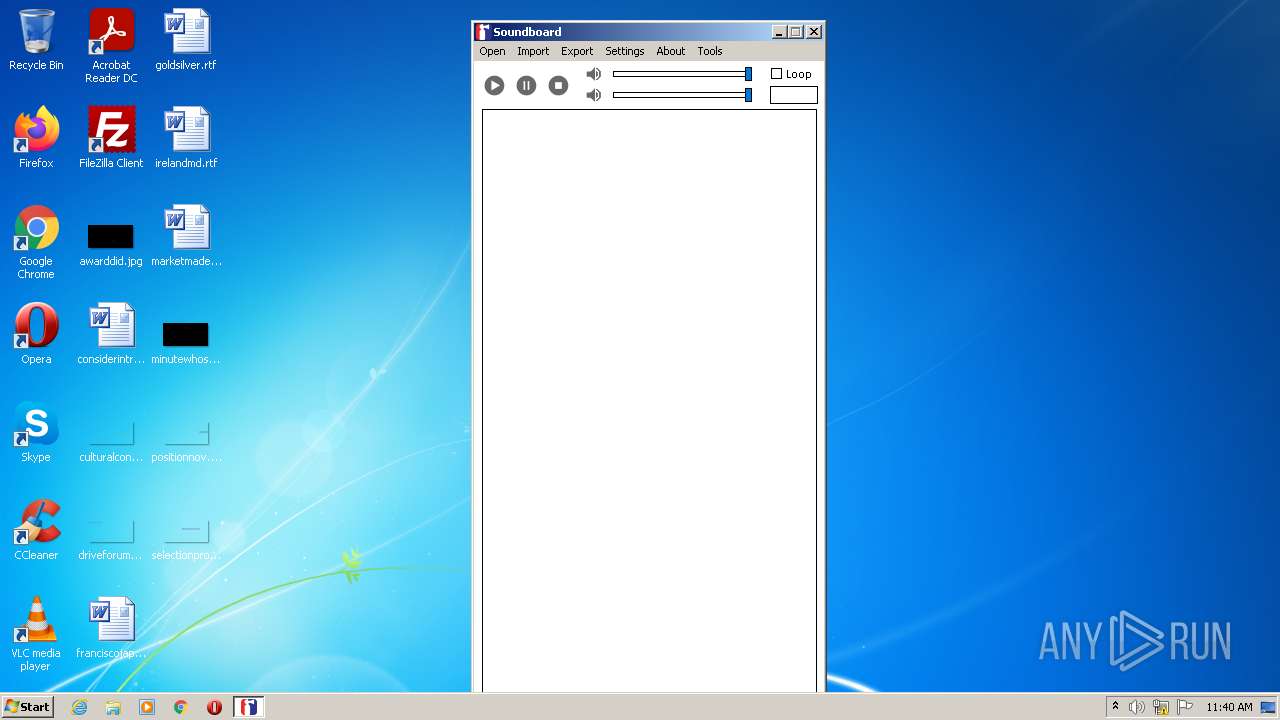
| File name: | Soundboard.exe |
| Full analysis: | https://app.any.run/tasks/4f67193d-1b22-4fda-a644-a339df3b74dd |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2022, 11:39:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 63782640DF64ED0731DF11FB964AB275 |
| SHA1: | D8E23B88F1013BFC04F95CFEA1352E9FBBA01984 |
| SHA256: | 1E654992424E243AC85F71C96D31422CF8F50F3DCA6F44858474DA8CBD740DB2 |
| SSDEEP: | 24576:8zDPCPqW5A/MSpIs9S79TyL+B4dP3yrSocY3pvtw81uTU+Z9T5djhqtBHJPBHJ8:8zLVKT8+B4dPirSok8UTPbT5hItBHJPD |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts Internet Explorer
- Soundboard.exe (PID: 2808)
Checks supported languages
- Soundboard.exe (PID: 2808)
Reads the computer name
- Soundboard.exe (PID: 2808)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2580)
INFO
Checks supported languages
- iexplore.exe (PID: 2580)
- iexplore.exe (PID: 3924)
Changes internet zones settings
- iexplore.exe (PID: 3924)
Reads the computer name
- iexplore.exe (PID: 2580)
- iexplore.exe (PID: 3924)
Application launched itself
- iexplore.exe (PID: 3924)
Reads settings of System Certificates
- iexplore.exe (PID: 2580)
- iexplore.exe (PID: 3924)
Reads internet explorer settings
- iexplore.exe (PID: 2580)
Checks Windows Trust Settings
- iexplore.exe (PID: 3924)
- iexplore.exe (PID: 2580)
Reads the date of Windows installation
- iexplore.exe (PID: 3924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (56.2) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (38.1) |
| .exe | | | Win32 EXE PECompact compressed (generic) (3.5) |
| .exe | | | Win32 Executable Delphi generic (1.1) |
| .exe | | | Win32 Executable (generic) (0.3) |
EXIF
EXE
| ProductVersion: | 1.0.0.0 |
|---|---|
| ProductName: | Soundboard |
| OriginalFileName: | Soundboard.exe |
| LegalCopyright: | Copyright WobbyChip |
| InternalName: | Soundboard.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Soundboard |
| CompanyName: | WobbyChip |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x100ecc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 207360 |
| CodeSize: | 1048576 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | WobbyChip |
| FileDescription: | Soundboard |
| FileVersion: | 1.0.0.0 |
| InternalName: | Soundboard.exe |
| LegalCopyright: | Copyright WobbyChip |
| OriginalFilename: | Soundboard.exe |
| ProductName: | Soundboard |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000FFFBC | 0x00100000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55339 |
DATA | 0x00101000 | 0x0000C564 | 0x0000C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.02795 |
BSS | 0x0010E000 | 0x00003B65 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00112000 | 0x000030E2 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.94947 |
.tls | 0x00116000 | 0x00000038 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00117000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x00118000 | 0x00010BCC | 0x00010C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.64961 |
.rsrc | 0x00129000 | 0x00012400 | 0x00012400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.08857 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06612 | 549 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.59414 | 4264 | UNKNOWN | Latvian - Latvia | RT_ICON |
3 | 3.1443 | 9640 | UNKNOWN | Latvian - Latvia | RT_ICON |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4072 | 3.07169 | 632 | UNKNOWN | UNKNOWN | RT_STRING |
4073 | 3.15559 | 872 | UNKNOWN | UNKNOWN | RT_STRING |
4074 | 3.14046 | 956 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
quartz.dll |
shell32.dll |
user32.dll |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2580 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3924 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2808 | "C:\Users\admin\AppData\Local\Temp\Soundboard.exe" | C:\Users\admin\AppData\Local\Temp\Soundboard.exe | — | Explorer.EXE | |||||||||||
User: admin Company: WobbyChip Integrity Level: MEDIUM Description: Soundboard Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3924 | "C:\Program Files\Internet Explorer\iexplore.exe" https://wobbychip.github.io/ | C:\Program Files\Internet Explorer\iexplore.exe | Soundboard.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 828
Read events
16 675
Write events
147
Delete events
6
Modification events
| (PID) Process: | (2808) Soundboard.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Soundboard.exe | |||
| (PID) Process: | (2808) Soundboard.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Soundboard.exe | |||
| (PID) Process: | (2808) Soundboard.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{E0F158E1-CB04-11D0-BD4E-00A0C911CE86}\Default DirectSound Device |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2808) Soundboard.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{E0F158E1-CB04-11D0-BD4E-00A0C911CE86} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2808) Soundboard.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{E0F158E1-CB04-11D0-BD4E-00A0C911CE86}\Speakers (Realtek AC'97 Audio) |
| Operation: | write | Name: | FriendlyName |
Value: Speakers (Realtek AC'97 Audio) | |||
| (PID) Process: | (2808) Soundboard.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{E0F158E1-CB04-11D0-BD4E-00A0C911CE86}\Speakers (Realtek AC'97 Audio) |
| Operation: | write | Name: | CLSID |
Value: {E30629D1-27E5-11CE-875D-00608CB78066} | |||
| (PID) Process: | (2808) Soundboard.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{E0F158E1-CB04-11D0-BD4E-00A0C911CE86}\Speakers (Realtek AC'97 Audio) |
| Operation: | write | Name: | FilterData |
Value: 02000000000020000100000000000000307069330200000000000000010000000000000000000000307479330000000038000000480000006175647300001000800000AA00389B7100000000000000000000000000000000 | |||
| (PID) Process: | (2808) Soundboard.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{E0F158E1-CB04-11D0-BD4E-00A0C911CE86}\Speakers (Realtek AC'97 Audio) |
| Operation: | write | Name: | WaveOutId |
Value: 0 | |||
| (PID) Process: | (2808) Soundboard.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{E0F158E1-CB04-11D0-BD4E-00A0C911CE86}\Speakers (Realtek AC'97 Audio) |
| Operation: | write | Name: | ClassManagerFlags |
Value: 2 | |||
| (PID) Process: | (2808) Soundboard.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{E0F158E1-CB04-11D0-BD4E-00A0C911CE86}\Default WaveOut Device |
| Operation: | write | Name: | FriendlyName |
Value: Default WaveOut Device | |||
Executable files
0
Suspicious files
18
Text files
14
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\script[1].js | text | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style[1].css | text | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\8MF5JSBJ.htm | html | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\css2[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
32
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2580 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEC5GLYwFefbxEgAAAAAAYIc%3D | US | der | 471 b | whitelisted |
2580 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGM9pOpF81f4CgAAAAEz%2Bqg%3D | US | der | 471 b | whitelisted |
2580 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2580 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3924 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3924 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3924 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2580 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2580 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2580 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c4651b305c706602 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | iexplore.exe | 185.199.111.153:443 | wobbychip.github.io | GitHub, Inc. | NL | shared |
2580 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
2580 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2580 | iexplore.exe | 104.18.22.52:443 | kit.fontawesome.com | Cloudflare Inc | US | unknown |
2580 | iexplore.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2580 | iexplore.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2580 | iexplore.exe | 142.250.181.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2580 | iexplore.exe | 188.114.96.7:443 | ka-f.fontawesome.com | Cloudflare Inc | US | malicious |
3924 | iexplore.exe | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
3924 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wobbychip.github.io |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
kit.fontawesome.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ka-f.fontawesome.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
i.imgur.com |
| malicious |
api.bing.com |
| whitelisted |