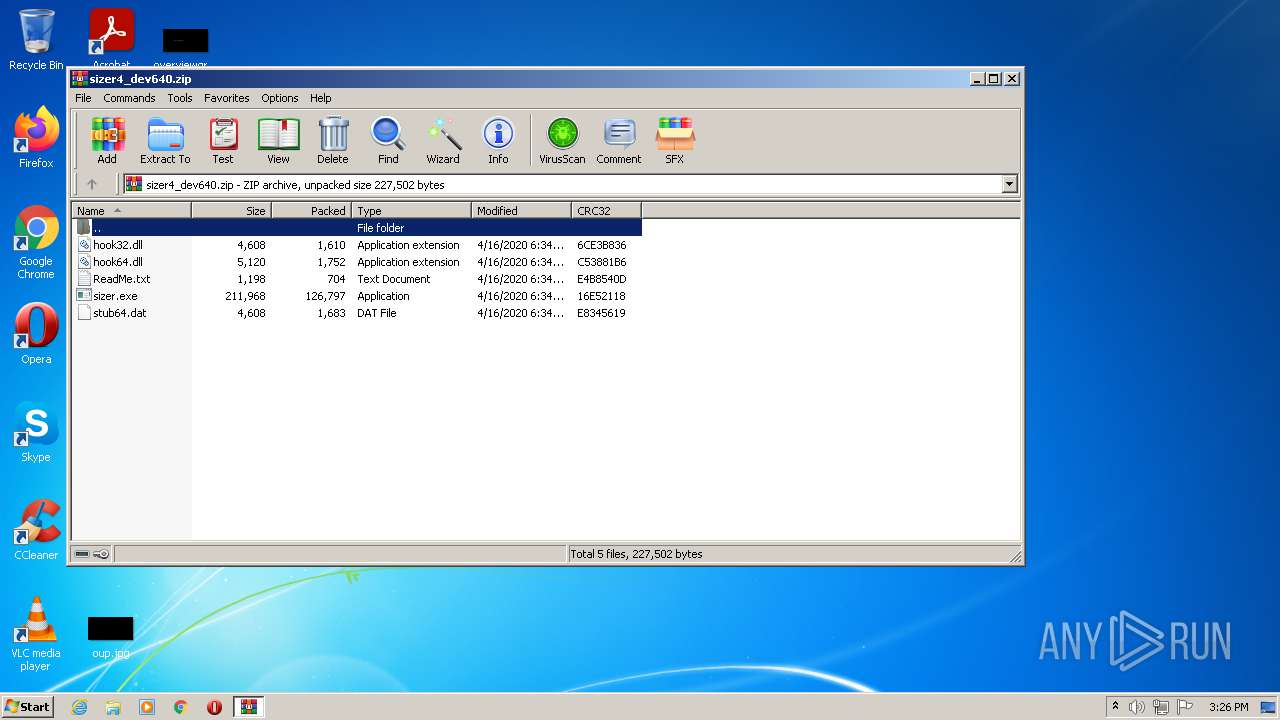
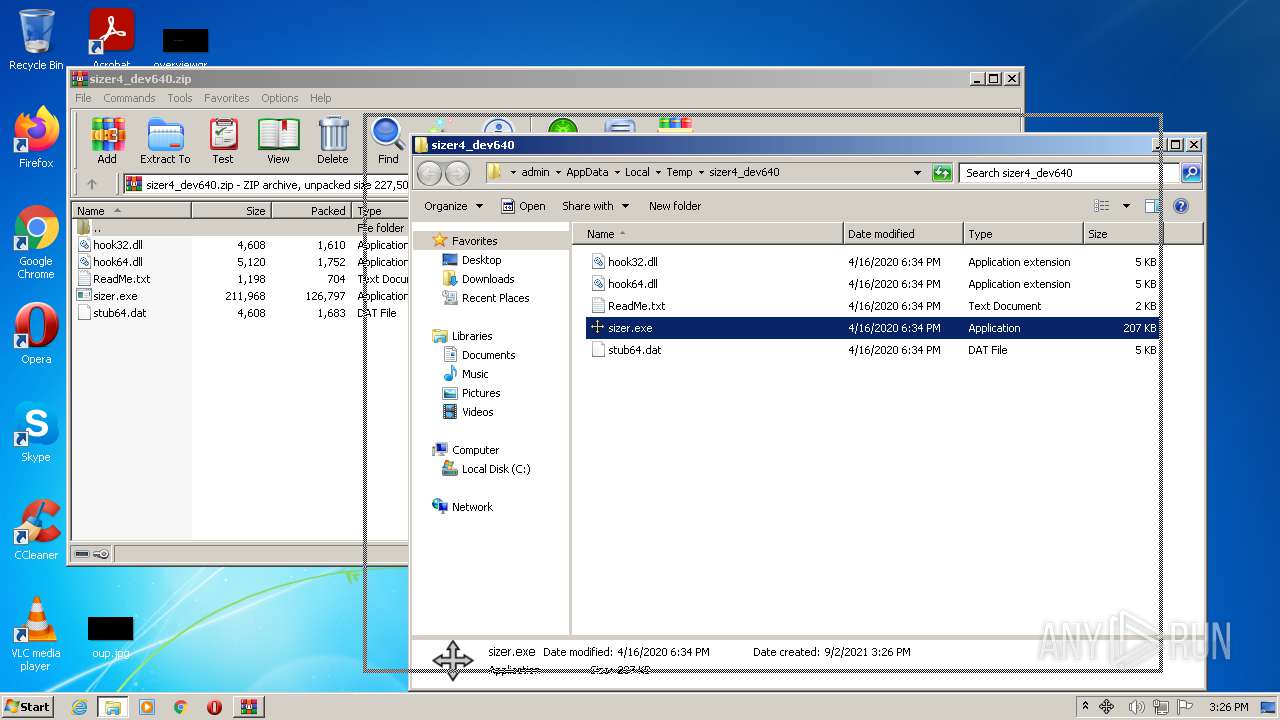
| File name: | sizer4_dev640.zip |
| Full analysis: | https://app.any.run/tasks/21dd79cc-b0b4-4a82-87ef-df125324dc9e |
| Verdict: | Malicious activity |
| Analysis date: | September 02, 2021, 14:25:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 24124614033653DC52A2F42DECC9D705 |
| SHA1: | 3F9B0FAEFCD02CA8877910B3C3B0BE88AB5B6C83 |
| SHA256: | 1E6560E2040F929503372F74BA93B521D9C2C90BC4667A9696B04E28D1044F1A |
| SSDEEP: | 1536:EpSQgWzAkw9/bNQ9ZiVK9jm/a7OCblRdzzKsd8e3Z1wHIAfjalllclJWxtajL+64:r+Pw9/JQ9r8iFbp/Z1w5jk3clJmuJNJe |
MALICIOUS
Loads dropped or rewritten executable
- sizer.exe (PID: 1568)
- Explorer.EXE (PID: 1724)
- DllHost.exe (PID: 3580)
- WinRAR.exe (PID: 3624)
Application was dropped or rewritten from another process
- sizer.exe (PID: 1568)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3624)
- sizer.exe (PID: 1568)
Reads the computer name
- WinRAR.exe (PID: 3624)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3624)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3624)
INFO
Reads the computer name
- DllHost.exe (PID: 3580)
Checks supported languages
- DllHost.exe (PID: 3580)
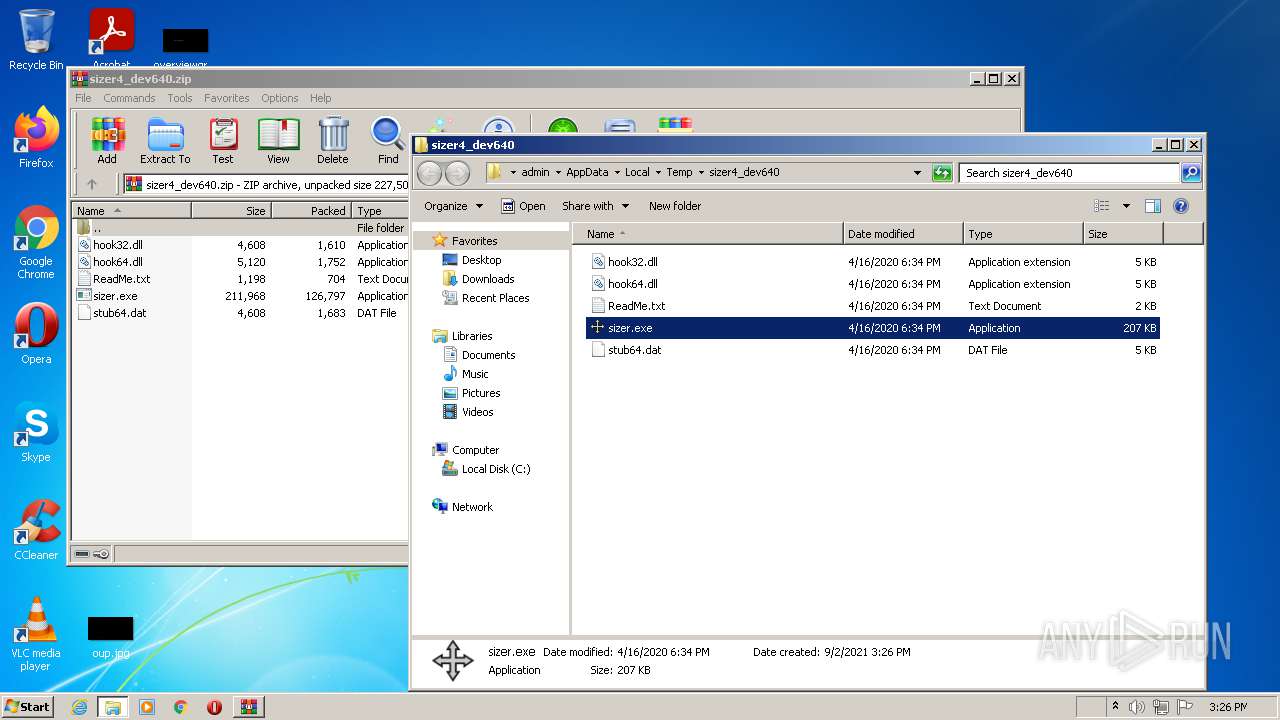
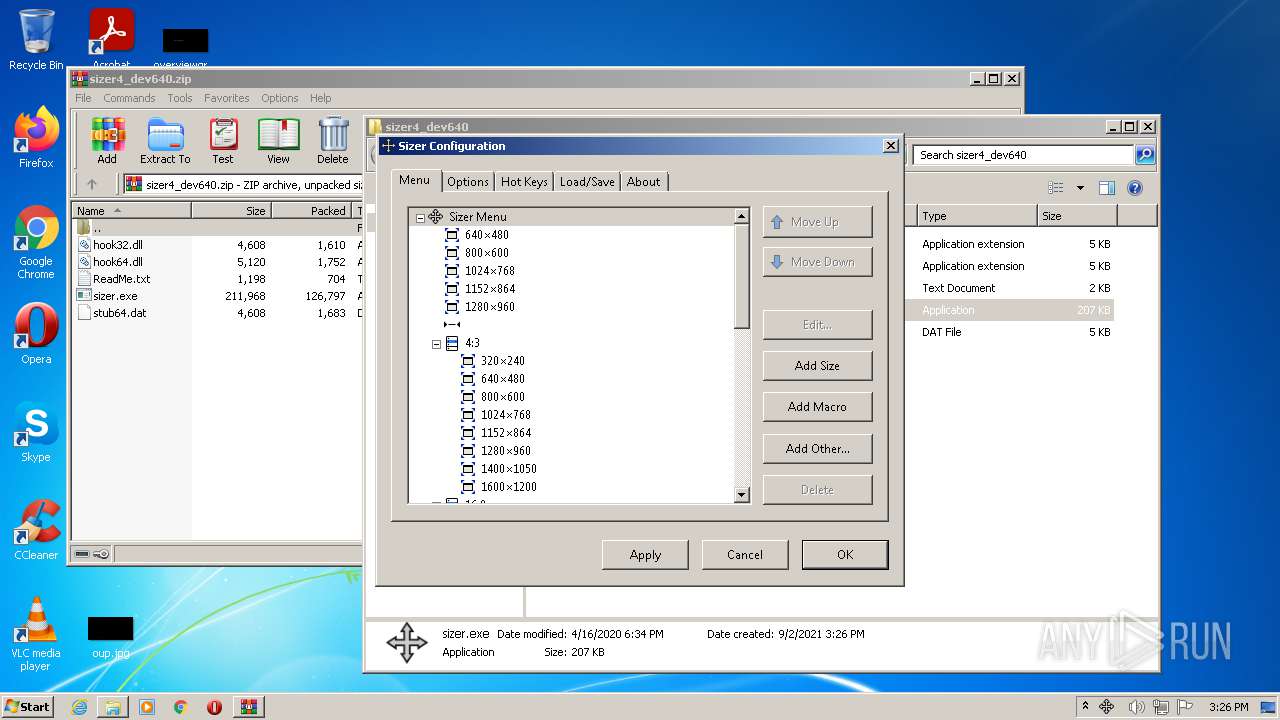
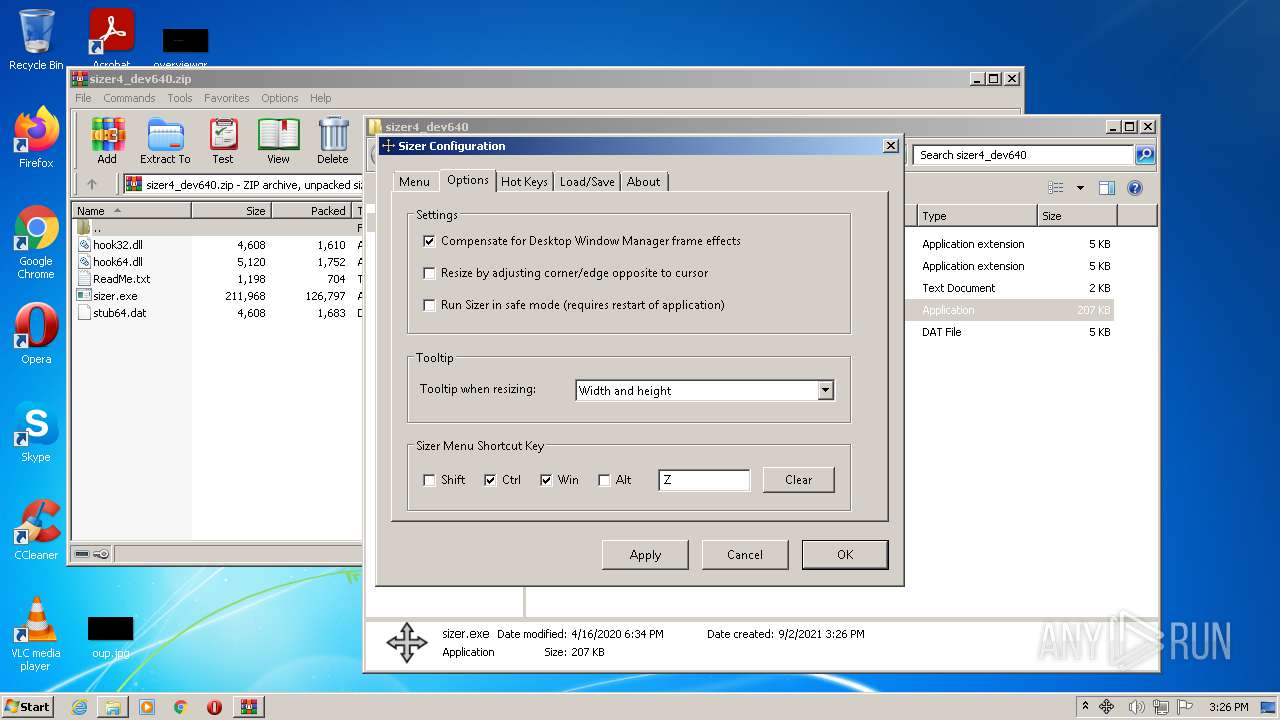
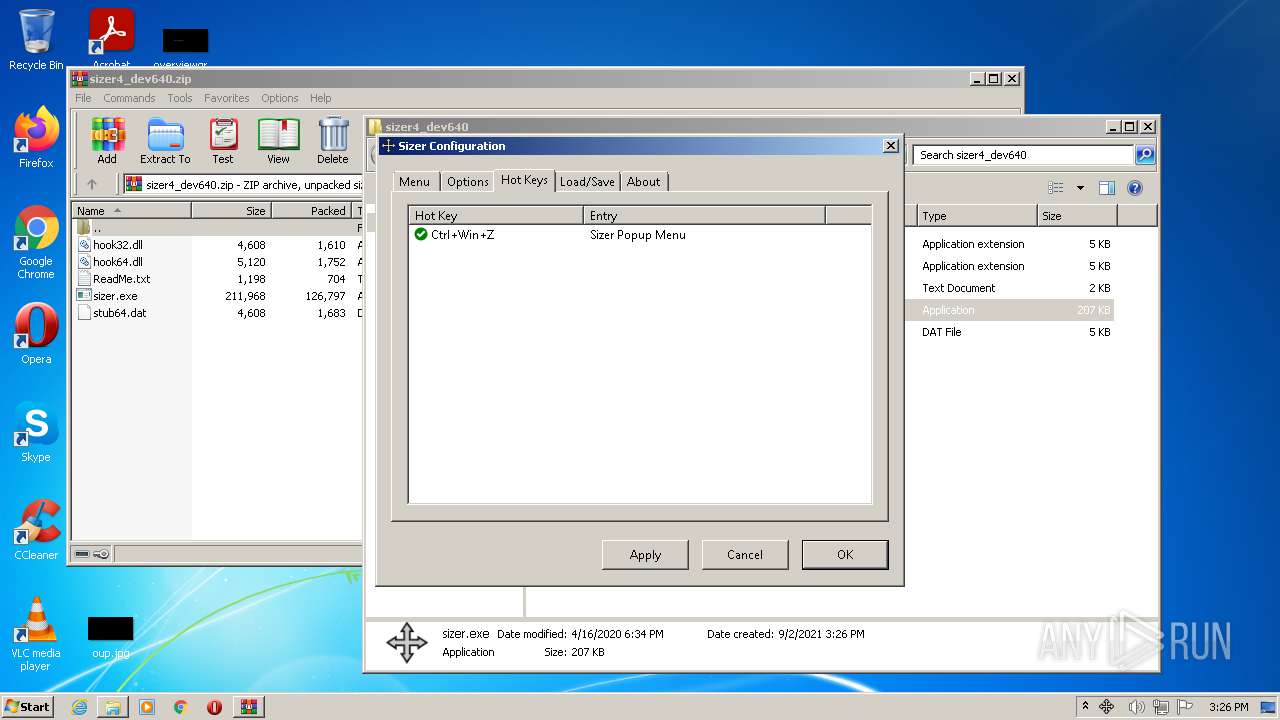
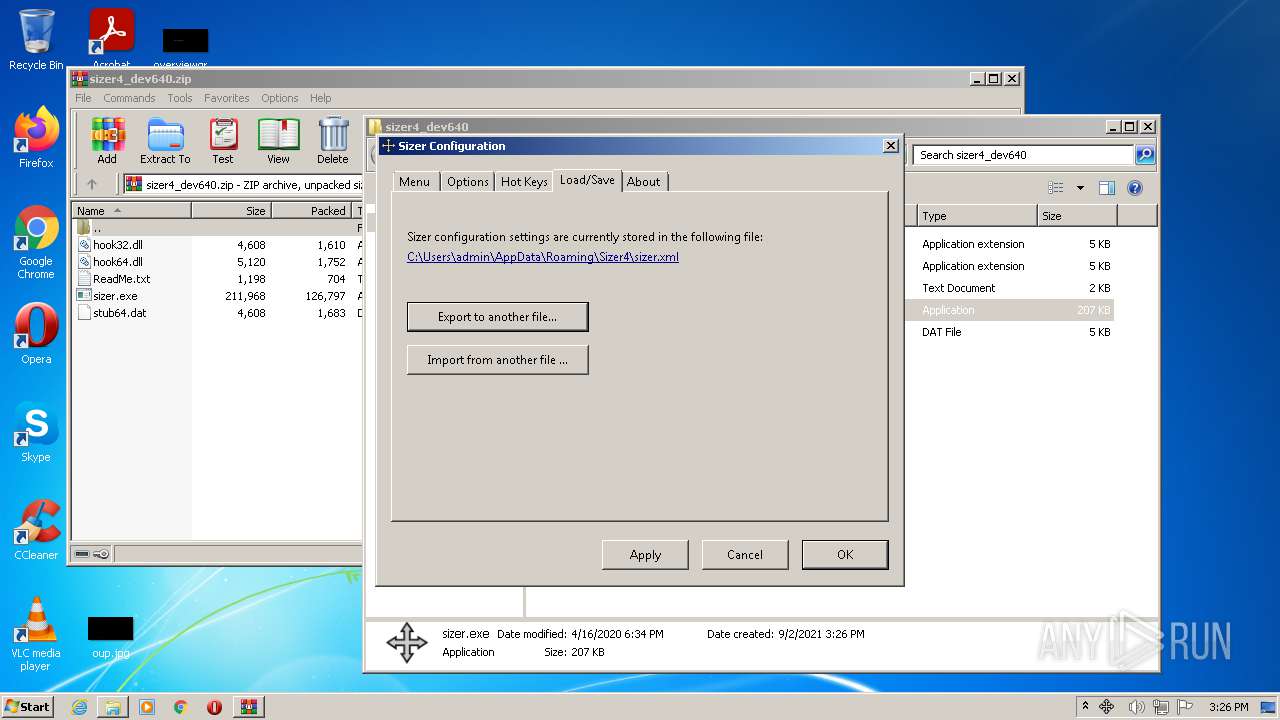
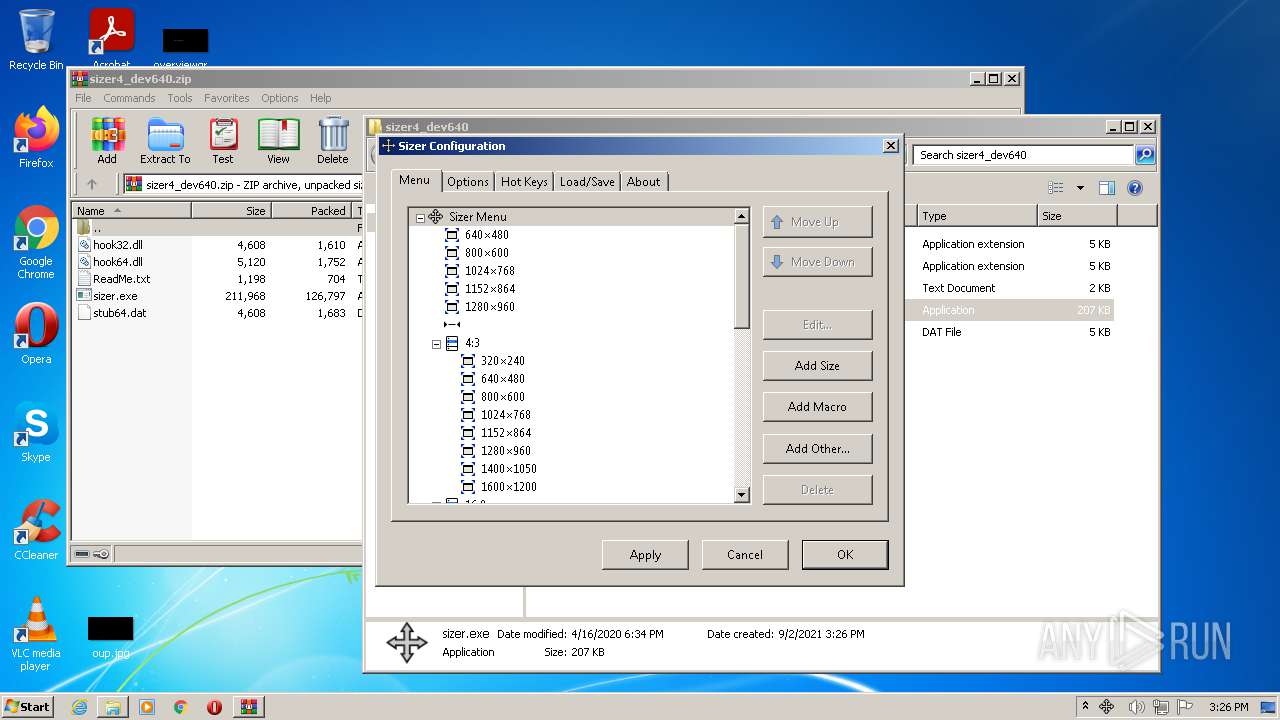
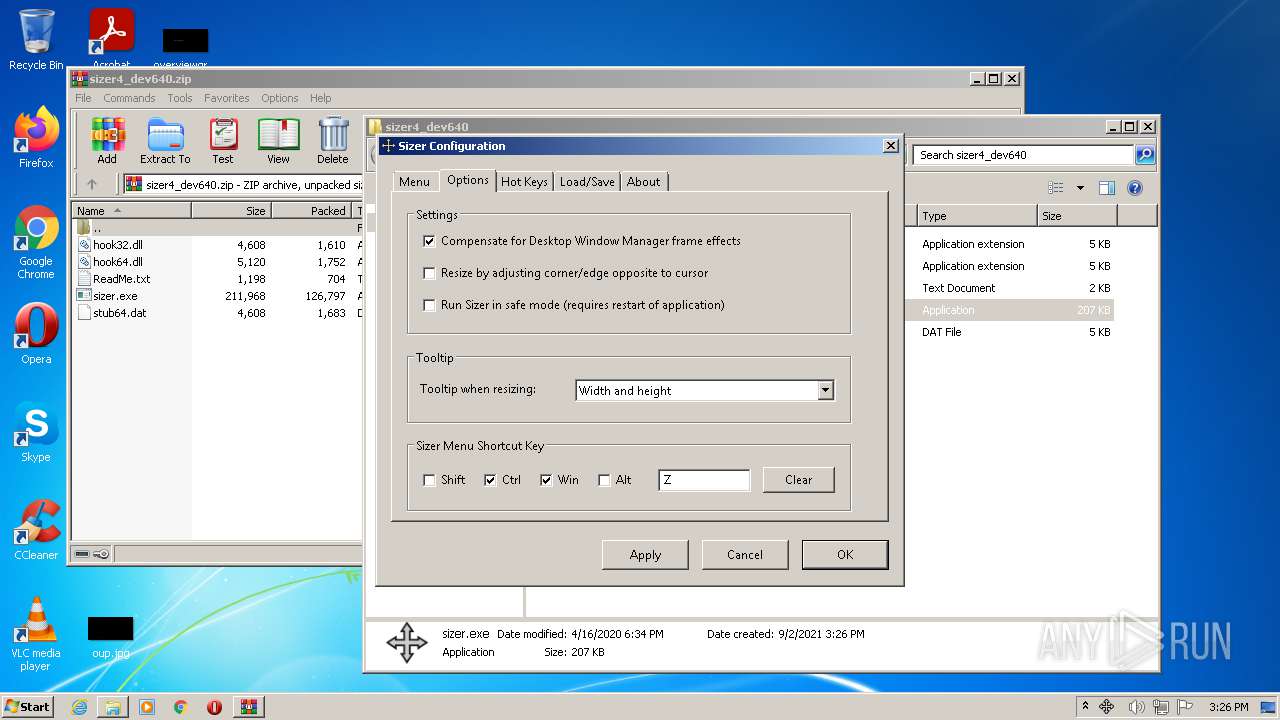
Manual execution by user
- sizer.exe (PID: 1568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | sizer.exe |
|---|---|
| ZipUncompressedSize: | 211968 |
| ZipCompressedSize: | 126797 |
| ZipCRC: | 0x16e52118 |
| ZipModifyDate: | 2020:04:16 18:34:09 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0002 |
| ZipRequiredVersion: | 20 |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
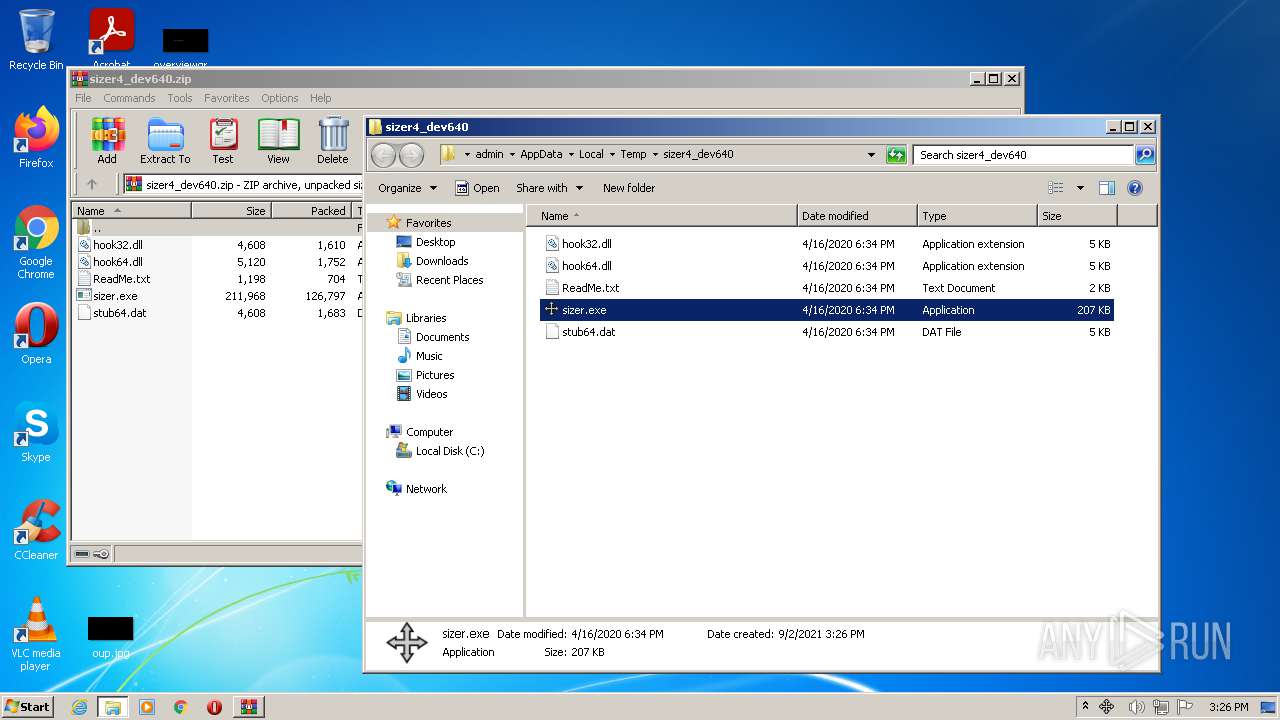
Process information
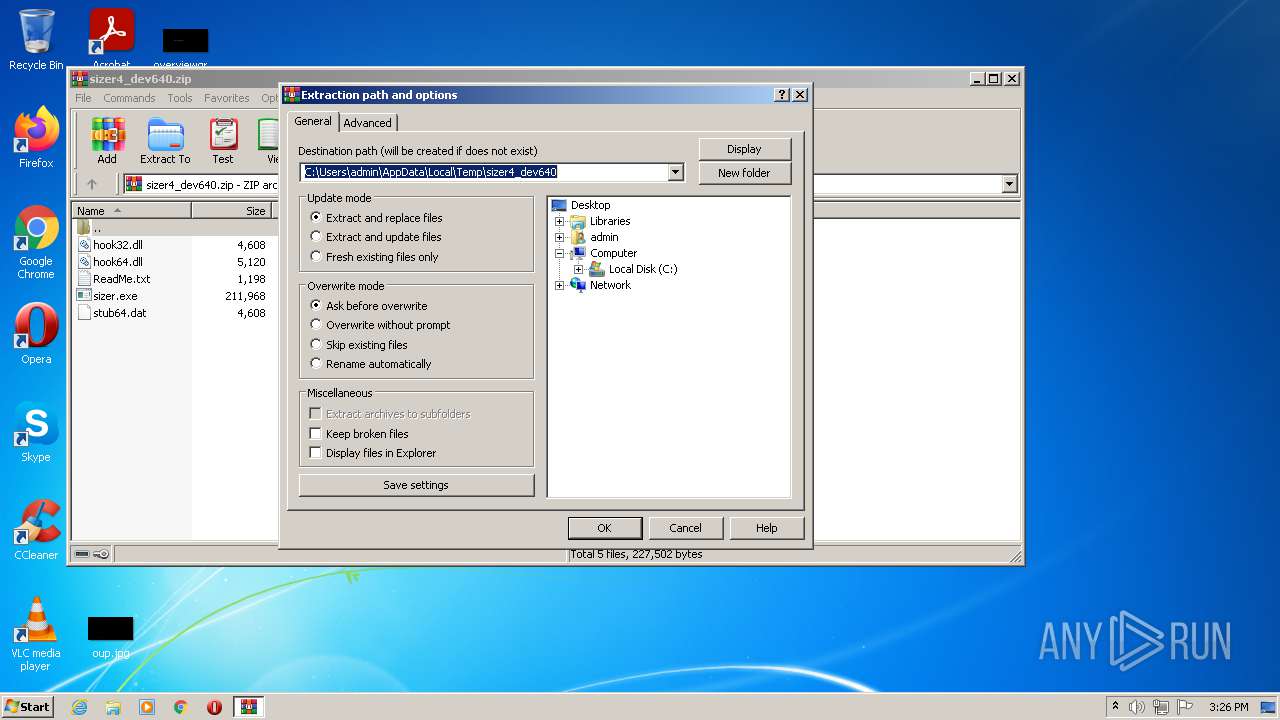
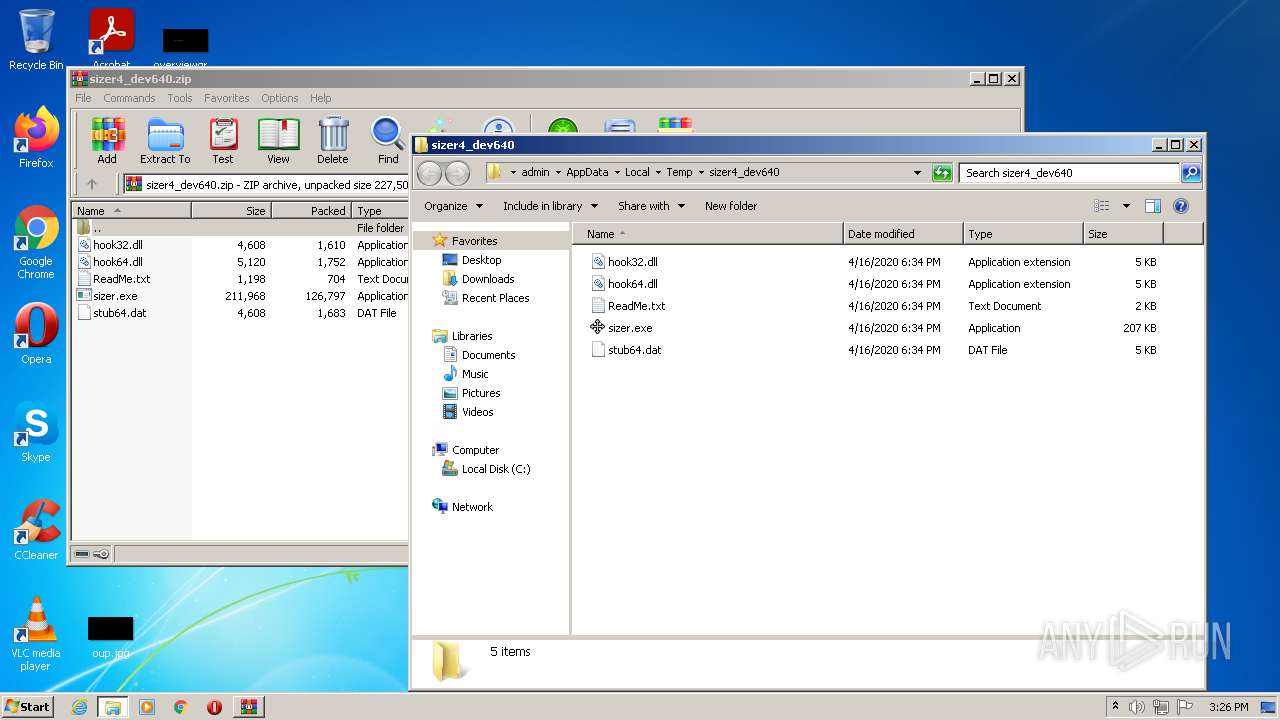
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
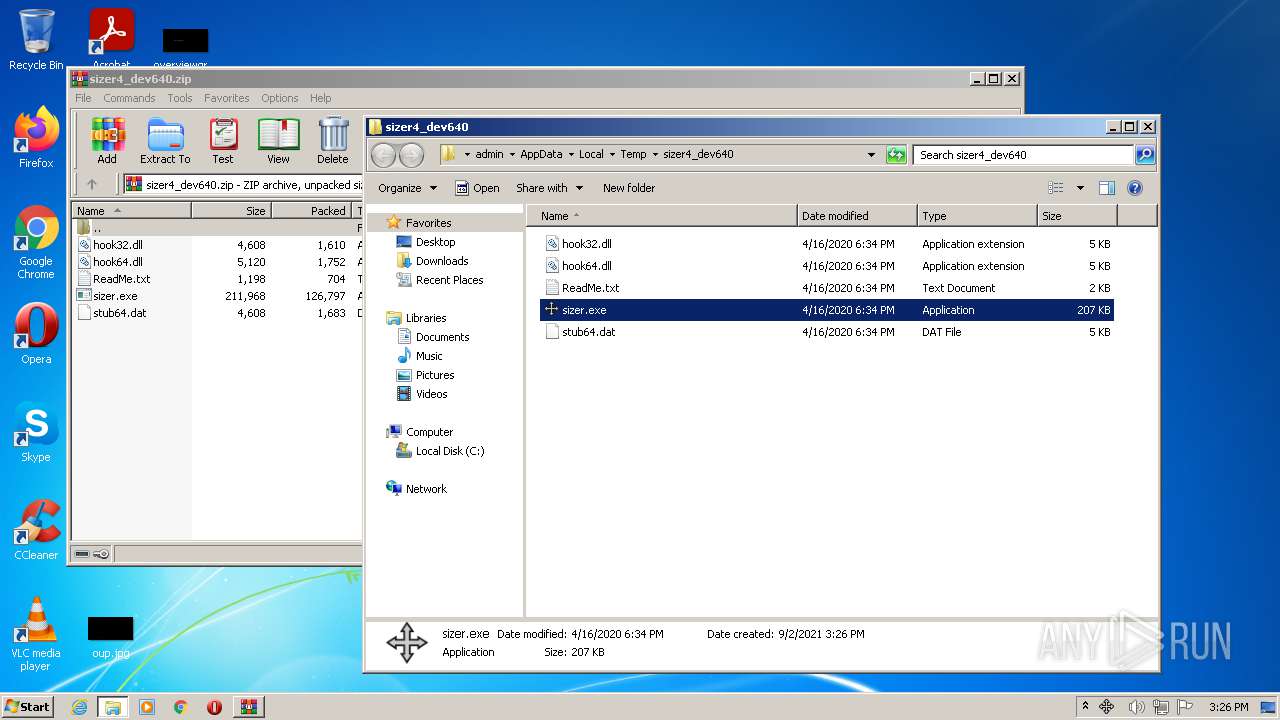
| 1568 | "C:\Users\admin\AppData\Local\Temp\sizer4_dev640\sizer.exe" | C:\Users\admin\AppData\Local\Temp\sizer4_dev640\sizer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Brian Apps Products Integrity Level: MEDIUM Description: Sizer Executable (DEVBUILD) Exit code: 0 Version: 4.0.0.640 Modules
| |||||||||||||||
| 1724 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3580 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3624 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sizer4_dev640.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
1 857
Read events
1 795
Write events
62
Delete events
0
Modification events
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sizer4_dev640.zip | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1724) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
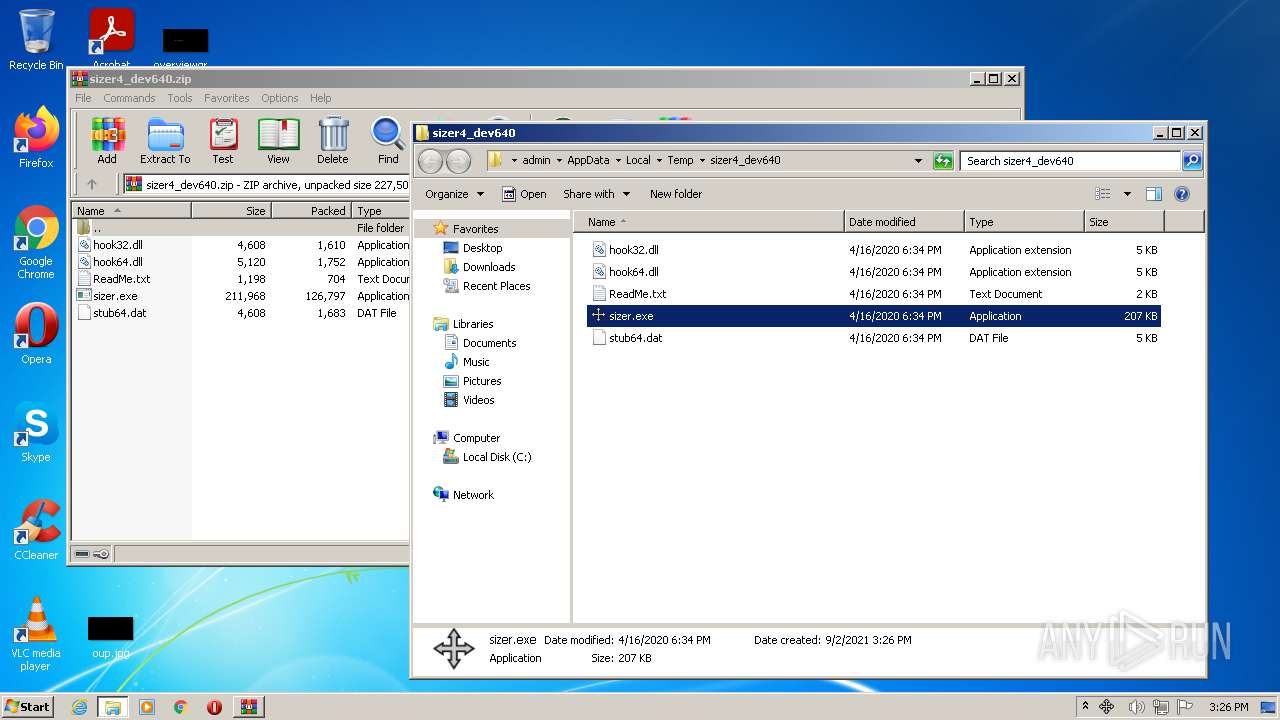
| (PID) Process: | (3624) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sizer4_dev640 | |||
Executable files
4
Suspicious files
0
Text files
1
Unknown types
0
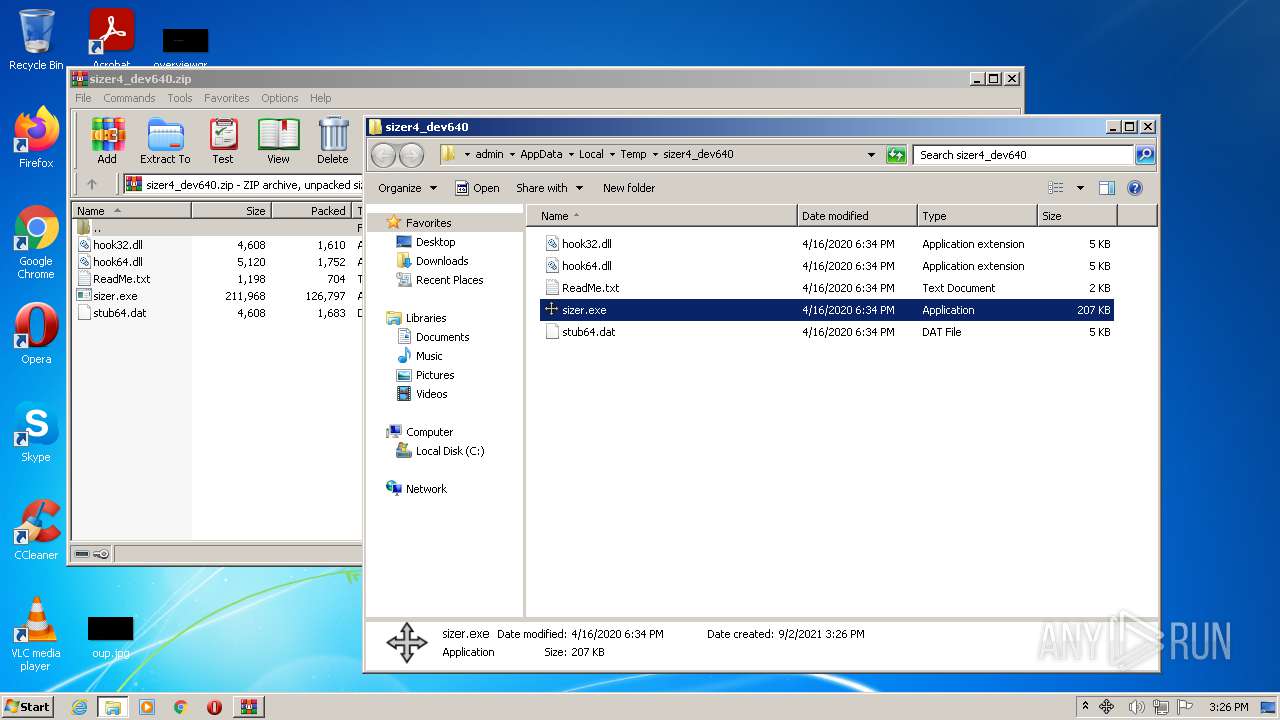
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3624 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\sizer4_dev640\hook32.dll | executable | |
MD5:EE922B592D246C9545D5965514F566A7 | SHA256:62F35DA33D623C5D04547B30597D62C787C3107B334C357C5294C326D75D8FFA | |||
| 3624 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\sizer4_dev640\ReadMe.txt | text | |
MD5:876AA2DDDC6B25FBE291391DC3CC29FD | SHA256:D3831A01621841F5795DFC9253C72CD1BF2321825259925EC39C7B66FD535C9E | |||
| 3624 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\sizer4_dev640\hook64.dll | executable | |
MD5:C0252168CC71801C2B912B24743E38C5 | SHA256:9813C005606F58715D4FEC7645A72A403C7DD0EE1EB2AF8966AF81C0AE001A22 | |||
| 3624 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\sizer4_dev640\sizer.exe | executable | |
MD5:A8DAB68D7B1B5D50774C3608DC8489AC | SHA256:DB42C58DB5B583677B3FE51773B25413945F9B4C135CEC5974EAAFE6FB5F77E5 | |||
| 3624 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\sizer4_dev640\stub64.dat | executable | |
MD5:B723052840461628254BD0E91B6C4B43 | SHA256:261BC00E81B3BB90876EBDAC71D03C1B2F3064B612681B44B6AB32F876291B96 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report