| download: | index.html |
| Full analysis: | https://app.any.run/tasks/07e4d75b-6da8-49c5-b41a-c8a56fae67cf |
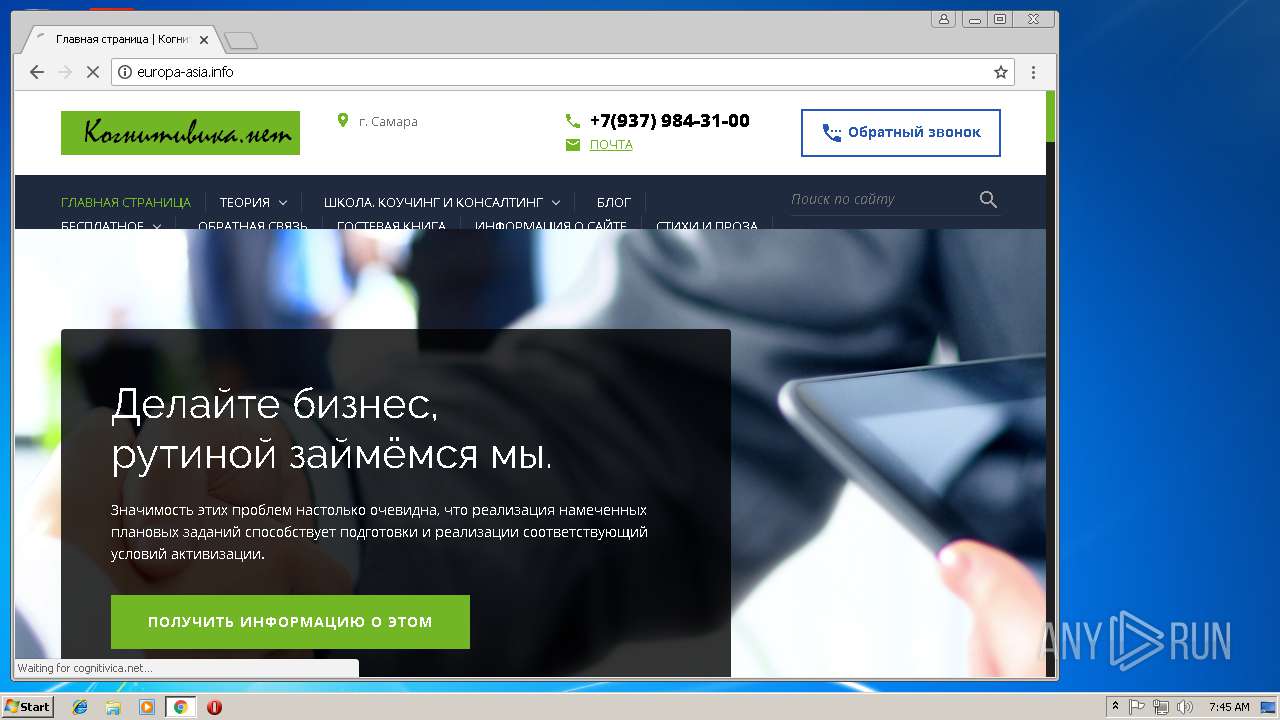
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 07:42:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | F493A691F3D374C9B69F6CA78D649FA8 |
| SHA1: | E6D048B41294F497D7523DD1F6CEFF54A9D93F8F |
| SHA256: | 1E636166DF9F2FB3ED23268FD725F14E03169AE9DE3EAE947890752B42D11CFD |
| SSDEEP: | 1536:tdmxbZVIDoAu+GaL3Unvh88F1PFKnBUuMEcyF9KCW1DGUj8v8kHIjQyi9S4Jmian:tnBUu/fWFGUjIHIjQb9aYqoNrw |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
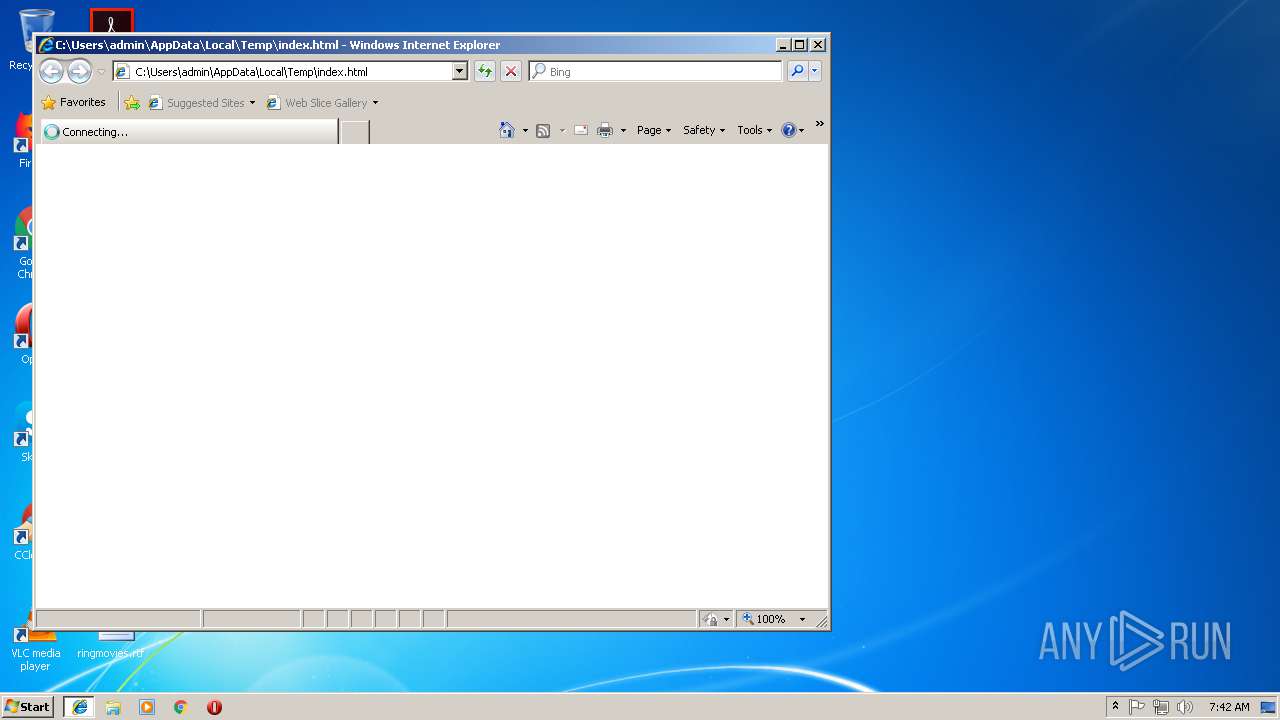
Application launched itself
- iexplore.exe (PID: 3864)
- chrome.exe (PID: 3148)
Changes internet zones settings
- iexplore.exe (PID: 3864)
Creates files in the user directory
- iexplore.exe (PID: 2124)
Reads internet explorer settings
- iexplore.exe (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html; charset=utf-8 |
|---|---|
| HTTPEquivXUACompatible: | IE=edge,chrome=1 |
| CacheControl: | no-cache |
| csrfToken: | 8eb503fab1d59facd0a97efe616b6315 |
| Title: | РБК — новости, акции, курсы валют, доллар, евро |
| Description: | "РосБизнесКонсалтинг" - ведущая российская компания, работающая в сферах масс-медиа и информационных технологий. |
| Keywords: | новости, доллар, политика, курс, акции, облигации, нефть, рубль, евро, финансы, экономика, банк, кредит, вексель, информация, фондовый, инвестиционный, рынок, недвижимость, валюта, эмитент, комментарии, аналитика, продаж/продажа, цена, компания, товары, исследование, прогноз, индекс, рейтинг, биржа, семинар, фондовый, ПИФ, доходность, IPO, паевой |
| ReplyTo: | webmaster@rbc.ru |
| twitterCard: | summary |
| twitterSite: | @ru_rbc |
| twitterCreator: | @ru_rbc |
| twitterTitle: | РБК – новости в реальном времени |
| twitterDescription: | Главные новости политики, экономики и бизнеса, комментарии аналитиков, финансовые данные с российских и мировых биржевых систем на сайте rbc.ru. |
Total processes
57
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,18219285468946687794,17168578975810867758,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C7729E6A8B3DD084034CB472CAAC653B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C7729E6A8B3DD084034CB472CAAC653B --renderer-client-id=16 --mojo-platform-channel-handle=3900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=872,18219285468946687794,17168578975810867758,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8CA3037210D4EFD9A761D23B3314952A --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,18219285468946687794,17168578975810867758,131072 --enable-features=PasswordImport --service-pipe-token=F5276787AE38F5CFBA779FA78977E5B7 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F5276787AE38F5CFBA779FA78977E5B7 --renderer-client-id=5 --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,18219285468946687794,17168578975810867758,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=ED84CE572782F88F91FAFB036DEF9FF3 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=ED84CE572782F88F91FAFB036DEF9FF3 --renderer-client-id=10 --mojo-platform-channel-handle=4084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,18219285468946687794,17168578975810867758,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=BD8228C7D97F5BE2B3AC70E9211B89AD --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=BD8228C7D97F5BE2B3AC70E9211B89AD --renderer-client-id=18 --mojo-platform-channel-handle=4556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,18219285468946687794,17168578975810867758,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F0339955FDF4AF2846989CE3EC889583 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F0339955FDF4AF2846989CE3EC889583 --renderer-client-id=6 --mojo-platform-channel-handle=1696 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,18219285468946687794,17168578975810867758,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=75DC7024431EC606C1E0F7C972BD5D55 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=75DC7024431EC606C1E0F7C972BD5D55 --renderer-client-id=12 --mojo-platform-channel-handle=2620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,18219285468946687794,17168578975810867758,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3F89B17EEC8E1401F69F86C2FC8CFFCE --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3F89B17EEC8E1401F69F86C2FC8CFFCE --renderer-client-id=19 --mojo-platform-channel-handle=4160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3864 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=872,18219285468946687794,17168578975810867758,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=31512D70CD79F7EBD58782527C2E5C18 --mojo-platform-channel-handle=3732 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
849
Read events
728
Write events
116
Delete events
5
Modification events
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {D42074C5-E329-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B000400080007002A0018002D00 | |||
Executable files
0
Suspicious files
135
Text files
283
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF857ACFBCB7925307.TMP | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4D497D5B0813CF38.TMP | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD1799A74097F2AAB.TMP | — | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2757bbde-ba8a-434e-88c1-c3a592b4f505.tmp | — | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{4BBB6F4B-AC5C-11E8-969E-5254004AAD11}.dat | binary | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{D42074C6-E329-11E8-BFAB-5254004AAD11}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
352
TCP/UDP connections
246
DNS requests
154
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
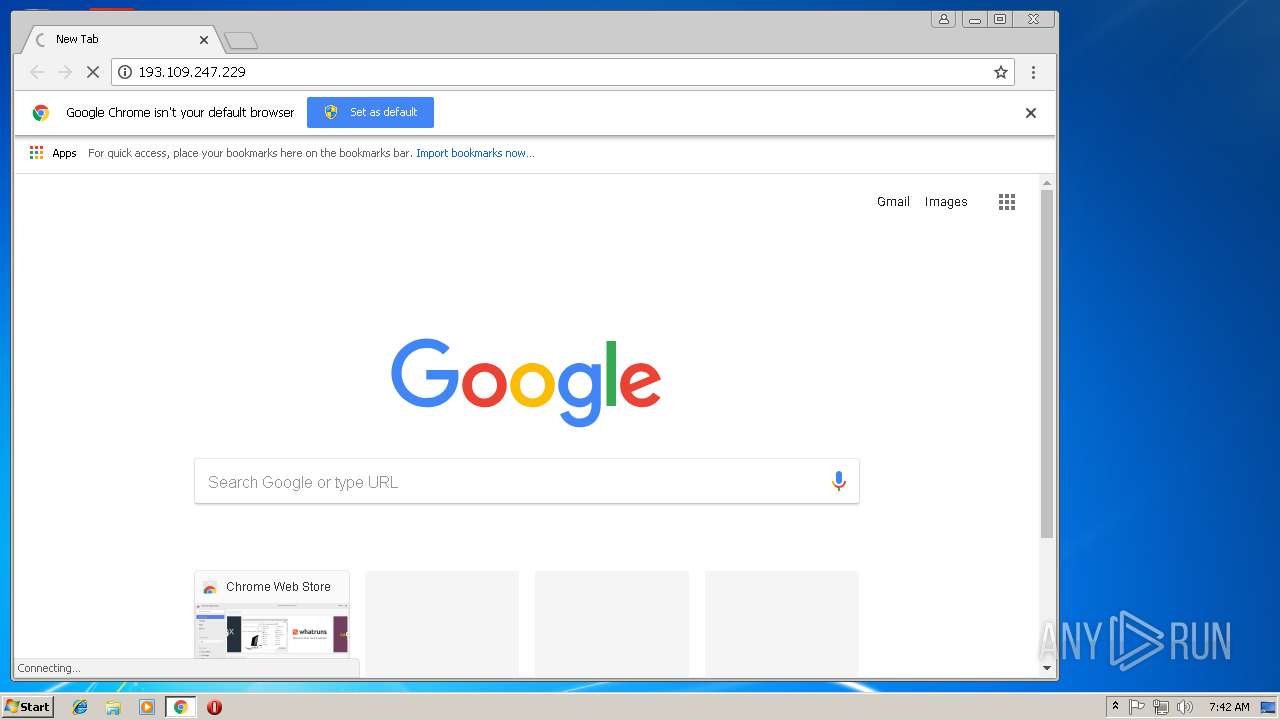
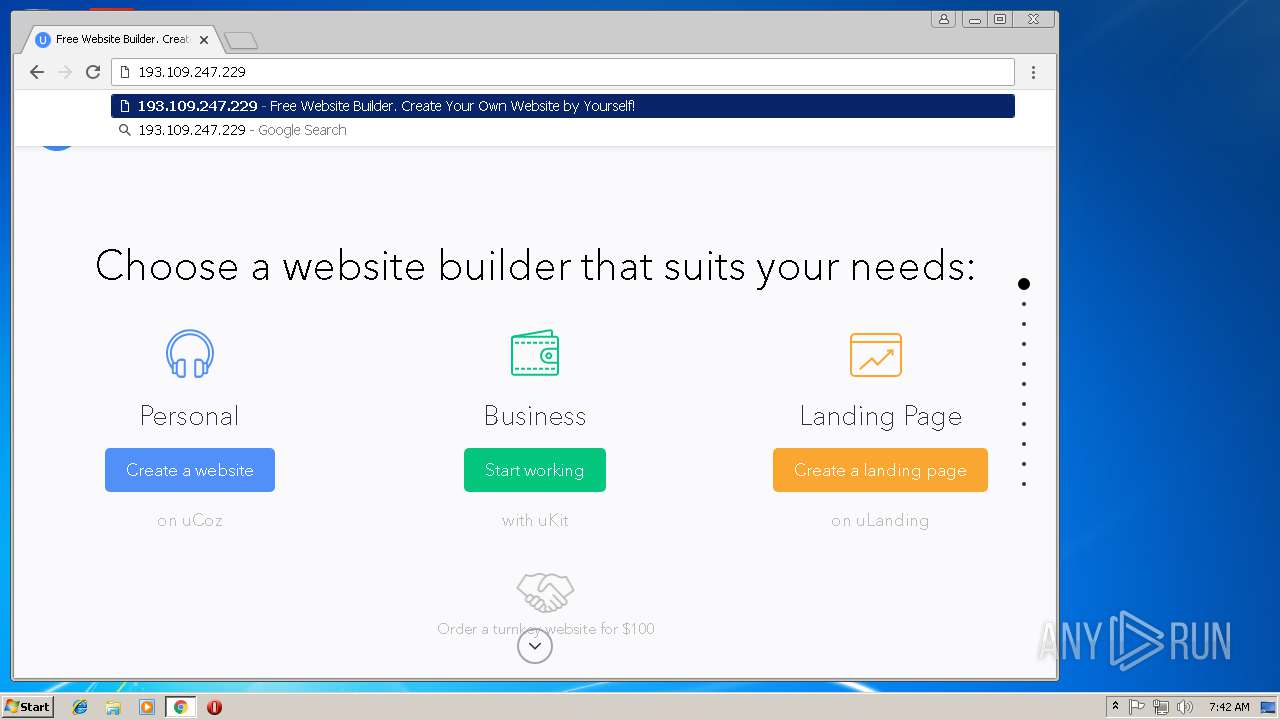
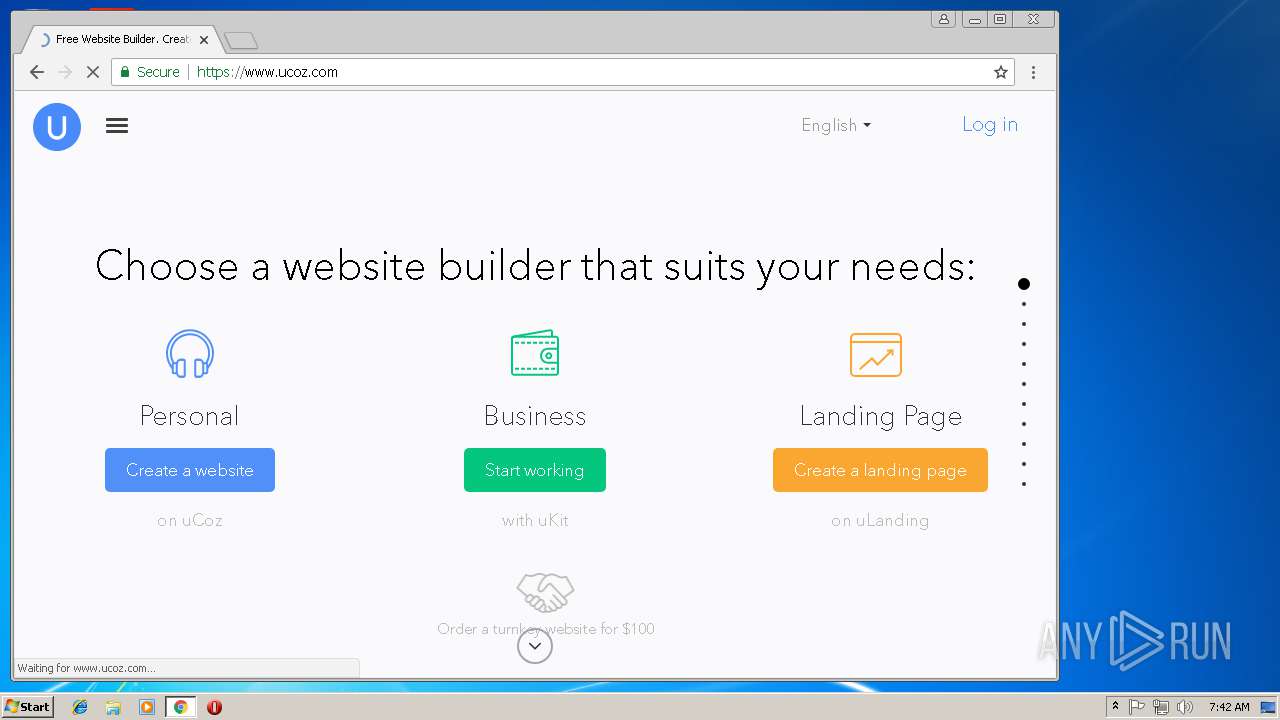
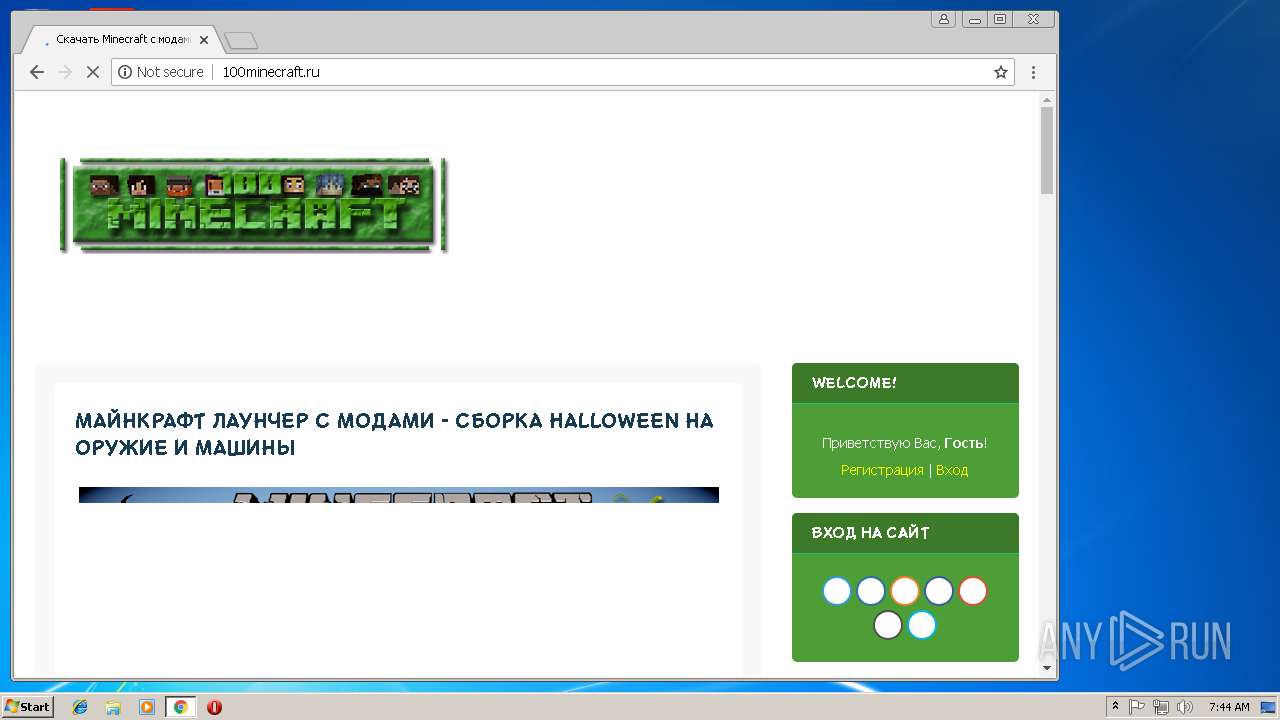
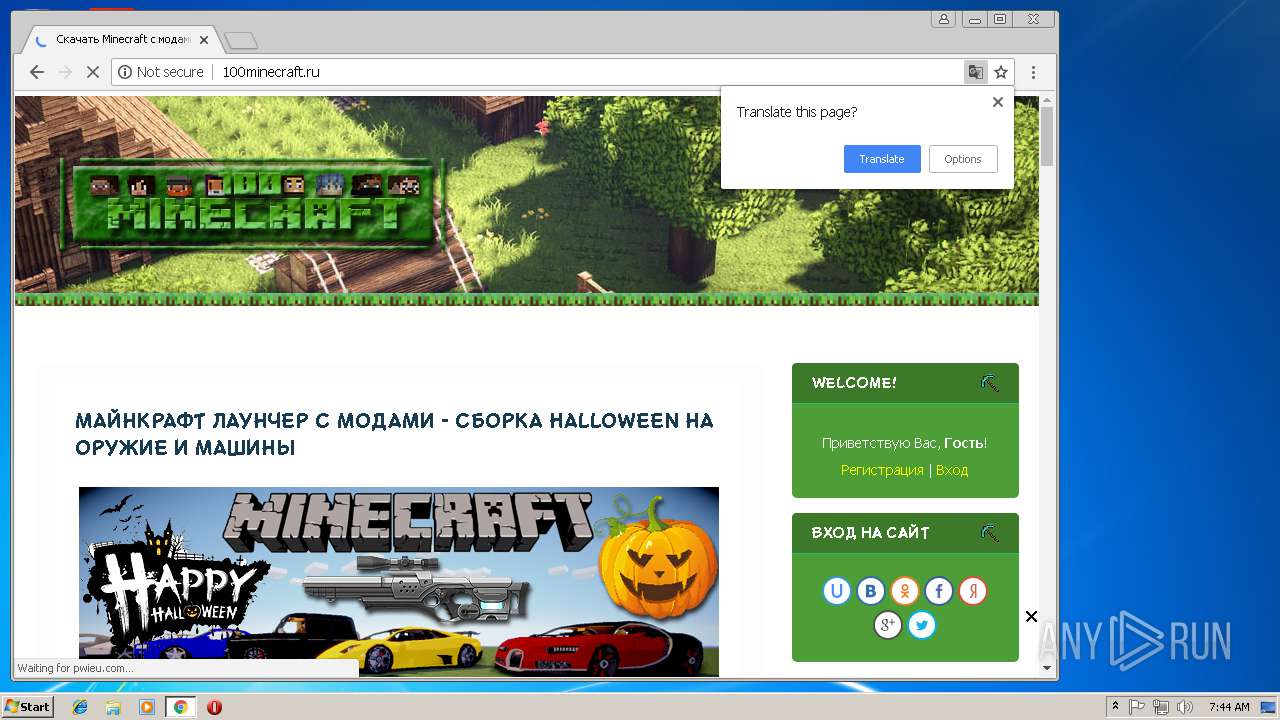
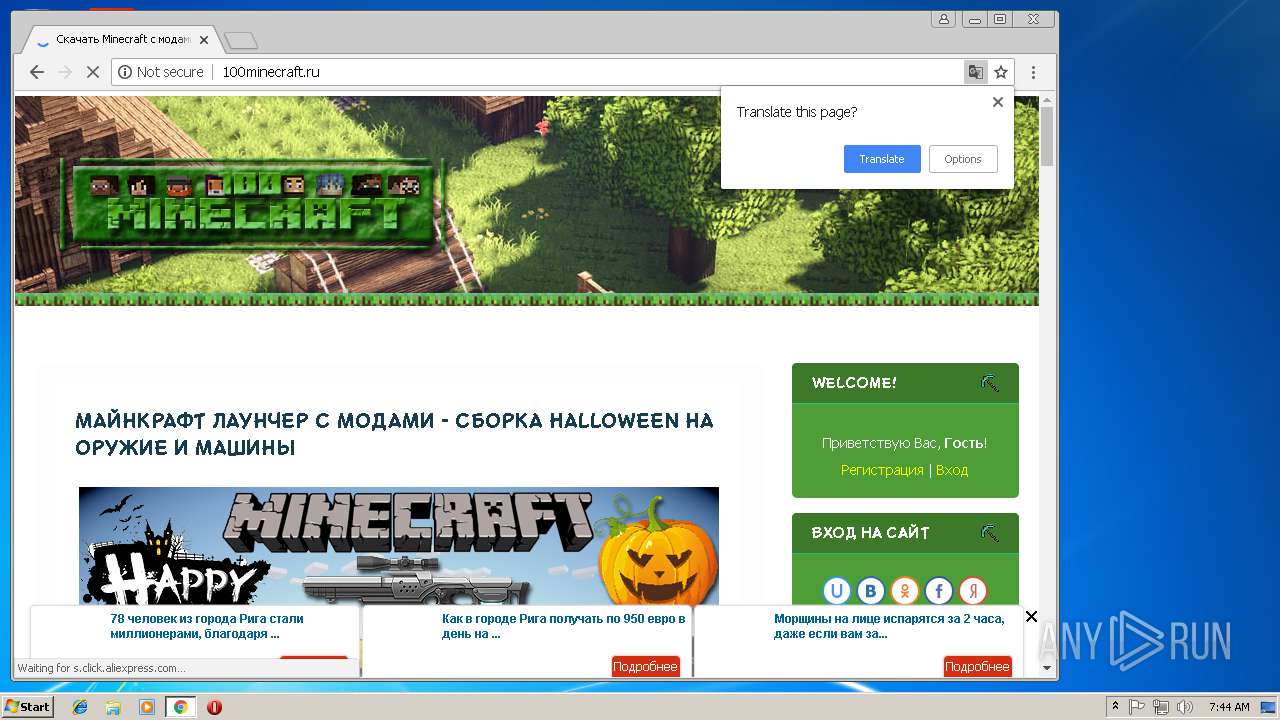
3148 | chrome.exe | GET | 200 | 193.109.247.229:80 | http://100minecraft.ru/so34nd3x/?ed8s8n3p=QTBlyYQOwTlFbSR19Igp3Hhnn9rqBV4YDD6Xzrx%5EuS%5EXUSSTWTBVWtkJks8KzCQZNZtxIVUIAhGEvOkyt1xhG2bOdDz6WfhxzyIPgs6GNliVAYA2%5EWhR18daVFeDvlr79IAP%5E3IS8CdN1QiHBPddSv0SNHpCO30o | RU | html | 705 b | suspicious |
3148 | chrome.exe | GET | 200 | 193.109.247.229:80 | http://100minecraft.ru/.s/src/ulightbox/ulightbox.min.css | RU | text | 1.50 Kb | suspicious |
3148 | chrome.exe | GET | 200 | 193.109.247.229:80 | http://100minecraft.ru/.s/src/base.css | RU | text | 4.88 Kb | suspicious |
3148 | chrome.exe | GET | 200 | 193.109.247.229:80 | http://100minecraft.ru/ | RU | html | 10.8 Kb | suspicious |
3148 | chrome.exe | GET | 200 | 193.109.247.229:80 | http://100minecraft.ru/.s/src/uwnd.min.js?2 | RU | text | 55.6 Kb | suspicious |
3148 | chrome.exe | GET | 200 | 193.109.247.229:80 | http://100minecraft.ru/.s/src/social.css | RU | text | 580 b | suspicious |
3148 | chrome.exe | GET | 200 | 193.109.247.229:80 | http://100minecraft.ru/.s/src/ulightbox/ulightbox.min.js | RU | text | 7.35 Kb | suspicious |
3148 | chrome.exe | GET | 200 | 193.109.247.229:80 | http://100minecraft.ru/img777/100minecraft-Logo-Site2.png | RU | image | 75.7 Kb | suspicious |
3148 | chrome.exe | GET | 200 | 172.217.168.34:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 27.3 Kb | whitelisted |
3148 | chrome.exe | GET | 200 | 193.109.247.229:80 | http://100minecraft.ru/.s/t/1703/ui.js | RU | text | 3.69 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3864 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 185.72.229.2:445 | s.rbk.ru | Rosbusinessconsulting Cjsc | RU | unknown |
3148 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
— | — | 80.68.253.2:137 | s.rbk.ru | Rosbusinessconsulting Cjsc | RU | unknown |
3148 | chrome.exe | 216.58.215.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.168.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 172.217.168.8:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 88.212.196.122:443 | counter.yadro.ru | United Network LLC | RU | unknown |
3148 | chrome.exe | 172.217.168.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 87.240.129.71:80 | vk.com | VKontakte Ltd | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s.rbk.ru |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
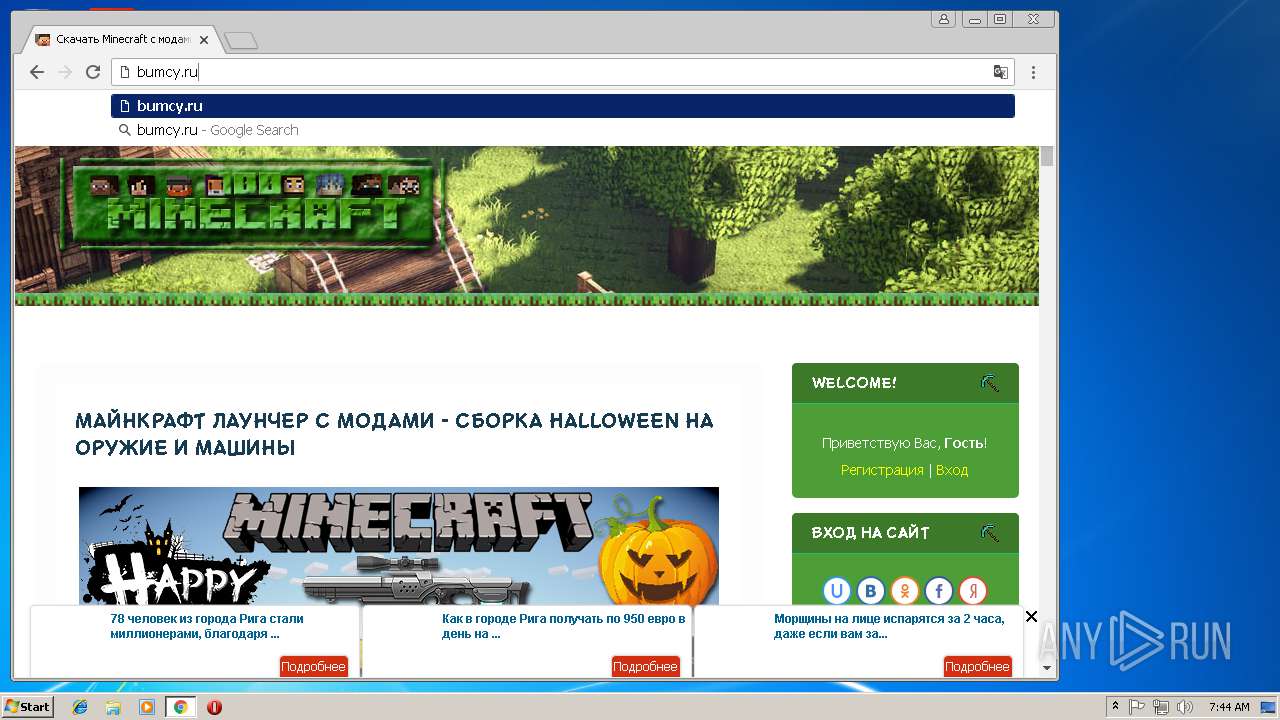
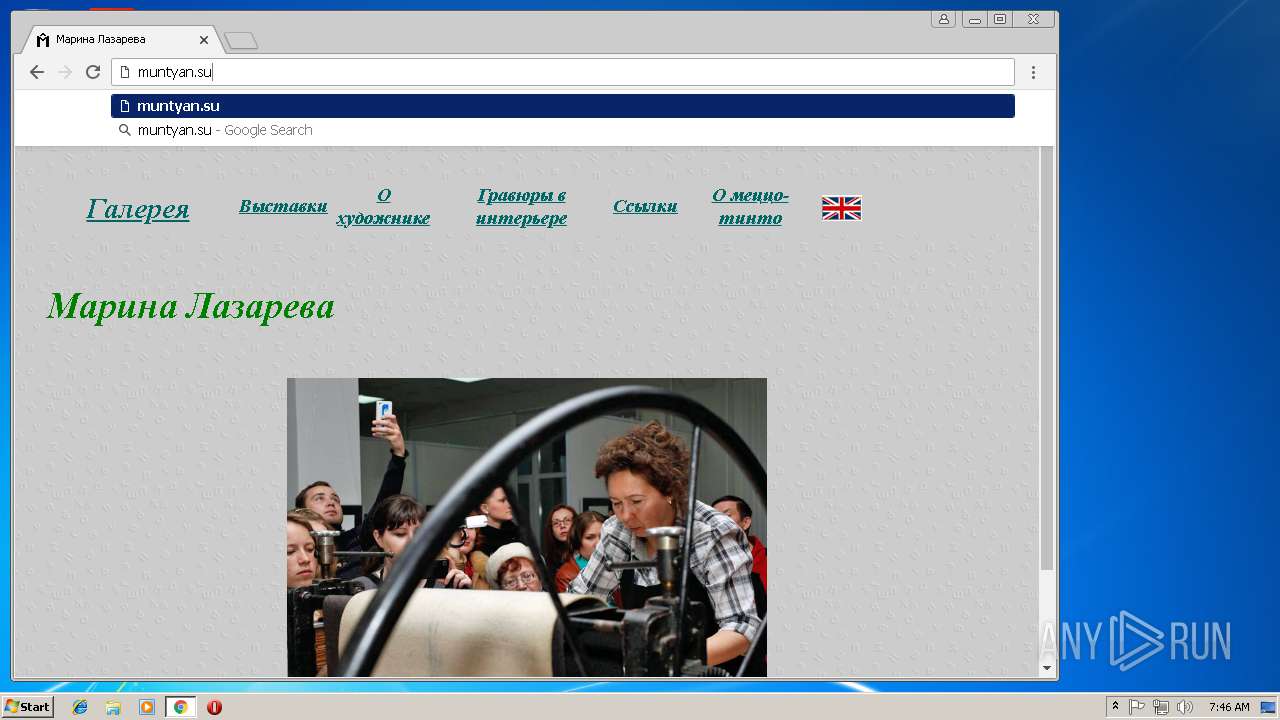
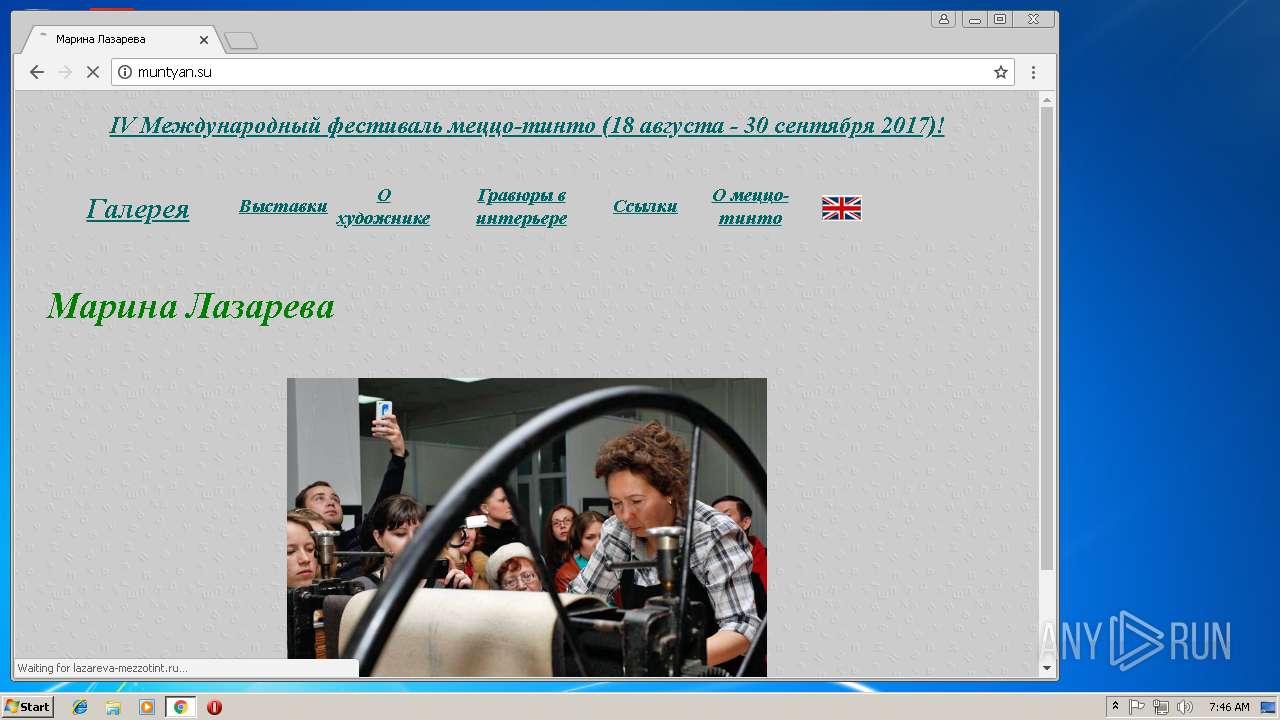
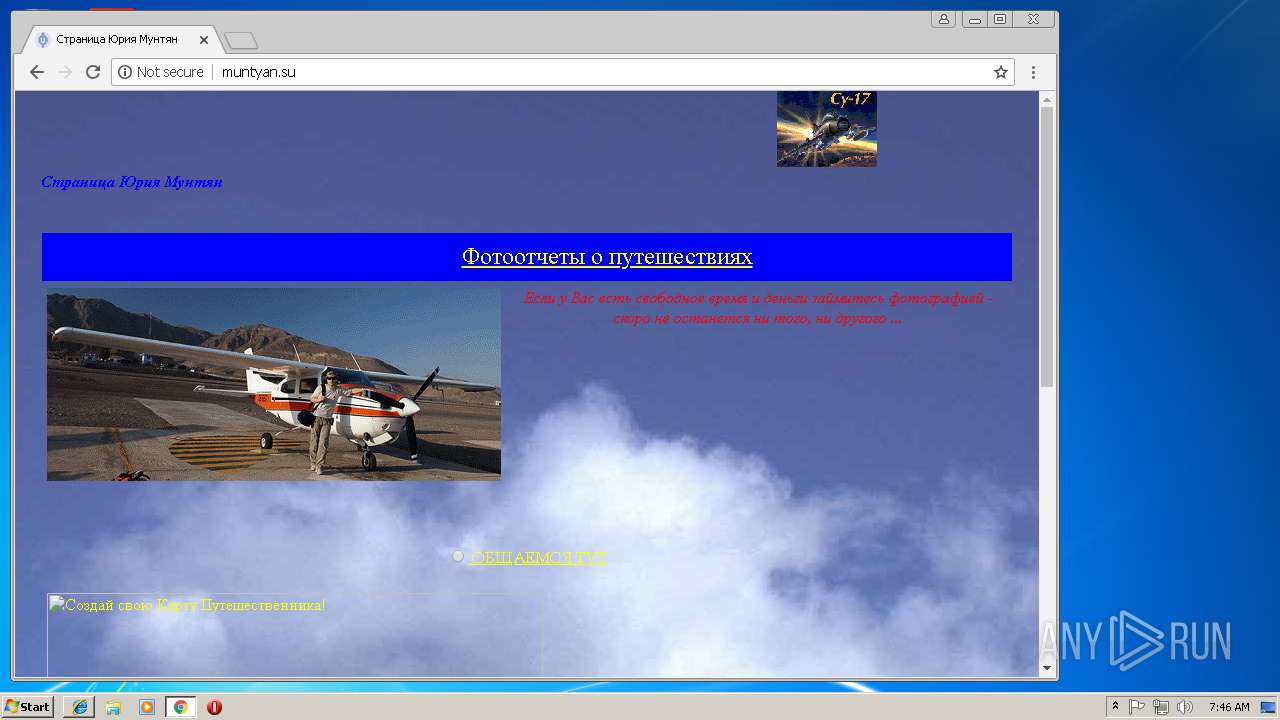
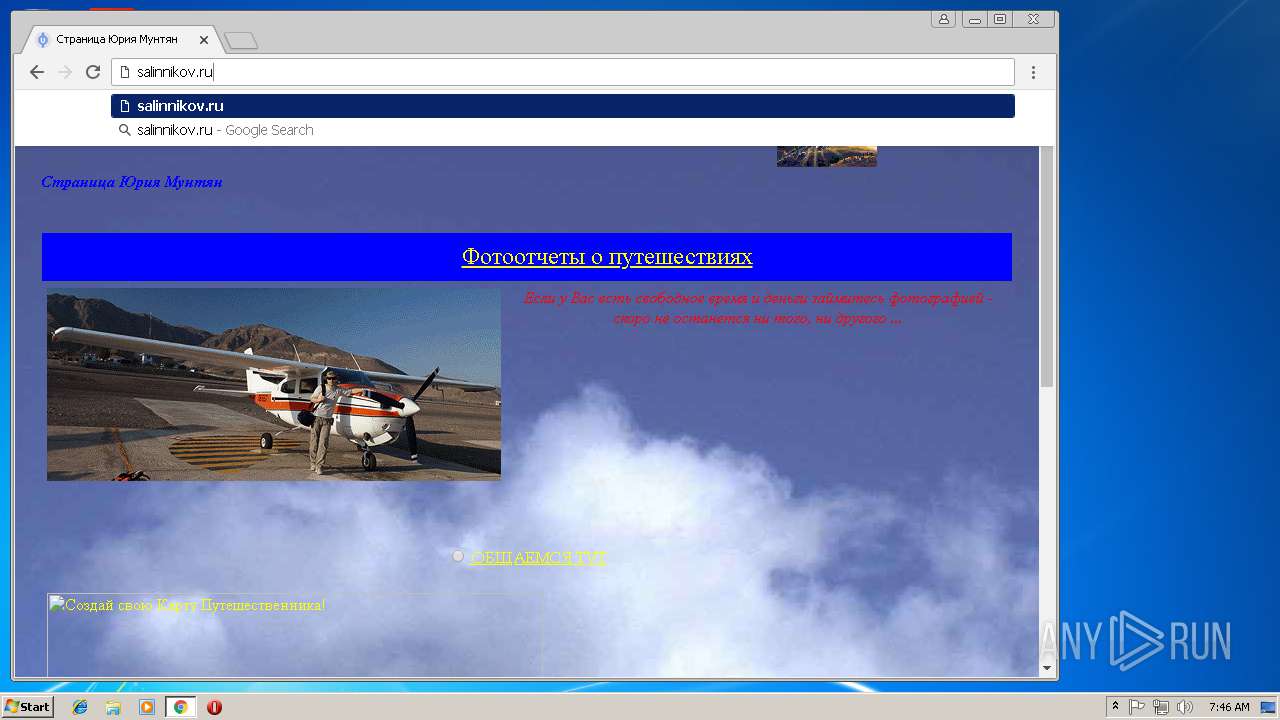
3148 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3148 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3148 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3148 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3148 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3148 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3148 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3148 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3148 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3148 | chrome.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |