| File name: | Invoice-4067893568954.doc |
| Full analysis: | https://app.any.run/tasks/b027b7de-bf17-4c7e-9863-6132c7c80f82 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 03:21:23 |
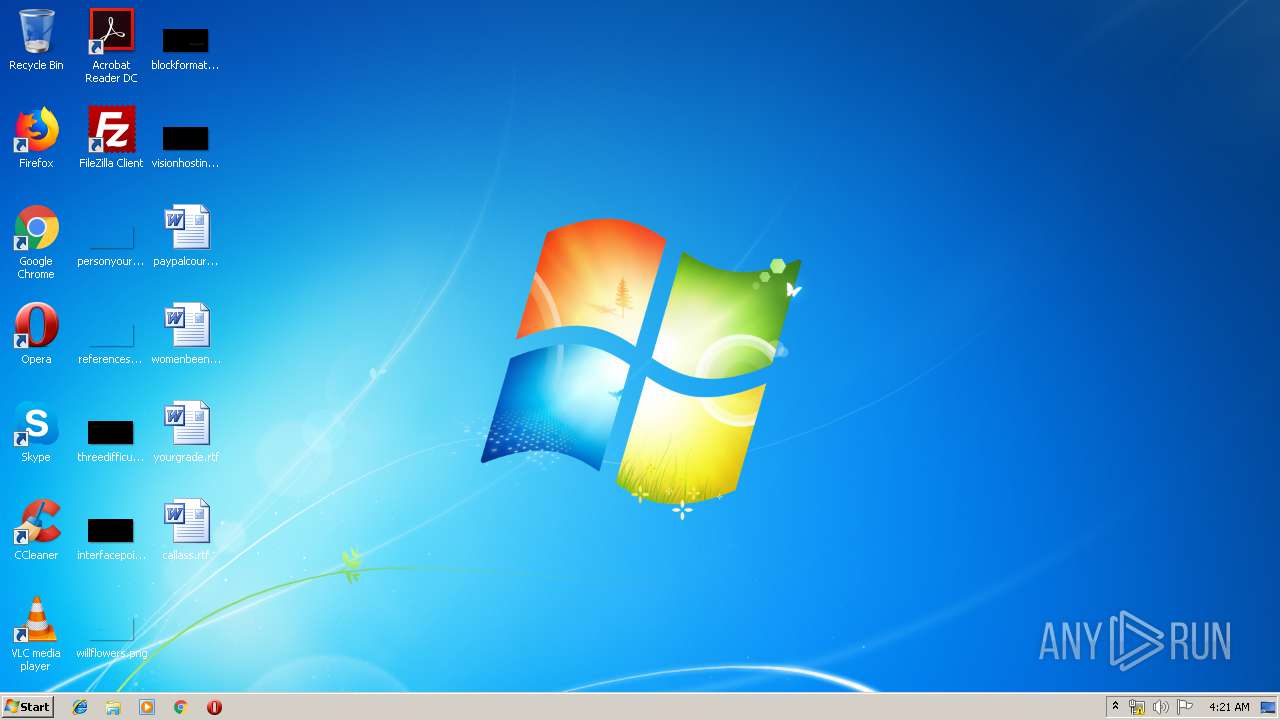
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
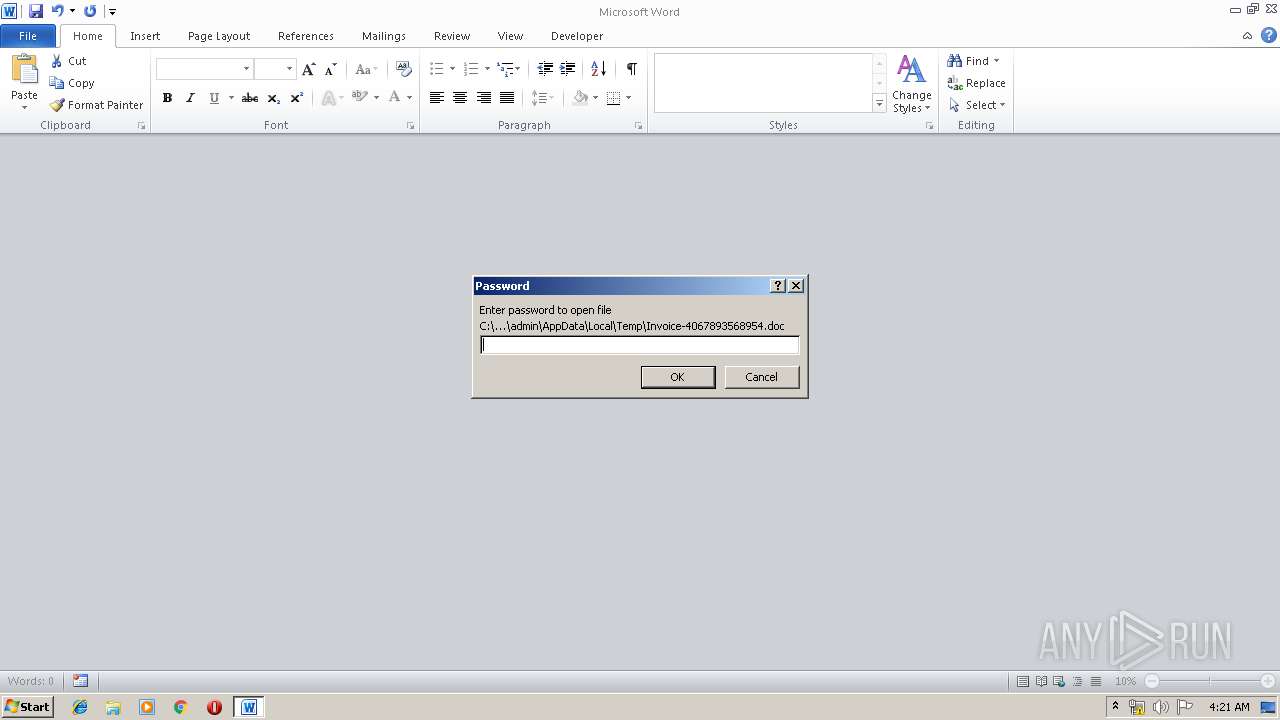
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | 1BE5B6C0788CAADA5E92D35DF96E4DDF |
| SHA1: | 7F081C4A9E567551D3320DED57CE6DDABE961FC9 |
| SHA256: | 1E77431AB2015B707C1DACA263AFB4DA7C5D9F889CD8E298B1DF3DB7F762F7D1 |
| SSDEEP: | 1536:Cxq5crCQNI9iEj185KNJp+0rpNGPFjUBZk/2V8ibp:cIcrFWi5aWiNGGVbbp |
MALICIOUS
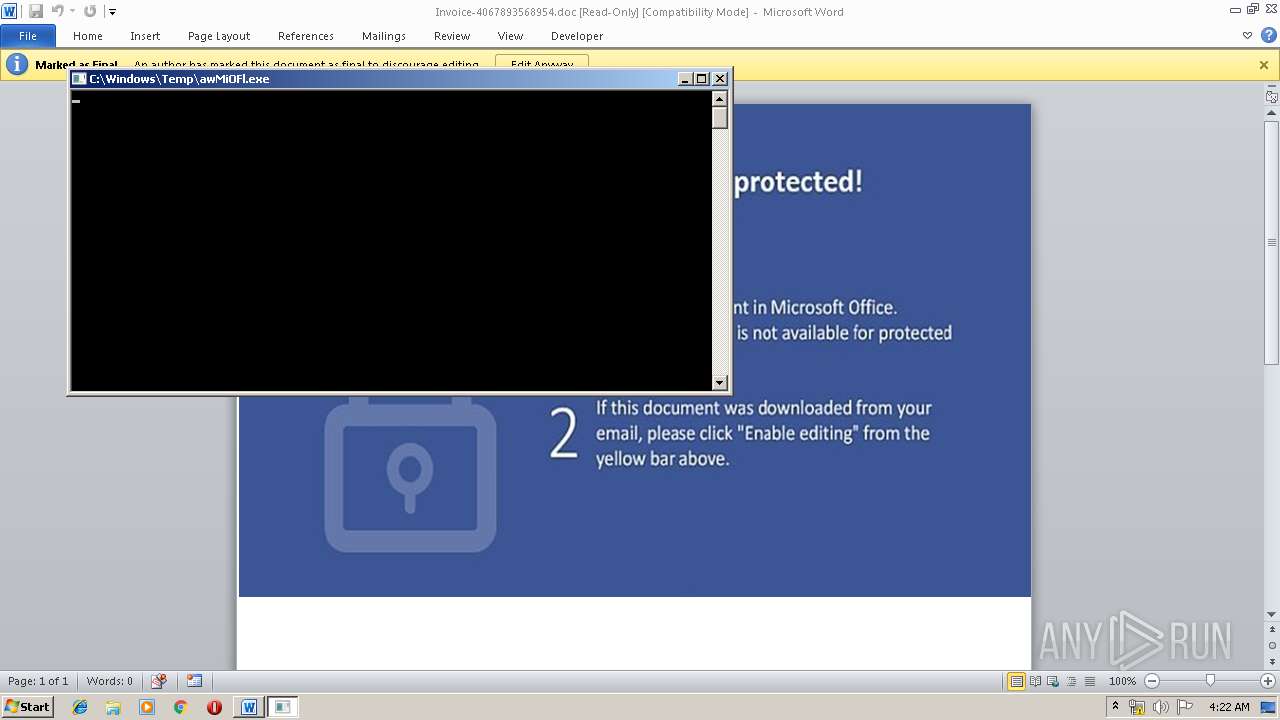
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3372)
Application was dropped or rewritten from another process
- awMiOFl.exe (PID: 2352)
SUSPICIOUS
Creates files in the Windows directory
- WINWORD.EXE (PID: 3372)
- wmic.exe (PID: 4040)
Executable content was dropped or overwritten
- wmic.exe (PID: 4040)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3372)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2352 | "C:\Windows\Temp\awMiOFl.exe" | C:\Windows\Temp\awMiOFl.exe | wmic.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3372 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Invoice-4067893568954.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4040 | wmic os get /format:"C:\\Windows\\Temp\\aXwZvnt48.xsl" | C:\Windows\System32\Wbem\wmic.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147614729 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 658
Read events
954
Write events
699
Delete events
5
Modification events
| (PID) Process: | (3372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | k*? |
Value: 6B2A3F002C0D0000010000000000000000000000 | |||
| (PID) Process: | (3372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3372) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1322450974 | |||
| (PID) Process: | (3372) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451088 | |||
| (PID) Process: | (3372) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451089 | |||
| (PID) Process: | (3372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 2C0D0000A8A51C224E26D50100000000 | |||
| (PID) Process: | (3372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ~,? |
Value: 7E2C3F002C0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ~,? |
Value: 7E2C3F002C0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3372) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFA3B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE01B538E8F490A3B.TMP | — | |
MD5:— | SHA256:— | |||
| 3372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFEF164CE17828CE9E.TMP | — | |
MD5:— | SHA256:— | |||
| 3372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF51F7A14FA86B1656.TMP | — | |
MD5:— | SHA256:— | |||
| 3372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF6A67D75A29E78C41.TMP | — | |
MD5:— | SHA256:— | |||
| 3372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF9499C75AAA93FF19.TMP | — | |
MD5:— | SHA256:— | |||
| 3372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFFAC6AAF3FEDEC076.TMP | — | |
MD5:— | SHA256:— | |||
| 3372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3372 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3372 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$voice-4067893568954.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4040 | wmic.exe | 49.51.12.195:443 | tor2net.com | Tencent Building, Kejizhongyi Avenue | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tor2net.com |
| malicious |
Threats
Process | Message |
|---|---|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|
awMiOFl.exe | Installing...
|