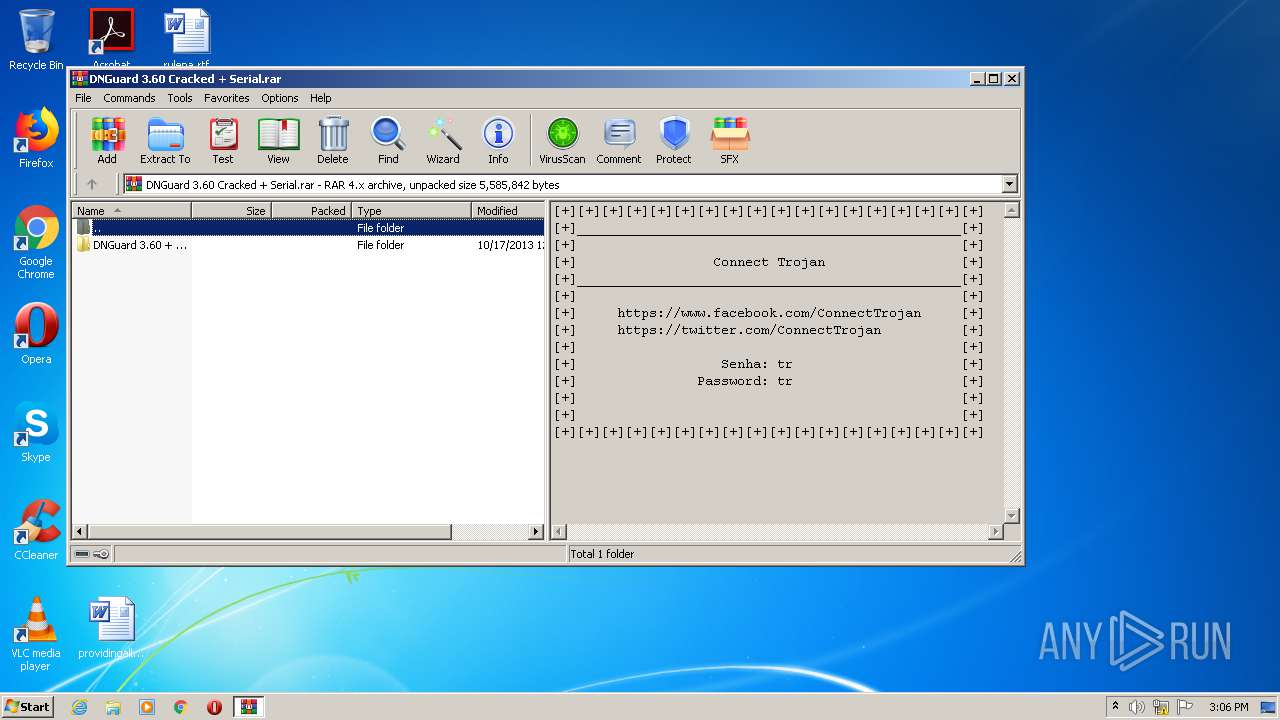
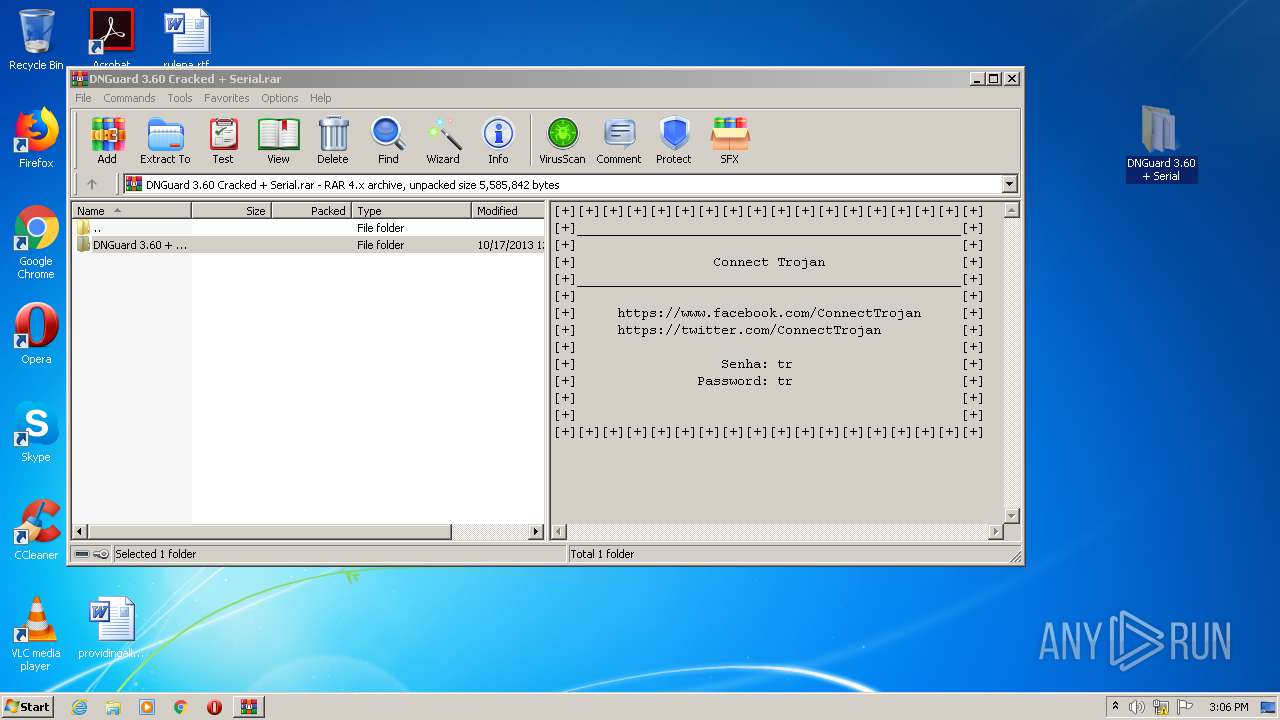
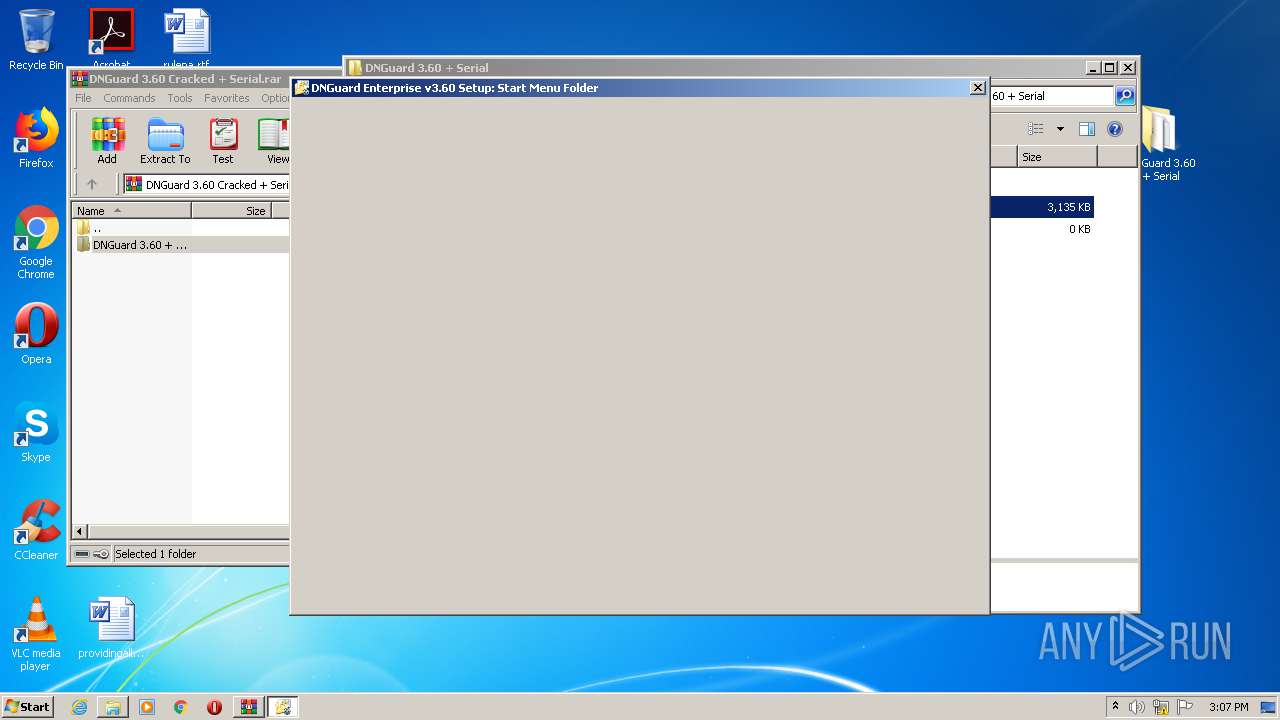
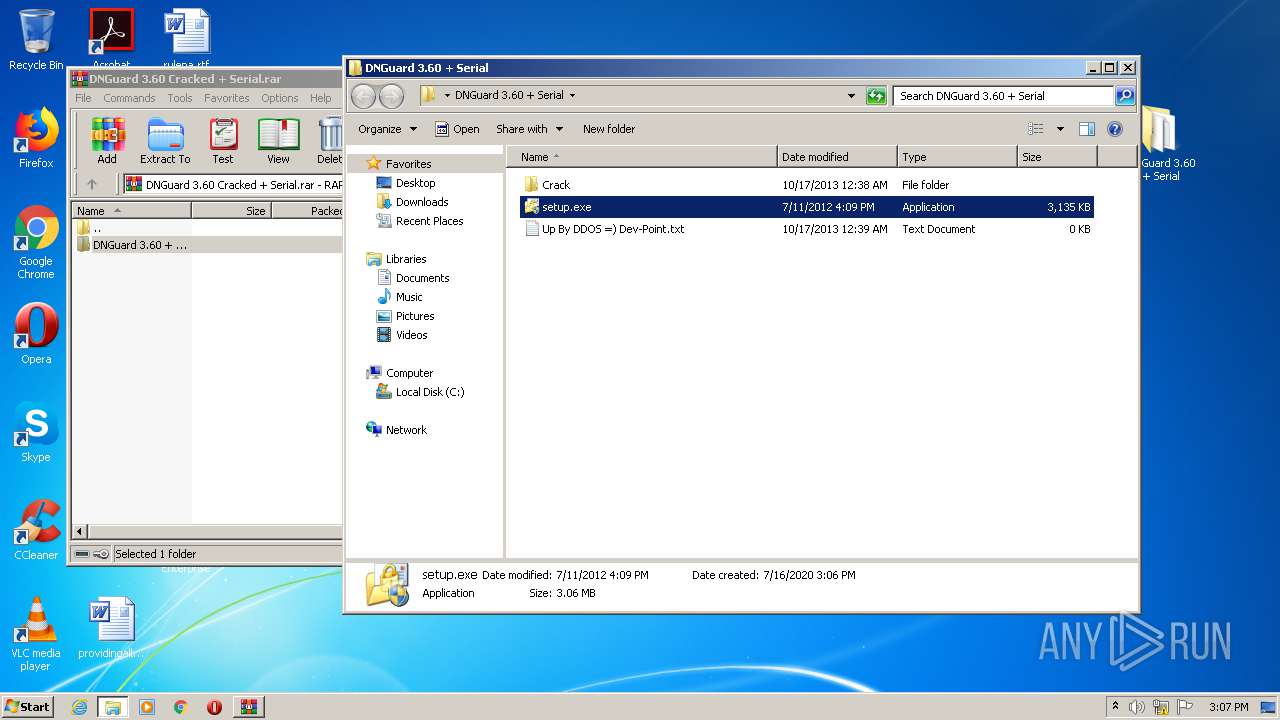
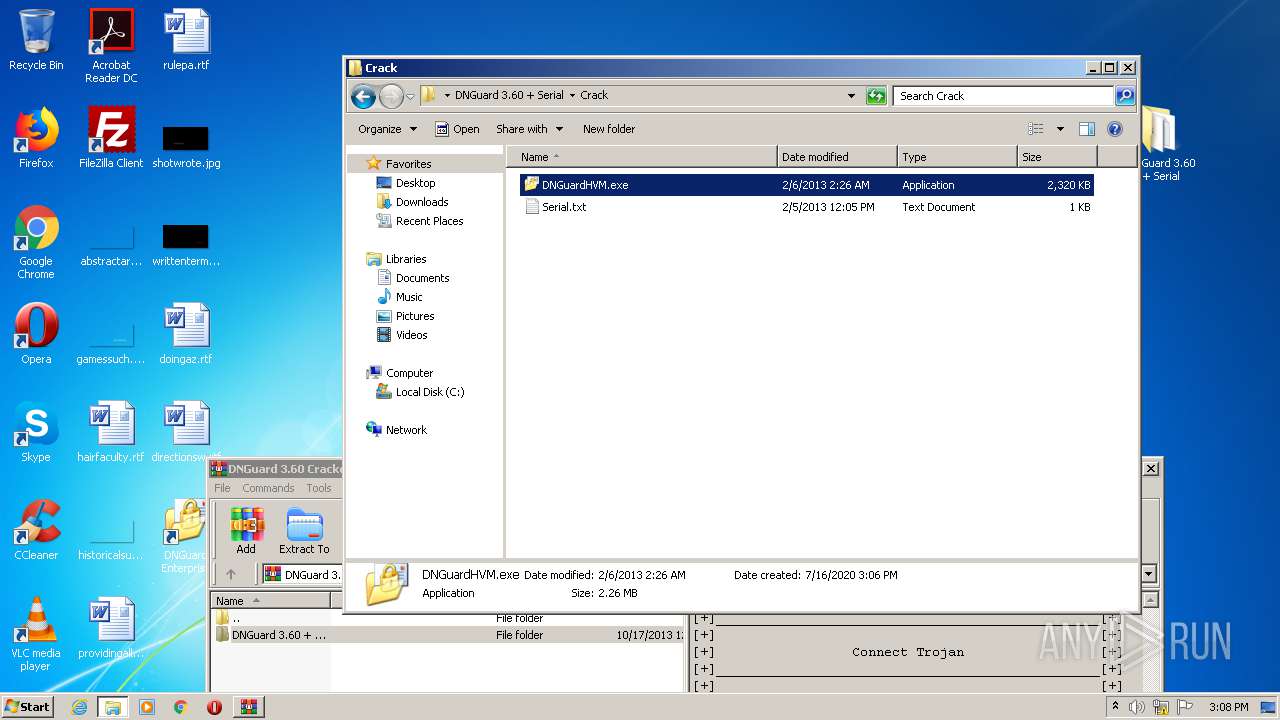
| File name: | DNGuard 3.60 Cracked + Serial.rar |
| Full analysis: | https://app.any.run/tasks/a6447b06-16d9-49d3-9f66-027bf0e93e06 |
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2020, 14:05:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | D1C4718FD9ADC34345CFC64AF839D760 |
| SHA1: | 62BCAC8E6D22FC1F291CD1AA401B30BED47B2801 |
| SHA256: | 1E666BD0B5AB208E339A09AAEAA10EE0780FD2C8166FB9EB3EFCF74DE13B133D |
| SSDEEP: | 98304:18sk1dapKfnKAFSqkPlrDdWvkIXvwxbpJkdzHs56zhfhiEce2mk6i:uskipKfnnENdI7qbpmd1zFhbceuj |
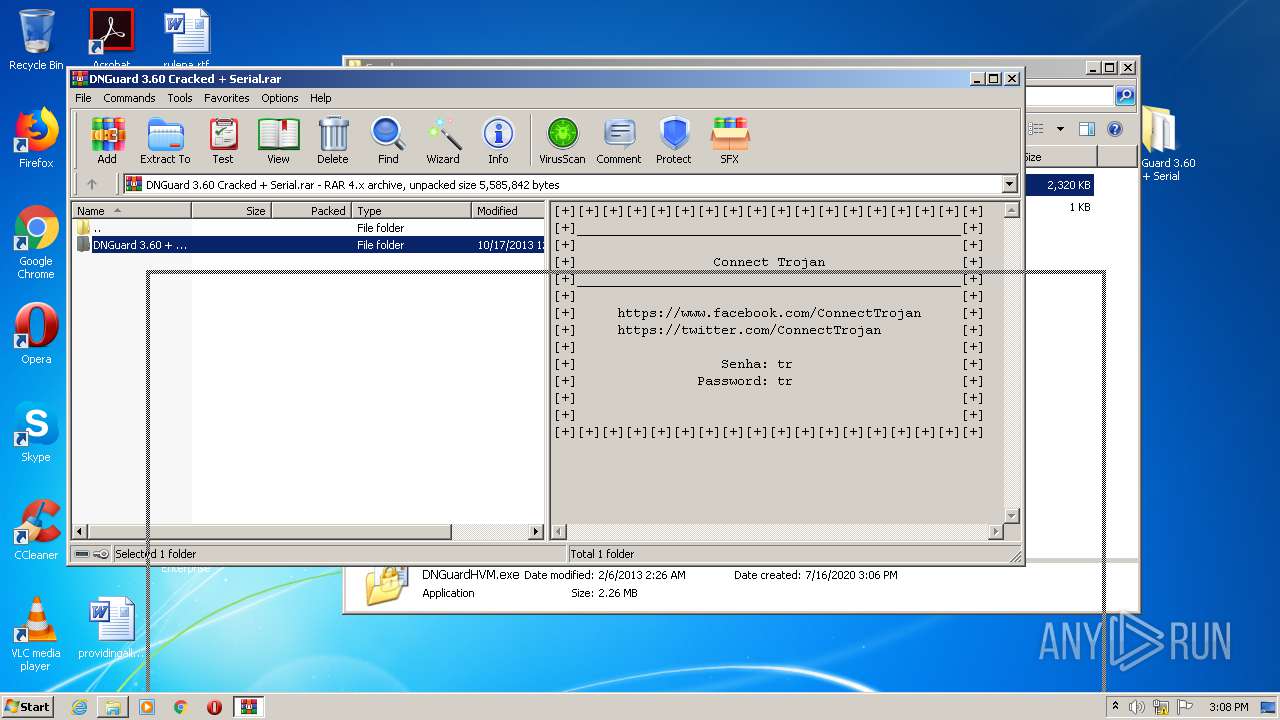
MALICIOUS
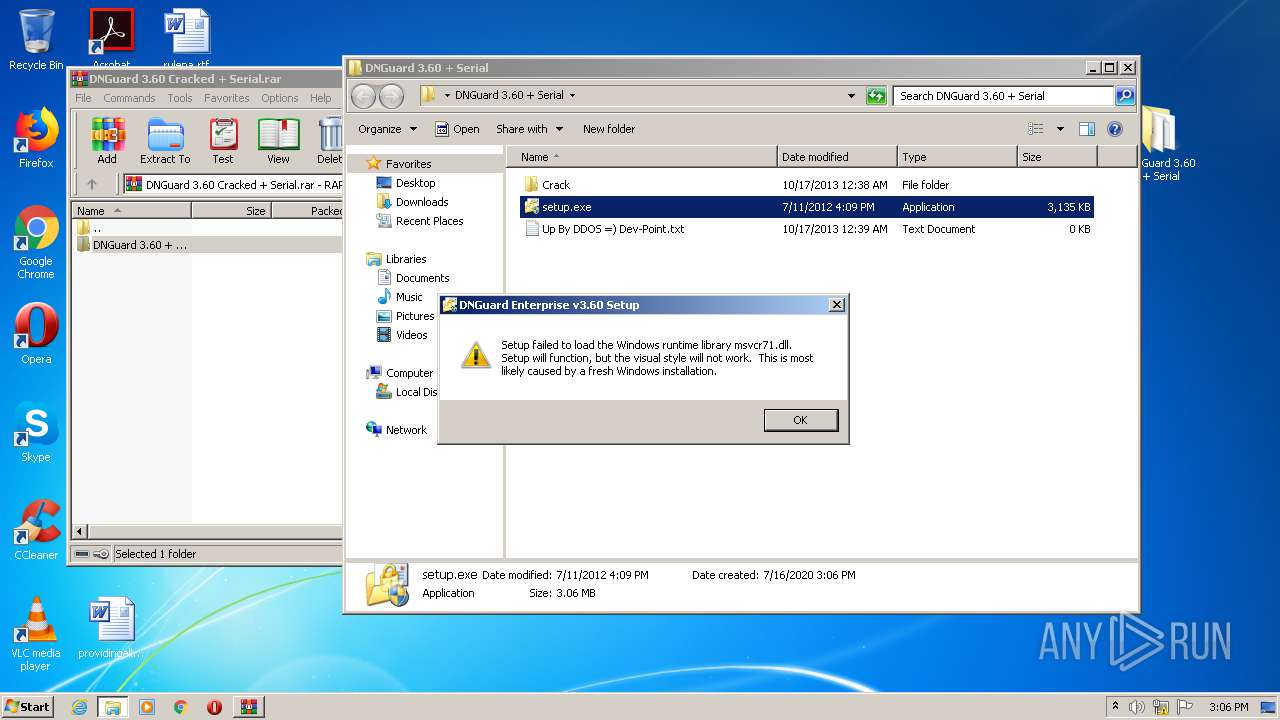
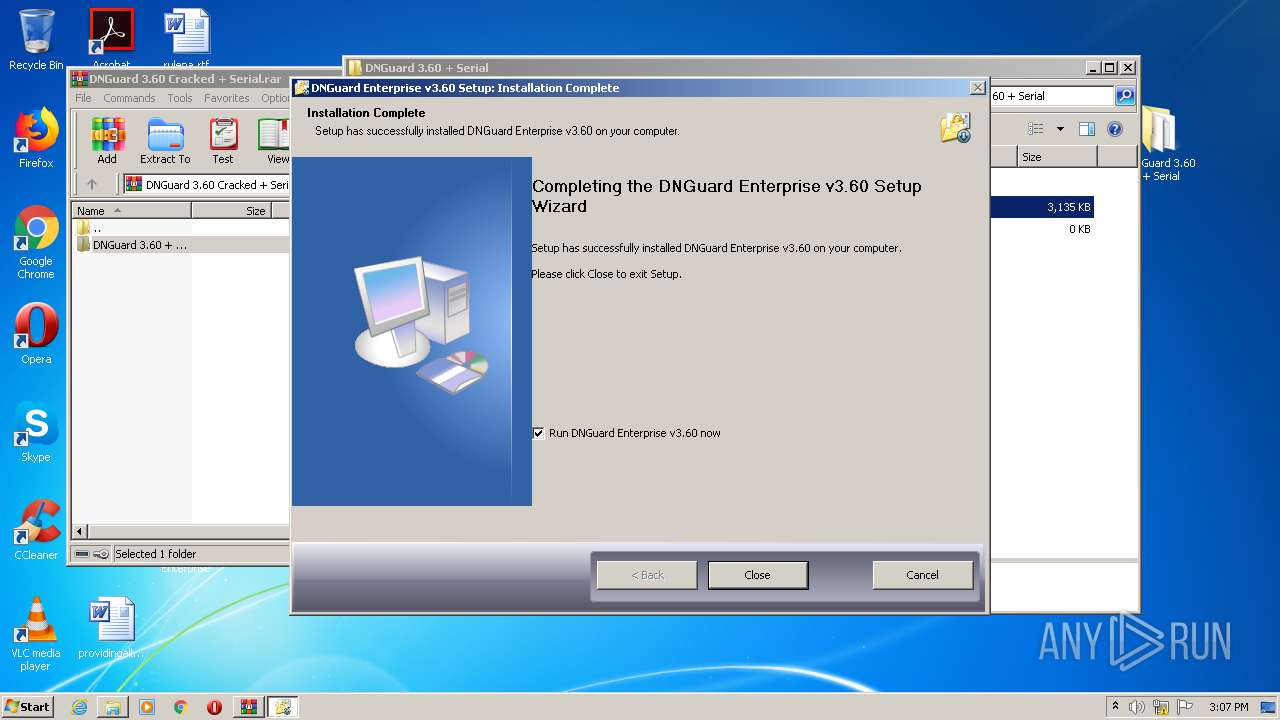
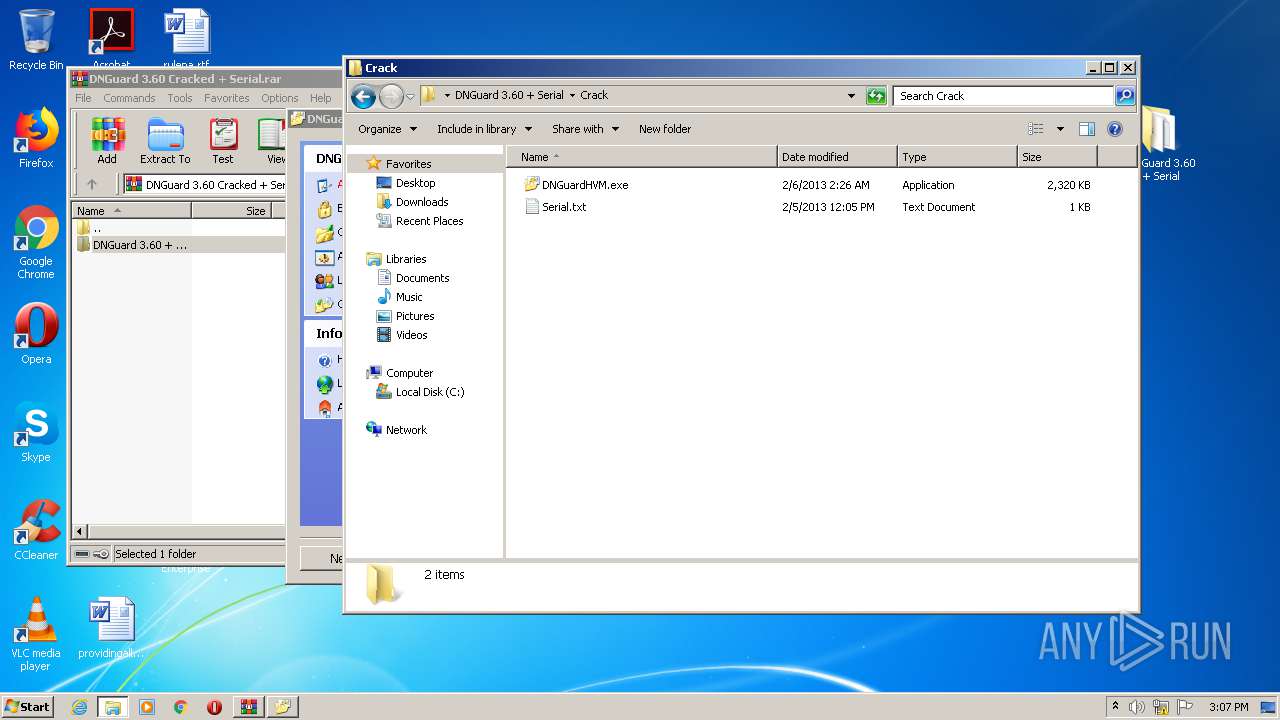
Loads dropped or rewritten executable
- setup.exe (PID: 2636)
Application was dropped or rewritten from another process
- setup.exe (PID: 2604)
- DNGuardHVM.exe (PID: 2488)
- setup.exe (PID: 2636)
SUSPICIOUS
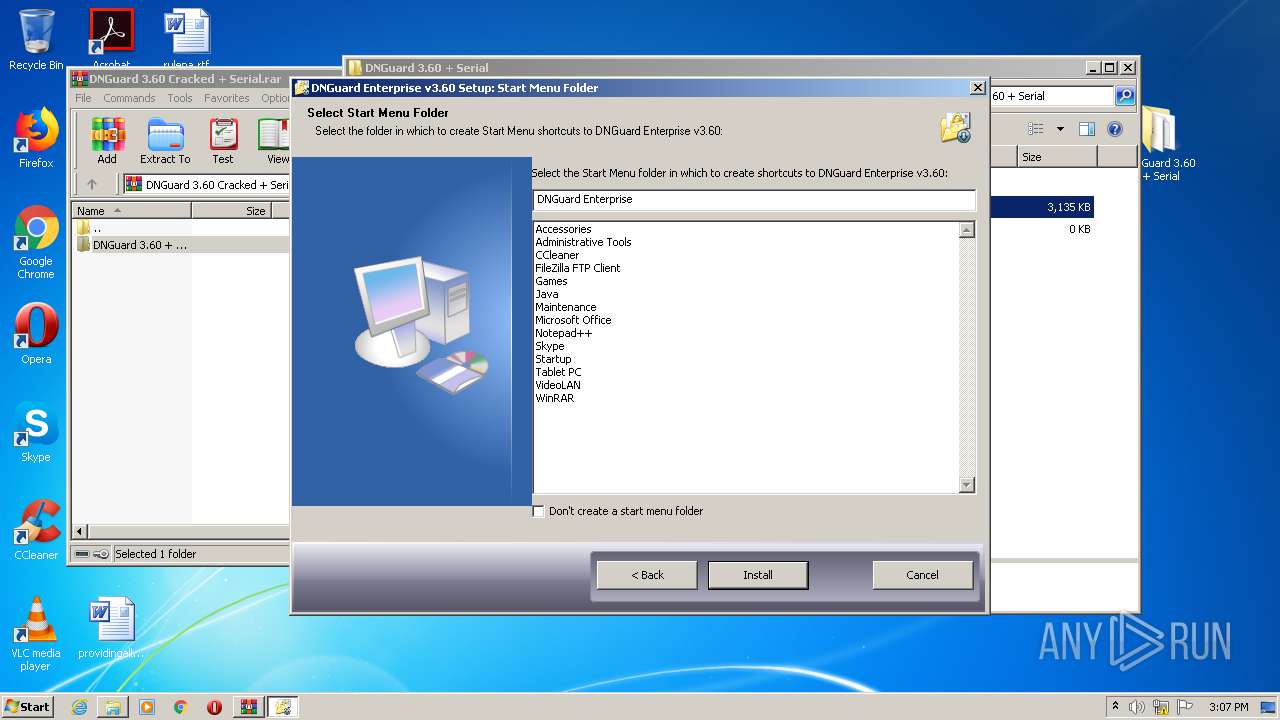
Creates a software uninstall entry
- setup.exe (PID: 2636)
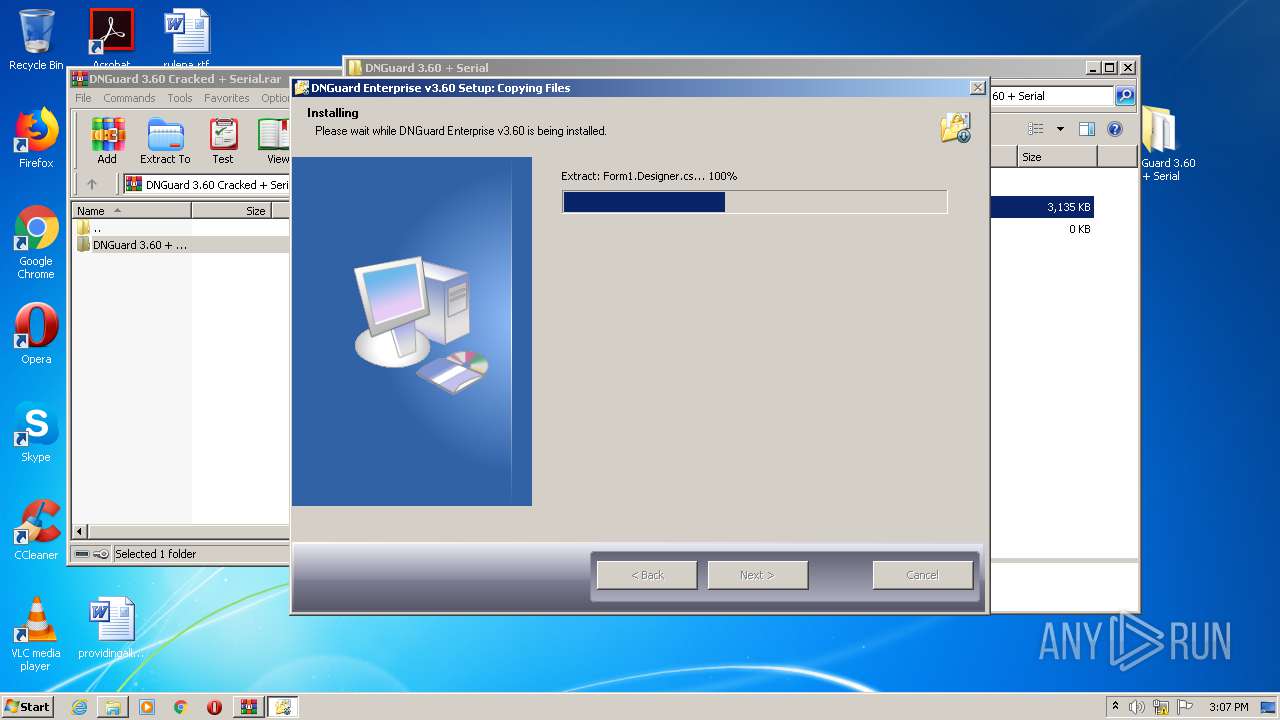
Executable content was dropped or overwritten
- setup.exe (PID: 2636)
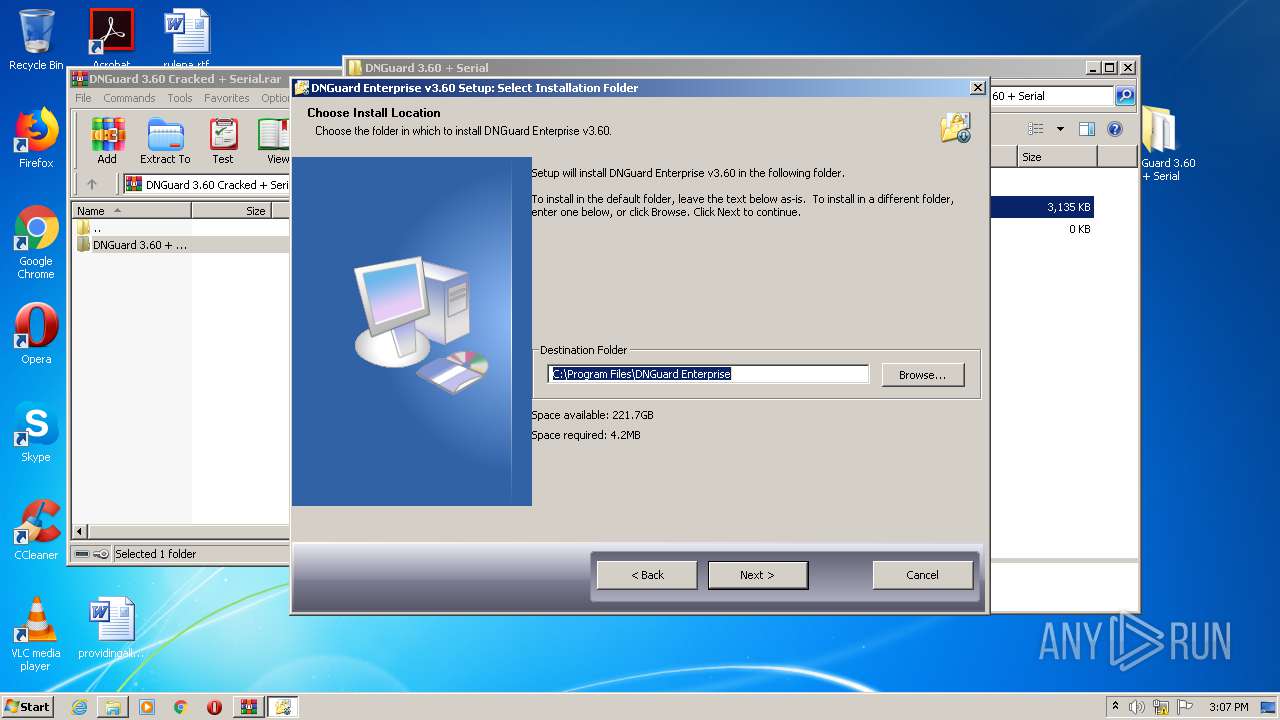
Creates files in the program directory
- setup.exe (PID: 2636)
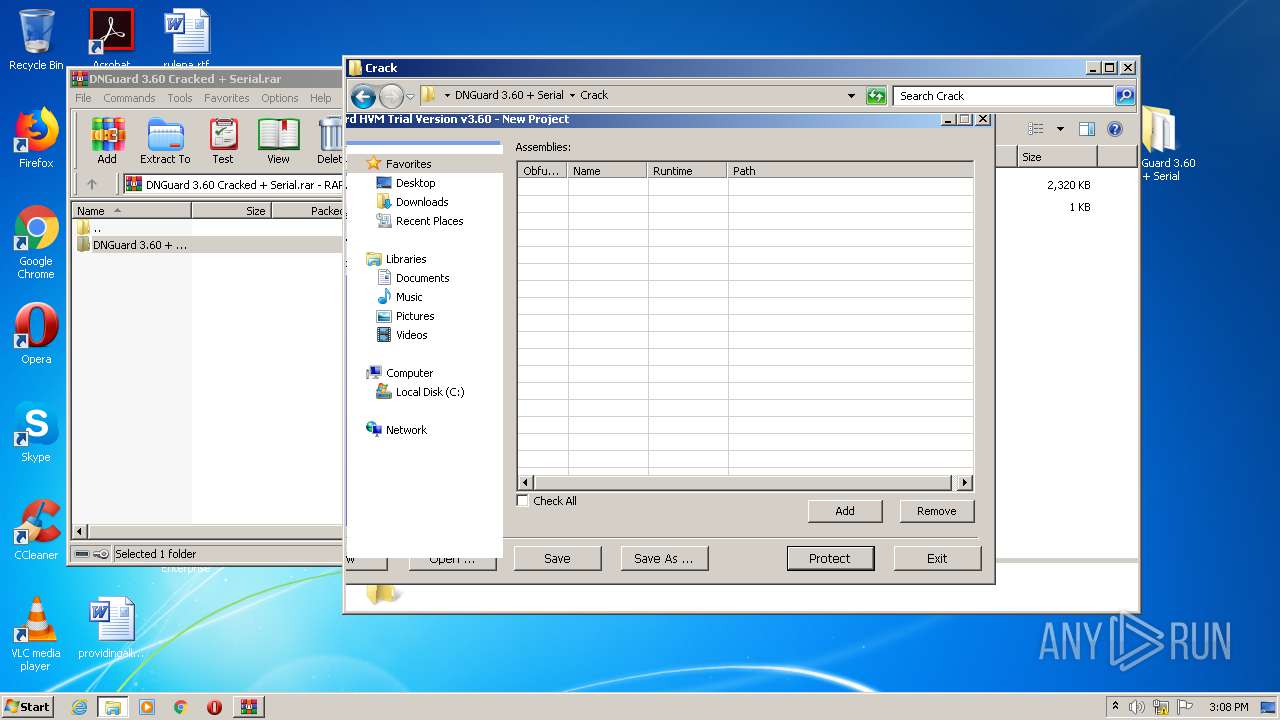
Low-level read access rights to disk partition
- DNGuardHVM.exe (PID: 2488)
INFO
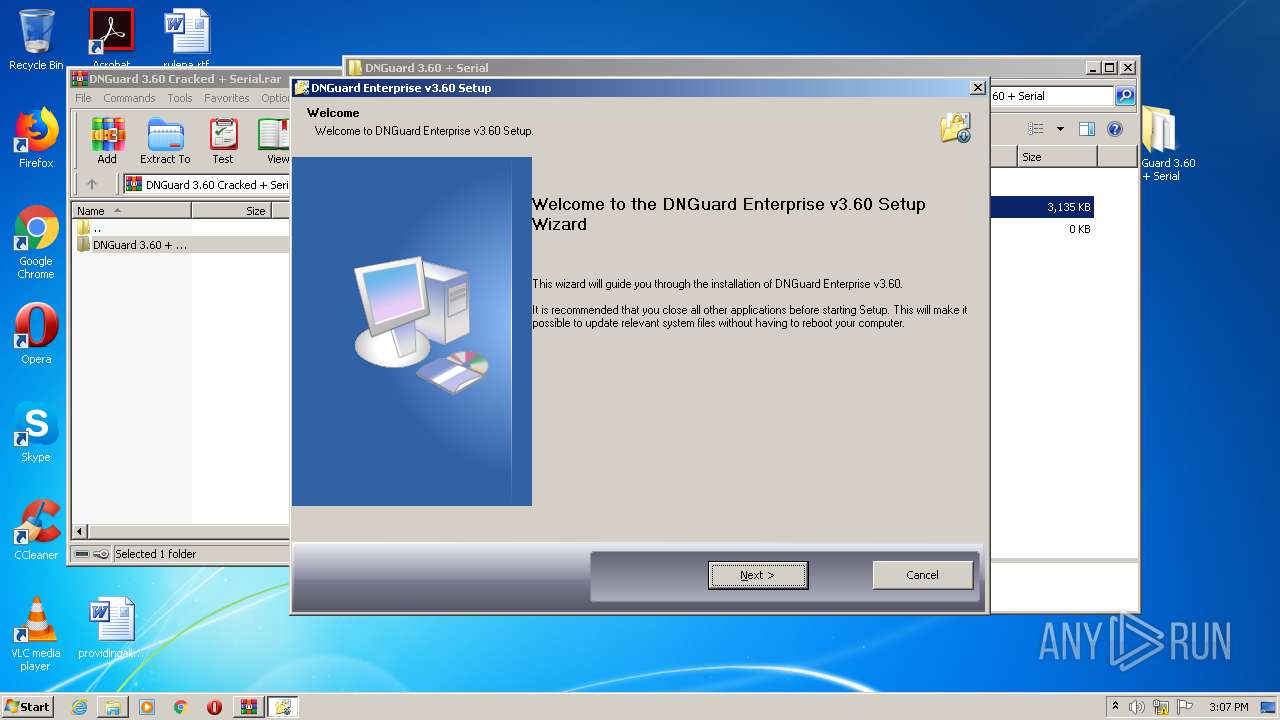
Manual execution by user
- setup.exe (PID: 2636)
- setup.exe (PID: 2604)
- iexplore.exe (PID: 3864)
- DNGuardHVM.exe (PID: 2604)
Changes internet zones settings
- iexplore.exe (PID: 3864)
Reads internet explorer settings
- iexplore.exe (PID: 1244)
Reads Internet Cache Settings
- iexplore.exe (PID: 1244)
- iexplore.exe (PID: 3864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 1654252 |
|---|---|
| UncompressedSize: | 2375680 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2013:02:06 02:26:00 |
| PackingMethod: | Normal |
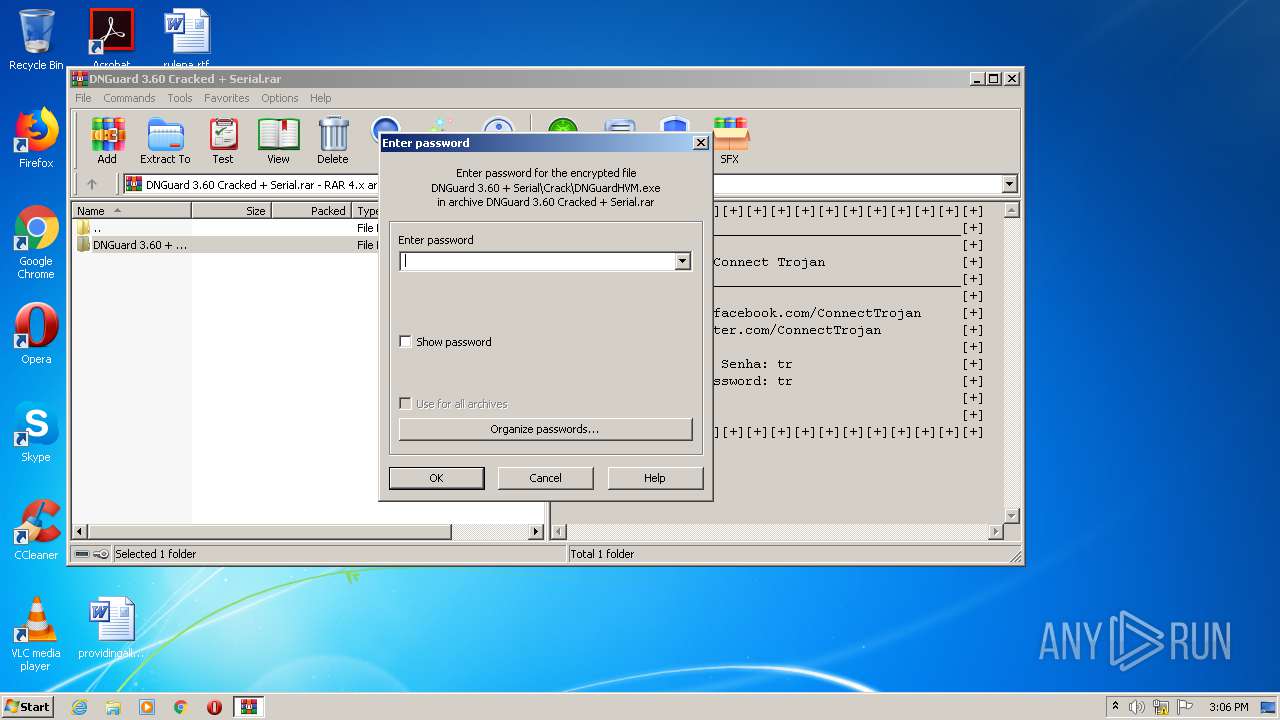
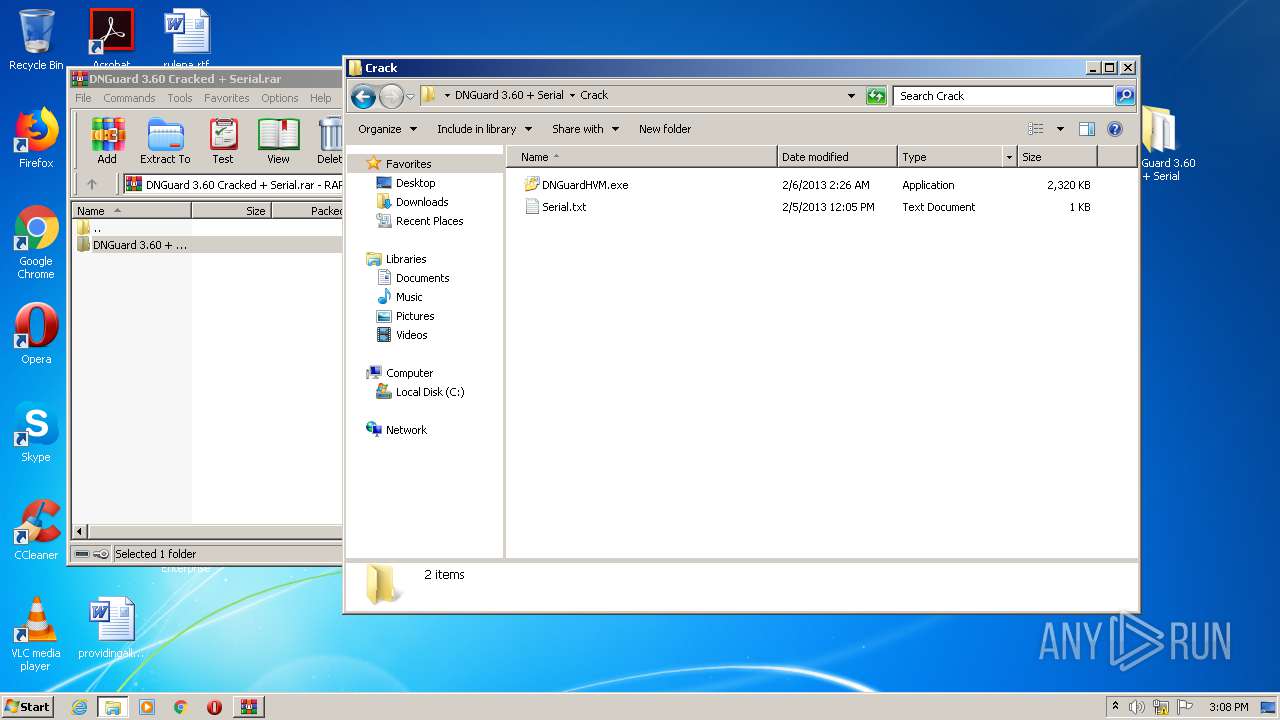
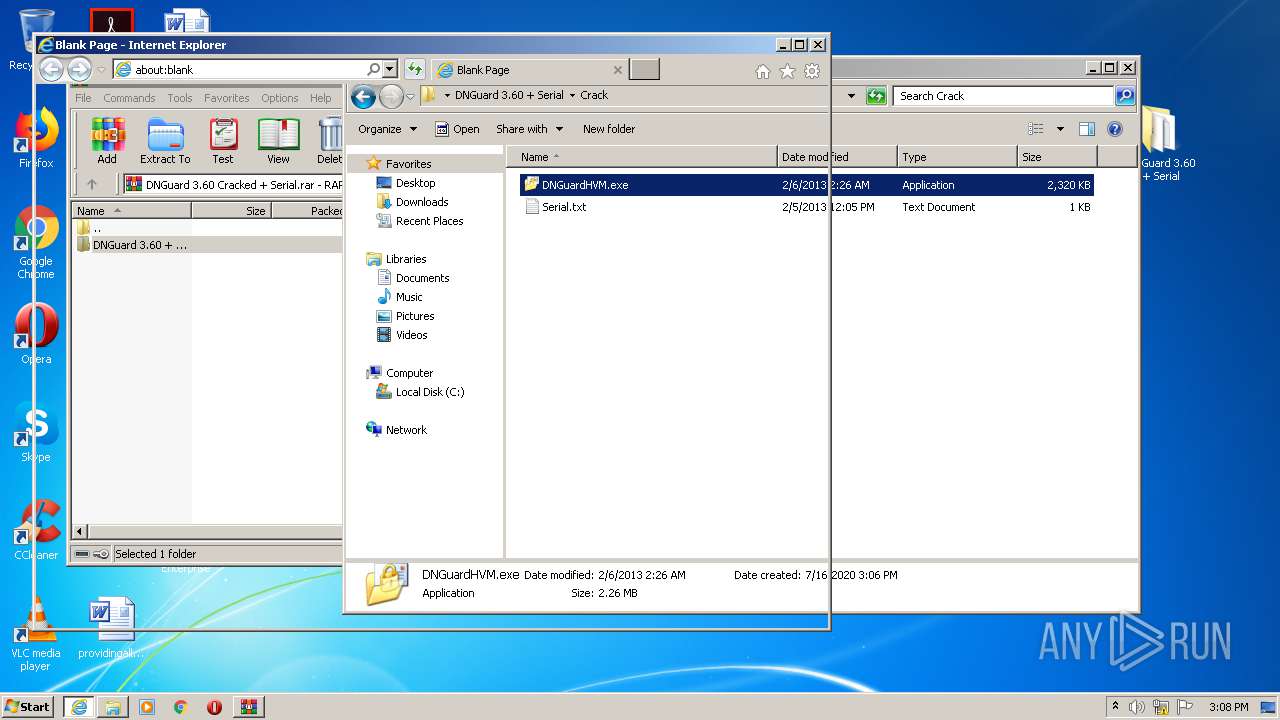
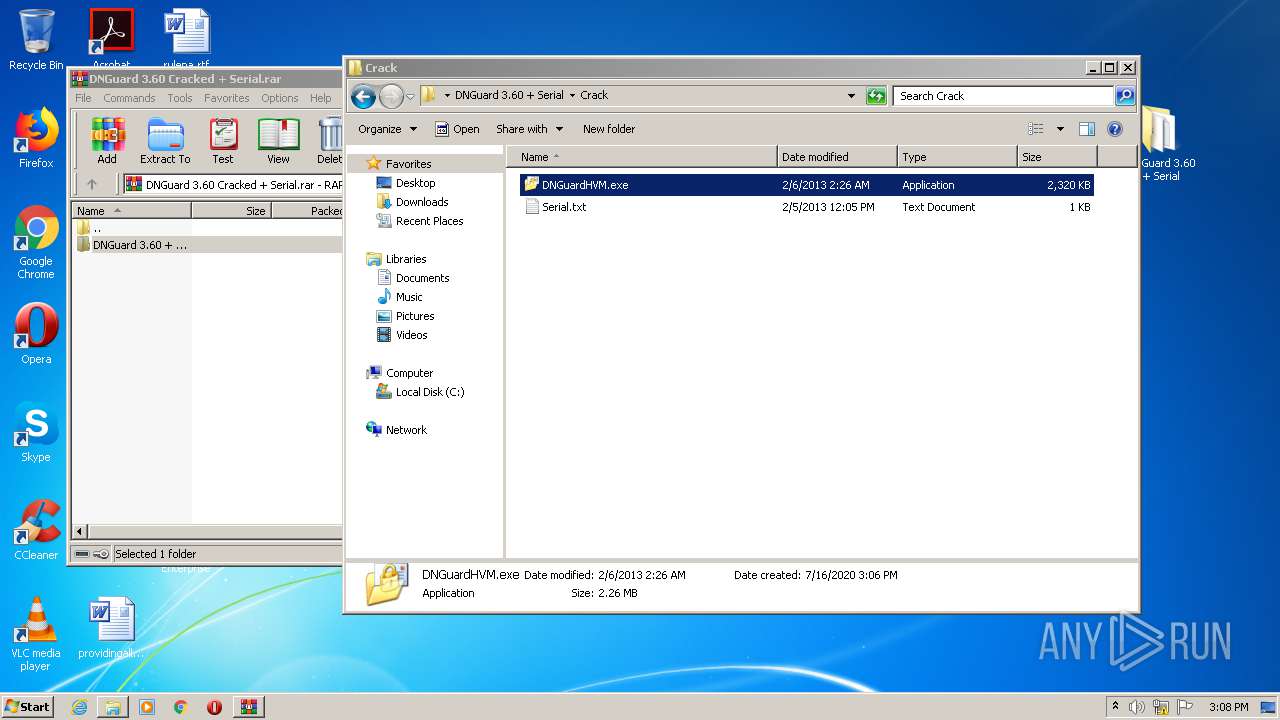
| ArchivedFileName: | DNGuard 3.60 + Serial\Crack\DNGuardHVM.exe |
Total processes
48
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3864 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2436 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\DNGuard 3.60 Cracked + Serial.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
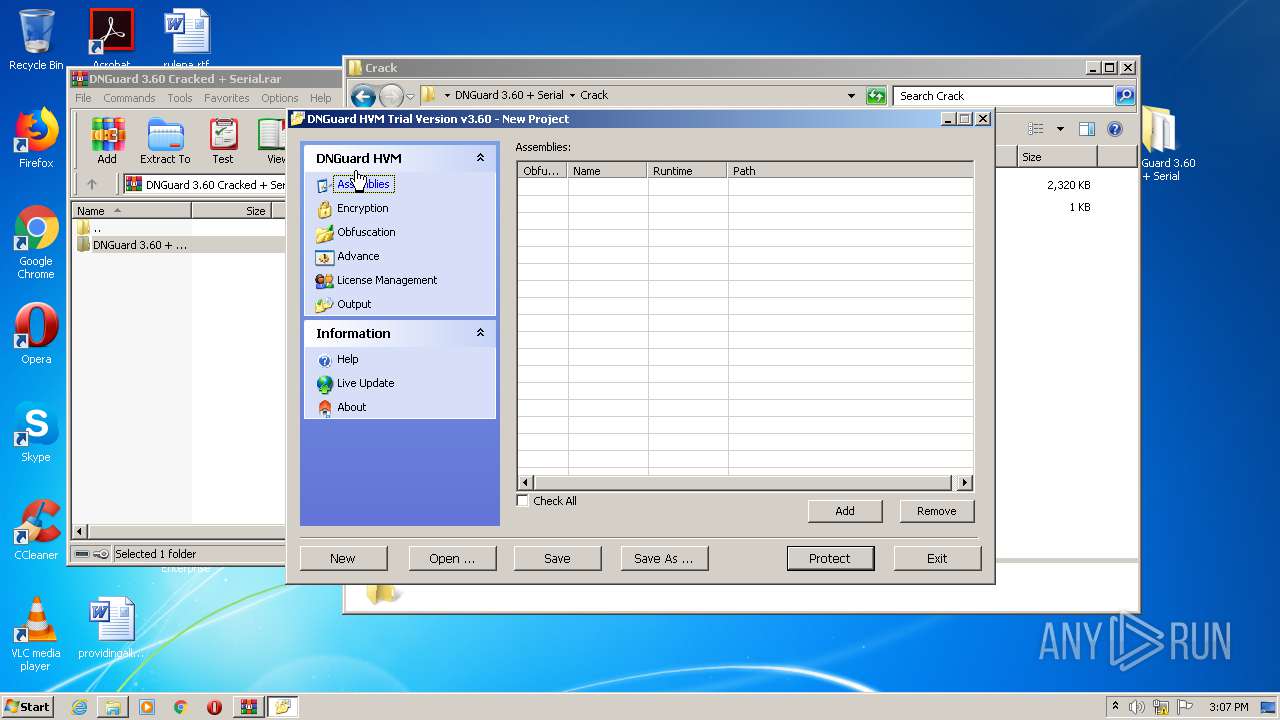
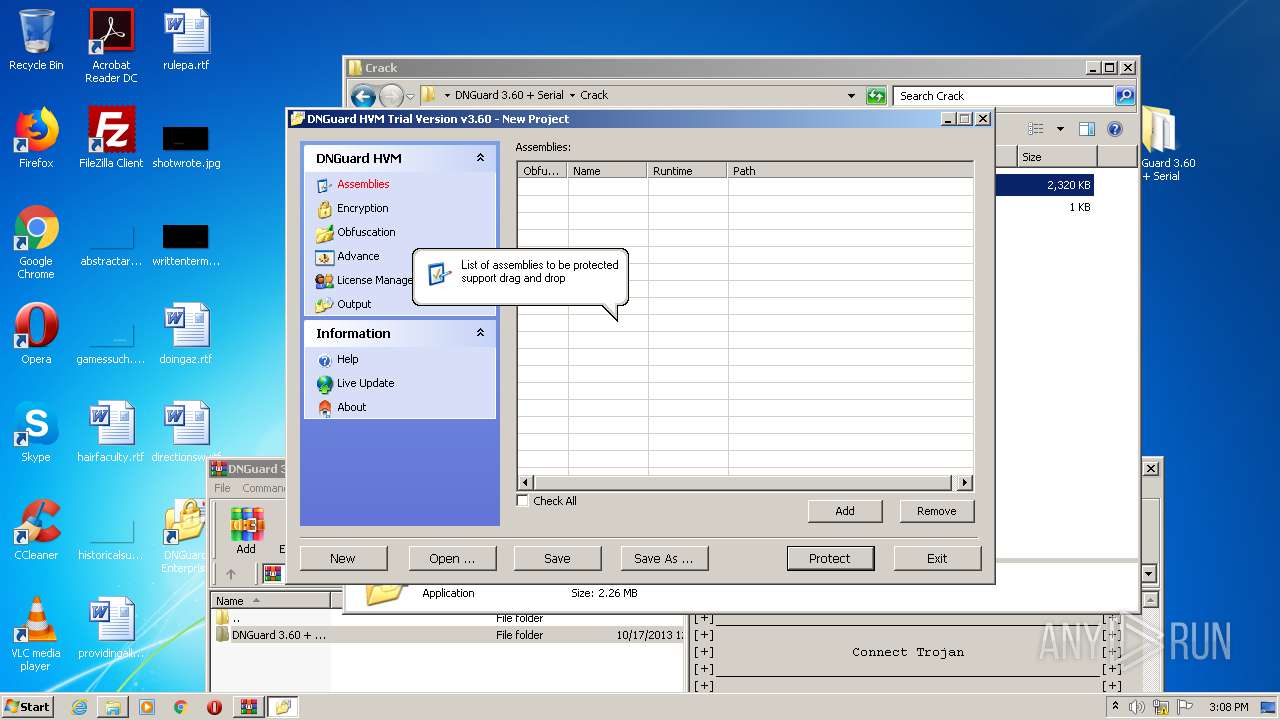
| 2488 | "C:\Program Files\DNGuard Enterprise\DNGuardHVM.exe" | C:\Program Files\DNGuard Enterprise\DNGuardHVM.exe | setup.exe | ||||||||||||
User: admin Company: ZiYuXuan Studio Integrity Level: HIGH Description: DotNet Guard HVM Exit code: 2 Version: 3, 6, 0, 0 Modules
| |||||||||||||||
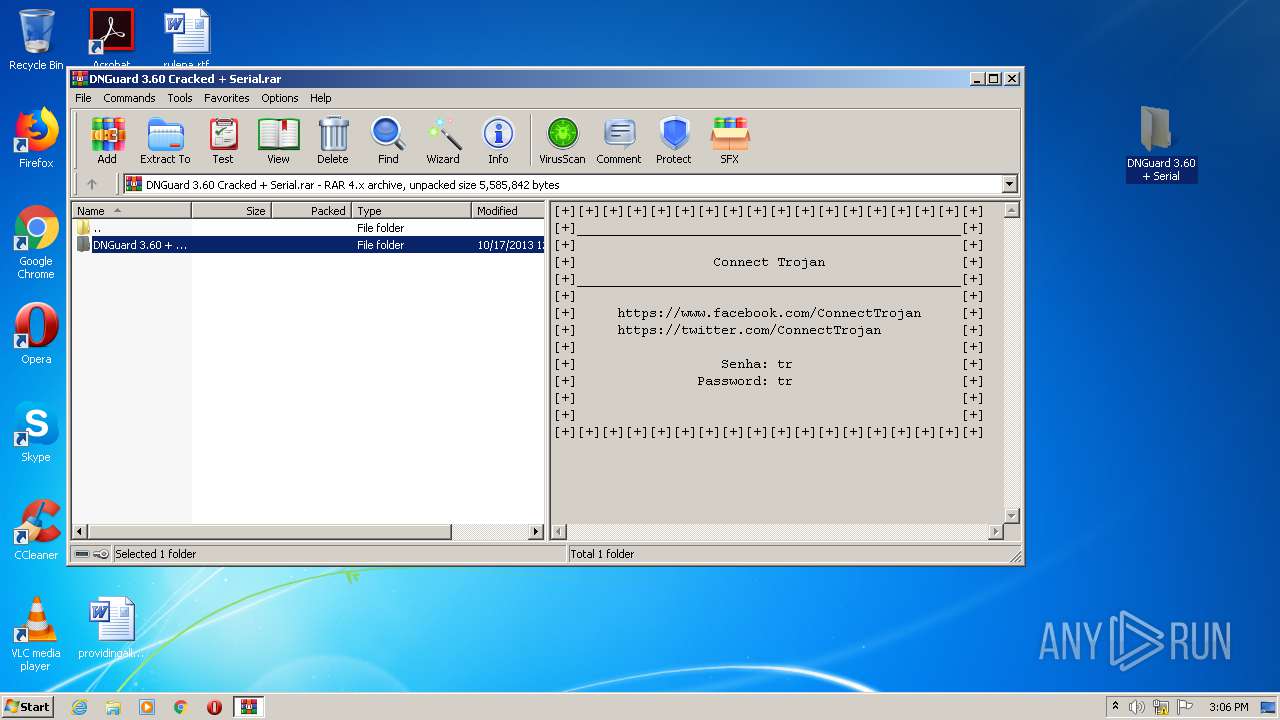
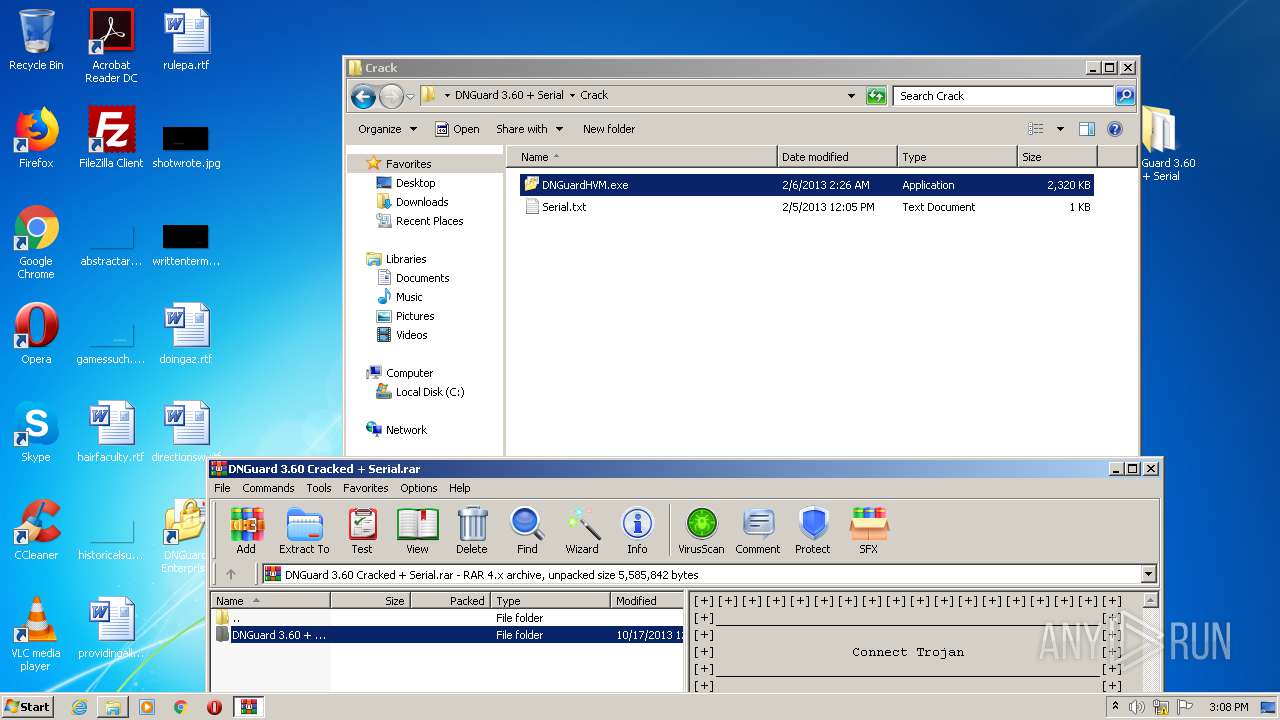
| 2604 | "C:\Users\admin\Desktop\DNGuard 3.60 + Serial\setup.exe" | C:\Users\admin\Desktop\DNGuard 3.60 + Serial\setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
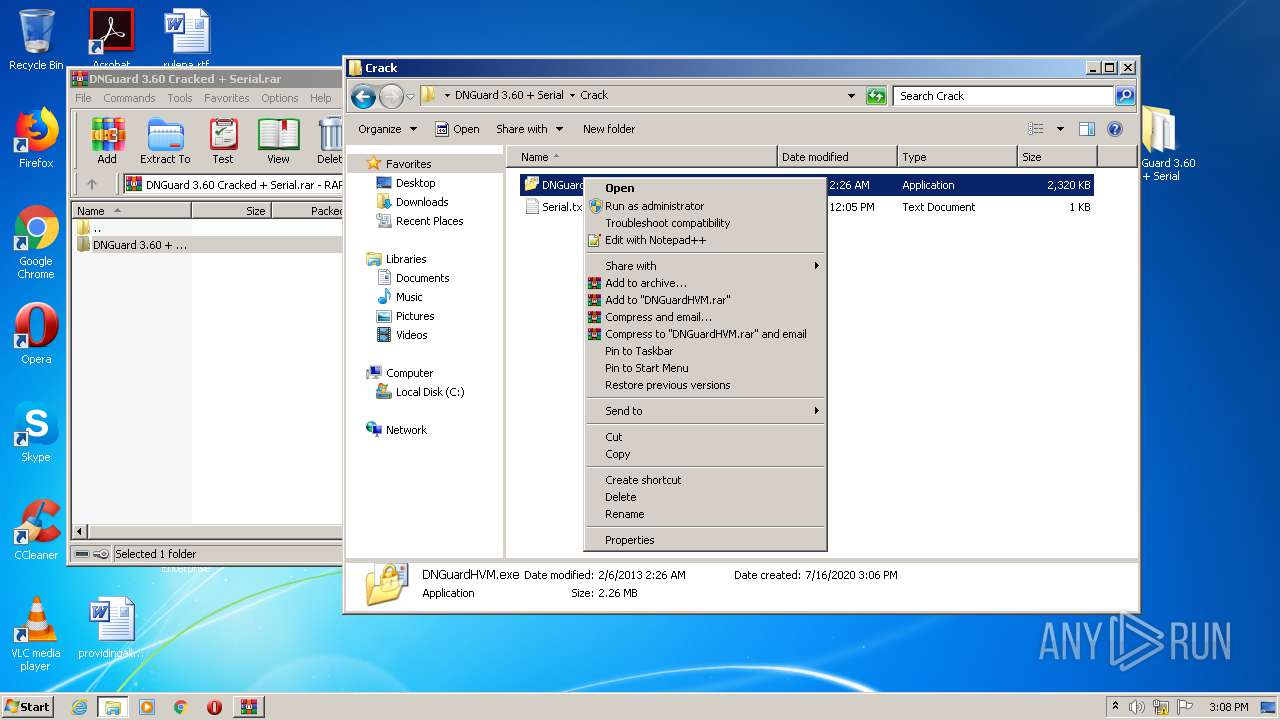
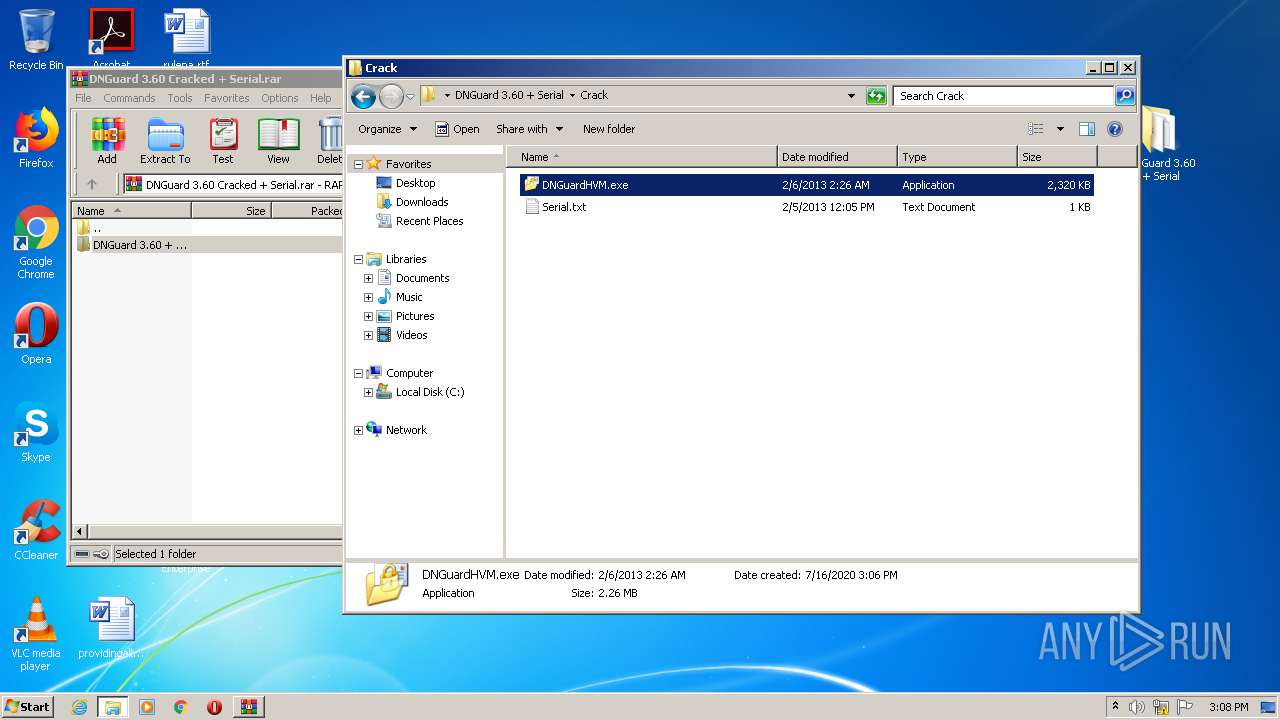
| 2604 | "C:\Users\admin\Desktop\DNGuard 3.60 + Serial\Crack\DNGuardHVM.exe" | C:\Users\admin\Desktop\DNGuard 3.60 + Serial\Crack\DNGuardHVM.exe | — | explorer.exe | |||||||||||
User: admin Company: ZiYuXuan Studio Integrity Level: MEDIUM Description: DotNet Guard HVM Exit code: 0 Version: 3, 6, 0, 0 Modules
| |||||||||||||||
| 2636 | "C:\Users\admin\Desktop\DNGuard 3.60 + Serial\setup.exe" | C:\Users\admin\Desktop\DNGuard 3.60 + Serial\setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
890
Read events
811
Write events
75
Delete events
4
Modification events
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DNGuard 3.60 Cracked + Serial.rar | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2436) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2636) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DNGuard Enterprise |
| Operation: | write | Name: | NSIS:StartMenuDir |
Value: DNGuard Enterprise | |||
Executable files
10
Suspicious files
2
Text files
68
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2436 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2436.23121\DNGuard 3.60 + Serial\Crack\DNGuardHVM.exe | — | |
MD5:— | SHA256:— | |||
| 2436 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2436.23121\DNGuard 3.60 + Serial\Crack\Serial.txt | — | |
MD5:— | SHA256:— | |||
| 2436 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2436.23121\DNGuard 3.60 + Serial\setup.exe | — | |
MD5:— | SHA256:— | |||
| 2436 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2436.23121\DNGuard 3.60 + Serial\Up By DDOS =) Dev-Point.txt | — | |
MD5:— | SHA256:— | |||
| 2636 | setup.exe | C:\Users\admin\AppData\Local\Temp\nsp8B80.tmp\Startmenu.ini | text | |
MD5:— | SHA256:— | |||
| 2636 | setup.exe | C:\Users\admin\AppData\Local\Temp\nsp8B80.tmp\NSISArray.dll | executable | |
MD5:EAFC4EB07D5527B374AA667ED663769E | SHA256:40800FC71777C8D4DA8013EE9BCCDBA0DBCA87AA064E188937AA565A10D859FE | |||
| 2636 | setup.exe | C:\Users\admin\AppData\Local\Temp\nsp8B80.tmp\StartMenu.ini | text | |
MD5:F6AFB9CAD7AB7188FEC2ADD695F8E774 | SHA256:B8B08D18D78DC360B83775BA3B88D47D5F04C49D0BDA921501398D51424D3530 | |||
| 2636 | setup.exe | C:\Program Files\DNGuard Enterprise\DNGuardHVM.exe | executable | |
MD5:AEA0EE460B326D4071E8012CB1A76F3F | SHA256:BB17335BD45D726D93B719325C451898B59EC2C951286B3C3AC7B8D4591F21C3 | |||
| 2636 | setup.exe | C:\Users\admin\AppData\Local\Temp\nsp8B80.tmp\leftimg.bmp | image | |
MD5:D406307F58C4153EF220913F35D1EADF | SHA256:FCC51C1EF8485C5DB06C9438AB54468746AF7520CE8AA8BAACC464F9228C0089 | |||
| 2636 | setup.exe | C:\Users\admin\AppData\Local\Temp\nsp8B80.tmp\gen.bmp | image | |
MD5:531F5B80CC823540F4EC85AAA37BA2D1 | SHA256:67C403510C173EBC3A61FFEEAECD58A2EF26734A04AF7E08553CA382D2A1BBFB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3864 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3864 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
DNGuardHVM.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2010 Oreans Technologies ---
------------------------------------------------
|