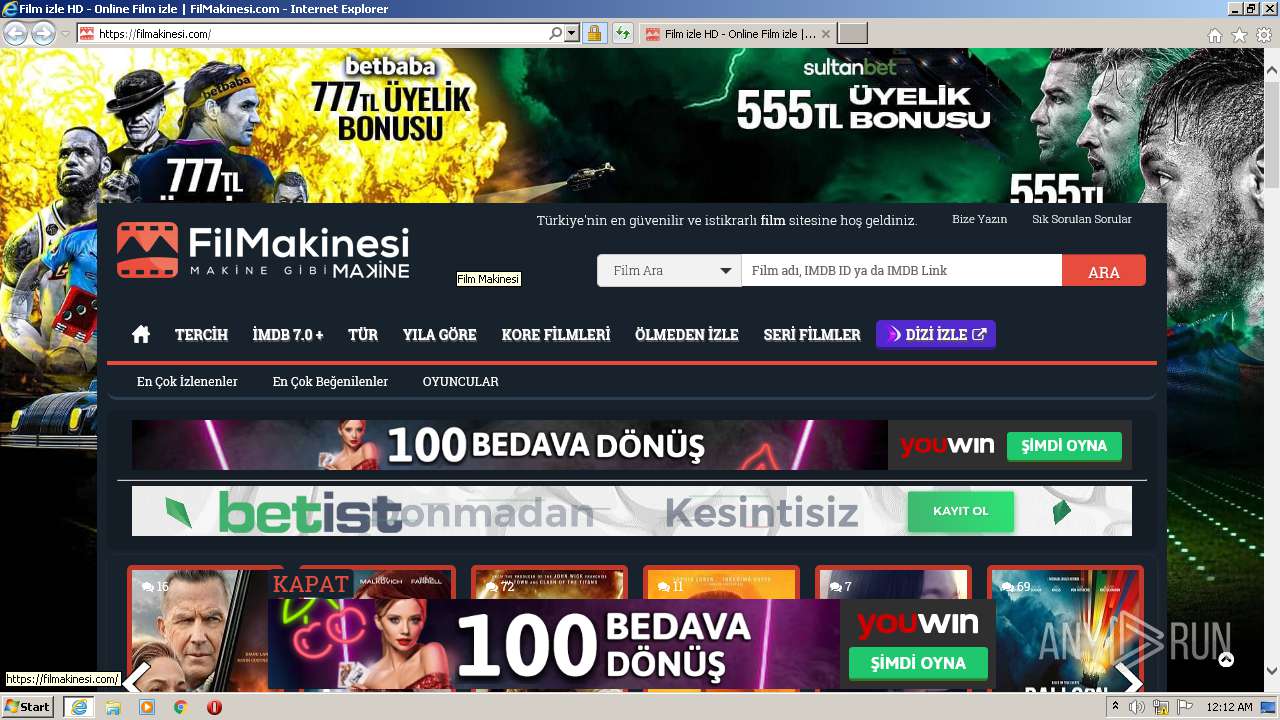
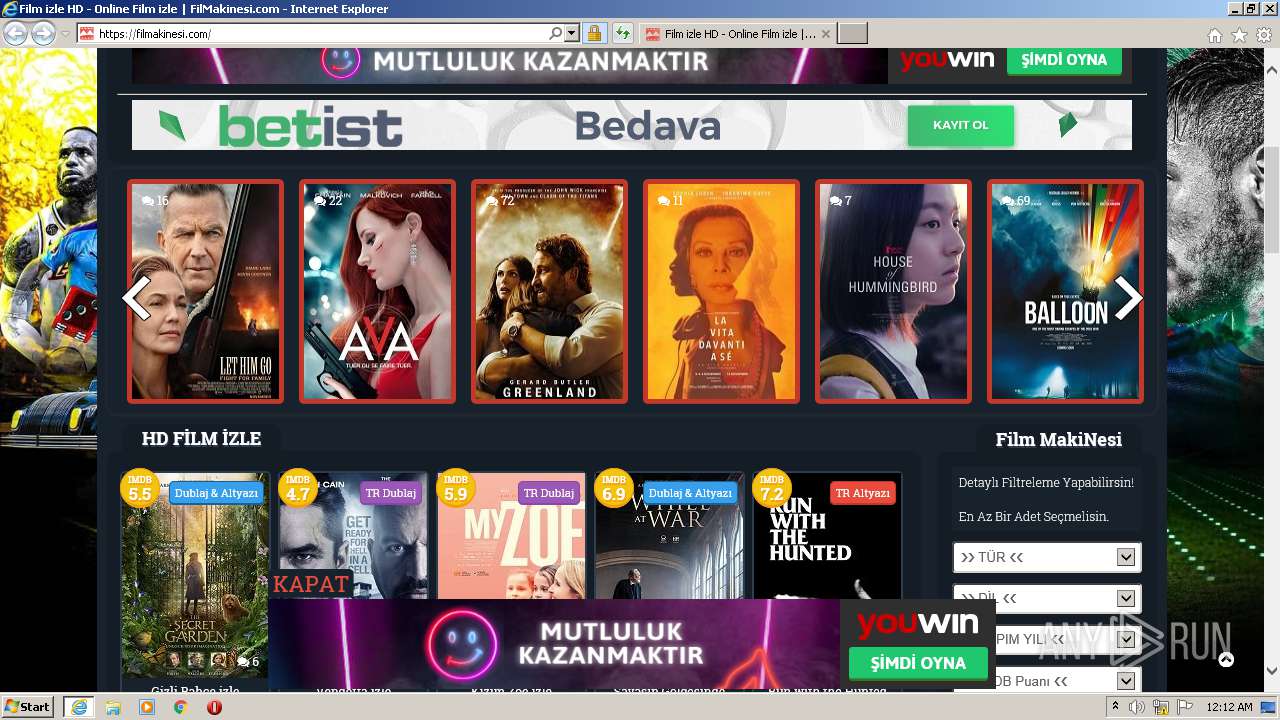
| URL: | https://filmakinesi.com/ |
| Full analysis: | https://app.any.run/tasks/39df8c69-8c74-463d-bd5b-9397e8f80a6d |
| Verdict: | Malicious activity |
| Analysis date: | December 03, 2020, 00:12:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 52D9C42644591D7E524C38E24BD83FFE |
| SHA1: | 9BBC821F352BA2F2B231AEFEC99D6A21DF40353C |
| SHA256: | 1EE6C0DC4E73579B9C32C0B140BBC7A83AF820C8DBCD763131F11604F6F484AC |
| SSDEEP: | 3:N8E0W1K:2jSK |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 1840)
Reads settings of System Certificates
- iexplore.exe (PID: 312)
- iexplore.exe (PID: 1840)
Changes settings of System certificates
- iexplore.exe (PID: 1840)
Creates files in the user directory
- iexplore.exe (PID: 1840)
- iexplore.exe (PID: 1452)
- iexplore.exe (PID: 312)
Reads internet explorer settings
- iexplore.exe (PID: 1452)
- iexplore.exe (PID: 312)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1840)
Application launched itself
- iexplore.exe (PID: 1840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1840 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1840 CREDAT:1840391 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://filmakinesi.com/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
728
Read events
583
Write events
143
Delete events
2
Modification events
| (PID) Process: | (1840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 418160540 | |||
| (PID) Process: | (1840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30853385 | |||
| (PID) Process: | (1840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
90
Text files
209
Unknown types
57
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 312 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab318E.tmp | — | |
MD5:— | SHA256:— | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar318F.tmp | — | |
MD5:— | SHA256:— | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\P3CC999I.txt | — | |
MD5:— | SHA256:— | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:59490F13154DD53151787F117C115E66 | SHA256:F105B2474799BE0CC0DD429104EB9C77F8802FFF90C56F44D8345AA12D495532 | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:9F3FB76392AE8C8BA5263F7D7E0EB0E7 | SHA256:41A1CAFDF2A4AFE6B4CAC27B8D25F751B5081AC9EBB5A8B0779EB37B935976F0 | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\XCGXPZJX.txt | text | |
MD5:1B616B29FACE52517570BFF4D3D2FCAD | SHA256:D604507D37D2E51FADACC60BE84450D6AEAFB94D8C8230721C17A027756E79EA | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\api[1].js | text | |
MD5:45F4F76A6767B7506D3CDBB7517DBADC | SHA256:3E46BFFB5F4BD8C42E67E417D2BBB3740EB7474E65C16E0053E736237380D77F | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\jcarousel.basic[1].css | text | |
MD5:5409EE036F7D1F19D8802F1B4E2A0648 | SHA256:6FDA628D16D089E75F11AA9D973671A3231E5BA47D3E3C75BEF5C4F0F94926AA | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\wp-page-numbers[1].css | text | |
MD5:910D0312739F0C57E396A6539E0AE604 | SHA256:CFB48552ECA4B6929C6C0CF6D20A4C150FAC78A60469344883E97E993F3435BA | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\custom-select[1].js | text | |
MD5:9A3A32C352A695414D909228A6D42179 | SHA256:AD7F321DD5D1777CC74D2F12287754CFCAD9E46E02ED48C8FC98E21B53549E04 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
89
TCP/UDP connections
119
DNS requests
46
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
312 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAjK4Od3FkRo%2BPSkMFWAFq4%3D | US | der | 278 b | whitelisted |
312 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
312 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
312 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAjK4Od3FkRo%2BPSkMFWAFq4%3D | US | der | 278 b | whitelisted |
312 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
312 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
312 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAIkedr766KI5t2gT55IKvU%3D | US | der | 280 b | whitelisted |
312 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
1840 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
312 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgMB6BKB85nmxgDd2KHXvl4JSw%3D%3D | unknown | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1840 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1452 | iexplore.exe | 107.154.251.88:443 | media.winaffiliates.com | Incapsula Inc | US | suspicious |
1452 | iexplore.exe | 108.161.188.196:80 | go.hepsibahis616.com | netDNA | US | unknown |
1452 | iexplore.exe | 151.101.2.109:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
1452 | iexplore.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
1452 | iexplore.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
312 | iexplore.exe | 104.26.2.186:443 | filmakinesi.com | Cloudflare Inc | US | malicious |
312 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
312 | iexplore.exe | 104.31.94.57:443 | bildirimci.net | Cloudflare Inc | US | unknown |
312 | iexplore.exe | 107.154.251.88:443 | media.winaffiliates.com | Incapsula Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
filmakinesi.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
bildirimci.net |
| unknown |
media.winaffiliates.com |
| suspicious |
flmplayer.online |
| suspicious |
code.createjs.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
cdn.bannerflow.com |
| suspicious |
58be65e203e67e24400a3c51.tracker.bannerflow.com |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |