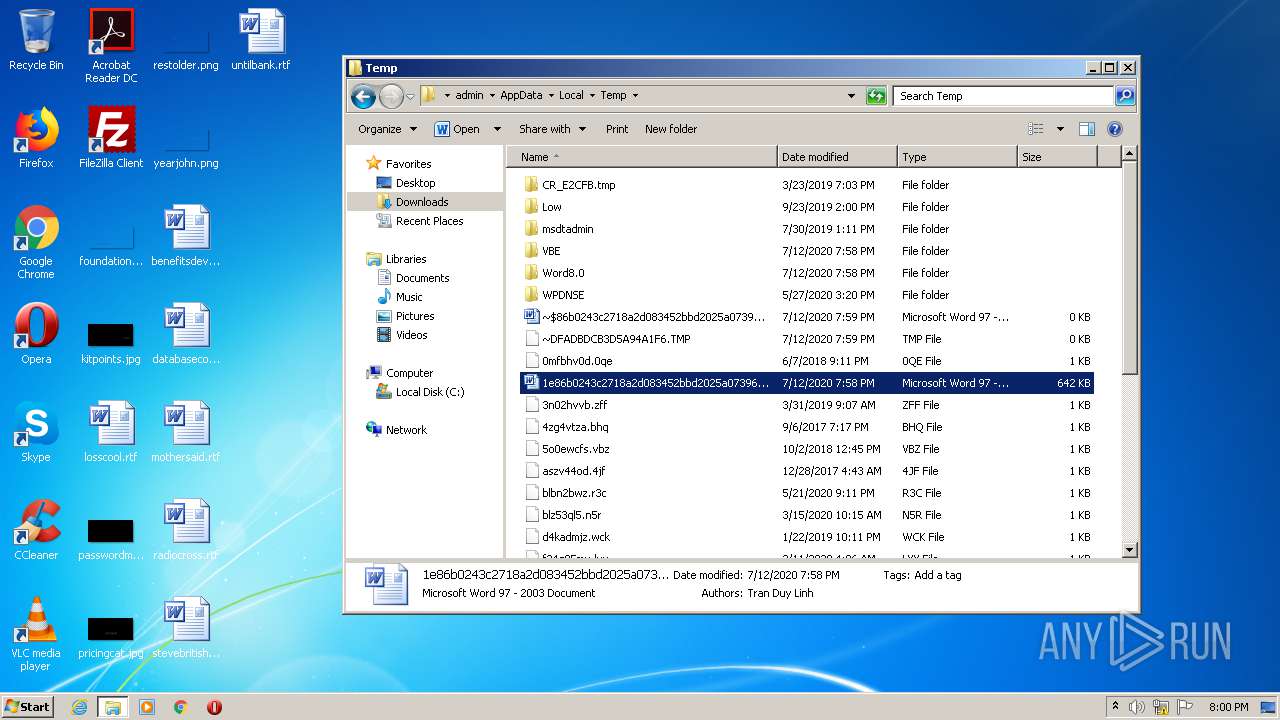
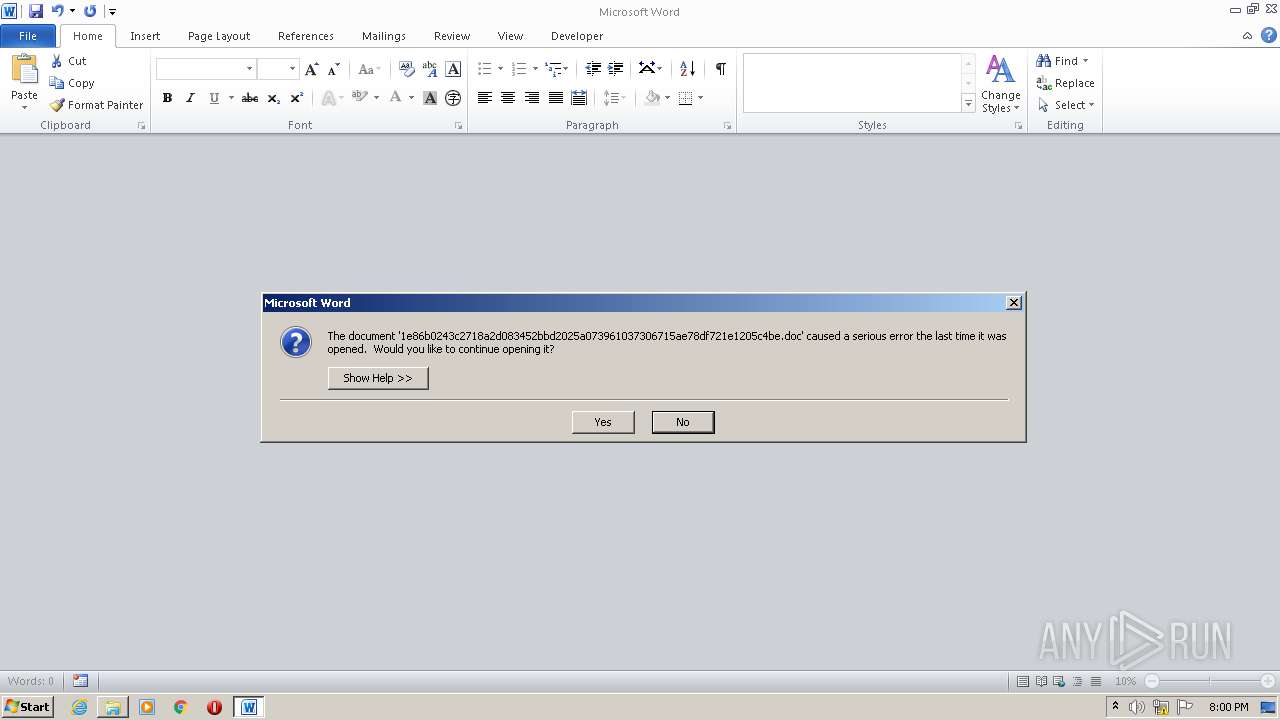
| File name: | 1e86b0243c2718a2d083452bbd2025a073961037306715ae78df721e1205c4be |
| Full analysis: | https://app.any.run/tasks/3912a99e-c6c7-41f7-9b41-358ce4c2f610 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 18:58:37 |
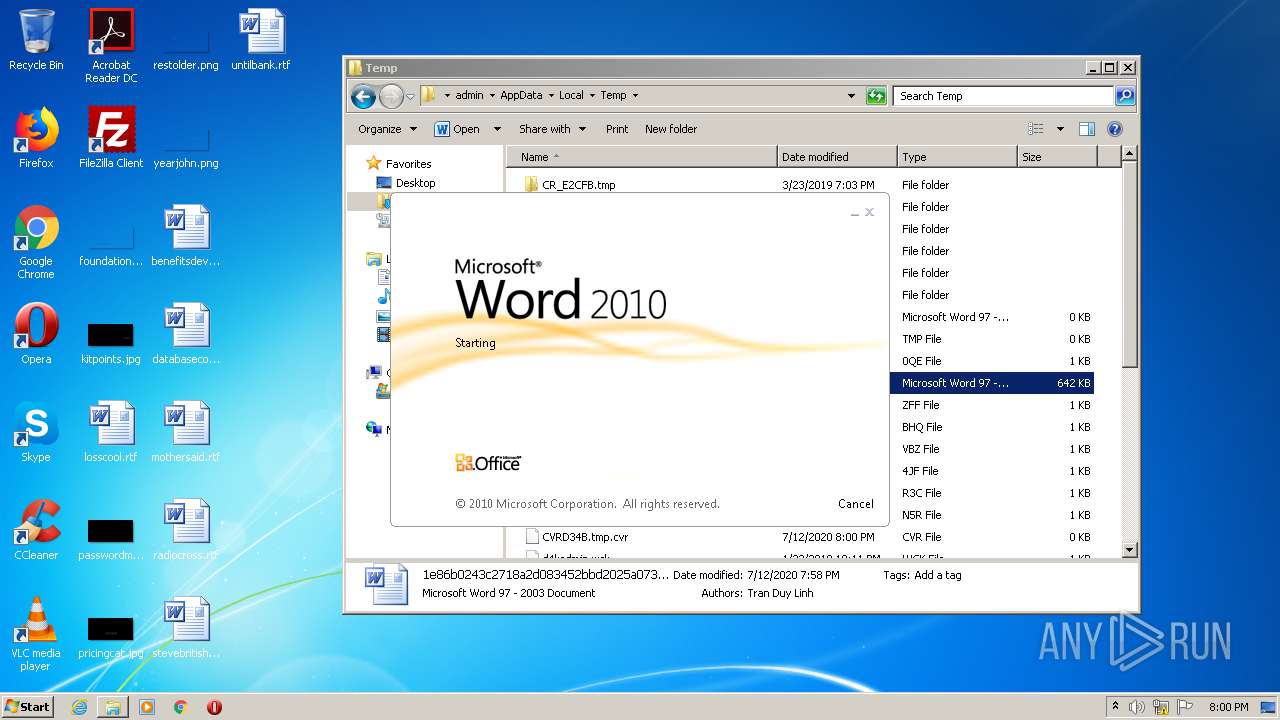
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 5.1, Code page: 949, Author: Tran Duy Linh, Template: Normal.dotm, Last Saved By: Tran Duy Linh, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Total Editing Time: 04:00, Create Time/Date: Fri Nov 23 04:35:00 2012, Last Saved Time/Date: Fri Nov 23 04:39:00 2012, Number of Pages: 1, Number of Words: 5, Number of Characters: 34, Security: 0 |
| MD5: | 8B14A1112979610E9714266676774340 |
| SHA1: | 15CED24005A13DEFA7BFCCF944D7792A1D164A7A |
| SHA256: | 1E86B0243C2718A2D083452BBD2025A073961037306715AE78DF721E1205C4BE |
| SSDEEP: | 12288:XgJyYU1qgqREBuHQO78VKorX72JgPufrNh6stzz:XgCqREQHQOoVXXHPufBhbz |
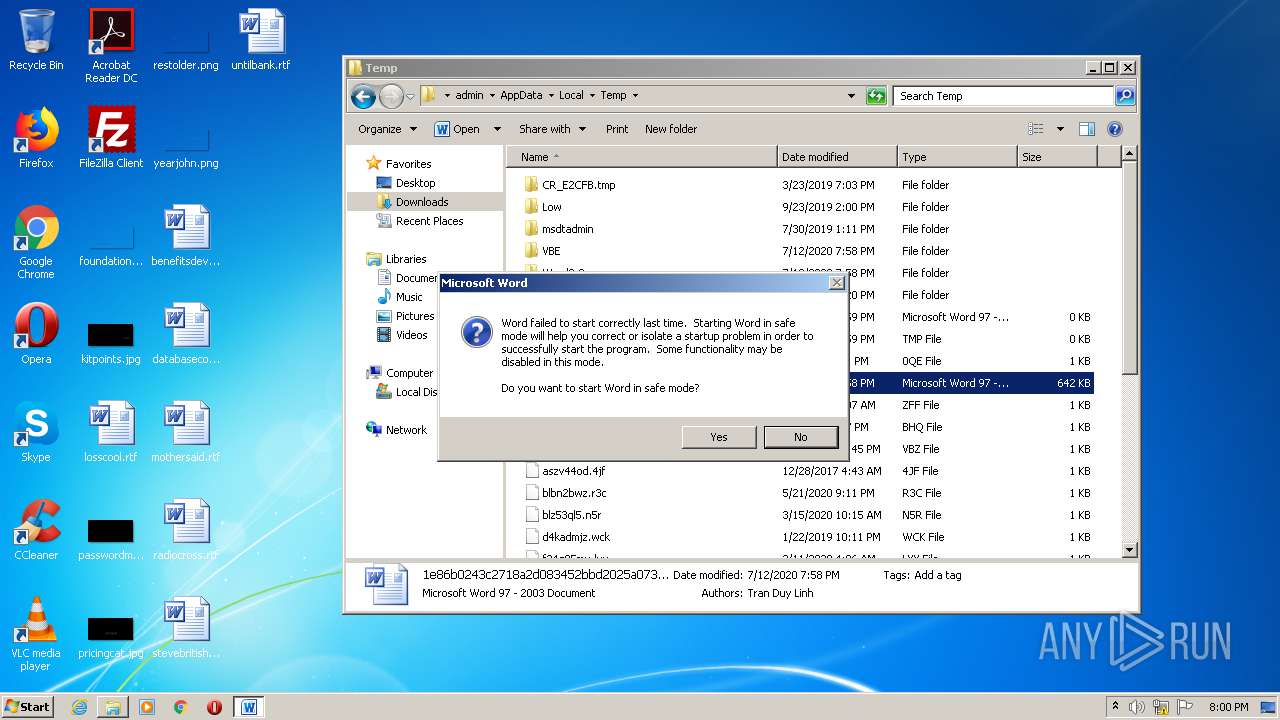
MALICIOUS
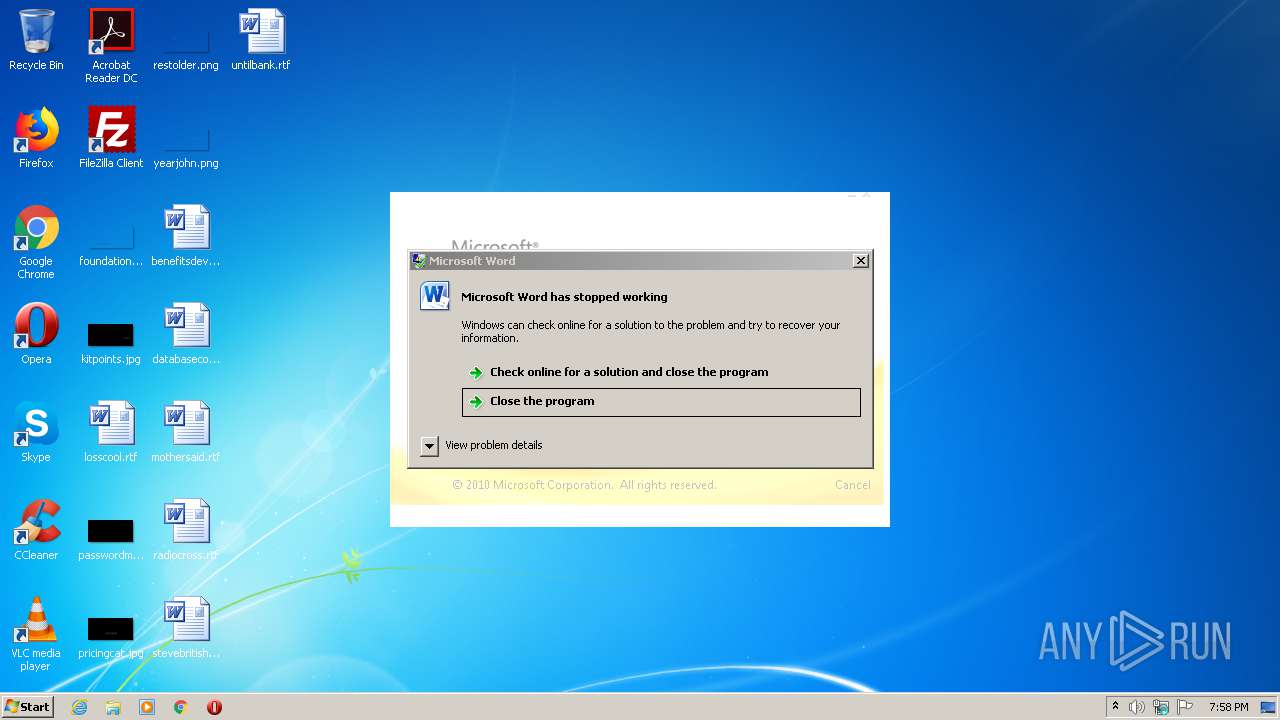
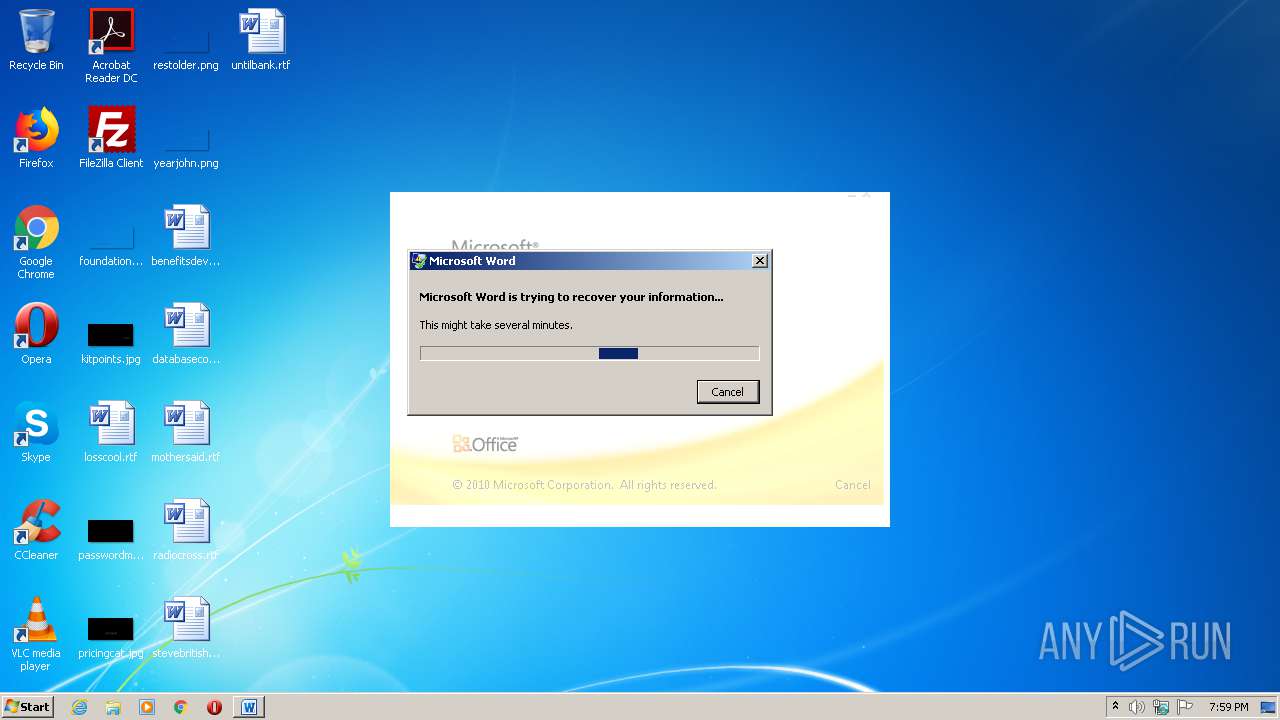
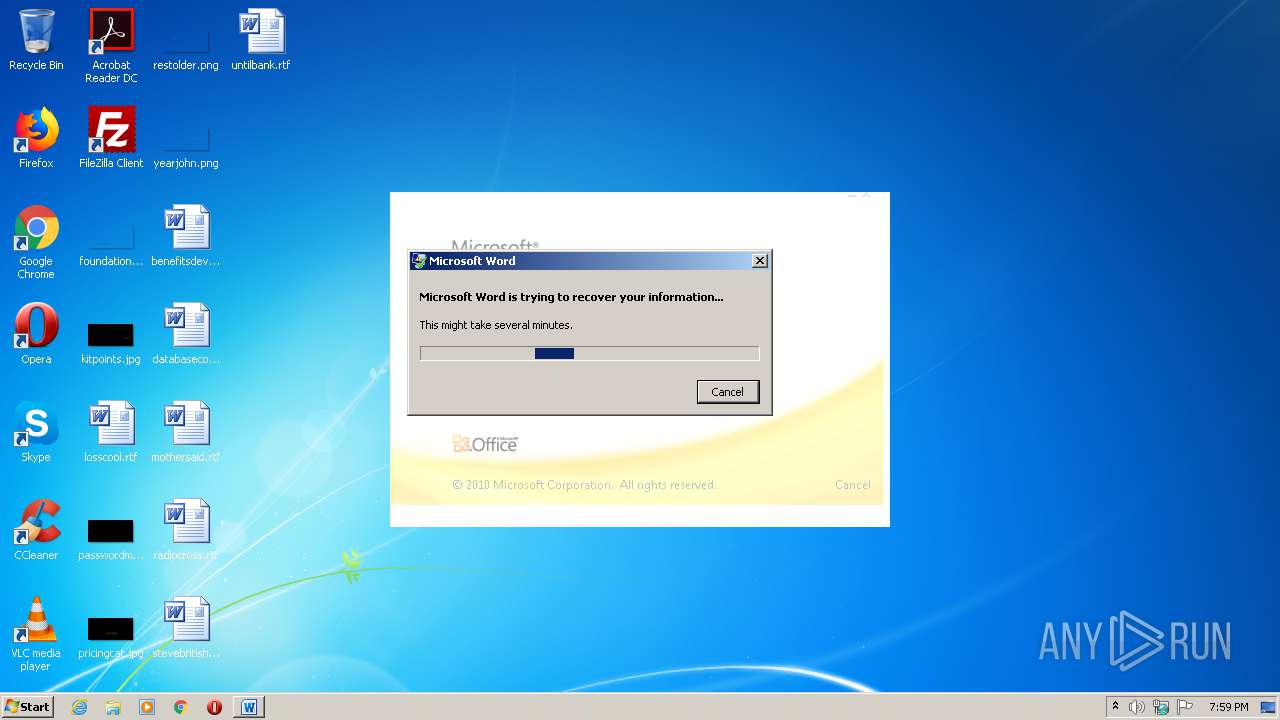
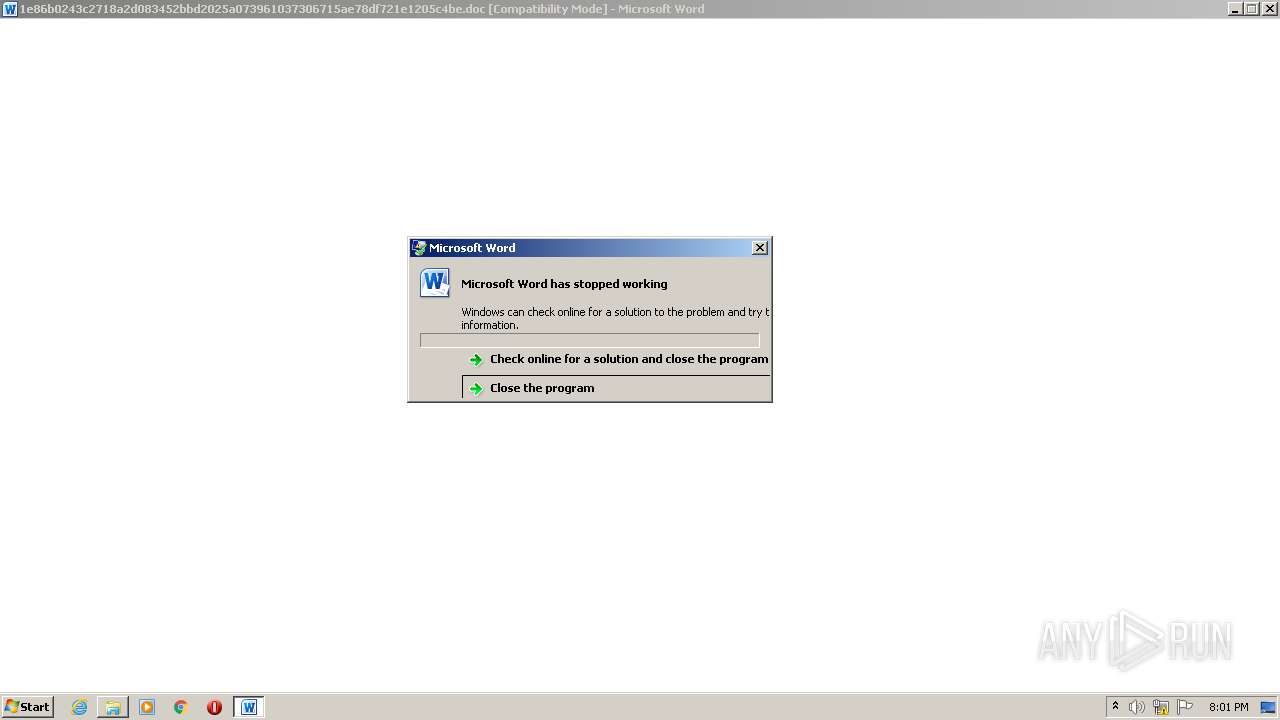
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1868)
- WINWORD.EXE (PID: 744)
SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1868)
- WINWORD.EXE (PID: 744)
Creates files in the user directory
- WINWORD.EXE (PID: 1868)
Manual execution by user
- WINWORD.EXE (PID: 744)
- explorer.exe (PID: 996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Subject: | - |
|---|---|
| Author: | Tran Duy Linh |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Tran Duy Linh |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 4.0 minutes |
| CreateDate: | 2012:11:23 04:35:00 |
| ModifyDate: | 2012:11:23 04:39:00 |
| Pages: | 1 |
| Words: | 5 |
| Characters: | 34 |
| Security: | None |
| CodePage: | Windows Korean (Unified Hangul Code) |
| Company: | DLC Corporation |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 38 |
| AppVersion: | 12 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 39 |
| CompObjUserType: | Microsoft Office Word 97-2003 Document |
Total processes
43
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
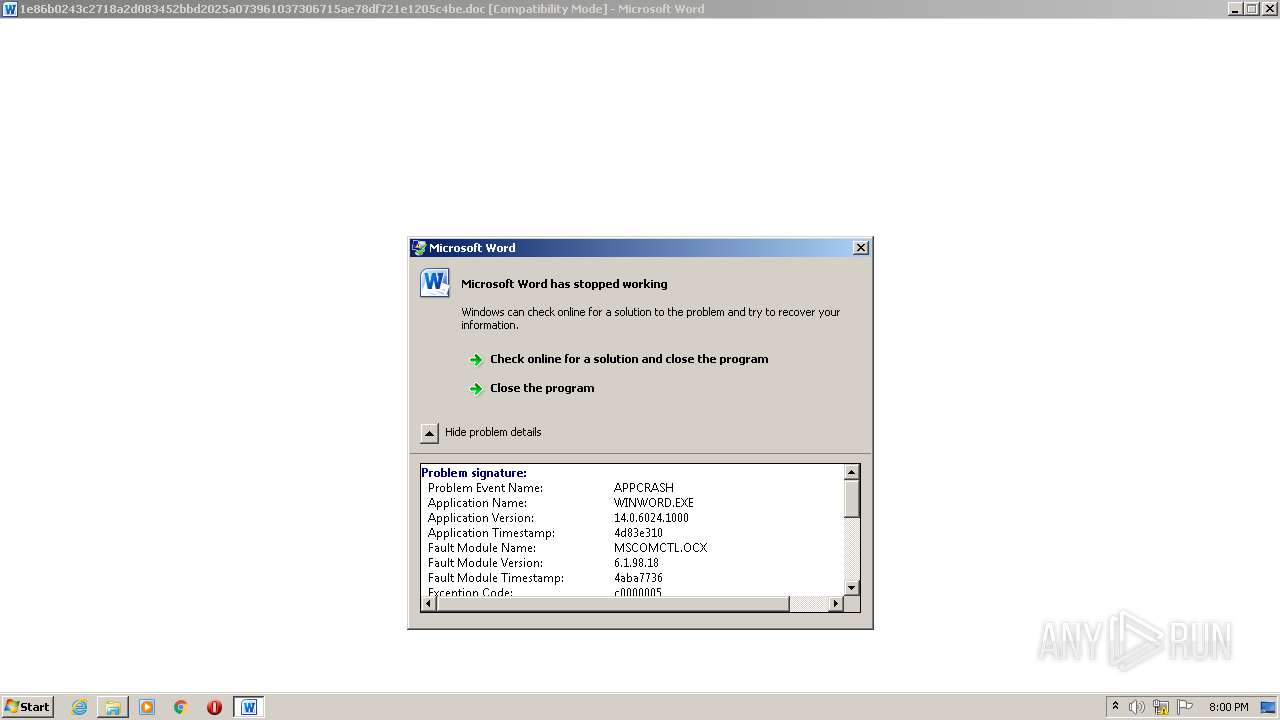
| 400 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 1368 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\1e86b0243c2718a2d083452bbd2025a073961037306715ae78df721e1205c4be.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 996 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\1e86b0243c2718a2d083452bbd2025a073961037306715ae78df721e1205c4be.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3364 | C:\Windows\system32\dwwin.exe -x -s 1368 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3620 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 1408 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
| 3948 | C:\Windows\system32\dwwin.exe -x -s 1408 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 922
Read events
1 696
Write events
181
Delete events
45
Modification events
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | j/7 |
Value: 6A2F37004C070000010000000000000000000000 | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
7
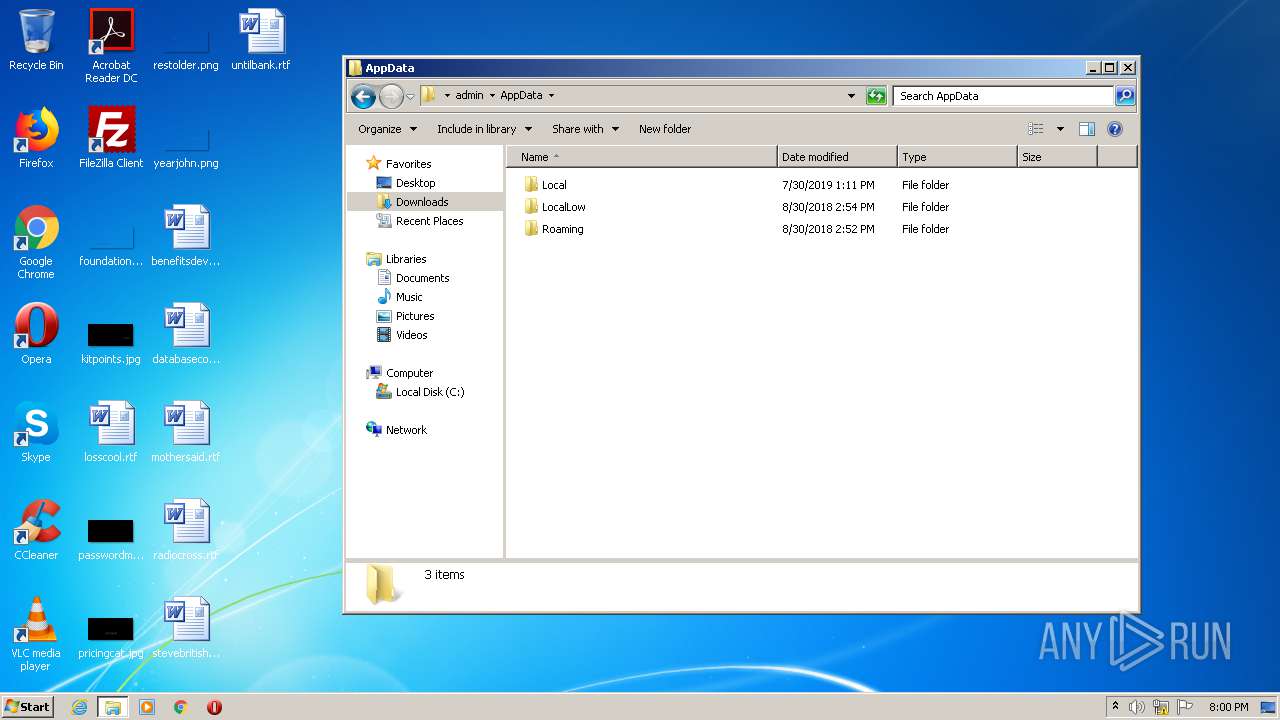
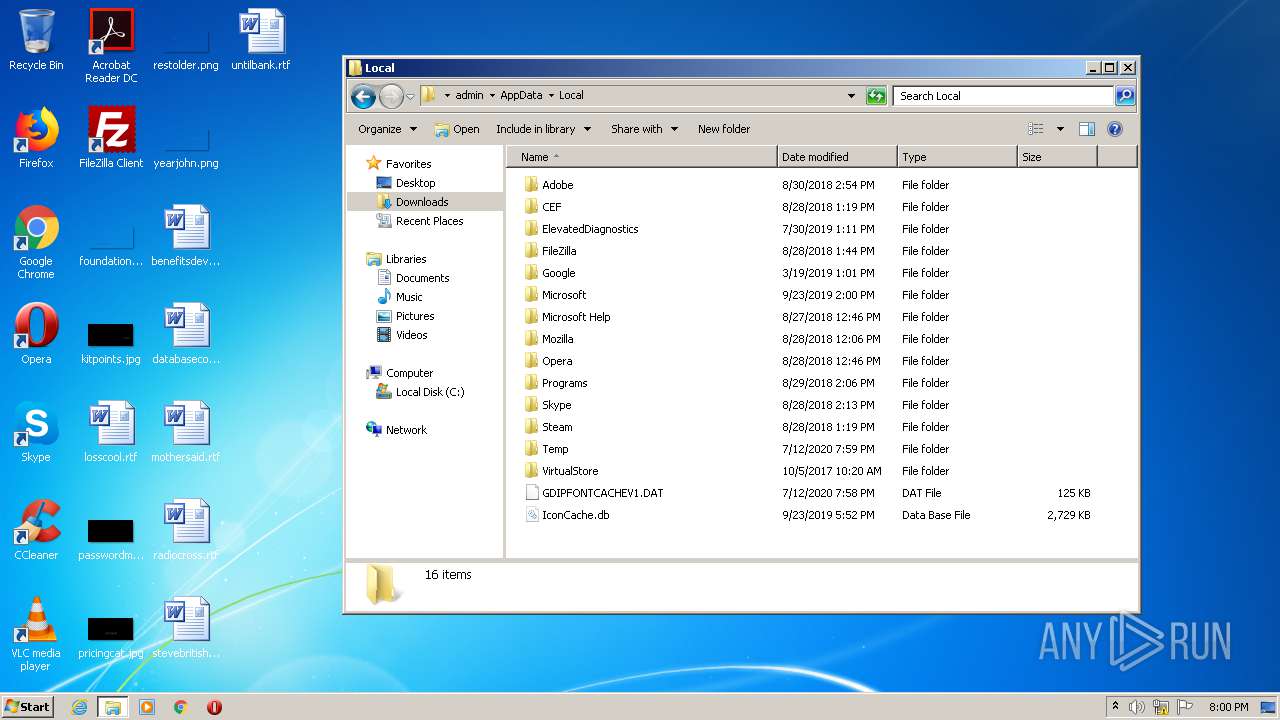
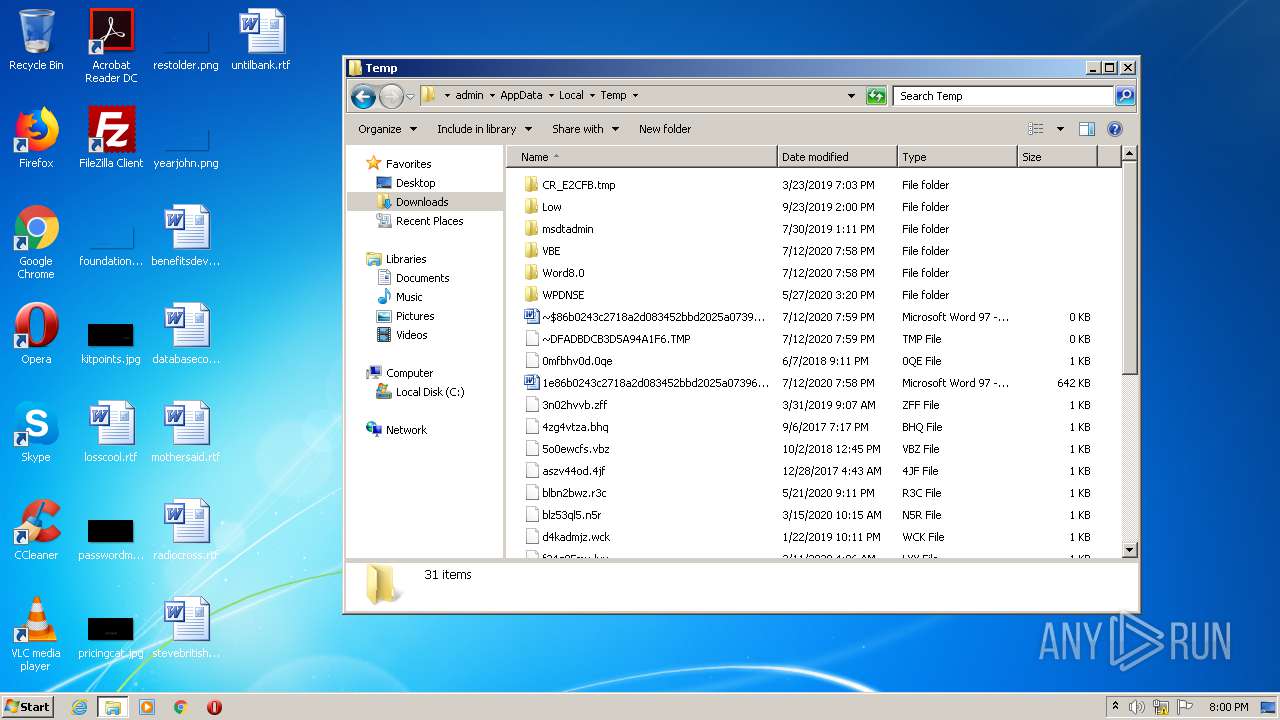
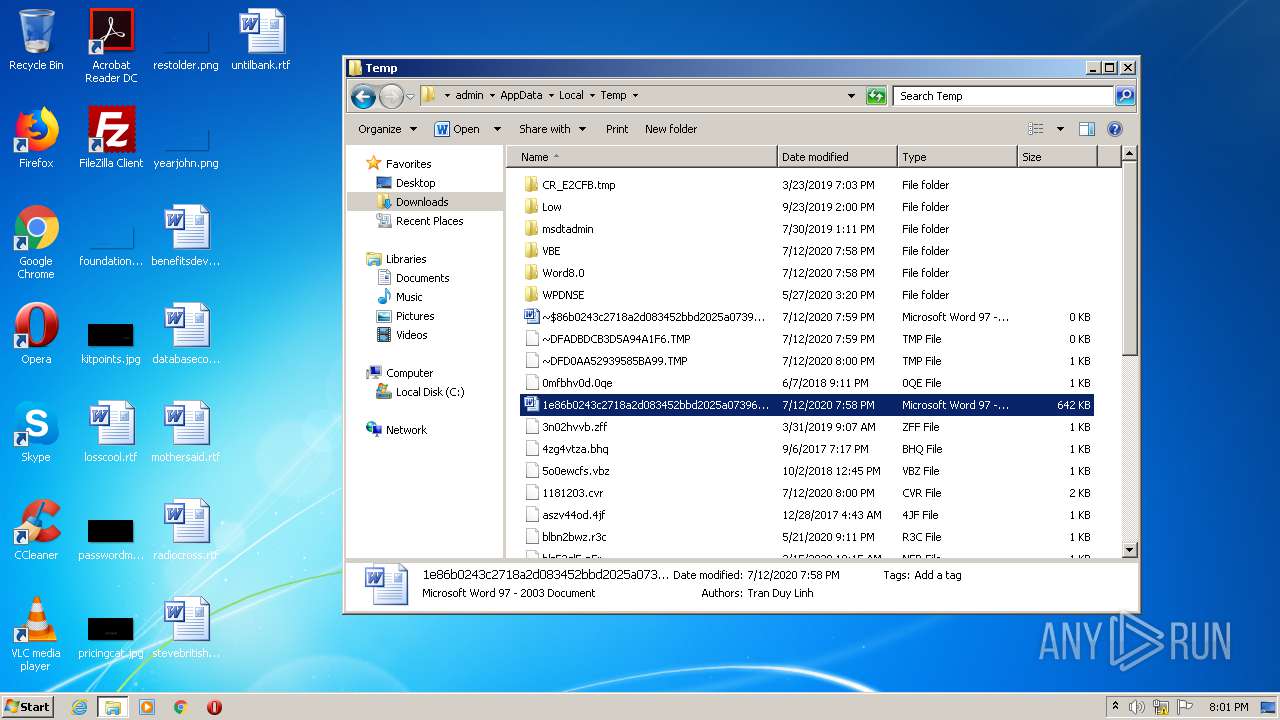
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR73DA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{59E12908-C2F7-4B72-8A85-25F33C7C38FE}.tmp | — | |
MD5:— | SHA256:— | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFADBDCB3D5A94A1F6.TMP | — | |
MD5:— | SHA256:— | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{D2335ADD-A403-4539-A10D-7B4A753DB3A1}.tmp | — | |
MD5:— | SHA256:— | |||
| 744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD34B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{39F9E309-9AE4-47B3-94E5-2D43904C653E}.tmp | — | |
MD5:— | SHA256:— | |||
| 744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD0AA52939585BA99.TMP | — | |
MD5:— | SHA256:— | |||
| 744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{669F926C-66CF-4361-A775-F83E89ACFEE1}.tmp | — | |
MD5:— | SHA256:— | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3364 | dwwin.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_WINWORD.EXE_cf67fe54793bee3a7b2969c253f078b28c4710_0d34ac7e\Report.wer | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report