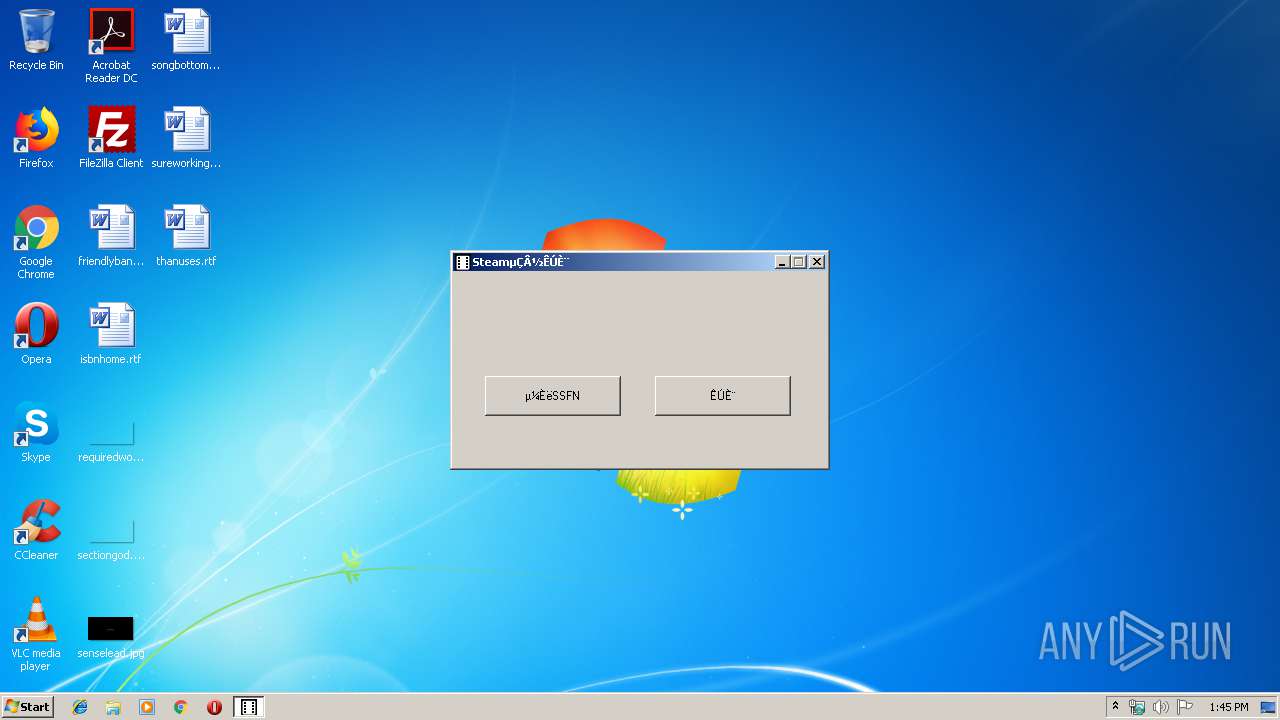
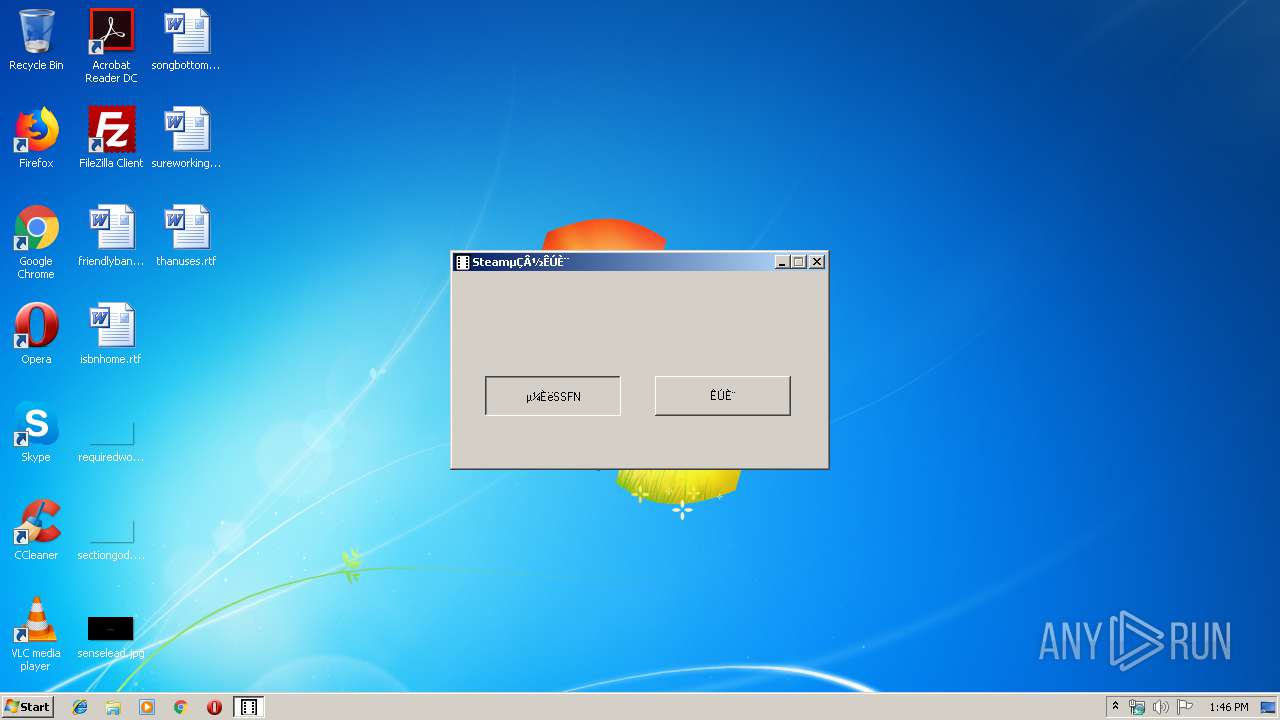
| File name: | Steam登陆授权.exe |
| Full analysis: | https://app.any.run/tasks/ff639c7d-51c9-43e6-bdff-792c1edba79d |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 12:45:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3EB0176FA3E29E1B3614334889E3B5B9 |
| SHA1: | 24CA9A4212CF03C1046551CED68CFE73FD7866DD |
| SHA256: | 1E6EF5515CB9F38AE8D9E1C7D2D5D22F6EFE8320234AAA88B2511D61F5814A00 |
| SSDEEP: | 12288:CWbZeLhGdlOPk83beblt8O4fZlzUu7bFjGYCNL:C1hG/R8rebQOYquvFjiNL |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
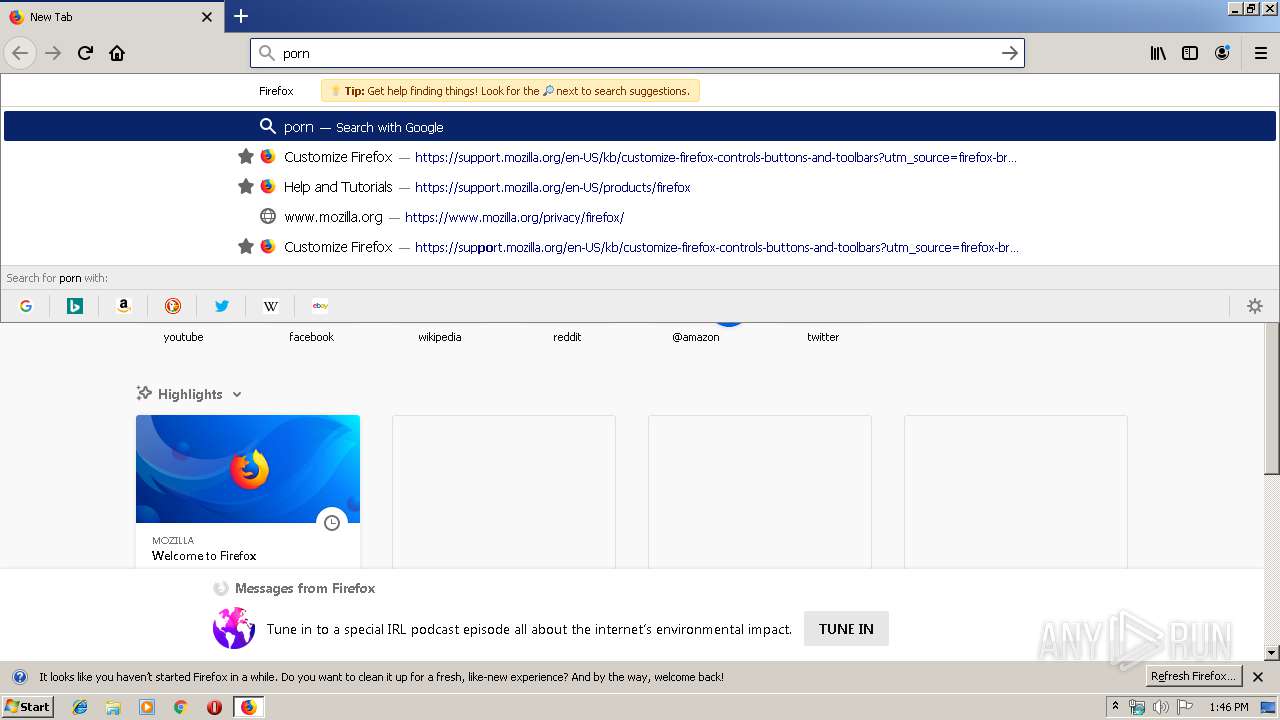
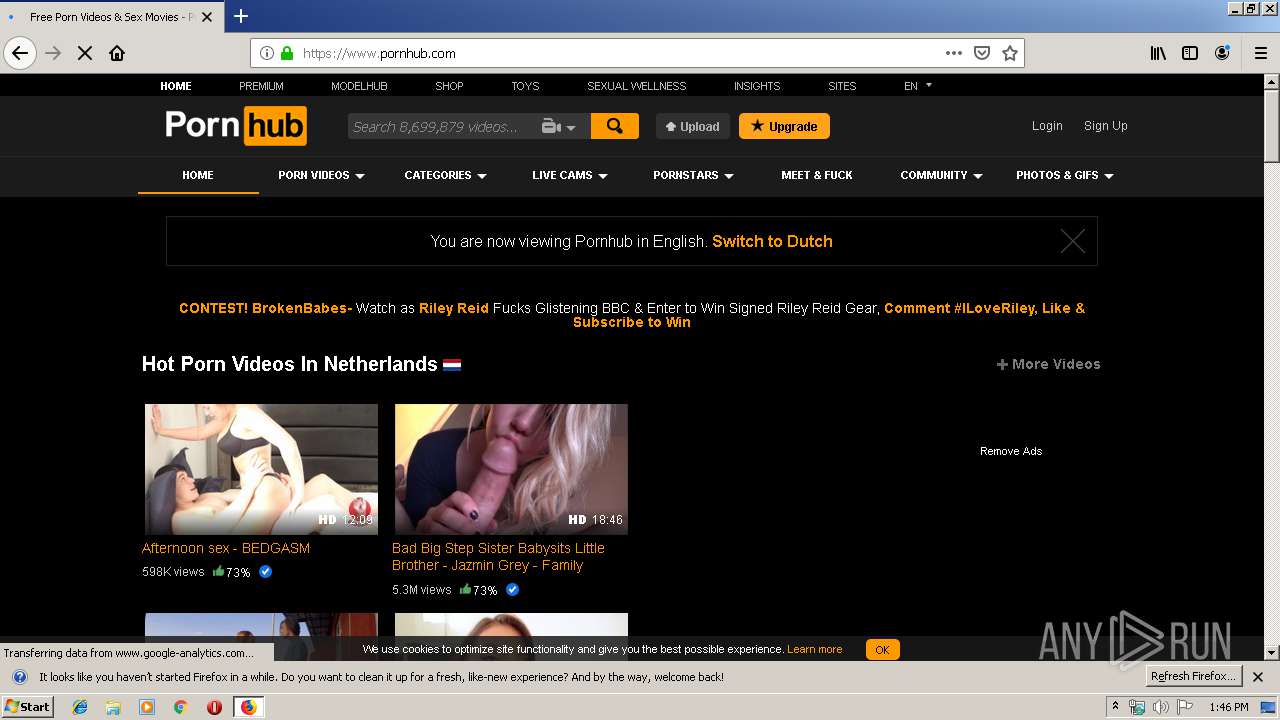
Application launched itself
- firefox.exe (PID: 3552)
Creates files in the user directory
- firefox.exe (PID: 3552)
Manual execution by user
- firefox.exe (PID: 3552)
Reads CPU info
- firefox.exe (PID: 3552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:07 06:14:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 528384 |
| InitializedDataSize: | 184320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x63021 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | 易语言程序 |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 本程序使用易语言编写(http://www.dywt.com.cn) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-May-2018 04:14:15 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | 易语言程序 |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 本程序使用易语言编写(http://www.dywt.com.cn) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 07-May-2018 04:14:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008089E | 0x00081000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57002 |
.rdata | 0x00082000 | 0x00012DD4 | 0x00013000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.54908 |
.data | 0x00095000 | 0x000246E8 | 0x00012000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.99486 |
.rsrc | 0x000BA000 | 0x000076D0 | 0x00008000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.54925 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 2.24373 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 1.02149 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.40965 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 2.96354 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 1.77646 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 2.78868 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
127 | 1.4183 | 12 | Latin 1 / Western European | Chinese - PRC | RT_MENU |
150 | 3.06278 | 152 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
WINSPOOL.DRV |
WS2_32.dll |
Total processes
38
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2380 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3552.13.242434138\342085571" -childID 2 -isForBrowser -prefsHandle 2672 -prefMapHandle 2676 -prefsLen 5842 -prefMapSize 188076 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3552 "\\.\pipe\gecko-crash-server-pipe.3552" 2728 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3552.20.2055729047\971574112" -childID 3 -isForBrowser -prefsHandle 3600 -prefMapHandle 3604 -prefsLen 6778 -prefMapSize 188076 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3552 "\\.\pipe\gecko-crash-server-pipe.3552" 3616 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3552.0.1955992710\218003012" -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3552 "\\.\pipe\gecko-crash-server-pipe.3552" 1168 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
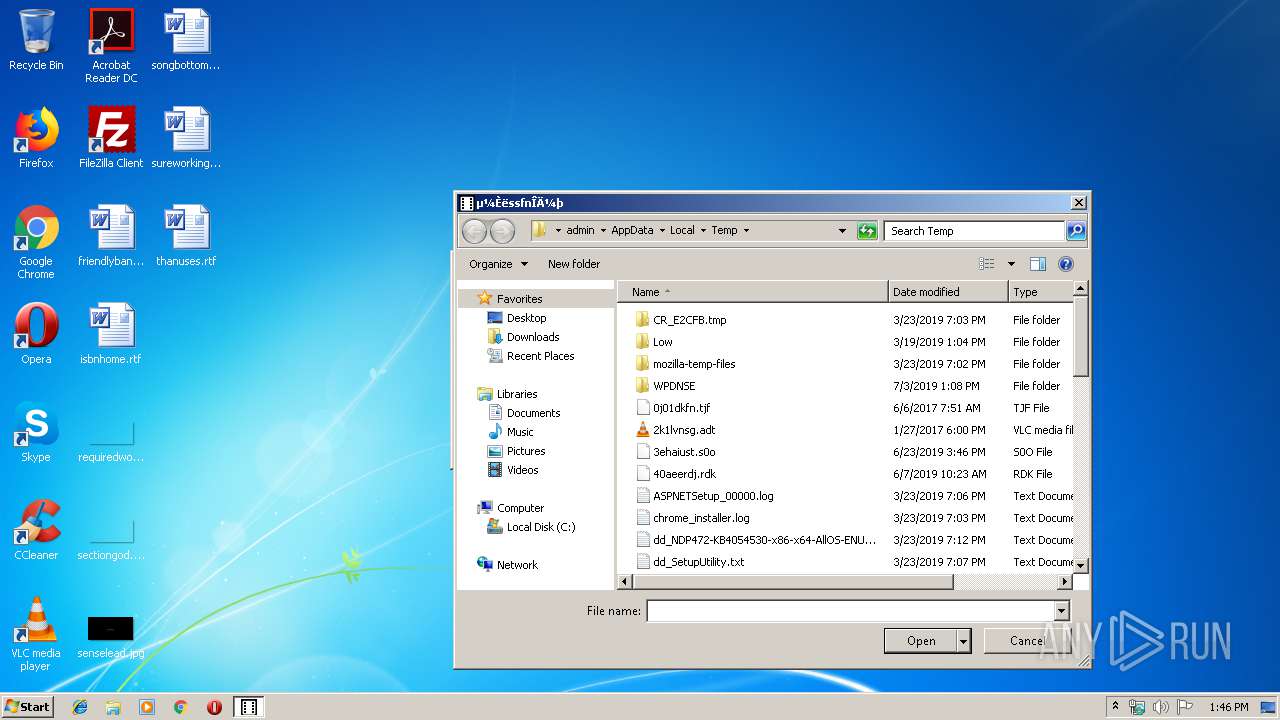
| 2992 | "C:\Users\admin\AppData\Local\Temp\Steam登陆授权.exe" | C:\Users\admin\AppData\Local\Temp\Steam登陆授权.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 3564 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3552.3.1059077551\1505444233" -childID 1 -isForBrowser -prefsHandle 1576 -prefMapHandle 1648 -prefsLen 1 -prefMapSize 188076 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3552 "\\.\pipe\gecko-crash-server-pipe.3552" 1720 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
Total events
950
Read events
877
Write events
70
Delete events
3
Modification events
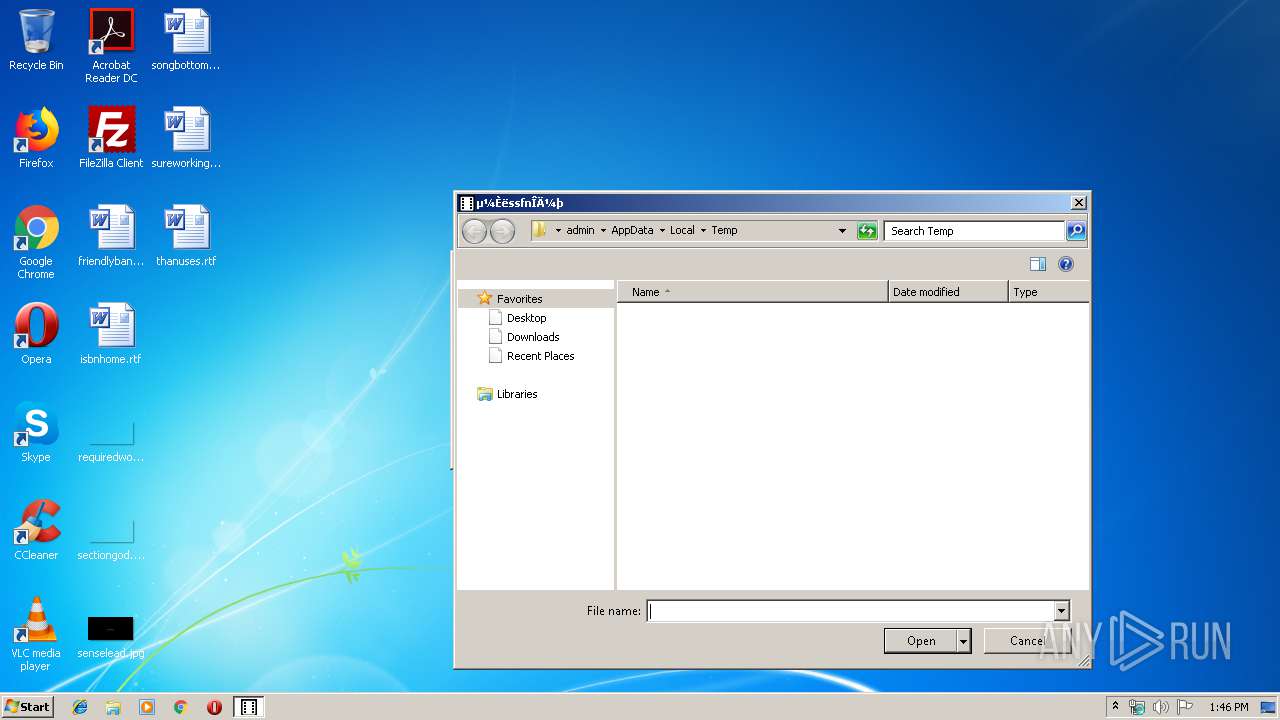
| (PID) Process: | (2992) Steam登陆授权.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0053007400650061006D007B764696886343672E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070000000 | |||
| (PID) Process: | (2992) Steam登陆授权.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (2992) Steam登陆授权.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2992) Steam登陆授权.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0700000001000000020000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2992) Steam登陆授权.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (2992) Steam登陆授权.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\1\0 |
| Operation: | write | Name: | 1 |
Value: 4A00310000000000F24EC065102054656D700000360008000400EFBE454B814AF24EC0652A00000090010000000002000000000000000000000000000000540065006D007000000014000000 | |||
| (PID) Process: | (2992) Steam登陆授权.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\1\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (2992) Steam登陆授权.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2992) Steam登陆授权.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\1\0\1 |
| Operation: | write | Name: | NodeSlot |
Value: 100 | |||
| (PID) Process: | (2992) Steam登陆授权.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\1\0\1 |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
Executable files
0
Suspicious files
104
Text files
88
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3552 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\pluginreg.dat.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 3552 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
67
DNS requests
109
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3552 | firefox.exe | POST | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3552 | firefox.exe | POST | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3552 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3552 | firefox.exe | POST | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3552 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3552 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3552 | firefox.exe | POST | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3552 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3552 | firefox.exe | POST | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3552 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3552 | firefox.exe | 95.100.39.17:80 | detectportal.firefox.com | Akamai International B.V. | DE | whitelisted |
3552 | firefox.exe | 52.50.56.62:443 | location.services.mozilla.com | Amazon.com, Inc. | IE | unknown |
3552 | firefox.exe | 34.218.190.17:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
3552 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3552 | firefox.exe | 34.213.89.114:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3552 | firefox.exe | 52.11.30.237:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3552 | firefox.exe | 172.217.23.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3552 | firefox.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
3552 | firefox.exe | 54.192.202.51:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3552 | firefox.exe | 172.217.21.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod1-elb-eu-west-1.prod.mozaws.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |