| File name: | jcopenglish.exe |
| Full analysis: | https://app.any.run/tasks/8b4bbbaf-00cf-4ee4-9a83-7dae955346fe |
| Verdict: | Malicious activity |
| Analysis date: | May 05, 2021, 04:55:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable, MZ for MS-DOS |
| MD5: | 0828480F98ADB533104D42AD42601F80 |
| SHA1: | 5528665C1E94EC7738174058196D3C818C64241E |
| SHA256: | 1ECFD3755EBA578108363C0705C6EC205972080739ED0FBD17439F8139BA7E08 |
| SSDEEP: | 49152:kSf/2SnB0juFU0dMIiK7eeDlI35dCWk7PrTsTp2DXdbr73PxrMM98ijeGfjAhWFe:XcuF1dXiK7eeU5+M2Frz2WjeGqWFby |
MALICIOUS
Application was dropped or rewritten from another process
- GPShell.exe (PID: 3800)
- GPShell.exe (PID: 3428)
- GPShell.exe (PID: 2144)
- GPShell.exe (PID: 1752)
- GPShell.exe (PID: 3976)
- GPShell.exe (PID: 2404)
- GPShell.exe (PID: 4004)
- GPShell.exe (PID: 2740)
Loads dropped or rewritten executable
- GPShell.exe (PID: 3800)
- GPShell.exe (PID: 3428)
- GPShell.exe (PID: 2144)
- GPShell.exe (PID: 3976)
- GPShell.exe (PID: 1752)
- GPShell.exe (PID: 2404)
- GPShell.exe (PID: 4004)
SUSPICIOUS
Drops a file with too old compile date
- jcopenglish.exe (PID: 2172)
Executable content was dropped or overwritten
- jcopenglish.exe (PID: 2172)
Application launched itself
- taskmgr.exe (PID: 2388)
INFO
Manual execution by user
- taskmgr.exe (PID: 2388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Comments: | - |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | - |
| OriginalFileName: | - |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | - |
| FileVersion: | 10.0.0.0 |
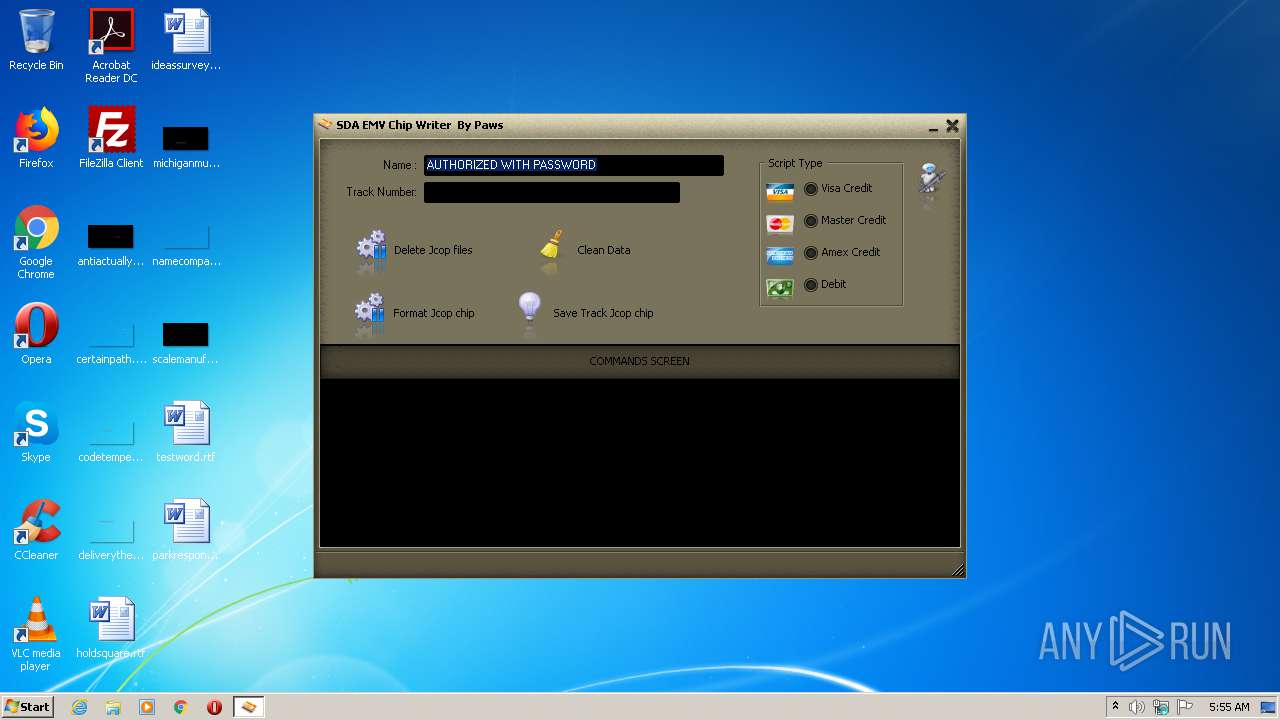
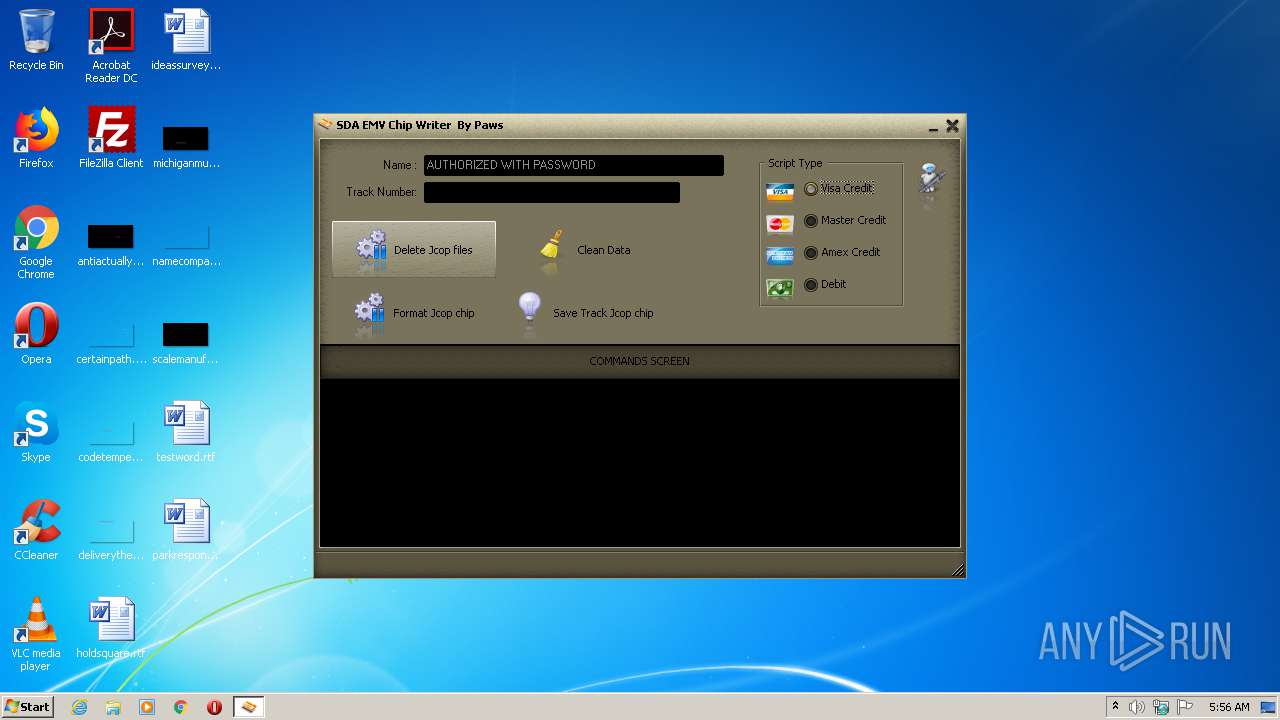
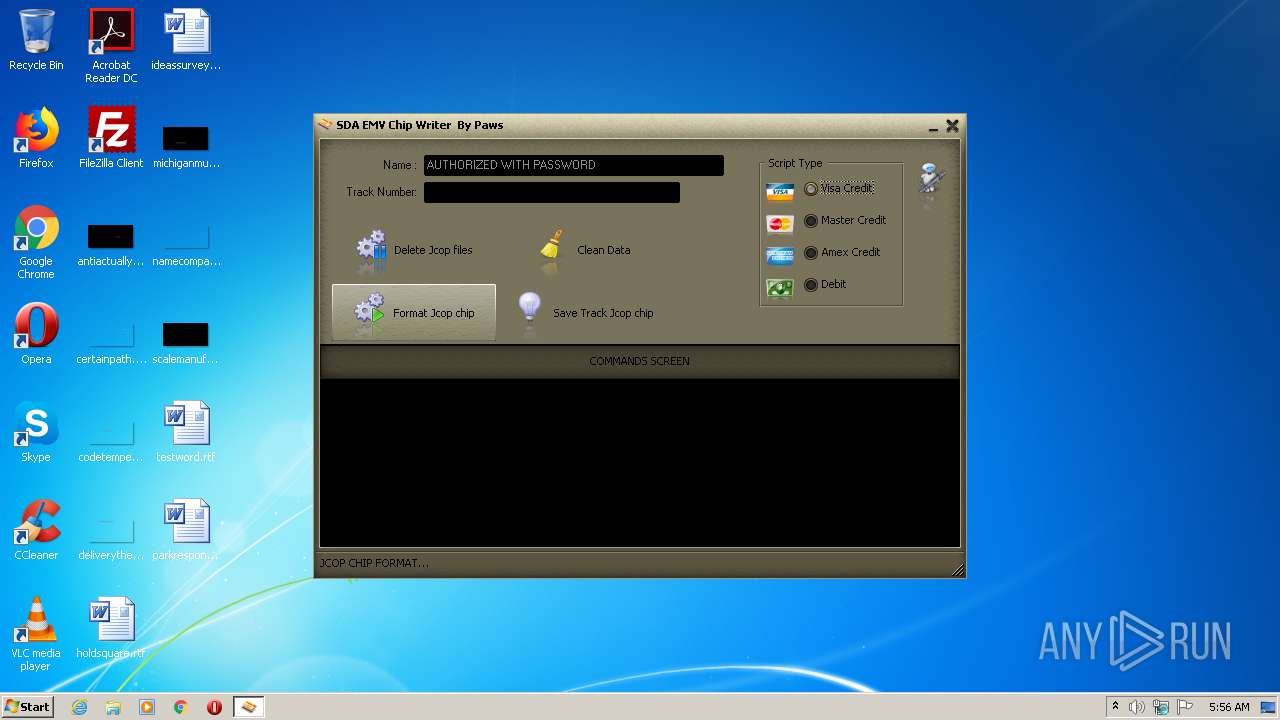
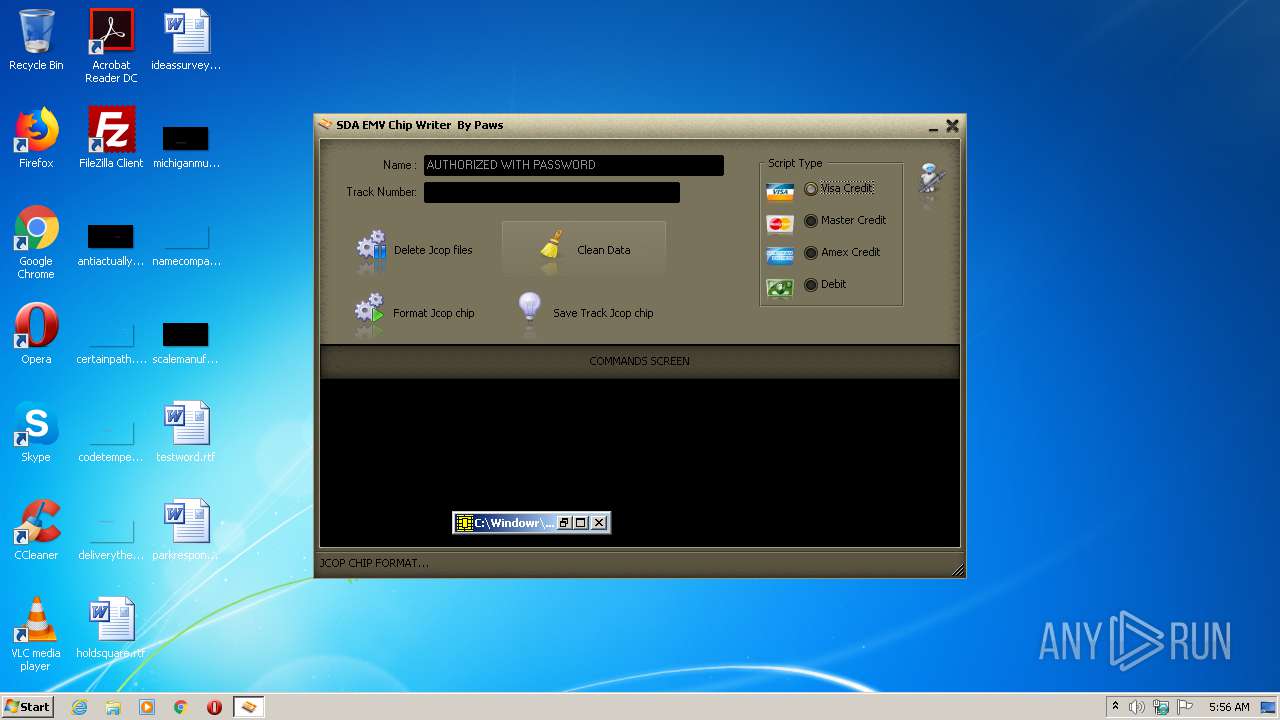
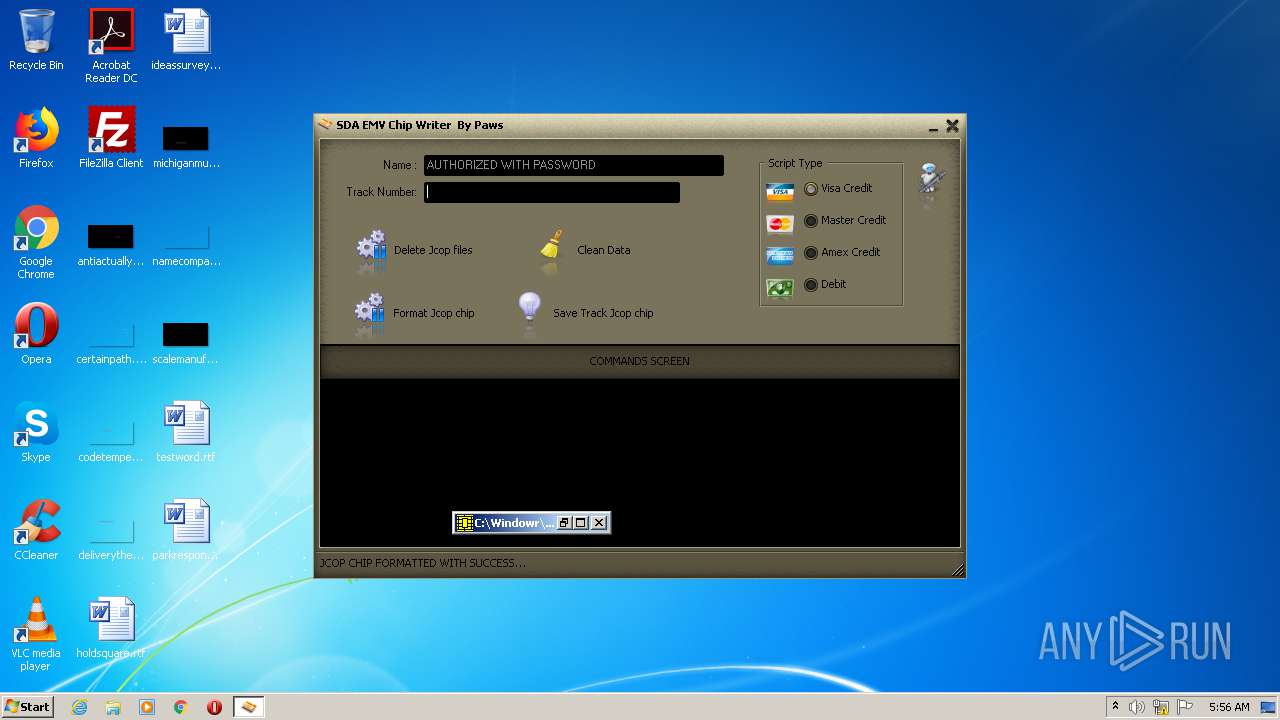
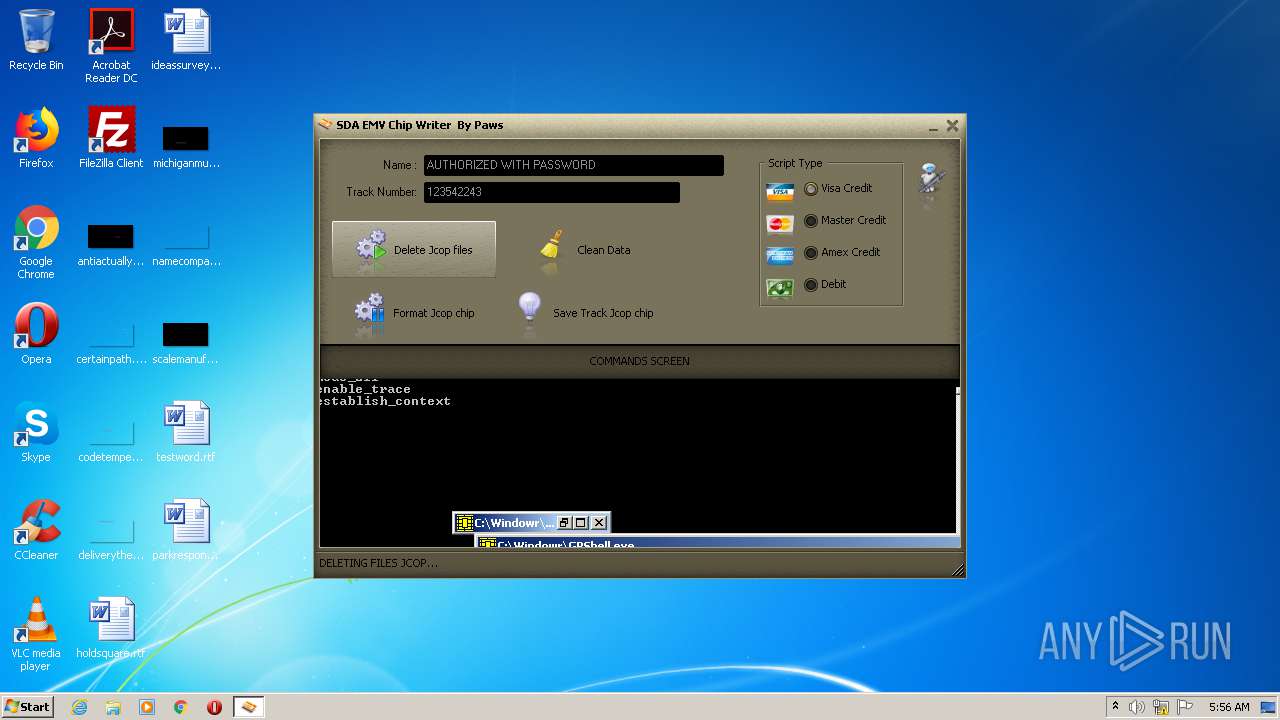
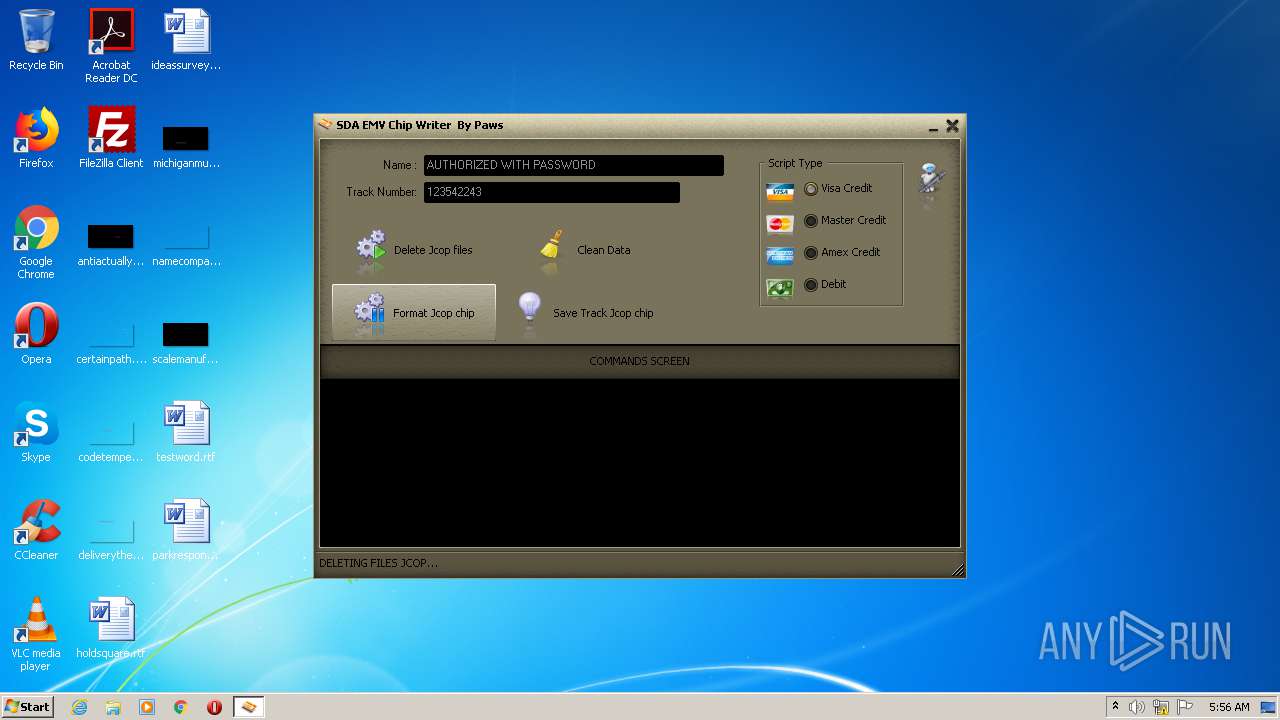
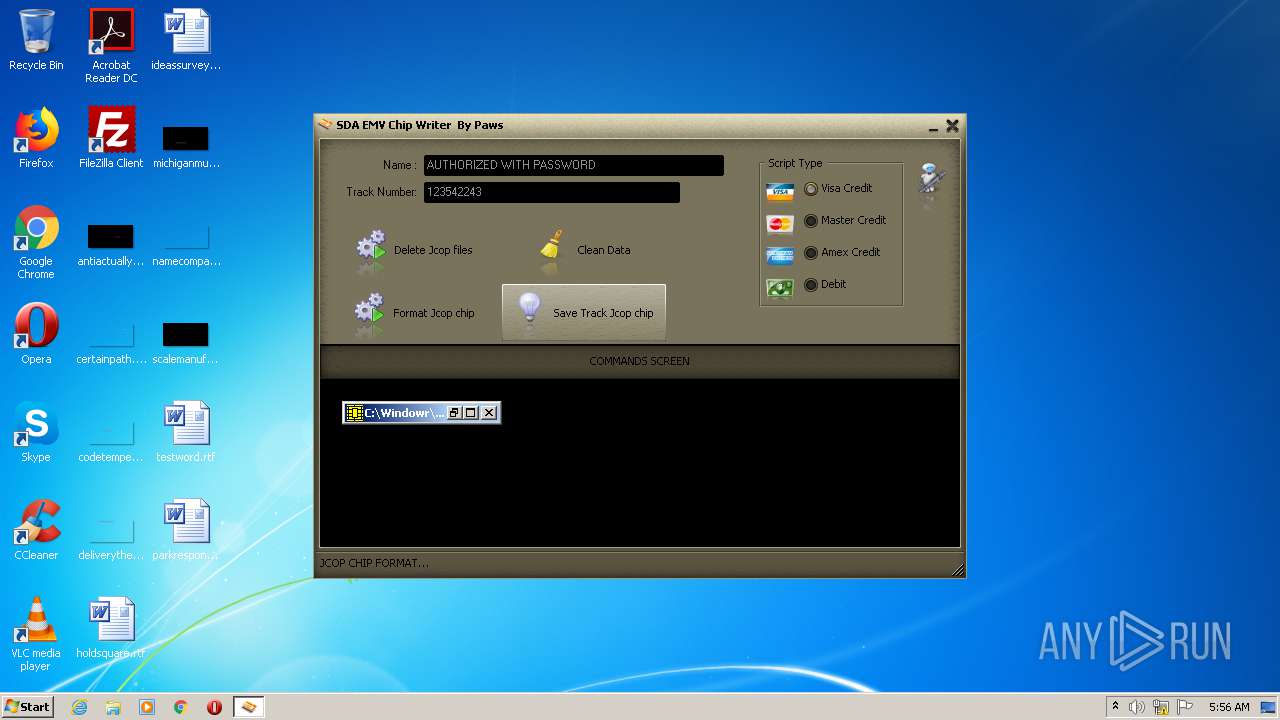
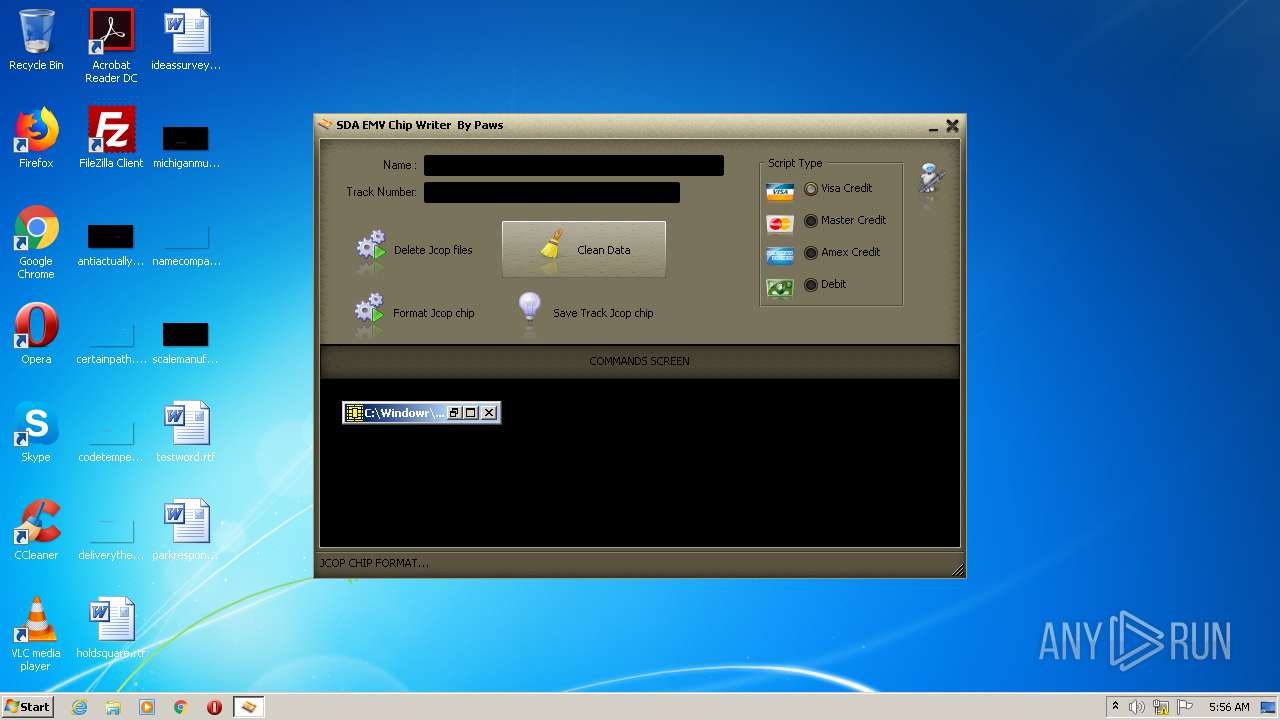
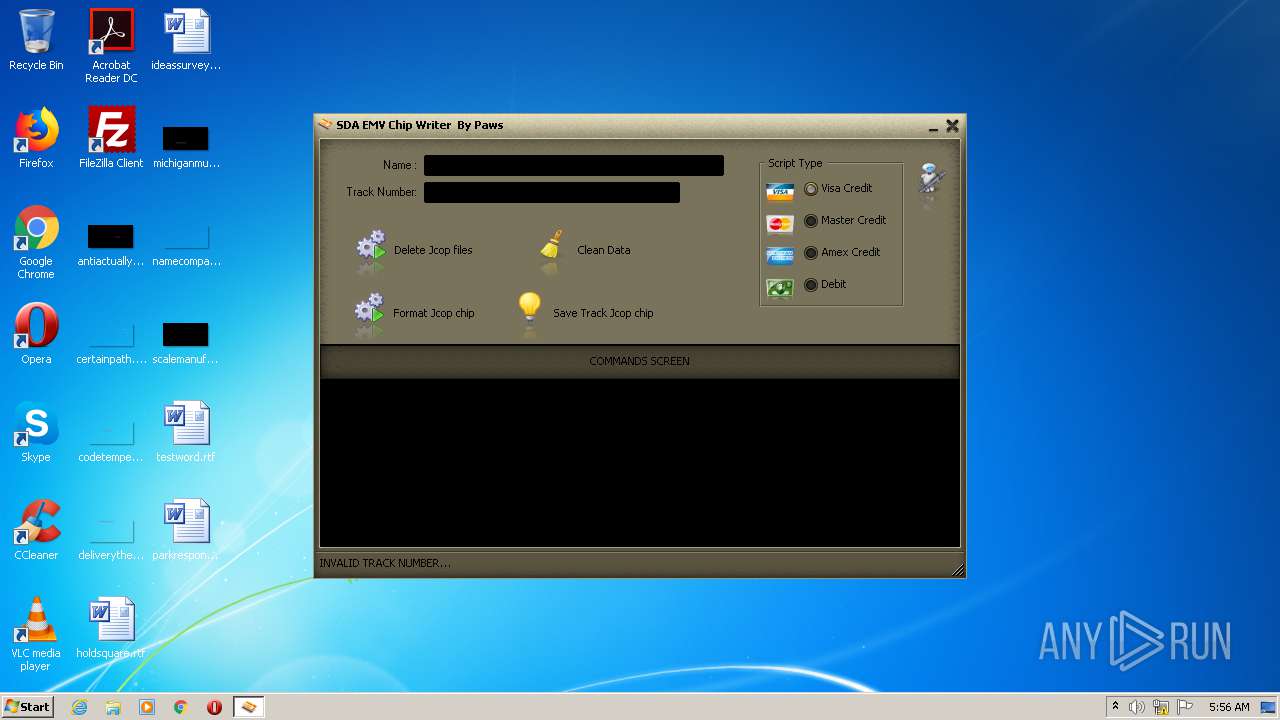
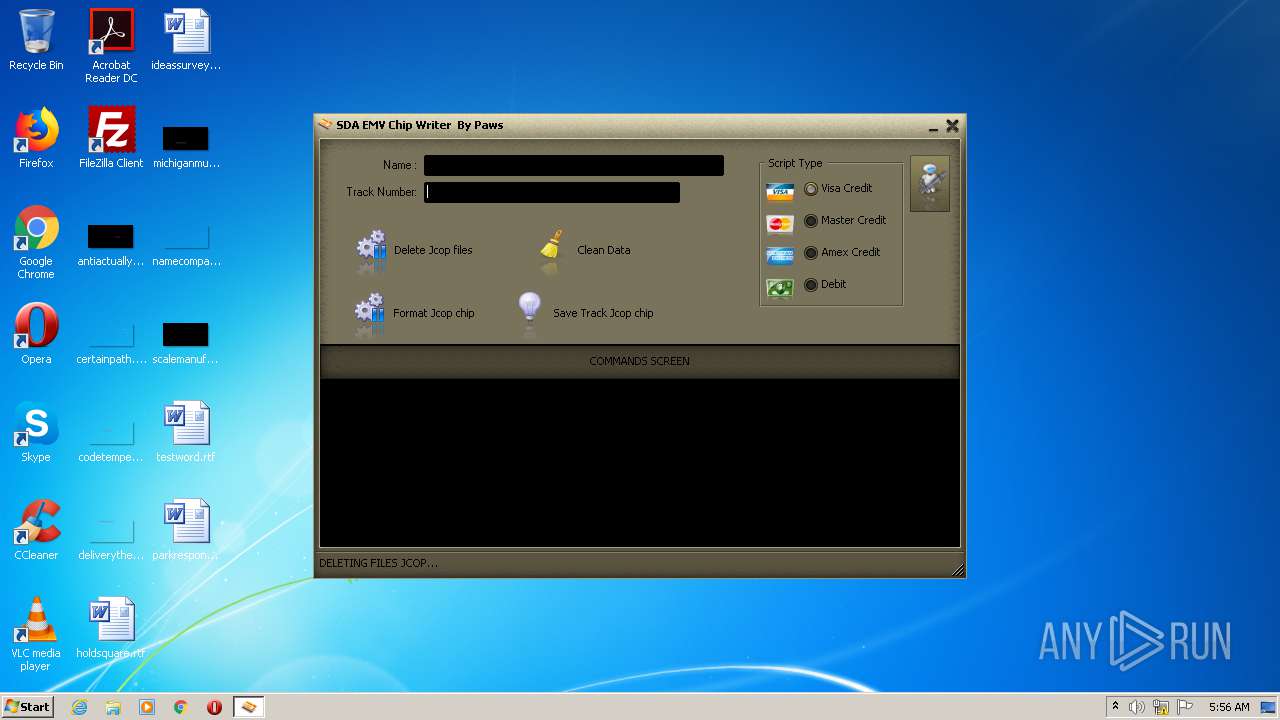
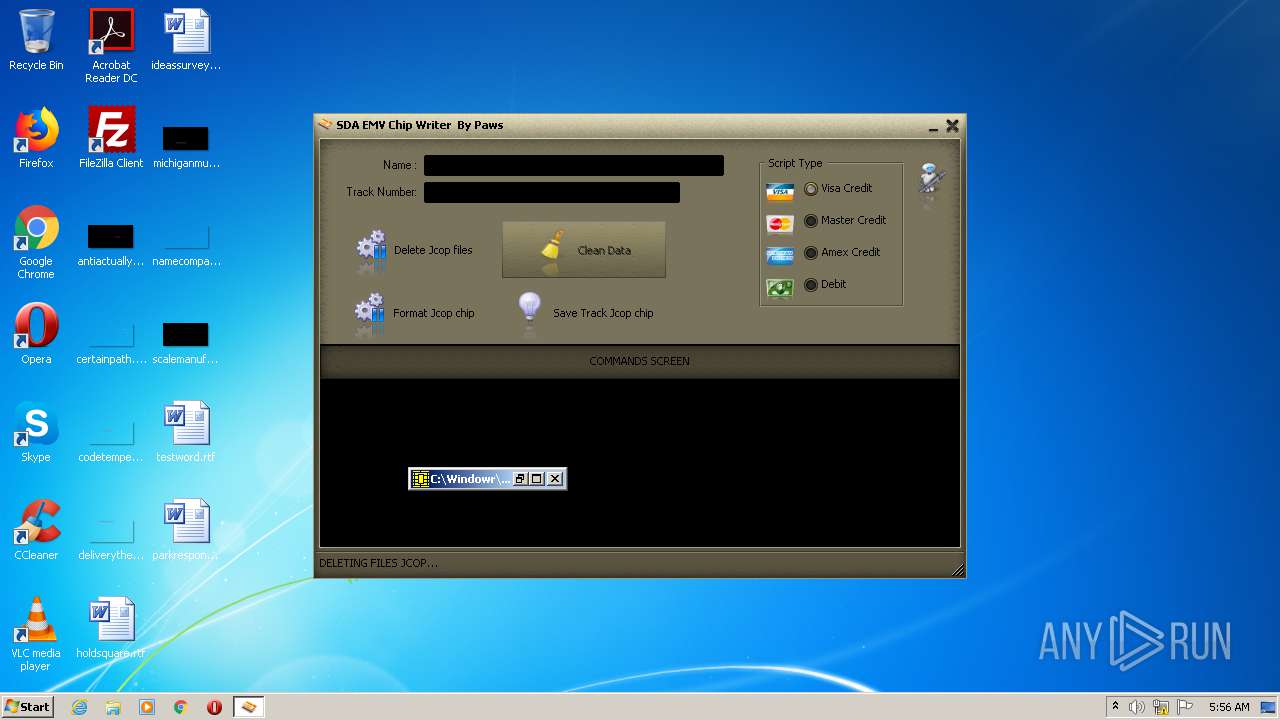
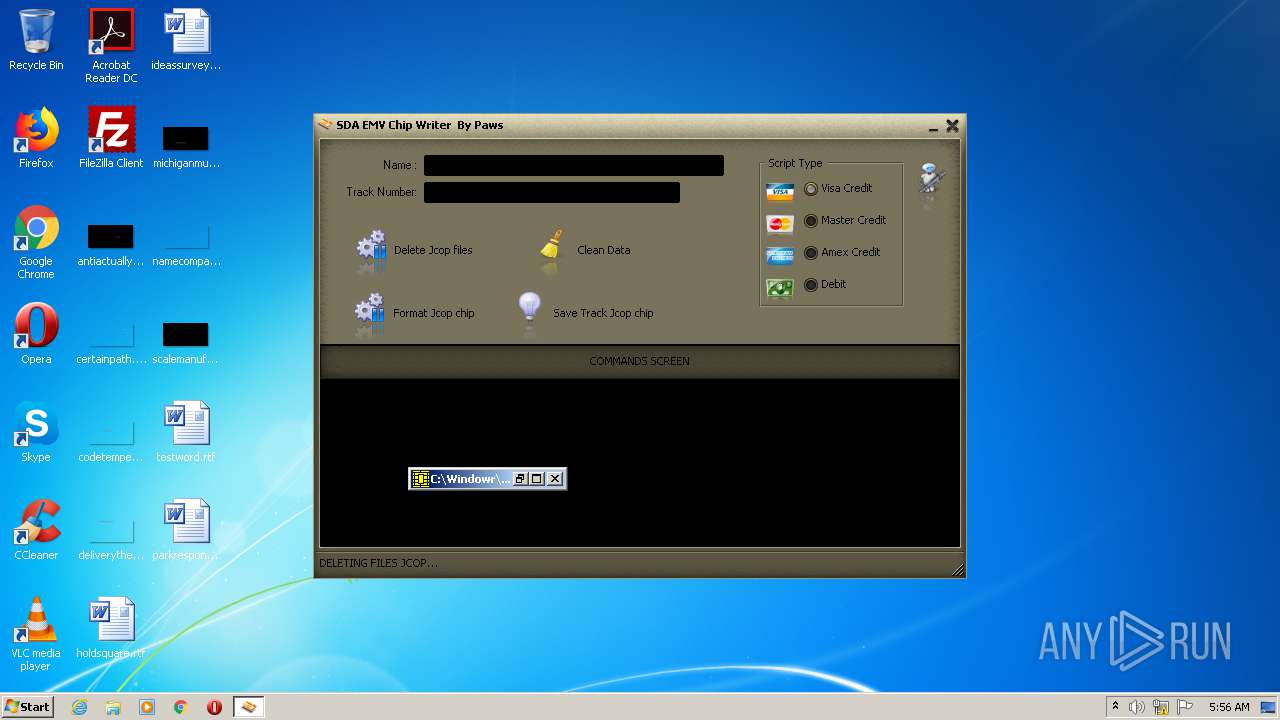
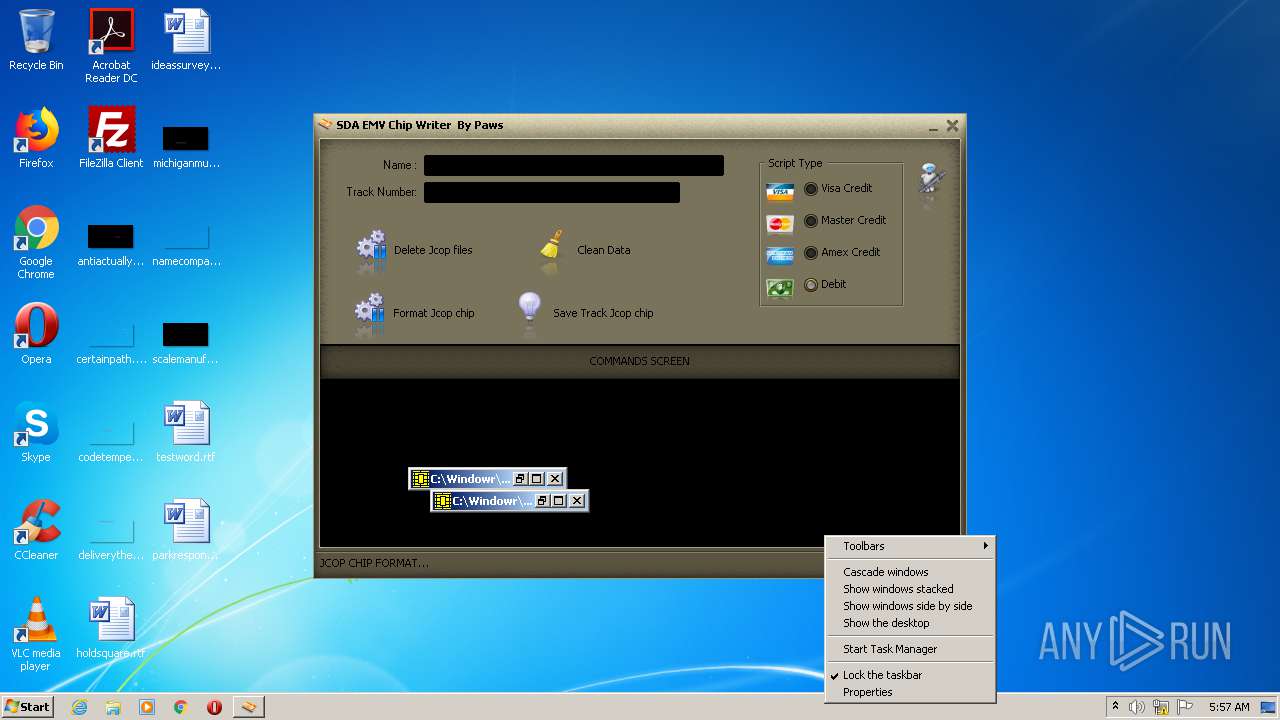
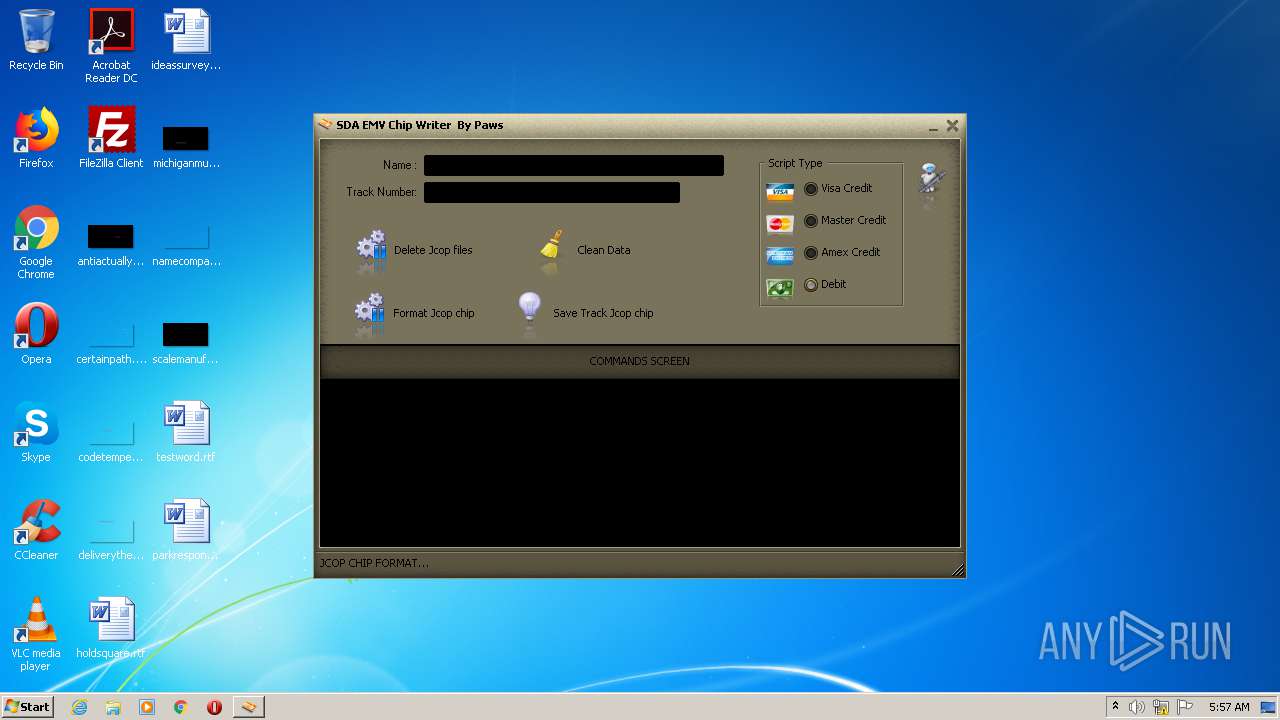
| FileDescription: | EMV Chip Writer |
| CompanyName: | EMV Writer Software by Paws |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | Portuguese (Brazilian) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 10.0.0.0 |
| FileVersionNumber: | 10.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x28b9e4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2461696 |
| CodeSize: | 2665472 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2014:12:03 17:07:48+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Dec-2014 16:07:48 |
| Detected languages: |
|
| CompanyName: | EMV Writer Software by Paws |
| FileDescription: | EMV Chip Writer |
| FileVersion: | 10.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0040 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0002 |
| Min extra paragraphs: | 0x0004 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0002 |
| Initial SP value: | 0x0040 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x000E |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x2032 |
| OEM information: | 0x6E6F |
| Address of NE header: | 0x00000040 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 03-Dec-2014 16:07:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00288000 | 0x00287F5F | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44484 |
.itext | 0x00289000 | 0x00003000 | 0x00002A3C | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.1712 |
.data | 0x0028C000 | 0x00016000 | 0x00015623 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.65441 |
.bss | 0x002A2000 | 0x00088000 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0032A000 | 0x00004000 | 0x000038EE | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.69515 |
.didata | 0x0032E000 | 0x00001000 | 0x000002EA | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.08318 |
.tls | 0x0032F000 | 0x00001000 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00330000 | 0x00001000 | 0x000000EA | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.379563 |
.reloc | 0x00331000 | 0x0002E000 | 0x0002DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0 |
.rsrc | 0x0035F000 | 0x00212000 | 0x00211A62 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.66883 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92007 | 850 | UNKNOWN | Portuguese - Brazil | RT_MANIFEST |
2 | 4.60981 | 4264 | UNKNOWN | Portuguese - Brazil | RT_ICON |
3 | 4.10535 | 9640 | UNKNOWN | Portuguese - Brazil | RT_ICON |
4 | 2.56318 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3682 | 2.04342 | 76 | UNKNOWN | UNKNOWN | RT_STRING |
3683 | 2.80433 | 146 | UNKNOWN | UNKNOWN | RT_STRING |
3684 | 3.47221 | 390 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
msimg32.dll |
msvcrt.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
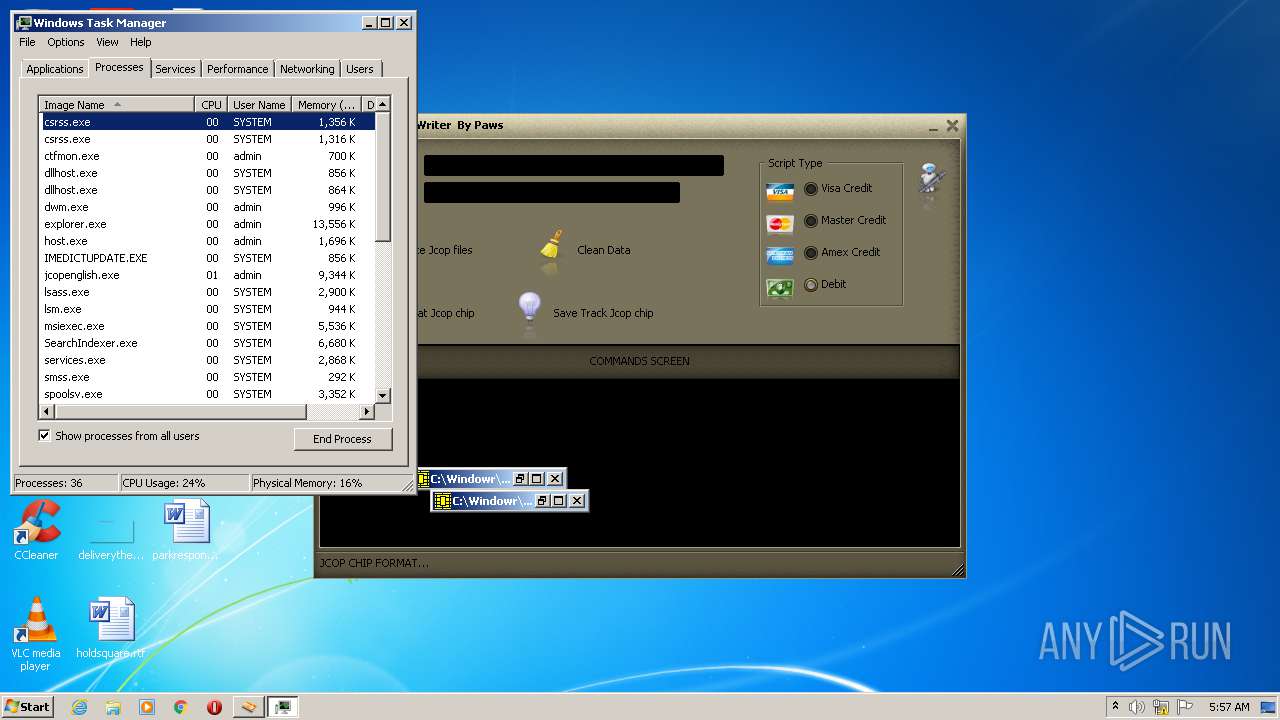
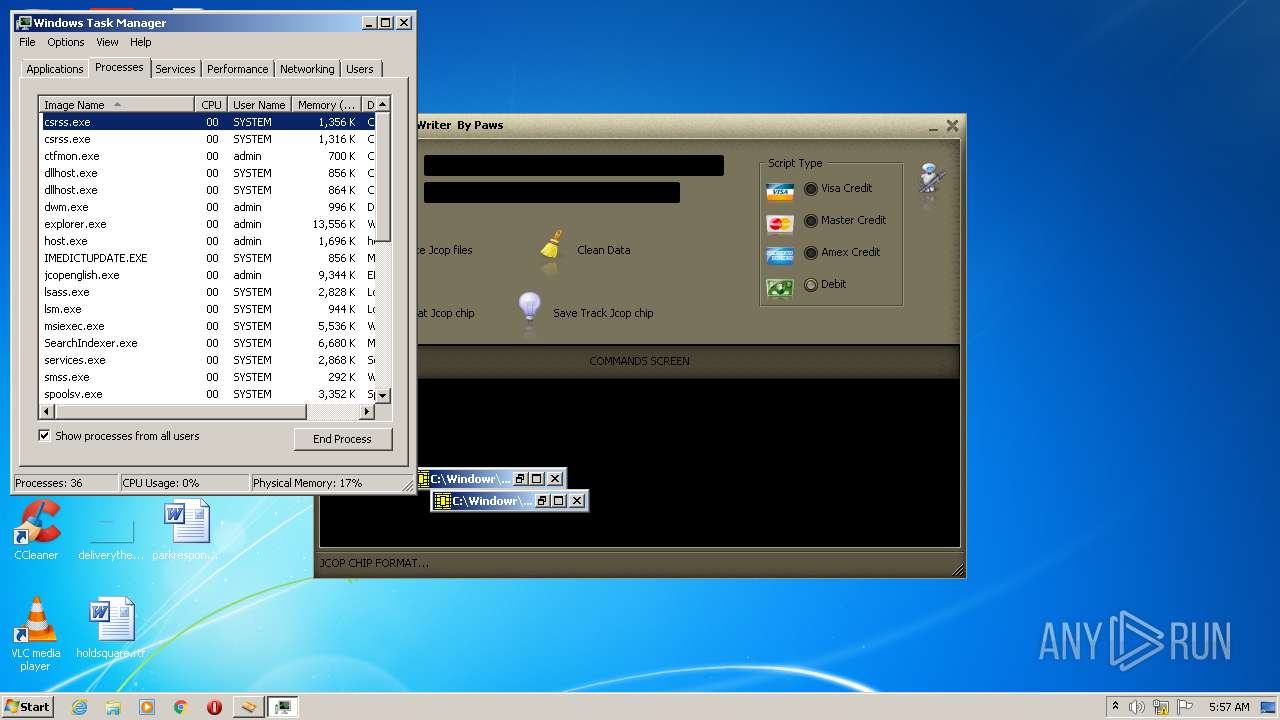
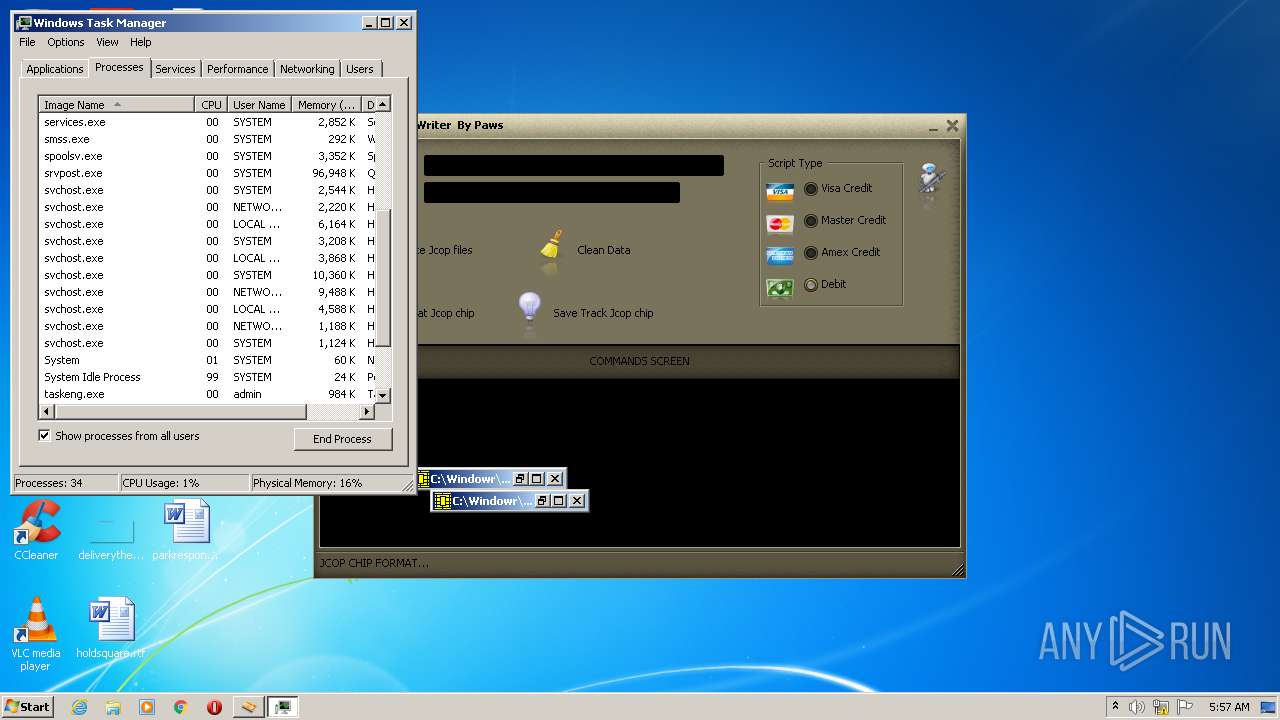
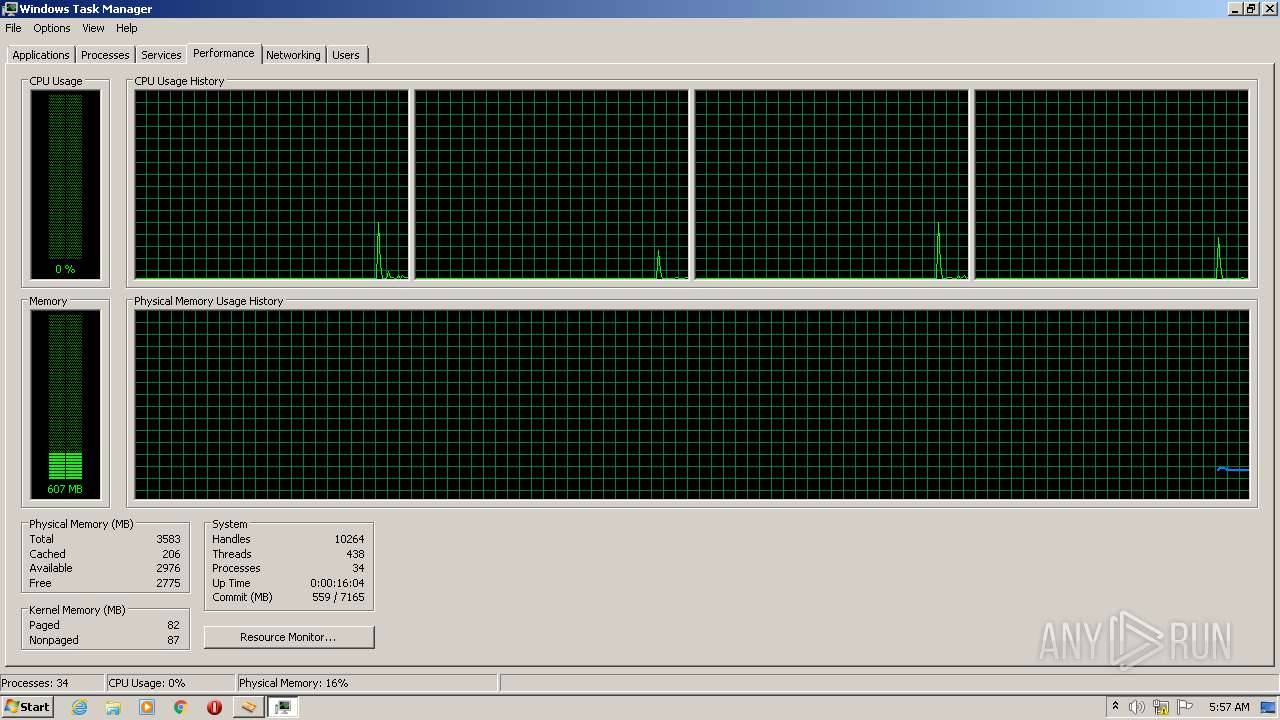
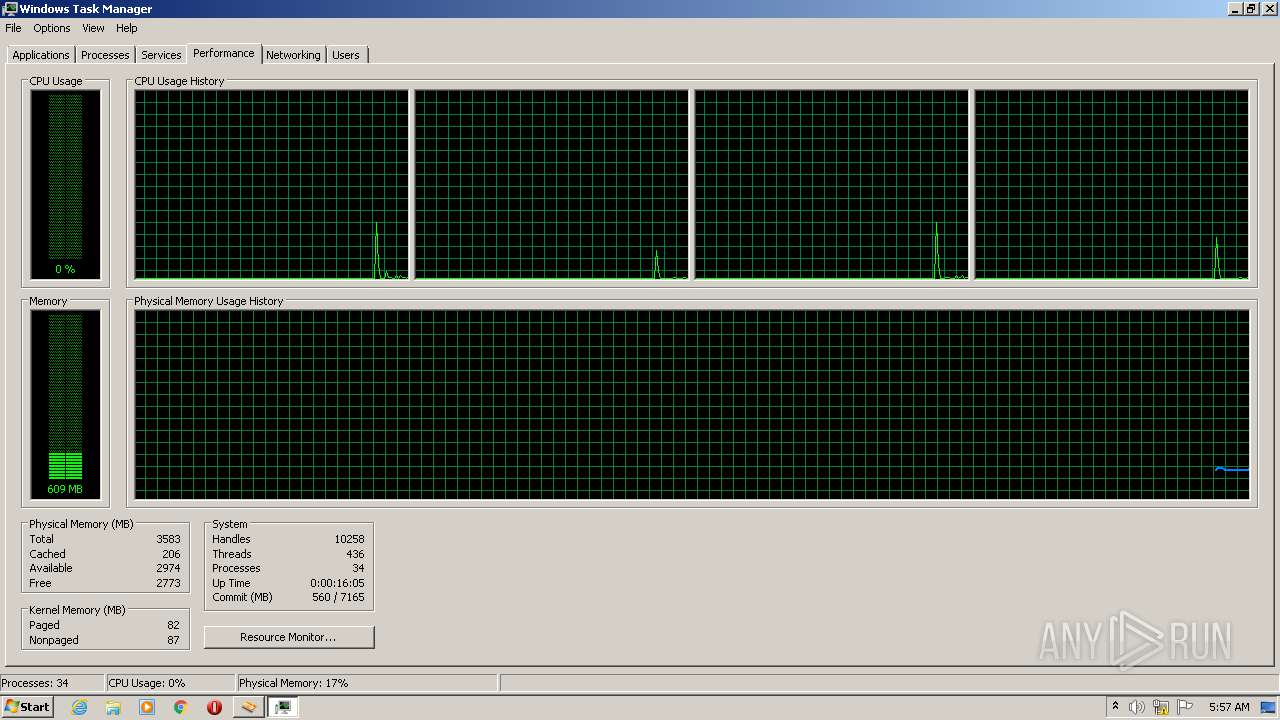
Total processes
58
Monitored processes
11
Malicious processes
1
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Windows\system32\taskmgr.exe" /1 | C:\Windows\system32\taskmgr.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
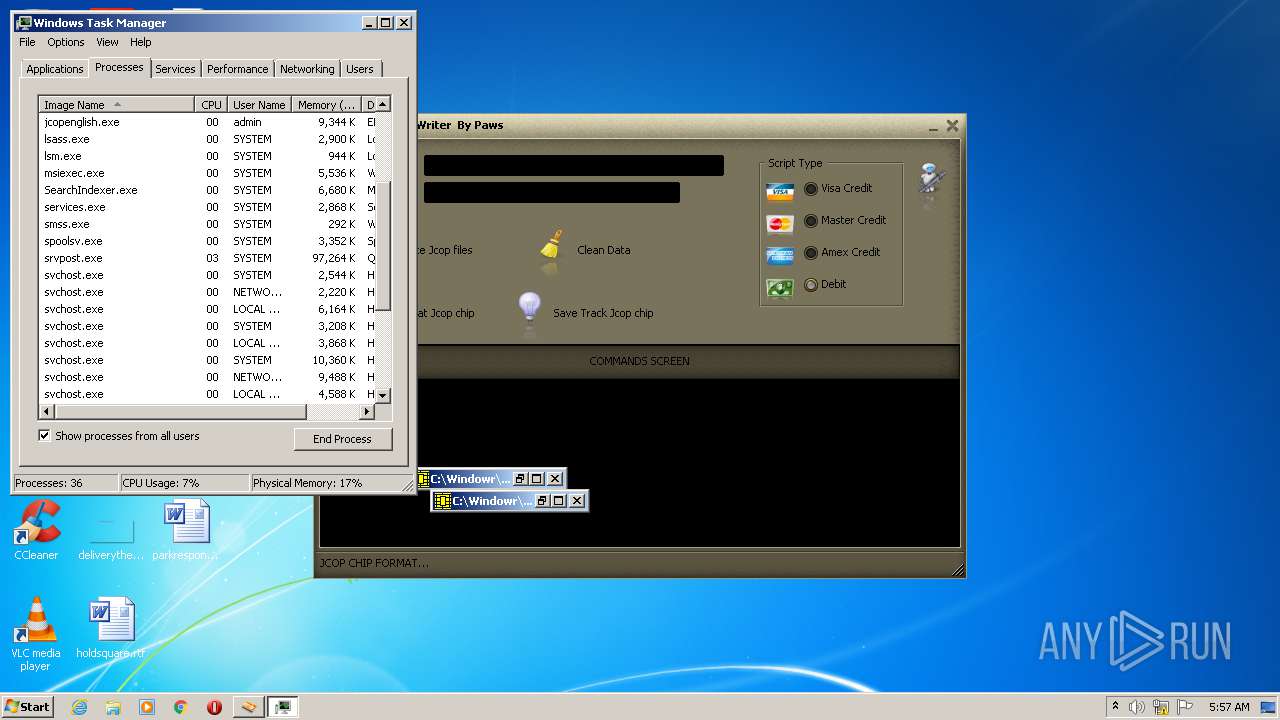
| 1752 | "C:\Windowr\GPShell.exe" apdu.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 2144 | "C:\Windowr\GPShell.exe" form.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 2172 | "C:\Users\admin\AppData\Local\Temp\jcopenglish.exe" | C:\Users\admin\AppData\Local\Temp\jcopenglish.exe | explorer.exe | ||||||||||||
User: admin Company: EMV Writer Software by Paws Integrity Level: MEDIUM Description: EMV Chip Writer Exit code: 0 Version: 10.0.0.0 Modules
| |||||||||||||||
| 2388 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | "C:\Windowr\GPShell.exe" del.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 2740 | "C:\Windowr\GPShell.exe" form.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 3428 | "C:\Windowr\GPShell.exe" form.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 3800 | "C:\Windowr\GPShell.exe" del.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
| 3976 | "C:\Windowr\GPShell.exe" del.dll | C:\Windowr\GPShell.exe | — | jcopenglish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 1, 4, 4, 0 Modules
| |||||||||||||||
Total events
436
Read events
423
Write events
13
Delete events
0
Modification events
| (PID) Process: | (2172) jcopenglish.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2172) jcopenglish.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2388) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2388) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2388) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000000A0000000A000000A2010000F00100000100000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
| (PID) Process: | (2388) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (532) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (532) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000000A0000000A000000A2010000F00100000300000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000630060003C005A00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
Executable files
6
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2172 | jcopenglish.exe | C:\Windowr\GPShell.exe | executable | |
MD5:50FCDD91AEE3EC8D7C54FEB63E324C03 | SHA256:BA5E9041668257393AE28413F5099DB5D12D7F48C239E8D19E9BEDA2036B31BE | |||
| 2172 | jcopenglish.exe | C:\Windowr\Global.drv | compressed | |
MD5:418F4F42405CEC3252F0B952ED9A642C | SHA256:148B8755D228F174F4DBD0B8454E3825F34E6D6E055341D4C3981C2BB7664C07 | |||
| 2172 | jcopenglish.exe | C:\Windowr\GPPcScConnectionPlugin.dll | executable | |
MD5:2F99E012379E8C950B0BDE761C5CCA0F | SHA256:5D84EC3F8DEE7438B0049D5DC201A68A99F3E471A4C9ACAC48DD7F67F89FD178 | |||
| 2172 | jcopenglish.exe | C:\Windowr\MacGyver.cap | compressed | |
MD5:3709E18B229E3DB113BF5C7863C59DB4 | SHA256:9DC70002E82C78EE34C813597925C6CF8AA8D68B7E9CE5BCC70EA9BCAB9DBF4A | |||
| 2172 | jcopenglish.exe | C:\Windowr\form.dll | text | |
MD5:20640673B59B3E298D00899F8EE77079 | SHA256:58C92AE2DE19A77BEA6F8A934FC317310E33030C93A01205BB375CBAE3E5706D | |||
| 2172 | jcopenglish.exe | C:\Windowr\ssleay32.dll | executable | |
MD5:63D26ECAFCF3B2CEBD5E2F05BCAD553D | SHA256:4F1BAD1A6B9E00473D885BF4E7F3D9D0EC3D91CBDCE05B46F6C6CB2D1FCA8C2B | |||
| 2172 | jcopenglish.exe | C:\Windowr\zlib1.dll | executable | |
MD5:C7D4D685A0AF2A09CBC21CB474358595 | SHA256:E96B397B499D9EAA3F52EAF496CA8941E80C0AD1544879CCADF02BF2C6A1ECFC | |||
| 2172 | jcopenglish.exe | C:\Windowr\GlobalPlatform.dll | executable | |
MD5:C035B189CCC0FA06E549CCABF7DFBA48 | SHA256:DAC5A4213654CAE1AA622877E7E156C0EFD77C0601440DF7CE9995E280DF8694 | |||
| 2172 | jcopenglish.exe | C:\Windowr\del.dll | text | |
MD5:39F489355AC6CCC48A810E2C867475FD | SHA256:71E16A8C9540CBEB6AFC80045A21F7C5954F9E54B5EC731C93AFCA6D67A61646 | |||
| 2172 | jcopenglish.exe | C:\Windowr\libeay32.dll | executable | |
MD5:A7EFD09E5B963AF88CE2FC5B8EB7127C | SHA256:FA4FB4F5A28BDE9C9CBC4BAA9E737C282799294C65E31D39CDF8E2C758969A70 | |||
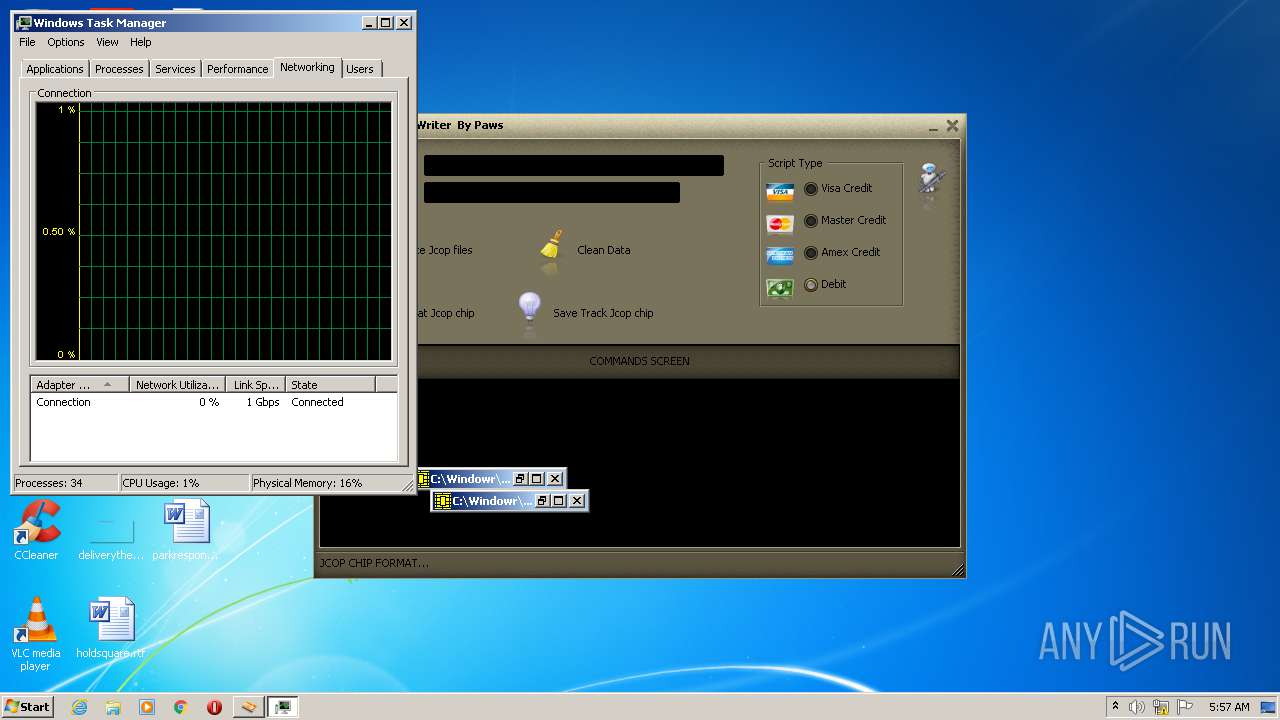
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report