| File name: | 1e78ebbfb5fd1ee66f44030d52f80806d184e6daa00dd7aaa1a30b53c629912d |
| Full analysis: | https://app.any.run/tasks/9d9b8ce4-34b7-4fc9-8804-a8731502cfed |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 08:17:08 |
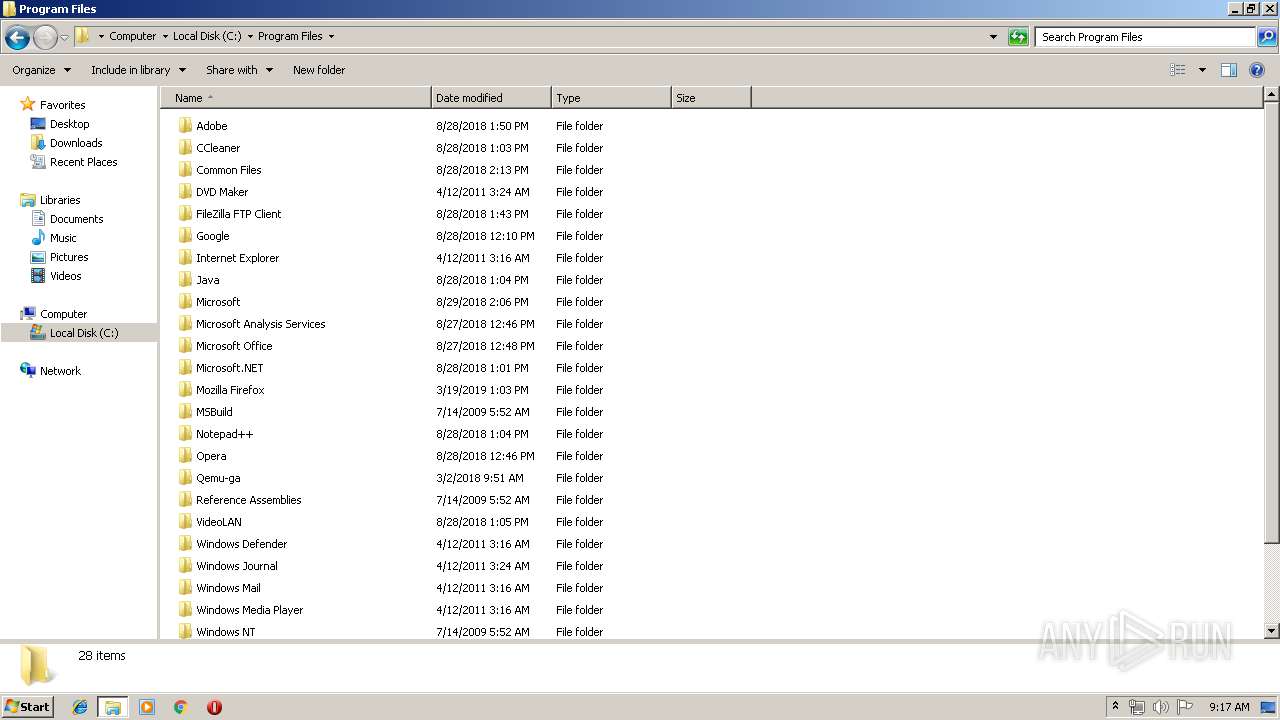
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 853136F00E87A1AB3E2FC3ACB309573E |
| SHA1: | E062AA5F39DF2DF55006331DB957D959A0910699 |
| SHA256: | 1E78EBBFB5FD1EE66F44030D52F80806D184E6DAA00DD7AAA1A30B53C629912D |
| SSDEEP: | 24576:k07XkFxxHMU02eFMeoEi1t/vRZDxkYL9qWGqfbTNBeiEINYH8vGdNDNUoloB+4o2:e |
MALICIOUS
Writes file to Word startup folder
- EQNEDT32.EXE (PID: 2156)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2280)
Loads dropped or rewritten executable
- WINWORD.EXE (PID: 2280)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2280)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2280)
Changes the autorun value in the registry
- WINWORD.EXE (PID: 2280)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3652)
- cmd.exe (PID: 3904)
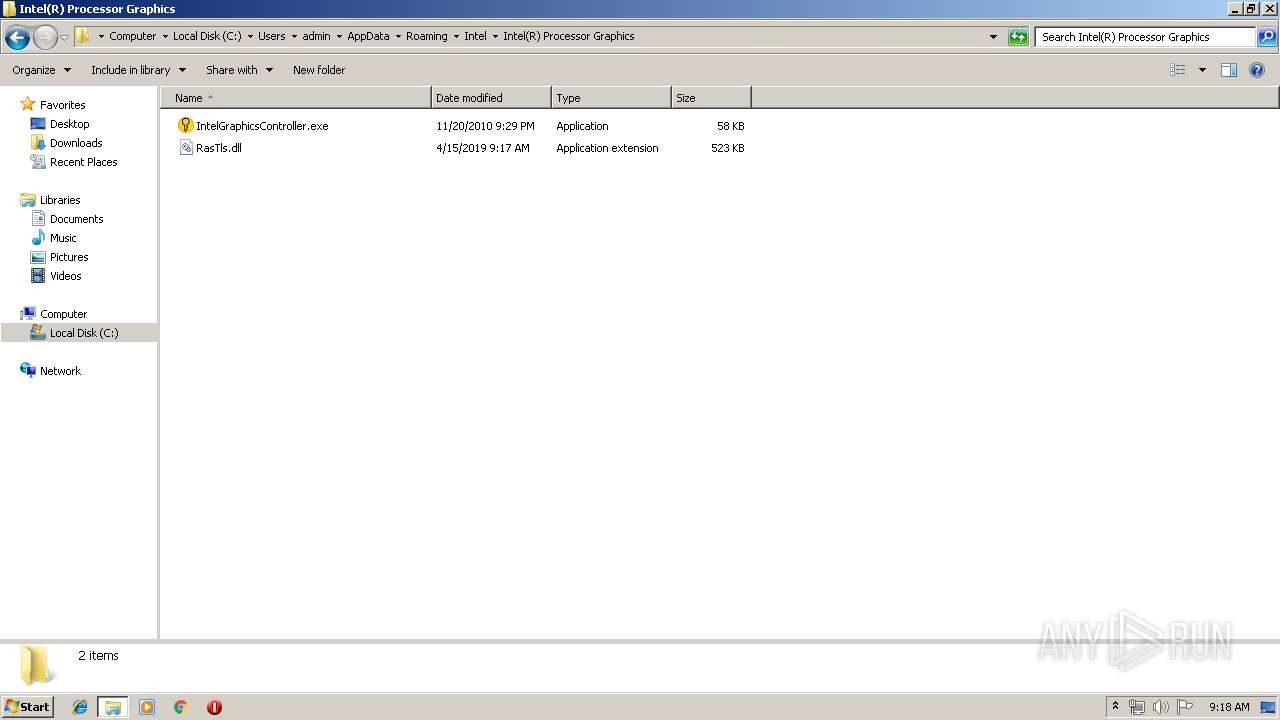
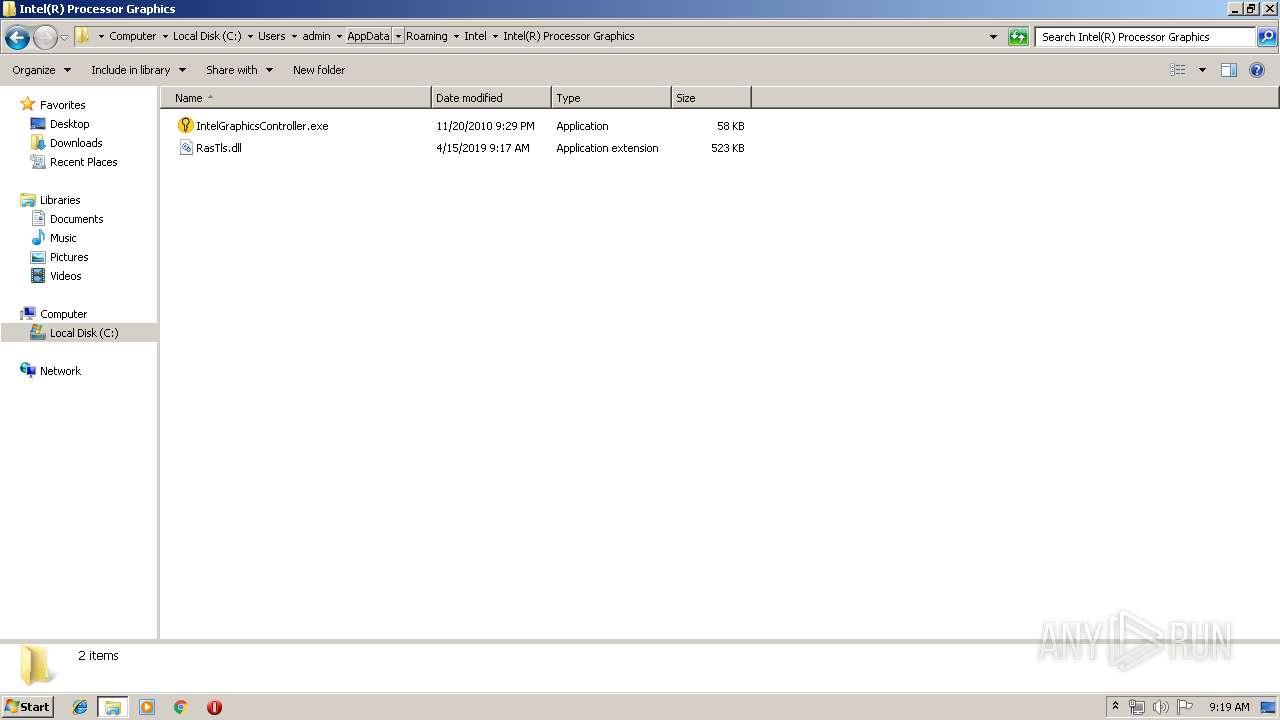
Application was dropped or rewritten from another process
- IntelGraphicsController.exe (PID: 2204)
SUSPICIOUS
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 2156)
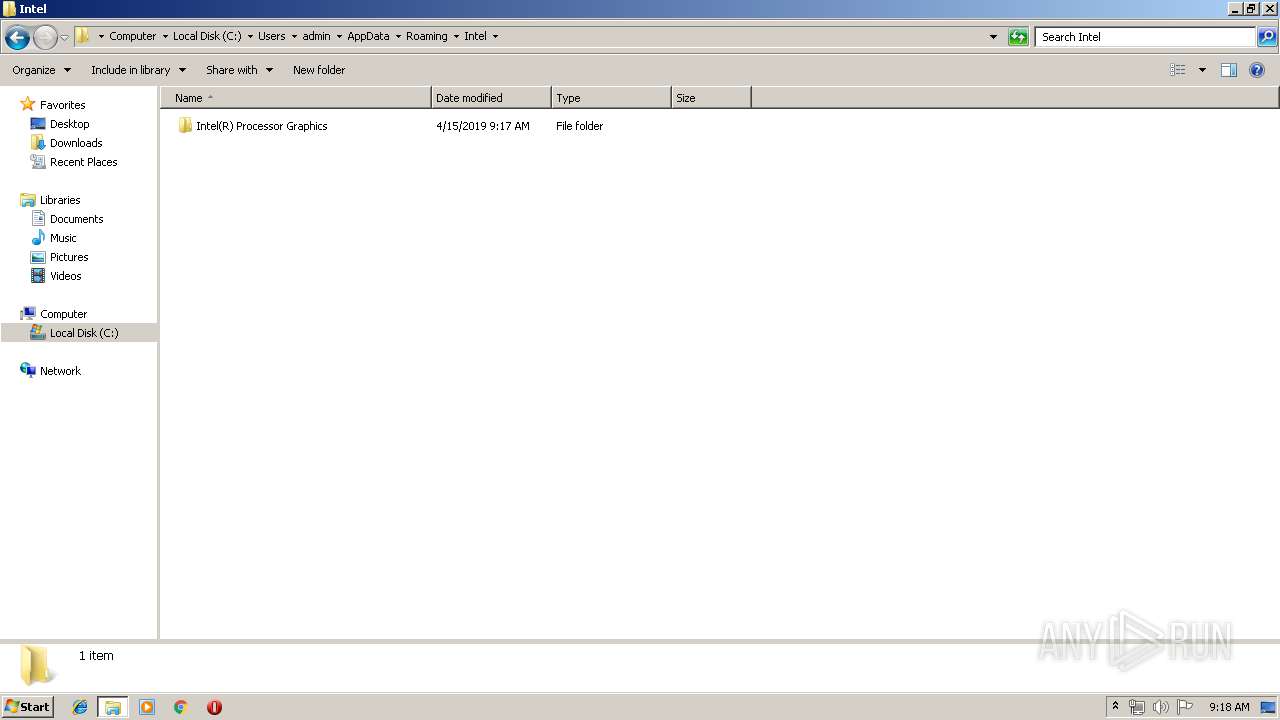
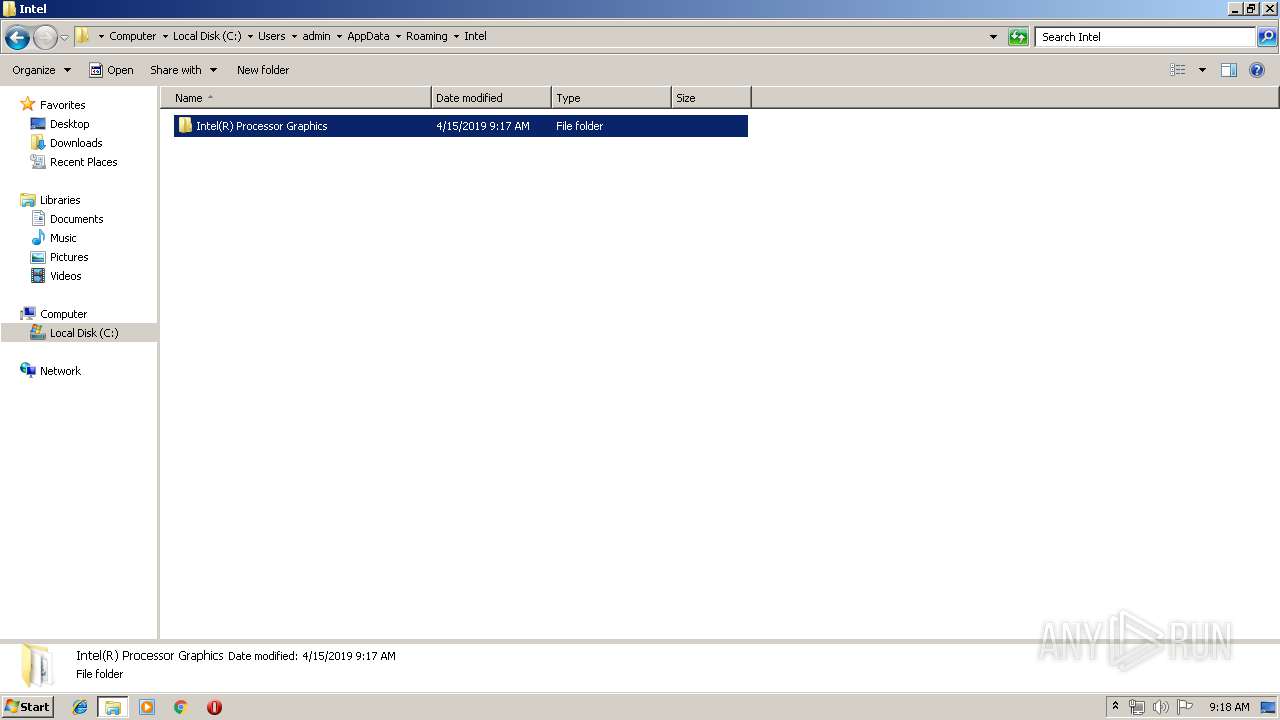
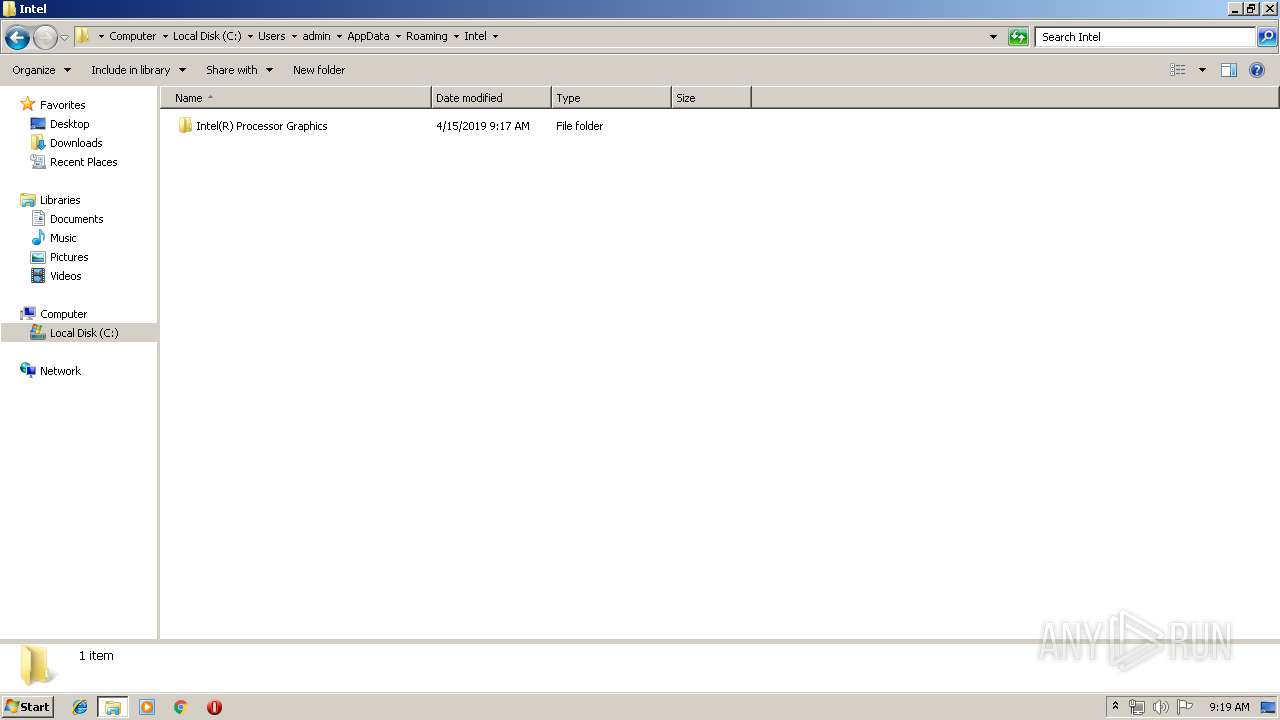
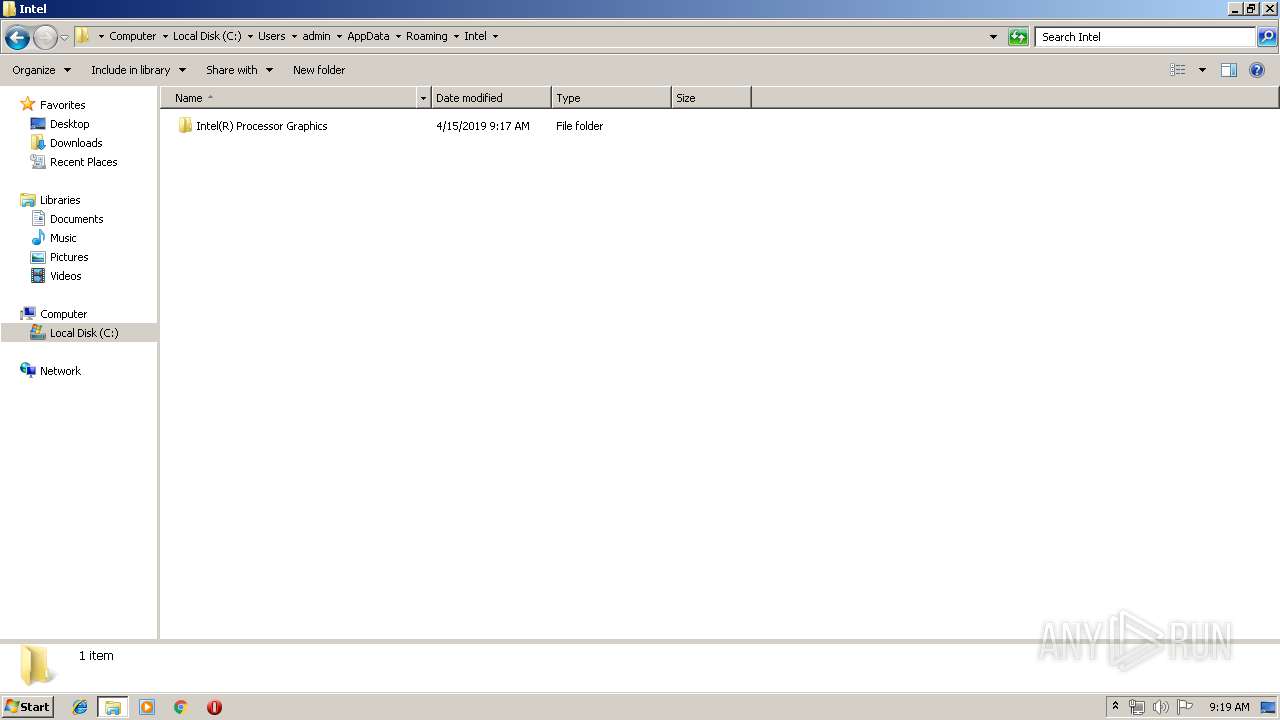
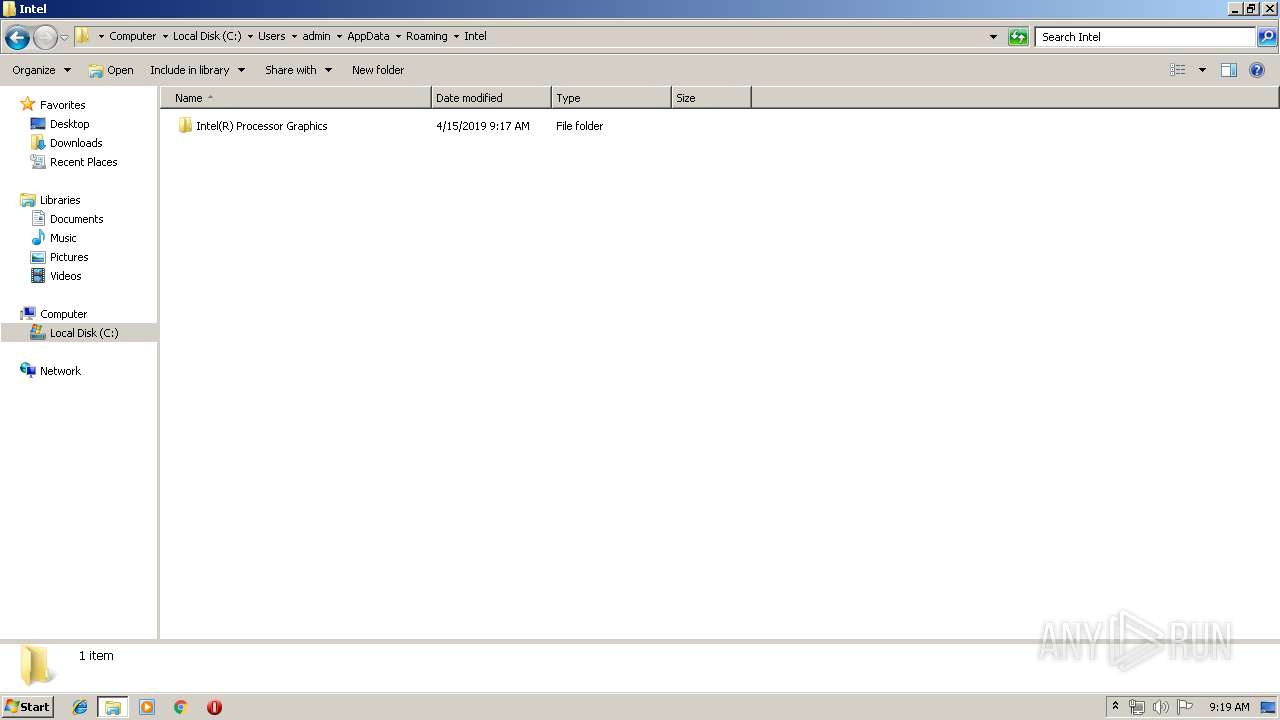
Creates files in the user directory
- EQNEDT32.EXE (PID: 2156)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 3144)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 4080)
- cmd.exe (PID: 3624)
- cmd.exe (PID: 3472)
- cmd.exe (PID: 752)
- cmd.exe (PID: 920)
- cmd.exe (PID: 3740)
Starts CMD.EXE for commands execution
- dllhost.exe (PID: 1864)
- dllhost.exe (PID: 1172)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2680)
- WINWORD.EXE (PID: 2280)
Creates files in the user directory
- WINWORD.EXE (PID: 2680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
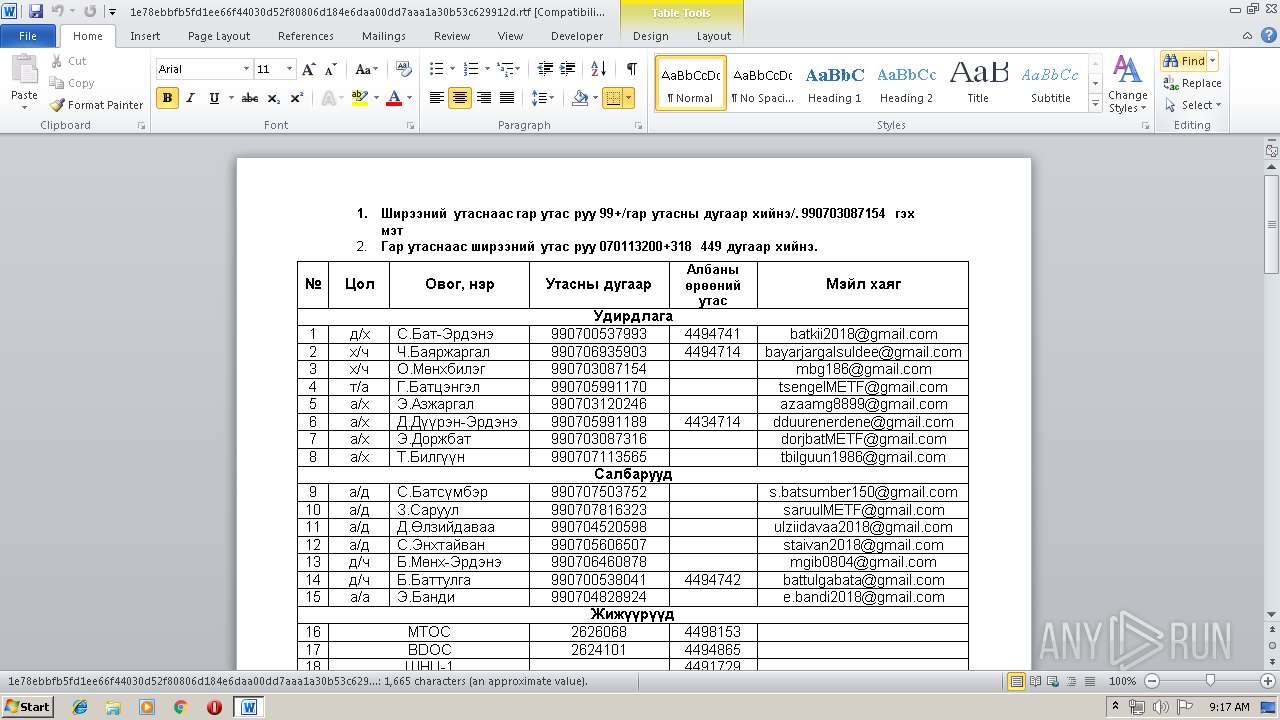
| Author: | chin.sukhbaatar.mng |
|---|---|
| LastModifiedBy: | user |
| CreateDate: | 2019:04:08 04:03:00 |
| ModifyDate: | 2019:04:08 04:03:00 |
| RevisionNumber: | 2 |
| TotalEditTime: | - |
| Pages: | 2 |
| Words: | 295 |
| Characters: | 1687 |
| Company: | US Army |
| CharactersWithSpaces: | 1979 |
| InternalVersionNumber: | 32859 |
Total processes
92
Monitored processes
37
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
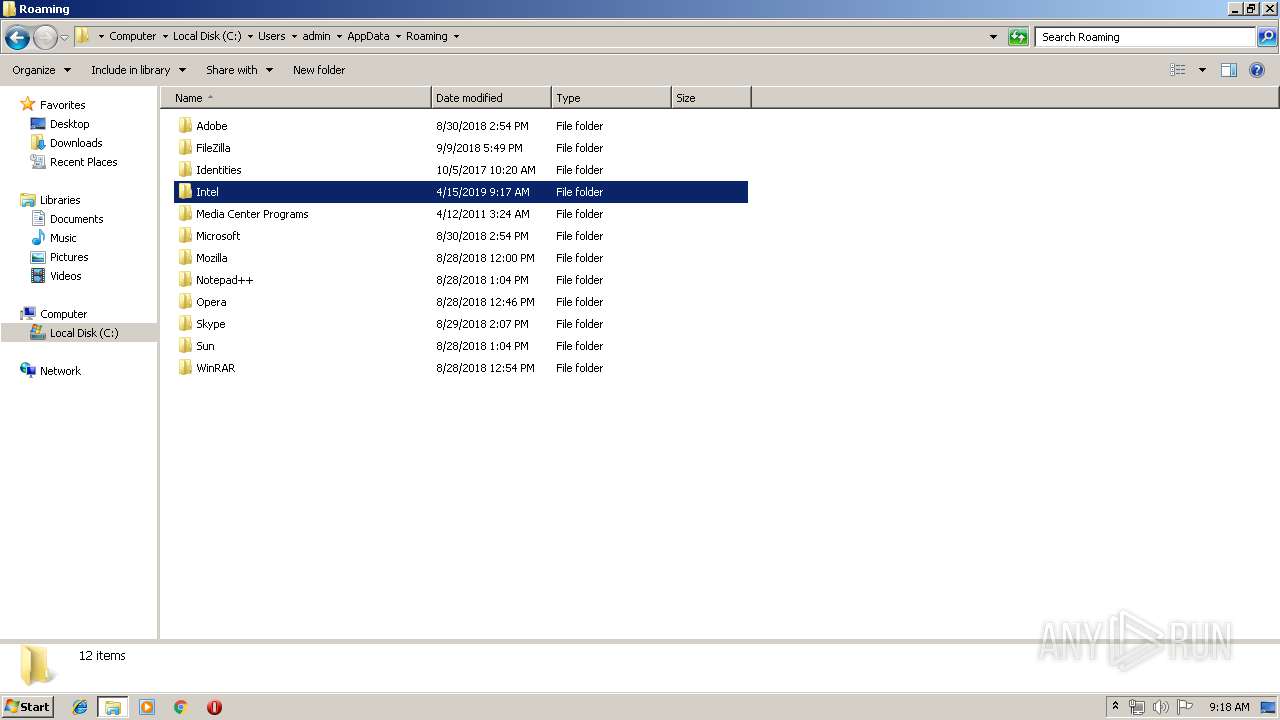
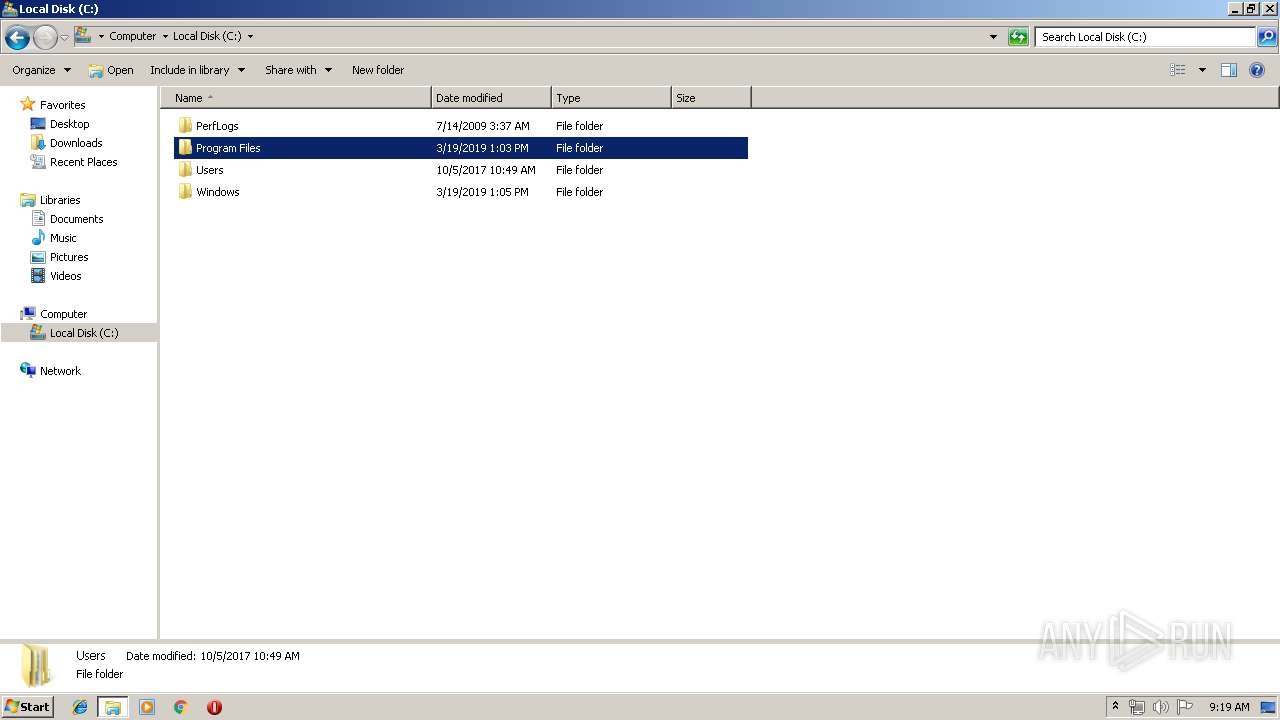
| 352 | C:\Windows\system32\cmd.exe /c "takeown /F "C:\Program Files\Intel\Intel(R) Processor Graphics\RasTls.dll"" | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 608 | Ping 127.0.0.1 -n 10 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | C:\Windows\system32\cmd.exe /c "icacls "C:\Program Files\Intel\Intel(R) Processor Graphics\RasTls.dll" /grant administrators:F" | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 760 | C:\Windows\system32\cmd.exe /c "rd /s/q "C:\ProgramData\Windows\Intel\Up\*"" | C:\Windows\system32\cmd.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 123 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 904 | icacls "C:\Users\admin\AppData\Roaming\Intel\Intel(R) Processor Graphics\IntelGraphicsController.exe" /grant administrators:F | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | C:\Windows\system32\cmd.exe /c "icacls "C:\Program Files\Intel\Intel(R) Processor Graphics\IntelGraphicsController.exe" /grant users:F" | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1172 | C:\Windows\system32\dllhost.exe /Processid:{712459B2-3311-54C3-910D-0415091743743} | C:\Windows\system32\dllhost.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | icacls "C:\Program Files\Intel\Intel(R) Processor Graphics\RasTls.dll" /grant administrators:F | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1548 | takeown /F "C:\Users\admin\AppData\Roaming\Intel\Intel(R) Processor Graphics\RasTls.dll" | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1864 | C:\Windows\system32\dllhost.exe /Processid:{712459B2-3311-54C3-910D-0415091829489} | C:\Windows\system32\dllhost.exe | IntelGraphicsController.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 311
Read events
980
Write events
321
Delete events
10
Modification events
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8,: |
Value: 382C3A00780A0000010000000000000000000000 | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1317994526 | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1317994640 | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1317994641 | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 780A0000767348AA63F3D40100000000 | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | `-: |
Value: 602D3A00780A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | `-: |
Value: 602D3A00780A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2680) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
2
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6498.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AEDC0009.wmf | — | |
MD5:— | SHA256:— | |||
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{70F857E8-E896-4C98-B411-4BCA3B312C55}.tmp | — | |
MD5:— | SHA256:— | |||
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{300BFEF4-91C6-4A9A-99CC-F2C5430229BB}.tmp | — | |
MD5:— | SHA256:— | |||
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{72696F18-F8B8-4684-B9AB-F108C6FC44E4}.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9675.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\1087546.tmp | — | |
MD5:— | SHA256:— | |||
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2680 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$78ebbfb5fd1ee66f44030d52f80806d184e6daa00dd7aaa1a30b53c629912d.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\UnI9E46.bat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1172 | dllhost.exe | 217.69.8.255:443 | — | Cosmoline Telecommunication Services S.A. | GR | malicious |
1864 | dllhost.exe | 217.69.8.255:443 | — | Cosmoline Telecommunication Services S.A. | GR | malicious |