832 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.62 |
| ProductVersionNumber: | 2.0.0.62 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | - |
| FileVersion: | 62 |
| LegalCopyright: | (c) Zoom Information, Inc. |
| ProductName: | ZoomInfo Contact Contributor |
| ProductVersion: | 62 |
Total processes
194
Monitored processes
48
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch --single-argument https://swapper-prd.zi-ext.com/client/installsuccess?client_version=62&os_version=&outlook_version=16&outlook_bitness=64&autostart=1&client_id={576649ED-7235-4F8B-AB5A-BAE93000E520}&reachout=true&appid=26 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7368,i,774737403576823898,16943372320476197967,262144 --variations-seed-version --mojo-platform-channel-handle=6952 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3652,i,774737403576823898,16943372320476197967,262144 --variations-seed-version --mojo-platform-channel-handle=3664 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 856 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\ZoomInfoCEUtility\launch.bat"" | C:\Windows\SysWOW64\cmd.exe | — | ZoomInfoContactContributor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | powershell -WindowStyle Hidden -Command "Expand-Archive -Path \"C:\Users\admin\AppData\Local\ZoomInfoCEUtility\ZoomInfo_CE.zip\" -DestinationPath \"C:\Users\admin\AppData\Local\ZoomInfoCEUtility\" -Force" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | ZoomInfoContactContributor.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1100 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6272,i,774737403576823898,16943372320476197967,262144 --variations-seed-version --mojo-platform-channel-handle=6364 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --always-read-main-dll --field-trial-handle=6908,i,774737403576823898,16943372320476197967,262144 --variations-seed-version --mojo-platform-channel-handle=6936 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1668 | powershell -WindowStyle Hidden -Command "$ProgressPreference = \"SilentlyContinue\"; [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12; try { Invoke-WebRequest -Uri \"https://swapper-prd.zi-ext.com/client/installopen?client_id={576649ED-7235-4F8B-AB5A-BAE93000E520}\" -OutFile \"installer_opened.txt\" -UseBasicParsing } catch { }" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | ZoomInfoContactContributor.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4880,i,2894448531932191210,12135910490920143653,262144 --variations-seed-version --mojo-platform-channel-handle=4160 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://swapper-prd.zi-ext.com/client/installsuccess?client_version=62&os_version=&outlook_version=16&outlook_bitness=64&autostart=1&client_id={576649ED-7235-4F8B-AB5A-BAE93000E520}&reachout=true&appid=26 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | ZoomInfoContactContributor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
30 094
Read events
29 994
Write events
93
Delete events
7
Modification events
| (PID) Process: | (1668) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1668) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1668) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1668) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1668) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1668) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1668) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1668) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1668) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1668) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
242
Suspicious files
1 019
Text files
1 070
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4036 | powershell.exe | C:\Users\admin\AppData\Local\ZoomInfoCEUtility\ZoomInfo_CE.zip | — | |
MD5:— | SHA256:— | |||
| 1668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4oct3un2.nv4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6640 | ZoomInfoContactContributor.exe | C:\Users\admin\AppData\Local\Temp\nsx5600.tmp\nsDialogs.dll | executable | |
MD5:B7D61F3F56ABF7B7FF0D4E7DA3AD783D | SHA256:89A82C4849C21DFE765052681E1FAD02D2D7B13C8B5075880C52423DCA72A912 | |||
| 4036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cjmj1bel.xak.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bxxwlana.fye.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1668 | powershell.exe | C:\Users\admin\Desktop\installer_opened.txt | binary | |
MD5:C4EA5C8E83D004E952237863EF3DDB68 | SHA256:53E43D3C8F93433F61AE2EA3A13E4376BF54BEC26EC94BE79E3ECDBEFB3CA293 | |||
| 1036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_o3i0nyox.wgt.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6640 | ZoomInfoContactContributor.exe | C:\Users\admin\AppData\Local\Temp\nsx5600.tmp\System.dll | executable | |
MD5:192639861E3DC2DC5C08BB8F8C7260D5 | SHA256:23D618A0293C78CE00F7C6E6DD8B8923621DA7DD1F63A070163EF4C0EC3033D6 | |||
| 6640 | ZoomInfoContactContributor.exe | C:\Users\admin\AppData\Local\Temp\nsx5600.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 6640 | ZoomInfoContactContributor.exe | C:\Users\admin\AppData\Local\Temp\nsx5600.tmp\nsExec.dll | executable | |
MD5:11092C1D3FBB449A60695C44F9F3D183 | SHA256:2CD3A2D4053954DB1196E2526545C36DFC138C6DE9B81F6264632F3132843C77 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
160
DNS requests
183
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
436 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | SE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 868 b | whitelisted |
1028 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
1028 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
2940 | svchost.exe | GET | 200 | 2.19.105.127:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
7156 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Ai3kMJH3dkkqw-OIaEHpbgqBGMlXq9VJDw2avkdv2S0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 312 b | whitelisted |
6256 | svchost.exe | HEAD | 200 | 23.32.238.152:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750171598&P2=404&P3=2&P4=H9wFktSfCeDzDjgmker%2bftBeg0YUH76eW4SWLDTp1yC9EnabB3Df9iV18UM3uW2qf4q0CsYV4TctmCu2HYZMhA%3d%3d | DE | — | — | whitelisted |
6256 | svchost.exe | GET | 206 | 23.32.238.152:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750171598&P2=404&P3=2&P4=H9wFktSfCeDzDjgmker%2bftBeg0YUH76eW4SWLDTp1yC9EnabB3Df9iV18UM3uW2qf4q0CsYV4TctmCu2HYZMhA%3d%3d | DE | binary | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1508 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1668 | powershell.exe | 104.18.38.148:443 | swapper-prd.zi-ext.com | CLOUDFLARENET | — | shared |
4036 | powershell.exe | 104.18.38.148:443 | swapper-prd.zi-ext.com | CLOUDFLARENET | — | shared |
436 | svchost.exe | 20.190.160.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
436 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
swapper-prd.zi-ext.com |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
storage.googleapis.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] PX-Cloud CDN (px-cloud .net) |
7156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] PX-Cloud CDN (px-cloud .net) |
7156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] PX-Cloud CDN (px-cloud .net) |
7156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] PX-Cloud CDN (px-cloud .net) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google App Engine (appspot .com) |
7156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7156 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |