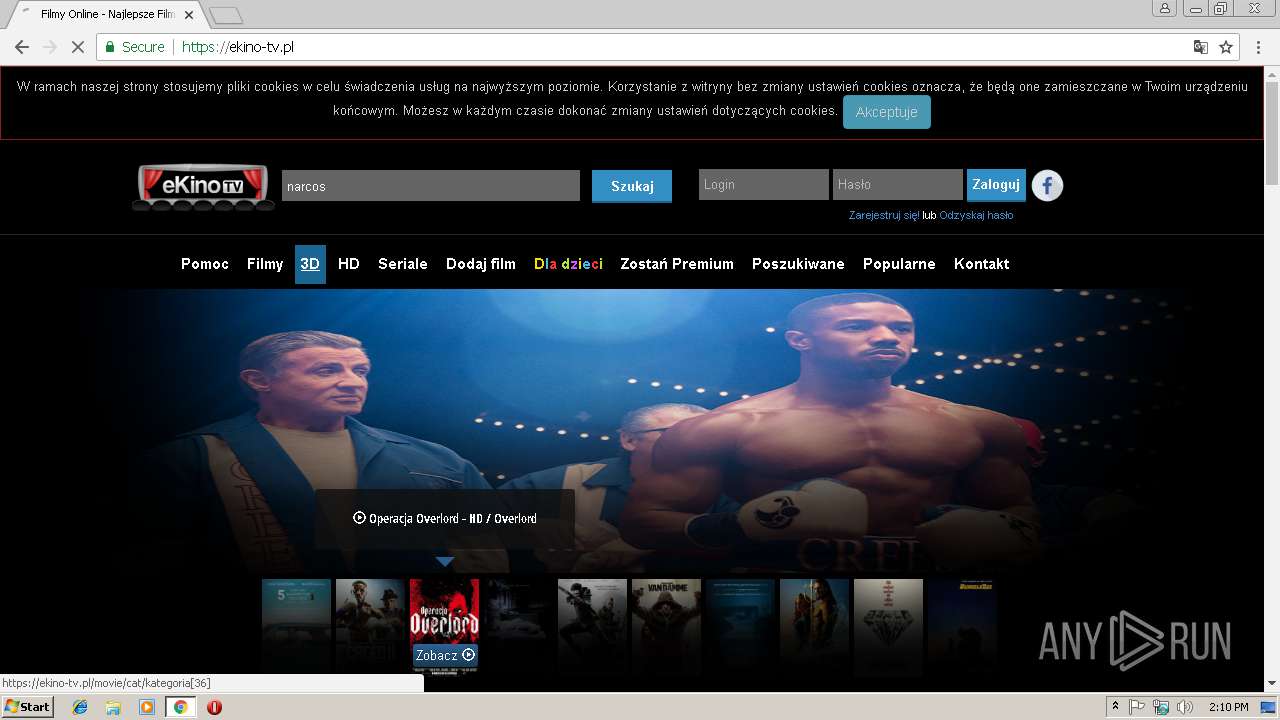
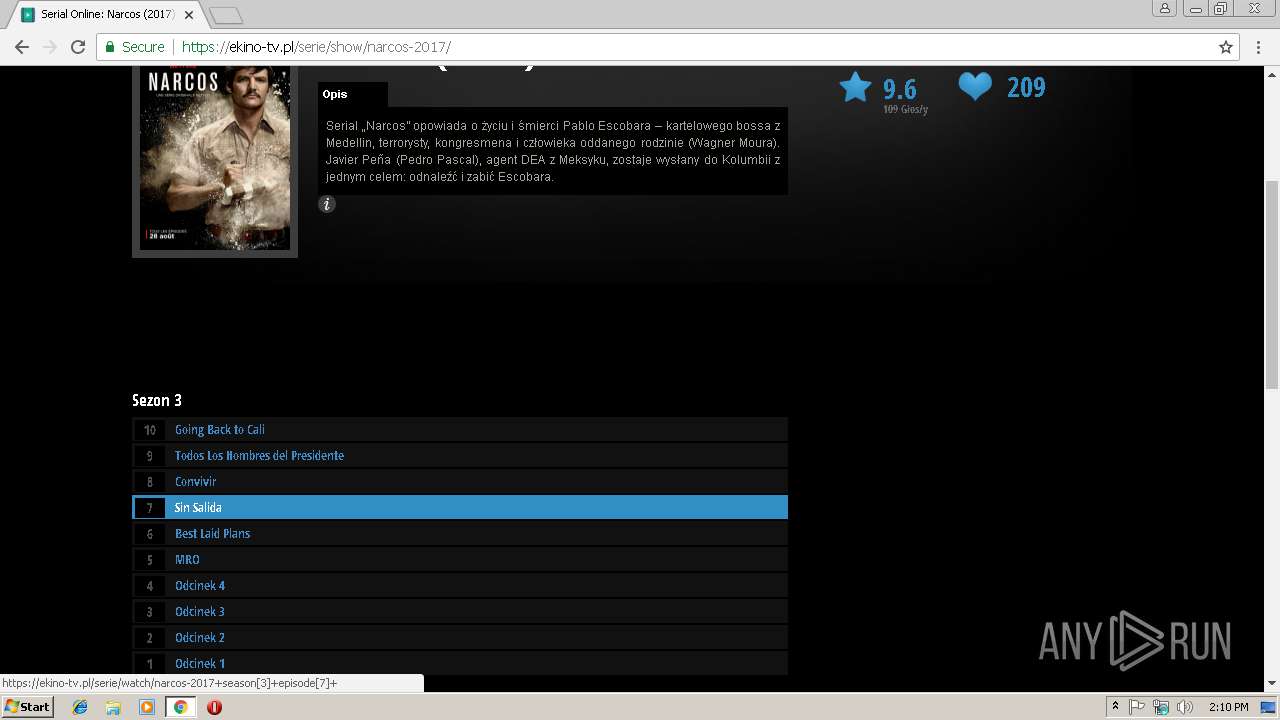
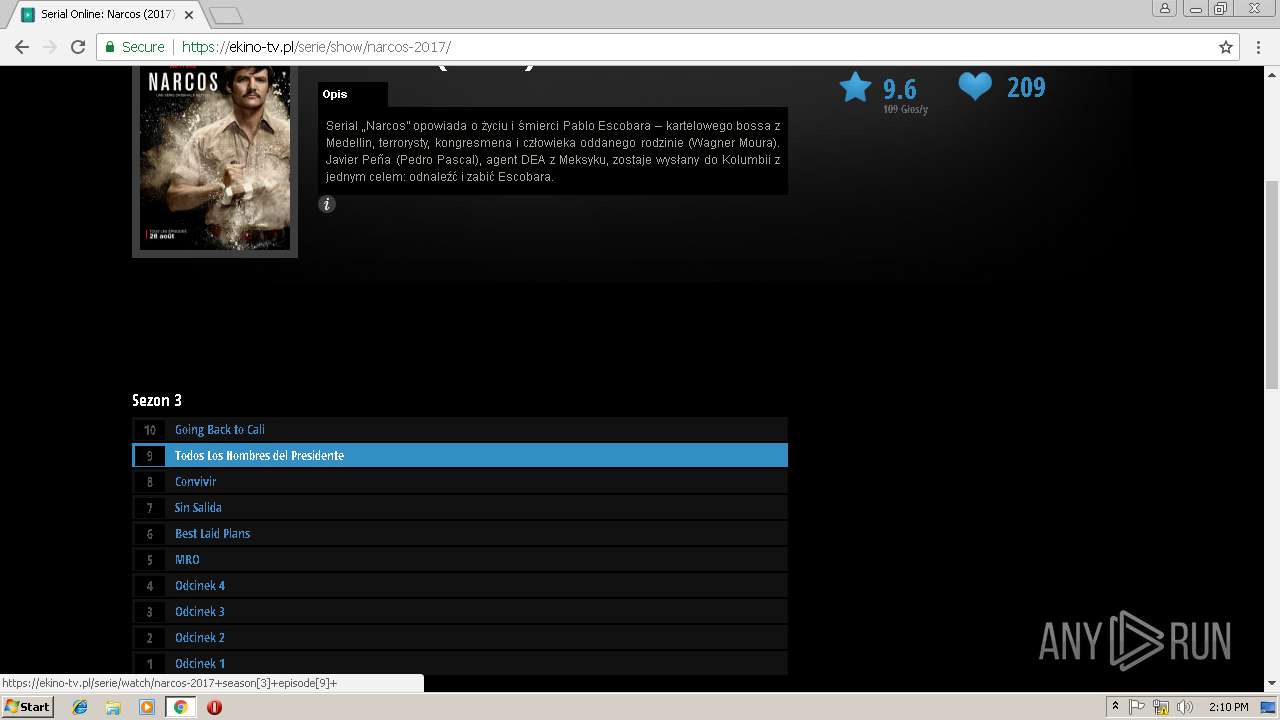
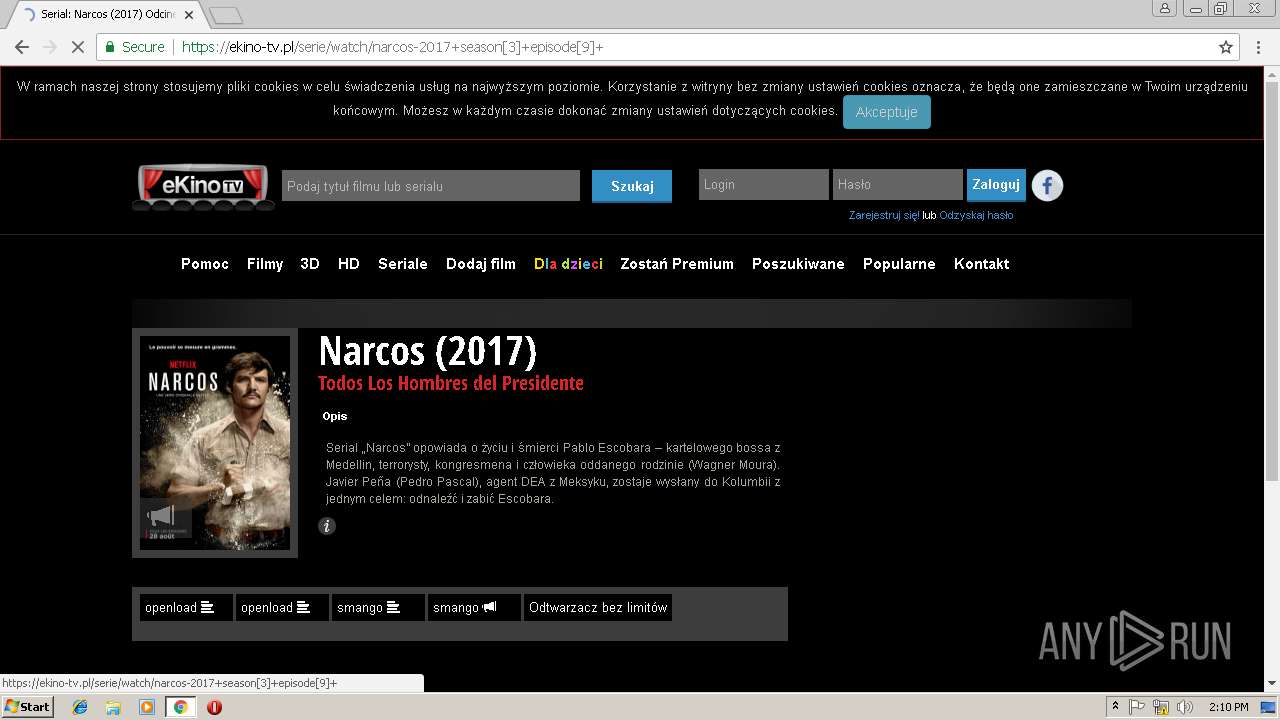
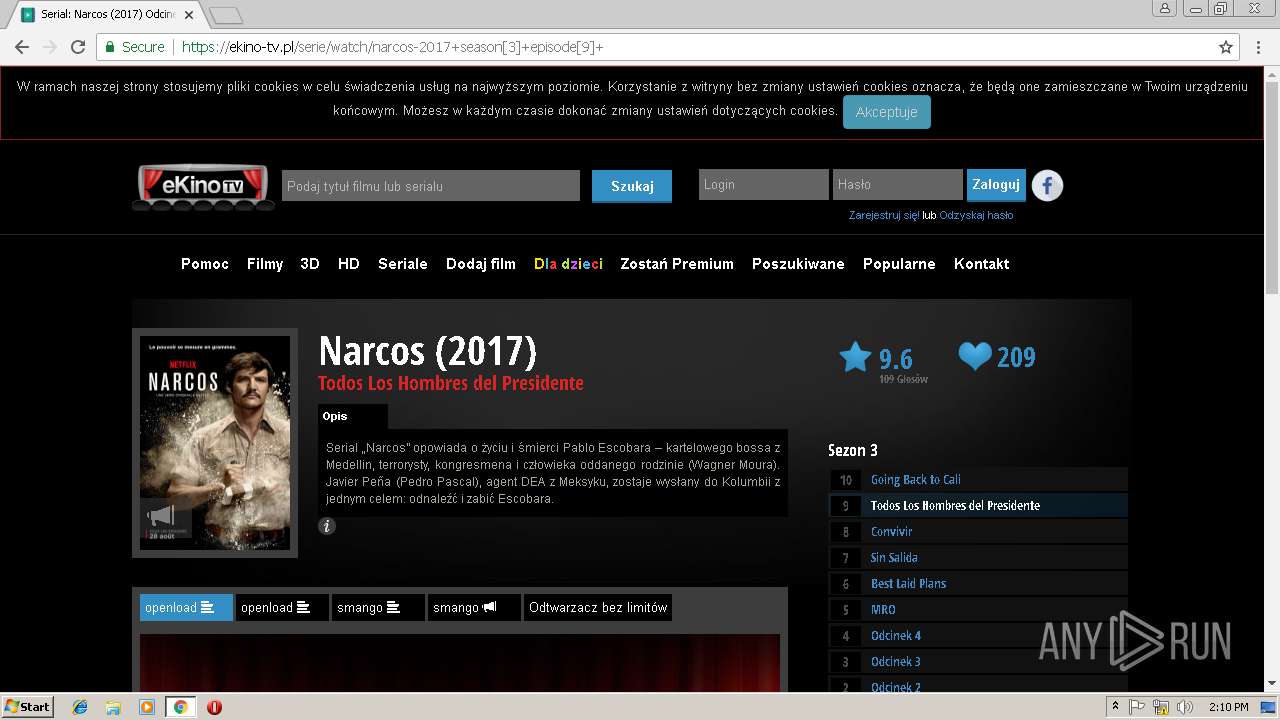
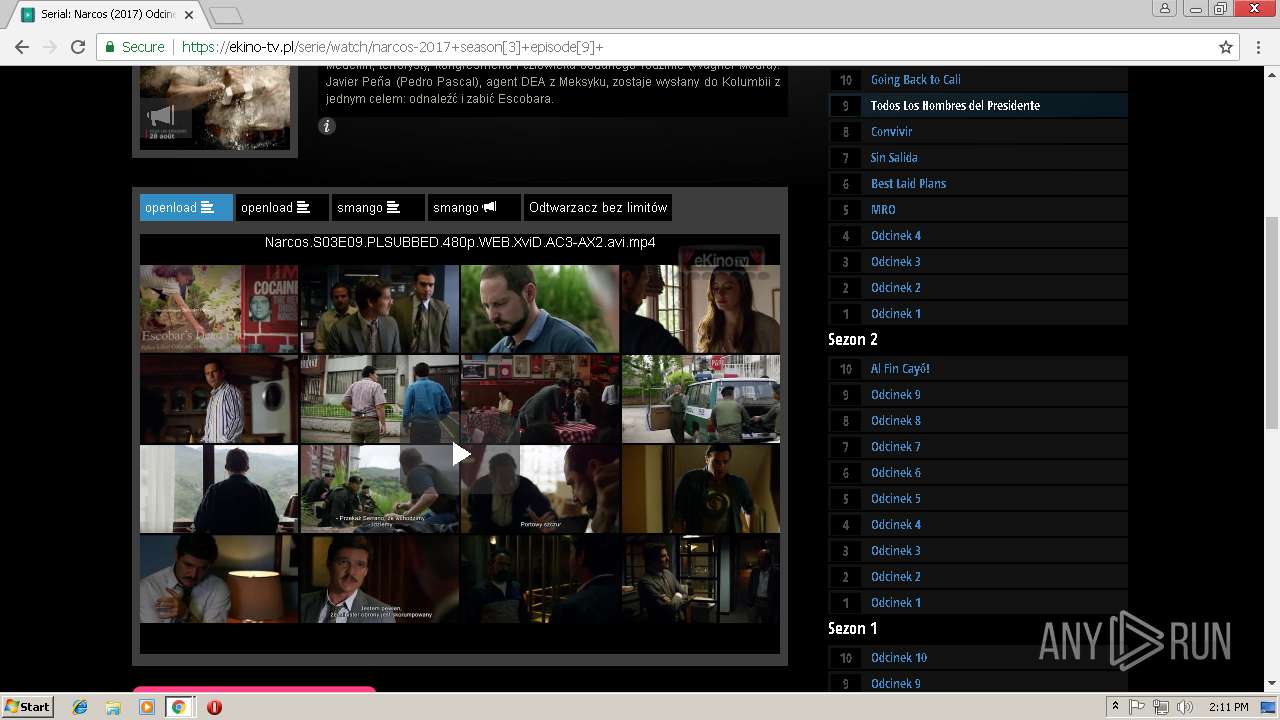
| URL: | https://ekino-tv.pl/watch.php |
| Full analysis: | https://app.any.run/tasks/bfe04ff4-db50-4712-b62f-a58d903c0327 |
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2019, 14:09:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0B4B9323901124AFB125C782BE9BC5A5 |
| SHA1: | 55B17C6245EBD8ABF1E4F1A540689A3C71688D50 |
| SHA256: | 1EC033D70617AA859931150D319FA80CC6DA68E7F39347D06DD19BCD2636520B |
| SSDEEP: | 3:N8kDKSERYn:28Kan |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 2980)
Application launched itself
- chrome.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D24AAD625AB16B6FA0E38663173B429A --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --service-pipe-token=7D54F1FD2EBDA03F550594F9872F4BC4 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7D54F1FD2EBDA03F550594F9872F4BC4 --renderer-client-id=4 --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1776372FEAC7A3421560BF684F873255 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1776372FEAC7A3421560BF684F873255 --renderer-client-id=8 --mojo-platform-channel-handle=516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2984 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://ekino-tv.pl/watch.php | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=542C179489F6C1F7A4624BEF0309858A --mojo-platform-channel-handle=3068 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi --field-trial-handle=988,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=4E201CE5121F66EEA420CD9F8A054522 --mojo-platform-channel-handle=3744 --ignored=" --type=renderer " /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --service-pipe-token=17B6551D34E6DD072F91D6ADBA1871ED --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17B6551D34E6DD072F91D6ADBA1871ED --renderer-client-id=3 --mojo-platform-channel-handle=2100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,242606157672125368,8062065844879851193,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5918BFD58B5FC1318D0632DA3086A4D5 --mojo-platform-channel-handle=3588 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6000b0,0x6f6000c0,0x6f6000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
590
Read events
539
Write events
48
Delete events
3
Modification events
| (PID) Process: | (2936) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2980-13196441374275875 |
Value: 259 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2980-13196441374275875 |
Value: 259 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
33
Text files
126
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1f26b8eb-87d5-4a32-b245-296b04b7c2a1.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\da626548-4c12-4ec4-98d0-dc0a748240b4.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF198c29.TMP | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF198c58.TMP | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
64
DNS requests
46
Threats
48
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2980 | chrome.exe | GET | 302 | 104.18.34.51:80 | http://beautytips.fun/ | US | — | — | suspicious |
2980 | chrome.exe | GET | 200 | 95.211.229.247:80 | http://syndication.exosrv.com/splash-zones-split.php?st=ref&main_zone=2792946&type=8&sub=5&ref=https%3A%2F%2Fekino-tv.pl%2Fwatch%2Ff%2Fopenload%2FlAa0Mt4UdGyXxxB4rblhlkGJK9wQYp-iK-Ex | NL | html | 621 b | whitelisted |
2980 | chrome.exe | GET | 302 | 95.211.229.247:80 | http://syndication.exosrv.com/splash-zones-split.php?st=ref&main_zone=2792946&type=8&sub=5&ref=https%3A%2F%2Fekino-tv.pl%2Fwatch%2Ff%2Fopenload%2FlAa0Mt4UdGyXxxB4rblhlkGJK9wQYp-iK-Ex&tested=1&check=a31b5a09a4064f651c12c8b2cfeac301&screen_resolution=1280x720&container_resolution=1274x662&iframe=0 | NL | compressed | 621 b | whitelisted |
2980 | chrome.exe | GET | 200 | 104.37.178.1:80 | http://cdn.welcome.pussysaga.com/awpx_click.js | US | text | 671 b | malicious |
2980 | chrome.exe | GET | 200 | 204.155.159.48:80 | http://welcome.cuntwars.com/landings/land/6_1/index.html?aff_cid=5c81267c72cca3000155e0da&aff_oid=34&aff_pid=101&aff_sub1=2579940_2792946&aff_sub2=&aff_sub3=&land=pl4&to=aHR0cHM6Ly90cmFjay5ob29saWdhcHBzLmNvbS9jbGljaz9vZmZlcl9pZD0zNCZwaWQ9MTAxJnN1YjE9MjU3OTk0MF8yNzkyOTQ2 | US | html | 1.67 Kb | unknown |
2980 | chrome.exe | GET | 200 | 18.209.26.215:80 | http://sp.popcash.net/go/219479/464844 | US | html | 271 b | suspicious |
2980 | chrome.exe | GET | 303 | 18.209.26.215:80 | http://sp.popcash.net/ad/ad?p=219479&w=464844&t=e69097065c76b8ee&r=&vw=1270&vh=635 | US | html | 111 b | suspicious |
2980 | chrome.exe | GET | 200 | 104.37.178.1:80 | http://cdn.welcome.cuntwars.com/landings/land/6_1/style.css | US | text | 787 b | malicious |
2980 | chrome.exe | GET | 200 | 204.155.147.176:80 | http://ln.gamesrevenue.com/px1.js | US | text | 8.28 Kb | suspicious |
2980 | chrome.exe | GET | 200 | 104.37.178.1:80 | http://cdn.welcome.cuntwars.com/landings/land/6_1/img/line3.png | US | image | 291 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 54.172.47.69:3478 | stun.services.mozilla.com | Amazon.com, Inc. | US | whitelisted |
2980 | chrome.exe | 104.27.147.19:443 | ekino-tv.pl | Cloudflare Inc | US | shared |
2980 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 216.58.207.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 104.19.197.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
2980 | chrome.exe | 172.217.18.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 216.58.205.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
ekino-tv.pl |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
cdnjs.cloudflare.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2980 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2980 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2980 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2980 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |